| File name: | generator.exe |
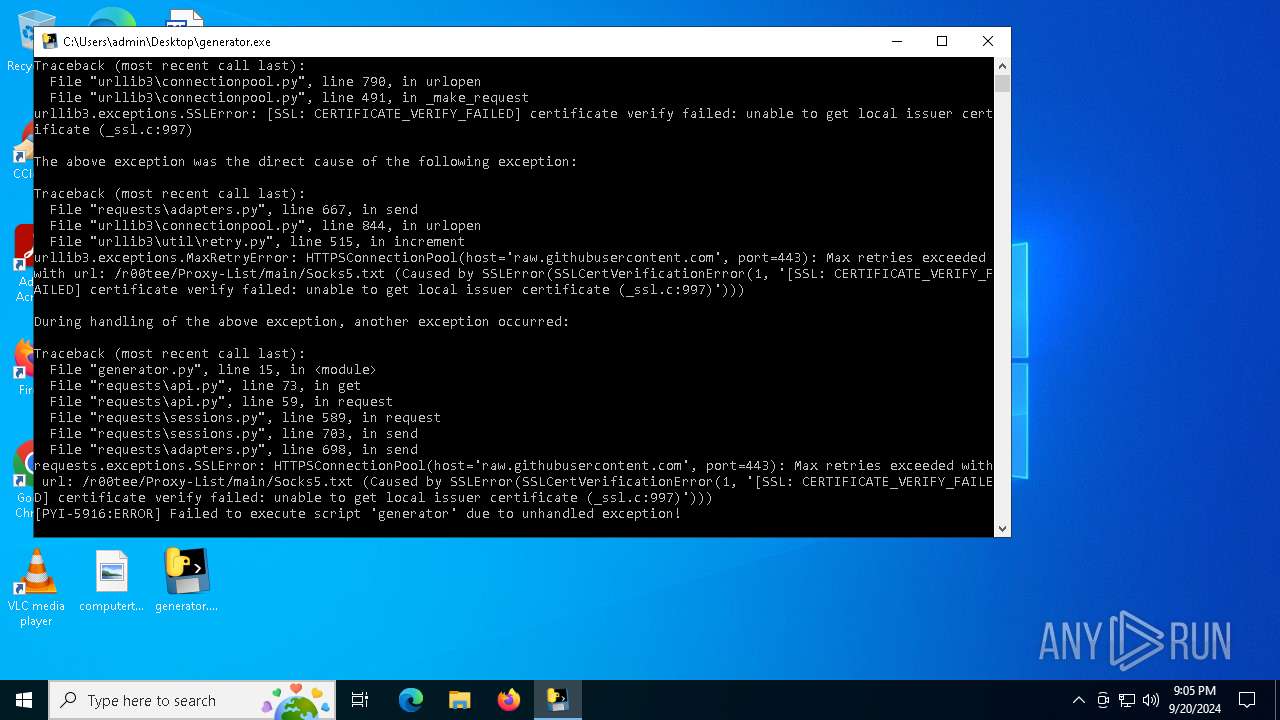
| Full analysis: | https://app.any.run/tasks/556d1154-a438-4deb-b3e9-b214cc21d244 |
| Verdict: | Malicious activity |
| Analysis date: | September 20, 2024, 21:05:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | 70392B0E7CE8038F6A1F252DA2F5E8A0 |
| SHA1: | 52DEF0CE9ACBE9933E8FE2A2F3ADACCE3E68EE68 |
| SHA256: | 223403AB429FD11730CC62C042EB14C3116033E1D6EAC49AA4F606BB0E526884 |
| SSDEEP: | 98304:wVIyDIsombg4tqaO9zzwIsRjE96eKNh6bRFs0gbJnIB+p74S5JZo//OUtHfktEzS:4Qt8XNhrhOLhhv6z |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- generator.exe (PID: 7092)
Application launched itself
- generator.exe (PID: 7092)
Process drops python dynamic module
- generator.exe (PID: 7092)
Executable content was dropped or overwritten
- generator.exe (PID: 7092)
Loads Python modules
- generator.exe (PID: 5916)
The process drops C-runtime libraries
- generator.exe (PID: 7092)
INFO
Checks supported languages
- generator.exe (PID: 7092)
- generator.exe (PID: 5916)
Reads the computer name
- generator.exe (PID: 7092)
- generator.exe (PID: 5916)
Create files in a temporary directory
- generator.exe (PID: 7092)
Reads the machine GUID from the registry
- generator.exe (PID: 5916)
Checks proxy server information
- generator.exe (PID: 5916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:09:15 17:55:31+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.4 |
| CodeSize: | 176640 |
| InitializedDataSize: | 152576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc320 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
121
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2400 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | generator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5916 | "C:\Users\admin\Desktop\generator.exe" | C:\Users\admin\Desktop\generator.exe | generator.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 7092 | "C:\Users\admin\Desktop\generator.exe" | C:\Users\admin\Desktop\generator.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
342
Read events
342
Write events
0
Delete events
0
Modification events
Executable files
64
Suspicious files
1
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7092 | generator.exe | C:\Users\admin\AppData\Local\Temp\_MEI70922\_cffi_backend.cp310-win_amd64.pyd | executable | |
MD5:2BAAA98B744915339AE6C016B17C3763 | SHA256:4F1CE205C2BE986C9D38B951B6BCB6045EB363E06DACC069A41941F80BE9068C | |||
| 7092 | generator.exe | C:\Users\admin\AppData\Local\Temp\_MEI70922\_ctypes.pyd | executable | |
MD5:CA4CEF051737B0E4E56B7D597238DF94 | SHA256:E60A2B100C4FA50B0B144CF825FE3CDE21A8B7B60B92BFC326CB39573CE96B2B | |||
| 7092 | generator.exe | C:\Users\admin\AppData\Local\Temp\_MEI70922\_decimal.pyd | executable | |
MD5:6339FA92584252C3B24E4CCE9D73EF50 | SHA256:4AE6F6FB3992BB878416211221B3D62515E994D78F72EAB51E0126CA26D0EE96 | |||
| 7092 | generator.exe | C:\Users\admin\AppData\Local\Temp\_MEI70922\VCRUNTIME140.dll | executable | |
MD5:870FEA4E961E2FBD00110D3783E529BE | SHA256:76FDB83FDE238226B5BEBAF3392EE562E2CB7CA8D3EF75983BF5F9D6C7119644 | |||
| 7092 | generator.exe | C:\Users\admin\AppData\Local\Temp\_MEI70922\_multiprocessing.pyd | executable | |
MD5:62733CE8AE95241BF9CA69F38C977923 | SHA256:AF84076B03A0EADEC2B75D01F06BB3765B35D6F0639FB7C14378736D64E1ACAA | |||
| 7092 | generator.exe | C:\Users\admin\AppData\Local\Temp\_MEI70922\_brotli.cp310-win_amd64.pyd | executable | |
MD5:EE3D454883556A68920CAAEDEFBC1F83 | SHA256:791E7195D7DF47A21466868F3D7386CFF13F16C51FCD0350BF4028E96278DFF1 | |||
| 7092 | generator.exe | C:\Users\admin\AppData\Local\Temp\_MEI70922\_lzma.pyd | executable | |
MD5:0A94C9F3D7728CF96326DB3AB3646D40 | SHA256:0A70E8546FA6038029F2A3764E721CEEBEA415818E5F0DF6B90D6A40788C3B31 | |||
| 7092 | generator.exe | C:\Users\admin\AppData\Local\Temp\_MEI70922\_ssl.pyd | executable | |
MD5:9DDB64354EF0B91C6999A4B244A0A011 | SHA256:E33B7A4AA5CDD5462EE66830636FDD38048575A43D06EB7E2F688358525DDEAB | |||
| 7092 | generator.exe | C:\Users\admin\AppData\Local\Temp\_MEI70922\_bz2.pyd | executable | |
MD5:BBE89CF70B64F38C67B7BF23C0EA8A48 | SHA256:775FBC6E9A4C7E9710205157350F3D6141B5A9E8F44CB07B3EAC38F2789C8723 | |||
| 7092 | generator.exe | C:\Users\admin\AppData\Local\Temp\_MEI70922\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:CFE0C1DFDE224EA5FED9BD5FF778A6E0 | SHA256:0D0F80CBF476AF5B1C9FD3775E086ED0DFDB510CD0CC208EC1CCB04572396E3E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
18
DNS requests
6
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4040 | RUXIMICS.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2456 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4040 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5916 | generator.exe | 185.199.108.133:443 | raw.githubusercontent.com | FASTLY | US | shared |
4040 | RUXIMICS.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2456 | svchost.exe | 52.185.211.133:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |