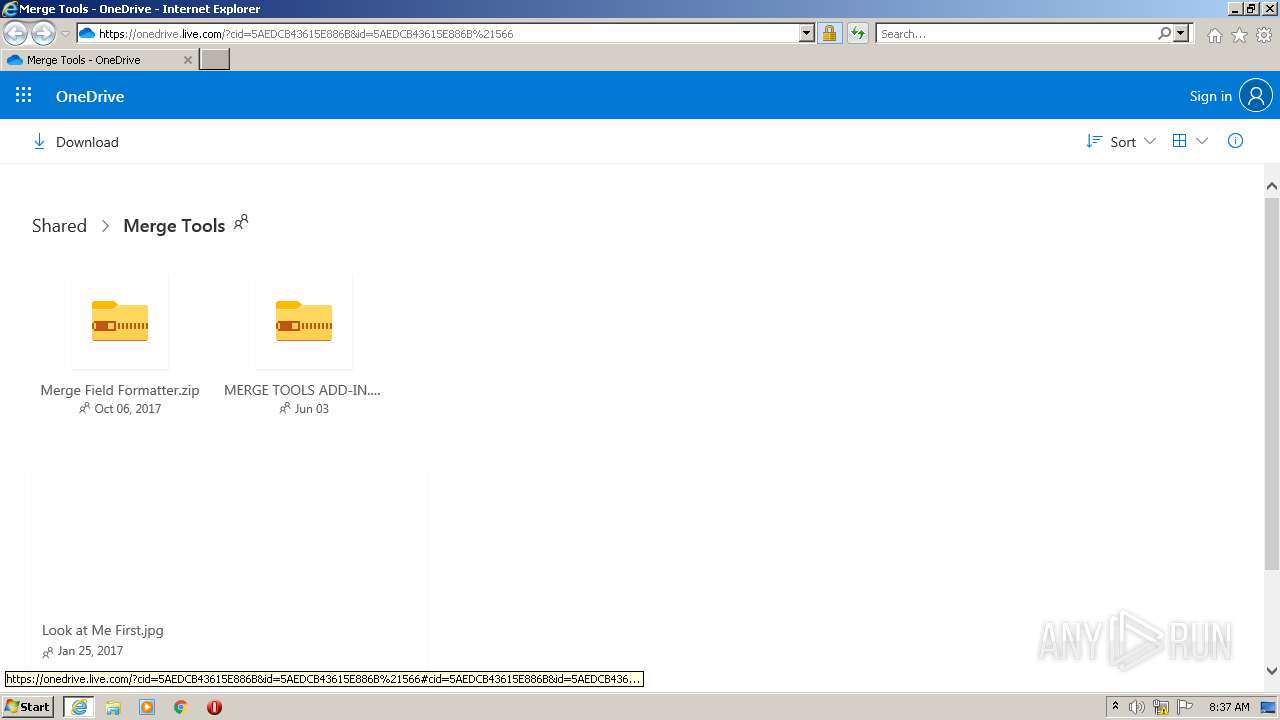
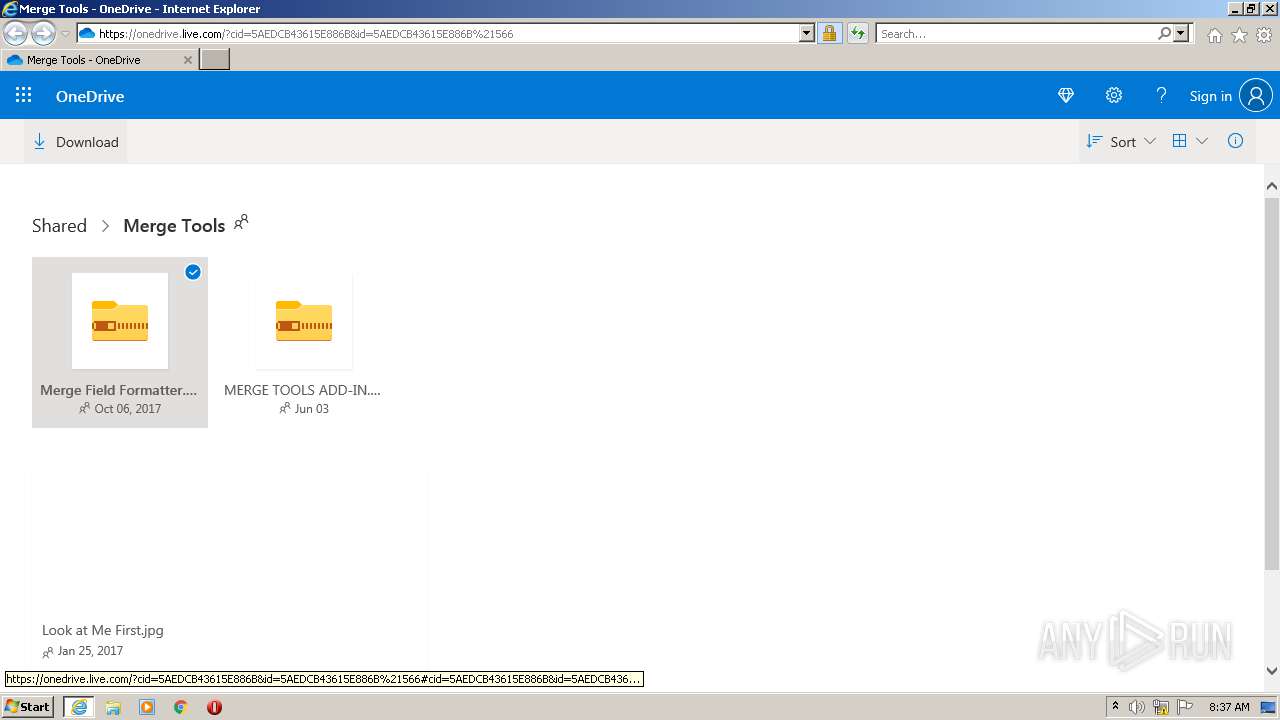
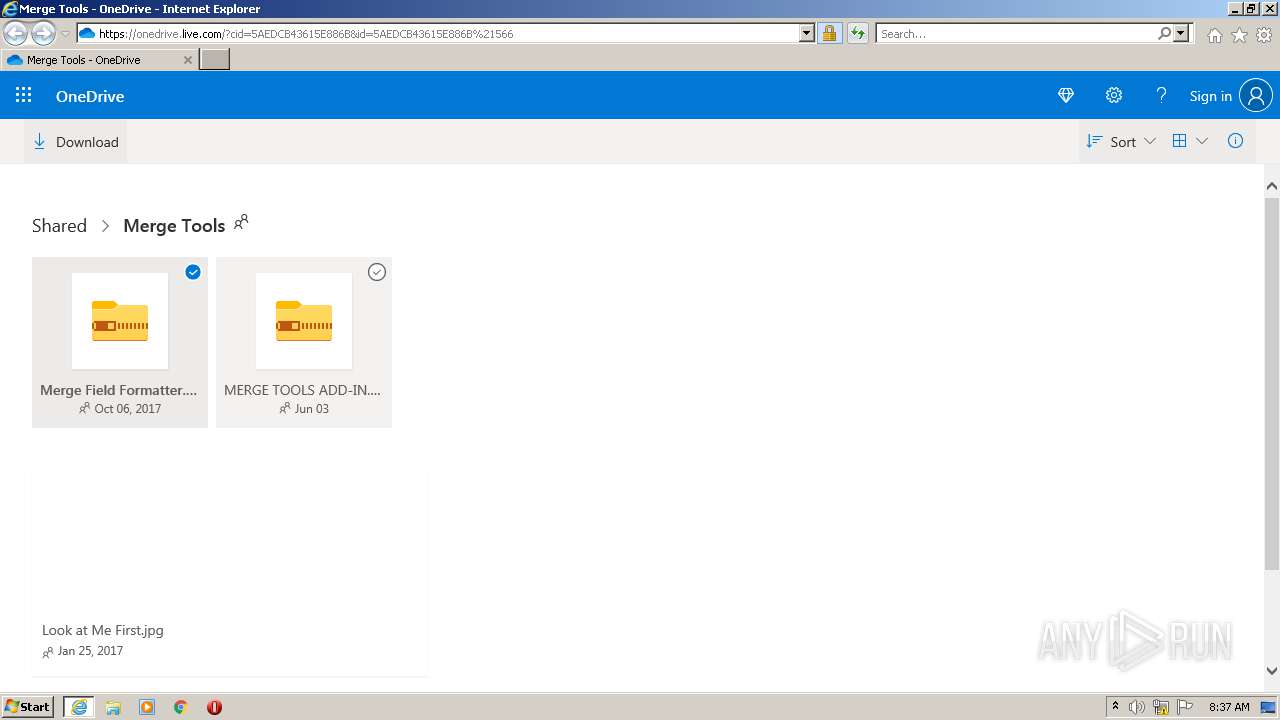
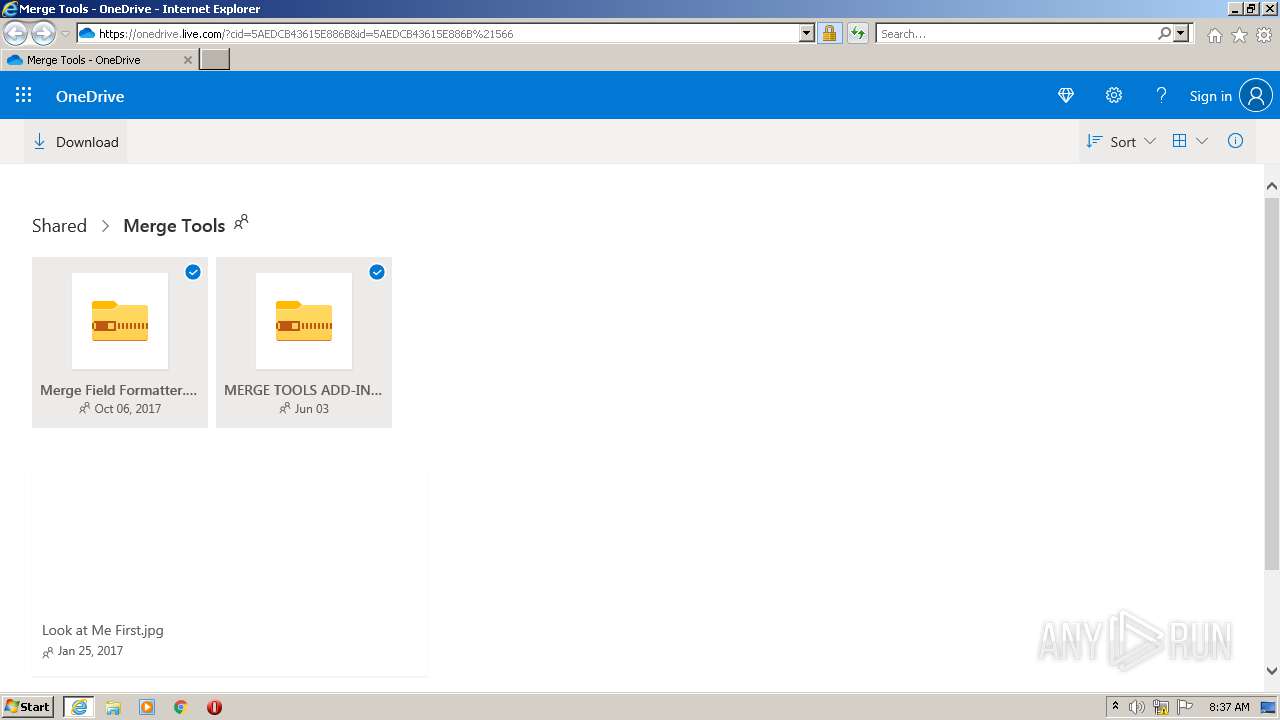
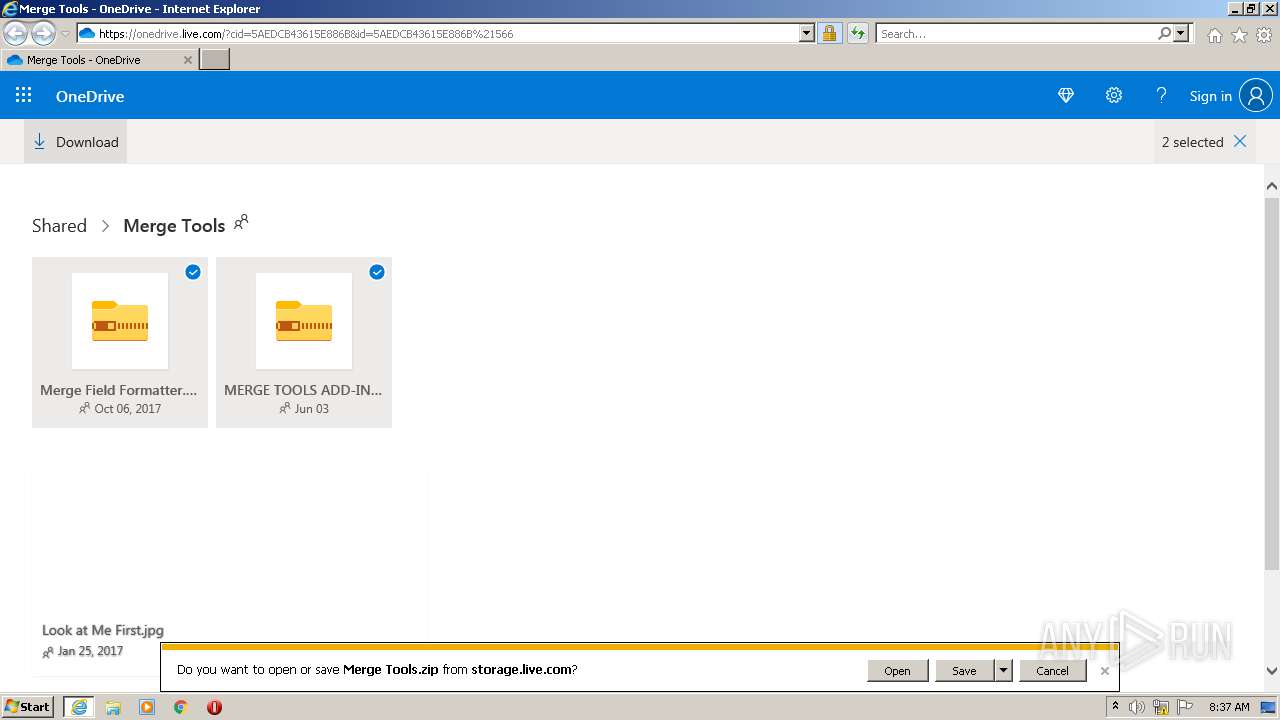
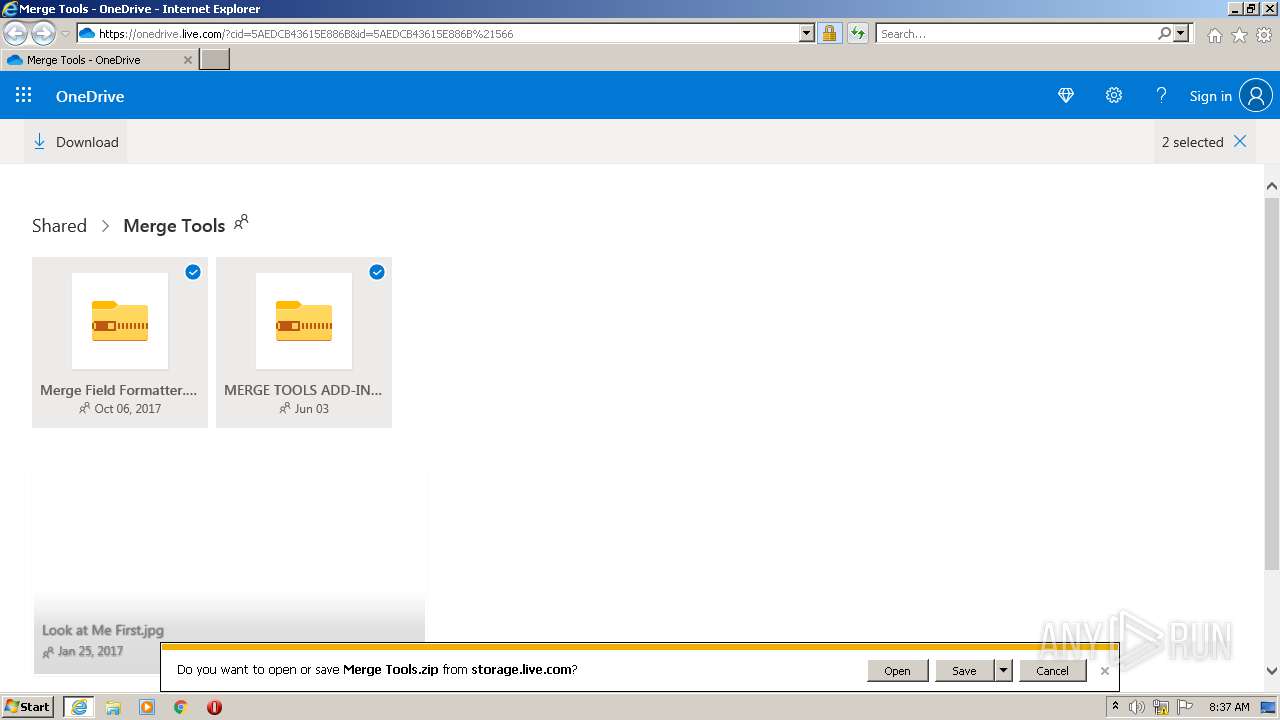
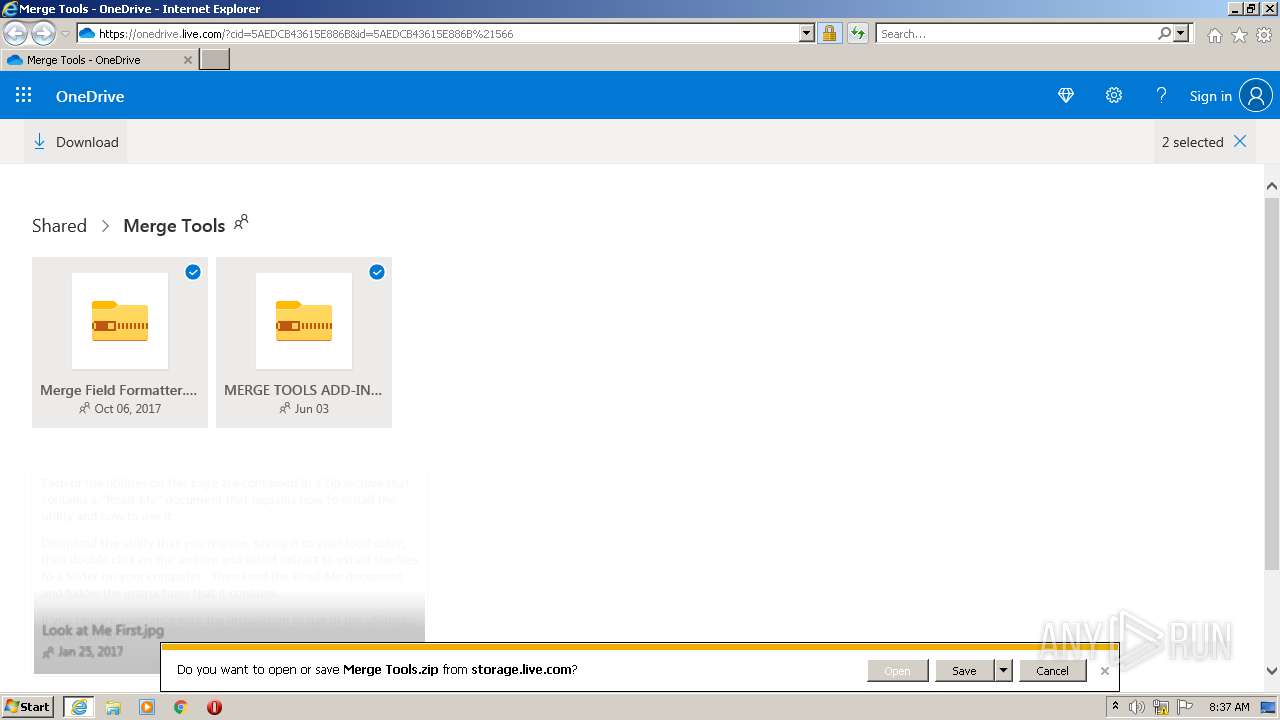
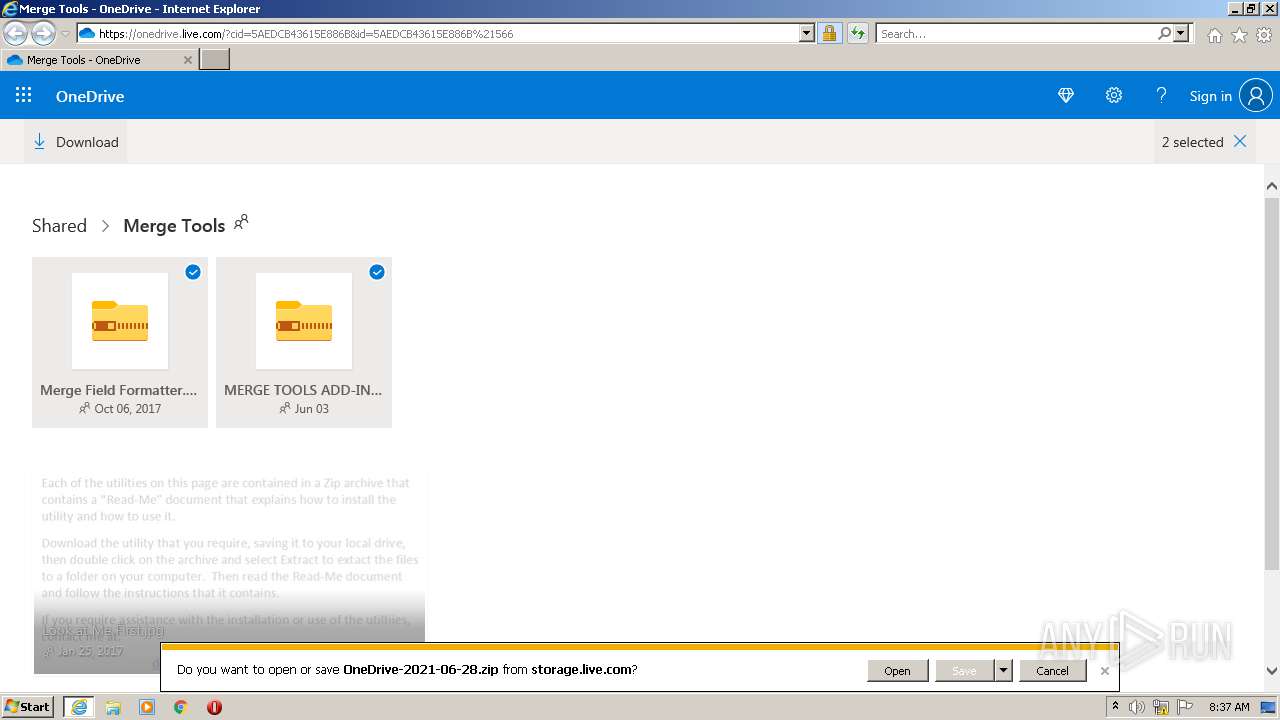
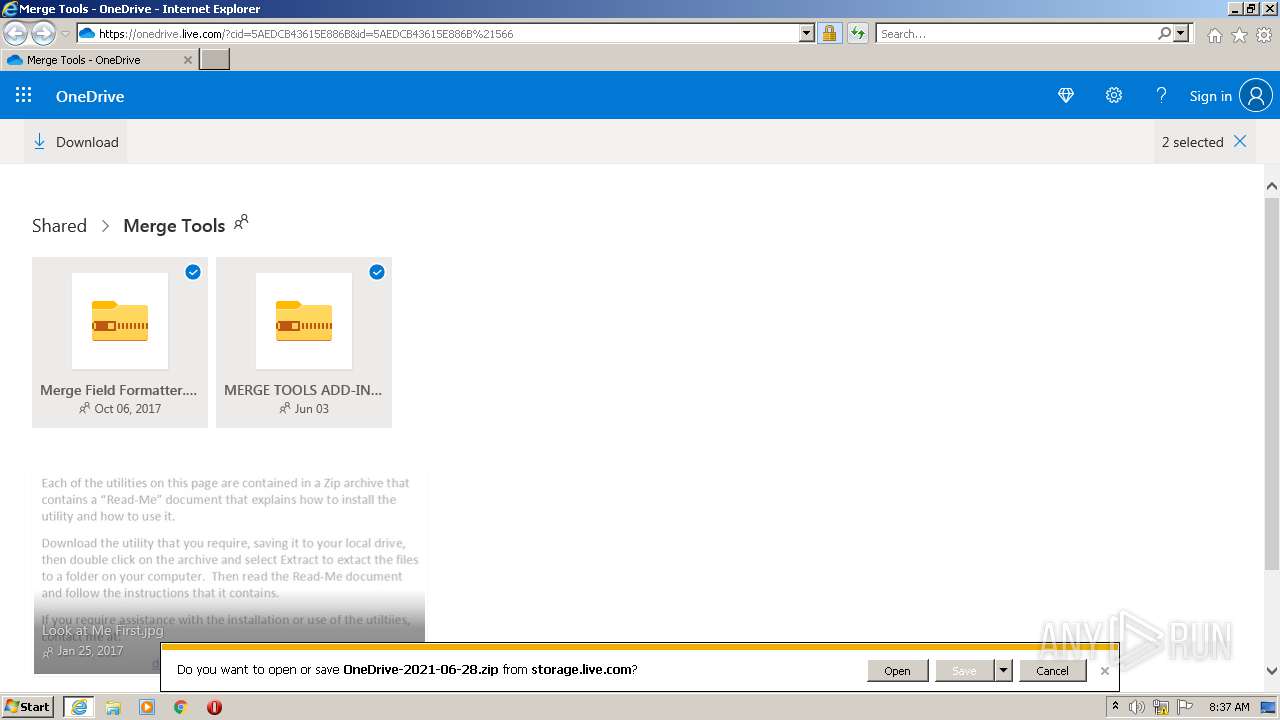
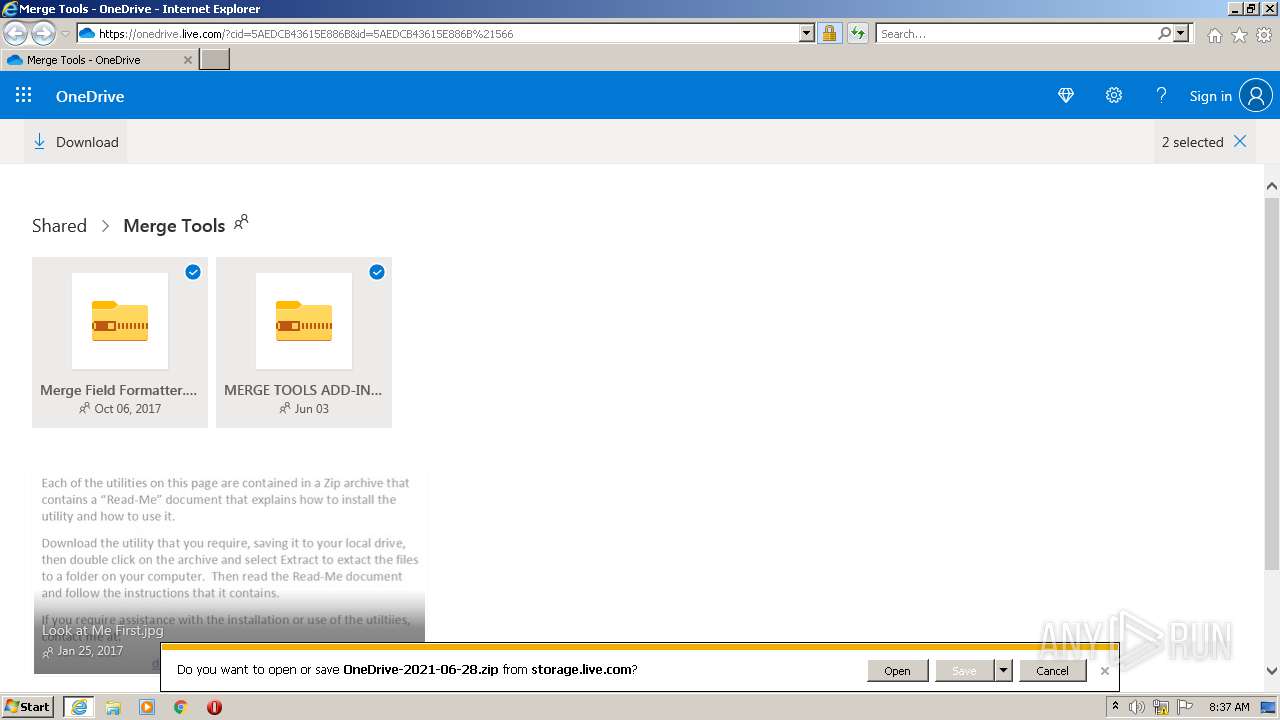
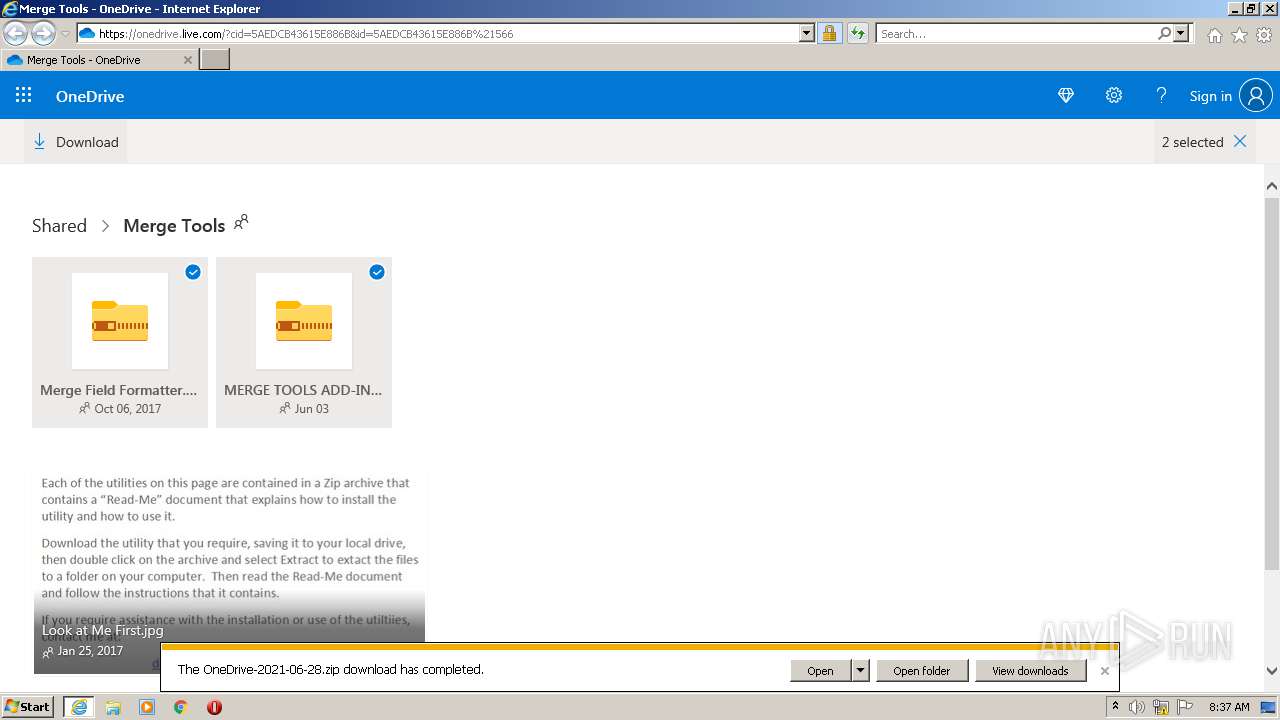
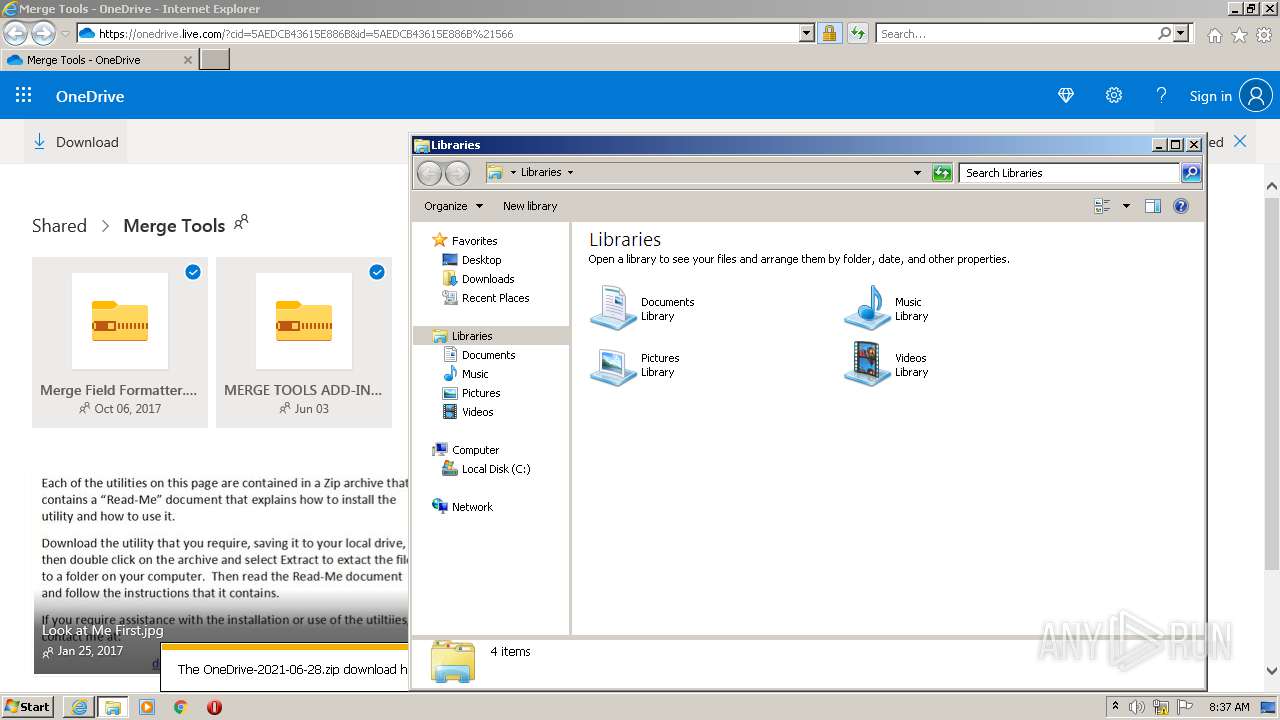
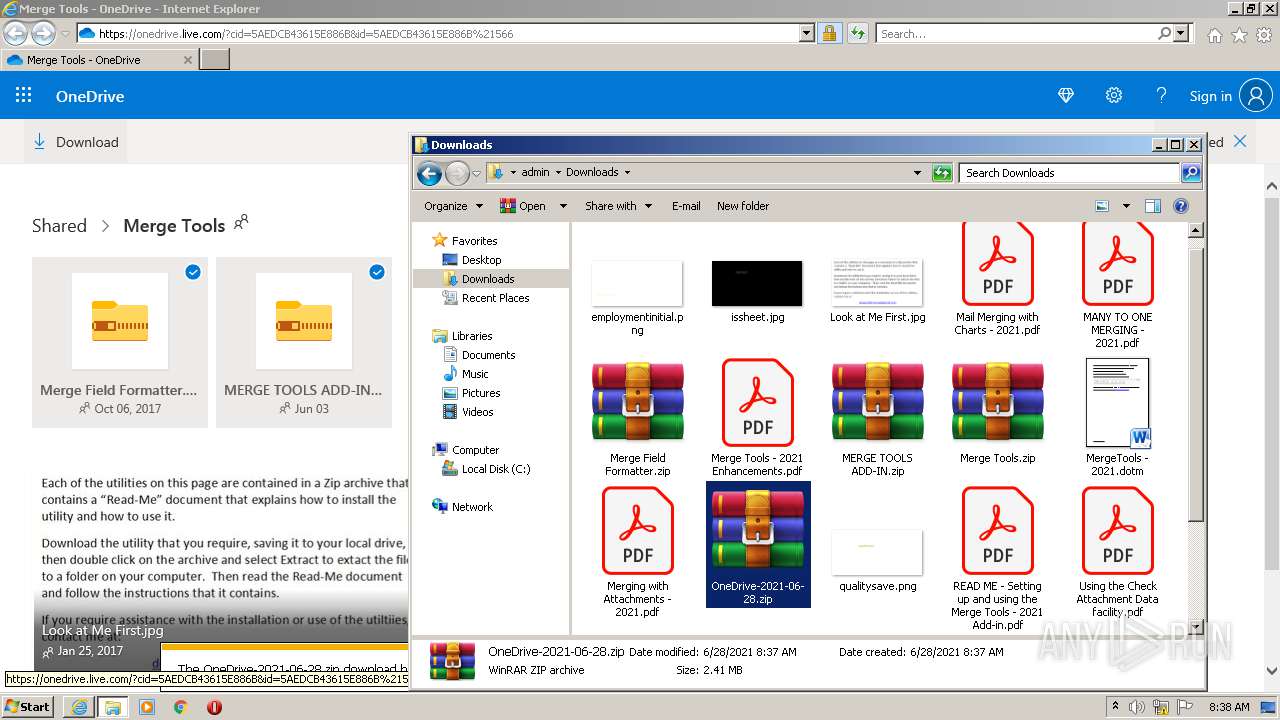
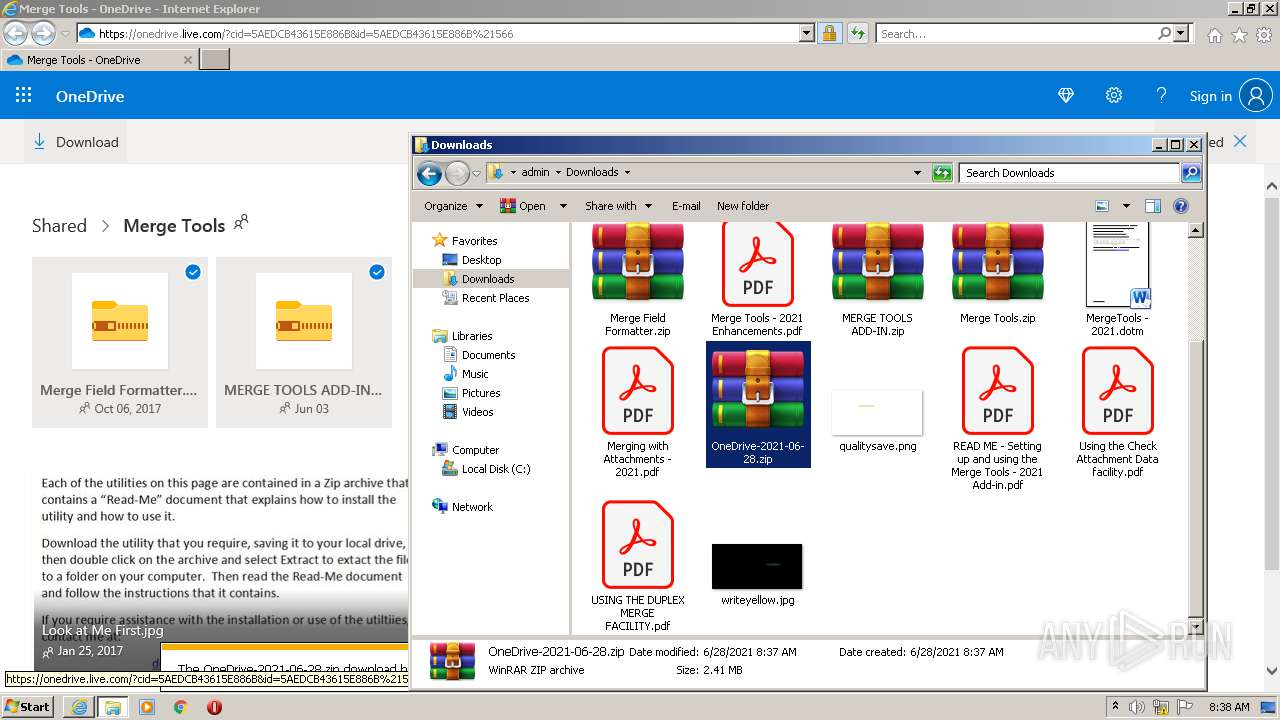
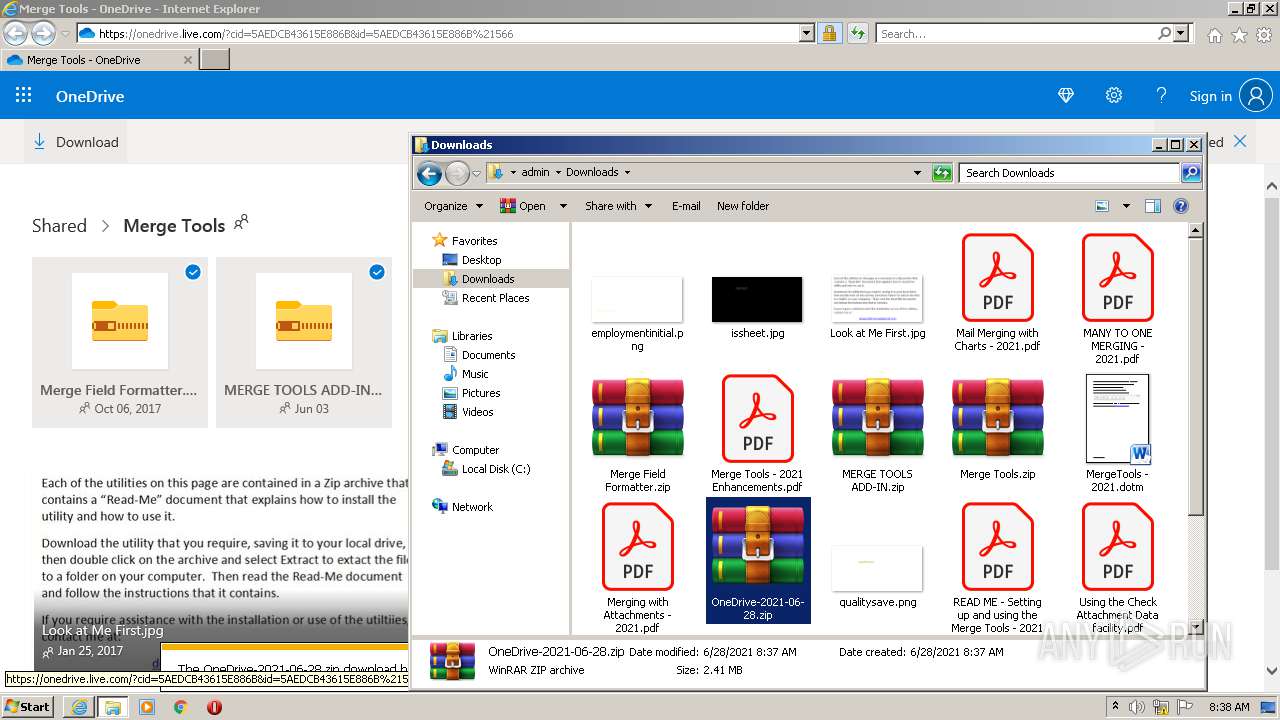
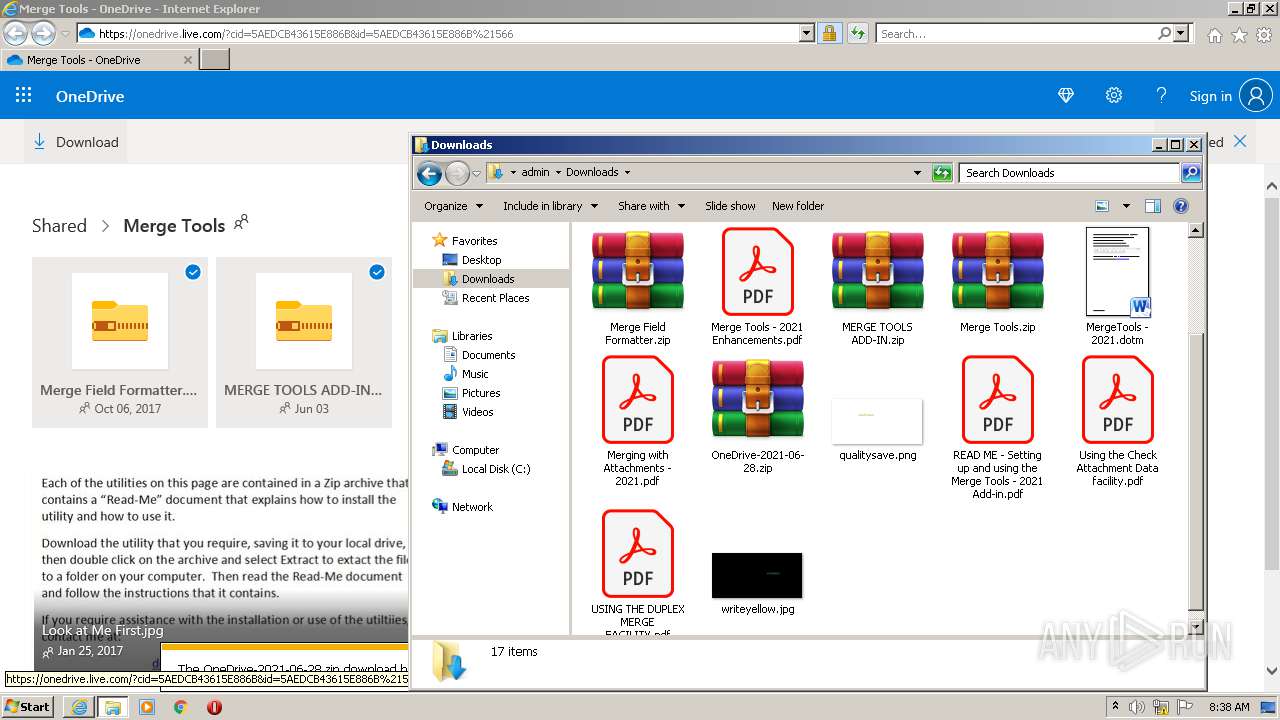
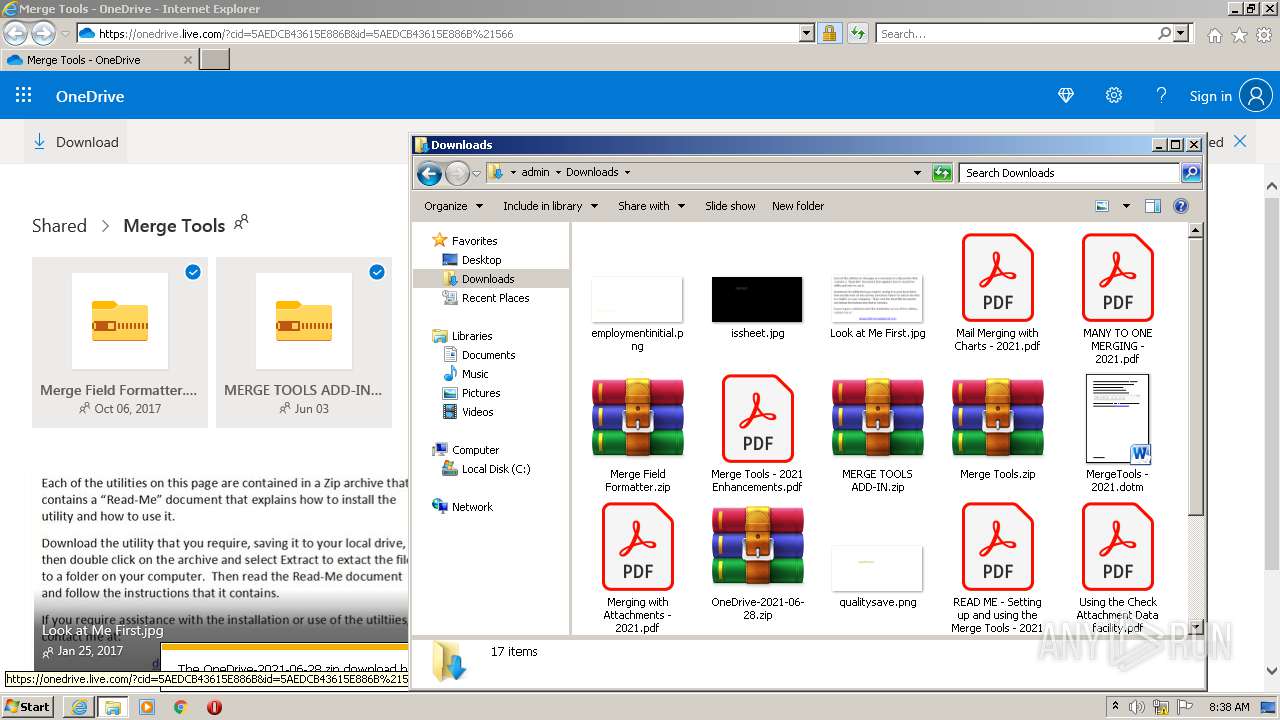
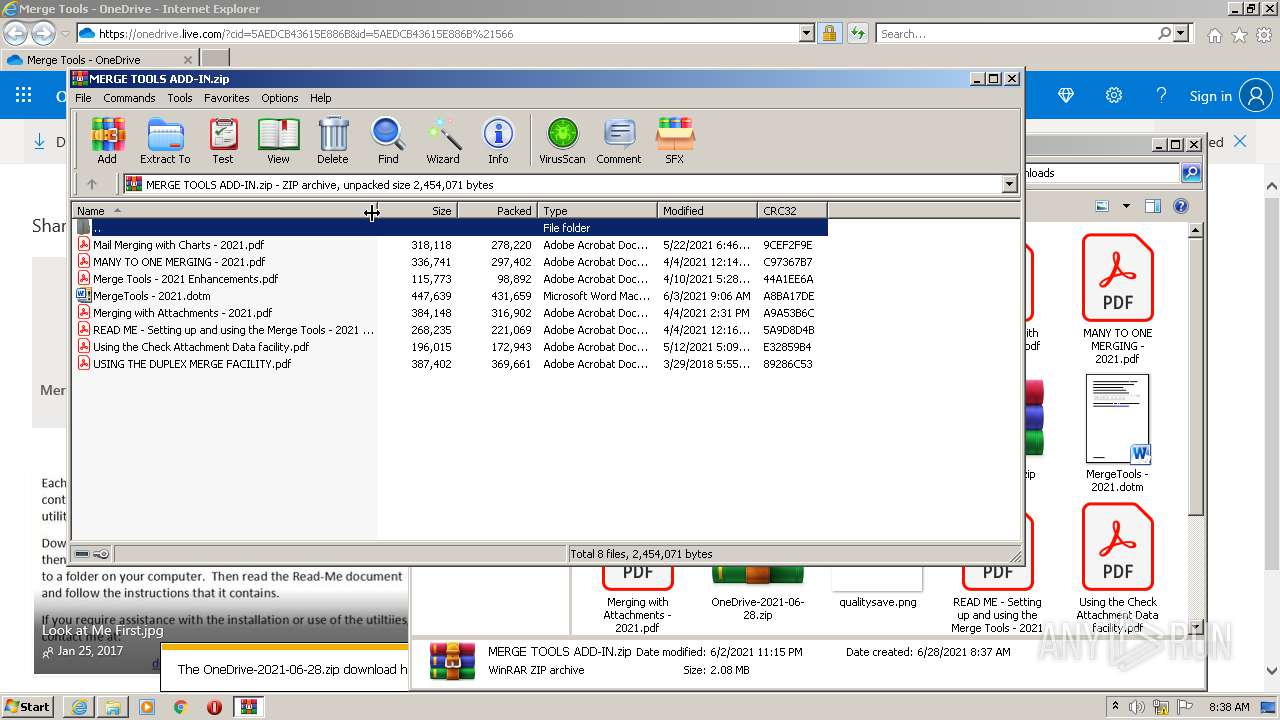
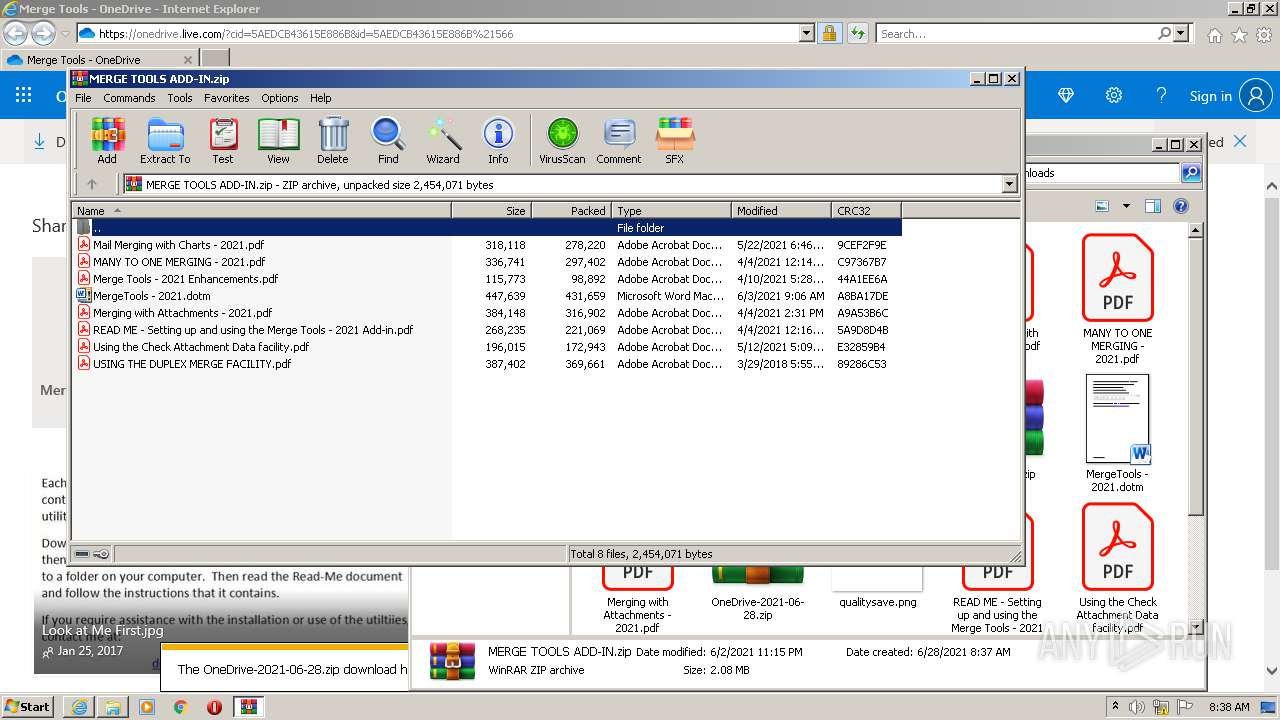
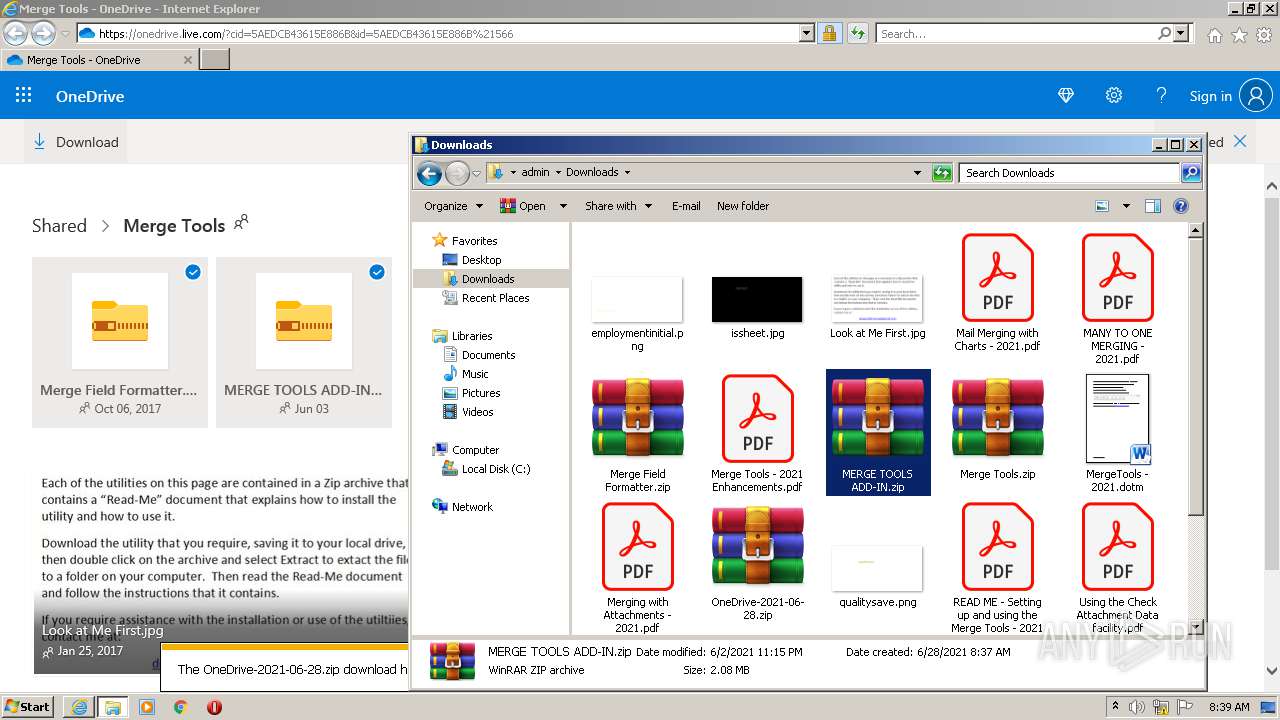
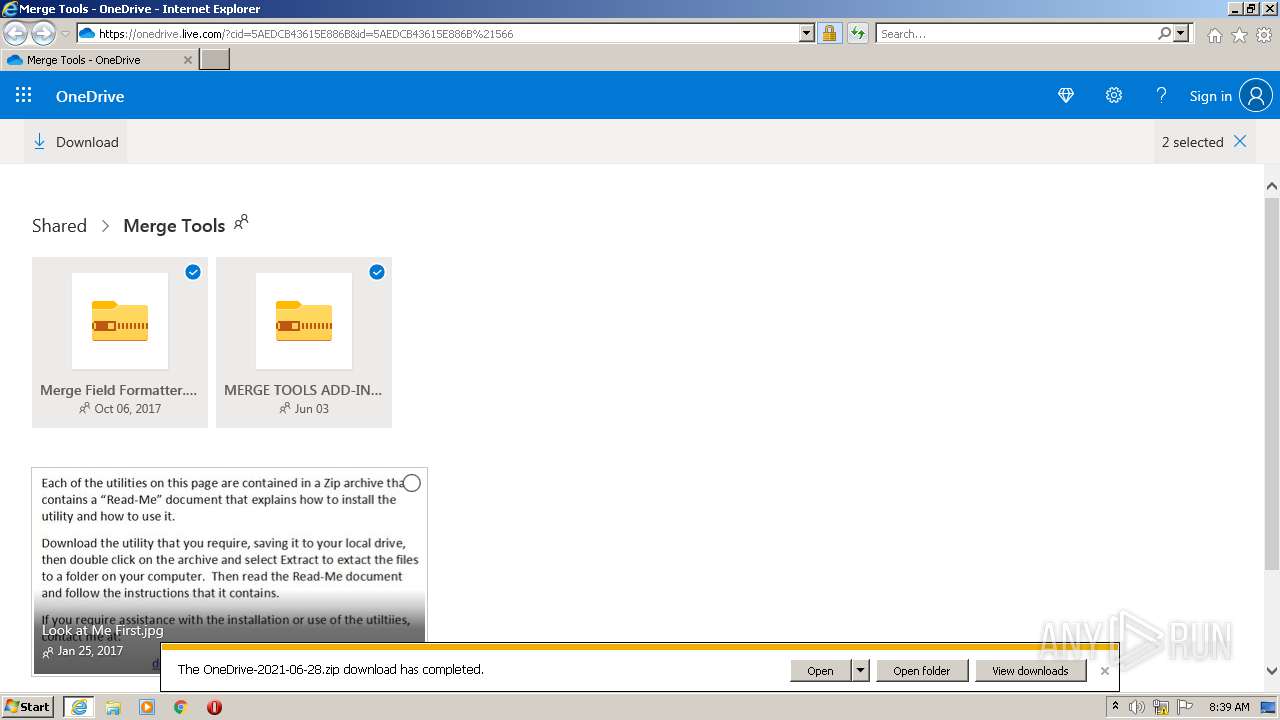
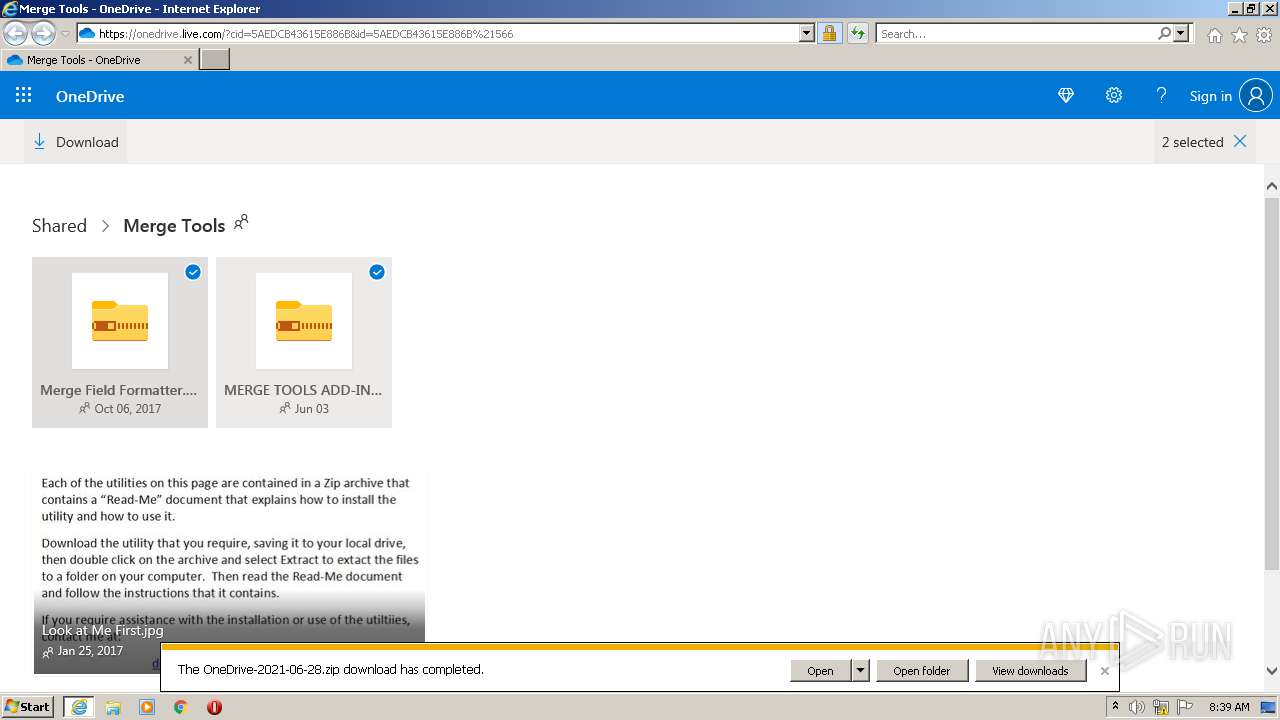
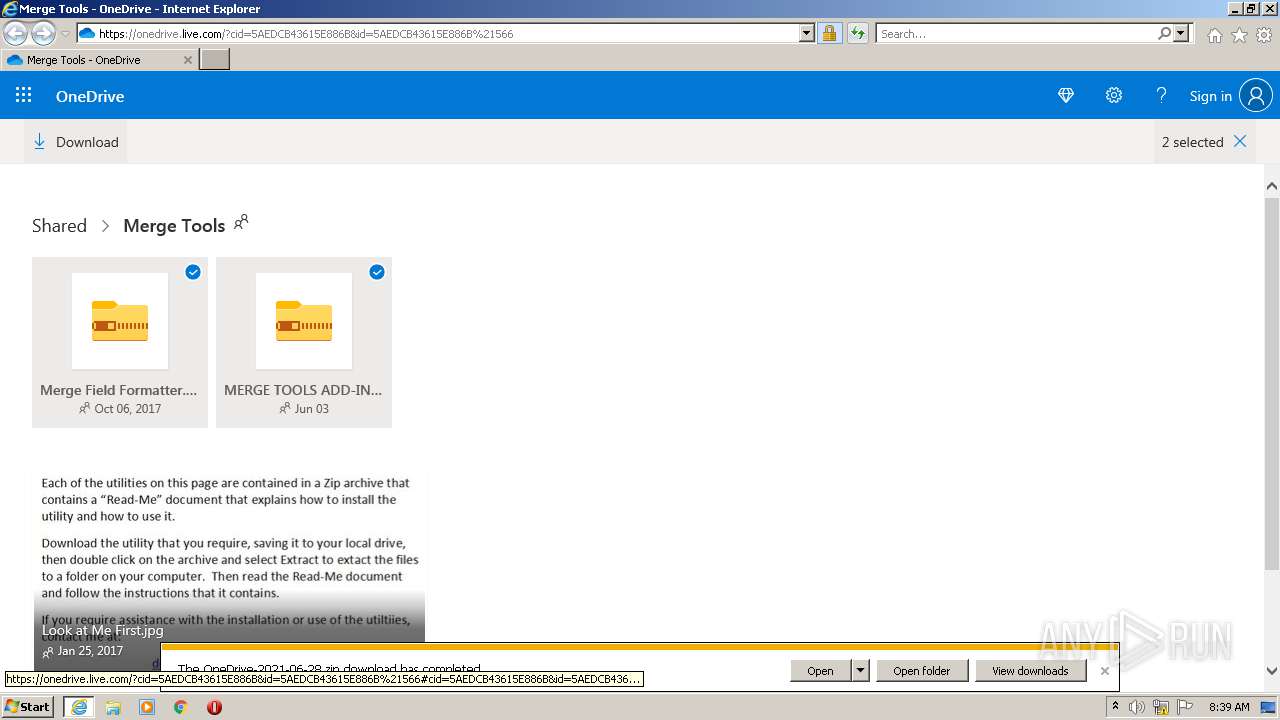
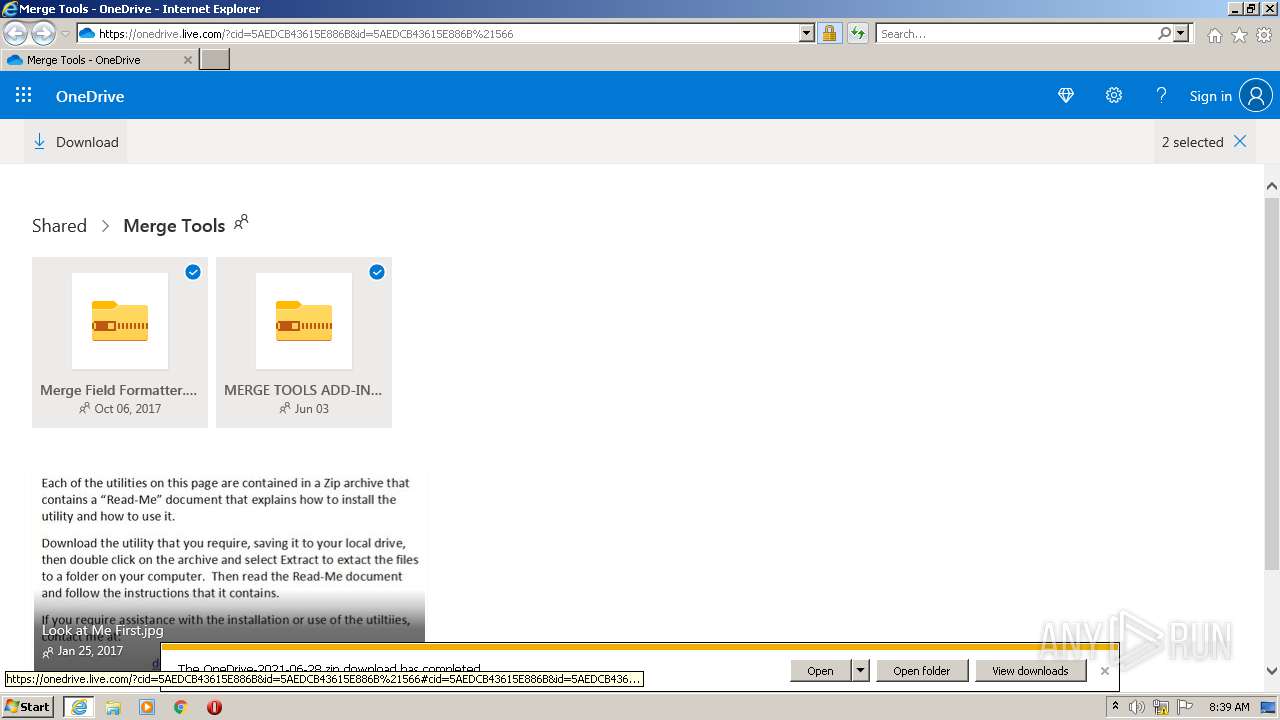
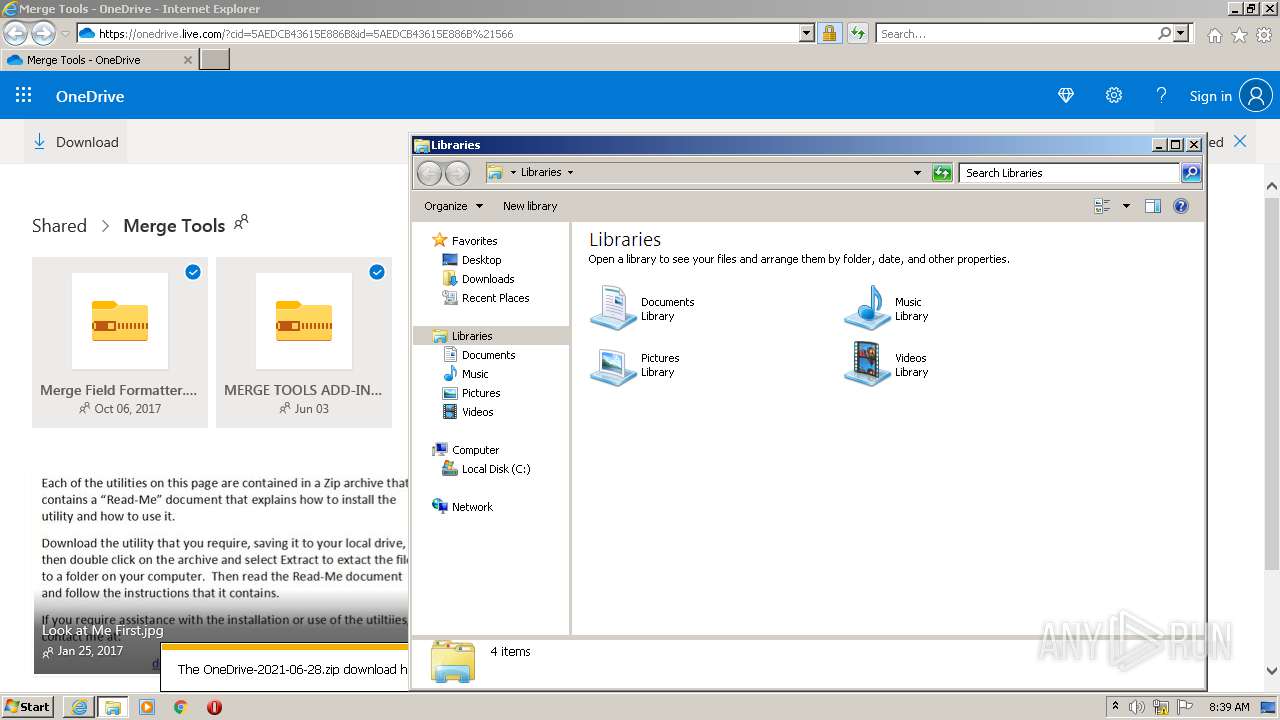
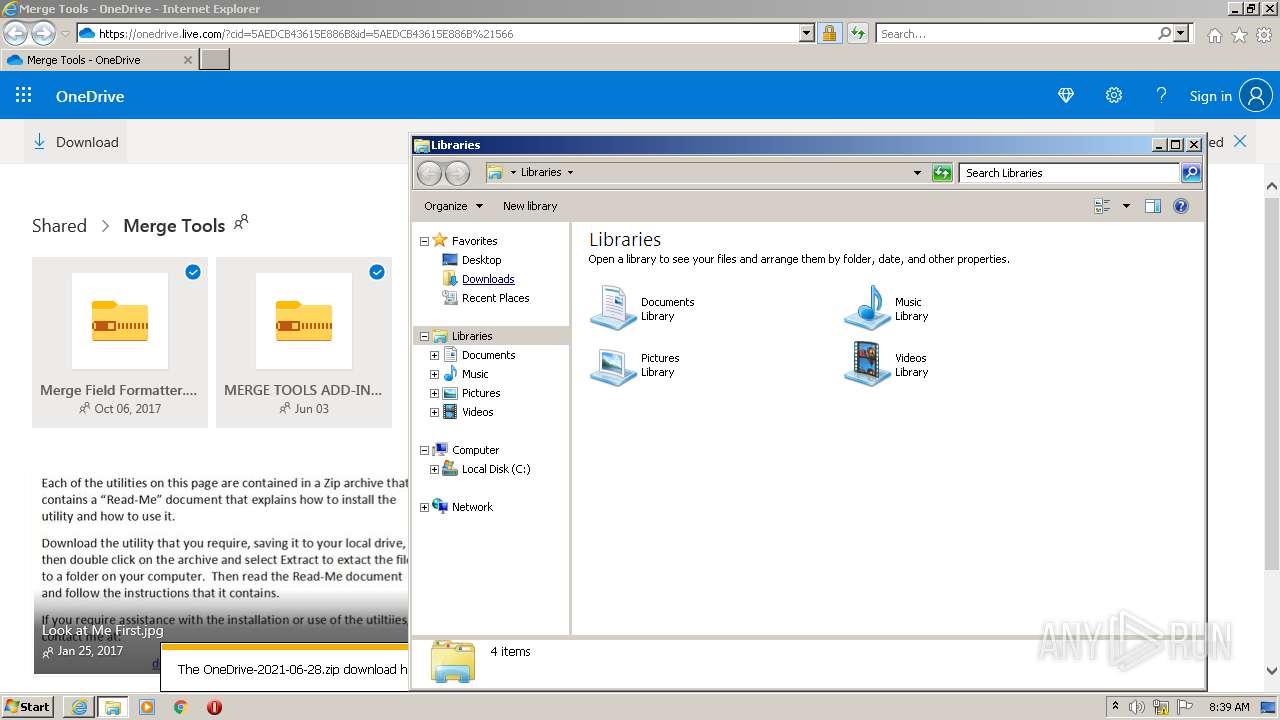
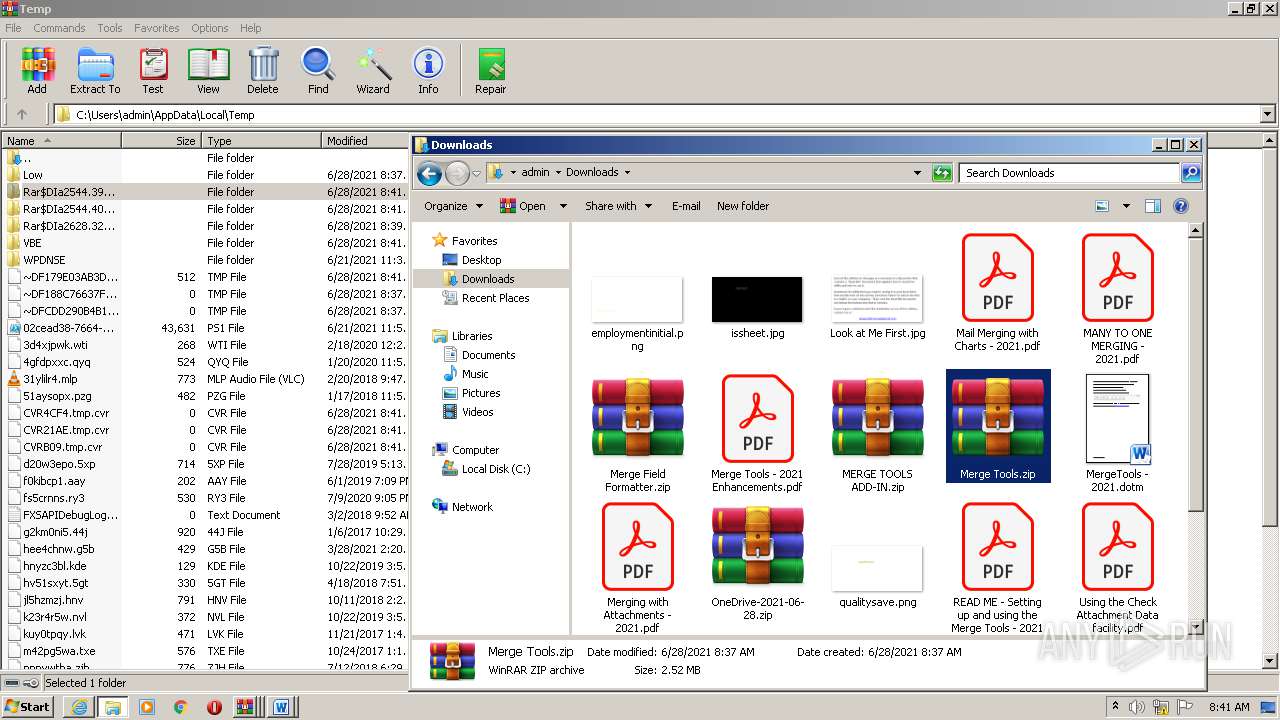
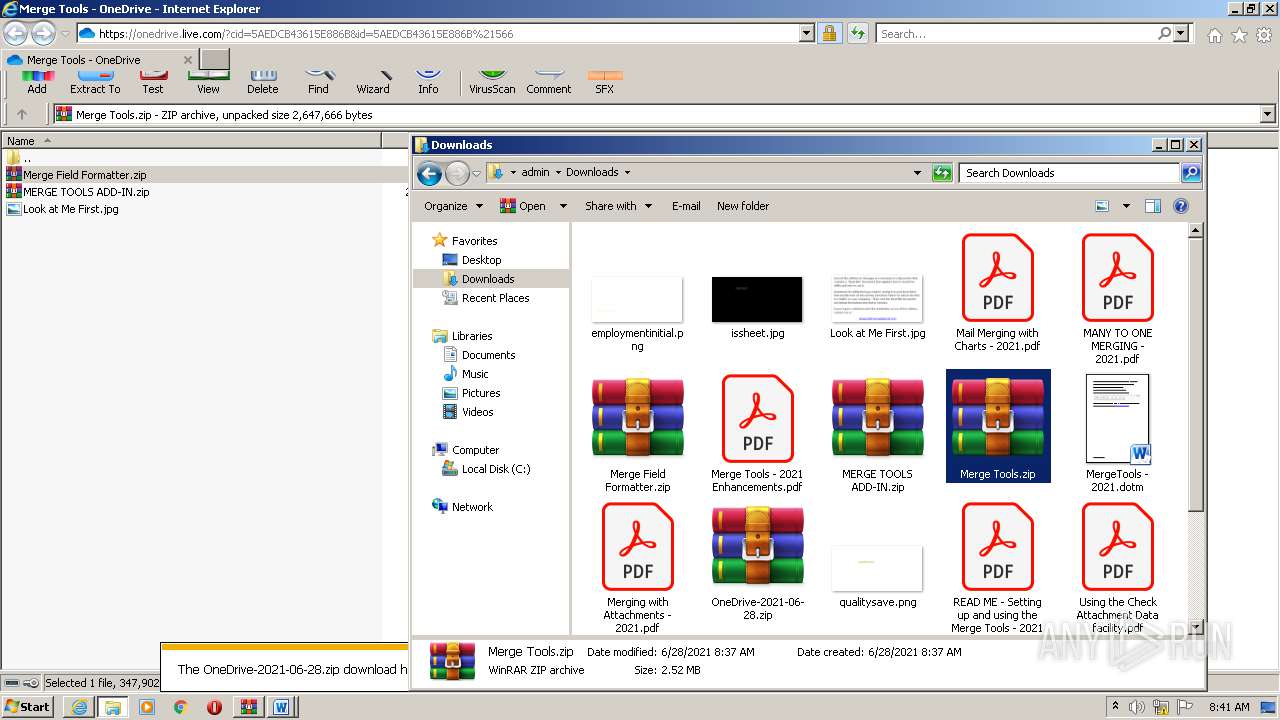
| URL: | https://onedrive.live.com/?cid=5AEDCB43615E886B&id=5AEDCB43615E886B%21566 |
| Full analysis: | https://app.any.run/tasks/b022295c-f77c-40cb-8520-2b999d23f778 |
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2021, 07:36:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 03B90A0EC15650C7FCA5129BC212F569 |
| SHA1: | 383A7F65EC3574A4E648C0497908398BB9668CD2 |
| SHA256: | 223BEBA4A5218439F229EF95F4B3793862F593C16D2397A3650B1935DE222F91 |
| SSDEEP: | 3:N8Ck3CTJYWEWeRnTghEWeRnk:2CkSTJYXWeBVWeBk |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2916)
Reads the time zone
- iexplore.exe (PID: 2916)
Checks supported languages
- WinRAR.exe (PID: 2348)
- WinRAR.exe (PID: 2808)
- WinRAR.exe (PID: 748)
- WinRAR.exe (PID: 424)
- WinRAR.exe (PID: 1260)
- WinRAR.exe (PID: 2628)
- WinRAR.exe (PID: 2960)
- WinRAR.exe (PID: 116)
- WinRAR.exe (PID: 368)
- WinRAR.exe (PID: 2544)
- WinRAR.exe (PID: 2360)
Reads the computer name
- WinRAR.exe (PID: 2348)
- WinRAR.exe (PID: 2808)
- WinRAR.exe (PID: 1260)
- WinRAR.exe (PID: 424)
- WinRAR.exe (PID: 748)
- WinRAR.exe (PID: 2960)
- WinRAR.exe (PID: 2628)
- WinRAR.exe (PID: 116)
- WinRAR.exe (PID: 368)
- WinRAR.exe (PID: 2544)
- WinRAR.exe (PID: 2360)
Application launched itself
- WinRAR.exe (PID: 116)
- WinRAR.exe (PID: 2628)
- WinRAR.exe (PID: 368)
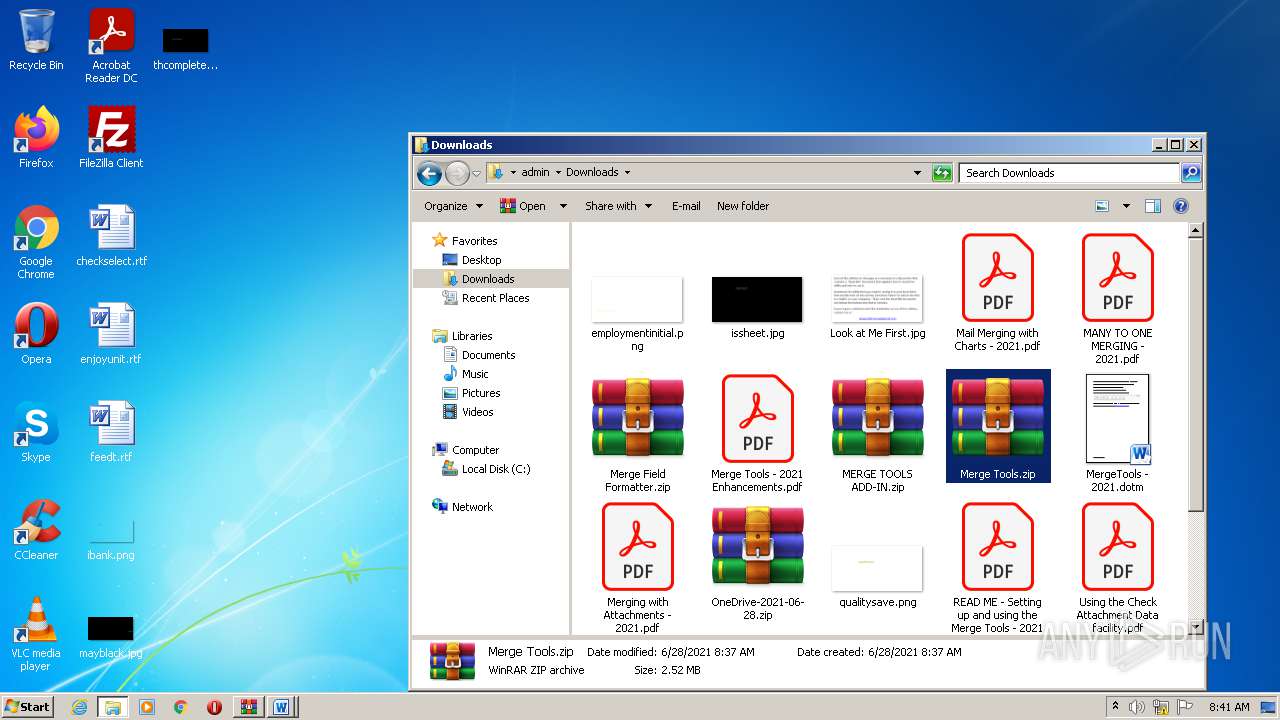
Starts Microsoft Office Application
- WinRAR.exe (PID: 2544)
- WinRAR.exe (PID: 2360)
INFO
Checks supported languages
- iexplore.exe (PID: 3560)
- iexplore.exe (PID: 2916)
- explorer.exe (PID: 3464)
- explorer.exe (PID: 2096)
- WINWORD.EXE (PID: 1124)
- WINWORD.EXE (PID: 2084)
- WINWORD.EXE (PID: 3432)
Reads the computer name
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 3560)
- explorer.exe (PID: 3464)
- explorer.exe (PID: 2096)
- WINWORD.EXE (PID: 1124)
Reads settings of System Certificates
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 3560)
Application launched itself
- iexplore.exe (PID: 3560)
Changes internet zones settings
- iexplore.exe (PID: 3560)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3560)
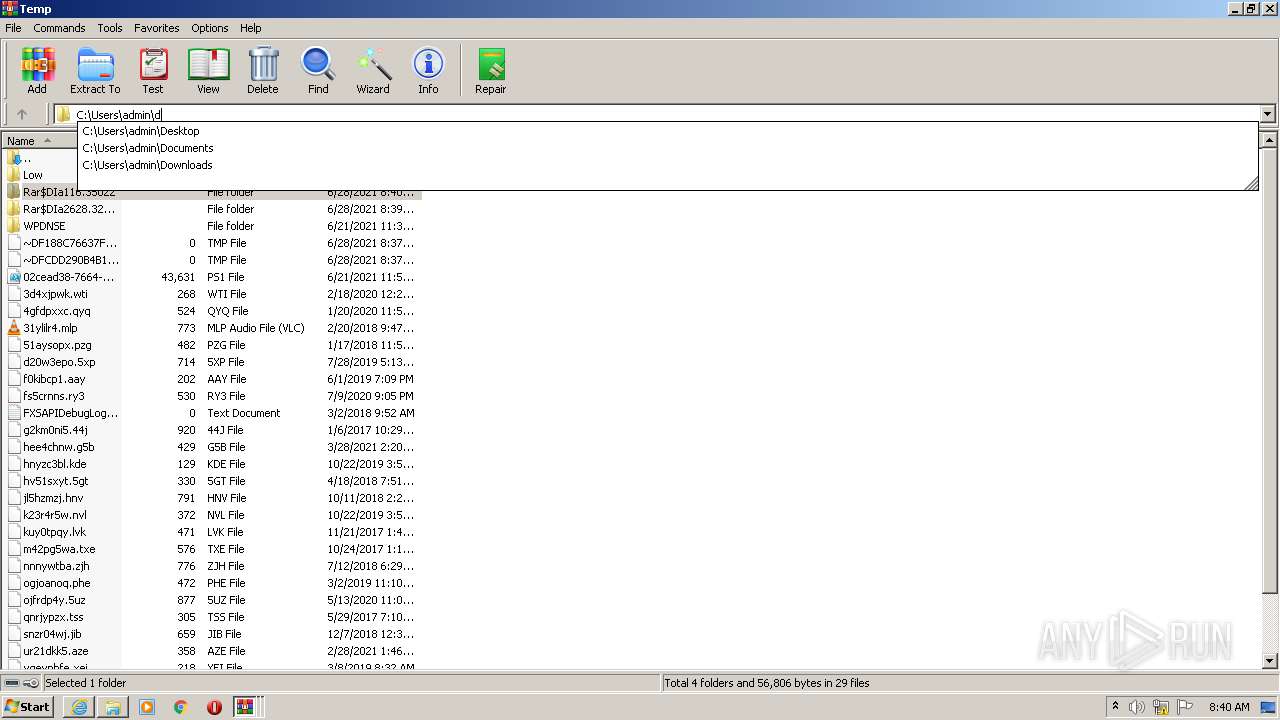
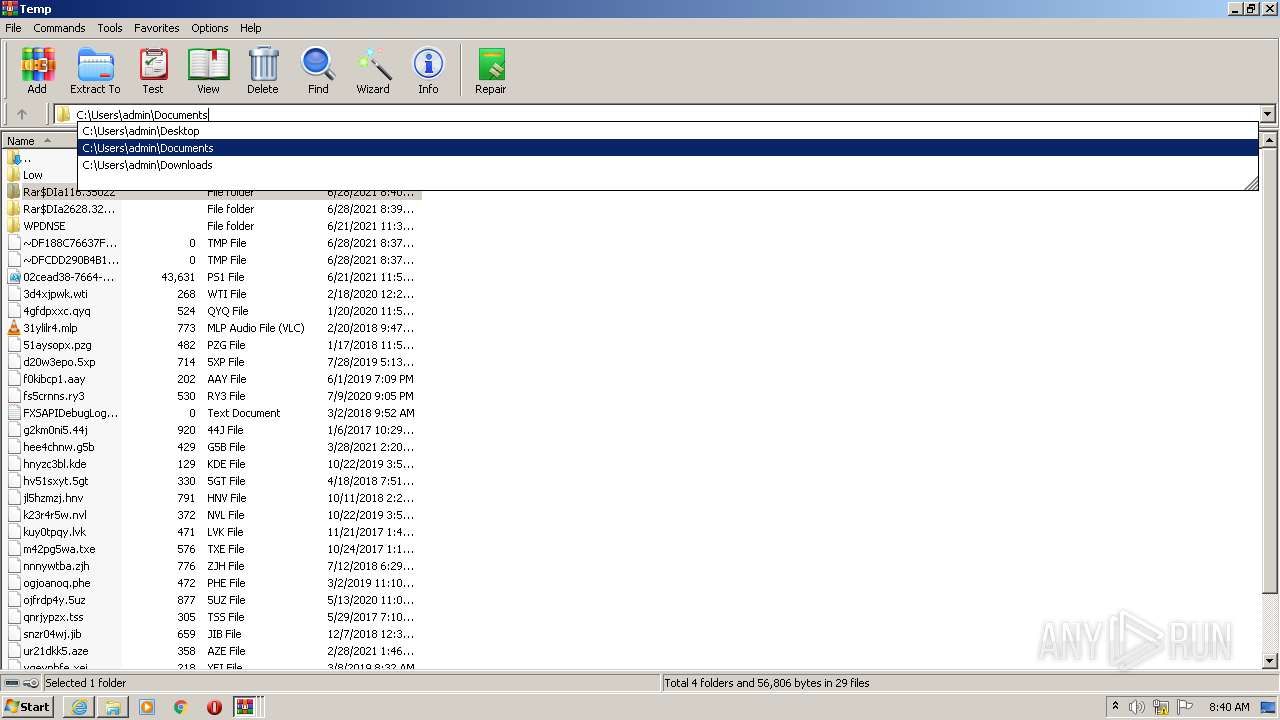
Manual execution by user
- explorer.exe (PID: 3464)
- WinRAR.exe (PID: 2348)
- WinRAR.exe (PID: 2808)
- WinRAR.exe (PID: 424)
- WinRAR.exe (PID: 1260)
- explorer.exe (PID: 2096)
- WinRAR.exe (PID: 748)
- WinRAR.exe (PID: 2628)
- WinRAR.exe (PID: 116)
Creates files in the user directory
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 3560)
- WINWORD.EXE (PID: 1124)
Checks Windows Trust Settings
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 3560)
Reads internet explorer settings
- iexplore.exe (PID: 2916)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3560)
Changes settings of System certificates
- iexplore.exe (PID: 3560)
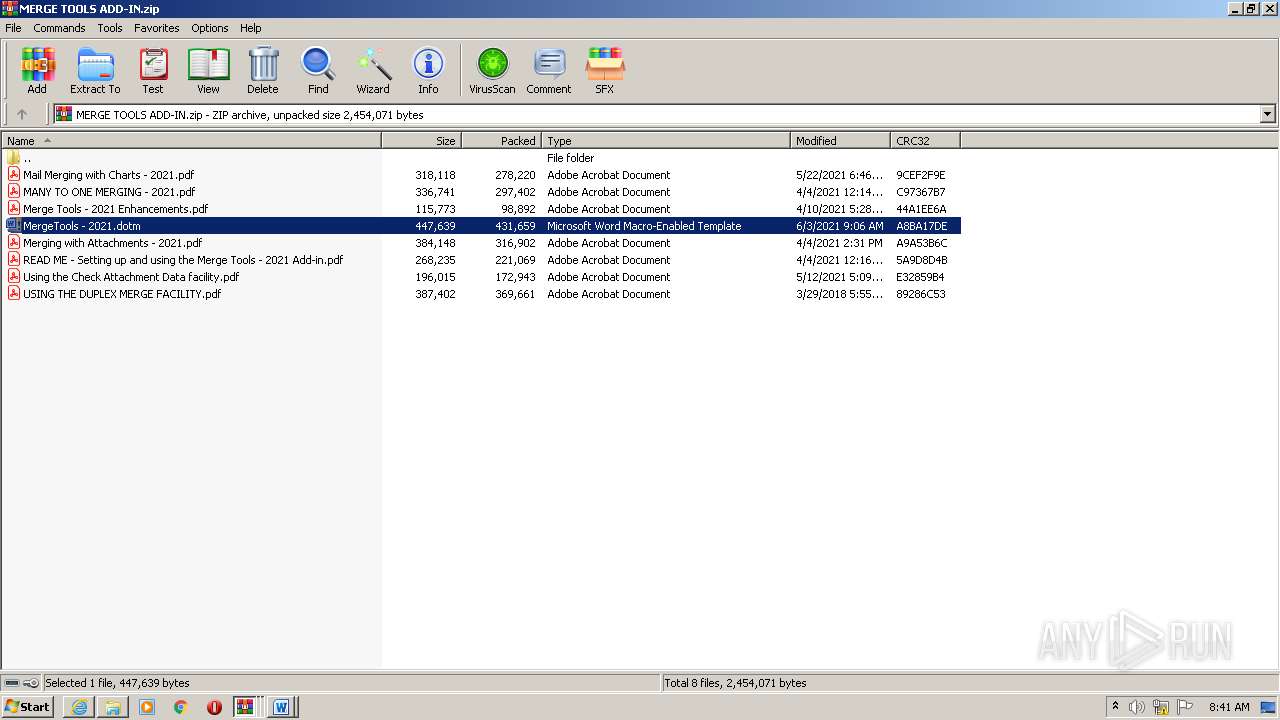
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 2544)
- WINWORD.EXE (PID: 2084)
- WINWORD.EXE (PID: 3432)
- WinRAR.exe (PID: 2360)
- WINWORD.EXE (PID: 1124)
Reads the date of Windows installation
- iexplore.exe (PID: 3560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
18
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
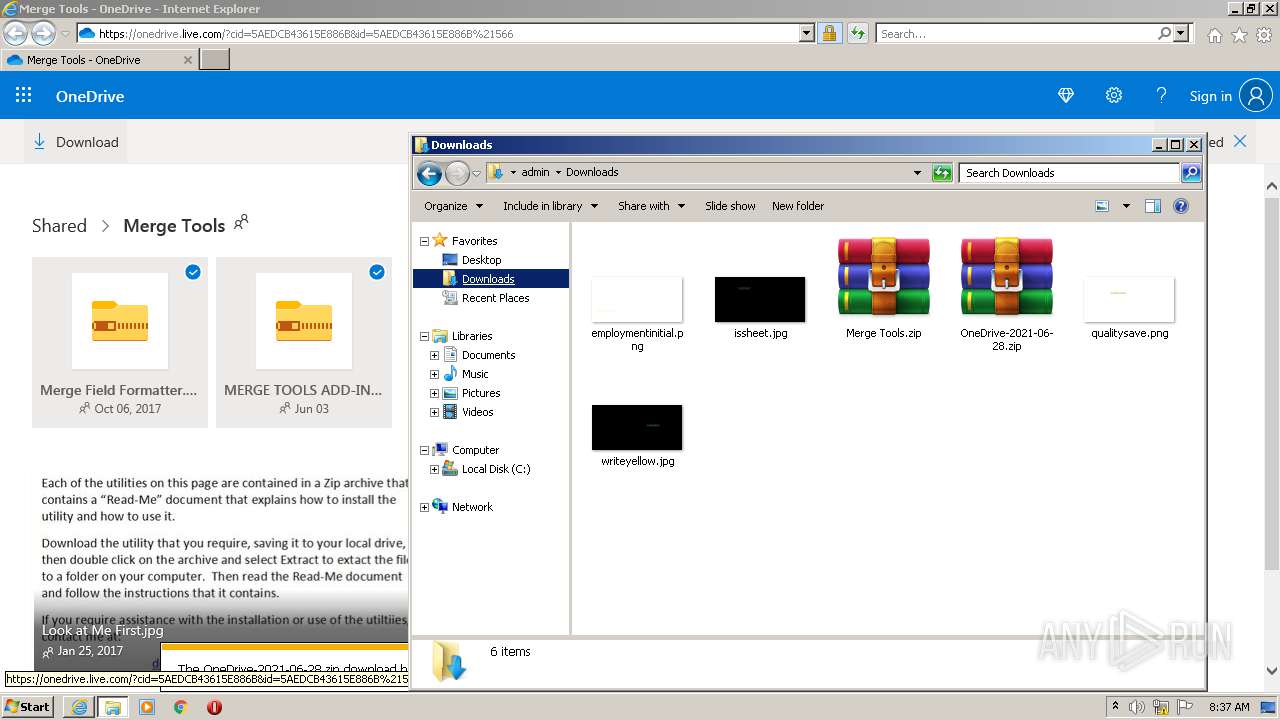
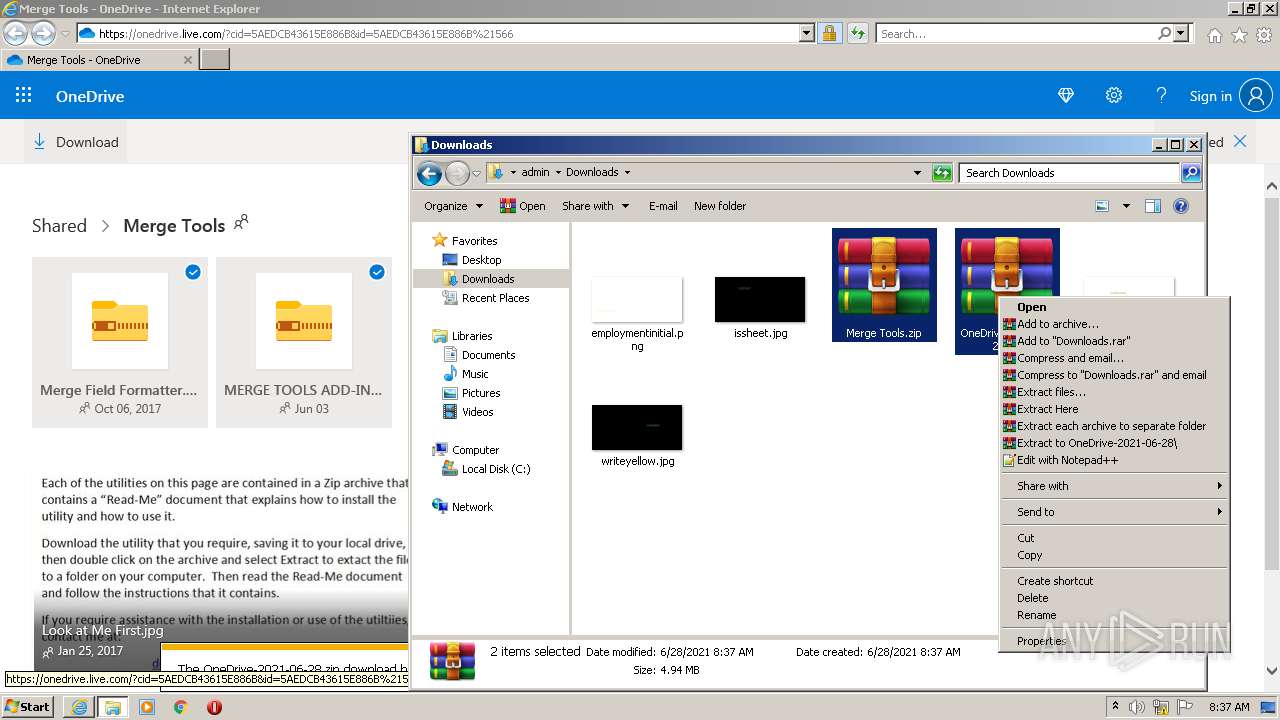
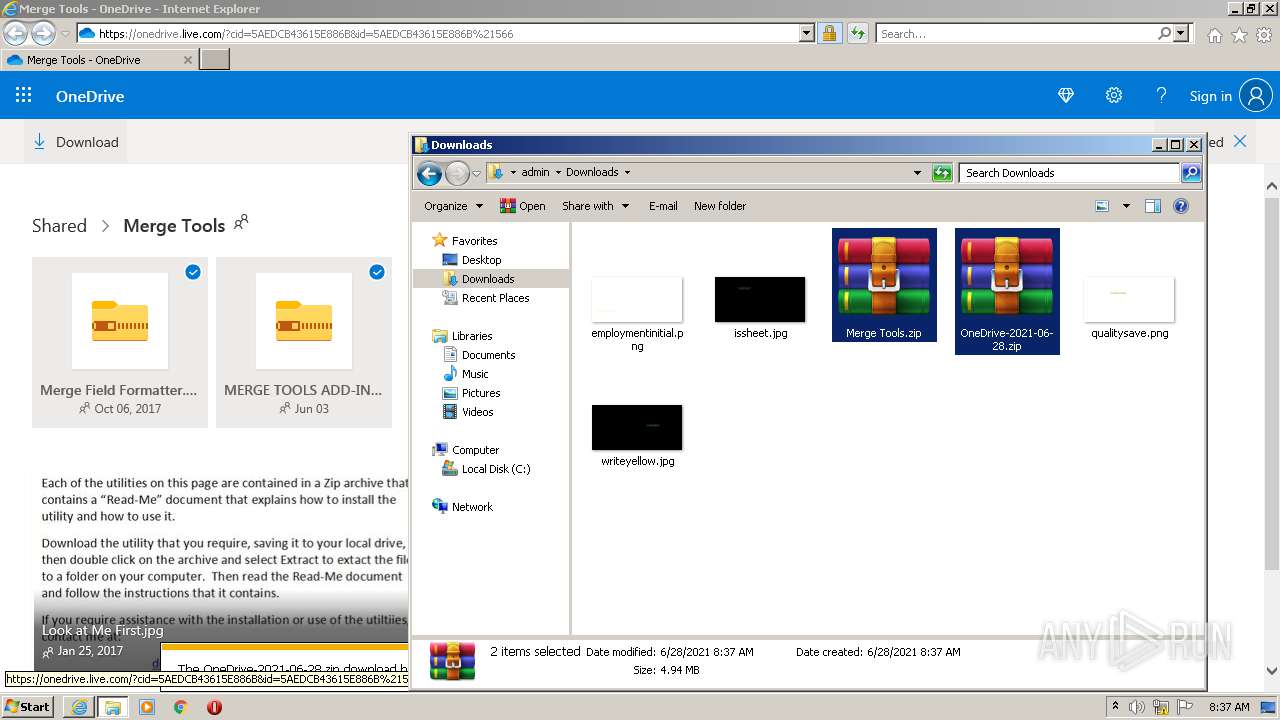
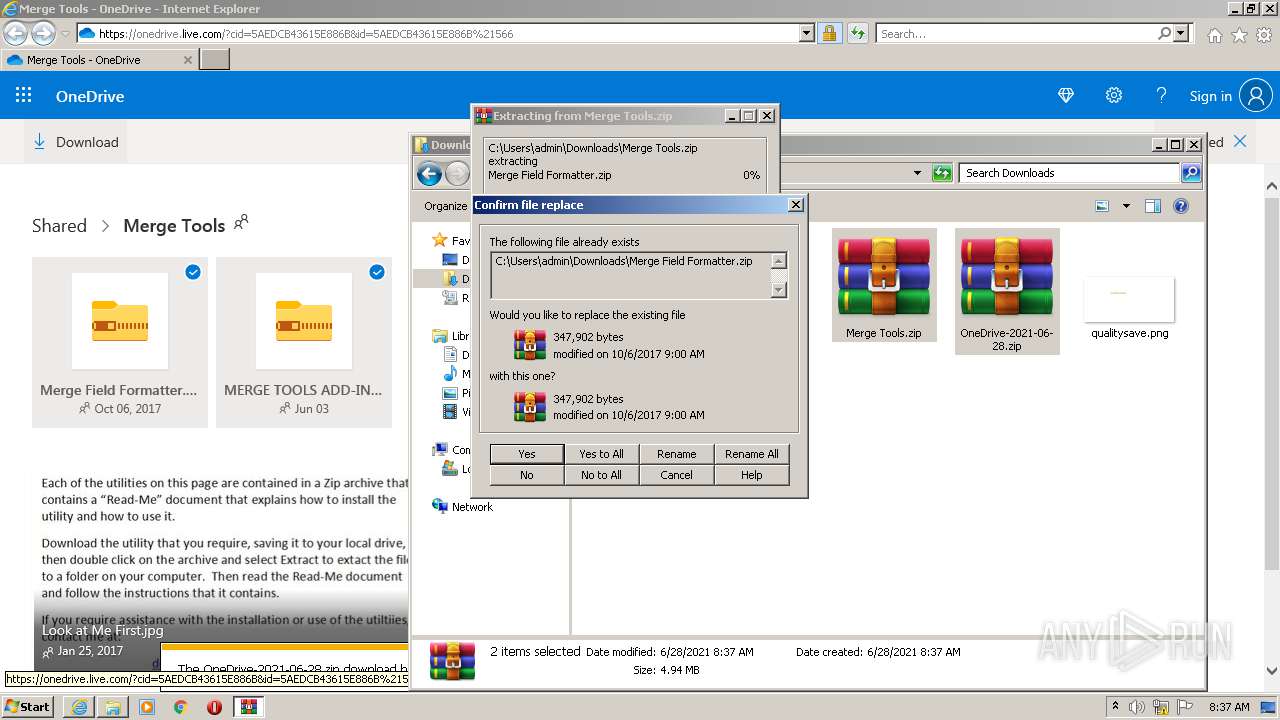
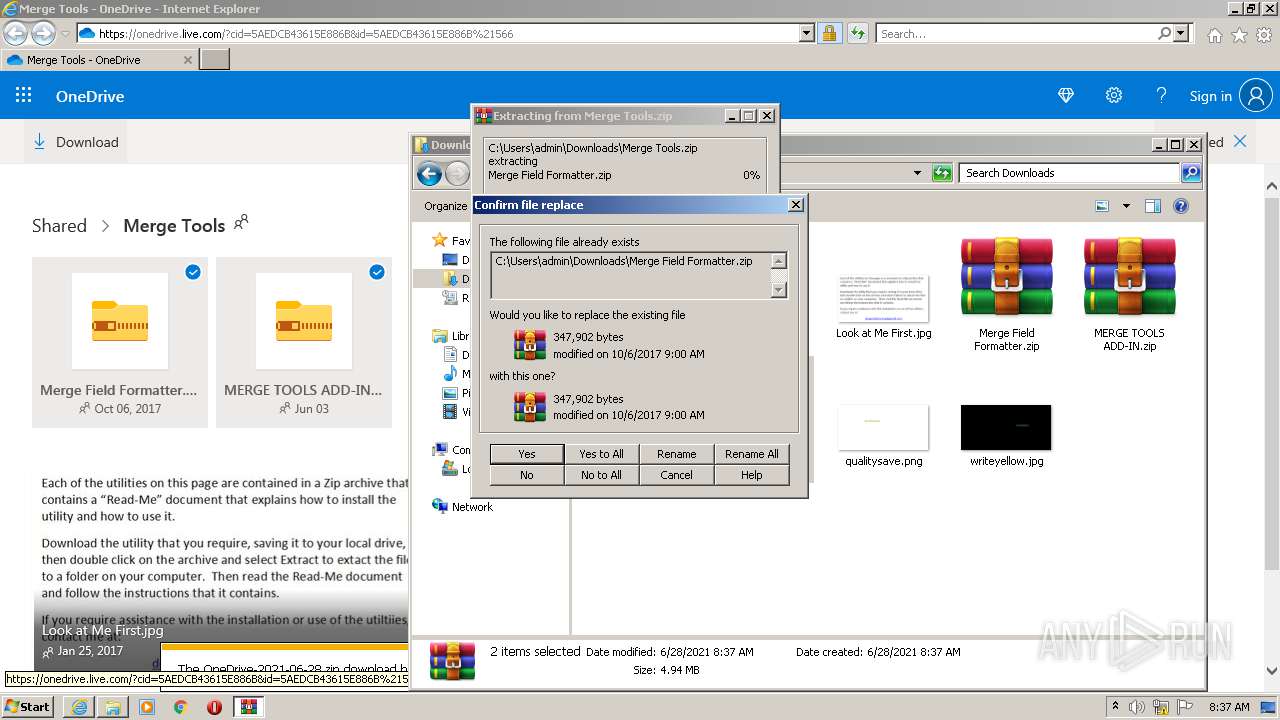
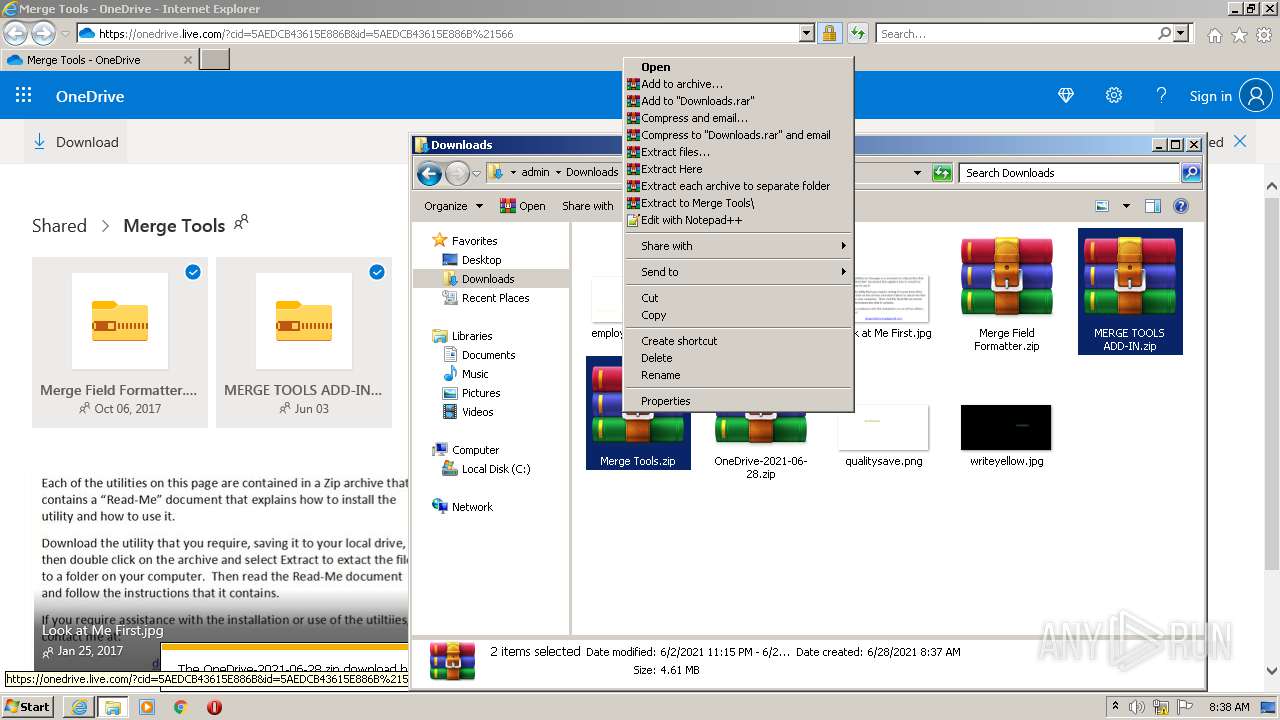
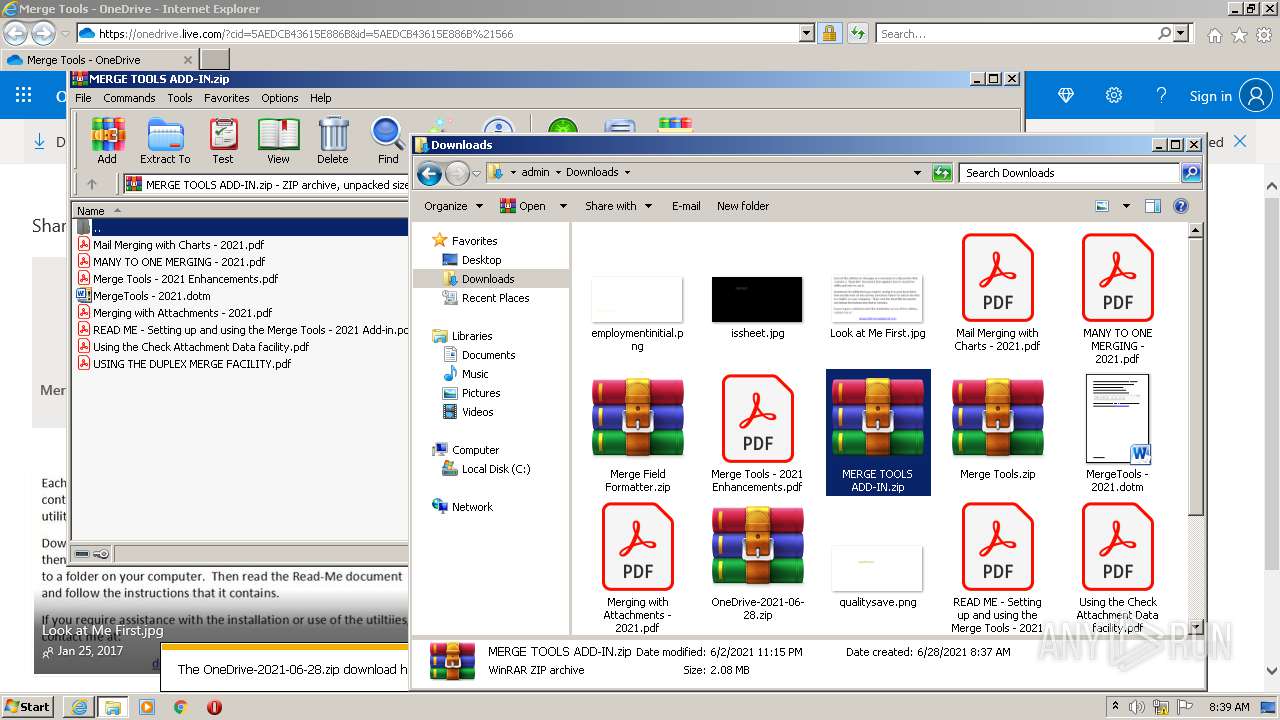
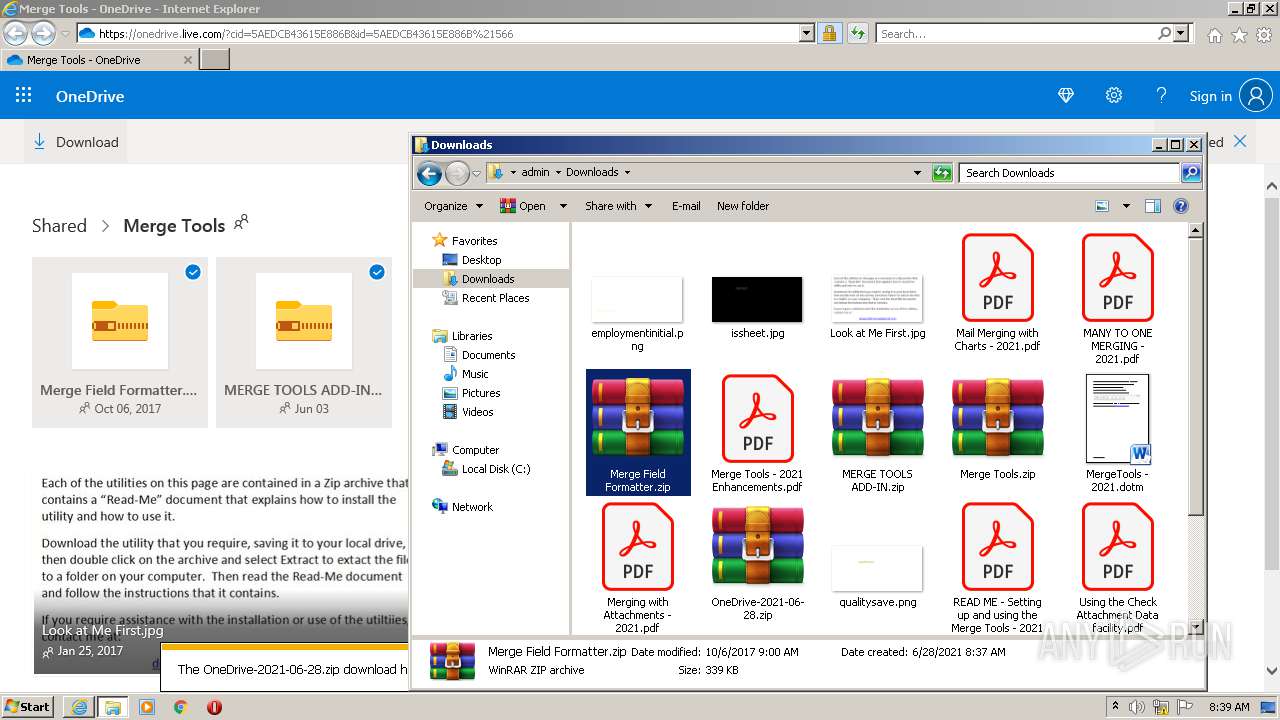
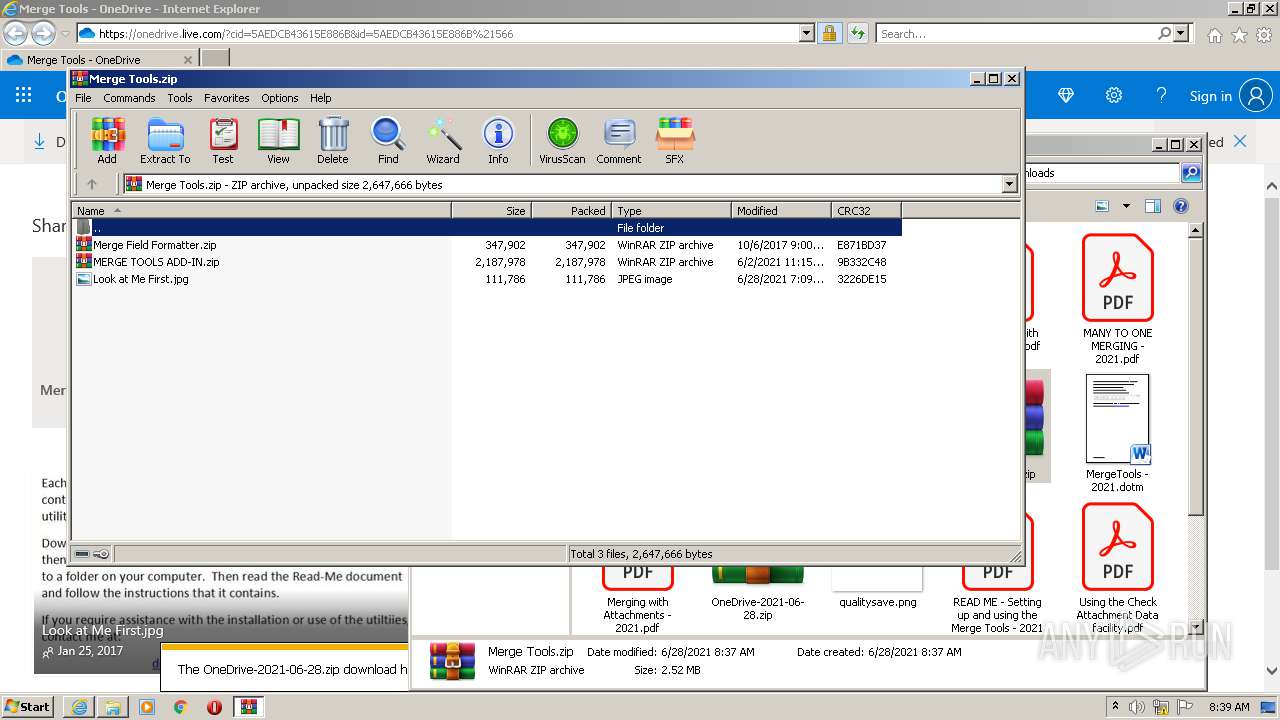
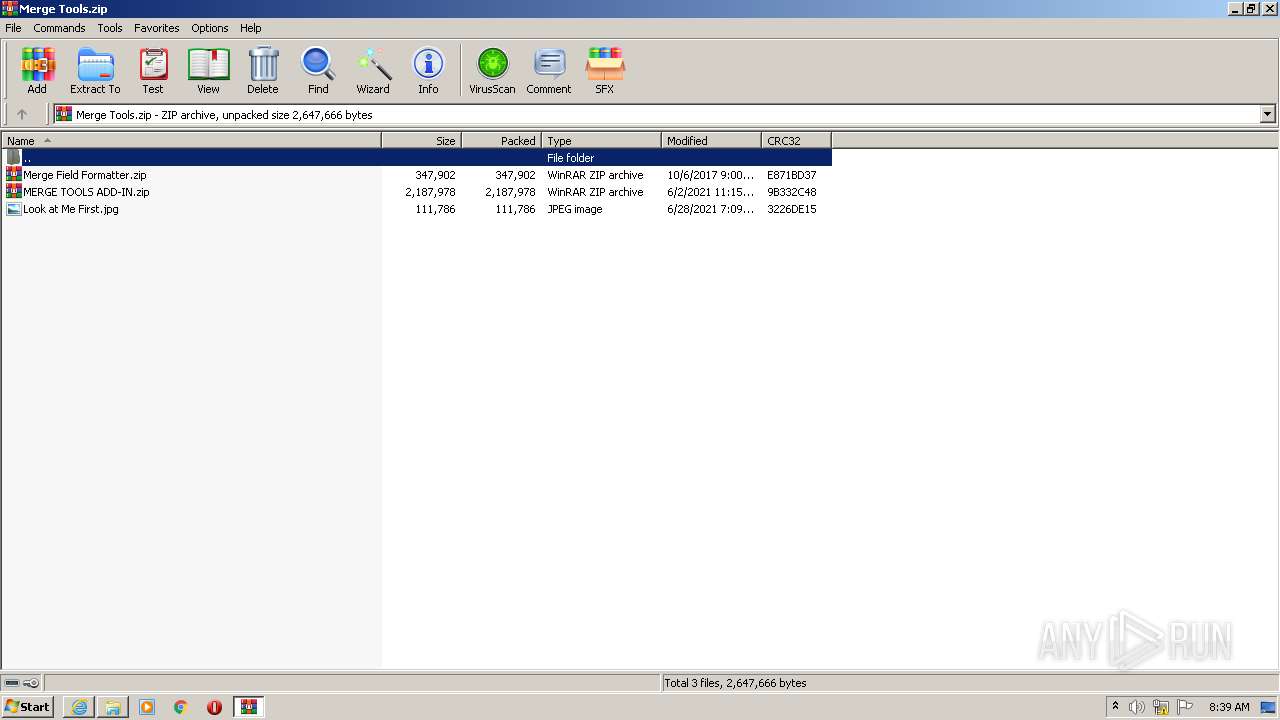
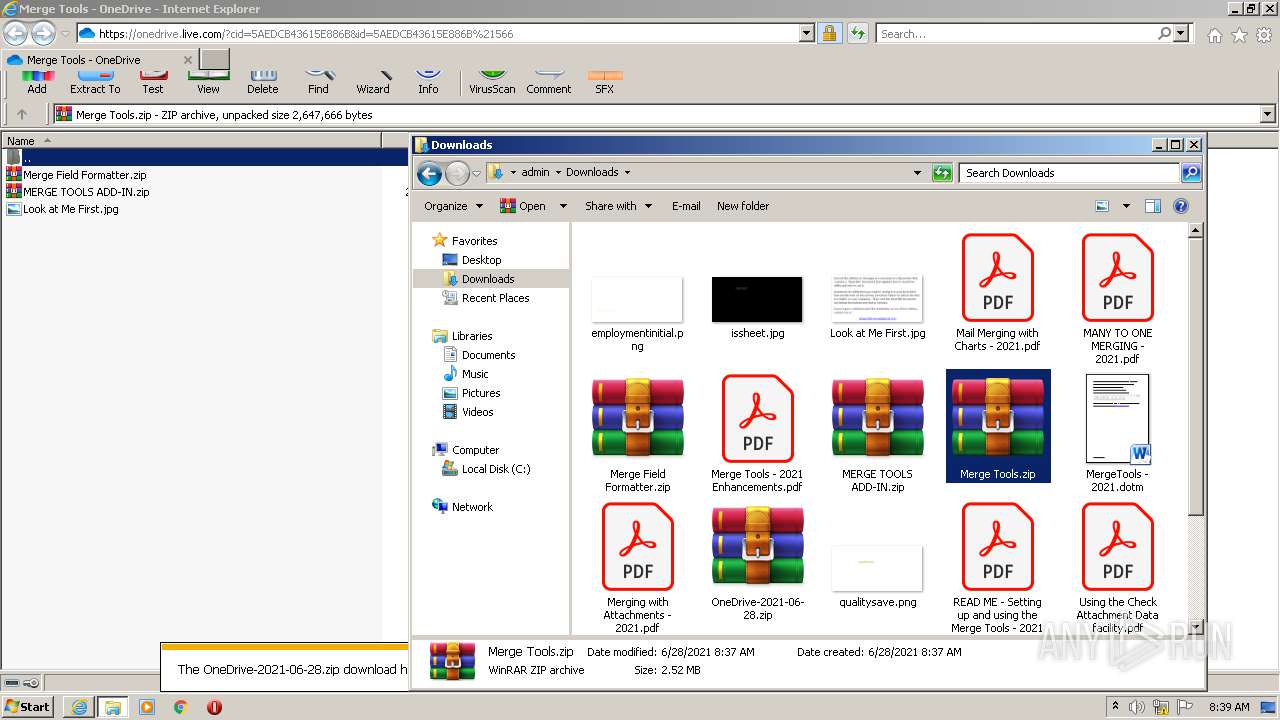
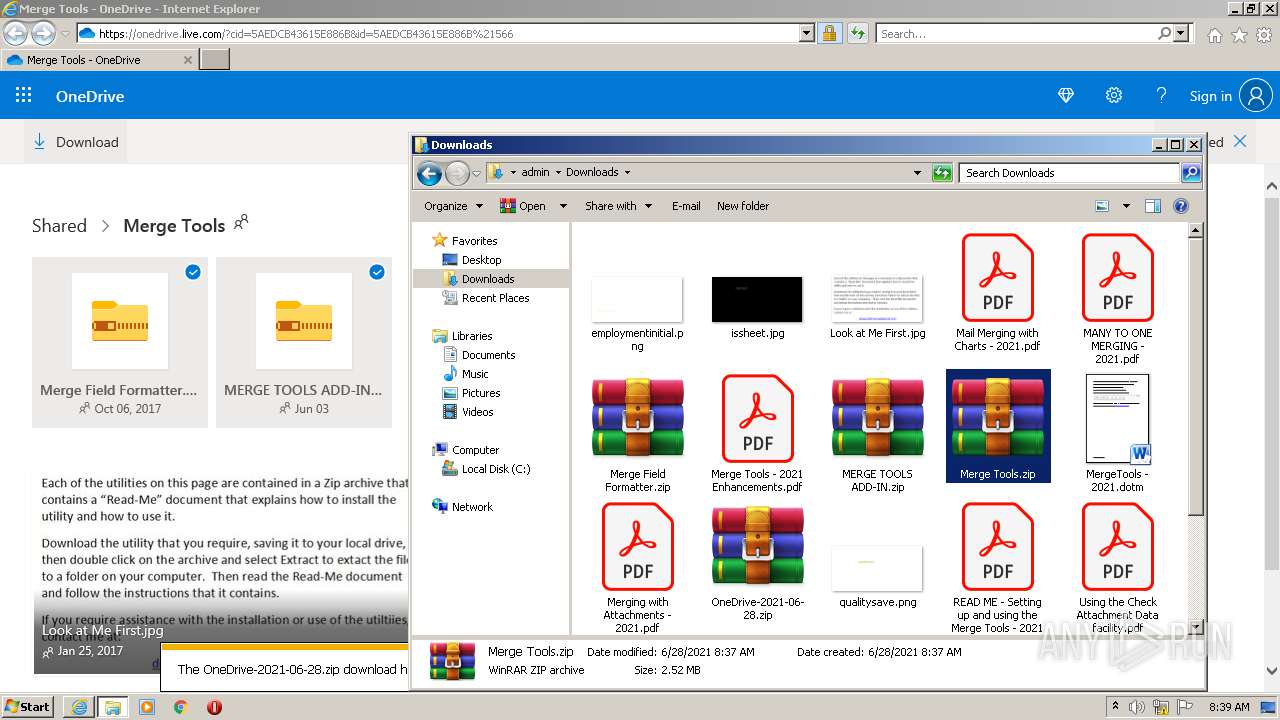
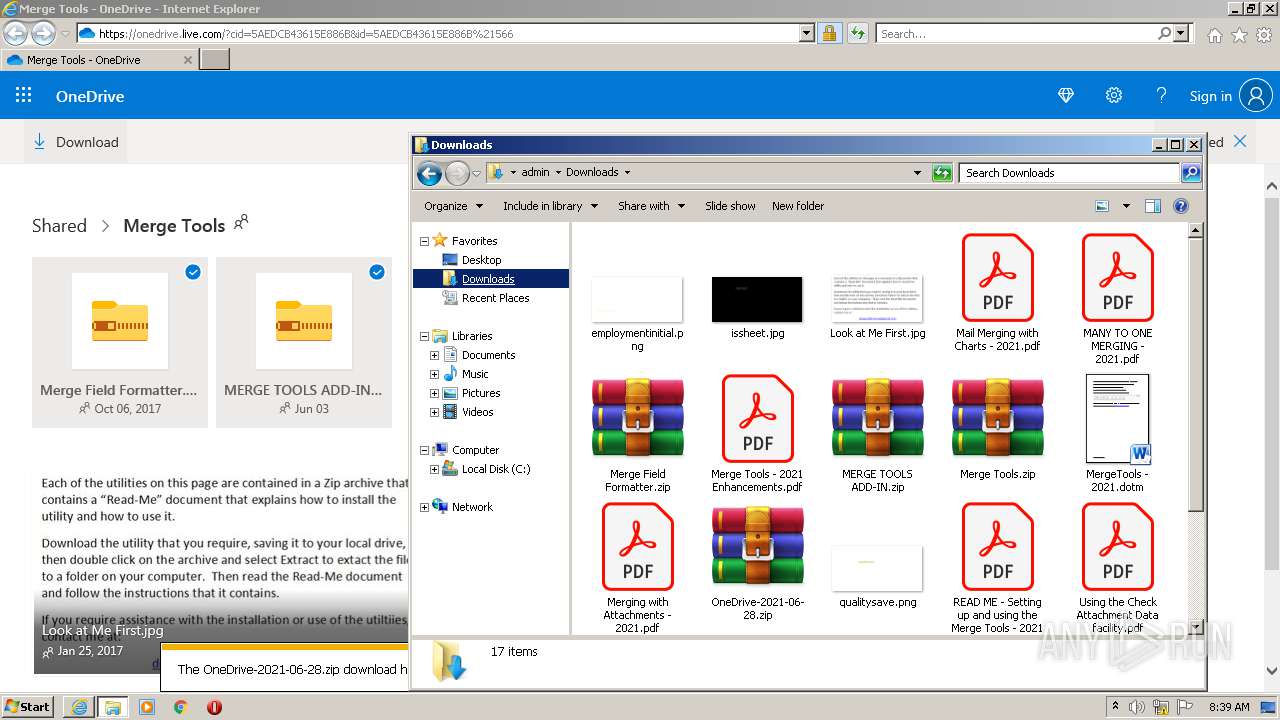
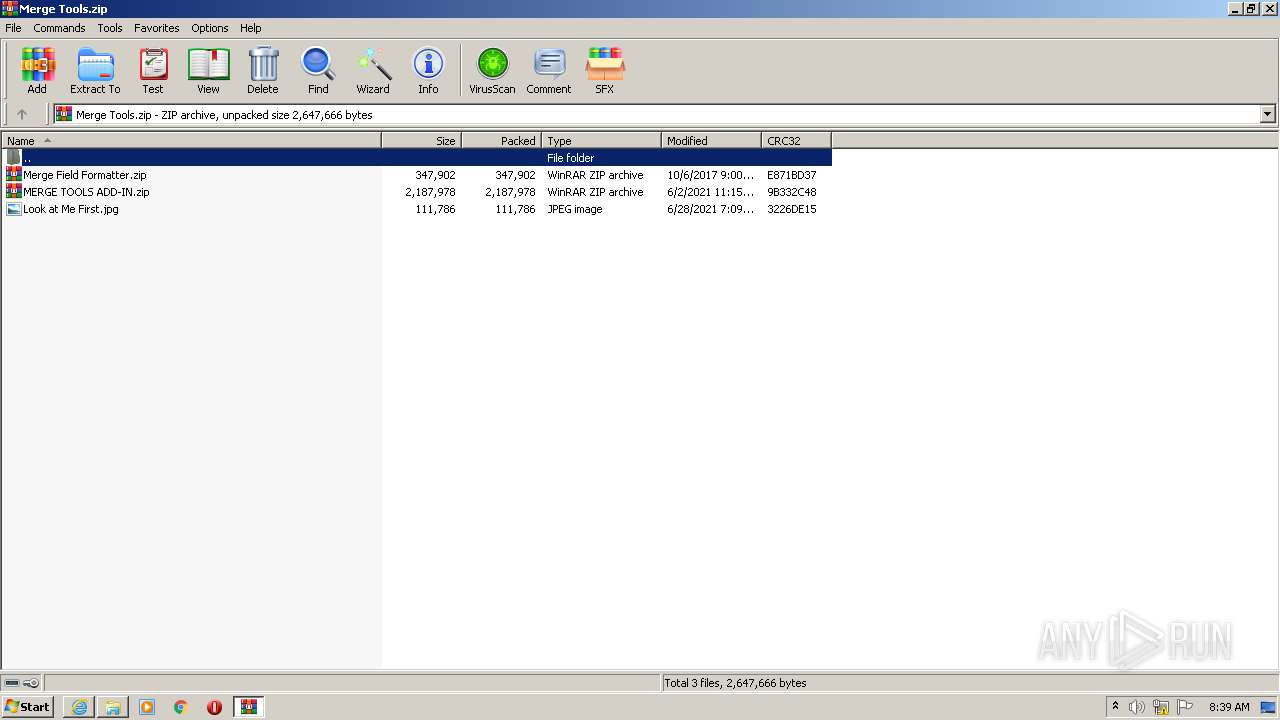
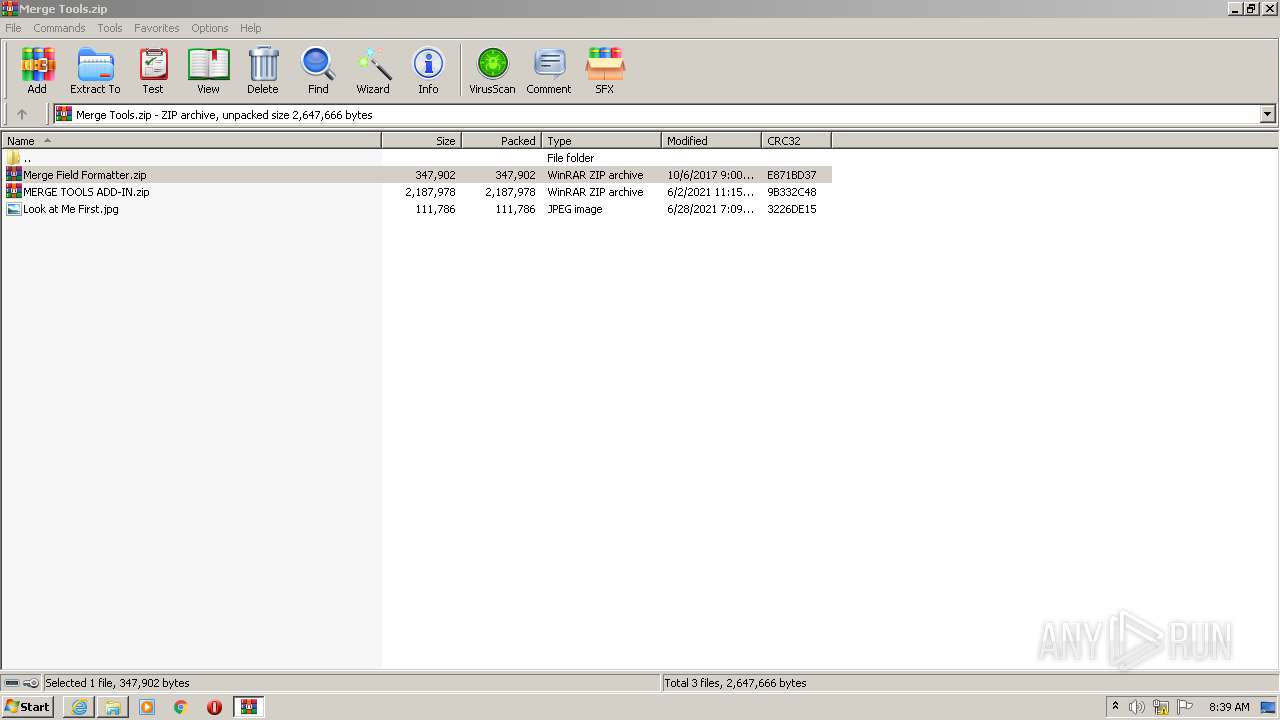
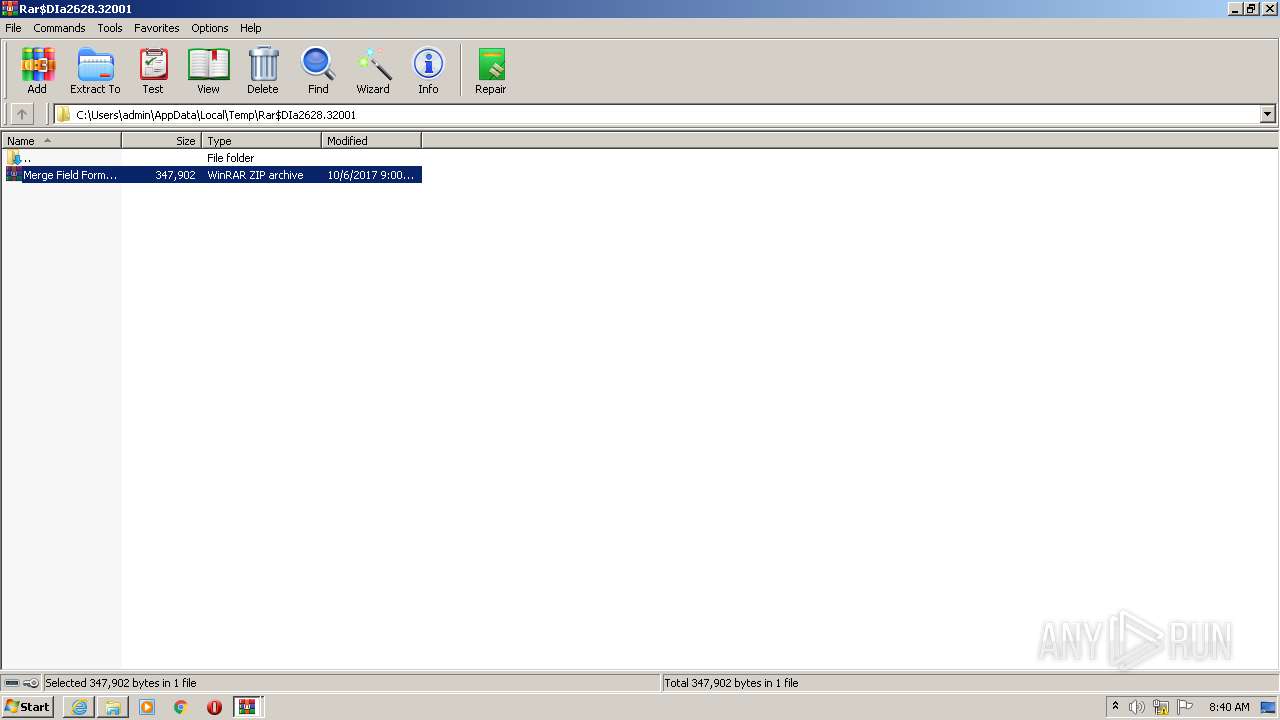
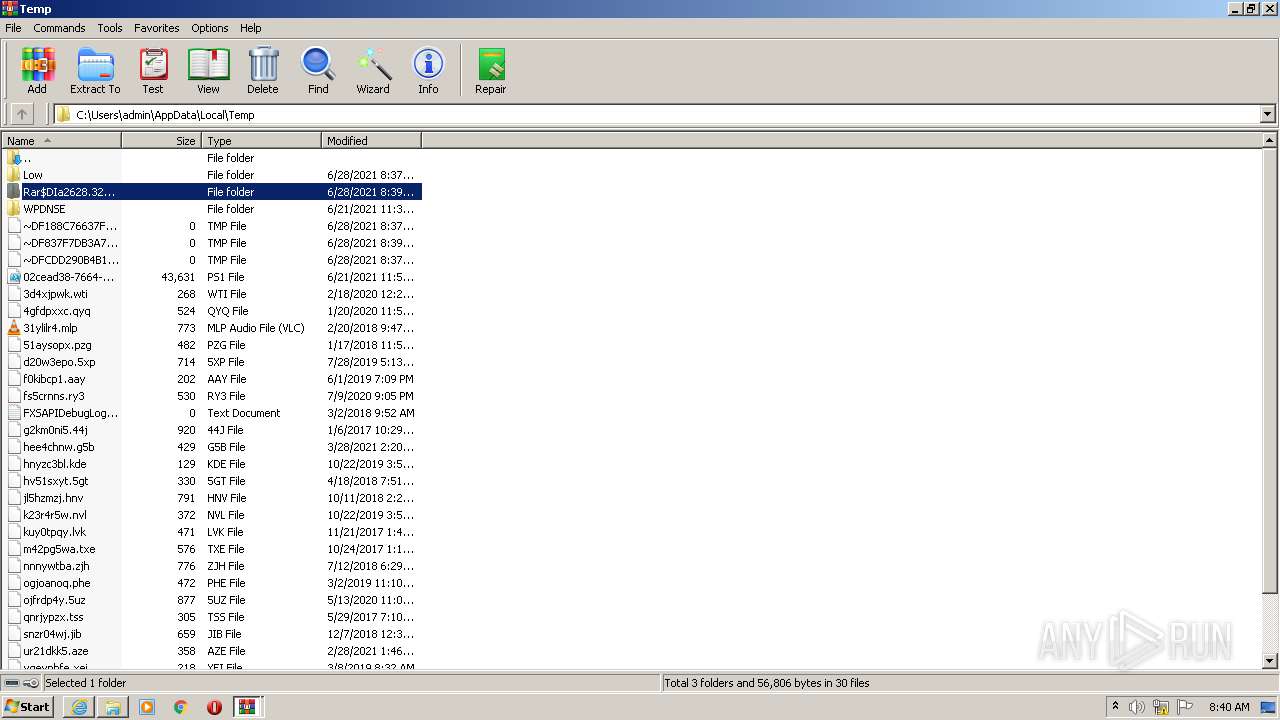
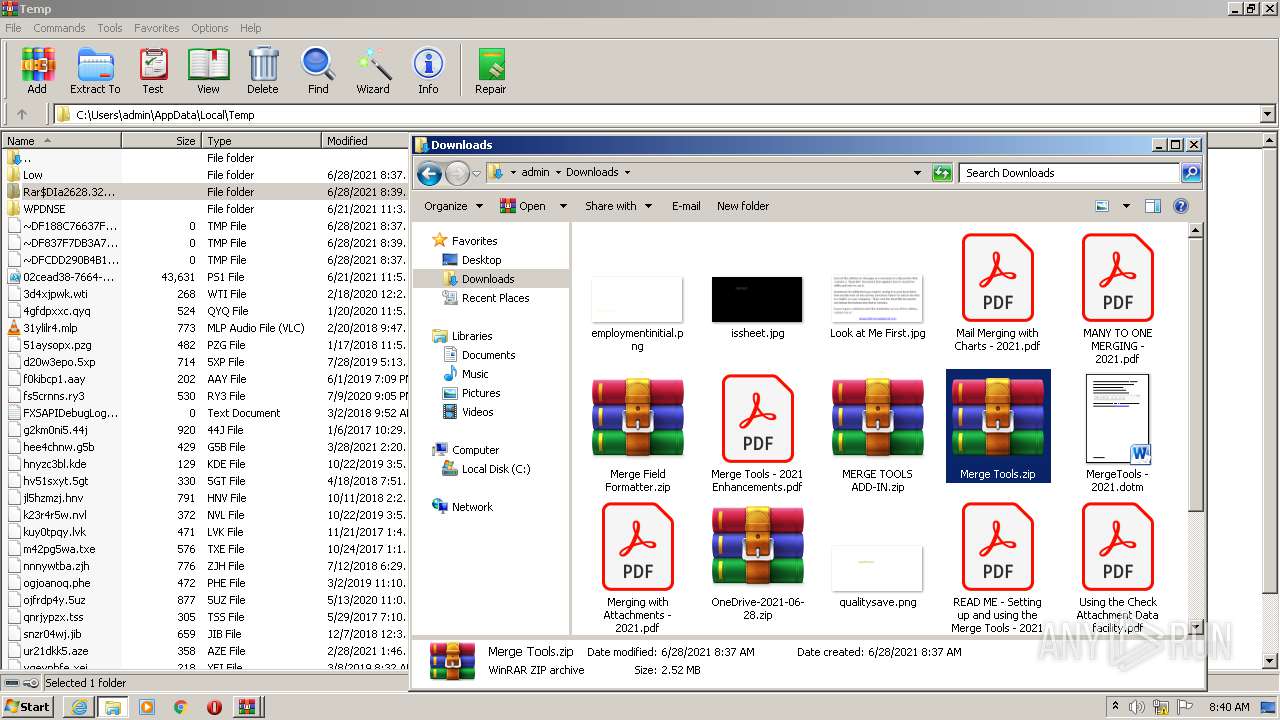
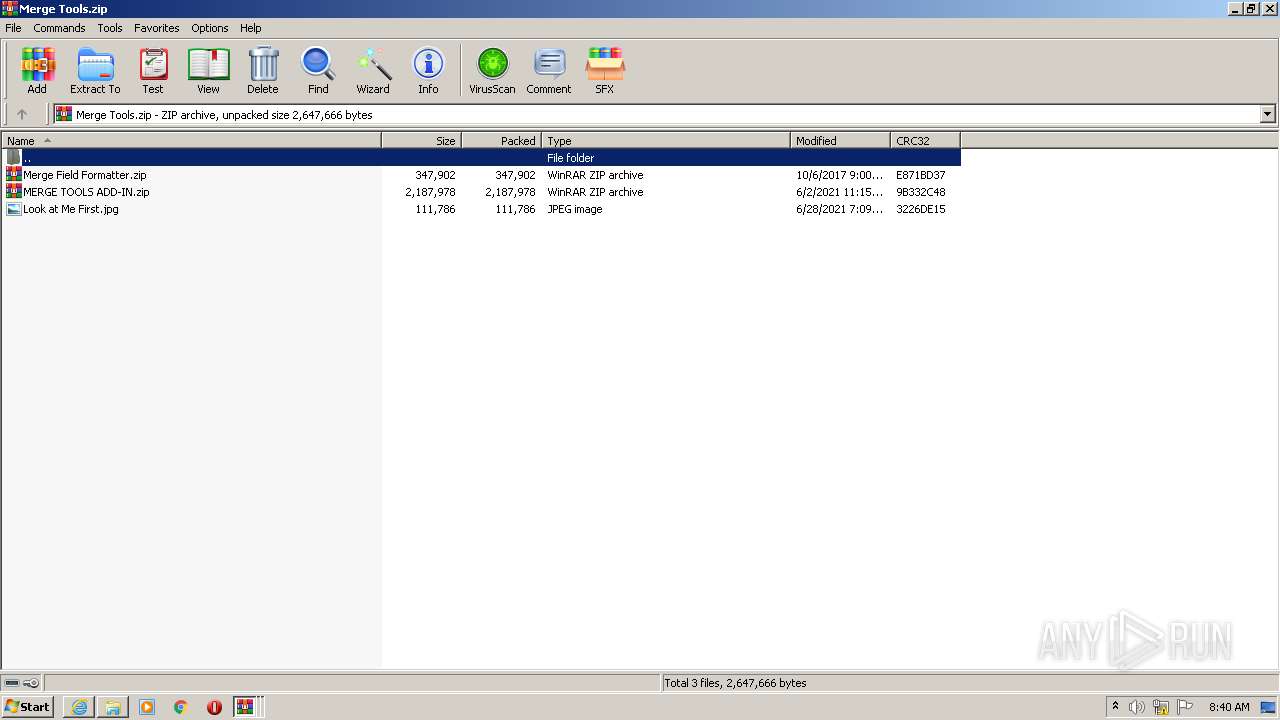
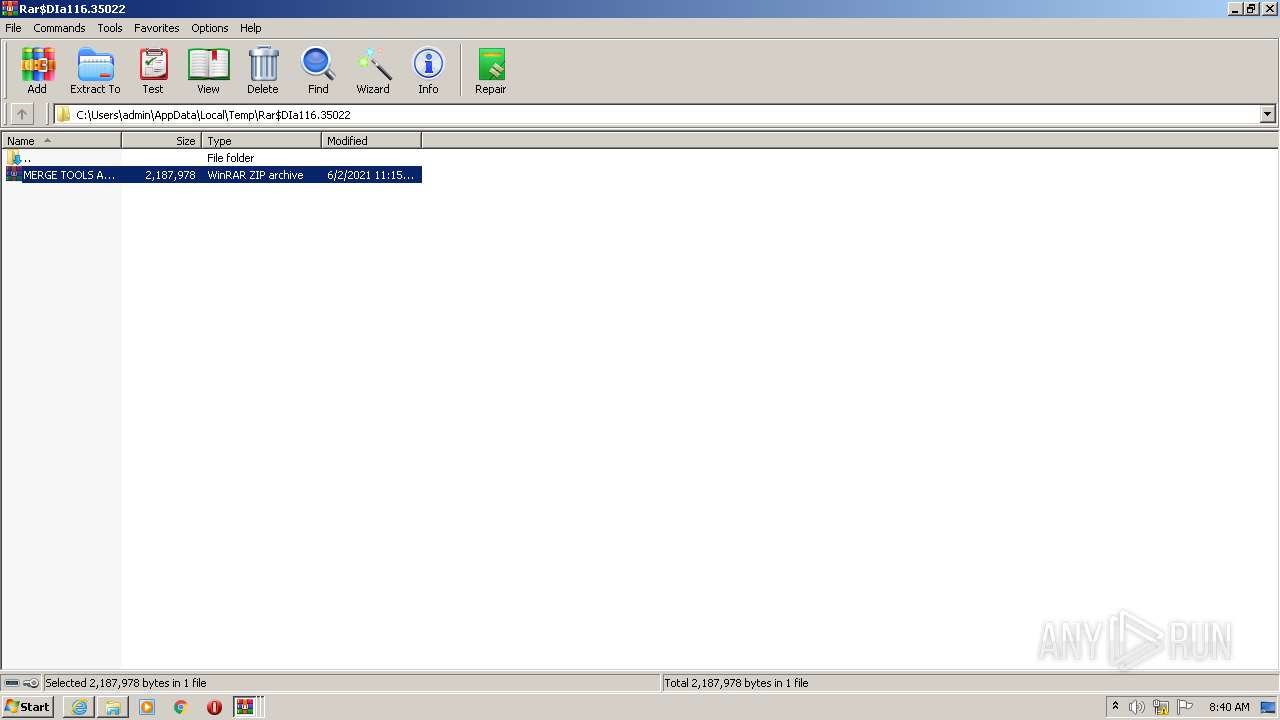
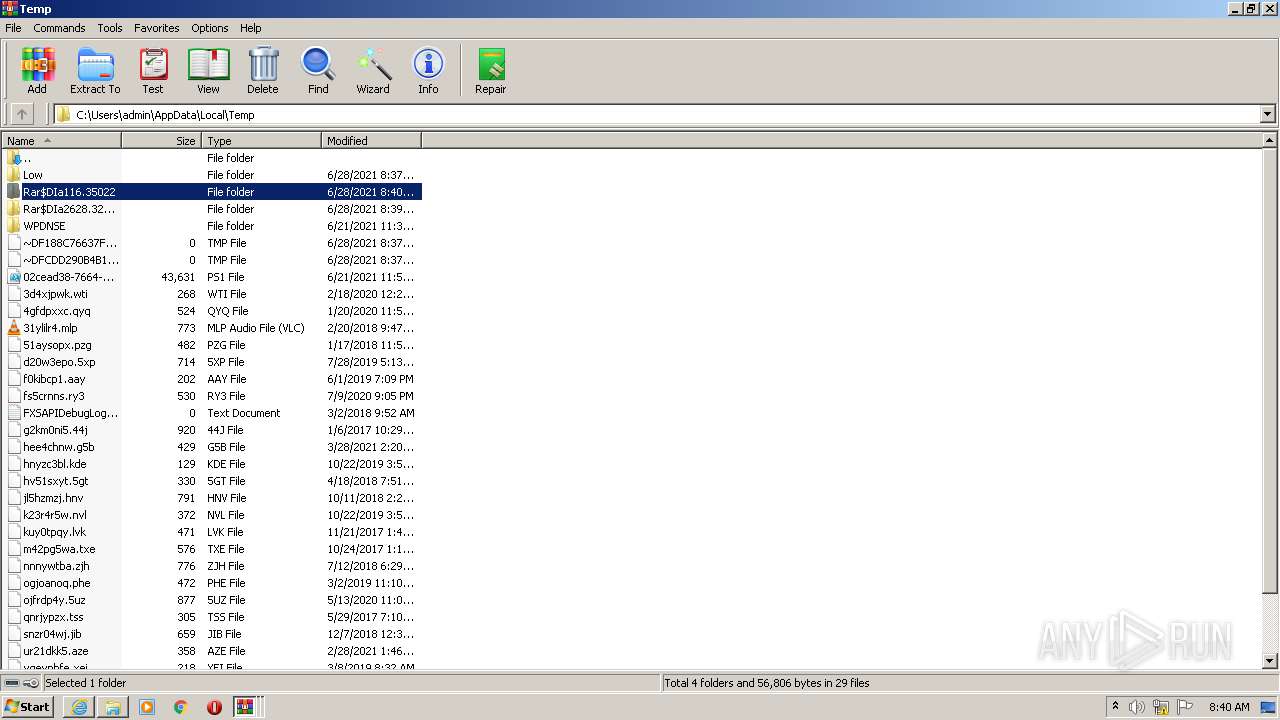
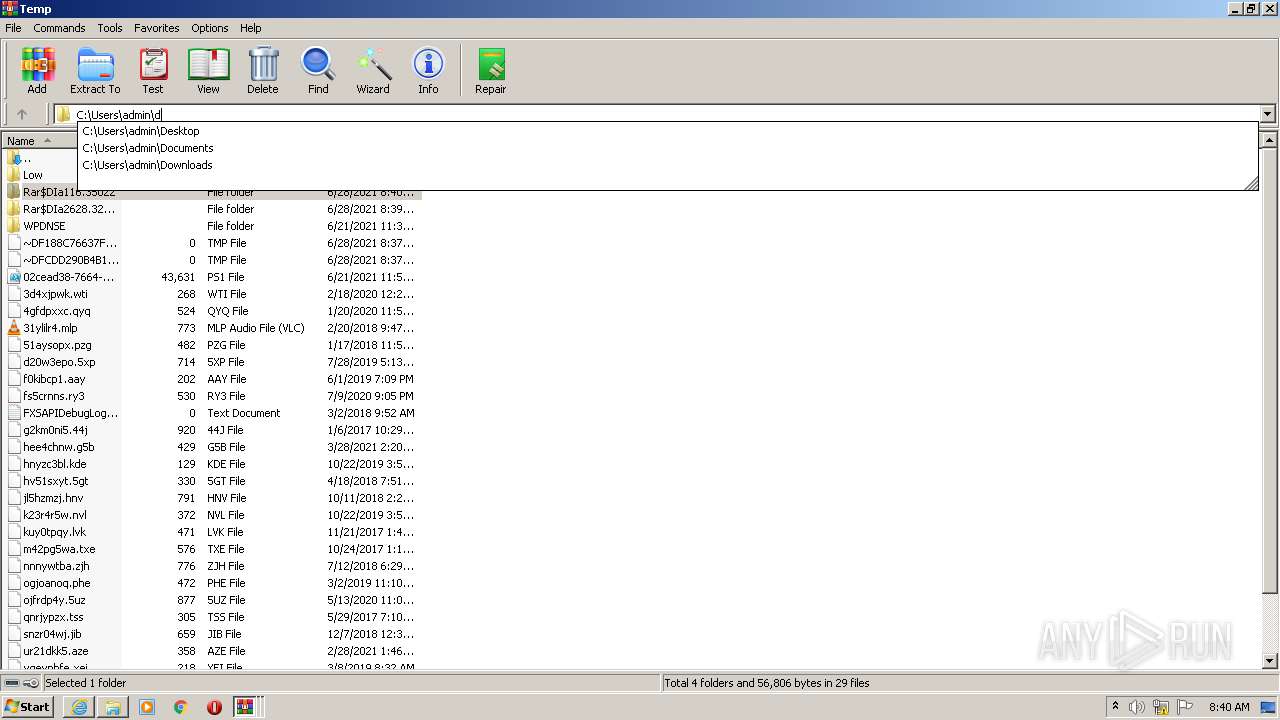
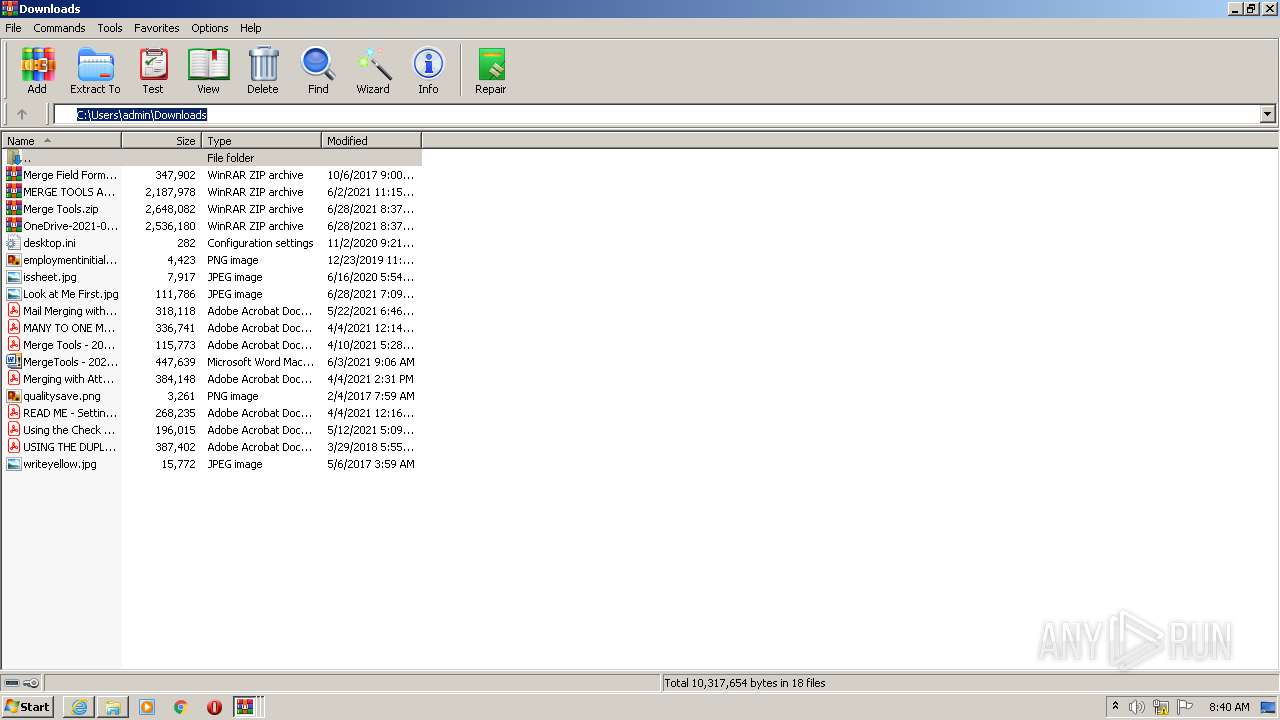
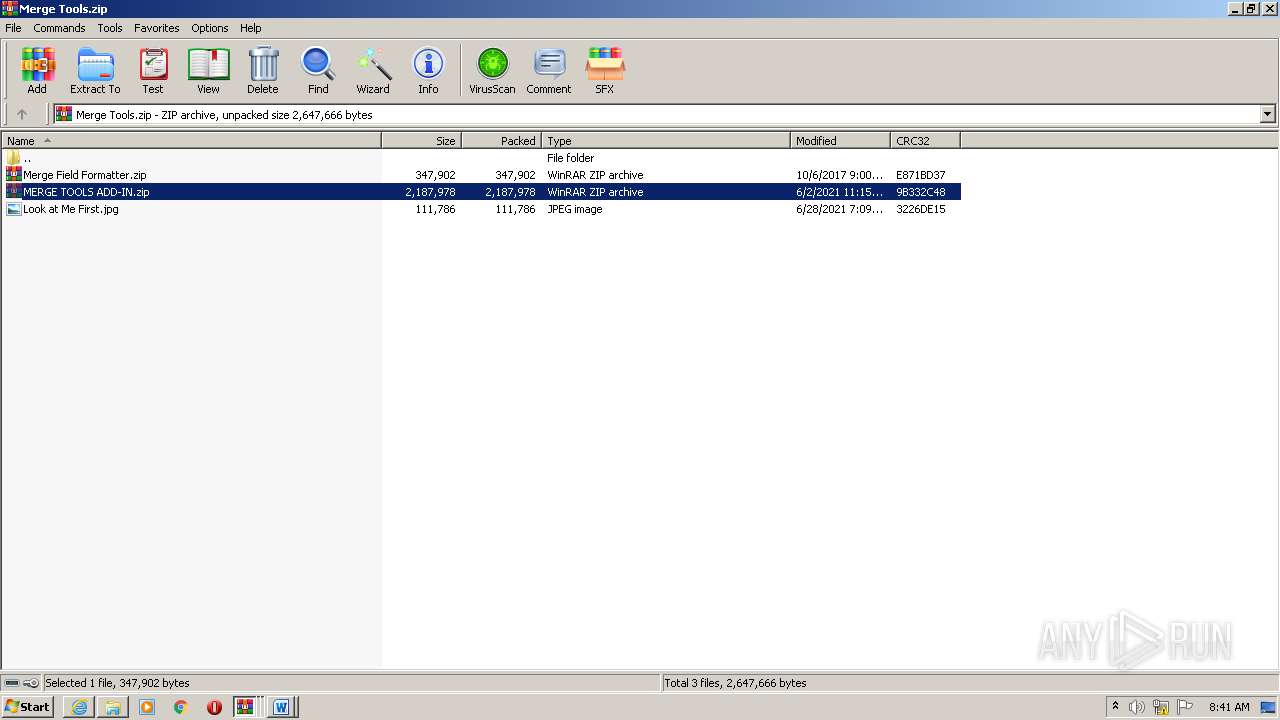
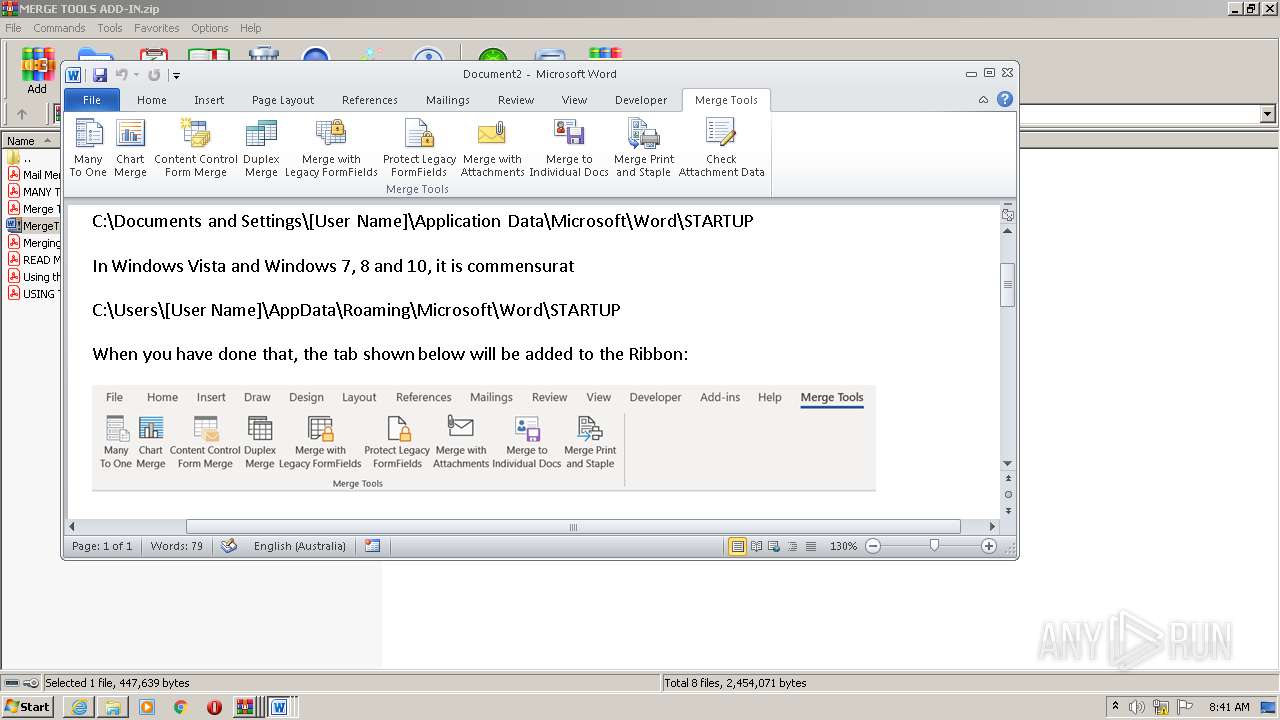
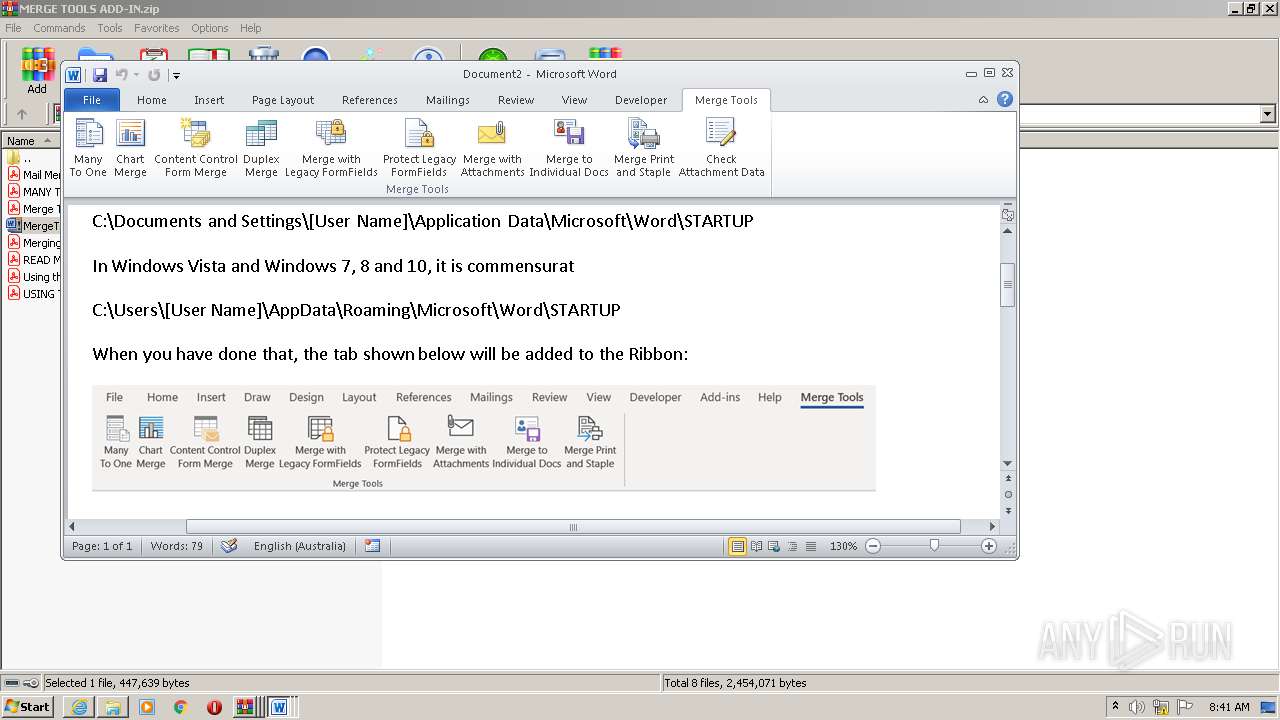
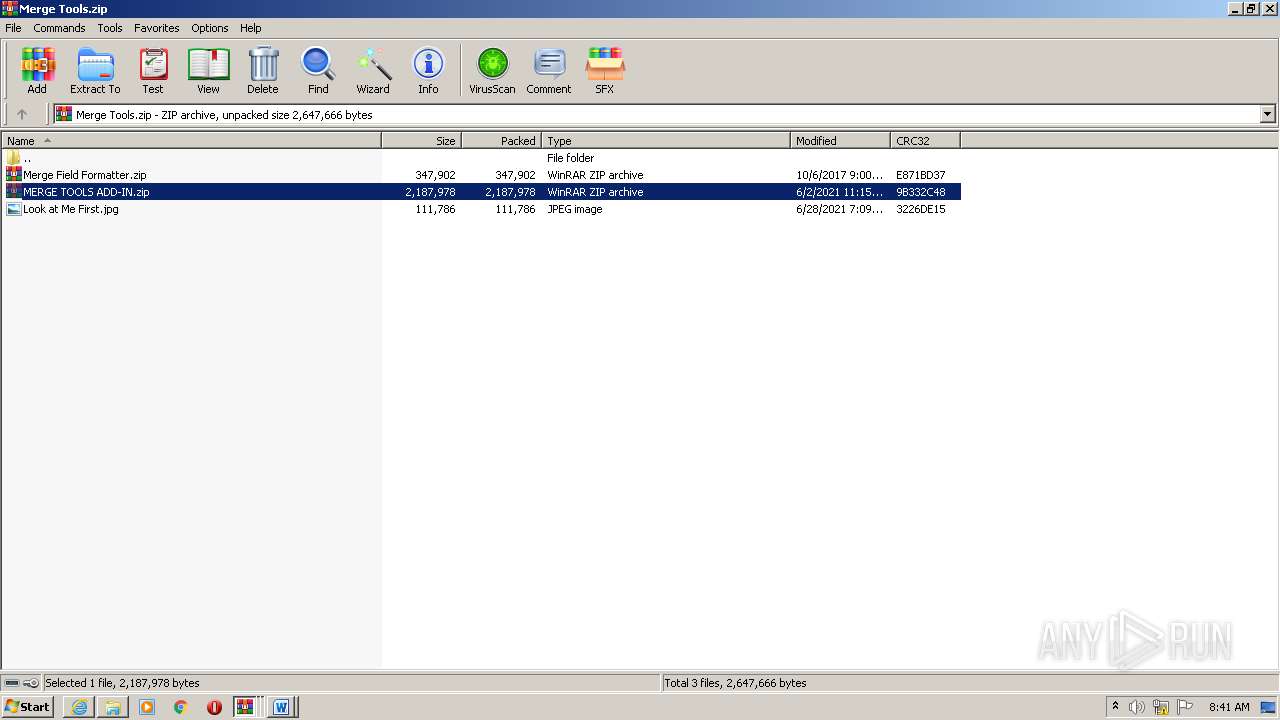
| 116 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Merge Tools.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
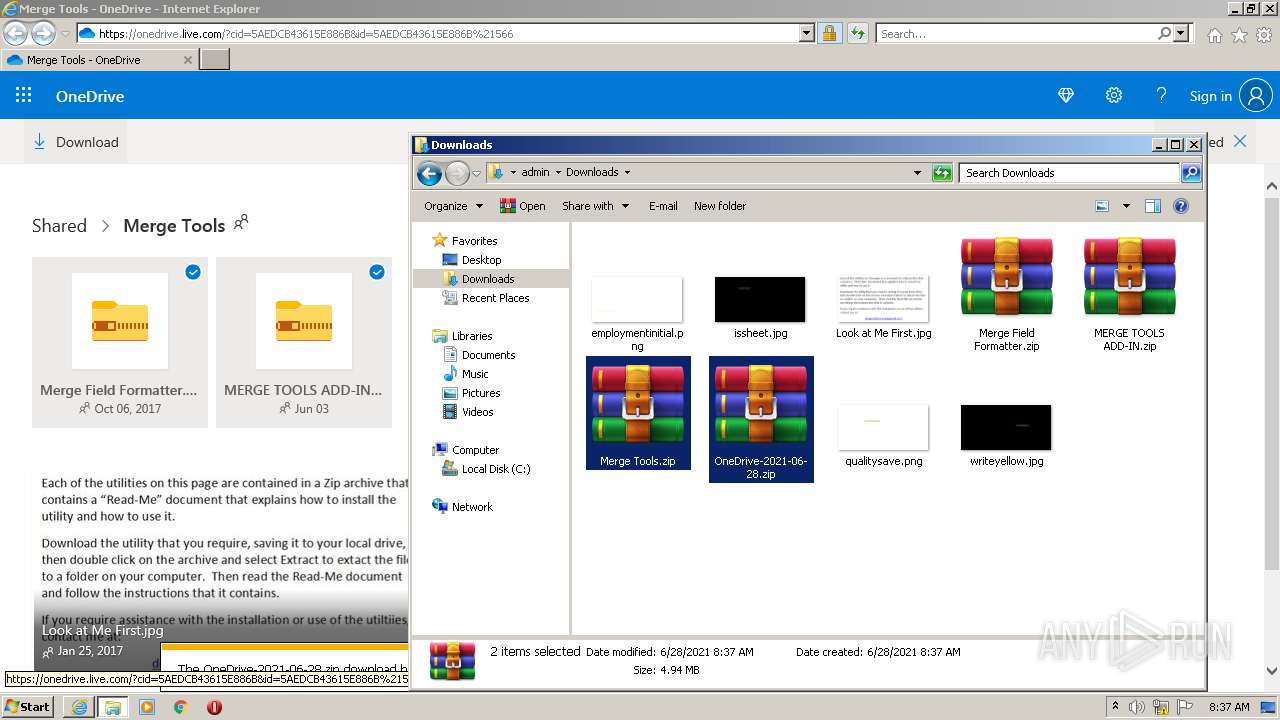
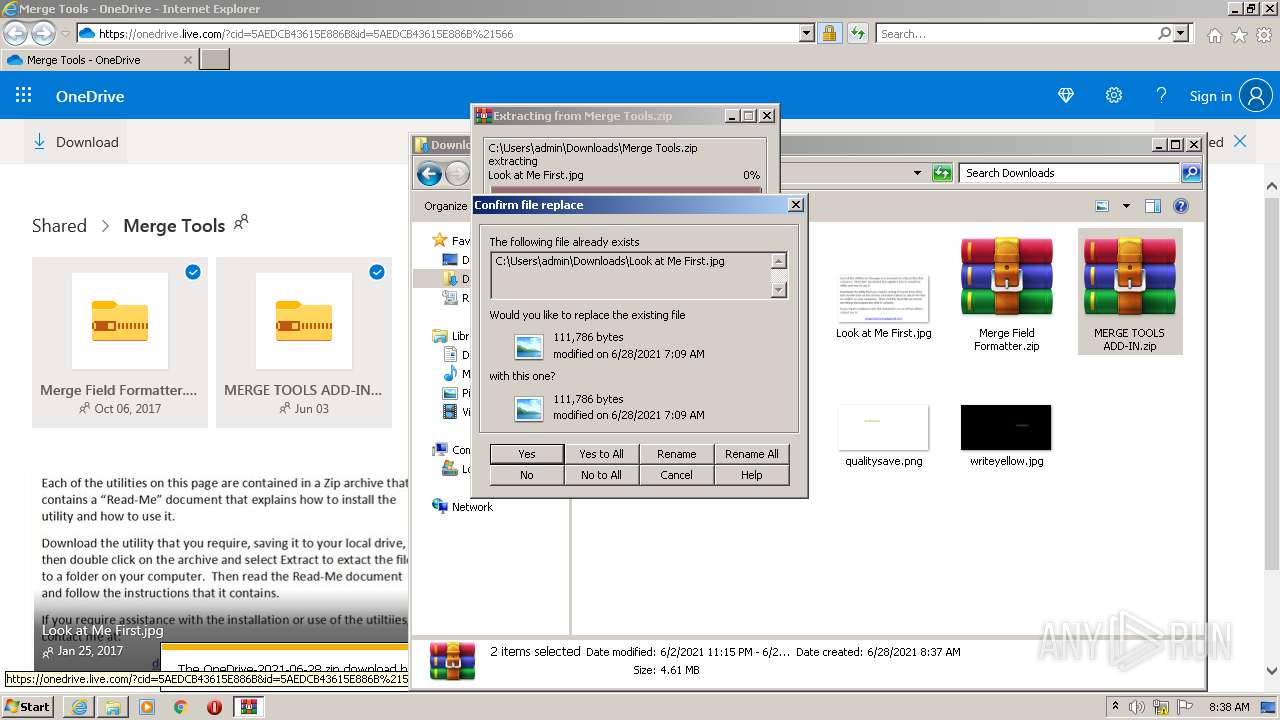
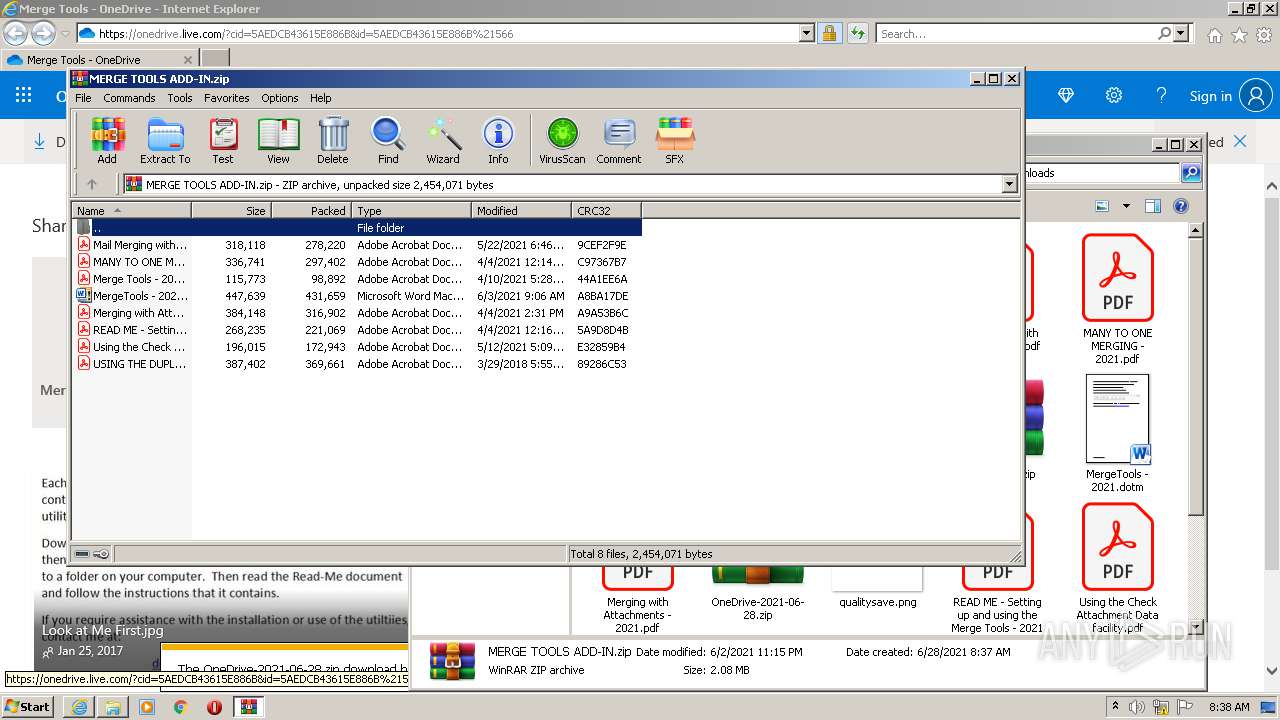
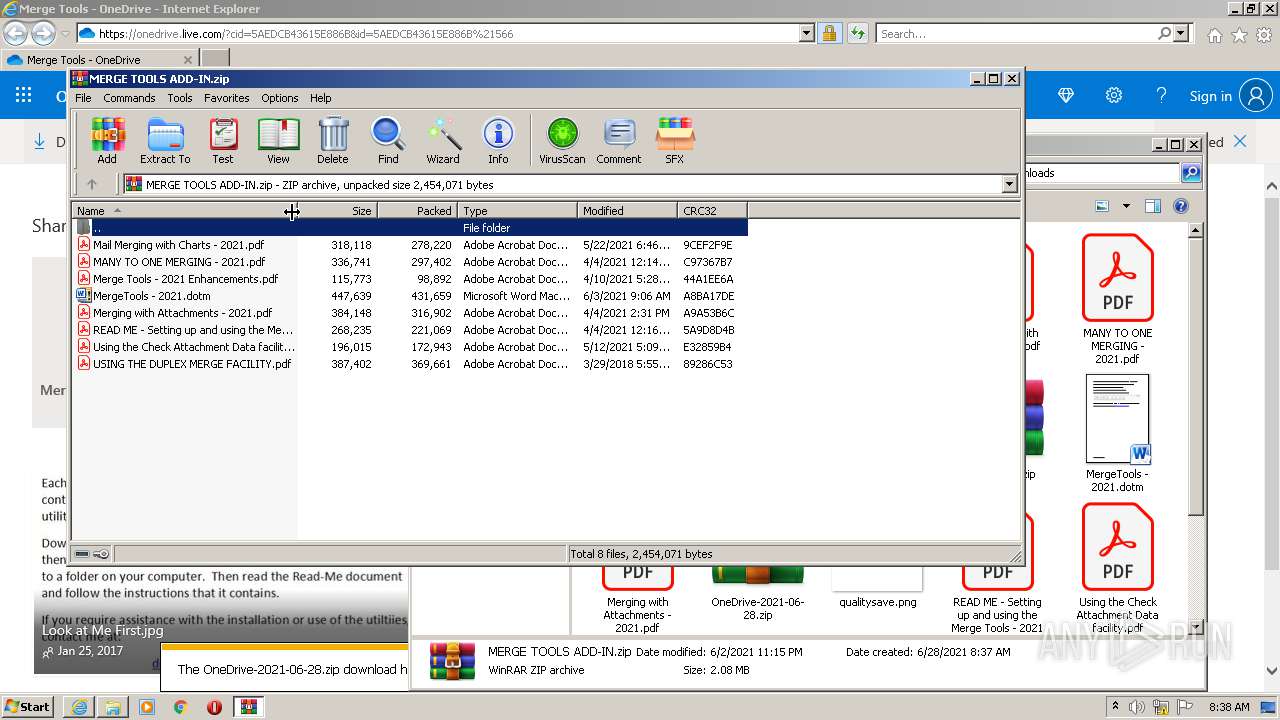
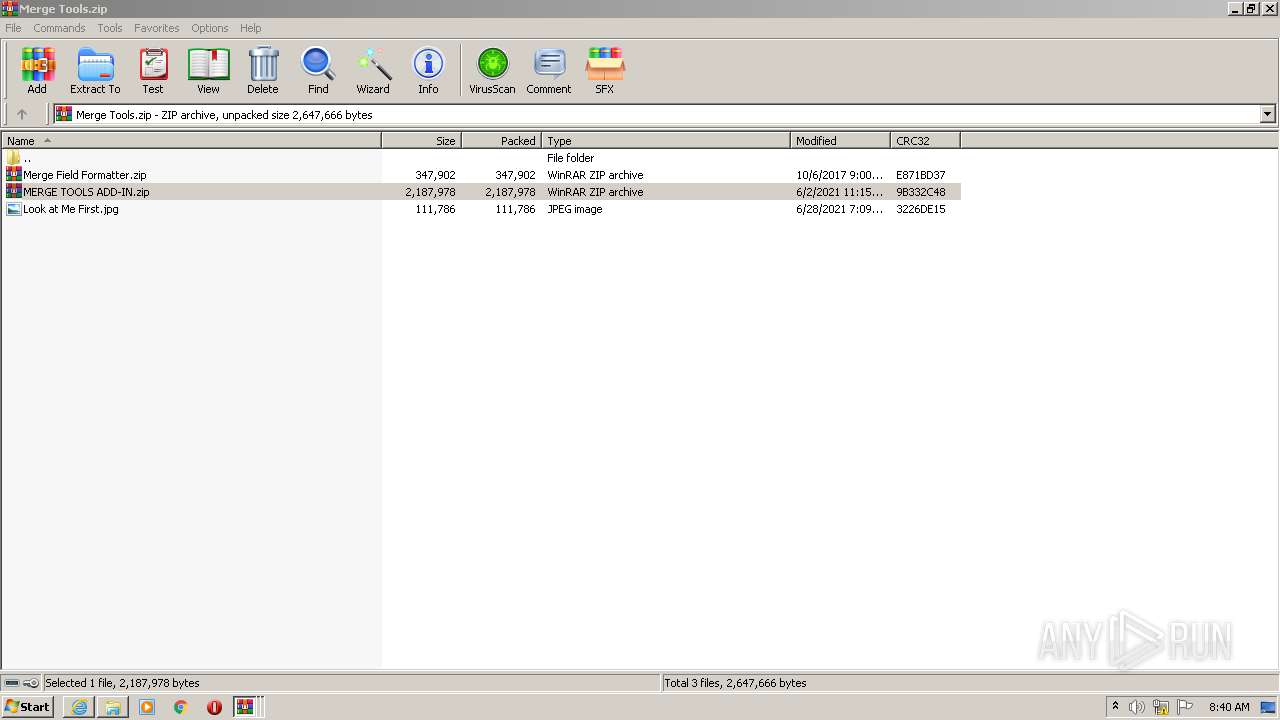
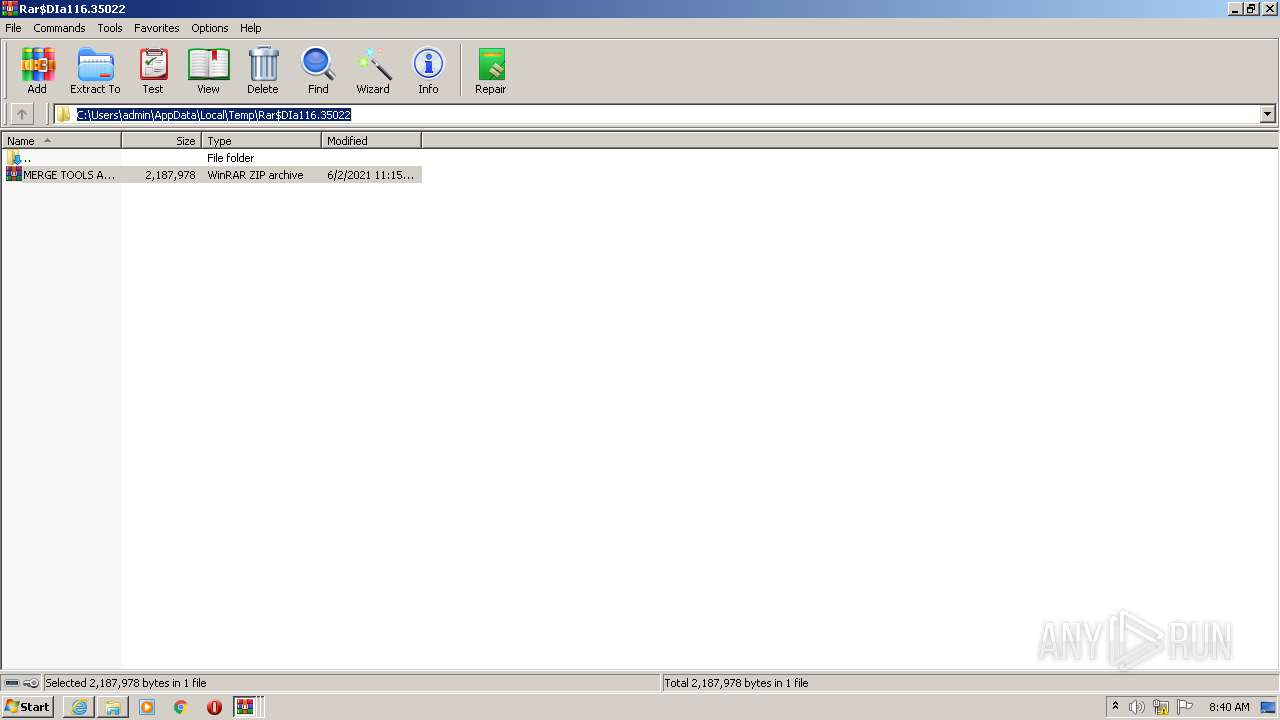
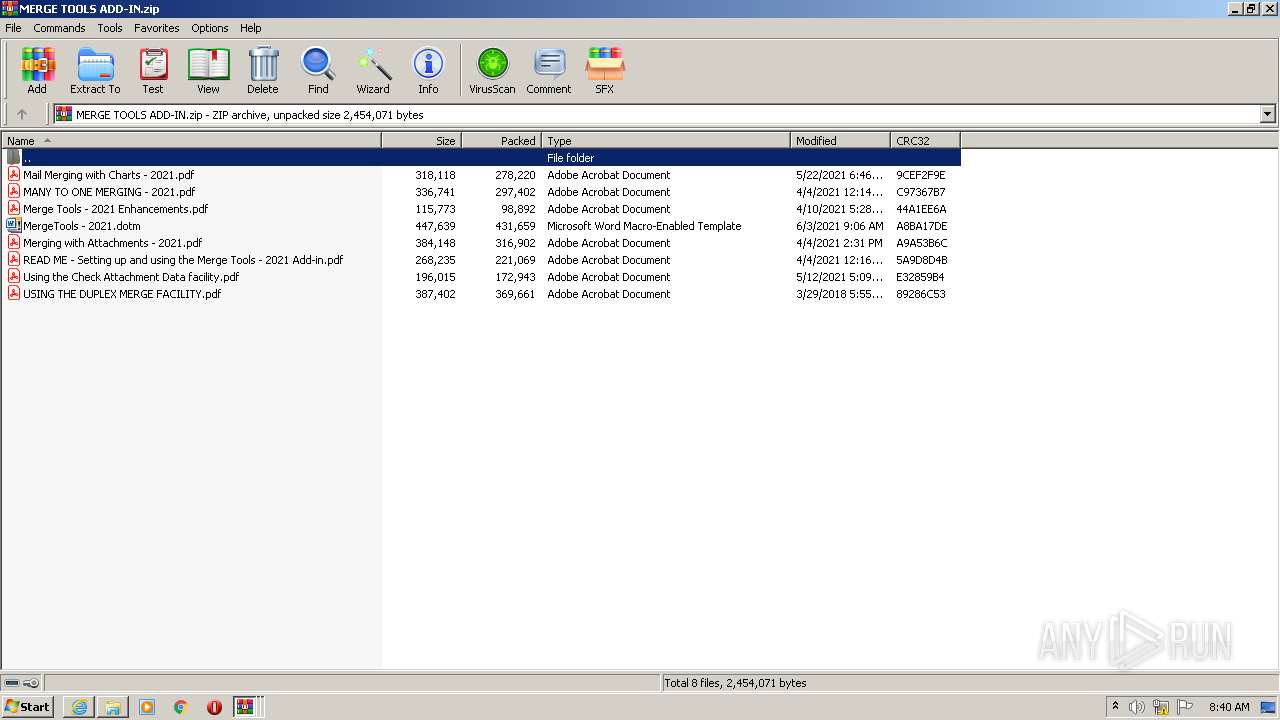
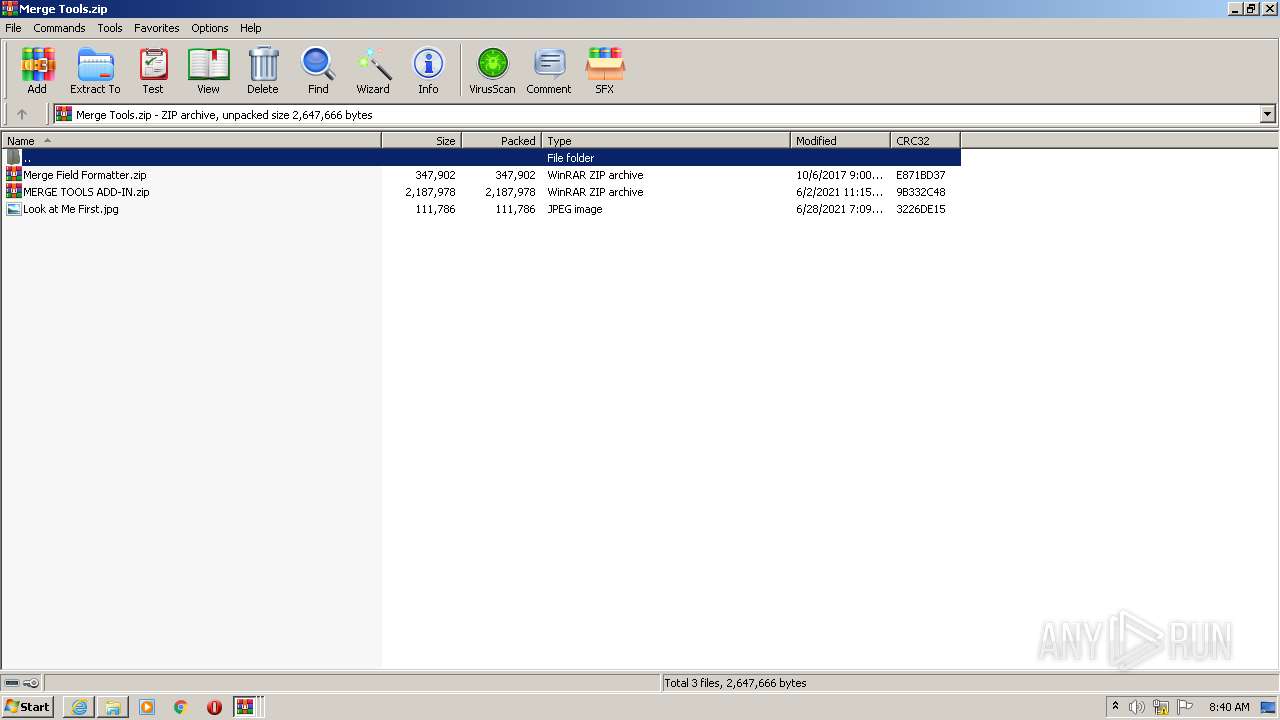
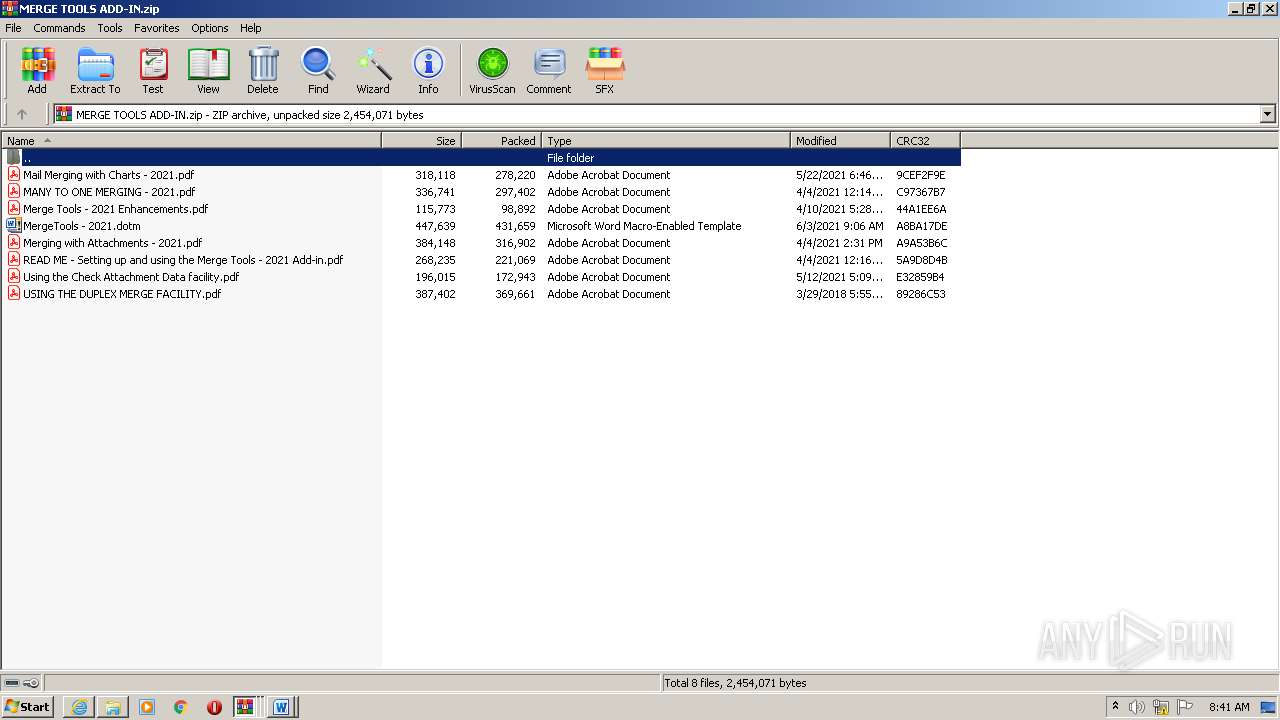
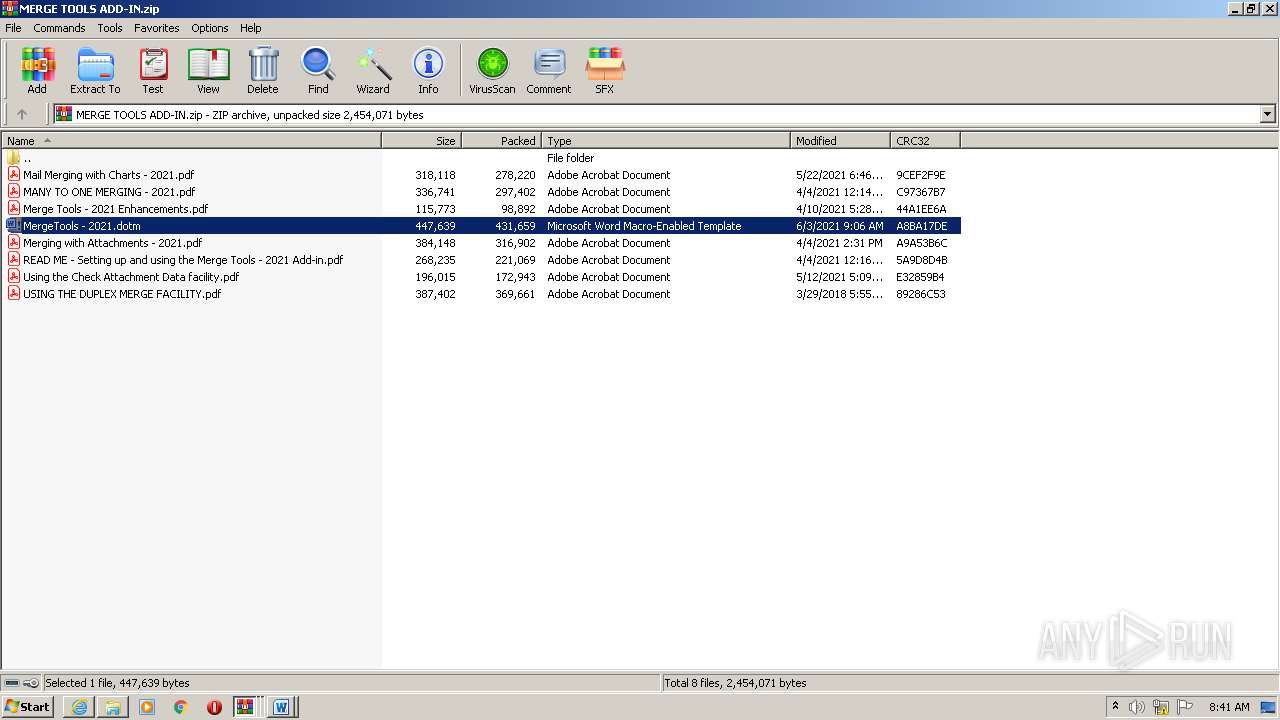
| 368 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa116.35022\MERGE TOOLS ADD-IN.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
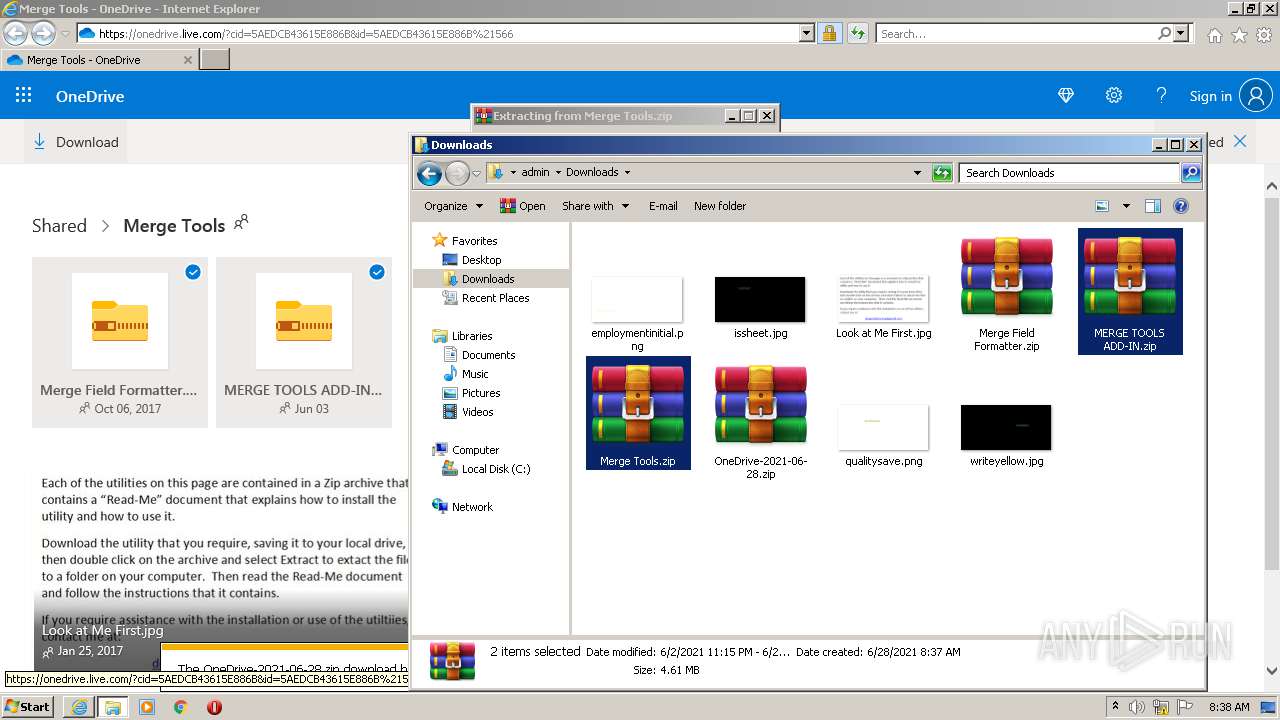
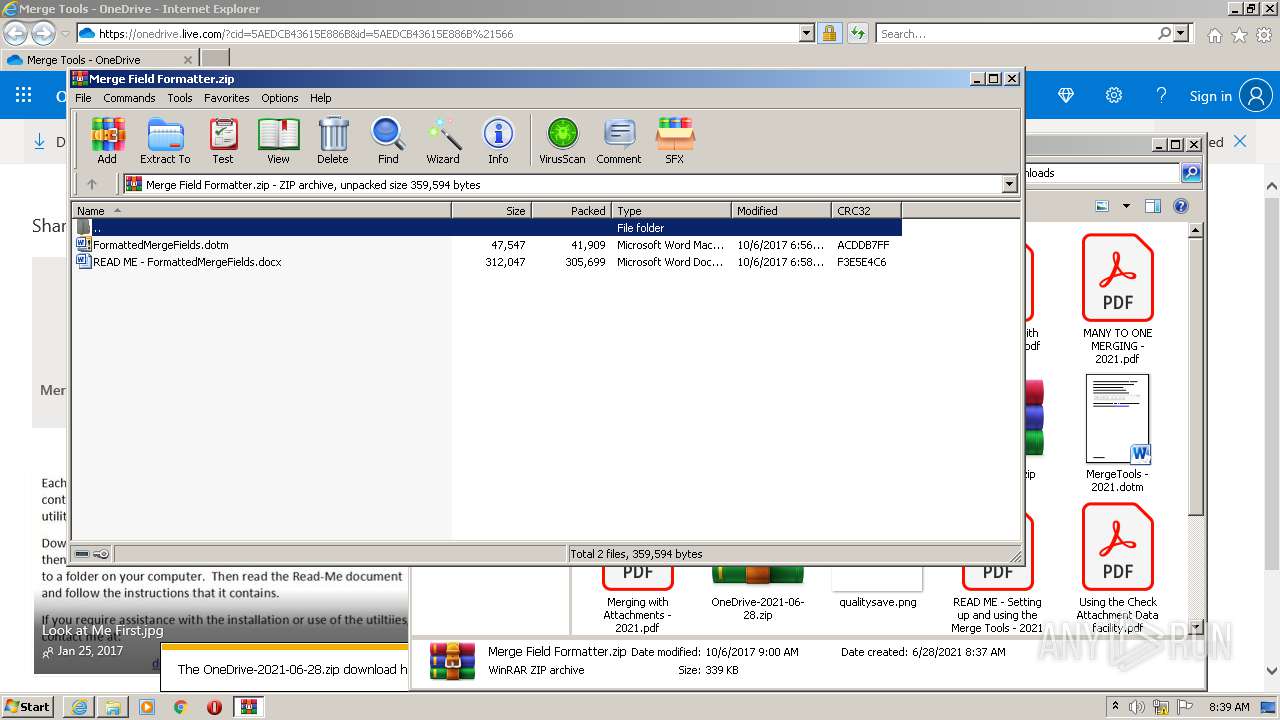
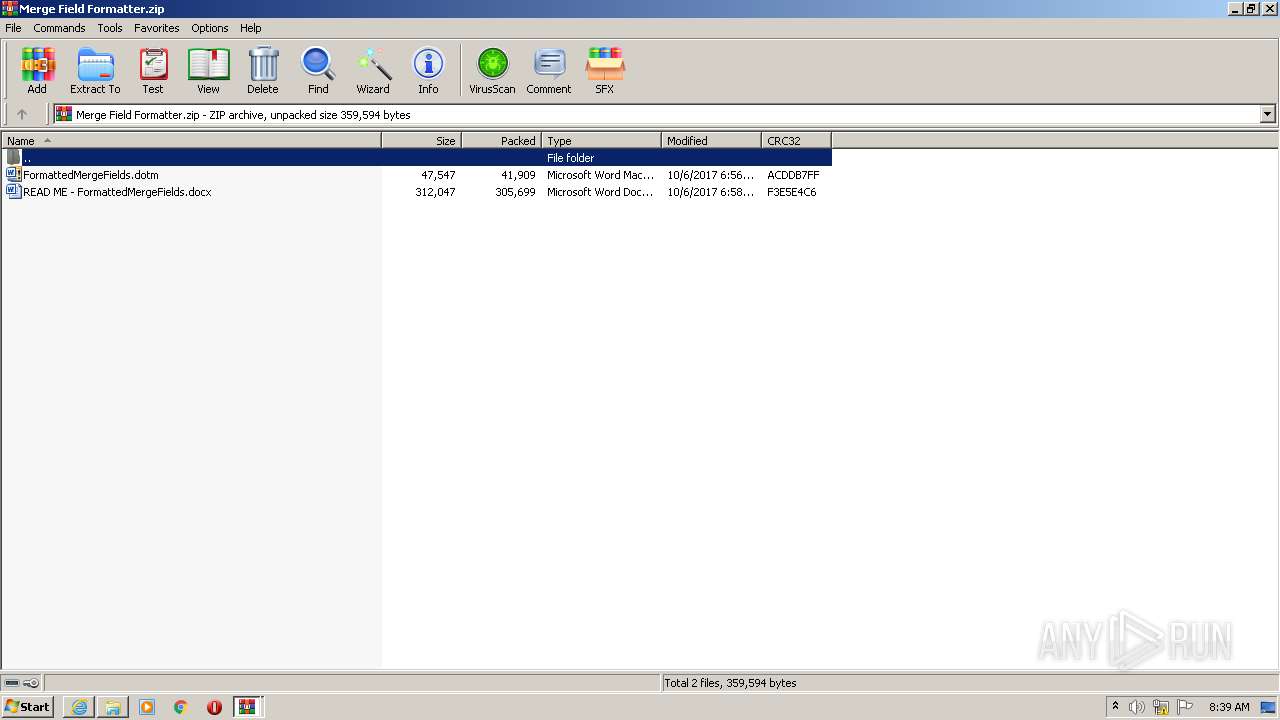
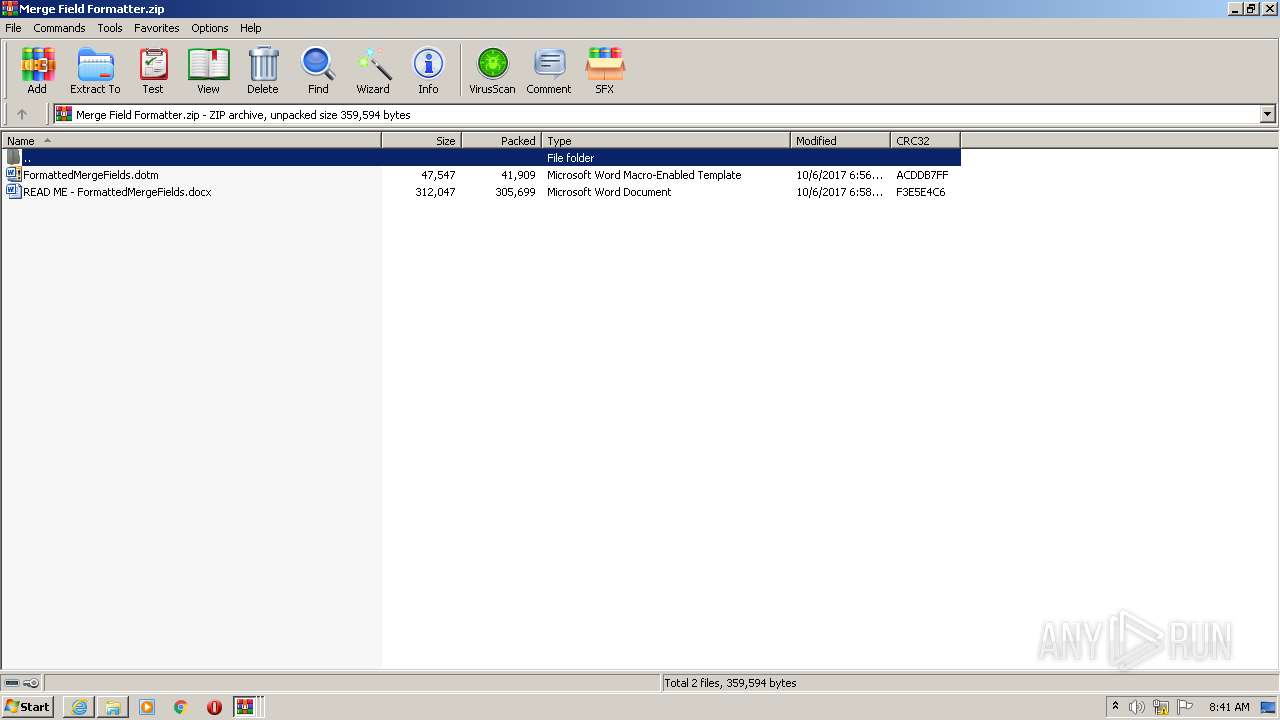
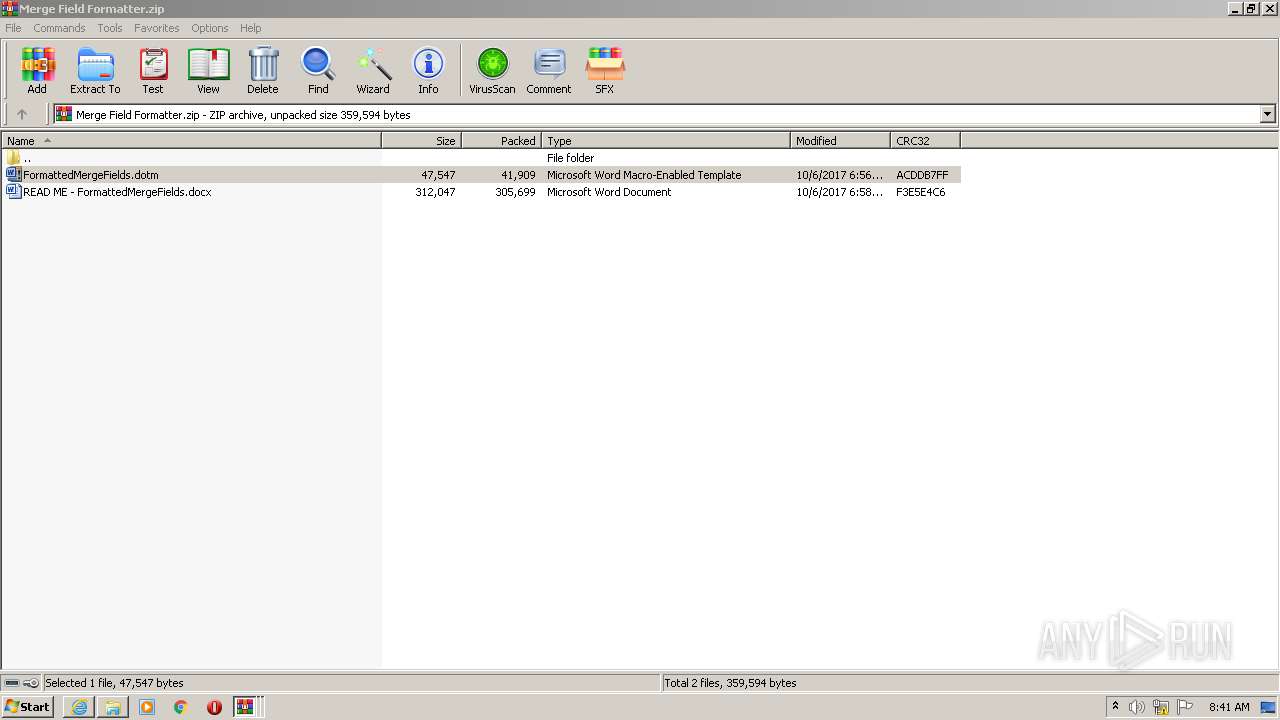
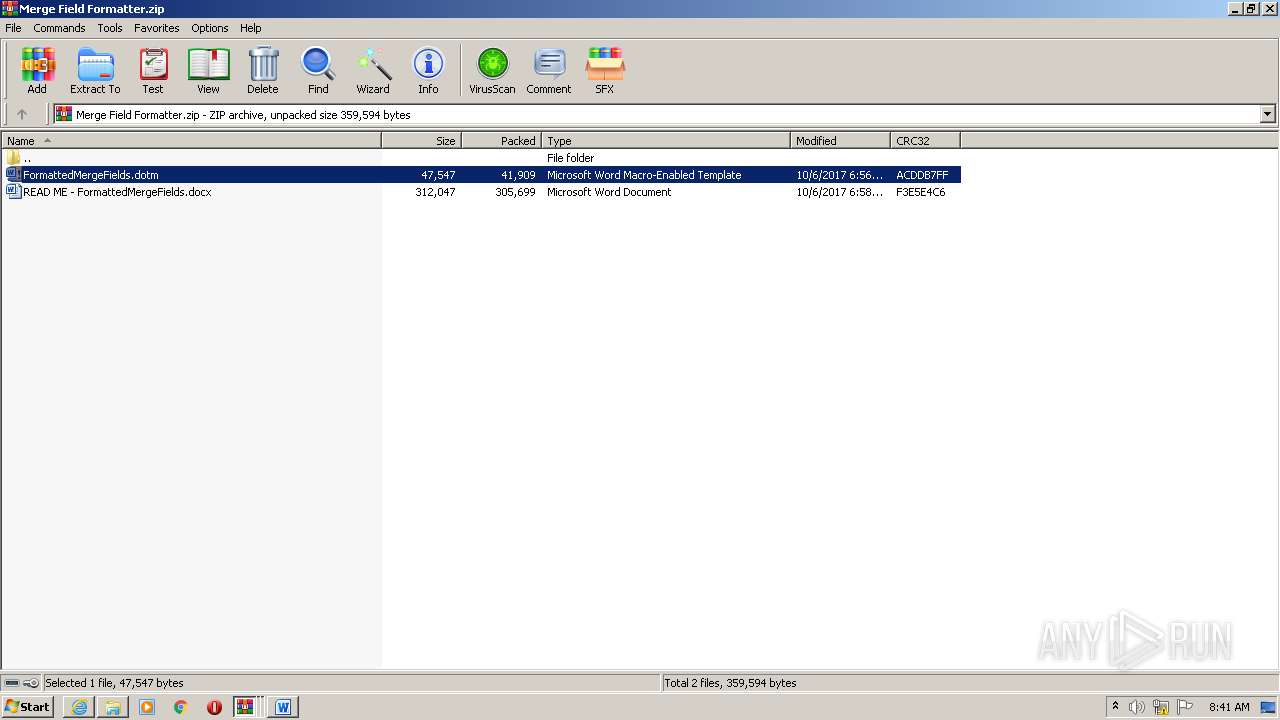
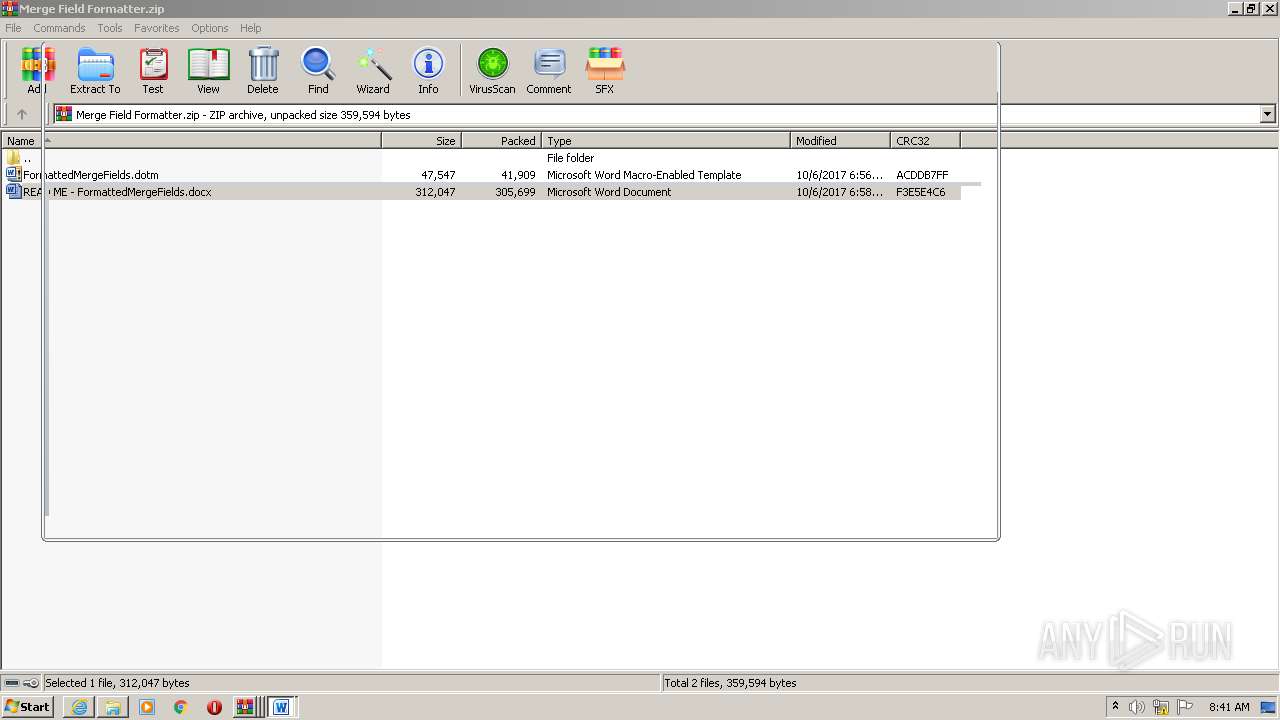
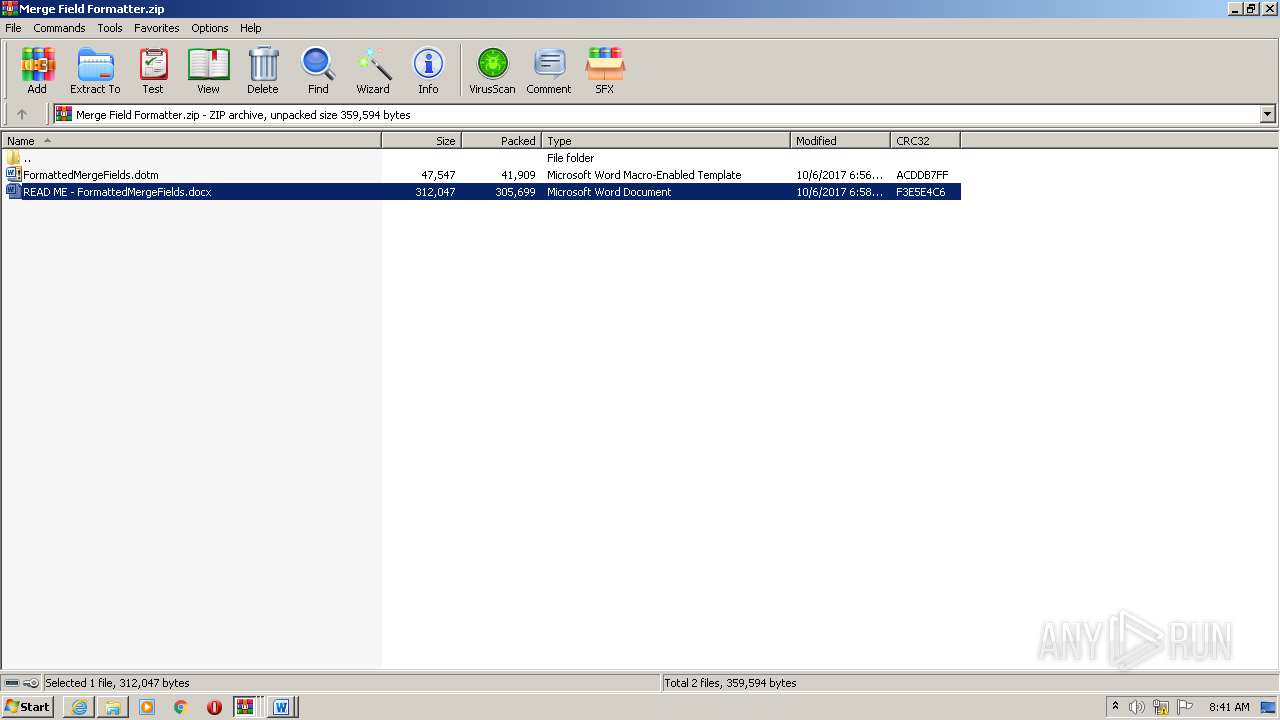
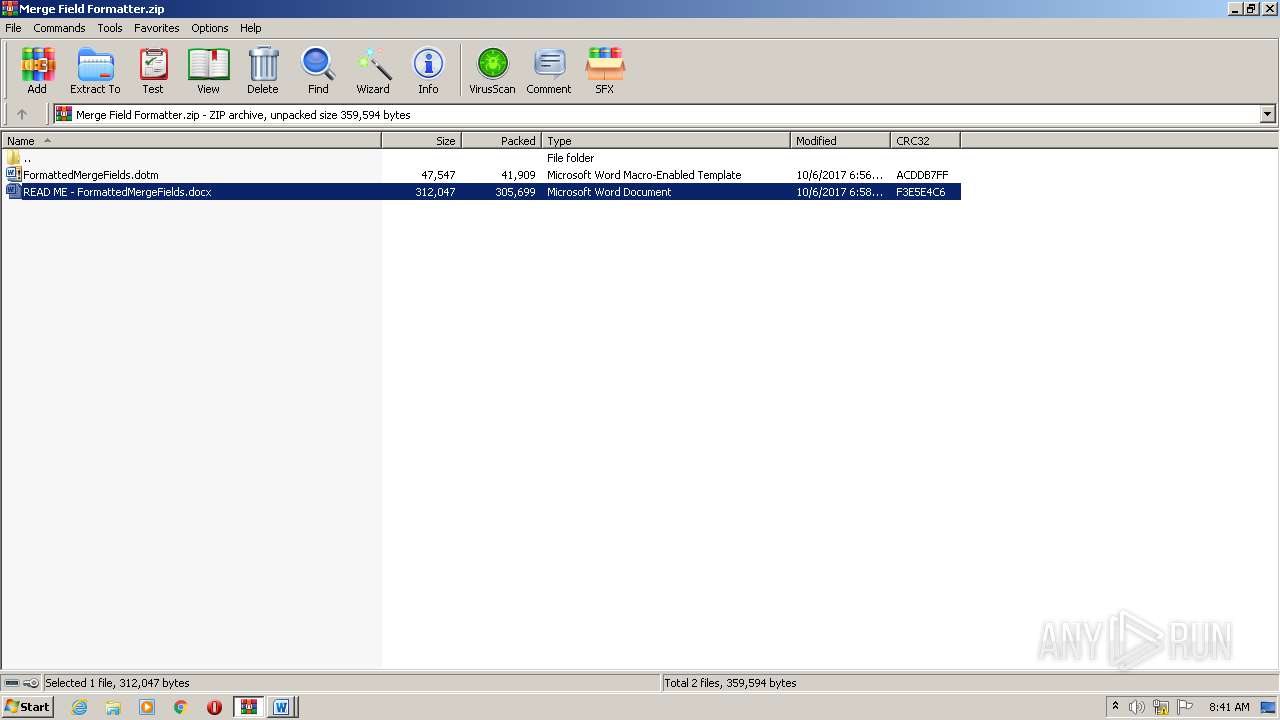
| 424 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Merge Field Formatter.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 748 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Merge Tools.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
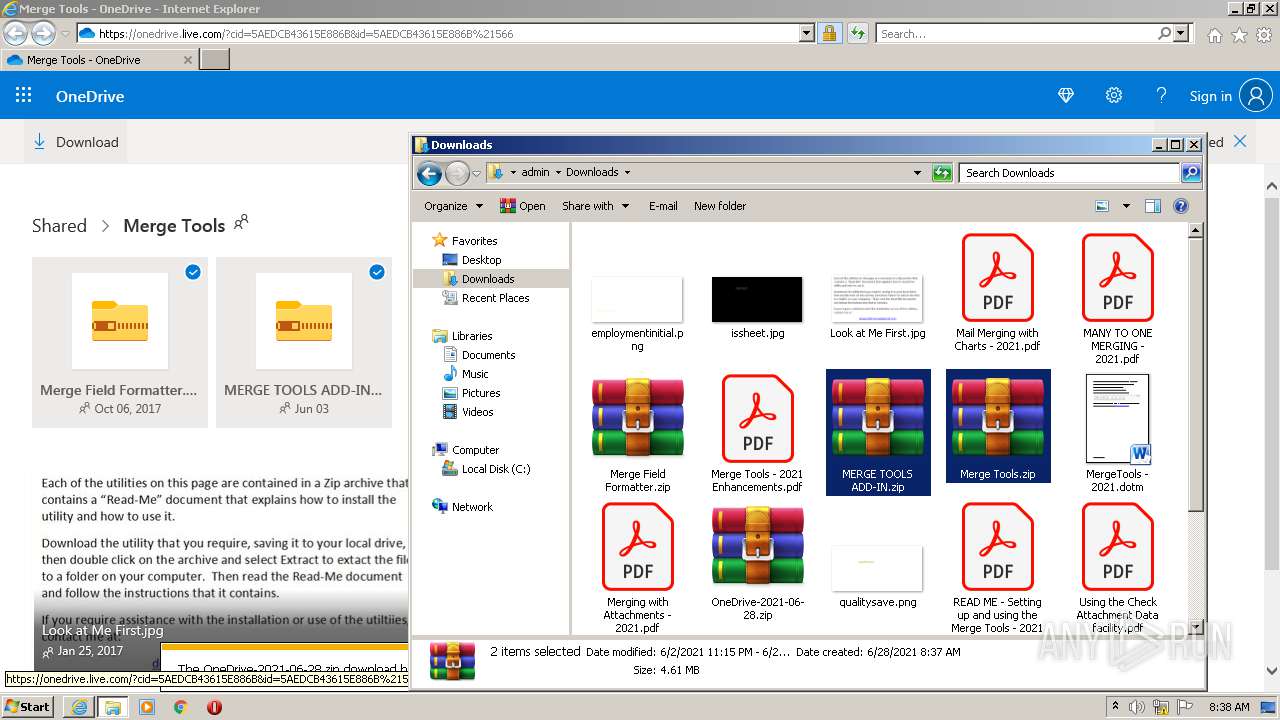
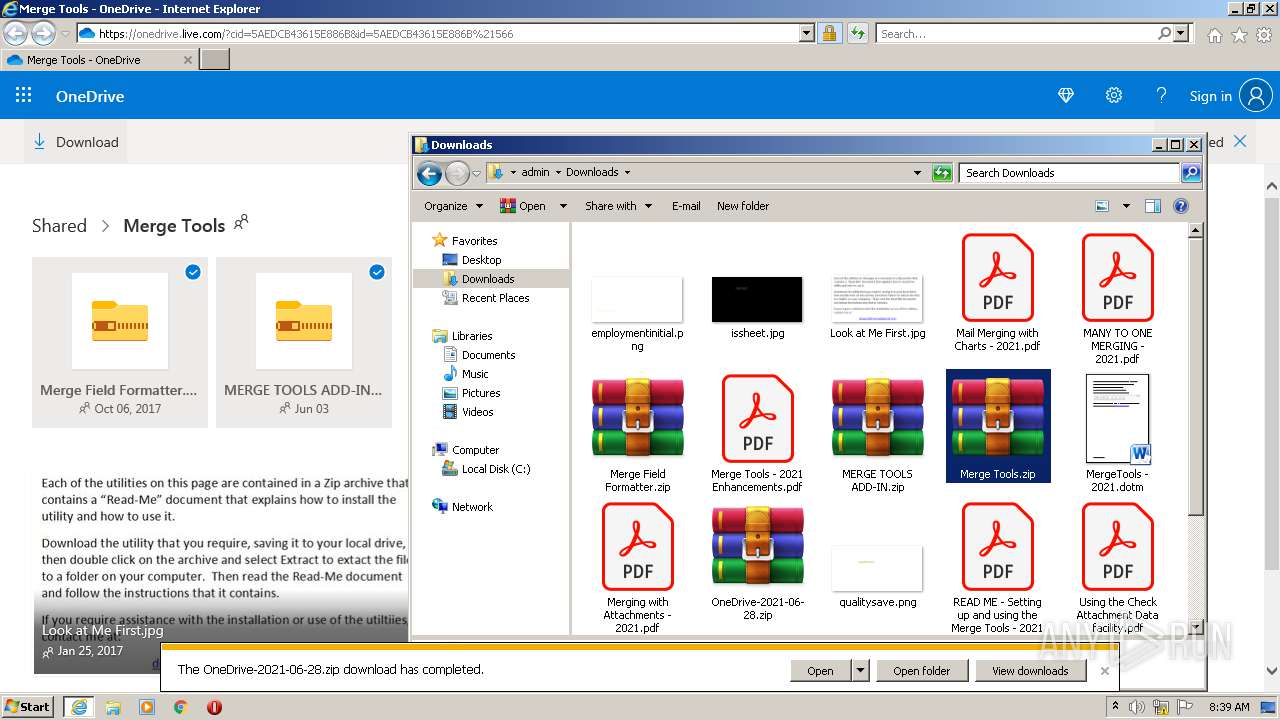
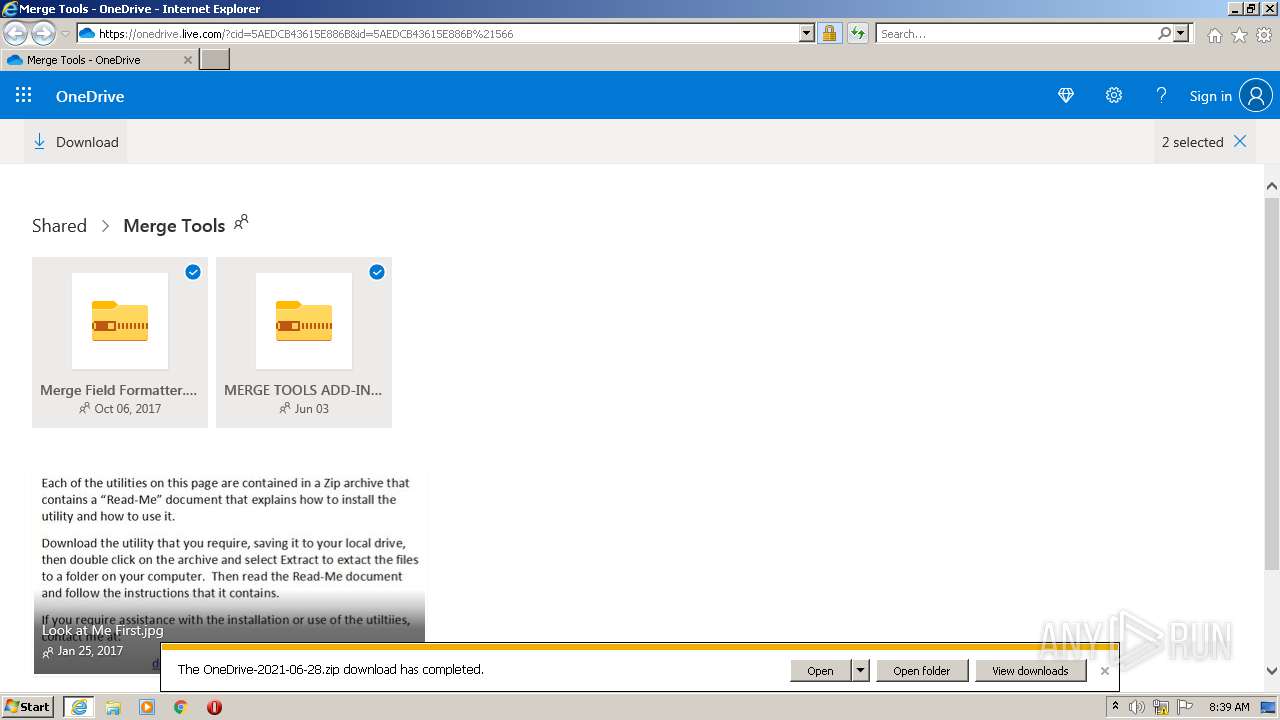
| 1124 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n /f "C:\Users\admin\AppData\Local\Temp\Rar$DIa2544.39467\FormattedMergeFields.dotm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
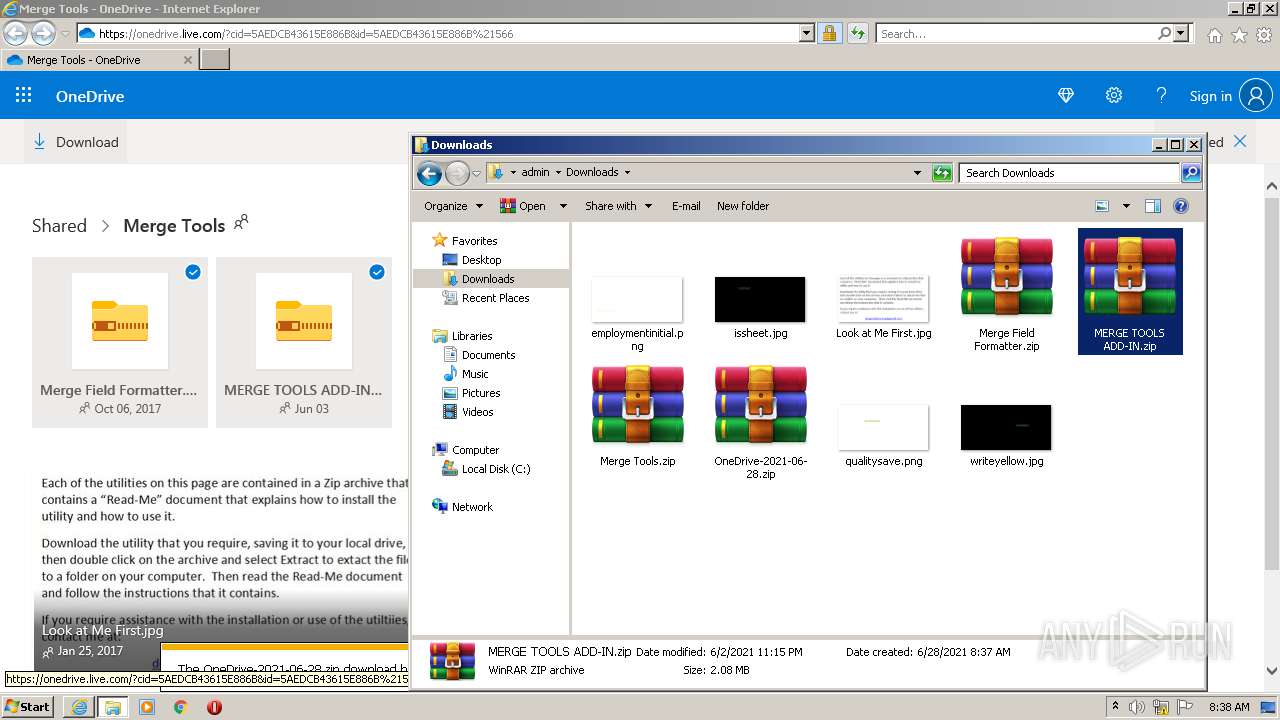
| 1260 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\MERGE TOOLS ADD-IN.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
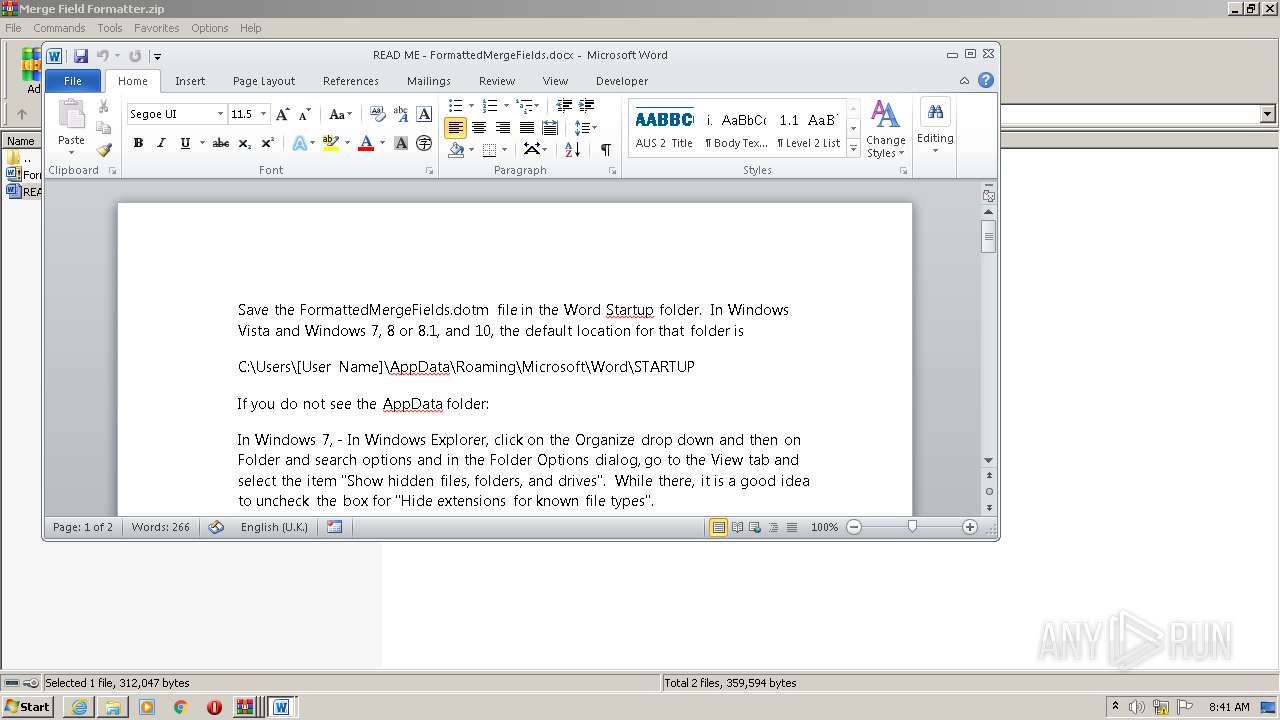
| 2084 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIa2544.40067\READ ME - FormattedMergeFields.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2096 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2348 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver "-an=C:\Users\admin\Downloads\OneDrive-2021-06-28.zip" -- "C:\Users\admin\Downloads\Merge Tools.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
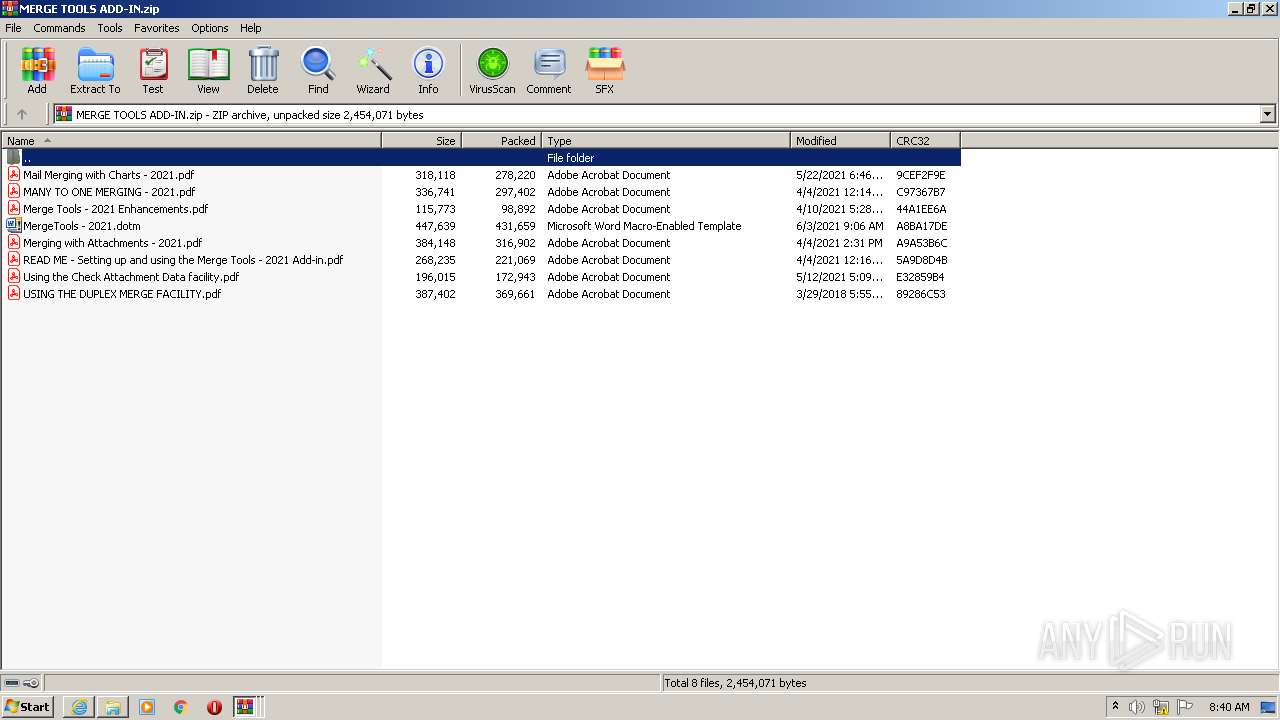
| 2360 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa368.40940\MERGE TOOLS ADD-IN.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
32 925
Read events
31 182
Write events
1 324
Delete events
419
Modification events
| (PID) Process: | (3560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30895088 | |||
| (PID) Process: | (3560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30895088 | |||
| (PID) Process: | (3560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3560) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
52
Text files
123
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_5FDD03068CBBD8A96F3AB9595BA10093 | binary | |
MD5:— | SHA256:— | |||
| 2916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\09722E241DA07BB8BCA1AB0EE758767E_A056E4699706E1854957F3388359507D | binary | |
MD5:— | SHA256:— | |||
| 2916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_5FDD03068CBBD8A96F3AB9595BA10093 | der | |
MD5:— | SHA256:— | |||
| 2916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2916 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\04U0D06P.txt | text | |
MD5:— | SHA256:— | |||
| 2916 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\onedrive-font-face-definitions[1].css | text | |
MD5:— | SHA256:— | |||
| 2916 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\plt.items-view.chunk[1].js | text | |
MD5:— | SHA256:— | |||
| 2916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 2916 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\plt.react.chunk[1].js | text | |
MD5:— | SHA256:— | |||
| 2916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
65
DNS requests
35
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2916 | iexplore.exe | GET | 200 | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSjA8CoiHvUecQnjrXXWH08EsBNpAQU%2Fy9%2F4Qb0OPMt7SWNmML%2BDvZs%2FPoCE38AAAYae8zhyn488usAAAAABho%3D | US | der | 1.70 Kb | whitelisted |
2916 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2916 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2916 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC3sP%2BMWqzHfwoAAAAA3JEd | US | der | 472 b | whitelisted |
3560 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | US | der | 471 b | whitelisted |
2916 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCvGbInaJdxsAoAAAAA3JGP | US | der | 472 b | whitelisted |
2916 | iexplore.exe | GET | 200 | 67.26.83.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?271403a351d88b7c | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3560 | iexplore.exe | 13.95.147.73:443 | p.sfx.ms | Microsoft Corporation | NL | whitelisted |
2916 | iexplore.exe | 104.111.225.185:443 | static2.sharepointonline.com | Akamai International B.V. | NL | unknown |
3560 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2916 | iexplore.exe | 2.16.186.25:443 | spoprod-a.akamaihd.net | Akamai International B.V. | — | whitelisted |
2916 | iexplore.exe | 13.105.66.144:443 | skyapi.onedrive.live.com | Microsoft Corporation | US | unknown |
2916 | iexplore.exe | 52.114.159.22:443 | browser.pipe.aria.microsoft.com | Microsoft Corporation | US | unknown |
2916 | iexplore.exe | 104.111.247.247:443 | shellprod.msocdn.com | Akamai International B.V. | NL | unknown |
2916 | iexplore.exe | 2.18.232.238:443 | shell.cdn.office.net | Akamai International B.V. | — | whitelisted |
2916 | iexplore.exe | 152.199.19.160:443 | az725175.vo.msecnd.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2916 | iexplore.exe | 13.107.43.12:443 | dsm01pap002files.storage.live.com | Microsoft Corporation | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
onedrive.live.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
static2.sharepointonline.com |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |
p.sfx.ms |
| whitelisted |
spoprod-a.akamaihd.net |
| whitelisted |
skyapi.onedrive.live.com |
| shared |