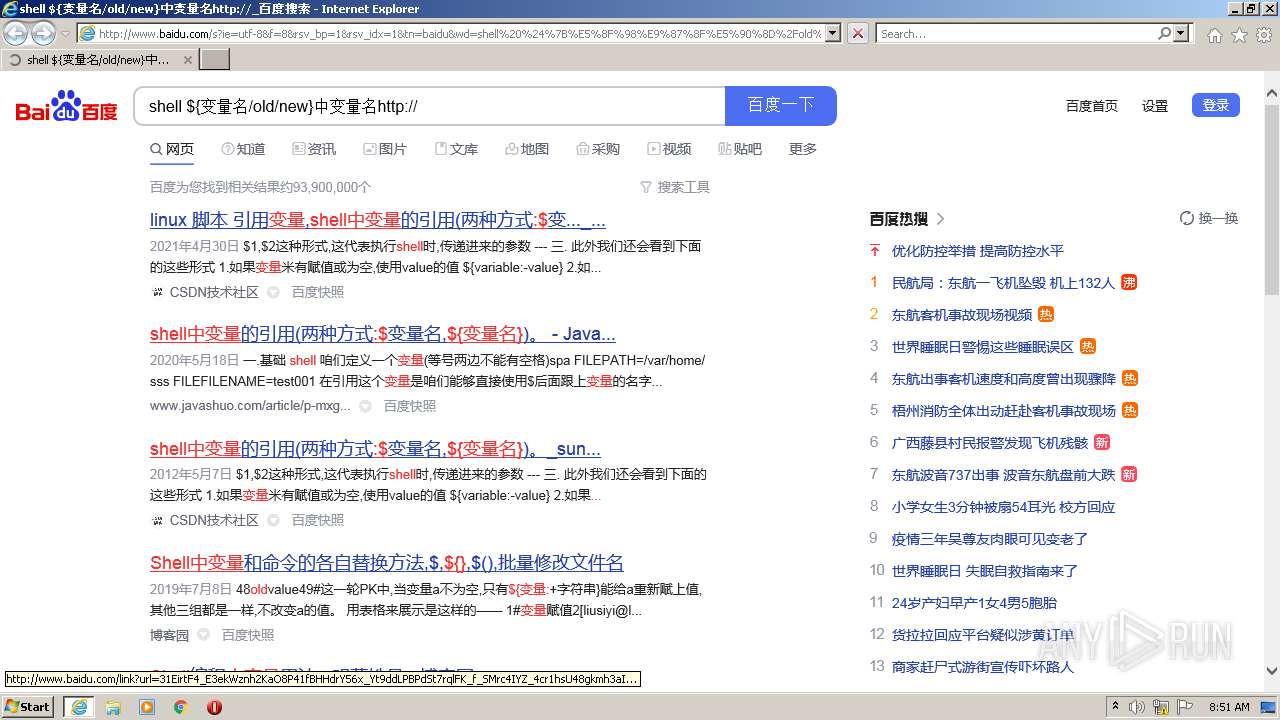
| URL: | http://www.baidu.com/s?ie=utf-8&f=8&rsv_bp=1&rsv_idx=1&tn=baidu&wd=shell%20%24%7B%E5%8F%98%E9%87%8F%E5%90%8D%2Fold%2Fnew%7D%E4%B8%AD%E5%8F%98%E9%87%8F%E5%90%8Dhttp%3A%2F%2F&fenlei=256&oq=shell%2520%2524%257B%25E5%258F%2598%25E9%2587%258F%25E5%2590%258D%252Fold%252Fnew%257D%25E5%25B8%25A6%252F%252F&rsv_pq=8fd9395d00017194&rsv_t=469fMqalms62fUM96vKOdsxylJ05VsGQ7CCBDgUyiS2wT6h3jF3T0bMmnCI&rqlang=cn&rsv_enter=1&rsv_dl=tb&rsv_sug3=41&rsv_sug1=6&rsv_sug7=100&rsv_sug2=0&rsv_btype=t&inputT=20072&rsv_sug4=20393 |
| Full analysis: | https://app.any.run/tasks/26d0377b-11f8-4d3c-9a90-b91ae05adedb |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2022, 08:50:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F15625411C7E2DFCF19F0813C73160AE |
| SHA1: | 5D7D6C1B0A4FC092955745E46DB084BEBCF89D3D |
| SHA256: | 226A0C4BE7473B114A93543E696C623313814ADD29A158702A3E3400CE9C86FF |
| SSDEEP: | 12:aDiLAuJnXuwn398svW6JQThuYyKeiMnLPE6nwjjR:IiLAuJnvQhuQernLP0jl |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3836)
- iexplore.exe (PID: 3228)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3080)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3080)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3080)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3080)
INFO
Checks supported languages
- iexplore.exe (PID: 3444)
- iexplore.exe (PID: 3836)
- iexplore.exe (PID: 3228)
Changes internet zones settings
- iexplore.exe (PID: 3444)
Checks Windows Trust Settings
- iexplore.exe (PID: 3228)
- iexplore.exe (PID: 3444)
- iexplore.exe (PID: 3836)
Creates files in the user directory
- iexplore.exe (PID: 3228)
- iexplore.exe (PID: 3444)
- iexplore.exe (PID: 3836)
Reads the computer name
- iexplore.exe (PID: 3836)
- iexplore.exe (PID: 3228)
- iexplore.exe (PID: 3444)
Reads internet explorer settings
- iexplore.exe (PID: 3836)
- iexplore.exe (PID: 3228)
Reads settings of System Certificates
- iexplore.exe (PID: 3836)
- iexplore.exe (PID: 3444)
- iexplore.exe (PID: 3228)
Changes settings of System certificates
- iexplore.exe (PID: 3444)
Reads CPU info
- iexplore.exe (PID: 3228)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3444)
Application launched itself
- iexplore.exe (PID: 3444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3080 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3228 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3444 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3444 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://www.baidu.com/s?ie=utf-8&f=8&rsv_bp=1&rsv_idx=1&tn=baidu&wd=shell%20%24%7B%E5%8F%98%E9%87%8F%E5%90%8D%2Fold%2Fnew%7D%E4%B8%AD%E5%8F%98%E9%87%8F%E5%90%8Dhttp%3A%2F%2F&fenlei=256&oq=shell%2520%2524%257B%25E5%258F%2598%25E9%2587%258F%25E5%2590%258D%252Fold%252Fnew%257D%25E5%25B8%25A6%252F%252F&rsv_pq=8fd9395d00017194&rsv_t=469fMqalms62fUM96vKOdsxylJ05VsGQ7CCBDgUyiS2wT6h3jF3T0bMmnCI&rqlang=cn&rsv_enter=1&rsv_dl=tb&rsv_sug3=41&rsv_sug1=6&rsv_sug7=100&rsv_sug2=0&rsv_btype=t&inputT=20072&rsv_sug4=20393" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3836 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3444 CREDAT:3216656 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
19 797
Read events
19 577
Write events
218
Delete events
2
Modification events
| (PID) Process: | (3444) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3444) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3444) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30948608 | |||
| (PID) Process: | (3444) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3444) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30948608 | |||
| (PID) Process: | (3444) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3444) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3444) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3444) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3444) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
21
Text files
206
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3228 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\II92HJOP.txt | text | |
MD5:— | SHA256:— | |||
| 3228 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\ULCAWSBV.txt | text | |
MD5:— | SHA256:— | |||
| 3228 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\R63W4T8F.txt | text | |
MD5:— | SHA256:— | |||
| 3228 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\H3CDIGAH.txt | text | |
MD5:— | SHA256:— | |||
| 3228 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\s[1].htm | html | |
MD5:— | SHA256:— | |||
| 3228 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\ACF244F1A10D4DBED0D88EBA0C43A9B5_16756CC7371BB76A269719AA1471E96C | der | |
MD5:— | SHA256:— | |||
| 3228 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\ACF244F1A10D4DBED0D88EBA0C43A9B5_16756CC7371BB76A269719AA1471E96C | binary | |
MD5:— | SHA256:— | |||
| 3228 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
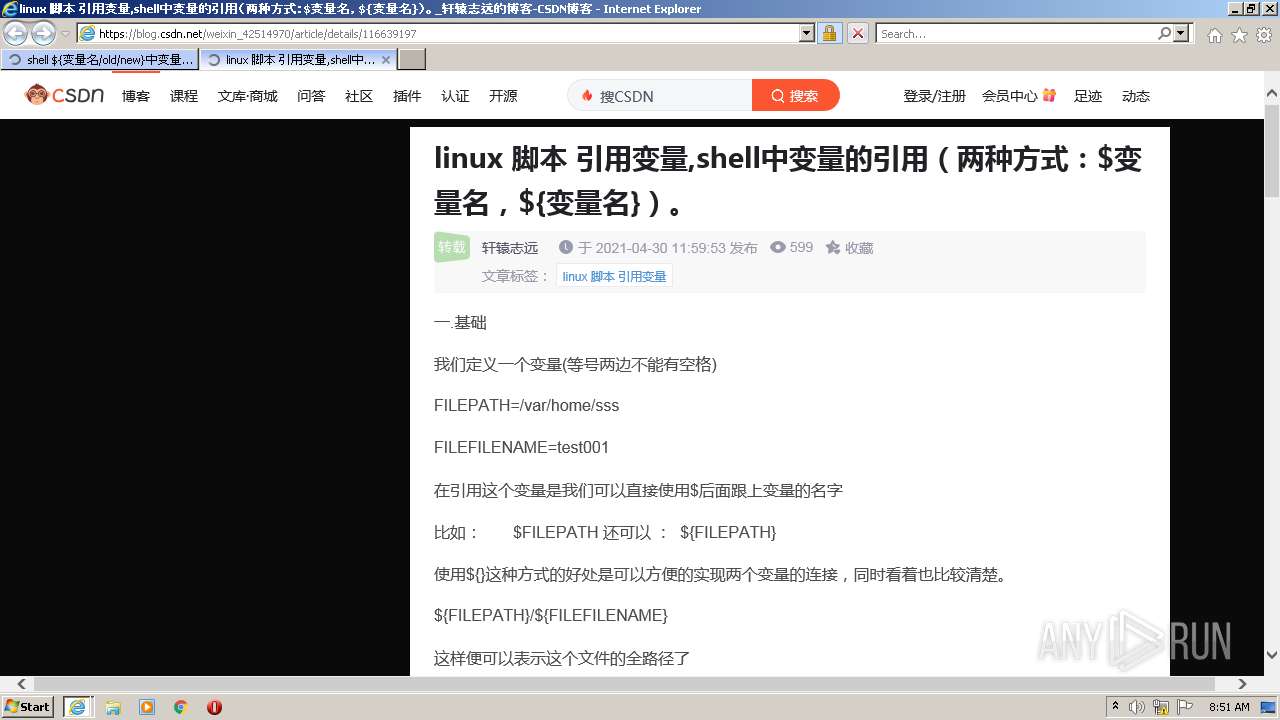
| 3228 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\cd37ed75a9387c5b[1].js | text | |
MD5:— | SHA256:— | |||
| 3228 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\u=188955431,3893600750&fm=195&app=88&f=JPEG[1].jpg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
208
DNS requests
48
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3228 | iexplore.exe | GET | 200 | 183.232.231.93:80 | http://sestat.baidu.com/wb.gif?type=3&fm=flow_monitor&data=%5B%7B%7D%5D&q=shell+%24%7B%B1%E4%C1%BF%C3%FB/old/new%7D%D6%D0%B1%E4%C1%BF%C3%FBhttp%3A//&qid=f9220e4000006b22&rsv_did=dff20609125da73a4148edbfc4ae9892&rsv_tn=baidu&rsv_sid=35104_31660_36086_34584_36141_36120_36034_35955_35326_26350_36100&t=1647852662692 | CN | — | — | whitelisted |
3228 | iexplore.exe | GET | 200 | 104.193.88.77:80 | http://www.baidu.com/s?ie=utf-8&f=8&rsv_bp=1&rsv_idx=1&tn=baidu&wd=shell%20%24%7B%E5%8F%98%E9%87%8F%E5%90%8D%2Fold%2Fnew%7D%E4%B8%AD%E5%8F%98%E9%87%8F%E5%90%8Dhttp%3A%2F%2F&fenlei=256&oq=shell%2520%2524%257B%25E5%258F%2598%25E9%2587%258F%25E5%2590%258D%252Fold%252Fnew%257D%25E5%25B8%25A6%252F%252F&rsv_pq=8fd9395d00017194&rsv_t=469fMqalms62fUM96vKOdsxylJ05VsGQ7CCBDgUyiS2wT6h3jF3T0bMmnCI&rqlang=cn&rsv_enter=1&rsv_dl=tb&rsv_sug3=41&rsv_sug1=6&rsv_sug7=100&rsv_sug2=0&rsv_btype=t&inputT=20072&rsv_sug4=20393 | US | html | 87.8 Kb | whitelisted |
3228 | iexplore.exe | GET | 200 | 103.235.46.39:80 | http://pcrec.baidu.com/link?url=31EirtF4_E3ekWznh2KaO8P41fBHHdrY56x_Yt9ddLPBPdSt7rqlFK_f_SMrc4IYZ_4cr1hsU48gkmh3aIVXmASnhN5F7zkP10r5beYuTV7&query=shell%20%24%7B%E5%8F%98%E9%87%8F%E5%90%8D%2Fold%2Fnew%7D%E4%B8%AD%E5%8F%98%E9%87%8F%E5%90%8Dhttp%3A%2F%2F&cb=jQuery110205804584000139847_1647852662333&data_name=recommend_common_merger_online&ie=utf-8&oe=utf-8&format=json&t=1647852663000&_=1647852662334 | HK | text | 111 b | malicious |
3228 | iexplore.exe | GET | 200 | 104.193.90.80:80 | http://pss.bdstatic.com/r/www/cache/static/soutu/css/soutu_new2_dd3a84f.css | US | text | 2.64 Kb | suspicious |
3228 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gsorganizationvalsha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQMnk2cPe3vhNiR6XLHz4QGvBl7BwQUlt5h8b0cFilTHMDMfTuDAEDmGnwCDBGYck9mdKPWIb%2B%2Bog%3D%3D | US | der | 1.42 Kb | whitelisted |
3228 | iexplore.exe | GET | 200 | 104.193.88.77:80 | http://www.baidu.com/sugrec?prod=pc_his&from=pc_web&json=1&sid=35104_31660_36086_34584_36141_36120_36034_35955_35326_26350_36100&hisdata=&_t=1647852662985&req=2&bs=shell%20%24%7B%E5%8F%98%E9%87%8F%E5%90%8D%2Fold%2Fnew%7D%E4%B8%AD%E5%8F%98%E9%87%8F%E5%90%8Dhttp%3A%2F%2F&csor=0 | US | binary | 53 b | whitelisted |
3444 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3228 | iexplore.exe | GET | 200 | 182.107.80.38:80 | http://hectorstatic.baidu.com/cd37ed75a9387c5b.js | CN | text | 14.4 Kb | suspicious |
3228 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/MEwwSjBIMEYwRDAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCCwQAAAAAAURO8EJH | US | der | 1.41 Kb | whitelisted |
3228 | iexplore.exe | GET | 200 | 104.193.90.80:80 | http://pss.bdstatic.com/r/www/cache/static/home/js/nu_instant_search_ac49315.js | US | html | 6.76 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3228 | iexplore.exe | 104.193.88.77:80 | www.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | US | malicious |
3228 | iexplore.exe | 104.193.90.87:443 | ss1.baidu.com | — | US | unknown |
3228 | iexplore.exe | 104.193.90.80:443 | pss.bdstatic.com | — | US | unknown |
3228 | iexplore.exe | 182.107.80.38:80 | hectorstatic.baidu.com | No.31,Jin-rong Street | CN | unknown |
3228 | iexplore.exe | 8.253.207.121:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3444 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3228 | iexplore.exe | 104.18.21.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
3228 | iexplore.exe | 104.18.20.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
3444 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3228 | iexplore.exe | 183.232.231.93:80 | sestat.baidu.com | China Mobile communications corporation | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.baidu.com |
| whitelisted |
ss1.baidu.com |
| whitelisted |
ss0.baidu.com |
| whitelisted |
pss.bdstatic.com |
| suspicious |
hectorstatic.baidu.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |