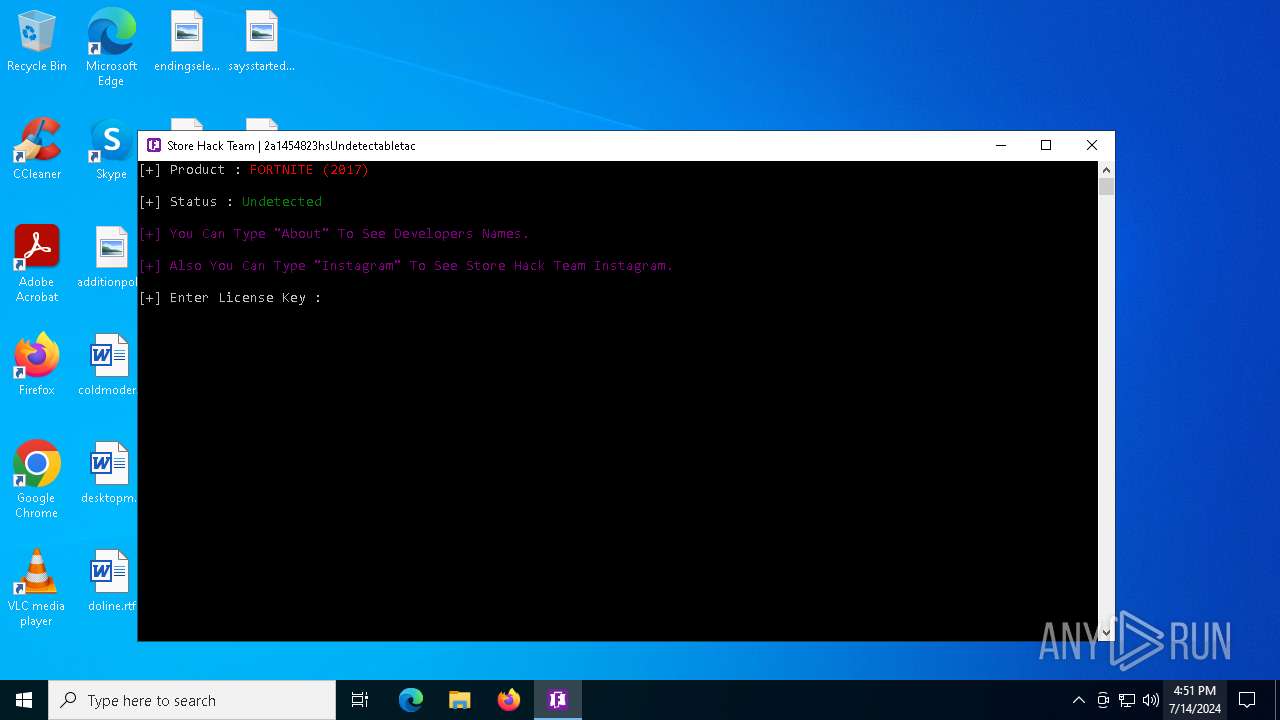
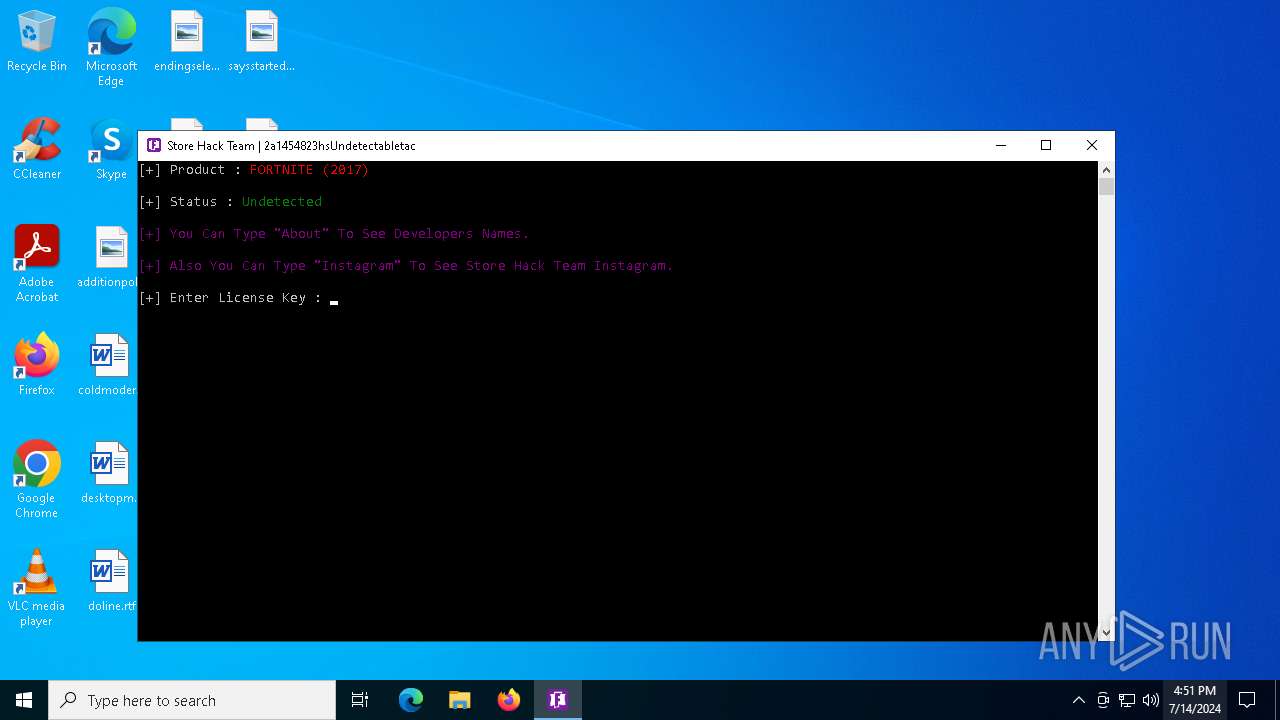
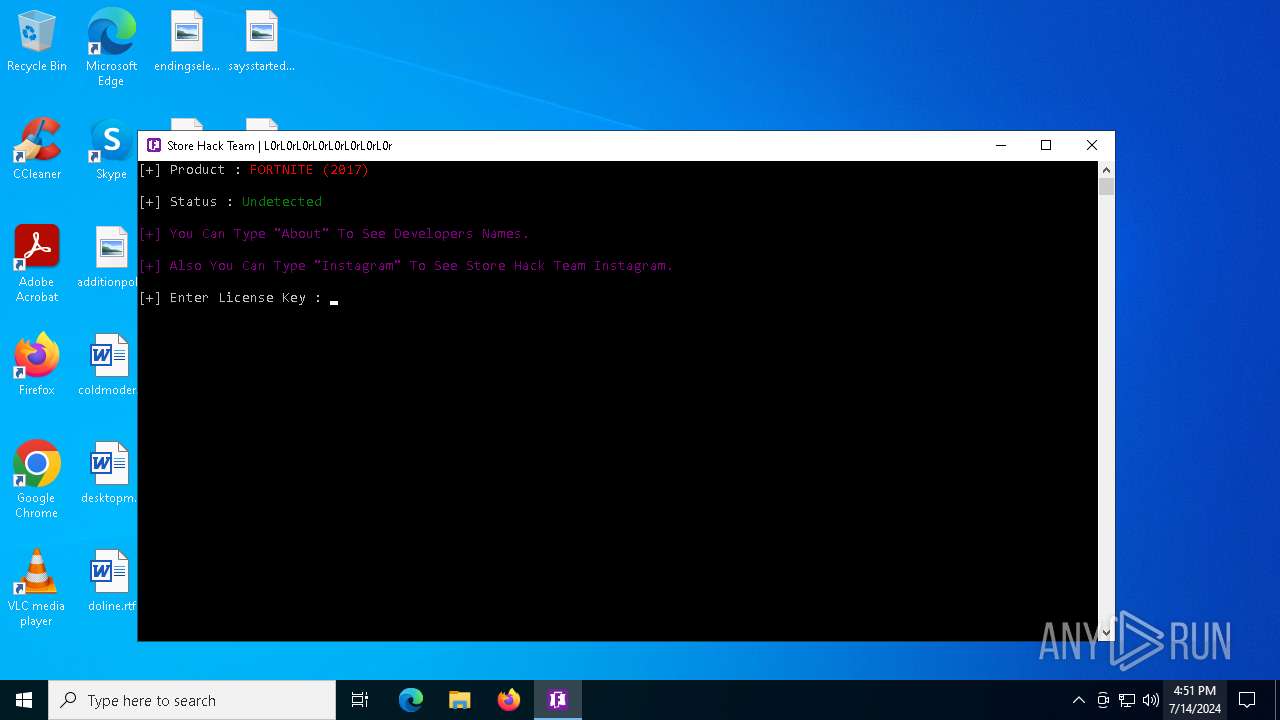
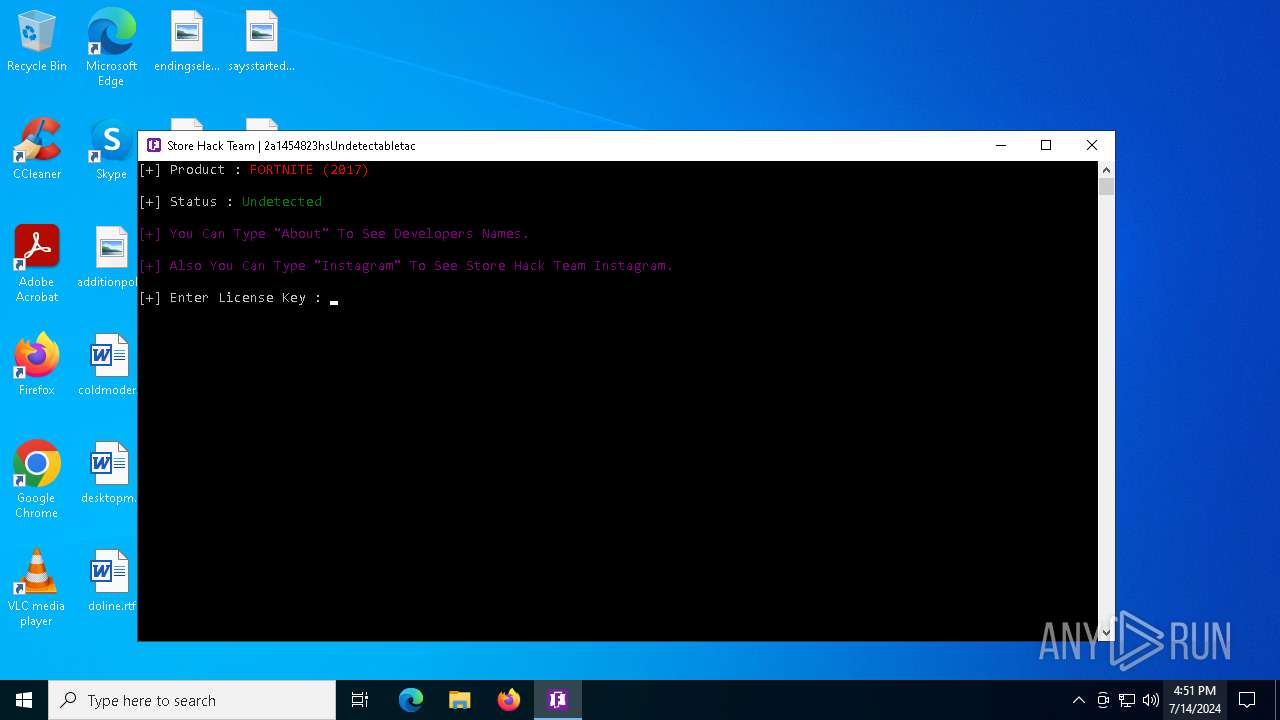
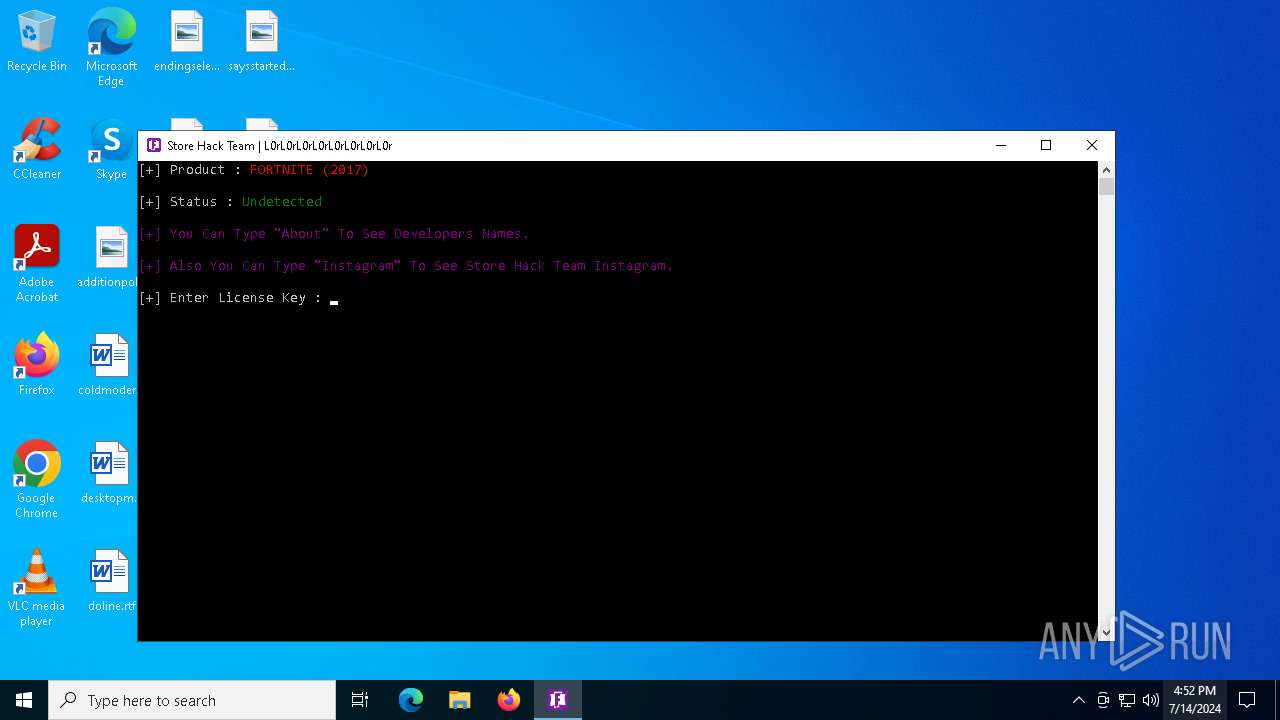
| File name: | Fortnite Hack.exe |
| Full analysis: | https://app.any.run/tasks/4e5dd6b1-a346-4aa6-8f24-f8f1f4246ca7 |
| Verdict: | Malicious activity |
| Analysis date: | July 14, 2024, 16:51:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 690B6178F5201B2AE4C6A004DA7ADF51 |
| SHA1: | A088C5F9CEC5368993BF261A94154A4B0ECC79EF |
| SHA256: | 226D0F9514ED305D80B63870F816C257E0C37CF3492895BBCC112B80590801DF |
| SSDEEP: | 3072:SkQYxW5zyWIhY+czb8Pc3IVv7pR6Qli086DB4:SkQYAzylYx8Ptp7po |
MALICIOUS
Drops the executable file immediately after the start
- Fortnite Hack.exe (PID: 1296)
- Hack Store.exe (PID: 7048)
Changes the autorun value in the registry
- Fortnite Hack.exe (PID: 1296)
Create files in the Startup directory
- taskhost.exe (PID: 6480)
Adds path to the Windows Defender exclusion list
- Fortnite Store.exe (PID: 884)
- cmd.exe (PID: 3128)
SUSPICIOUS
Reads the date of Windows installation
- Fortnite Hack.exe (PID: 1296)
- Hack Store.exe (PID: 6396)
- Hack Store.exe (PID: 7048)
Executable content was dropped or overwritten
- Fortnite Hack.exe (PID: 1296)
- Hack Store.exe (PID: 7048)
Reads security settings of Internet Explorer
- Hack Store.exe (PID: 6396)
- Fortnite Hack.exe (PID: 1296)
- Hack Store.exe (PID: 7048)
Application launched itself
- Hack Store.exe (PID: 6396)
The process creates files with name similar to system file names
- Fortnite Hack.exe (PID: 1296)
Starts CMD.EXE for commands execution
- Fortnite Store.exe (PID: 884)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3128)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 3128)
Connects to unusual port
- taskhost.exe (PID: 6480)
INFO
Reads the machine GUID from the registry
- Fortnite Hack.exe (PID: 1296)
- taskhost.exe (PID: 6480)
- Hack Store.exe (PID: 7048)
Create files in a temporary directory
- Fortnite Hack.exe (PID: 1296)
- Hack Store.exe (PID: 7048)
Checks supported languages
- Fortnite Hack.exe (PID: 1296)
- Hack Store.exe (PID: 6396)
- taskhost.exe (PID: 6480)
- Hack Store.exe (PID: 7048)
- Fortnite Store.exe (PID: 884)
Reads the computer name
- Fortnite Hack.exe (PID: 1296)
- Hack Store.exe (PID: 6396)
- taskhost.exe (PID: 6480)
- Hack Store.exe (PID: 7048)
Process checks computer location settings
- Hack Store.exe (PID: 6396)
- Fortnite Hack.exe (PID: 1296)
- Hack Store.exe (PID: 7048)
Creates files or folders in the user directory
- taskhost.exe (PID: 6480)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (64.5) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (13.6) |
| .exe | | | Win32 Executable (generic) (9.3) |
| .exe | | | Win16/32 Executable Delphi generic (4.2) |
| .exe | | | Generic Win/DOS Executable (4.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:05:15 06:00:58+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 88064 |
| InitializedDataSize: | 33280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2400a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.2.0.9 |
| ProductVersionNumber: | 3.2.0.9 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Instagram : Sotre Hack |
| FileDescription: | Store Hacker For Game |
| FileVersion: | 3.2.0.9 |
| InternalName: | Fortnite Hack.exe |
| LegalCopyright: | Copyright (C) 2020 |
| OriginalFileName: | Fortnite Hack.exe |
| ProductName: | Store Hack Fortnite for all Chapters |
| ProductVersion: | 3.2.0.9 |
| AssemblyVersion: | 3.2.0.9 |
Total processes
145
Monitored processes
11
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 884 | "C:\Users\admin\AppData\Local\Temp\Fortnite Store.exe" | C:\Users\admin\AppData\Local\Temp\Fortnite Store.exe | — | Hack Store.exe | |||||||||||
User: admin Company: Instagram : Sotre Hack Integrity Level: HIGH Description: Store Hacker For Game Version: 3.2.0.9 Modules
| |||||||||||||||
| 1120 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Fortnite Store.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | "C:\Users\admin\Desktop\Fortnite Hack.exe" | C:\Users\admin\Desktop\Fortnite Hack.exe | explorer.exe | ||||||||||||
User: admin Company: Instagram : Sotre Hack Integrity Level: MEDIUM Description: Store Hacker For Game Exit code: 0 Version: 3.2.0.9 Modules
| |||||||||||||||
| 3128 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\Temp\taskhost.exe'" | C:\Windows\SysWOW64\cmd.exe | — | Fortnite Store.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5344 | powershell -Command "Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\Temp\taskhost.exe'" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5960 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6396 | "C:\Users\admin\AppData\Local\Temp\Hack Store.exe" | C:\Users\admin\AppData\Local\Temp\Hack Store.exe | — | Fortnite Hack.exe | |||||||||||
User: admin Company: Instagram : Sotre Hack Integrity Level: MEDIUM Description: Store Hacker For Game Exit code: 0 Version: 3.2.0.9 Modules
| |||||||||||||||
| 6480 | "C:\Users\admin\AppData\Local\Temp\taskhost.exe" | C:\Users\admin\AppData\Local\Temp\taskhost.exe | Fortnite Hack.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Version: 1.0.0.0 Modules
| |||||||||||||||
| 6560 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6756 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\SysWOW64\cmd.exe | — | Fortnite Store.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 693
Read events
20 659
Write events
34
Delete events
0
Modification events
| (PID) Process: | (1296) Fortnite Hack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1296) Fortnite Hack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1296) Fortnite Hack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1296) Fortnite Hack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1296) Fortnite Hack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | taskhost |
Value: C:\Users\admin\AppData\Local\Temp\taskhost.exe | |||
| (PID) Process: | (1296) Fortnite Hack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (6396) Hack Store.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6396) Hack Store.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6396) Hack Store.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6396) Hack Store.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
3
Suspicious files
2
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7048 | Hack Store.exe | C:\Users\admin\AppData\Local\Temp\Fortnite Store.exe | executable | |
MD5:1A7144B53D2C1402759E730E2CECE8BC | SHA256:39475E2D7B8F90FD9226A41FC39E2B8AD7AA291AD3C9BFC4CF89FC42075D4C99 | |||
| 5344 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_q4yvw02s.12j.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5344 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_z05qylx0.m1z.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5344 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_m0joyipi.x5k.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5344 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:394E595314BEE729BAC9FA6A15399167 | SHA256:8325DB9A87D7C77DCE1D27F4318542758ABBFF73C09D8A06B08D5F9441411D46 | |||
| 6480 | taskhost.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\taskhost.lnk | lnk | |
MD5:129A4C1DDEB9B69E3A59040BD8332CDD | SHA256:4045C390F29717EF3108DD0609AE27F6309FC446A92222A64DD38811CC727D0F | |||
| 5344 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_va0kytr3.1zi.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1296 | Fortnite Hack.exe | C:\Users\admin\AppData\Local\Temp\taskhost.exe | executable | |
MD5:E248FE85AC55B289AC8EB79183EFA854 | SHA256:70171E6B5A338DAA730B4BE04DD84DF43B5ADA322357B0EA7F5D5CC10EB461BF | |||
| 1296 | Fortnite Hack.exe | C:\Users\admin\AppData\Local\Temp\Hack Store.exe | executable | |
MD5:EE36797C89C2DA5B08C29CF413C95378 | SHA256:002721D876E2BEF274958976E481564560B91240E155F94C8D214F6E0D866C5A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
74
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4392 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6192 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7144 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7144 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4392 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3716 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6180 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2056 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4656 | SearchApp.exe | 92.123.104.66:443 | www.bing.com | Akamai International B.V. | DE | unknown |
1376 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4392 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4392 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2168 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |