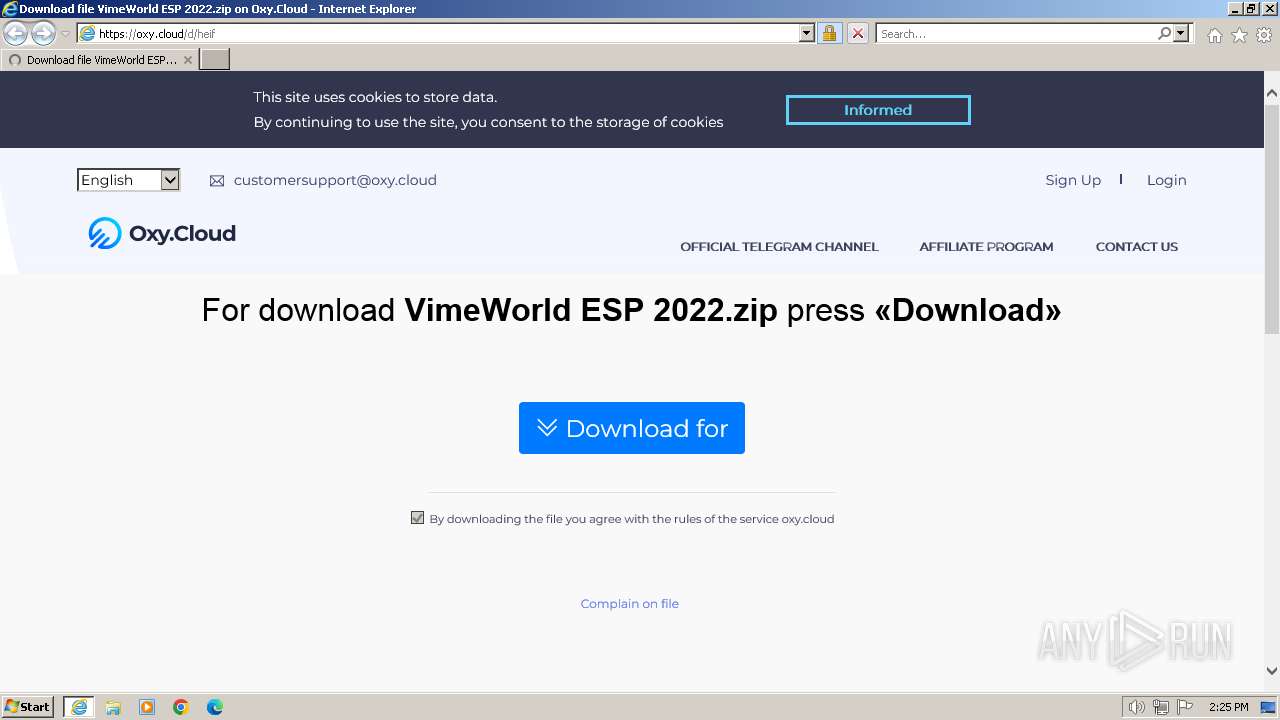
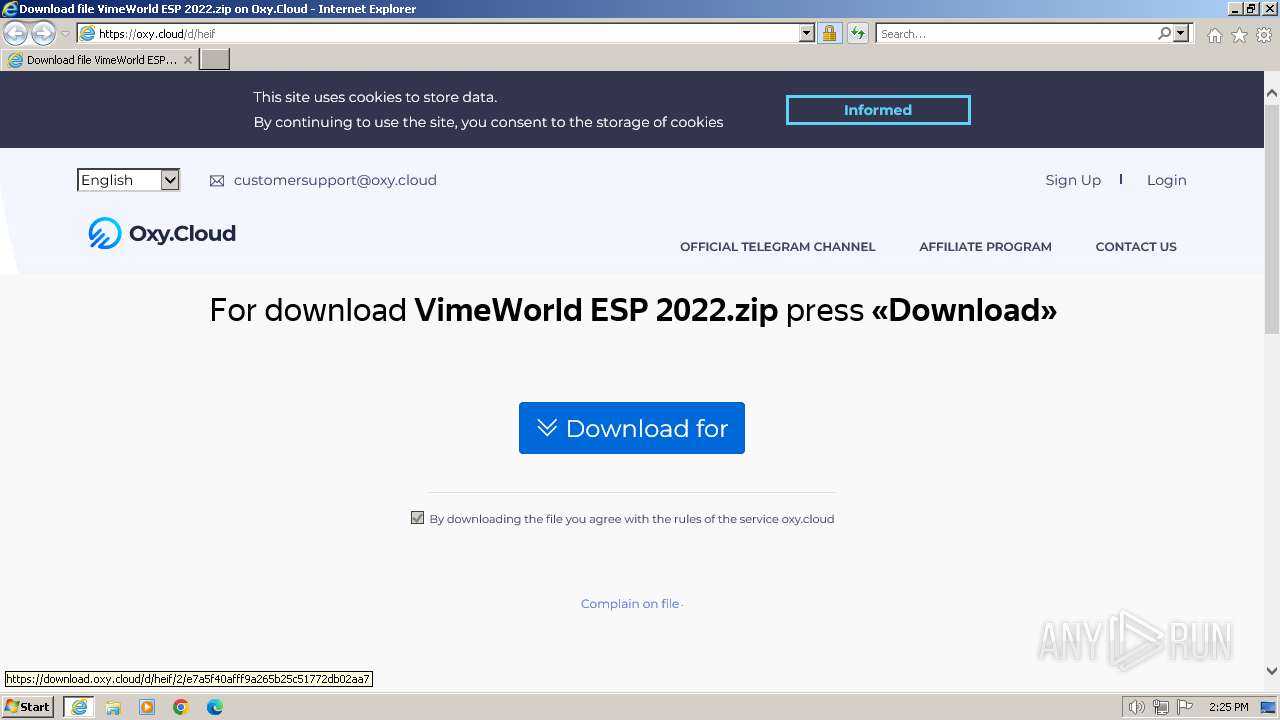
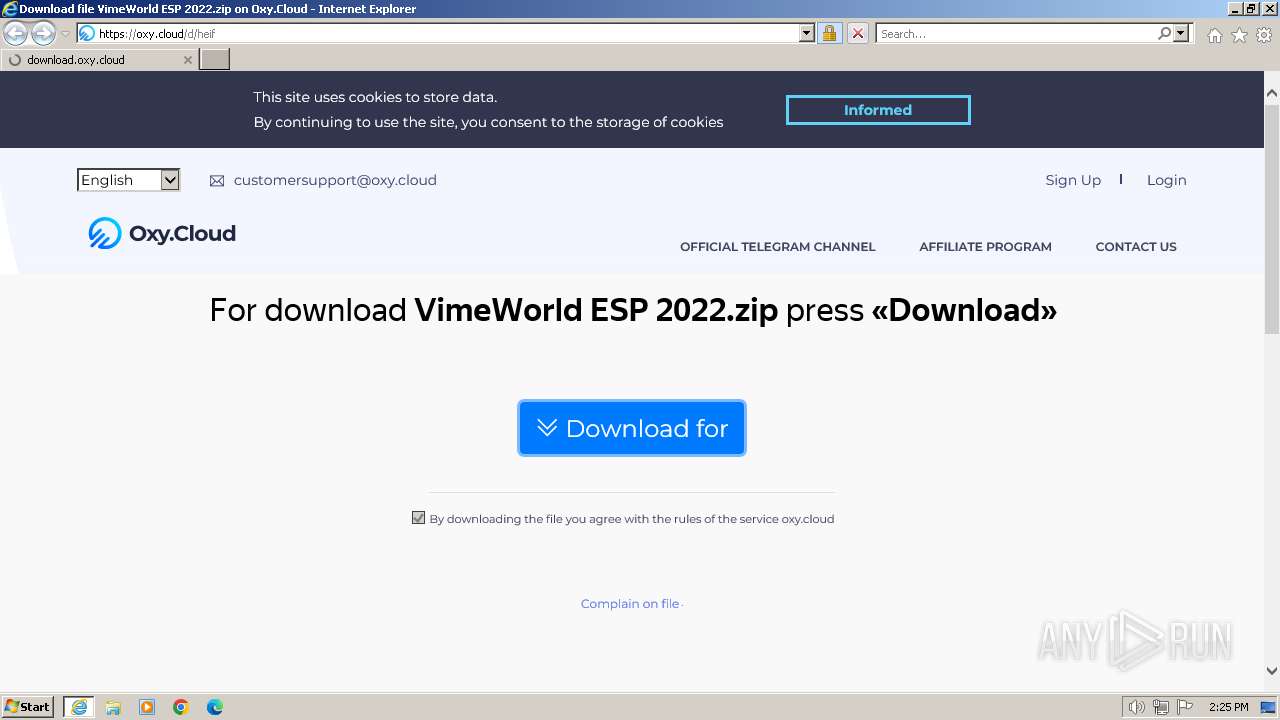
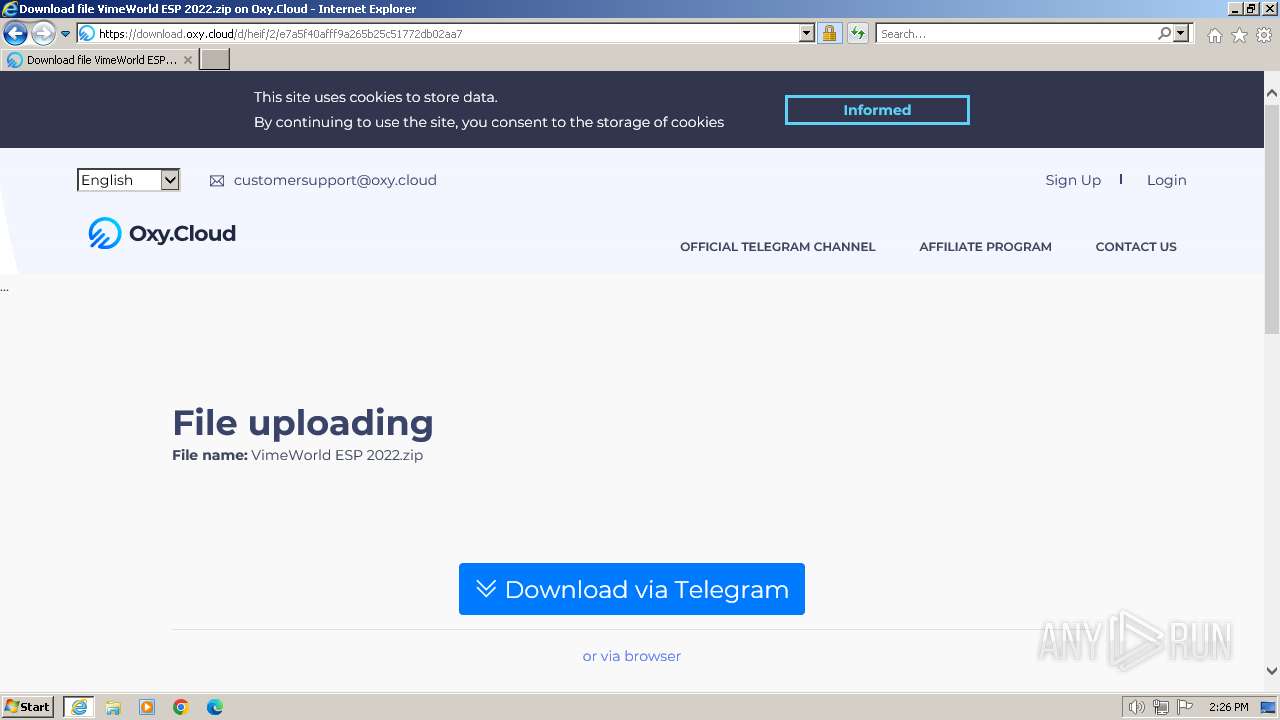
| URL: | https://oxy.cloud/d/heif |
| Full analysis: | https://app.any.run/tasks/021f4bc9-3f7b-4459-9920-3ac01c133329 |
| Verdict: | Malicious activity |
| Analysis date: | March 09, 2024, 14:25:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A6BE87C2BBE4DF04B59442E7357DC191 |
| SHA1: | D48CB865FEE9C34EE1FE2398914695BABC4FDE87 |
| SHA256: | 223332993672851BF49776AE15A6B78BF7E426CF6277C8F749CDE792053950F7 |
| SSDEEP: | 3:N8UOQaMDn:2UOFCn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
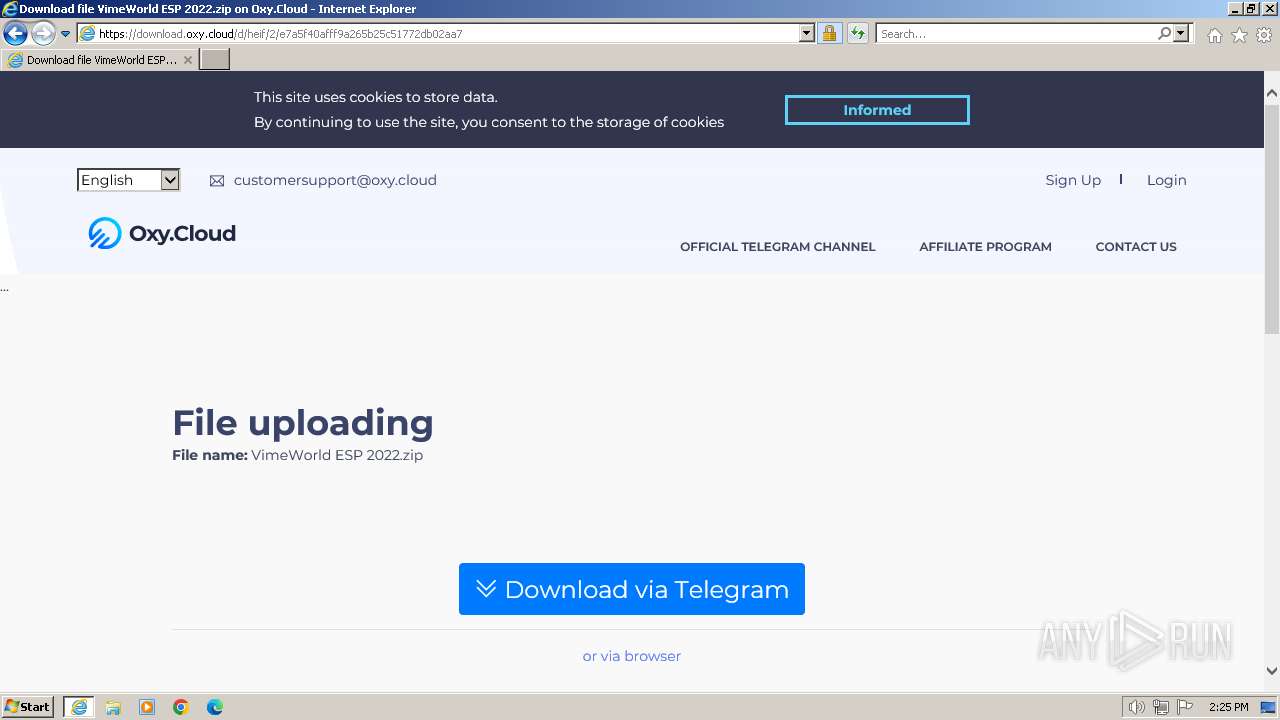
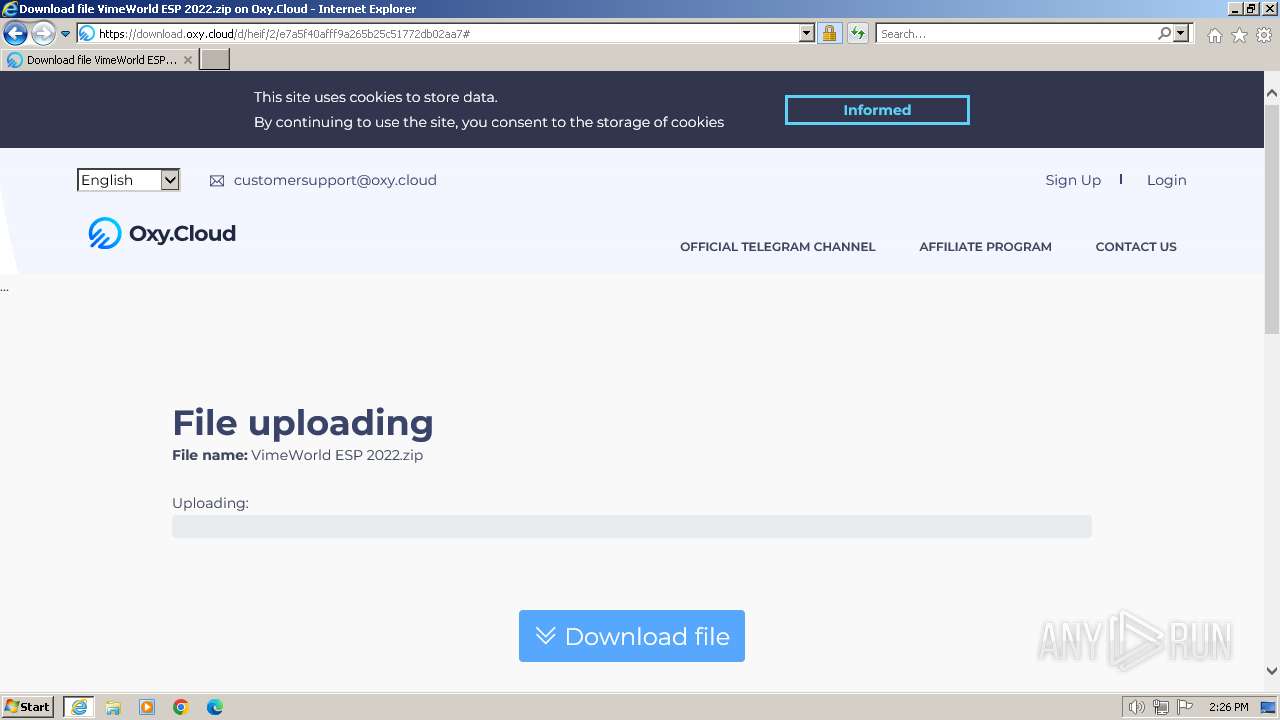
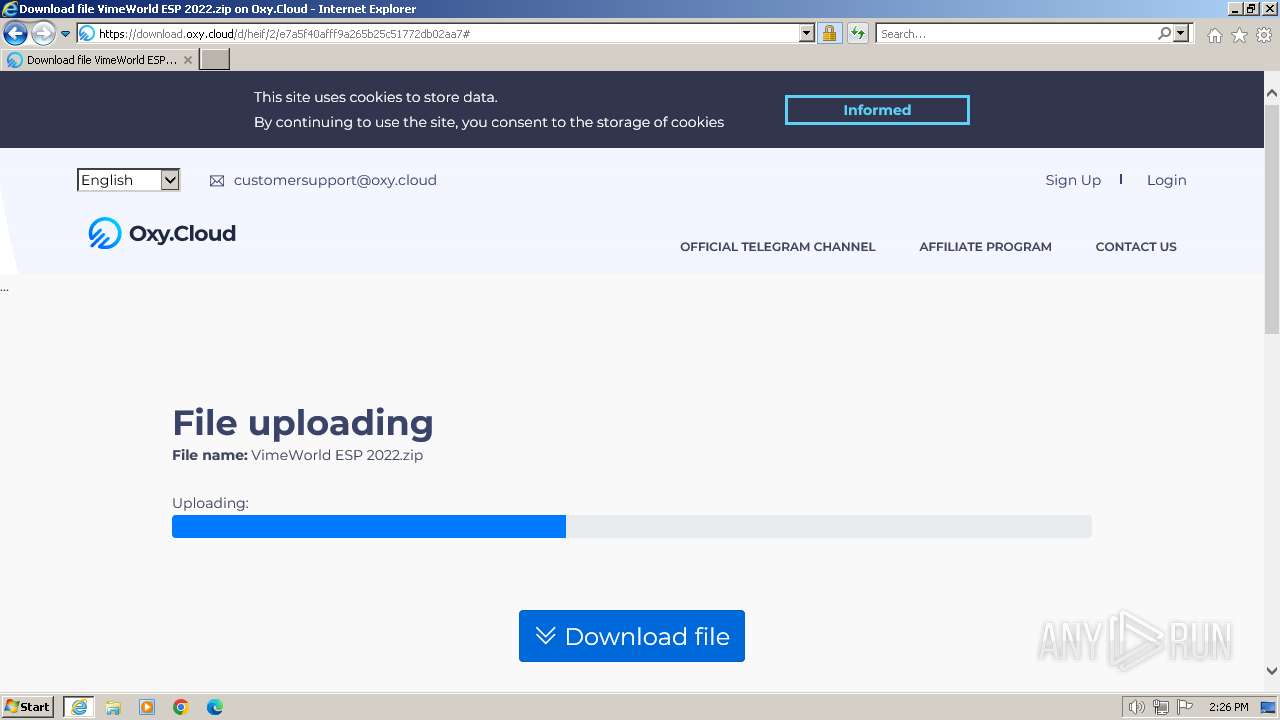
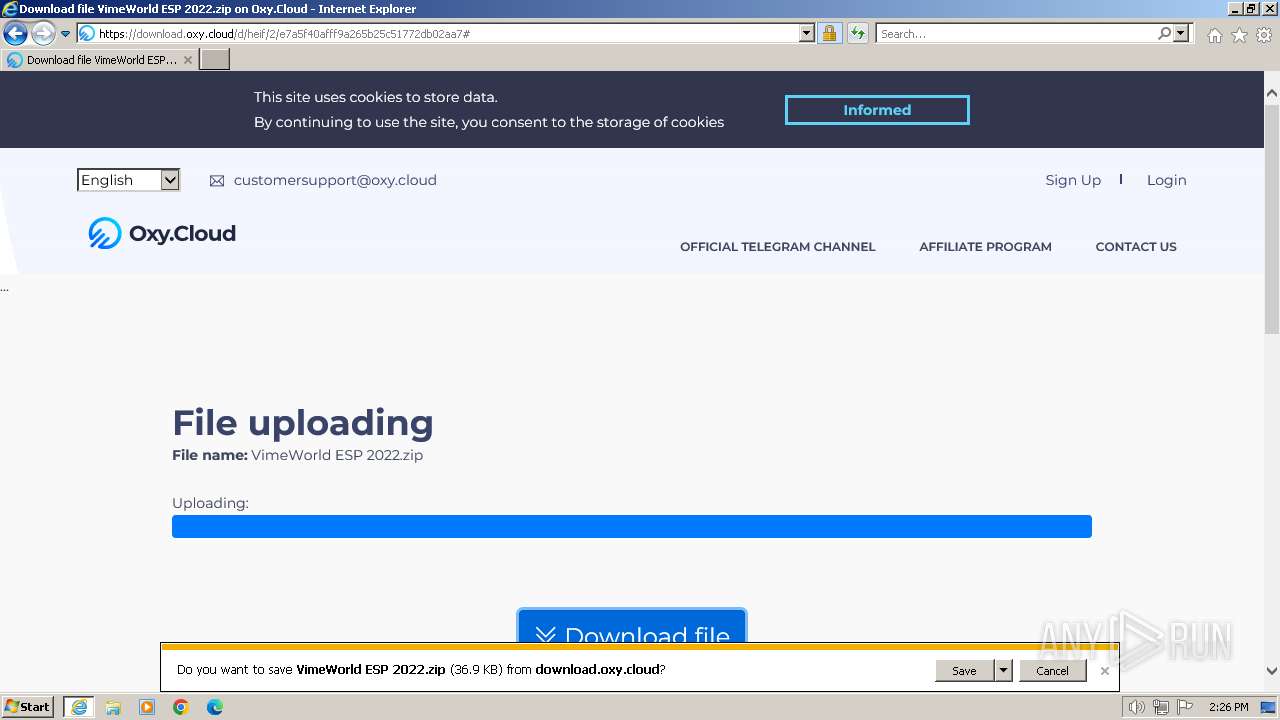
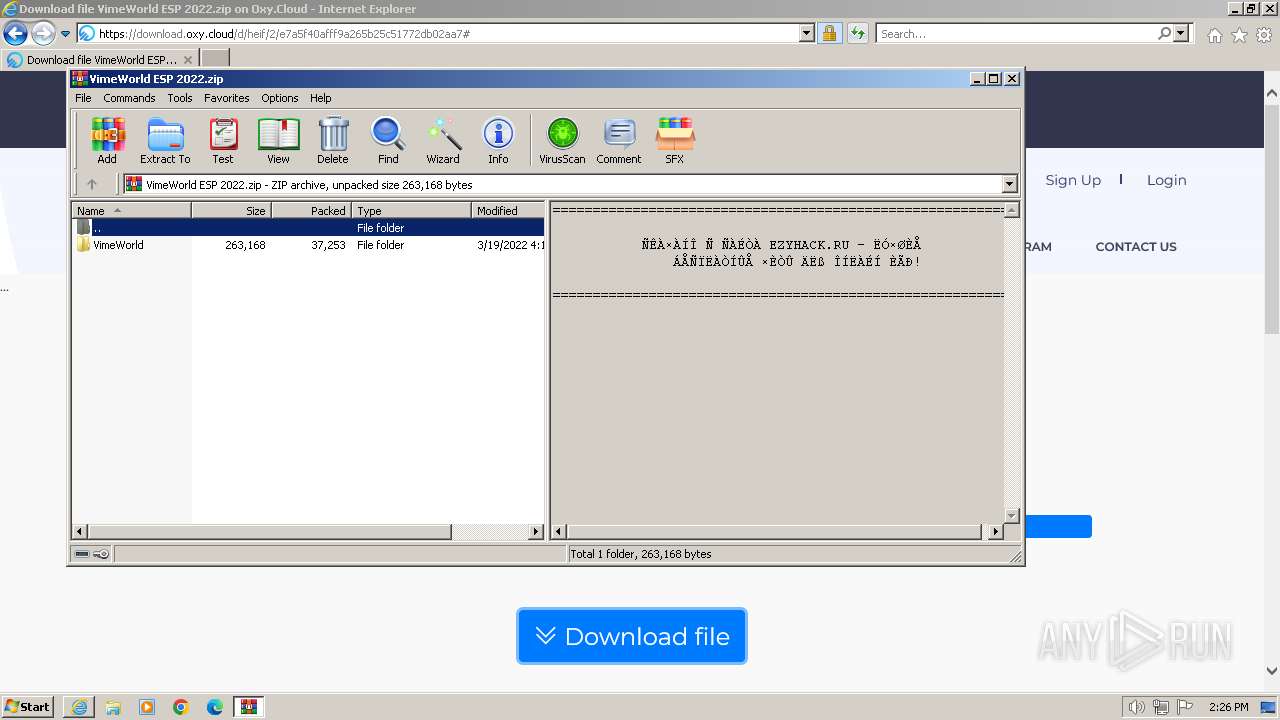
The process uses the downloaded file
- iexplore.exe (PID: 3700)
- WinRAR.exe (PID: 2072)
Application launched itself
- iexplore.exe (PID: 3700)
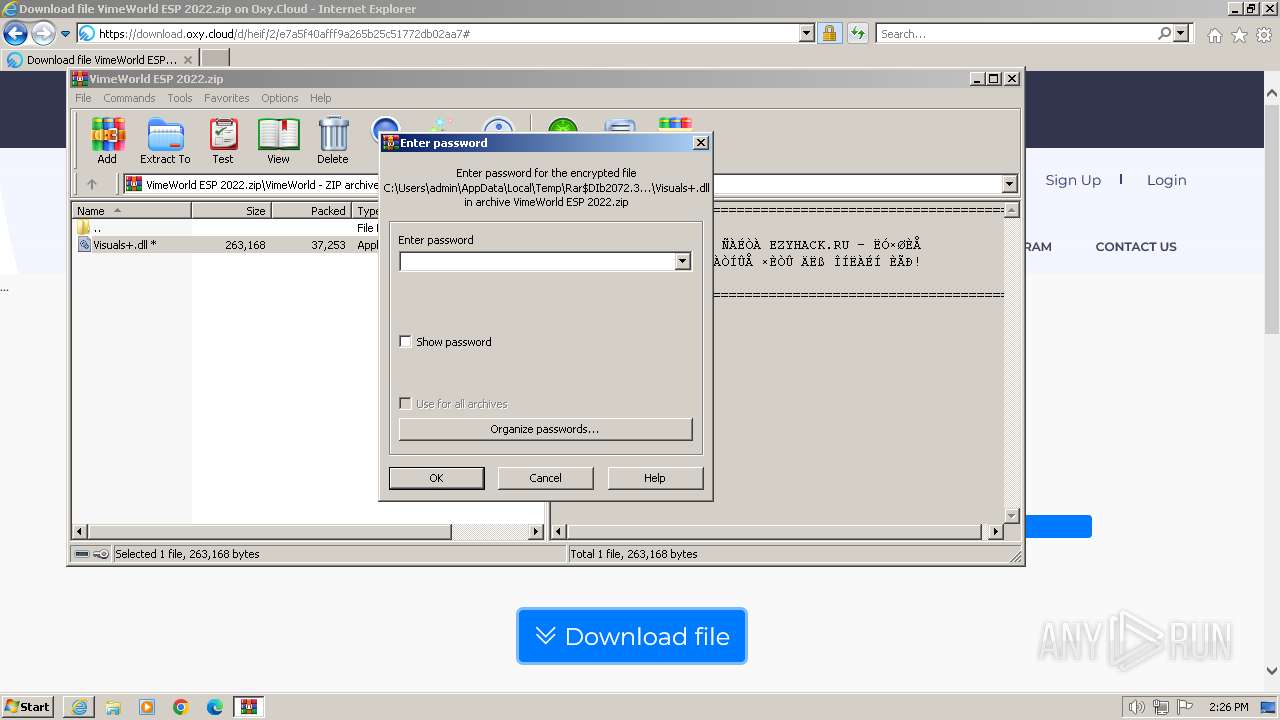
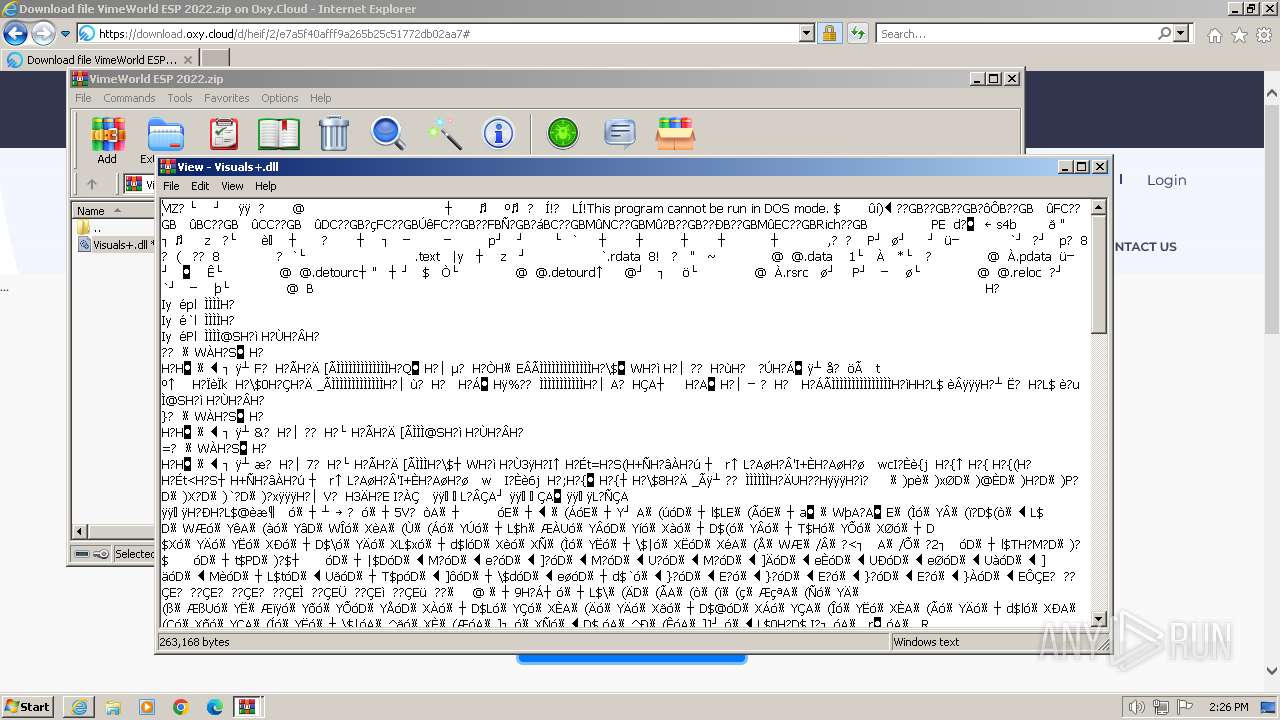
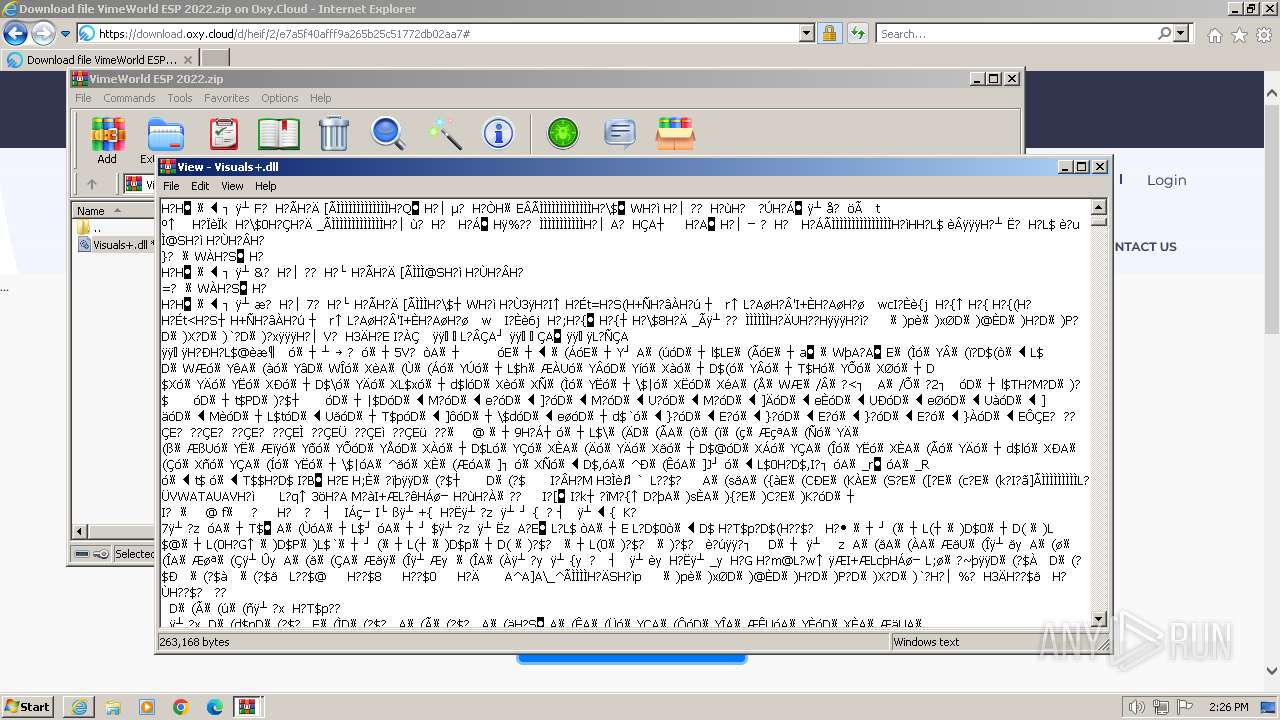
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2072)
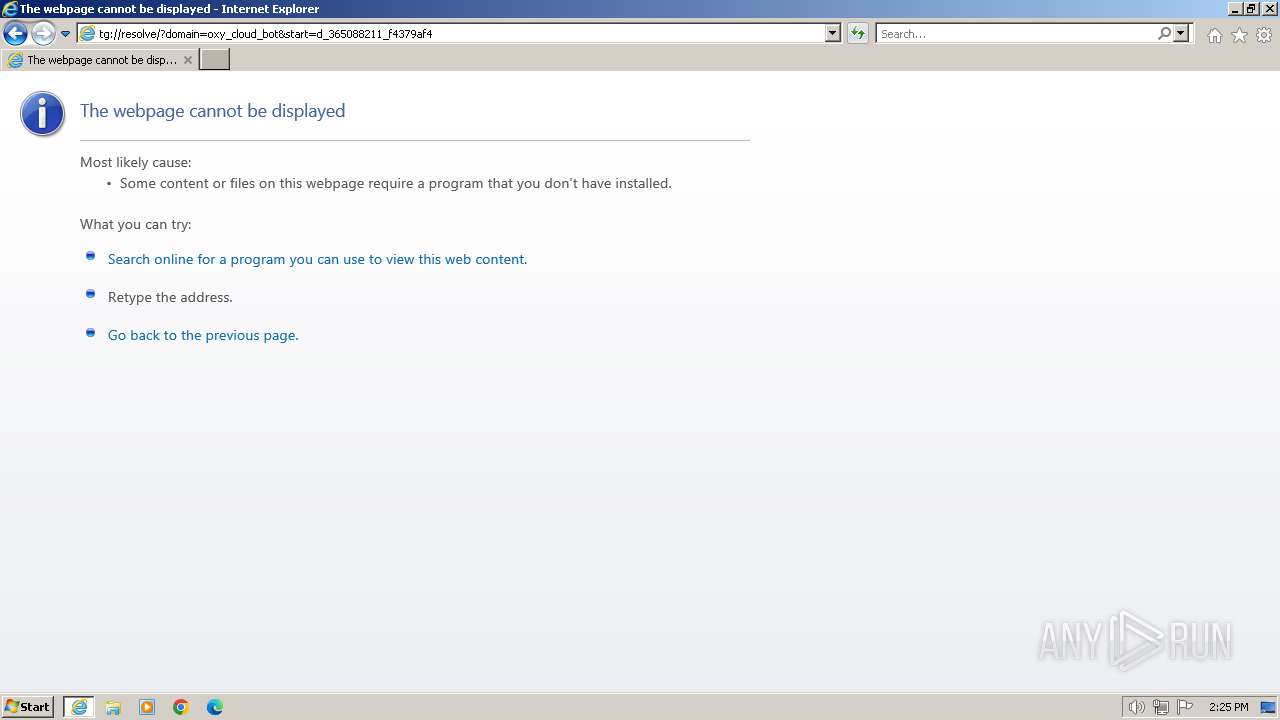
Modifies the phishing filter of IE
- iexplore.exe (PID: 3700)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
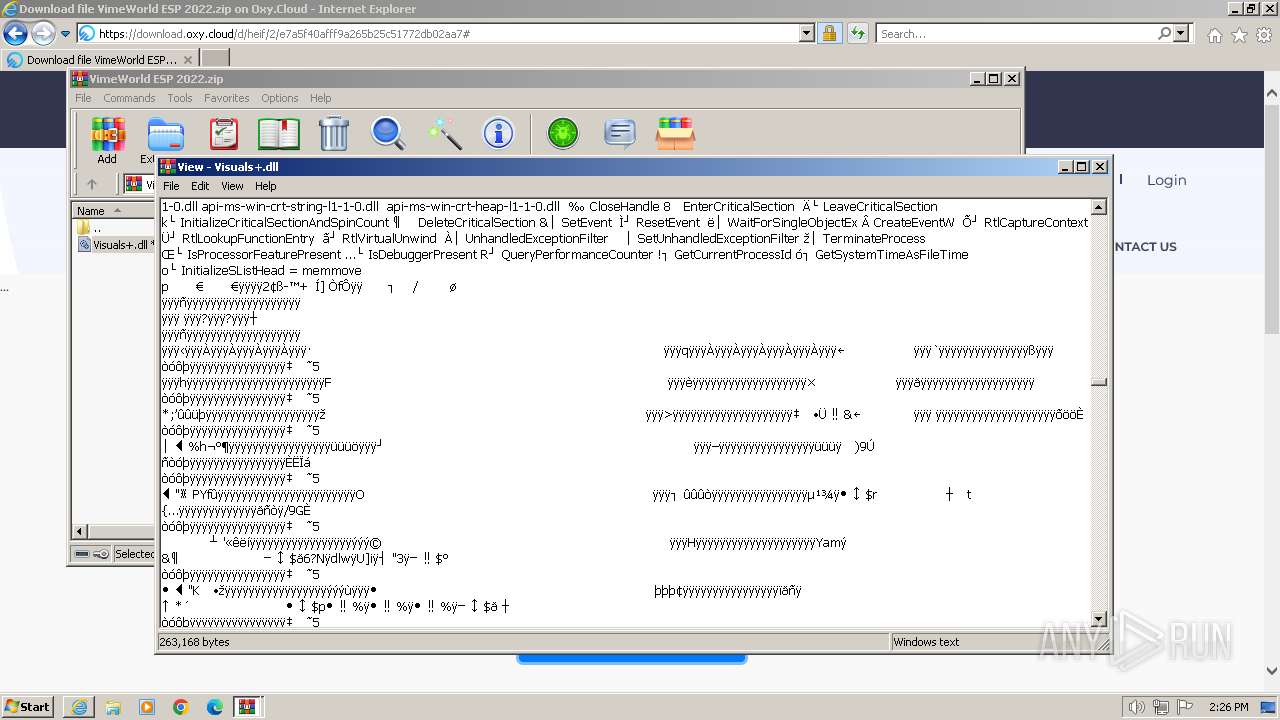
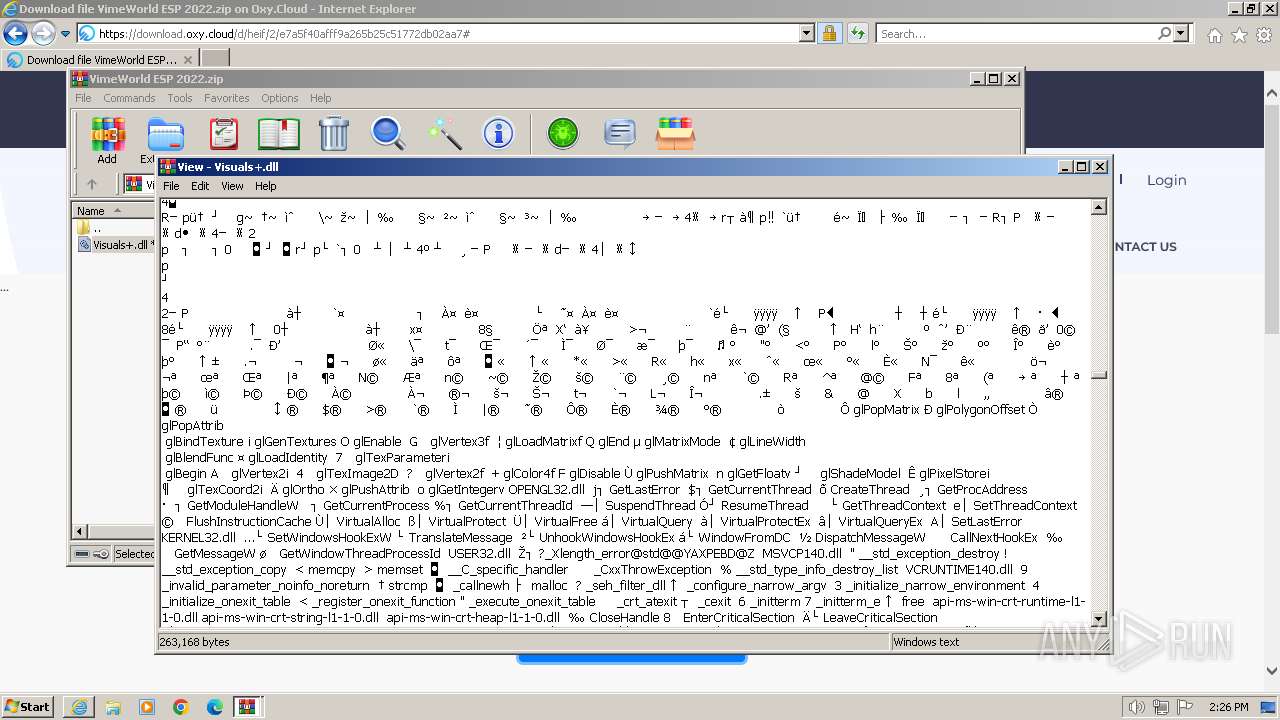
| 2072 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\VimeWorld ESP 2022.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
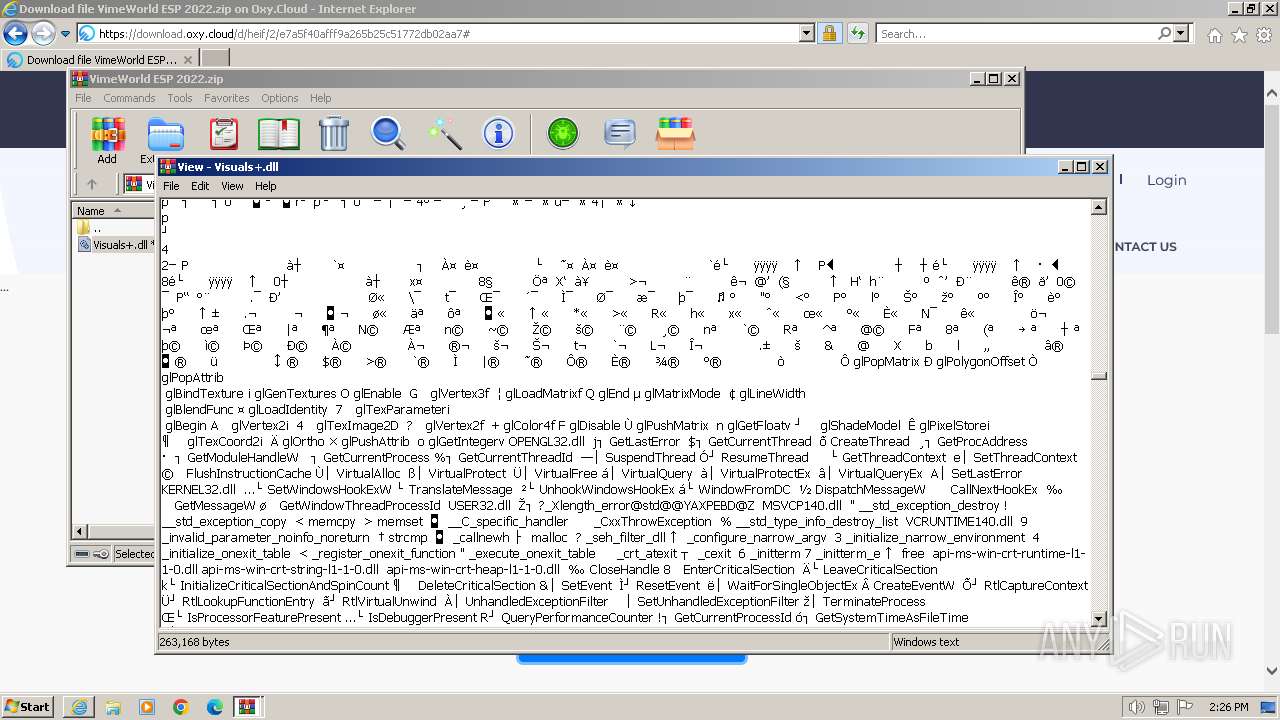
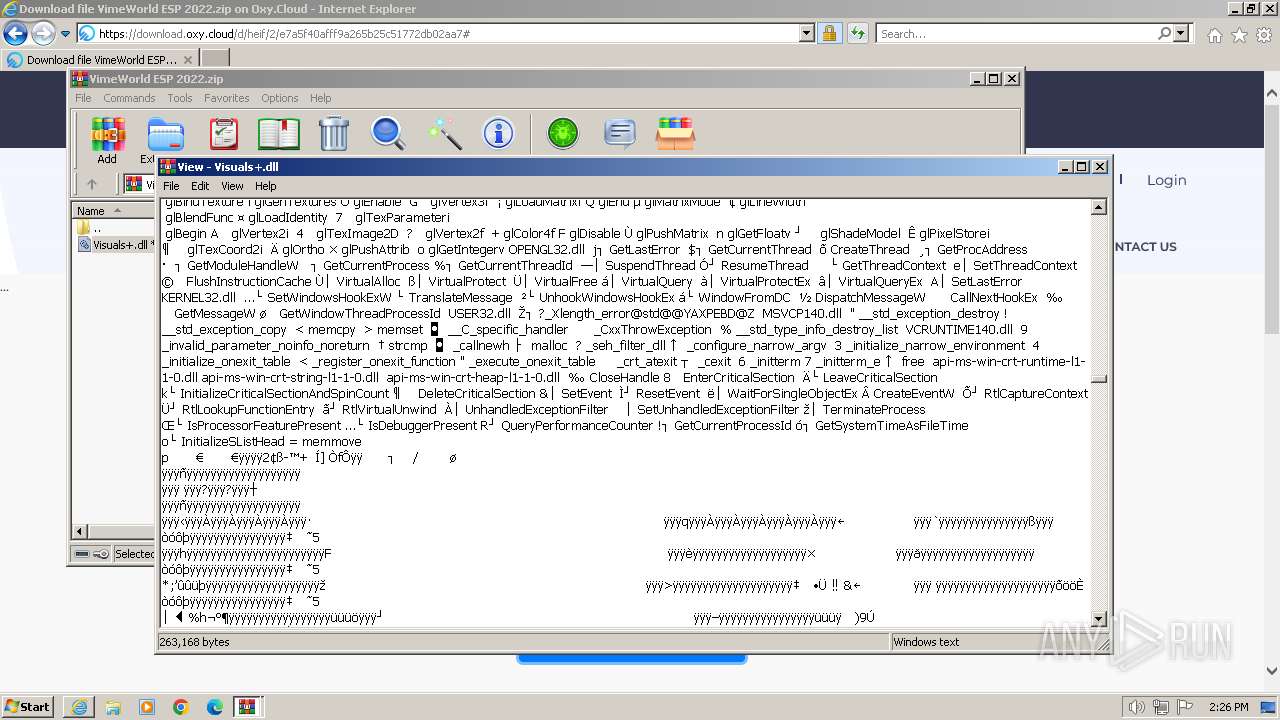
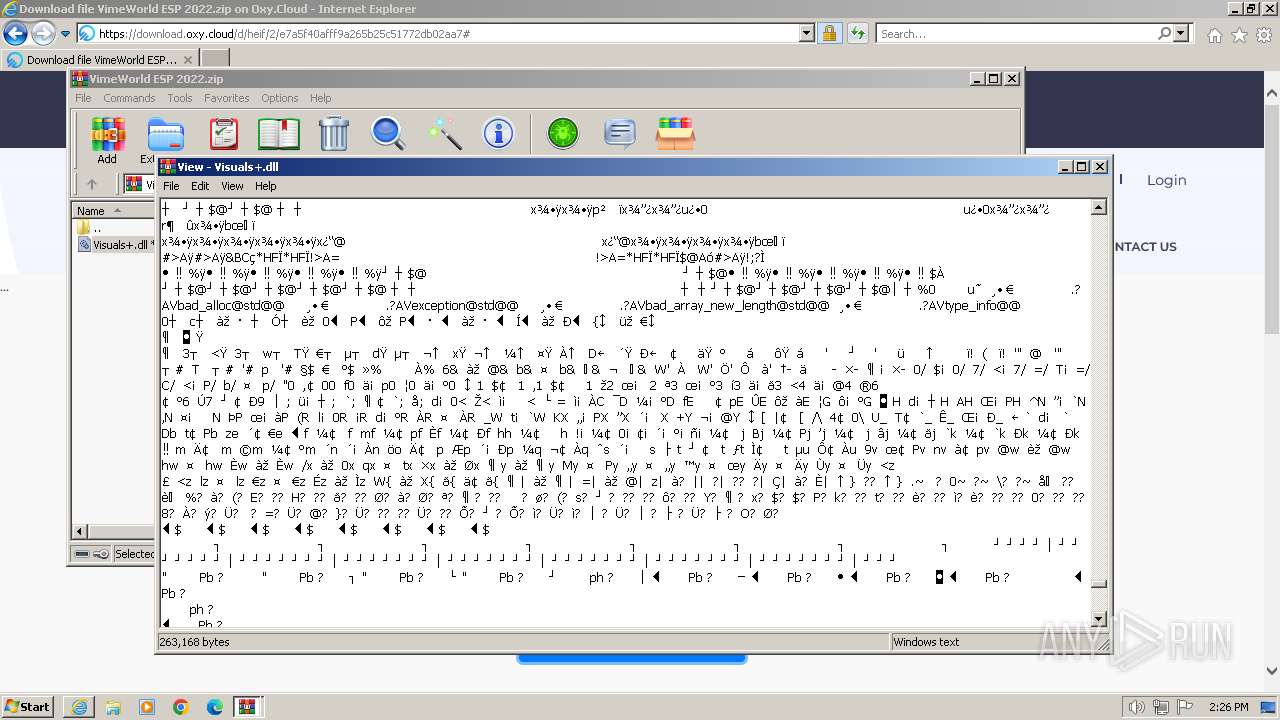
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2920 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3700 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3700 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://oxy.cloud/d/heif" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
28 635
Read events
28 461
Write events
124
Delete events
50
Modification events
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31093293 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31093293 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
54
Text files
72
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2920 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\7JONOM7H.txt | text | |
MD5:4C473A48FBDB19F5F72EFAA2CB856D30 | SHA256:56152750DE971929A823707307D5544F9A464B8F2A26C933E6DFD8DF701FD993 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\heif[1].htm | html | |
MD5:F1C61FC8BAB3473AF1FA7121BAF66F45 | SHA256:E5462FBE6487357D09655CDBCF466052BEF301F823E424DBDA0350846B017152 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CF4997C12995A87D9031622D2C7ADDCA | binary | |
MD5:3445954B12CEFD9F83CED6CB88EED944 | SHA256:26D2ECB4E1ABB3D7B9C4A721391E7D3FB5E177A6A33CB2F8A21D0F701B3E9CAE | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:C4CF6F6F3FC9287B5BB2611170926138 | SHA256:2B53661C4793AA9D83F45333FF5EA2FEA00F5F25314EEF6DA5B3F567C4AED3D8 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\style[1].css | text | |
MD5:43BBB018DBFB3C985D19043D1C7006FB | SHA256:8B40AF05F3B3D6374C0964E7561EA6A74F80230FFAD28B281D8D0772696EB344 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:C1F350B6D2F9DB175AD87E8393EC58FE | SHA256:A2E7CF2DDAC112499276D62261822688488B62B914AAF9AD063C09A21A0A2984 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\cloud[1].css | text | |
MD5:526B65035FF31BD7147BE9E785A768AC | SHA256:8996A1606A4793B1A05580FF47567F4467C2D16BBE7CBCB049DC849E0105DA86 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\0DA515F703BB9B49479E8697ADB0B955_96EEC010953ED454BBCDFA69FC071E7C | der | |
MD5:519A6130C2C00060032D67735FD73EAD | SHA256:07FDD4EDD67140FE918A1AA8717AA002B7BAFD145052FF17E1EB6B7BB4D5FC3C | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CF4997C12995A87D9031622D2C7ADDCA | binary | |
MD5:FBA9C325BA9C4D4545570F20A570F0D0 | SHA256:0371DF156AEF1E7662DA8C165CF20BB1A4C49FAFC50A0C565B3FA087A59F866F | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:11461C173C6F16C7D21C7A5D19A58A09 | SHA256:3EB73D60055DD42D663194BE58BC09F92686599AB34CCA9E9083B1146777BE80 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
67
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2920 | iexplore.exe | GET | 304 | 23.53.41.249:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c9f2b763ba05a2db | unknown | — | — | unknown |
2920 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
2920 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/alphasslcasha256g4/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBSPdwLcDiHQXlVfp8h37hrpMerTggQUT8usqMLvq92Db2u%2Fzpg9XFgldhUCDHMpyMx9IikDqs0mIw%3D%3D | unknown | binary | 1.40 Kb | unknown |
2920 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEH6FWuT3fbHwEAPEHSB2q%2B0%3D | unknown | binary | 471 b | unknown |
2920 | iexplore.exe | GET | 304 | 23.53.42.59:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?14266dff8470122f | unknown | — | — | unknown |
2920 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
3700 | iexplore.exe | GET | 304 | 23.53.42.59:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4dd617501e33218a | unknown | — | — | unknown |
— | — | GET | 200 | 23.32.238.82:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgQFr%2FgSJuIBXtSHpo%2BwkA%2BxEg%3D%3D | unknown | binary | 503 b | unknown |
2920 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEmjnEcAcBIRCdkf7NhadAI%3D | unknown | binary | 471 b | unknown |
2920 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2920 | iexplore.exe | 185.178.208.145:443 | oxy.cloud | Ddos-guard Ltd | RU | unknown |
2920 | iexplore.exe | 23.53.42.59:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2920 | iexplore.exe | 23.53.41.249:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2920 | iexplore.exe | 23.39.157.155:80 | x1.c.lencr.org | AKAMAI-AS | US | unknown |
2920 | iexplore.exe | 23.32.238.82:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
2920 | iexplore.exe | 142.250.186.138:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
oxy.cloud |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
contextual.media.net |
| shared |
fonts.googleapis.com |
| whitelisted |
ads.themoneytizer.com |
| whitelisted |
smatr.net |
| unknown |
cdn.adlook.me |
| unknown |
ocsp.pki.goog |
| whitelisted |