| File name: | 2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701 |
| Full analysis: | https://app.any.run/tasks/b5556b13-69b7-49f8-bc32-e2d7d3291cae |
| Verdict: | Malicious activity |
| Analysis date: | April 21, 2020, 03:23:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | CD24BAFC660E5ECCF6BEF8F206E73566 |
| SHA1: | 33B702D4386D2A9FCA05B560486569181F0BB8D3 |
| SHA256: | 2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701 |
| SSDEEP: | 98304:xTQjRN3itmqGrg+Dt6yZD8Cr86vhUETykTJzKpKdPia/wr8pf/rD9vT0byQT:xTQv3i8pr7t6yXvhRFNWh2/f9voOQT |
MALICIOUS
Loads dropped or rewritten executable
- 2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701.exe (PID: 3928)
- BASupApp.exe (PID: 4052)
Application was dropped or rewritten from another process
- BASupApp.exe (PID: 4052)
SUSPICIOUS
Executable content was dropped or overwritten
- 2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701.exe (PID: 3928)
INFO
Dropped object may contain Bitcoin addresses
- 2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701.exe (PID: 3928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 05:20:09+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 120320 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x326c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Apr-2016 03:20:09 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Apr-2016 03:20:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C74 | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41039 |
.rdata | 0x00007000 | 0x00001196 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.20374 |
.data | 0x00009000 | 0x0001B058 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.13053 |
.ndata | 0x00025000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002D000 | 0x000480E8 | 0x00048200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.99044 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22372 | 947 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.39561 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 2.41163 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 2.77017 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 2.39653 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 1.93409 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 3.03674 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.71787 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
36
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3928 | "C:\Users\admin\AppData\Local\Temp\2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701.exe" | C:\Users\admin\AppData\Local\Temp\2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
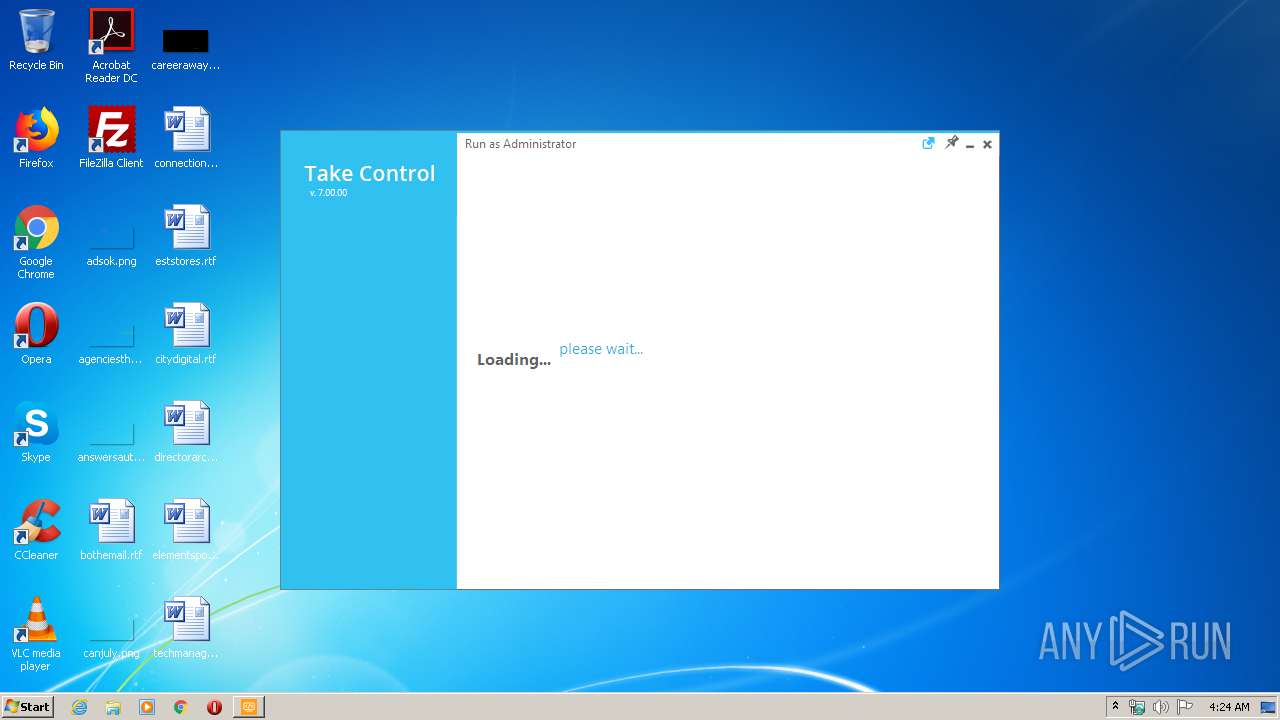
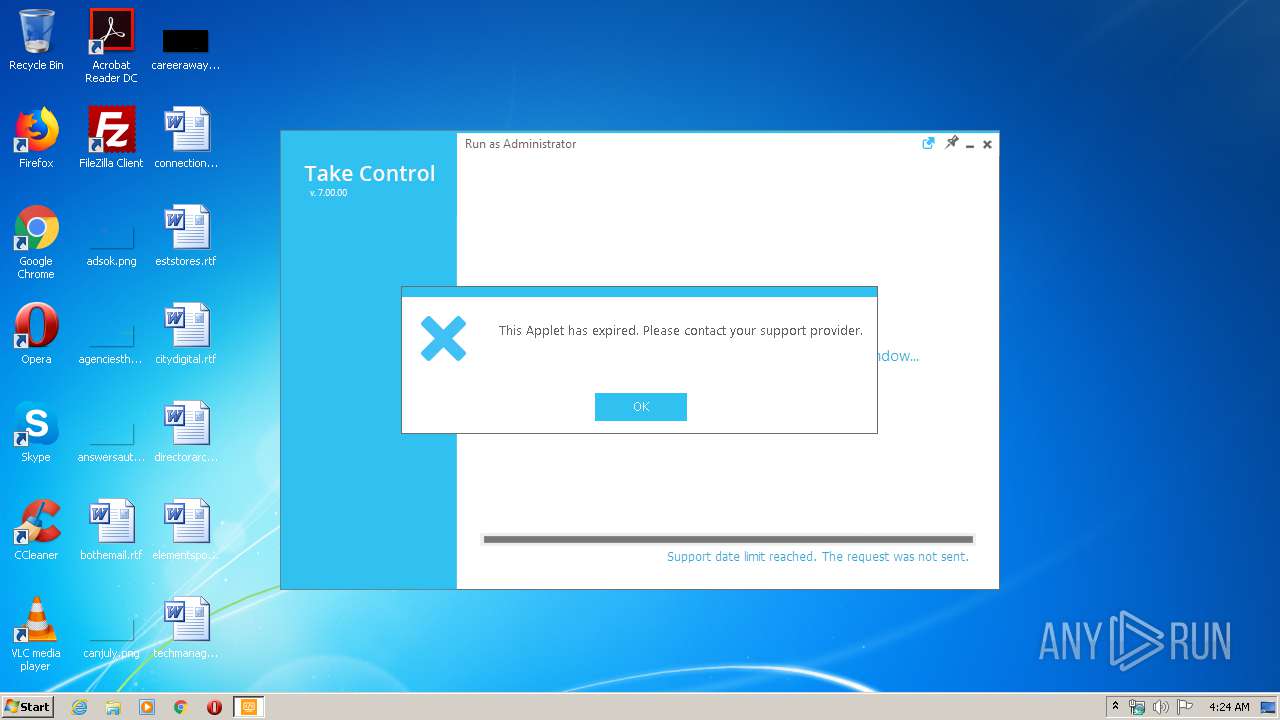
| 4052 | "C:\Users\admin\AppData\Local\BeAnywhere Support Express\GetSupport\BASupApp.exe" -from_installer | C:\Users\admin\AppData\Local\BeAnywhere Support Express\GetSupport\BASupApp.exe | 2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701.exe | ||||||||||||
User: admin Company: SolarWinds Take Control Integrity Level: MEDIUM Description: SolarWinds Take Control Applet Exit code: 0 Version: 7.0.0.1100 Modules
| |||||||||||||||
Total events
404
Read events
394
Write events
10
Delete events
0
Modification events
| (PID) Process: | (4052) BASupApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
65
Suspicious files
4
Text files
85
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3928 | 2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701.exe | C:\Users\admin\AppData\Local\Temp\nsqEF3C.tmp\System.dll | — | |
MD5:— | SHA256:— | |||
| 3928 | 2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701.exe | C:\Users\admin\AppData\Local\BeAnywhere Support Express\GetSupport\BASupRestoreBootSrvc.exe | executable | |
MD5:— | SHA256:— | |||
| 3928 | 2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701.exe | C:\Users\admin\AppData\Local\BeAnywhere Support Express\GetSupport\BASupSysShell.exe | executable | |
MD5:— | SHA256:— | |||
| 3928 | 2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701.exe | C:\Users\admin\AppData\Local\BeAnywhere Support Express\GetSupport\BASupApp.exe | executable | |
MD5:— | SHA256:— | |||
| 3928 | 2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701.exe | C:\Users\admin\AppData\Local\BeAnywhere Support Express\GetSupport\BASupAppSrvc.exe | executable | |
MD5:— | SHA256:— | |||
| 3928 | 2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701.exe | C:\Users\admin\AppData\Local\BeAnywhere Support Express\GetSupport\BASupSysShell64.exe | executable | |
MD5:— | SHA256:— | |||
| 3928 | 2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701.exe | C:\Users\admin\AppData\Local\BeAnywhere Support Express\GetSupport\BASupAppFR.dll | executable | |
MD5:— | SHA256:— | |||
| 3928 | 2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701.exe | C:\Users\admin\AppData\Local\BeAnywhere Support Express\GetSupport\BASupSysInf.exe | executable | |
MD5:— | SHA256:— | |||
| 3928 | 2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701.exe | C:\Users\admin\AppData\Local\BeAnywhere Support Express\GetSupport\BASupAppElev.exe | executable | |
MD5:— | SHA256:— | |||
| 3928 | 2276DA82D2A2D18C02BD9D45E1F0FA158D766C84809CDAC8A7A46E7F009E6701.exe | C:\Users\admin\AppData\Local\BeAnywhere Support Express\GetSupport\BAWHook.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4052 | BASupApp.exe | GET | 200 | 23.51.123.27:80 | http://s2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCED141%2Fl2SWCyYX308B7Khio%3D | NL | der | 1.71 Kb | whitelisted |
4052 | BASupApp.exe | GET | 200 | 23.51.123.27:80 | http://ocsp.thawte.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQJ1TBLBrQ9OnPHXPVaWb87MxkNlgQUwu79F9f%2Btw%2FGciJ7fvbA4gIz7D4CEH6T6%2Ft8xk5Z6kuad9QG%2FDs%3D | NL | der | 1.30 Kb | whitelisted |
4052 | BASupApp.exe | GET | 200 | 23.51.123.27:80 | http://ts-ocsp.ws.symantec.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRi82PVYYKWGJWdgVNyePy5kYTdqQQUX5r1blzMzHSa1N197z%2Fb7EyALt0CEA7P9DjI%2Fr81bgTYapgbGlA%3D | NL | der | 1.43 Kb | whitelisted |
4052 | BASupApp.exe | GET | 200 | 23.51.123.27:80 | http://sv.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQe6LNDJdqx%2BJOp7hVgTeaGFJ%2FCQgQUljtT8Hkzl699g%2B8uK8zKt4YecmYCEBxKAwiu6ahMg2xw0vULnD4%3D | NL | der | 1.57 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4052 | BASupApp.exe | 23.51.123.27:80 | s2.symcb.com | Akamai Technologies, Inc. | NL | whitelisted |
4052 | BASupApp.exe | 23.21.86.197:443 | comserver.corporate.beanywhere.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
s2.symcb.com |
| whitelisted |
sv.symcd.com |
| shared |
ocsp.thawte.com |
| whitelisted |
ts-ocsp.ws.symantec.com |
| whitelisted |
comserver.corporate.beanywhere.com |
| suspicious |