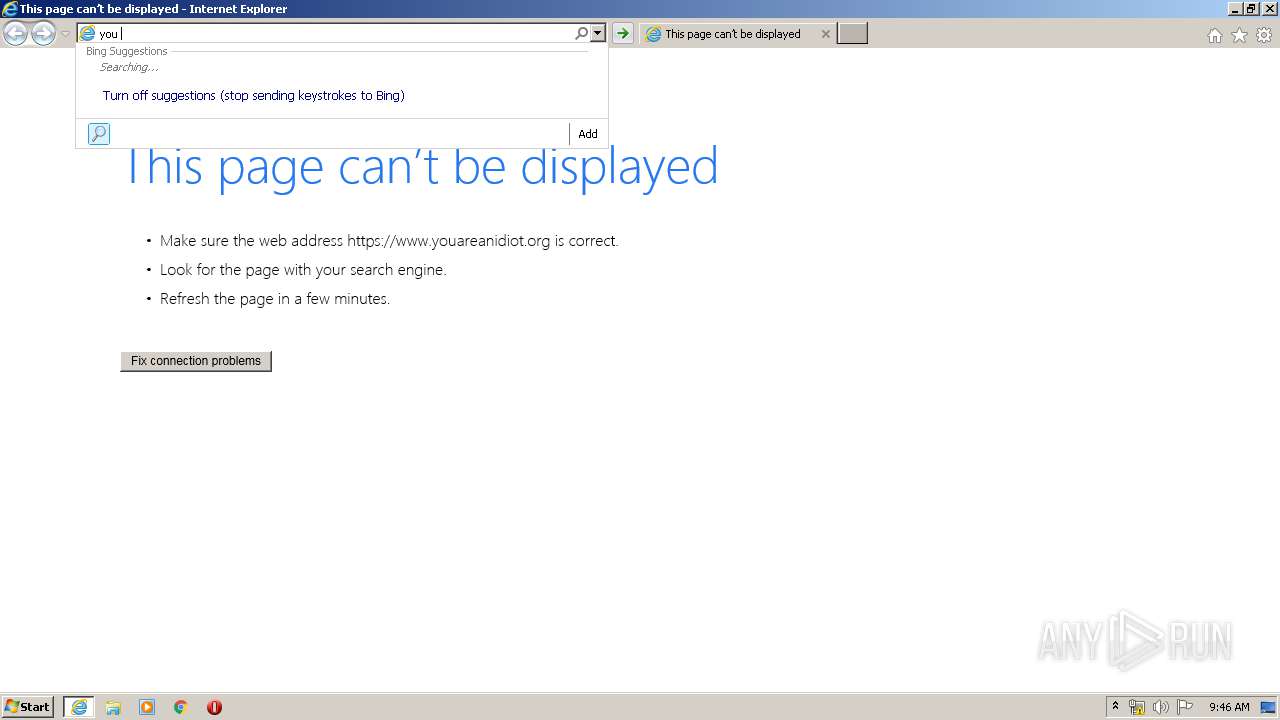
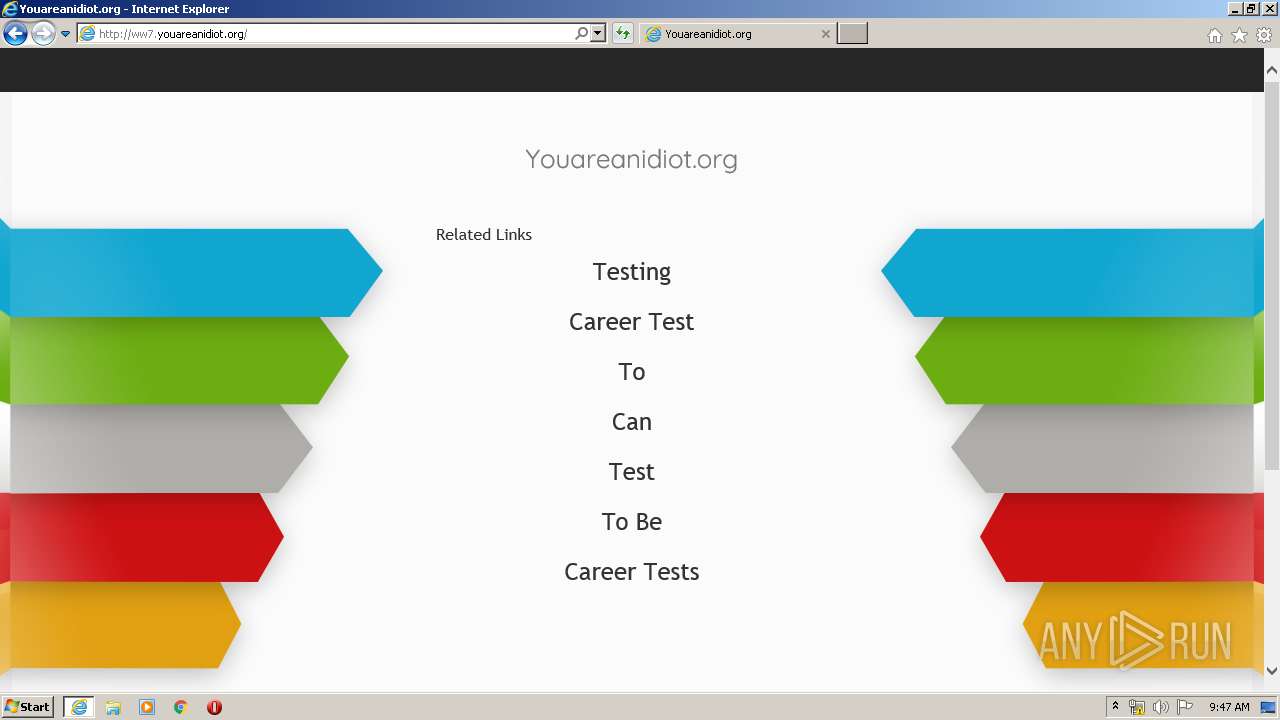
| URL: | https://www.youareanidiot.org |
| Full analysis: | https://app.any.run/tasks/c8ad76b7-9c5c-4228-b3c8-ca75f9da702f |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2020, 08:46:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C0CE6530304F008A5C55E86D22BE8359 |
| SHA1: | C00DC43A6E08CC240A79B26DC60C2594AF2E6696 |
| SHA256: | 2225DC8C99C126ED9DFA6E5CA4B08F1E86B96F9767972E1C15E92C598E0828EC |
| SSDEEP: | 3:N8DSLU+dpQKS:2OLUv |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3552)
- iexplore.exe (PID: 2492)
Application launched itself
- iexplore.exe (PID: 3552)
Changes internet zones settings
- iexplore.exe (PID: 3552)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2492)
Reads internet explorer settings
- iexplore.exe (PID: 2492)
Creates files in the user directory
- iexplore.exe (PID: 3552)
- iexplore.exe (PID: 2492)
Reads settings of System Certificates
- iexplore.exe (PID: 2492)
- iexplore.exe (PID: 3552)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3552)
Changes settings of System certificates
- iexplore.exe (PID: 3552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2492 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3552 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3552 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.youareanidiot.org" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
7 915
Read events
1 146
Write events
4 521
Delete events
2 248
Modification events
| (PID) Process: | (2492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3262757580 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30808395 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
0
Suspicious files
38
Text files
108
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3552 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2492 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\3PLWVN89.txt | — | |
MD5:— | SHA256:— | |||
| 2492 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\R04YRGR8.txt | — | |
MD5:— | SHA256:— | |||
| 2492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[1].htm | — | |
MD5:— | SHA256:— | |||
| 2492 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\C5MD1VIC.txt | — | |
MD5:— | SHA256:— | |||
| 2492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\-nK5HAtc03YD_-fIE4Q-t8DnnZY[1].js | — | |
MD5:— | SHA256:— | |||
| 2492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\errorPageStrings[1] | text | |
MD5:— | SHA256:— | |||
| 2492 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\JACMPQQT.txt | text | |
MD5:— | SHA256:— | |||
| 2492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 2492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\CsAE8FzFtr1QQehpi1WOCi9zJu0[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
198
TCP/UDP connections
88
DNS requests
29
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
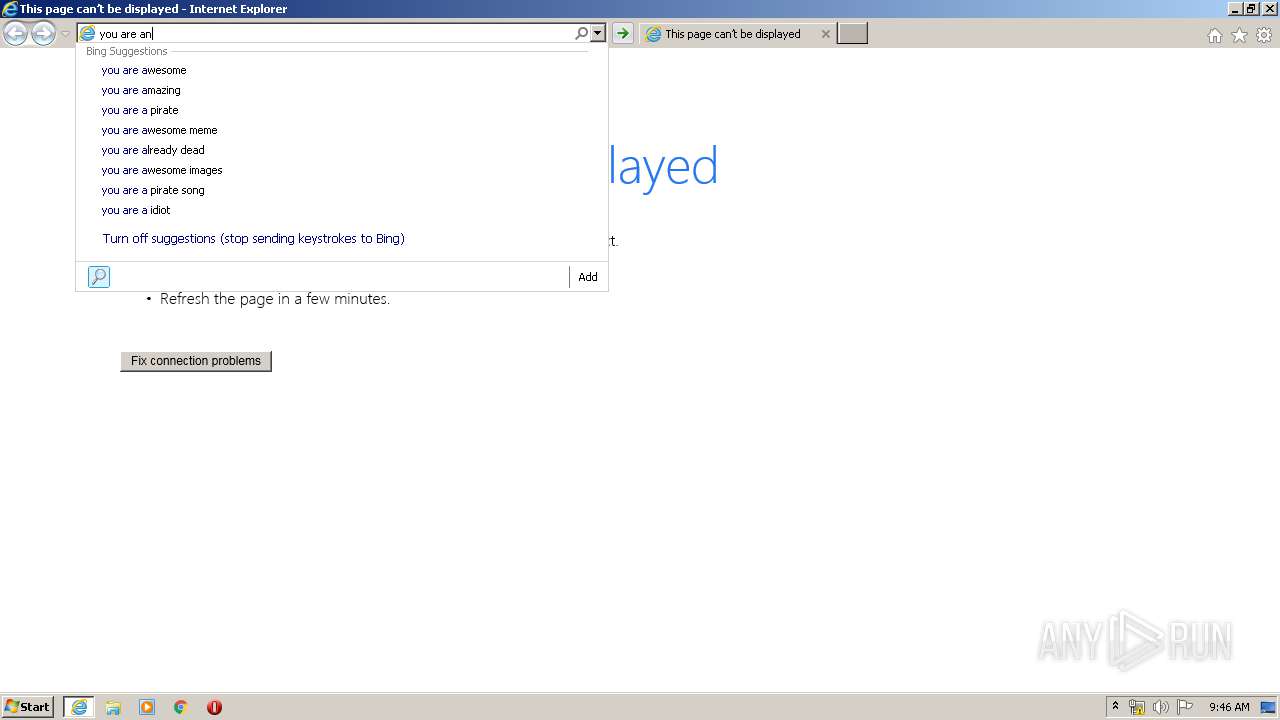
2492 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=y&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
2492 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=you+are+an&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
2492 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=you+are+an+i&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
2492 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=you&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
2492 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=you+are+a&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 237 b | whitelisted |
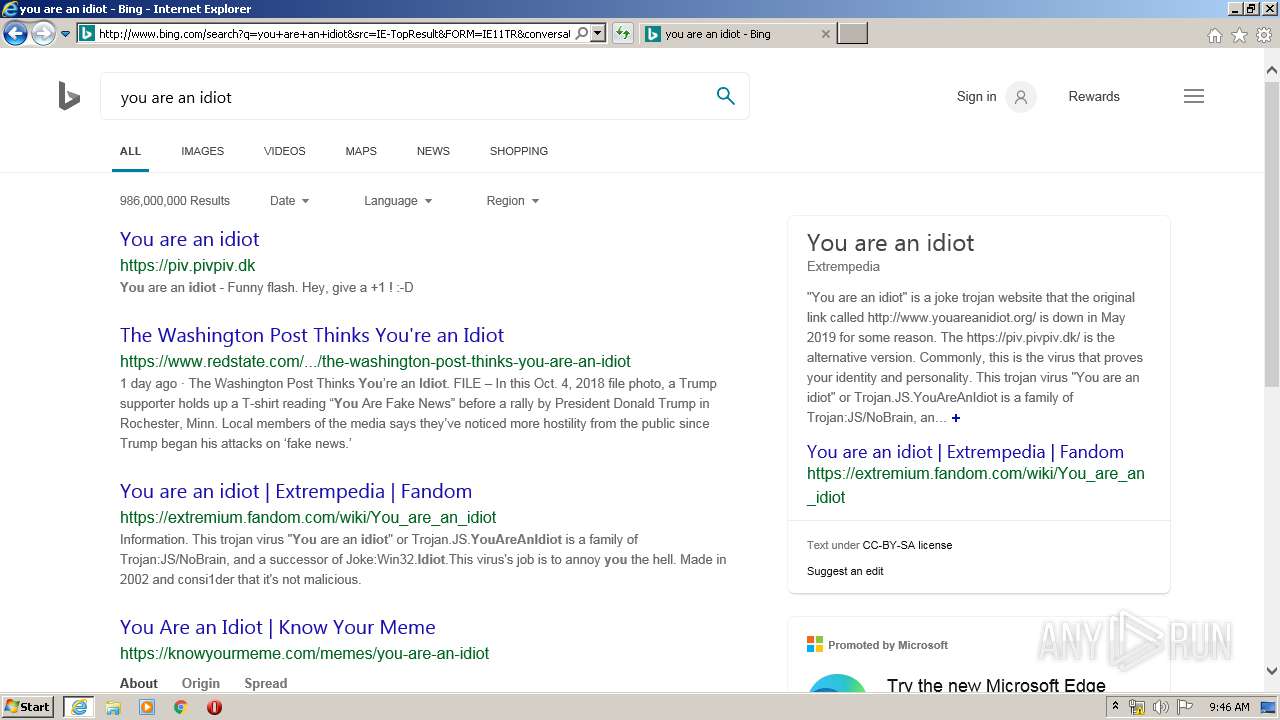
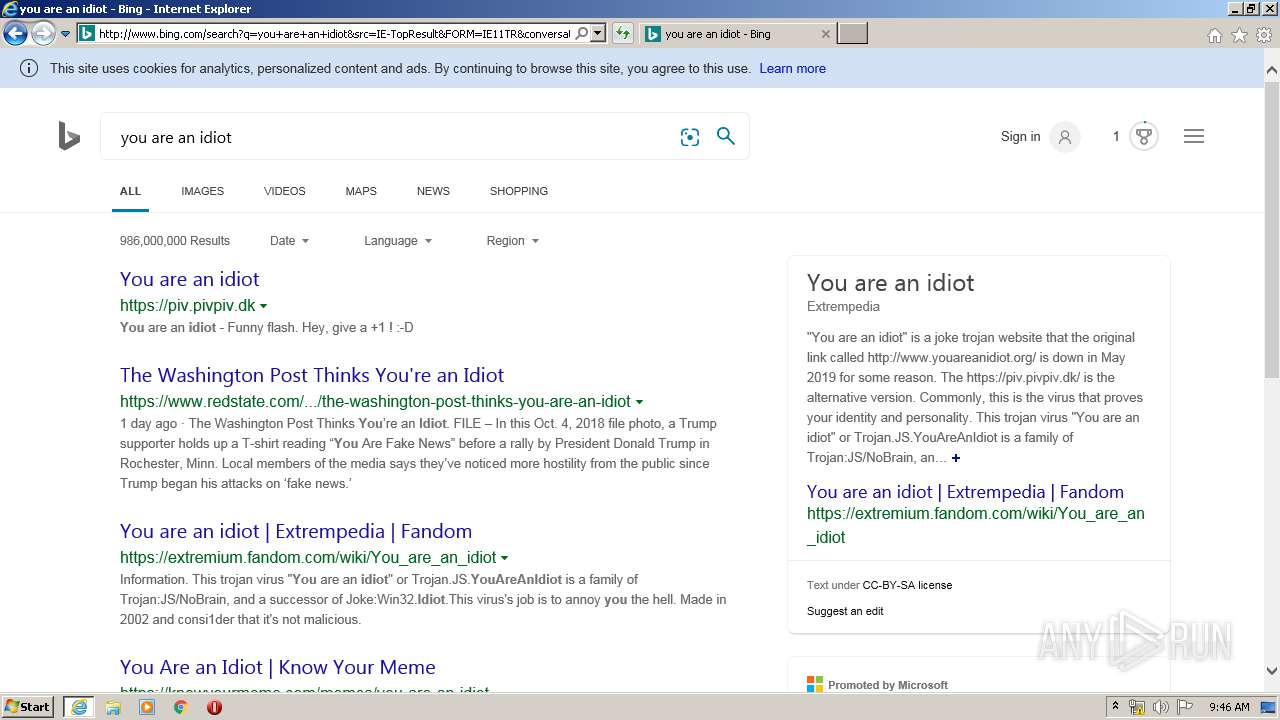
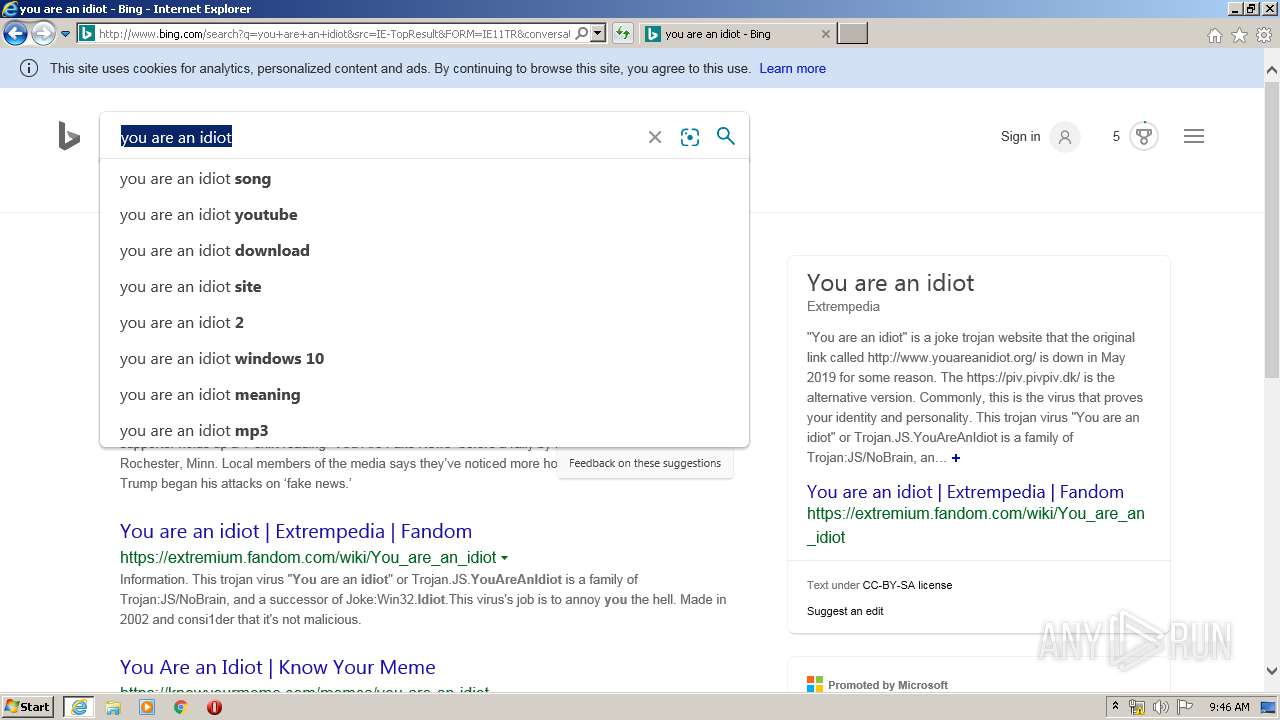
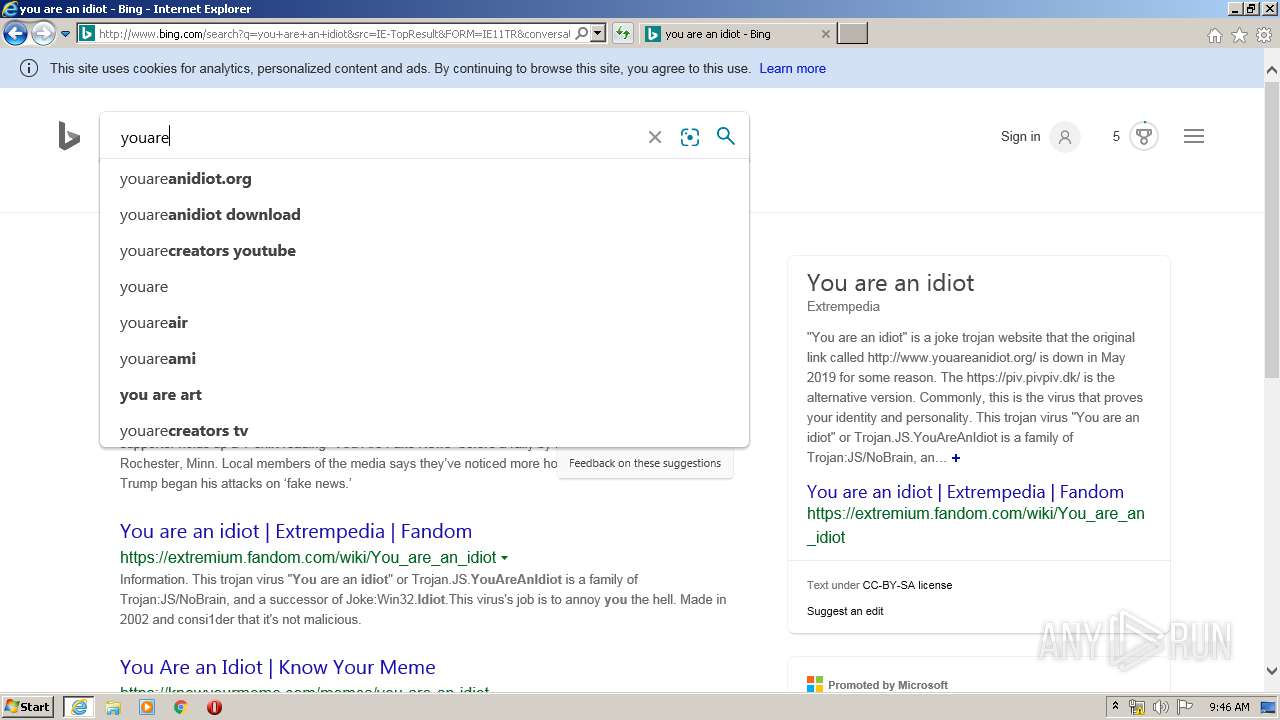
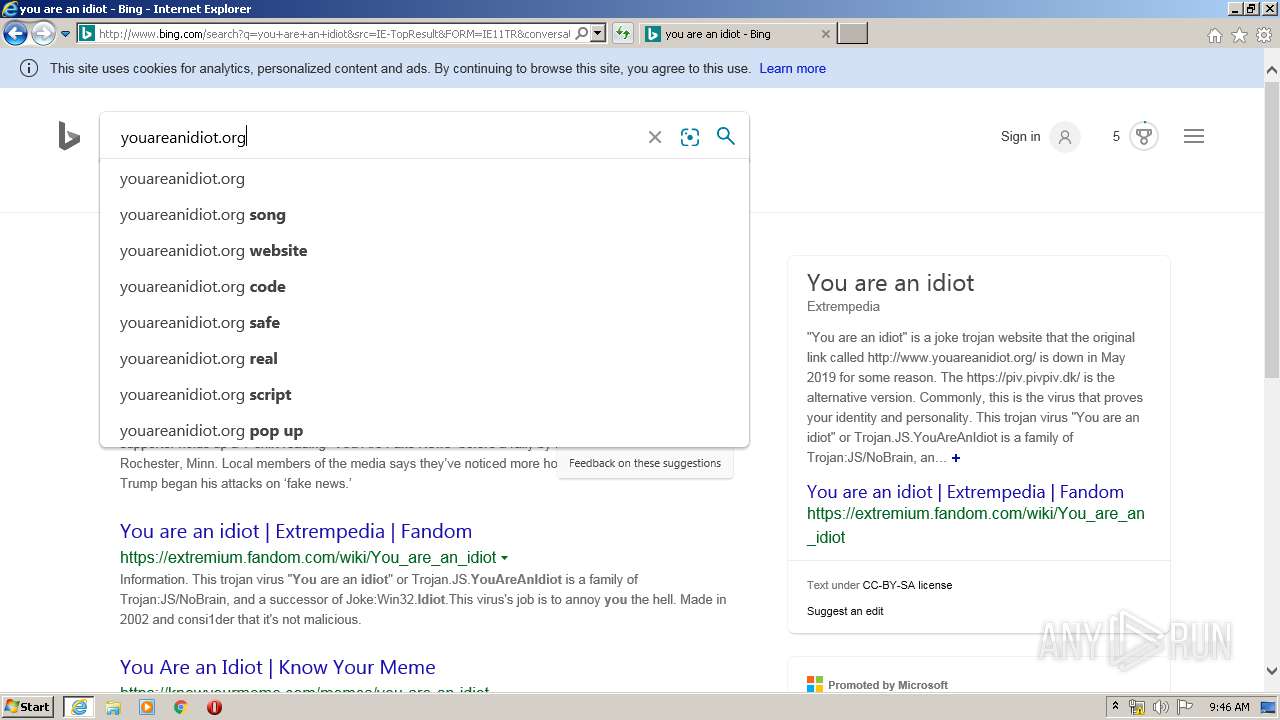
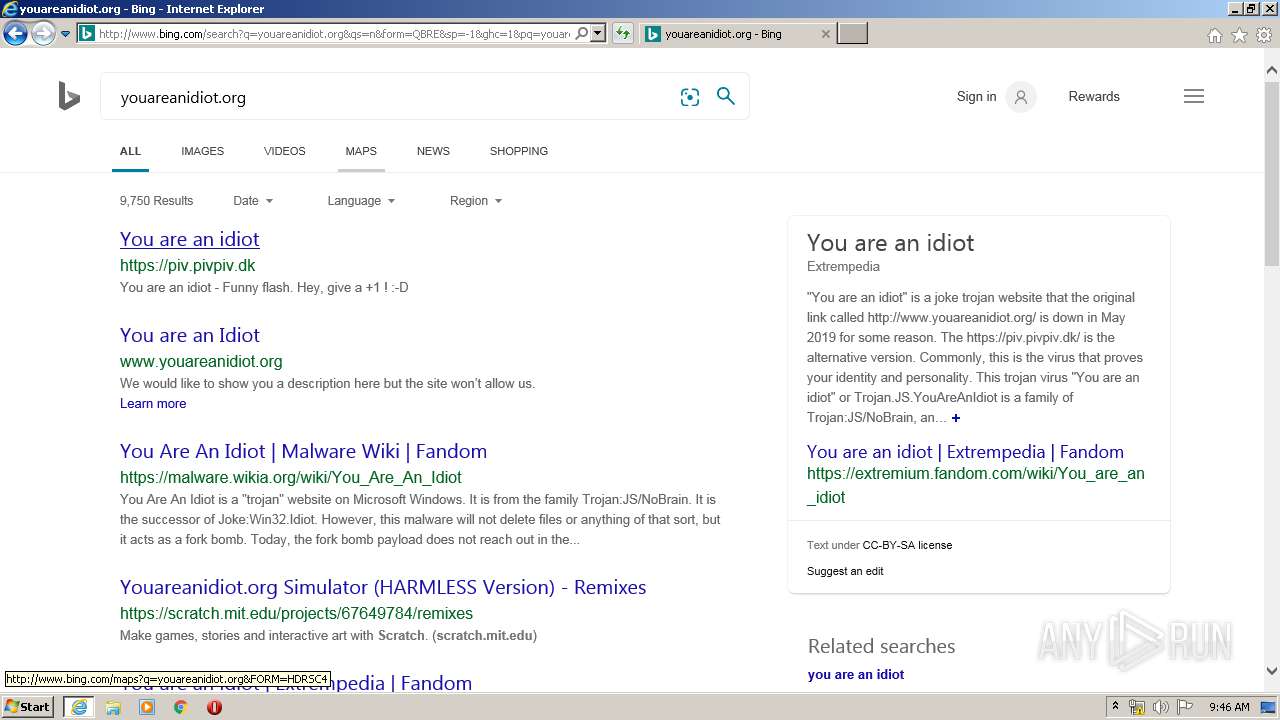
2492 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/search?q=you+are+an+idiot&src=IE-TopResult&FORM=IE11TR&conversationid= | US | html | 55.9 Kb | whitelisted |
2492 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=you+are&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 244 b | whitelisted |
2492 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=you+are+an+idiot&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 238 b | whitelisted |
2492 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=9018097B9E6C4207A0D49142F4997AF1&CID=2A8507D4F77265D306890961F63264BB&Type=Event.CPT&DATA={"pp":{"S":"L","FC":33,"BC":479,"SE":-1,"TC":-1,"H":530,"BP":532,"CT":546,"IL":4},"ad":[-1,-1,1264,644,1264,1163,0]}&P=SERP&DA=DUB02 | US | compressed | 55.9 Kb | whitelisted |
2492 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rp/727Lg9_HUEvgiUGiGz5osrE6zMg.gz.js | US | text | 297 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2492 | iexplore.exe | 13.107.5.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
2492 | iexplore.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2492 | iexplore.exe | 104.18.24.243:80 | ocsp.msocsp.com | Cloudflare Inc | US | shared |
2492 | iexplore.exe | 204.79.197.222:80 | 21e9ed3caac25b5fa0ad4ba71f83bd36.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
2492 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2492 | iexplore.exe | 23.53.40.168:80 | a4.bing.com | Telia Company AB | NL | suspicious |
2492 | iexplore.exe | 52.231.32.10:80 | d0836628e08a9dc73e04ea9bcea254b4.clo.footprintdns.com | Microsoft Corporation | KR | whitelisted |
2492 | iexplore.exe | 13.107.6.163:80 | 234784f41d3ebbd263a68bad7af567ce.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
2492 | iexplore.exe | 104.211.224.23:80 | e551e3fa1067b4d22b4a330993702d0e.clo.footprintdns.com | Microsoft Corporation | IN | whitelisted |
3552 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youareanidiot.org |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |
d0836628e08a9dc73e04ea9bcea254b4.clo.footprintdns.com |
| unknown |
www2.bing.com |
| whitelisted |
21e9ed3caac25b5fa0ad4ba71f83bd36.clo.footprintdns.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2492 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |