| download: | pepek.msi |
| Full analysis: | https://app.any.run/tasks/a3bfa0de-d351-4182-8381-82b6556c5a0b |
| Verdict: | Malicious activity |
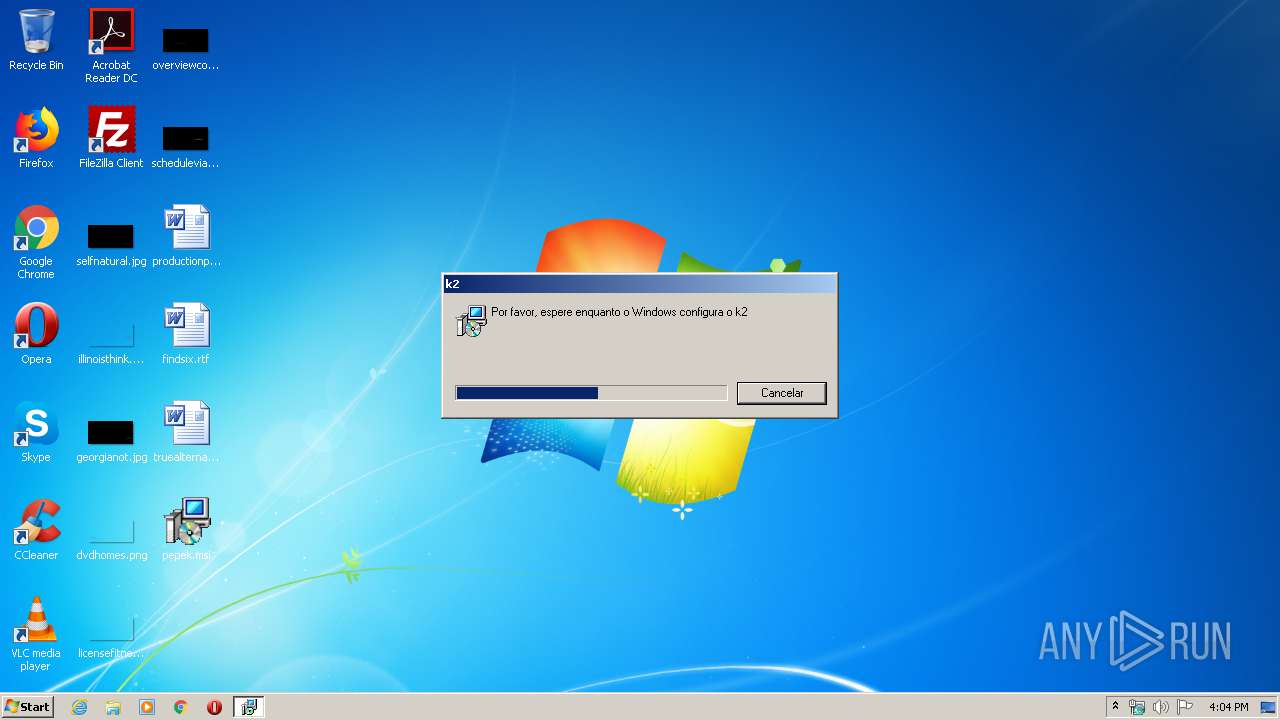
| Analysis date: | March 22, 2020, 16:04:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Dec 11 11:47:44 2009, Code page: 1252, Revision Number: {FD4C1C80-243E-4795-9D4A-18611A9A705B}, Number of Words: 10, Subject: Adobe Acrobat Reader, Author: Adobe Systems Incorporated, Name of Creating Application: Advanced Installer 12.3 build 64631, Template: ;1046, Comments: This installer database contains the logic and data required to install Adobe Acrobat Reader., Title: Installation Database, Keywords: Installer, MSI, Database, Security: 0, Number of Pages: 200 |
| MD5: | FC946F4CD0281BAF8C004DA19F712281 |
| SHA1: | F32D735738EEED6A81D49E260B5E9568EE07AEC9 |
| SHA256: | 2218902BC67A30F600AFADA4A77540EAE6E415634AD420D9DCE315F8F1E45DEA |
| SSDEEP: | 3072:tIygYXkj7q0vTYDryO1nF52QyI/+eybXqJU6ij4qpXqnnDibAJBVkA9GY5AQ3DrG:tmir2QyI/+eyoTqp4nwEWY5AQ3D |
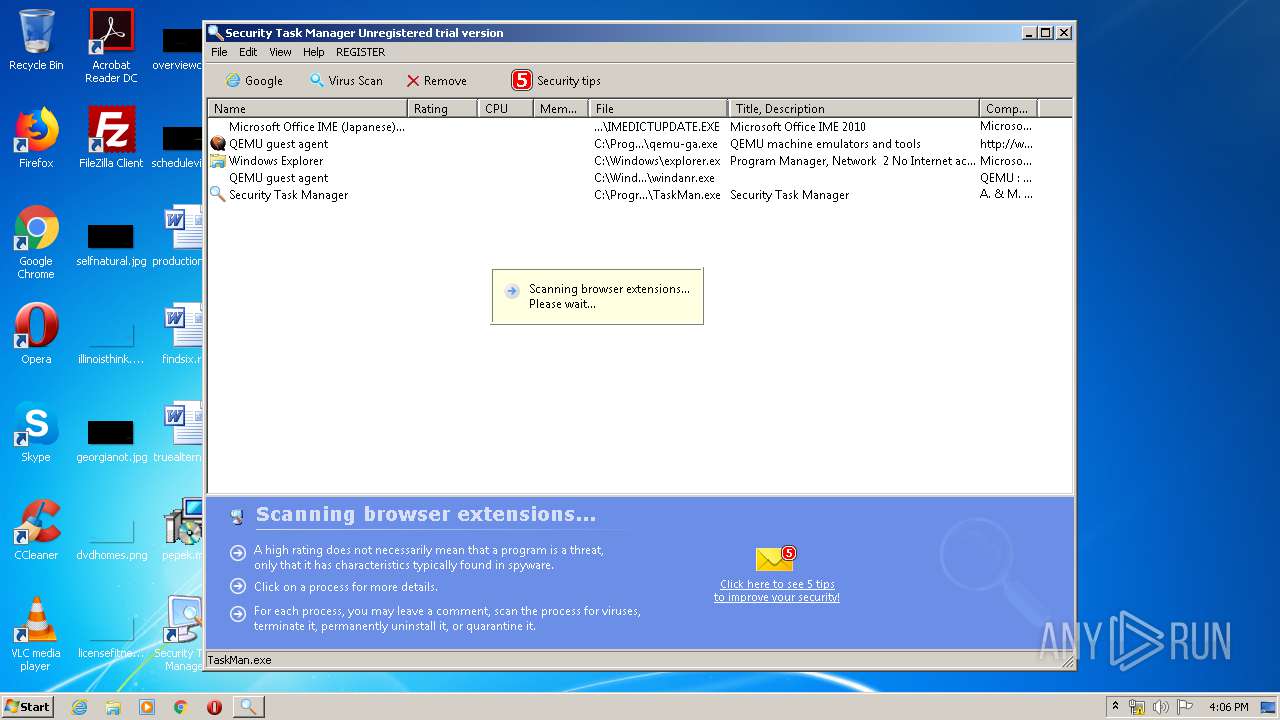
MALICIOUS
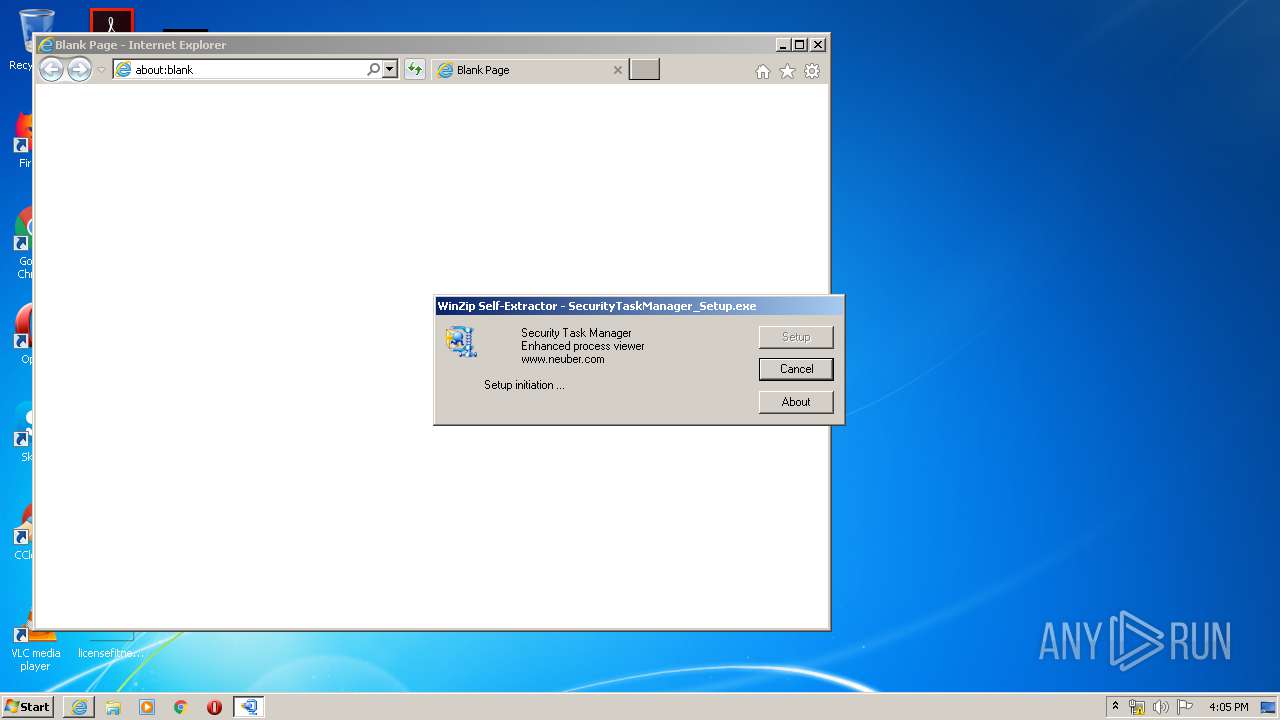
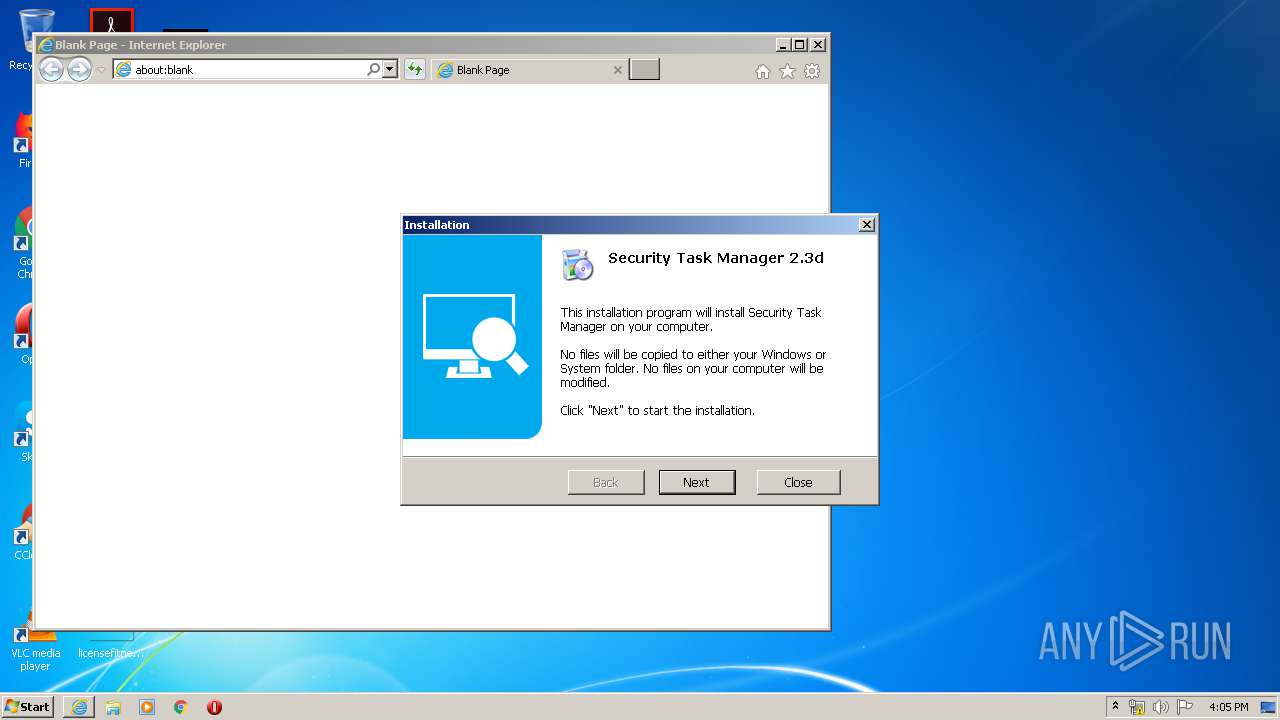
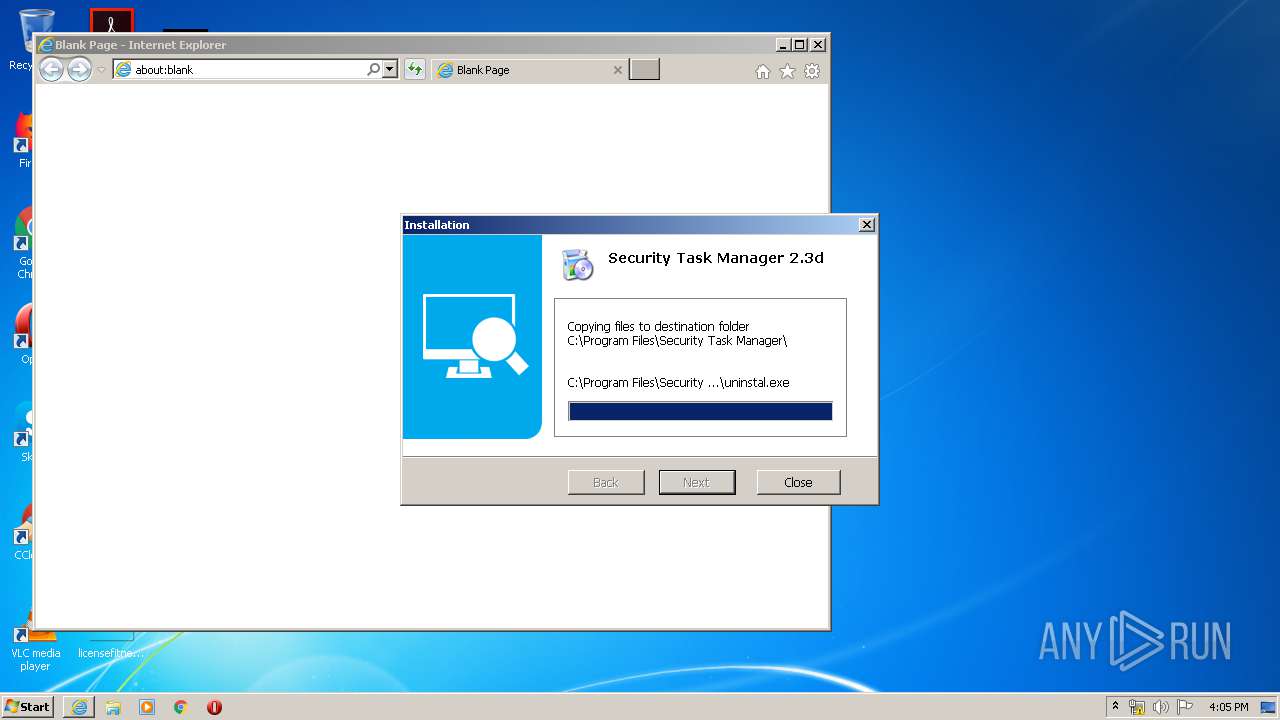
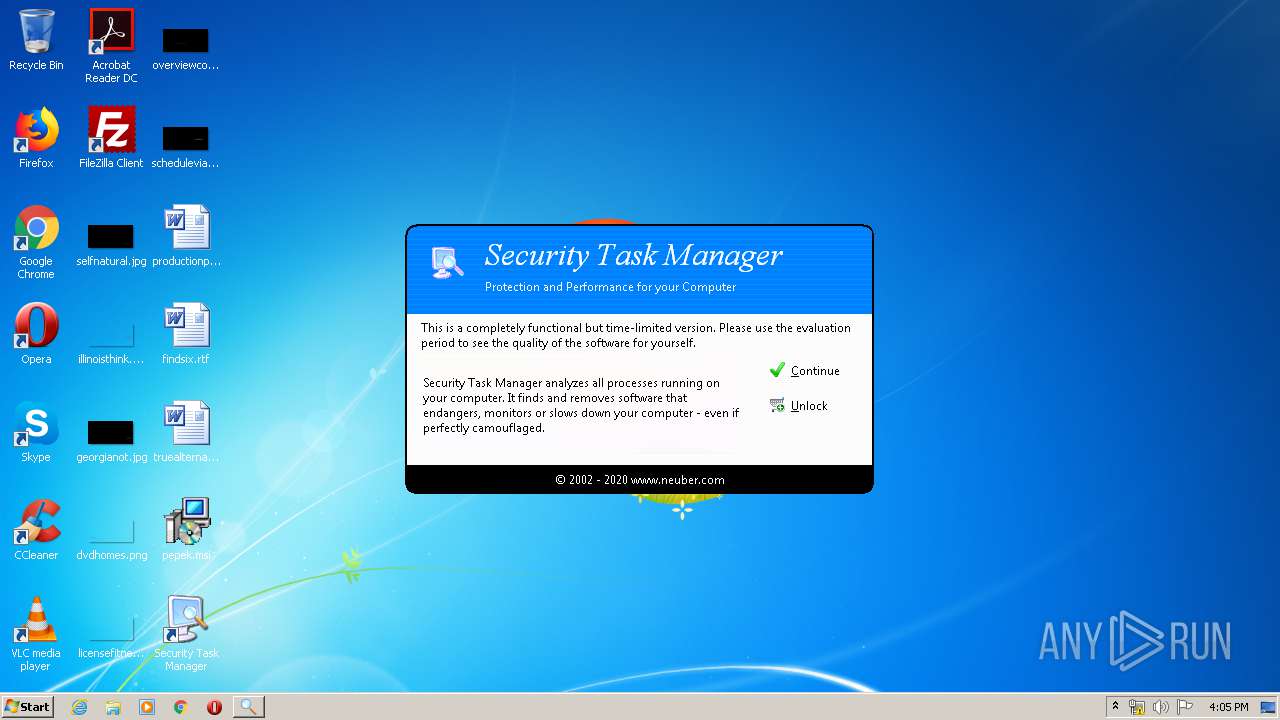
Application was dropped or rewritten from another process
- SecurityTaskManager_Setup.exe (PID: 3368)
- SecurityTaskManager_Setup.exe (PID: 576)
- setup.exe (PID: 984)
- TaskMan.exe (PID: 3924)
- TaskMan.exe (PID: 3916)
Loads dropped or rewritten executable
- TaskMan.exe (PID: 3924)
- explorer.exe (PID: 372)
- ctfmon.exe (PID: 652)
- TaskMan.exe (PID: 3916)
Loads the Task Scheduler COM API
- TaskMan.exe (PID: 3924)
- TaskMan.exe (PID: 3916)
SUSPICIOUS
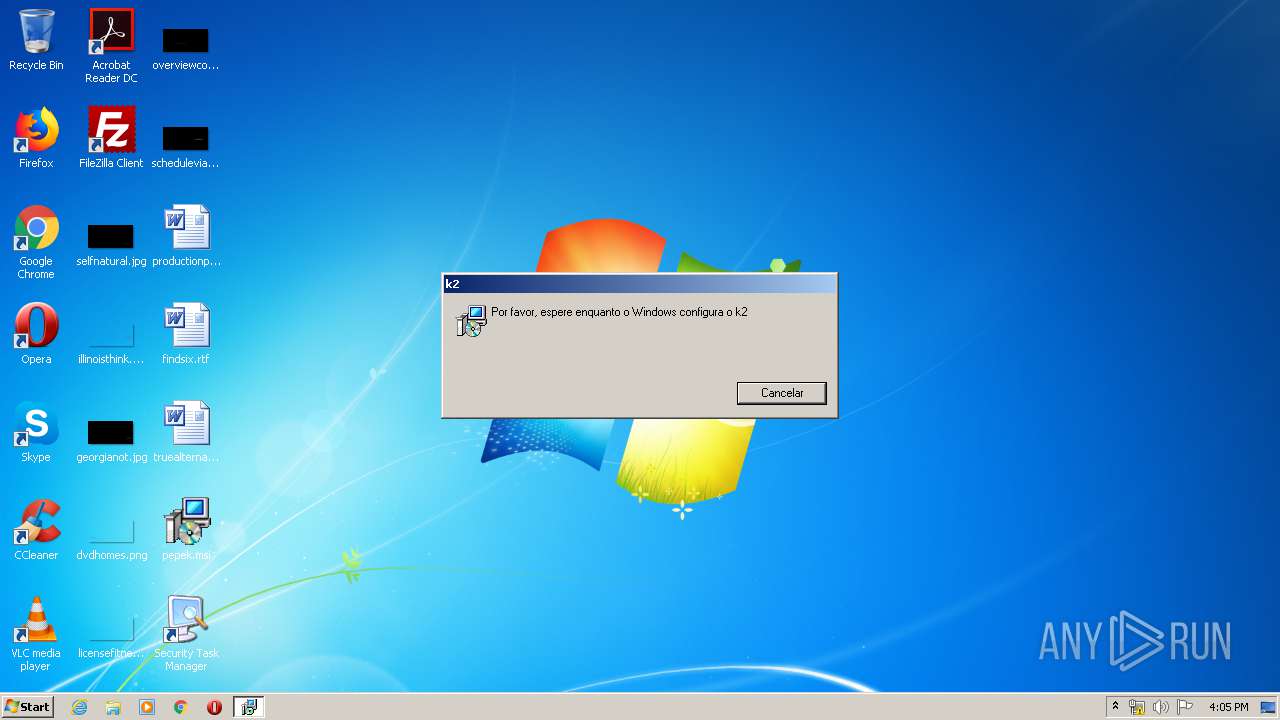
Starts Microsoft Installer
- explorer.exe (PID: 372)
Changes the autorun value in the registry
- MsiExec.exe (PID: 1748)
- MsiExec.exe (PID: 3568)
Reads Internet Cache Settings
- MsiExec.exe (PID: 1748)
- MsiExec.exe (PID: 3568)
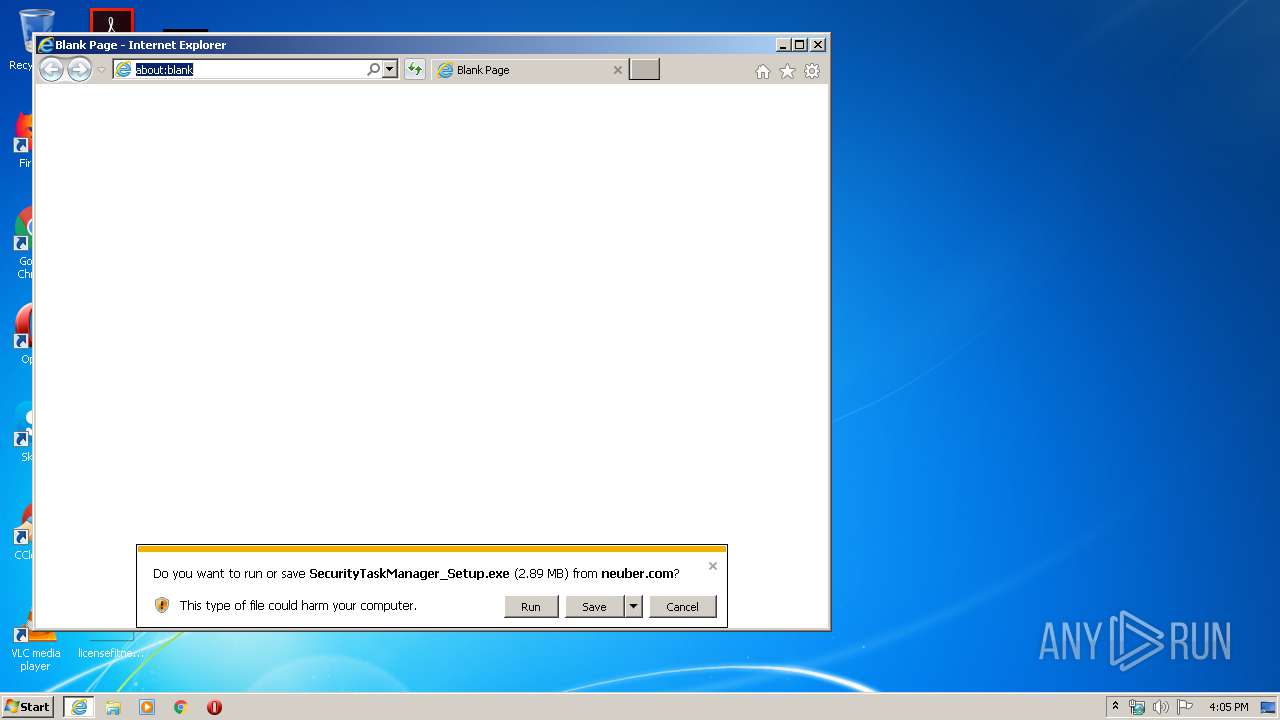
Starts Internet Explorer
- explorer.exe (PID: 372)
Executable content was dropped or overwritten
- msiexec.exe (PID: 680)
- iexplore.exe (PID: 3892)
- iexplore.exe (PID: 1536)
- SecurityTaskManager_Setup.exe (PID: 576)
- setup.exe (PID: 984)
Creates files in the program directory
- setup.exe (PID: 984)
- TaskMan.exe (PID: 3916)
- TaskMan.exe (PID: 3924)
Creates a software uninstall entry
- setup.exe (PID: 984)
Executed via COM
- explorer.exe (PID: 3692)
Creates files in the user directory
- TaskMan.exe (PID: 3924)
- TaskMan.exe (PID: 3916)
Searches for installed software
- TaskMan.exe (PID: 3924)
- TaskMan.exe (PID: 3916)
INFO
Manual execution by user
- iexplore.exe (PID: 1536)
Reads Internet Cache Settings
- iexplore.exe (PID: 1536)
- iexplore.exe (PID: 3892)
Application launched itself
- msiexec.exe (PID: 680)
Changes internet zones settings
- iexplore.exe (PID: 1536)
Creates files in the user directory
- iexplore.exe (PID: 3892)
Reads internet explorer settings
- iexplore.exe (PID: 3892)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1536)
Reads settings of System Certificates
- iexplore.exe (PID: 3892)
- iexplore.exe (PID: 1536)
- TaskMan.exe (PID: 3924)
- TaskMan.exe (PID: 3916)
Reads the hosts file
- TaskMan.exe (PID: 3924)
- TaskMan.exe (PID: 3916)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1536)
Changes settings of System certificates
- iexplore.exe (PID: 1536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (88.6) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (10) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| LastPrinted: | 2009:12:11 11:47:44 |
|---|---|
| CreateDate: | 2009:12:11 11:47:44 |
| ModifyDate: | 2009:12:11 11:47:44 |
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {FD4C1C80-243E-4795-9D4A-18611A9A705B} |
| Words: | 10 |
| Subject: | Adobe Acrobat Reader |
| Author: | Adobe Systems Incorporated |
| LastModifiedBy: | - |
| Software: | Advanced Installer 12.3 build 64631 |
| Template: | ;1046 |
| Comments: | This installer database contains the logic and data required to install Adobe Acrobat Reader. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| Security: | None |
| Pages: | 200 |
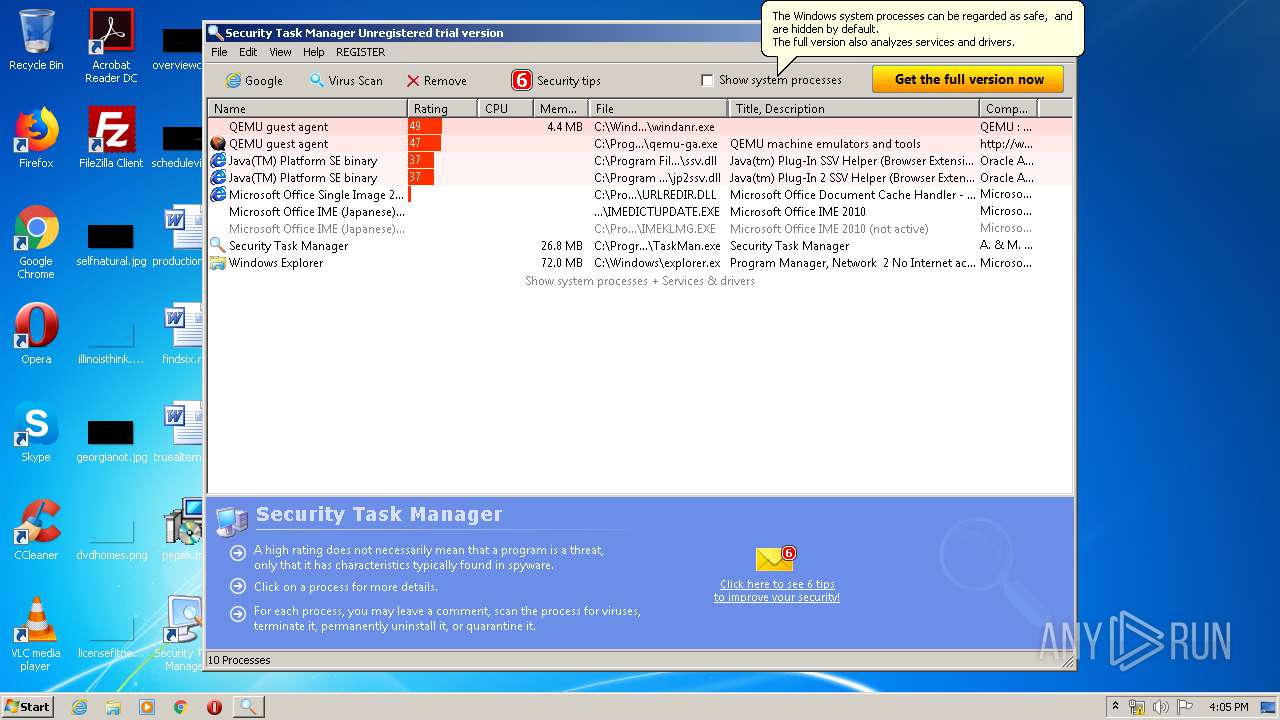
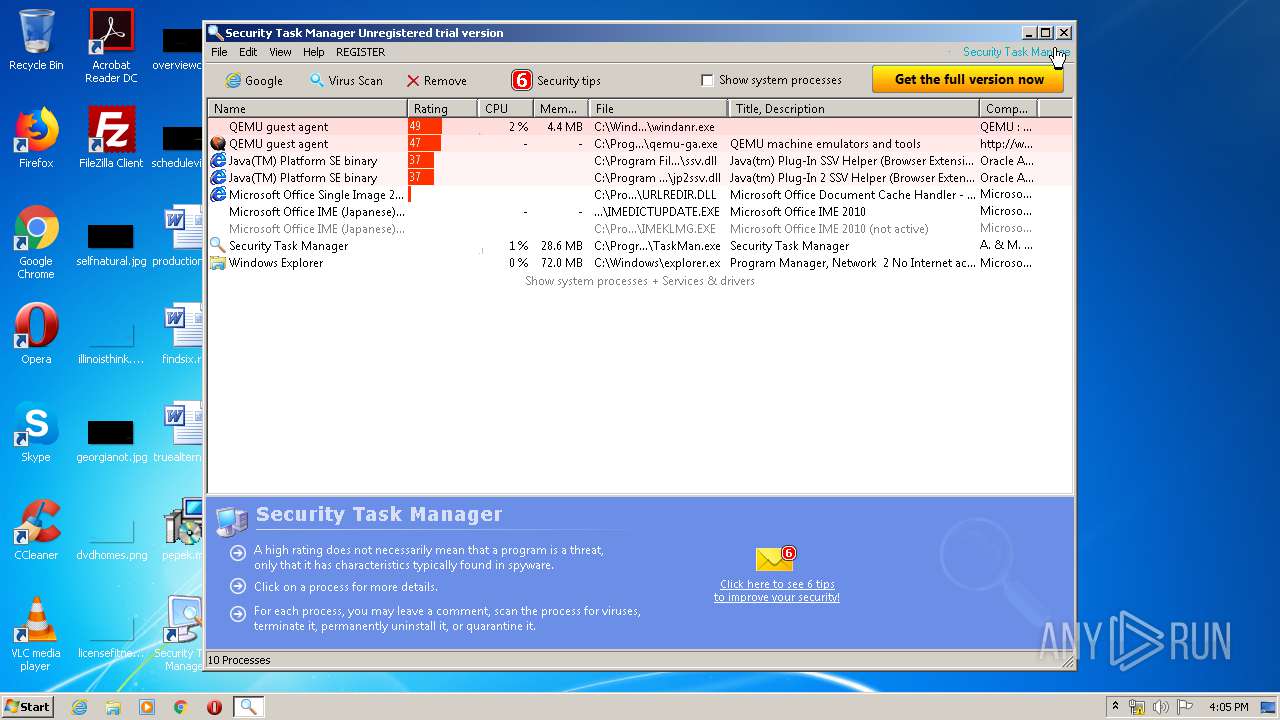
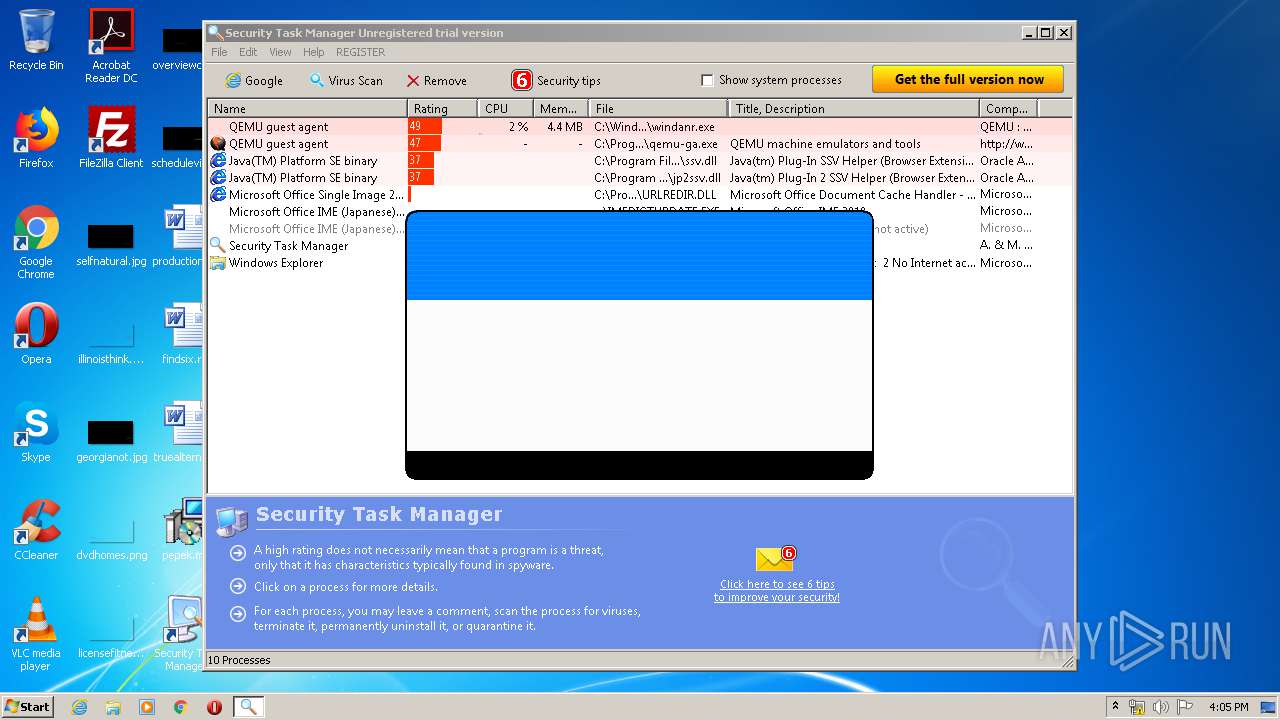
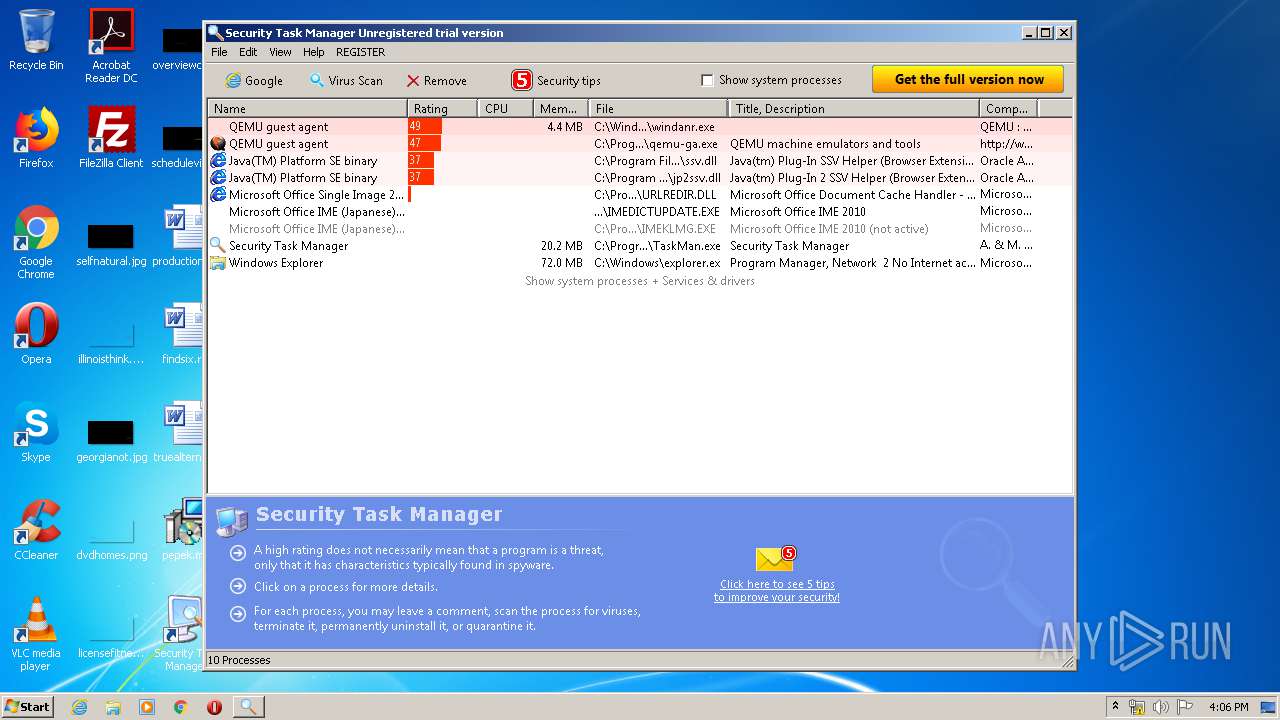
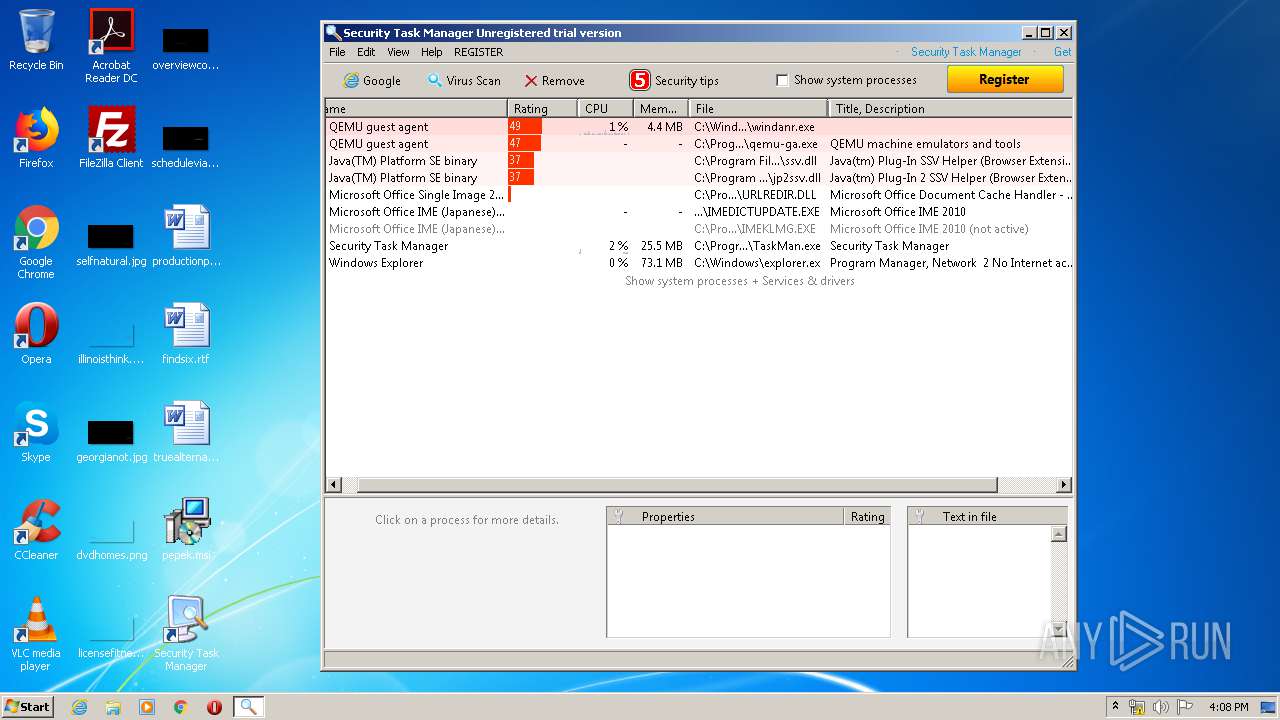
Total processes
53
Monitored processes
16
Malicious processes
6
Suspicious processes
2
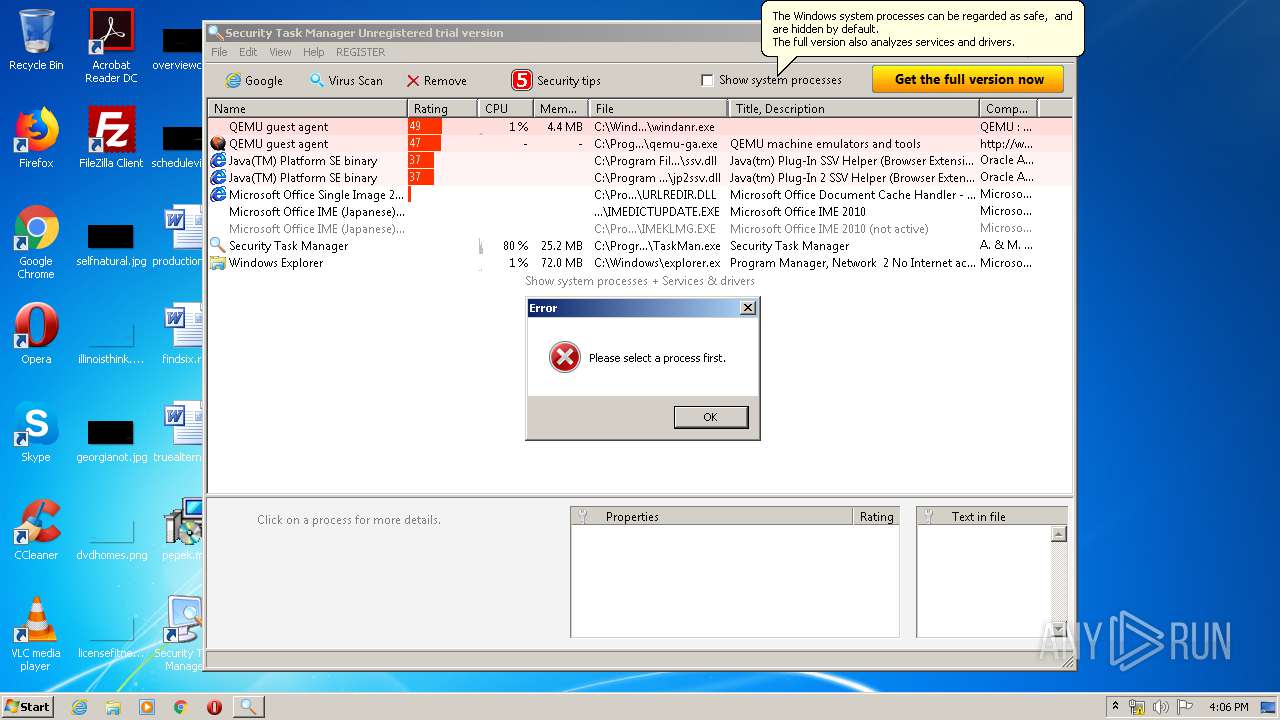
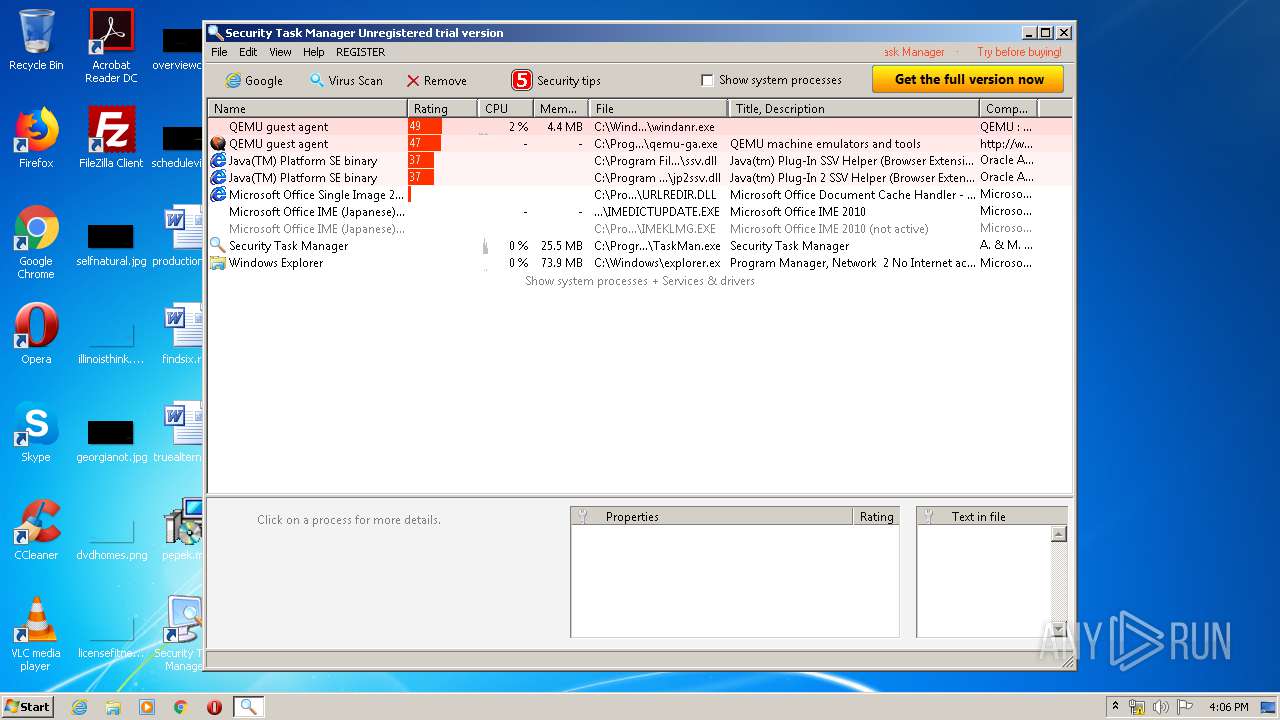
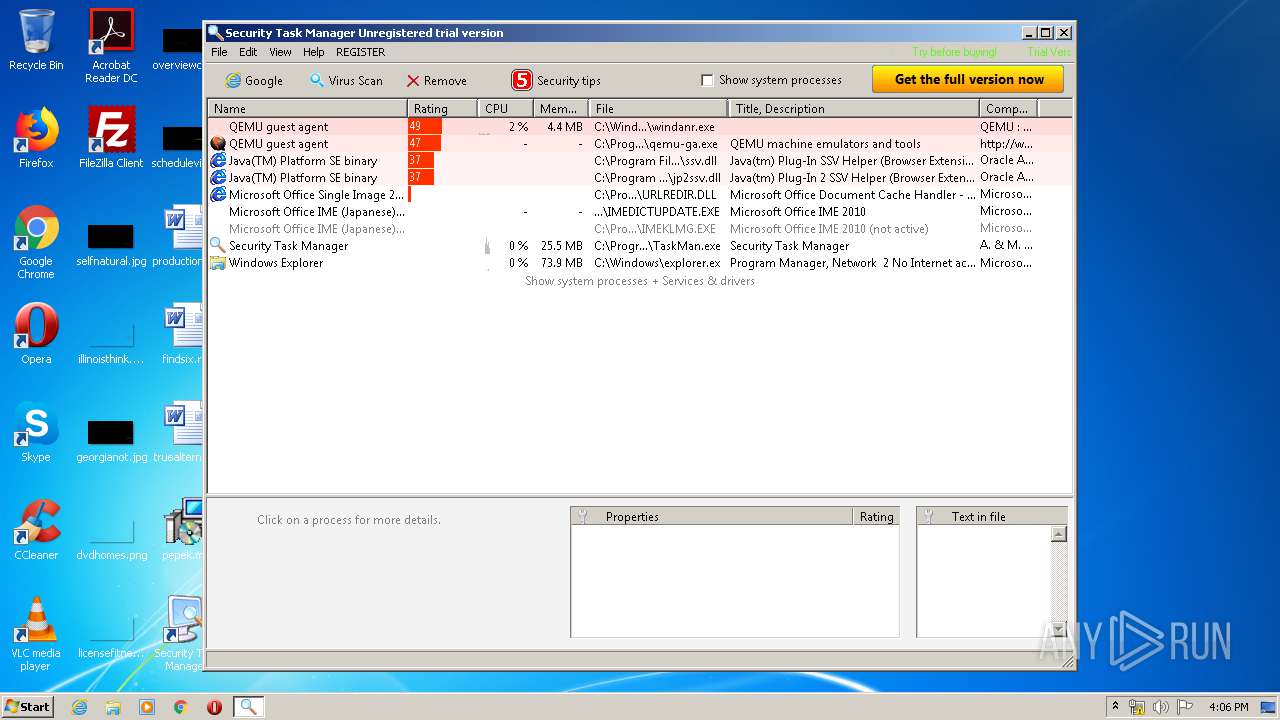
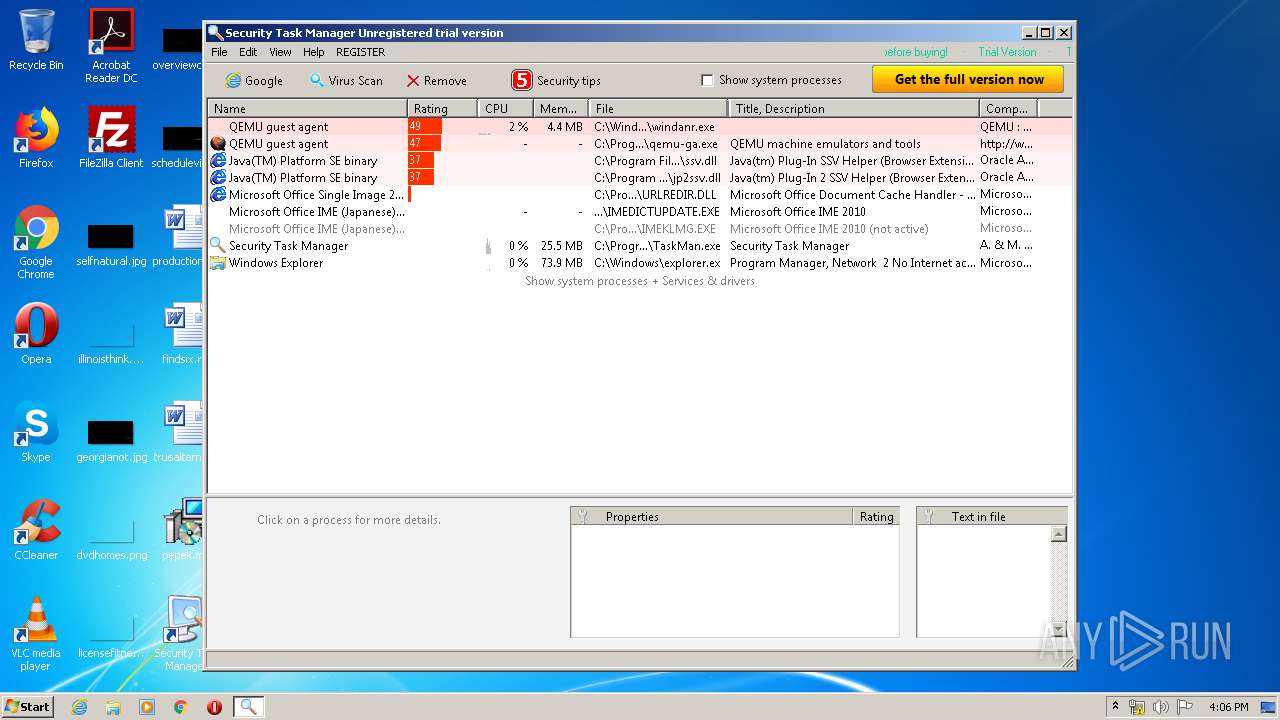
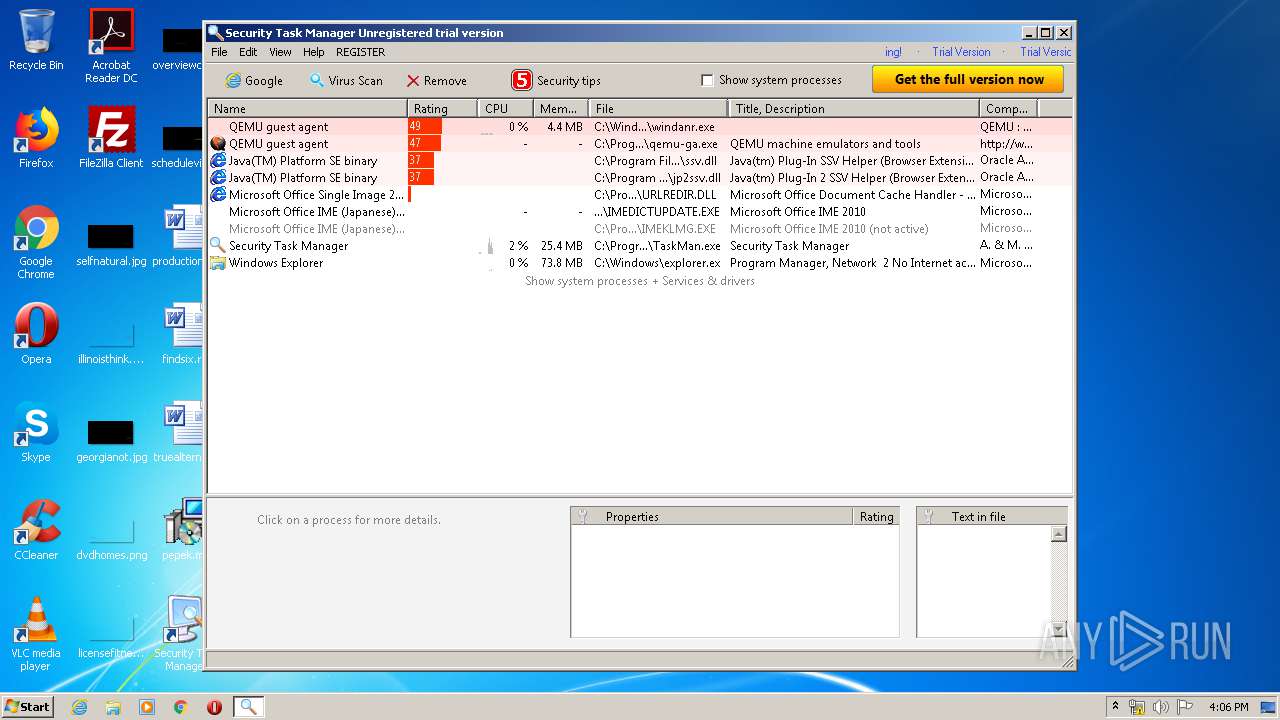
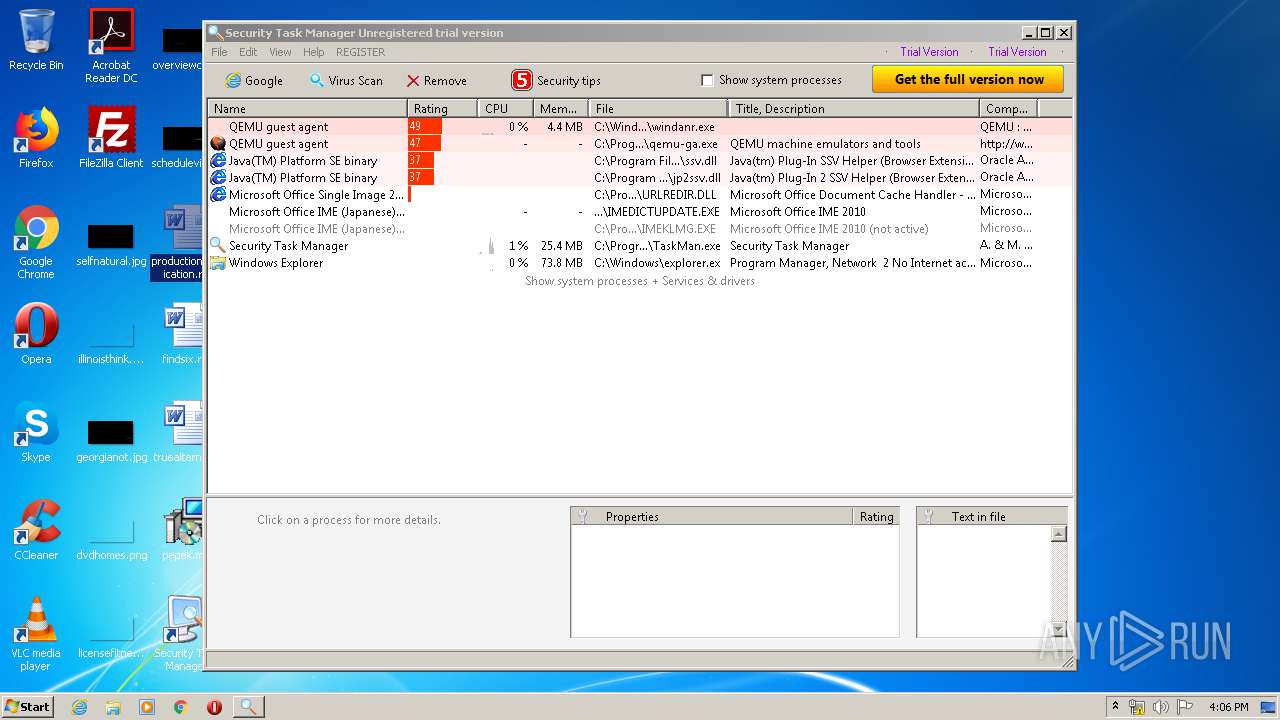
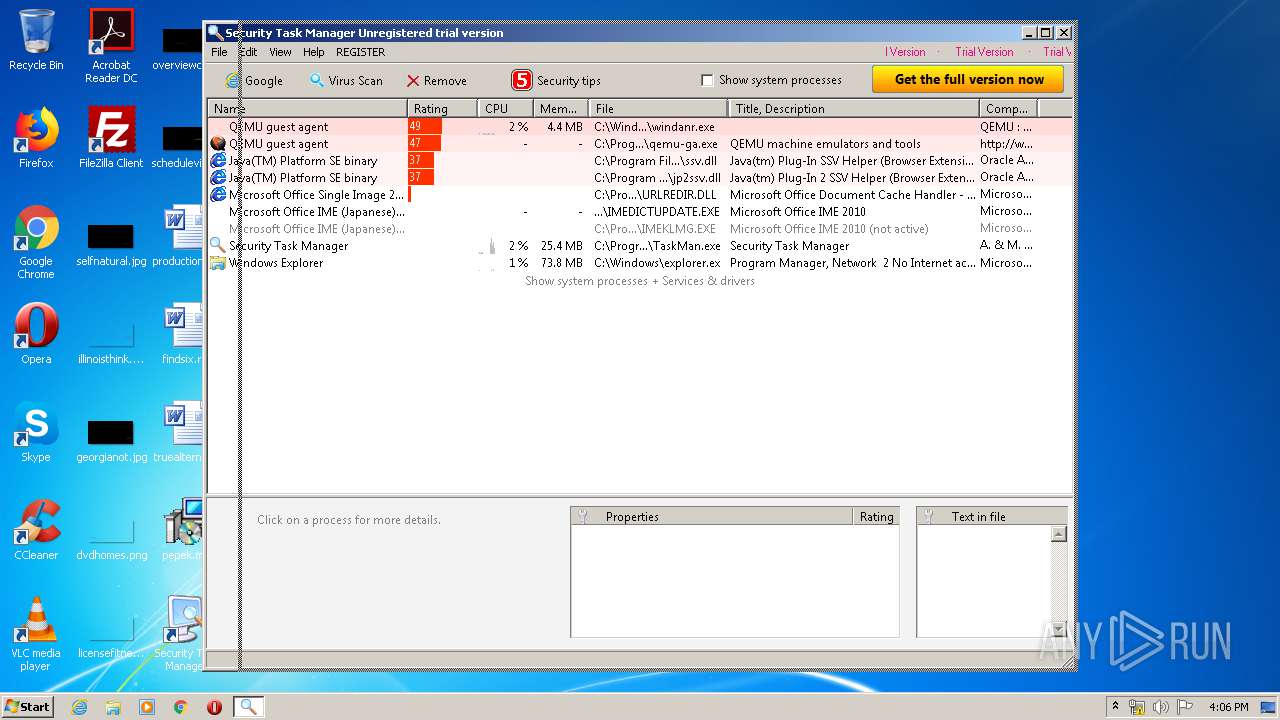
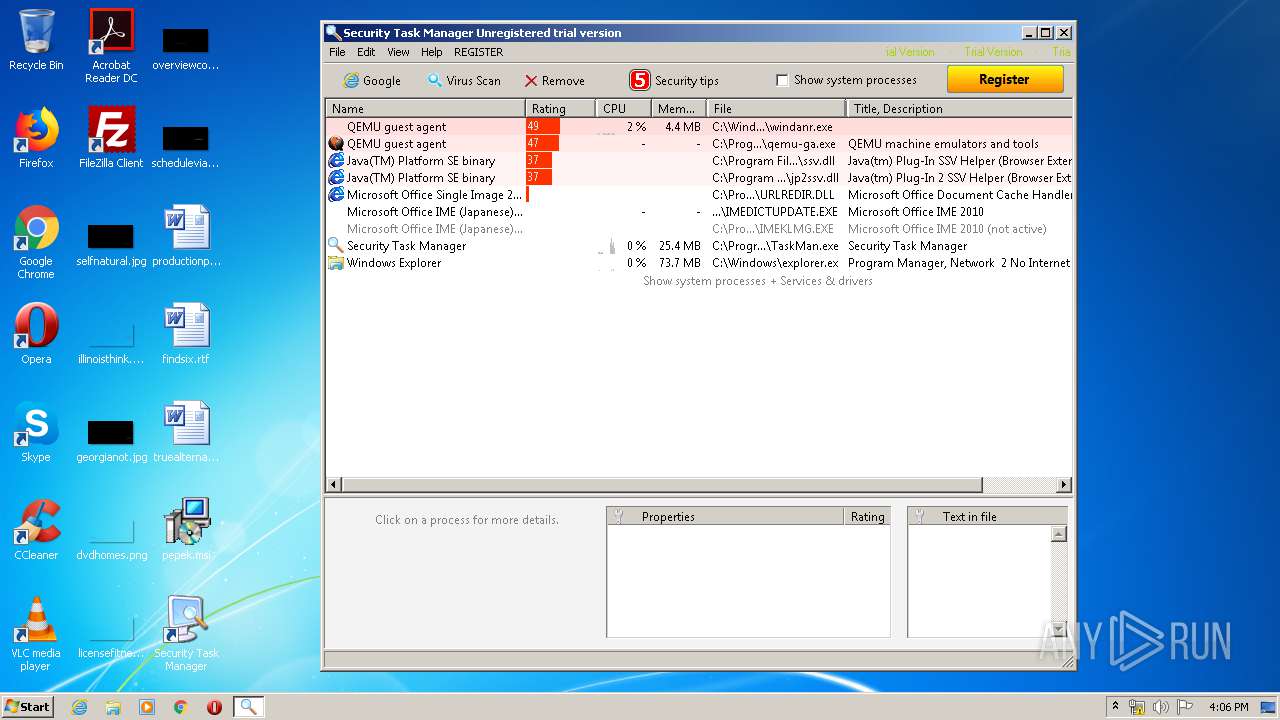
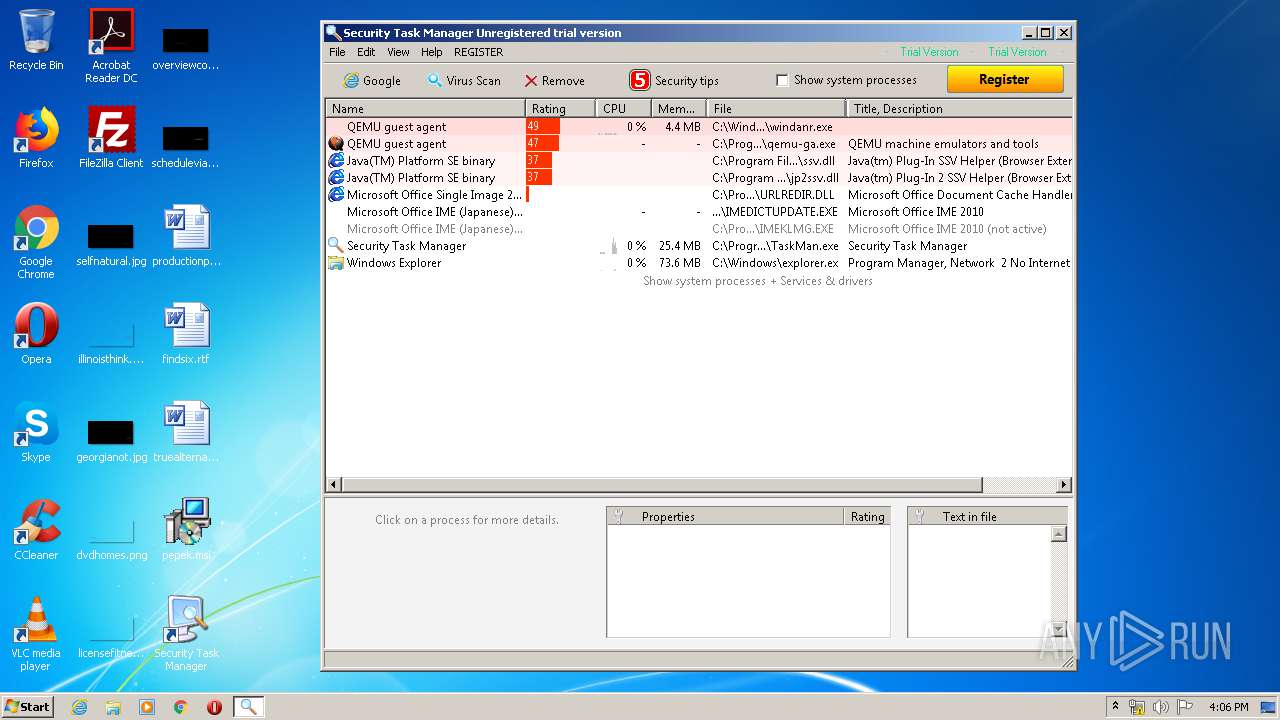
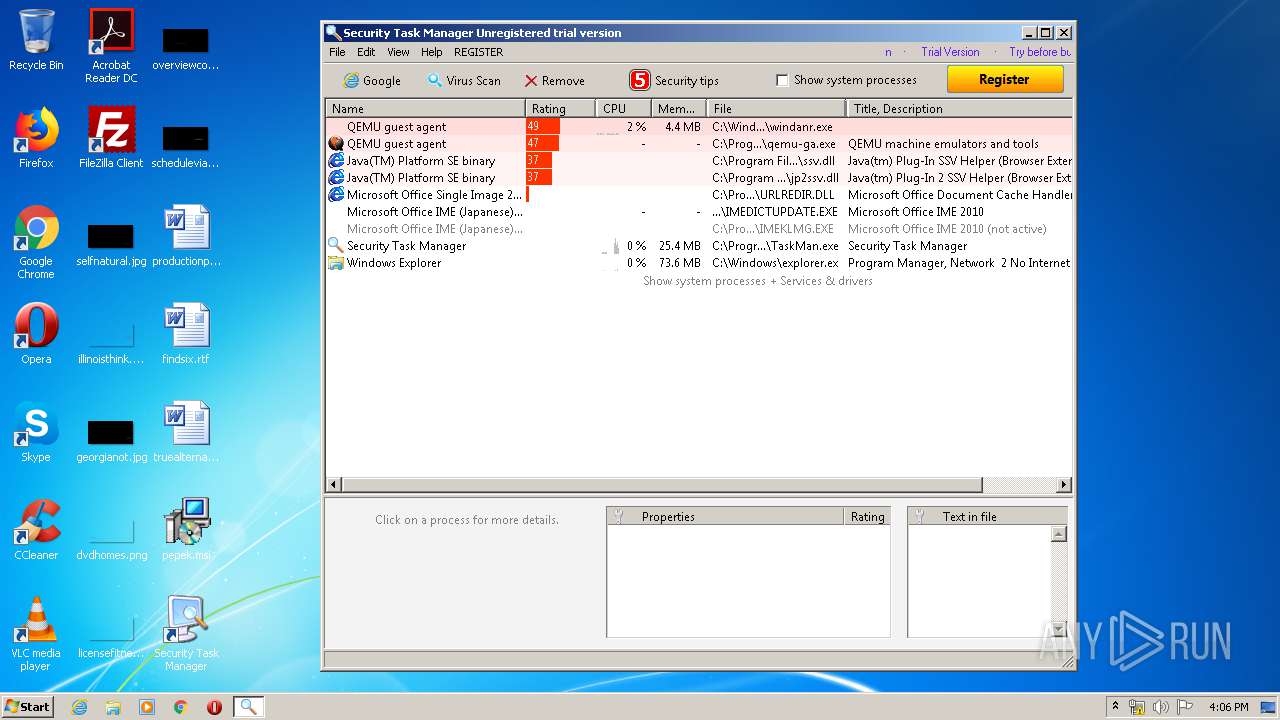
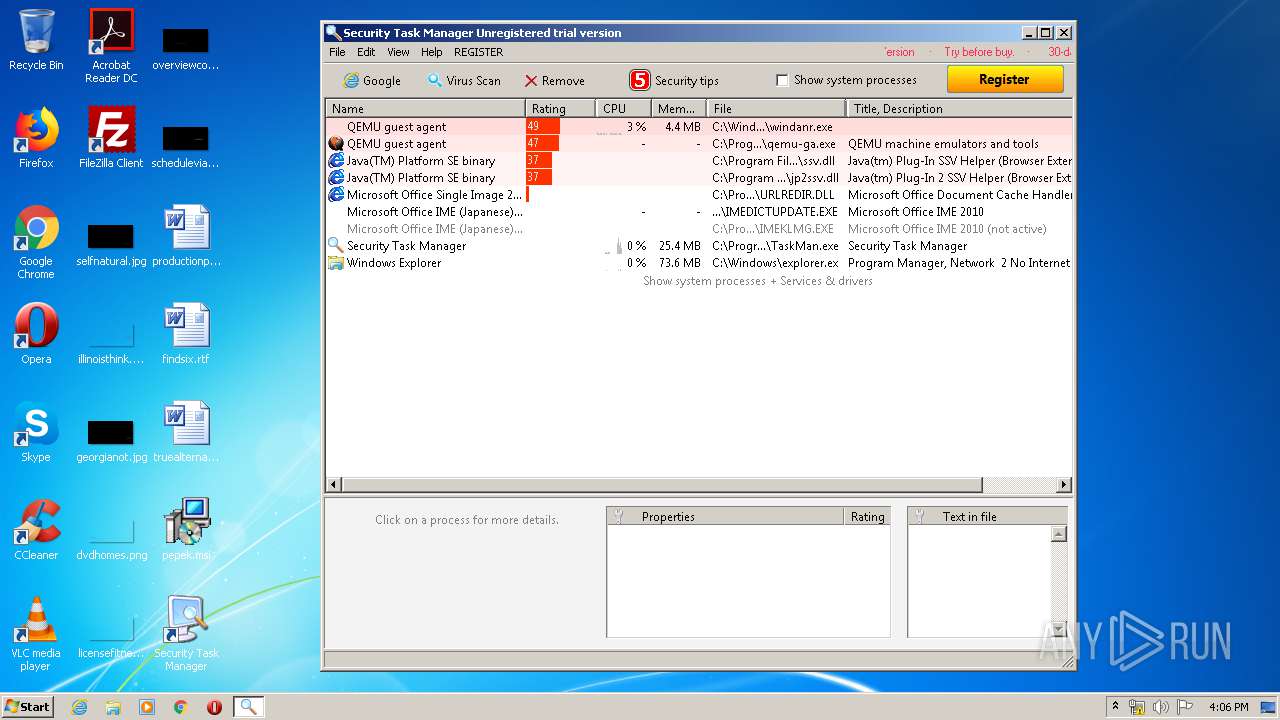
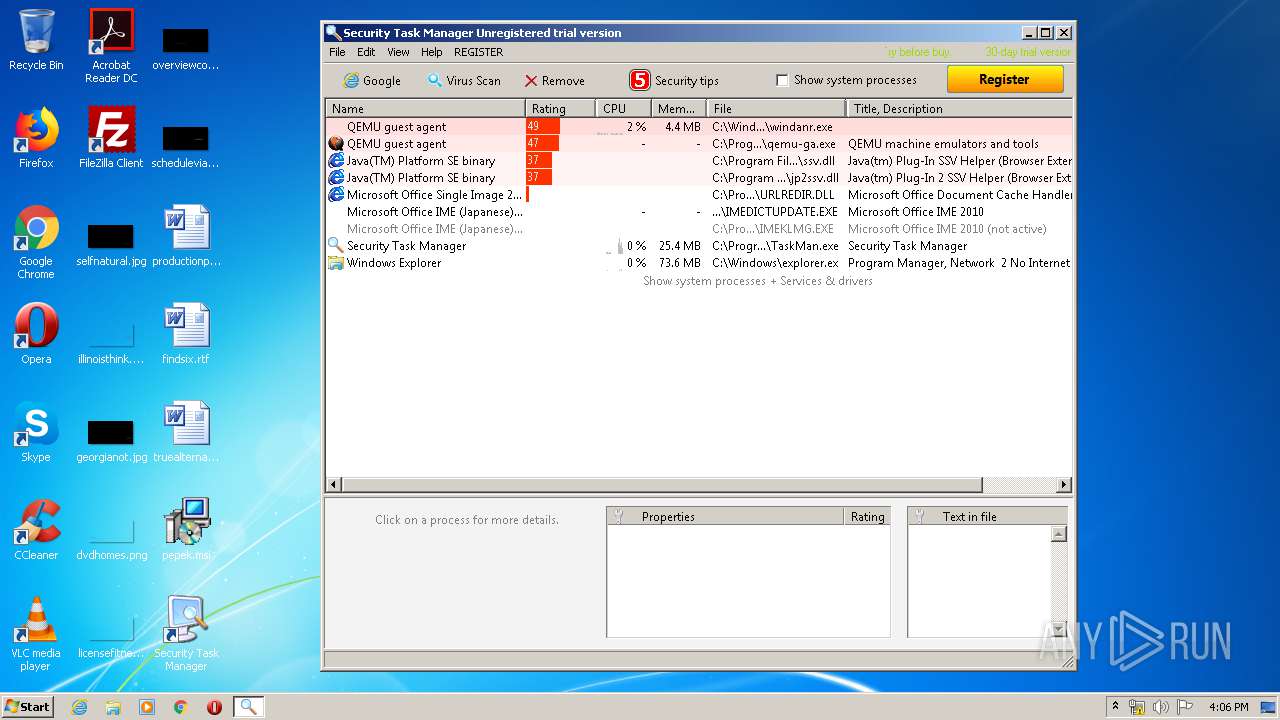
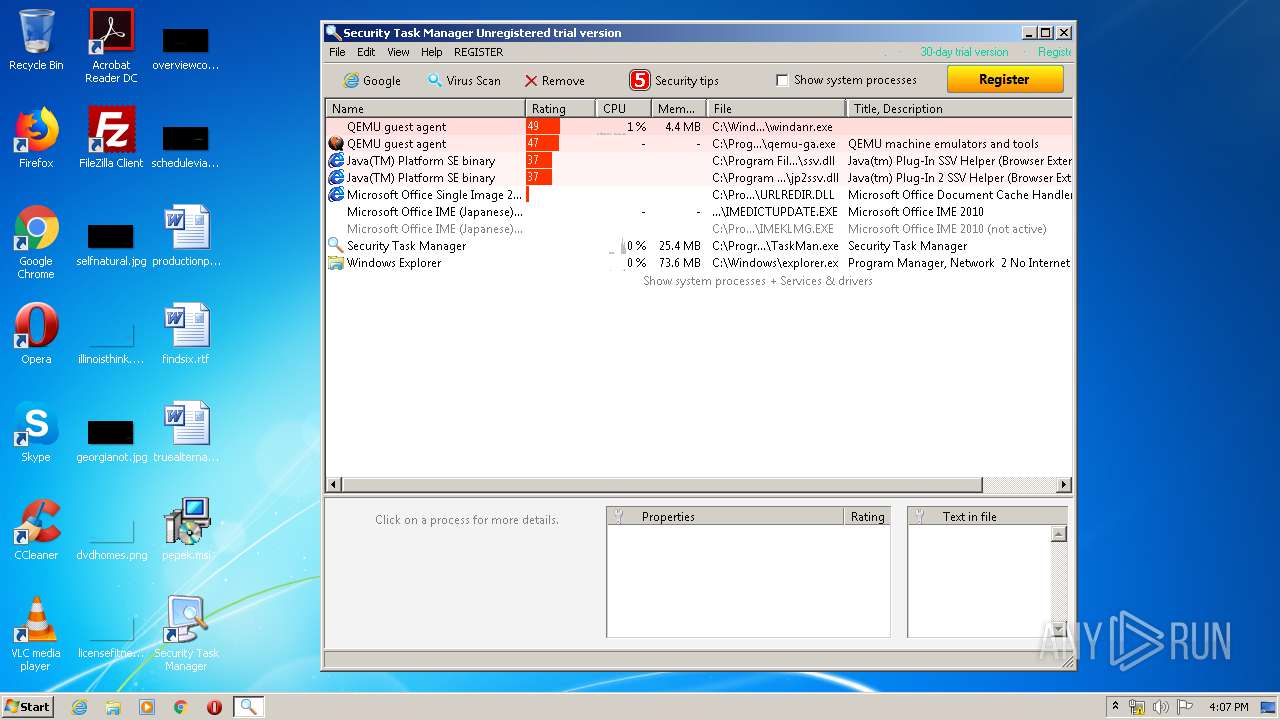
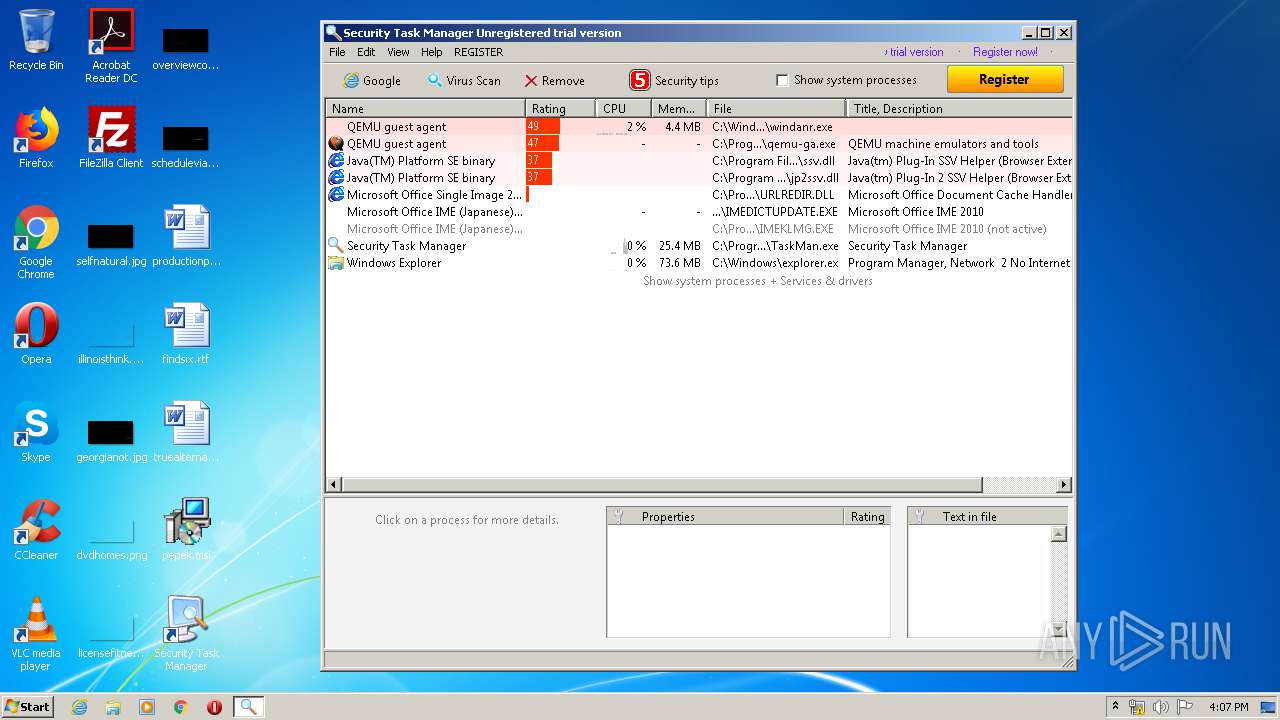
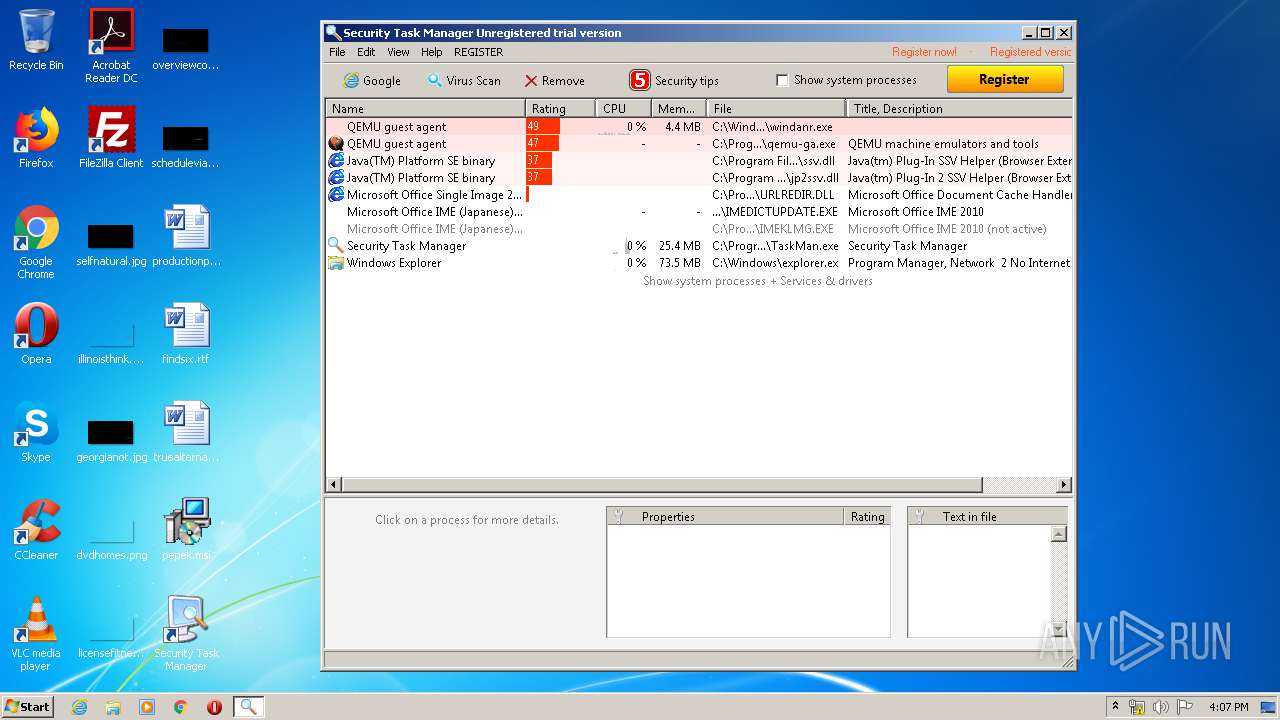
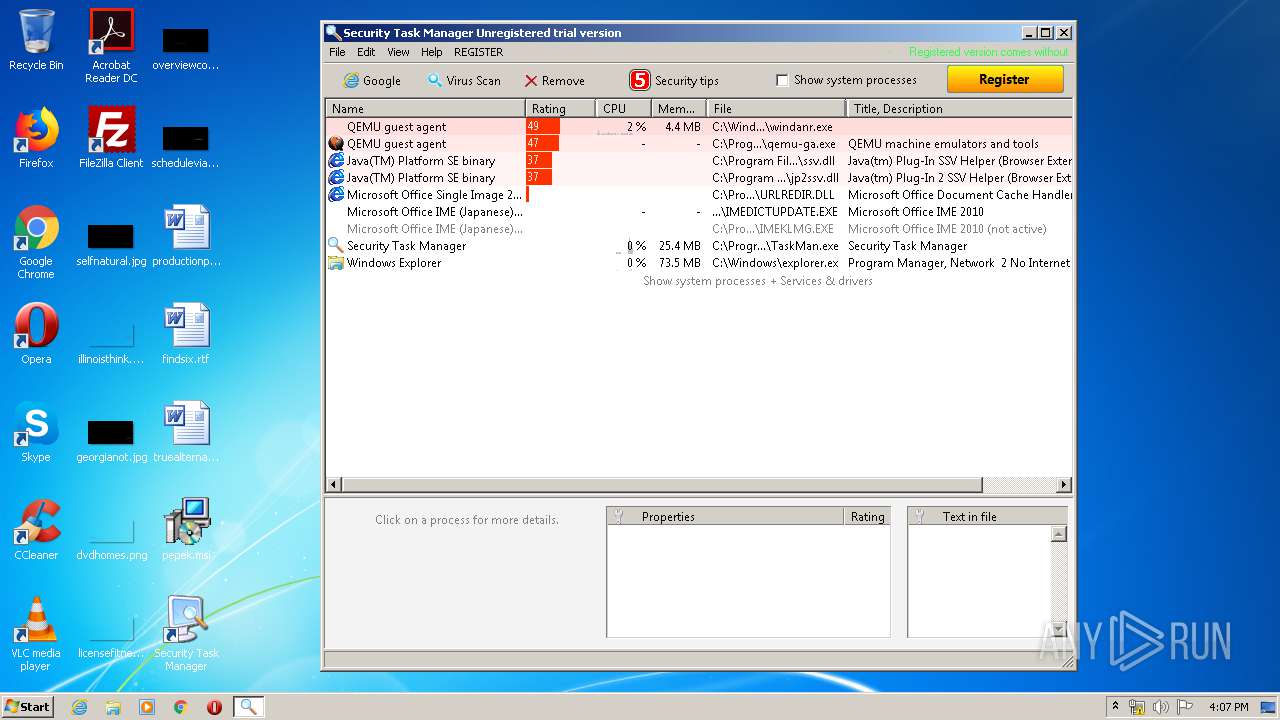
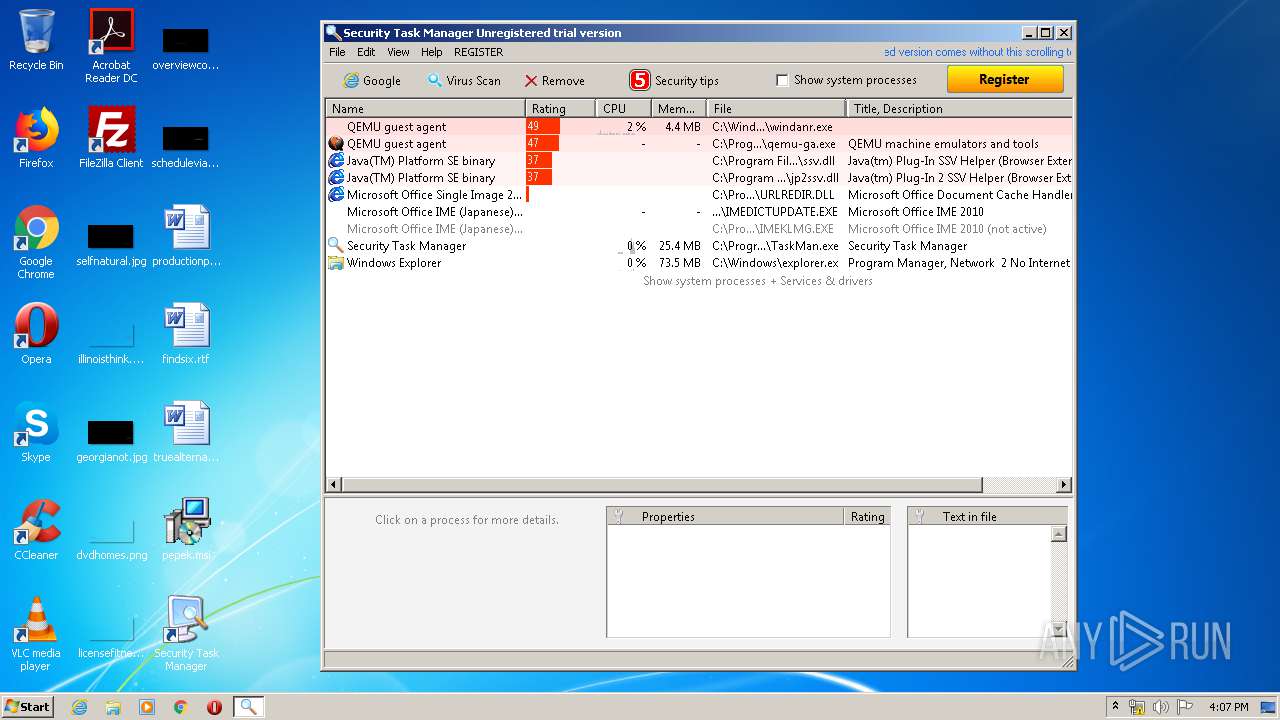
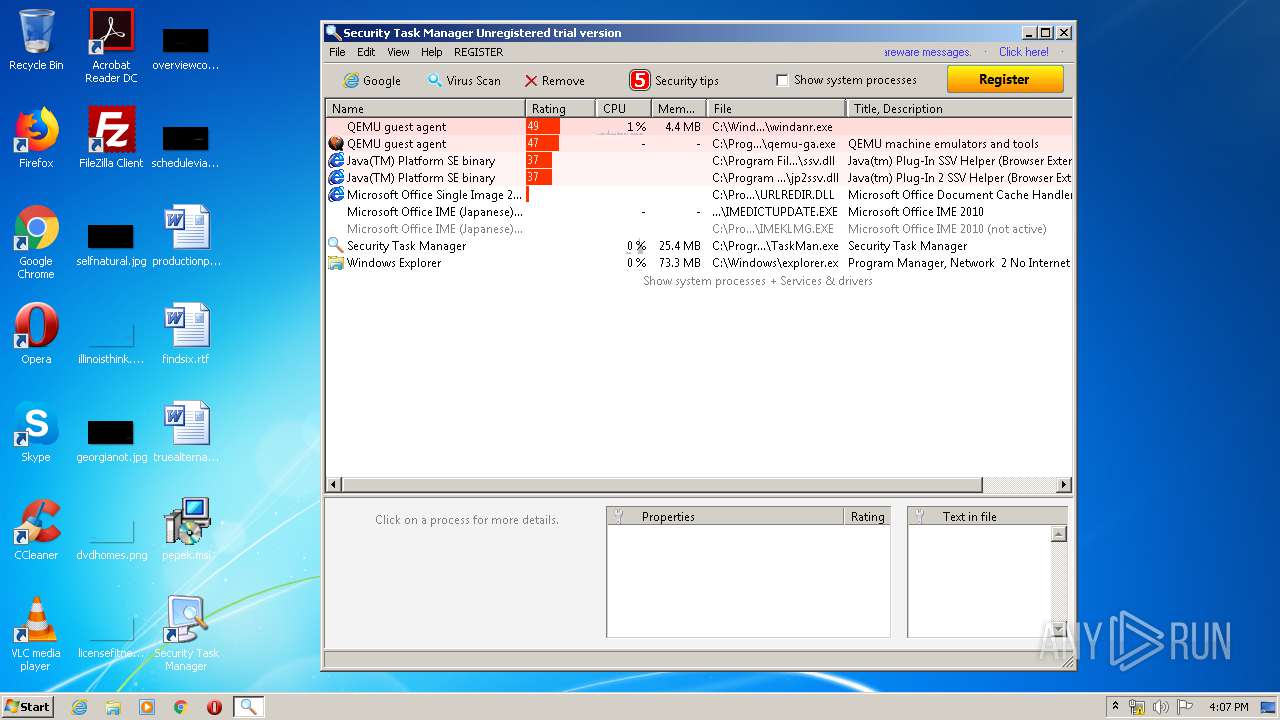
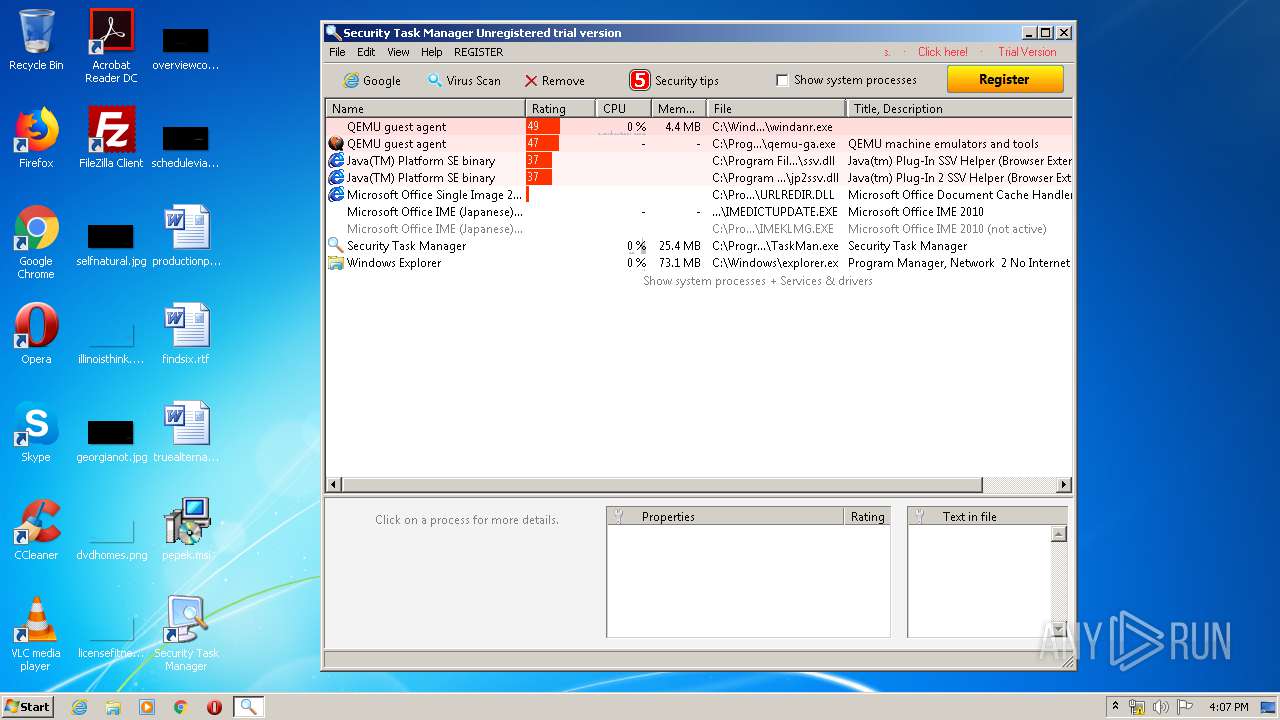
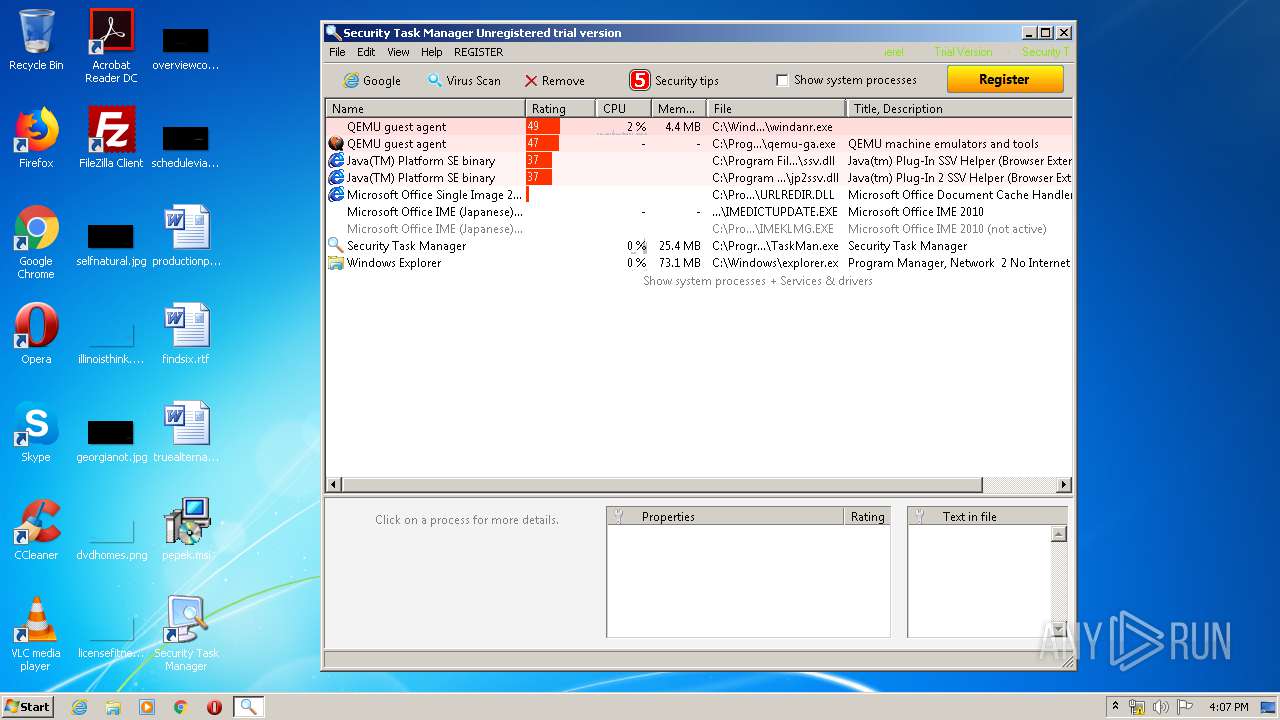
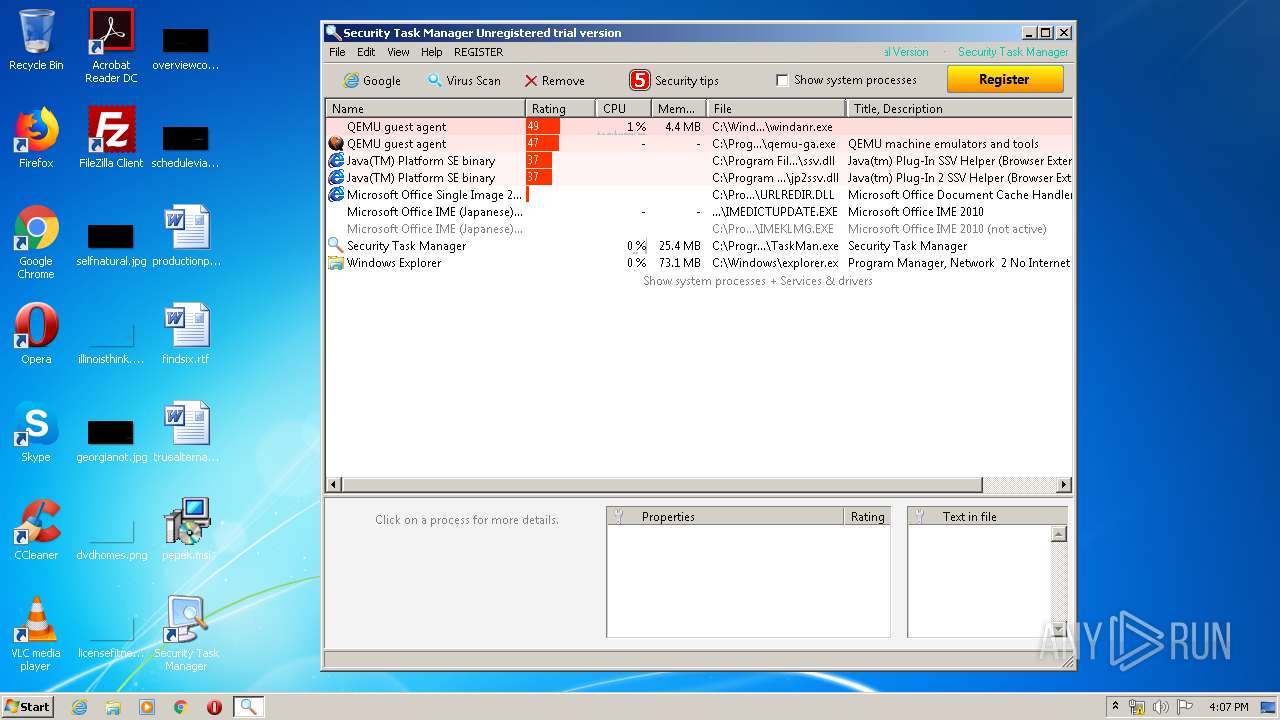
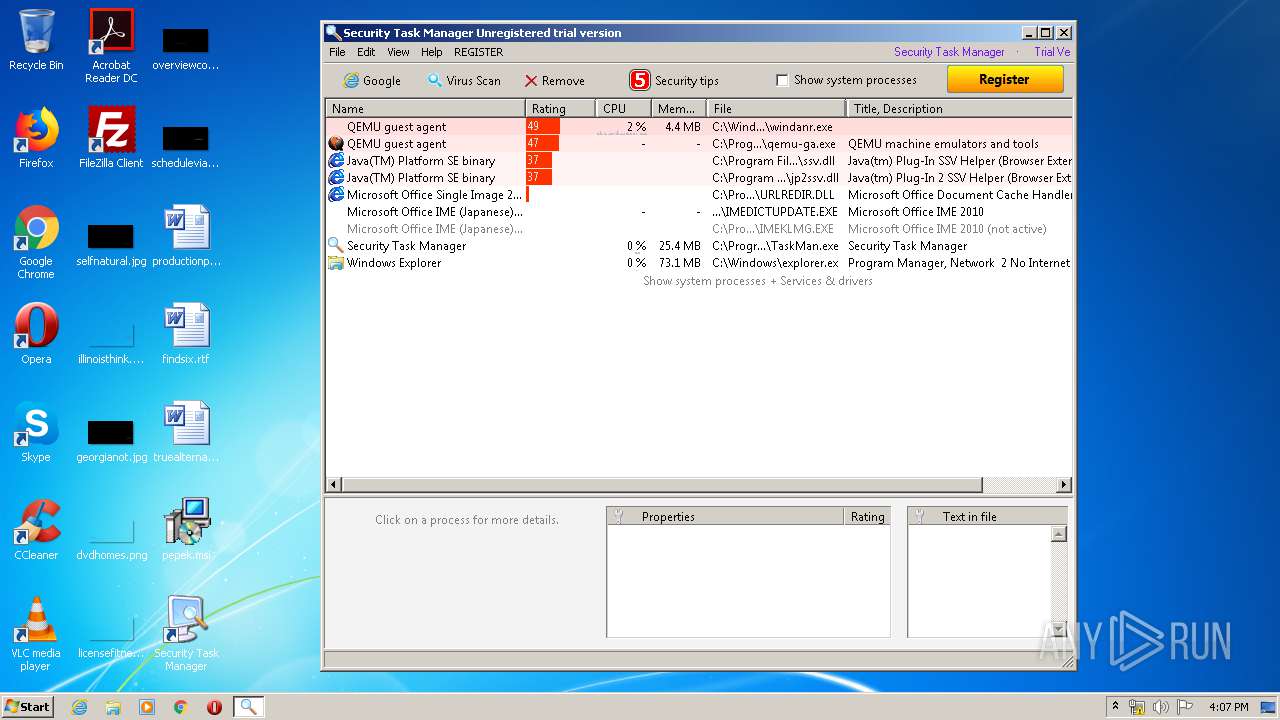
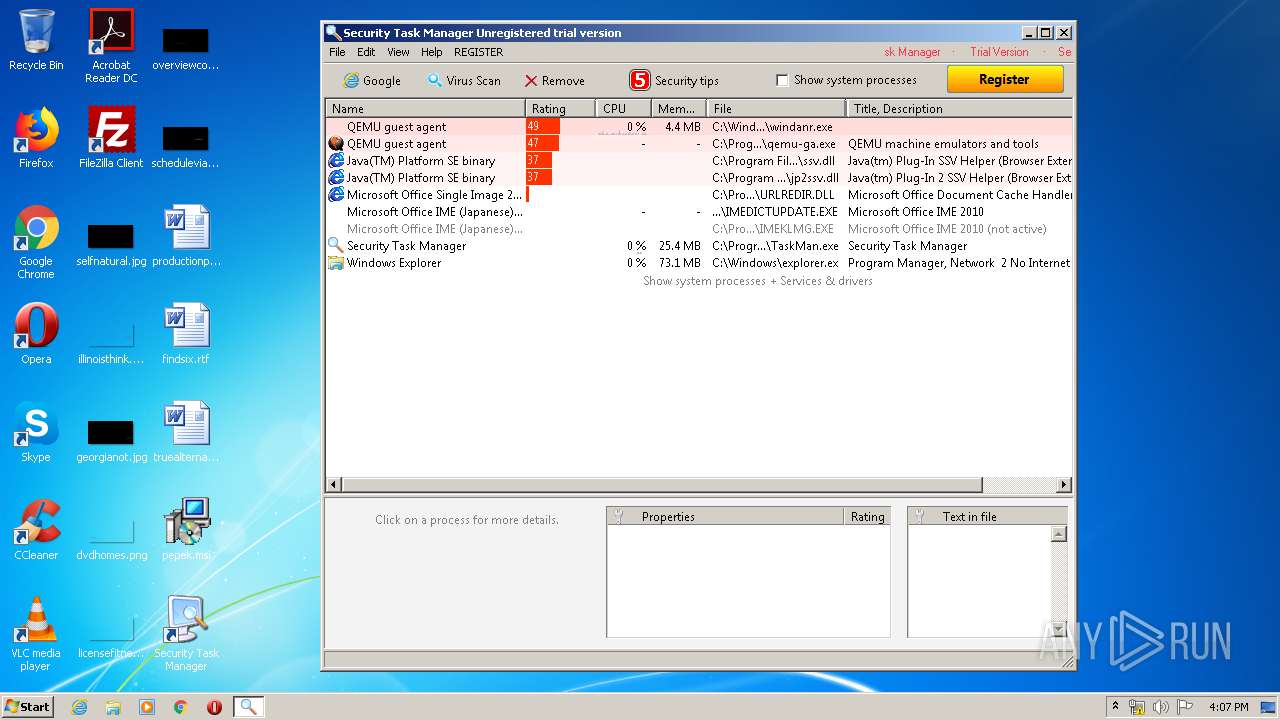
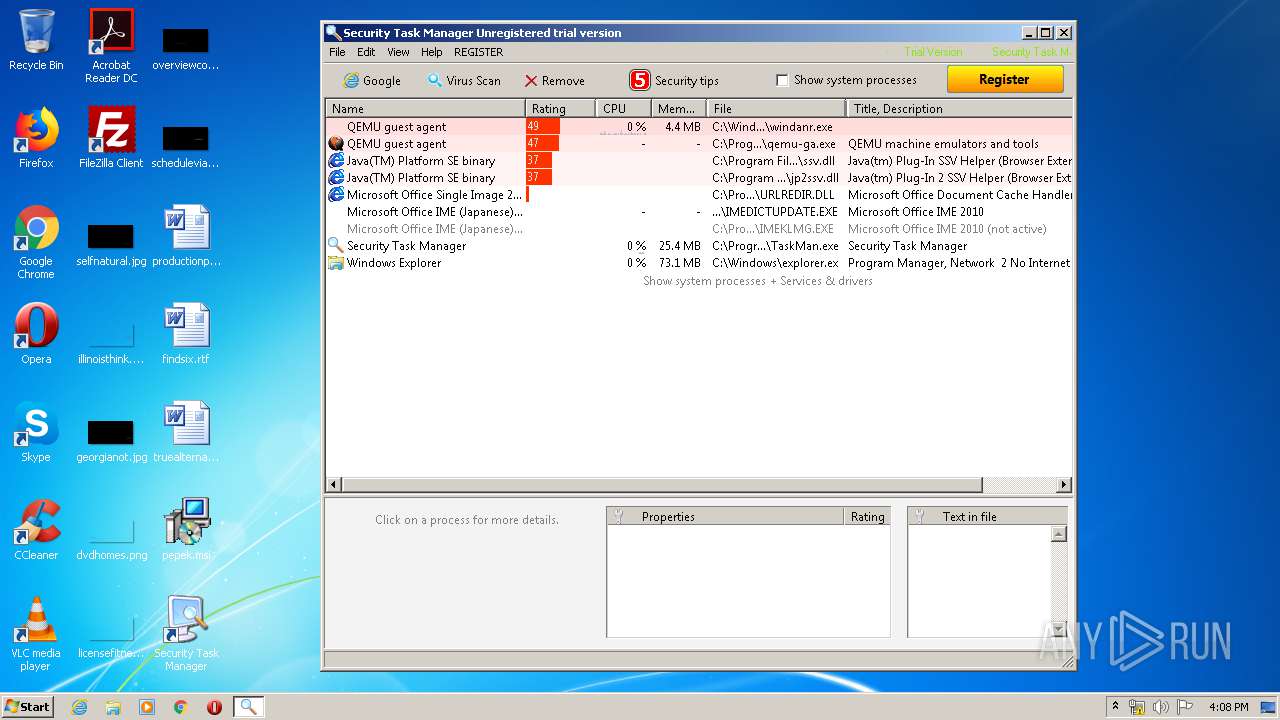
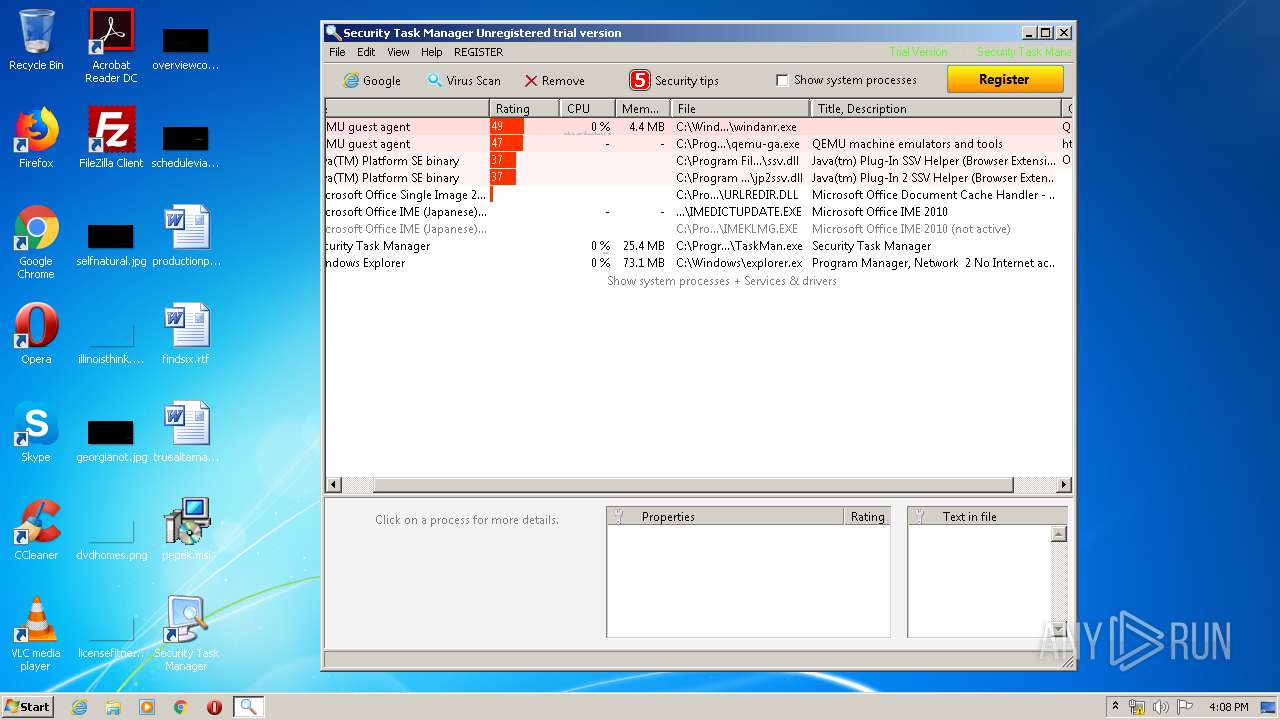
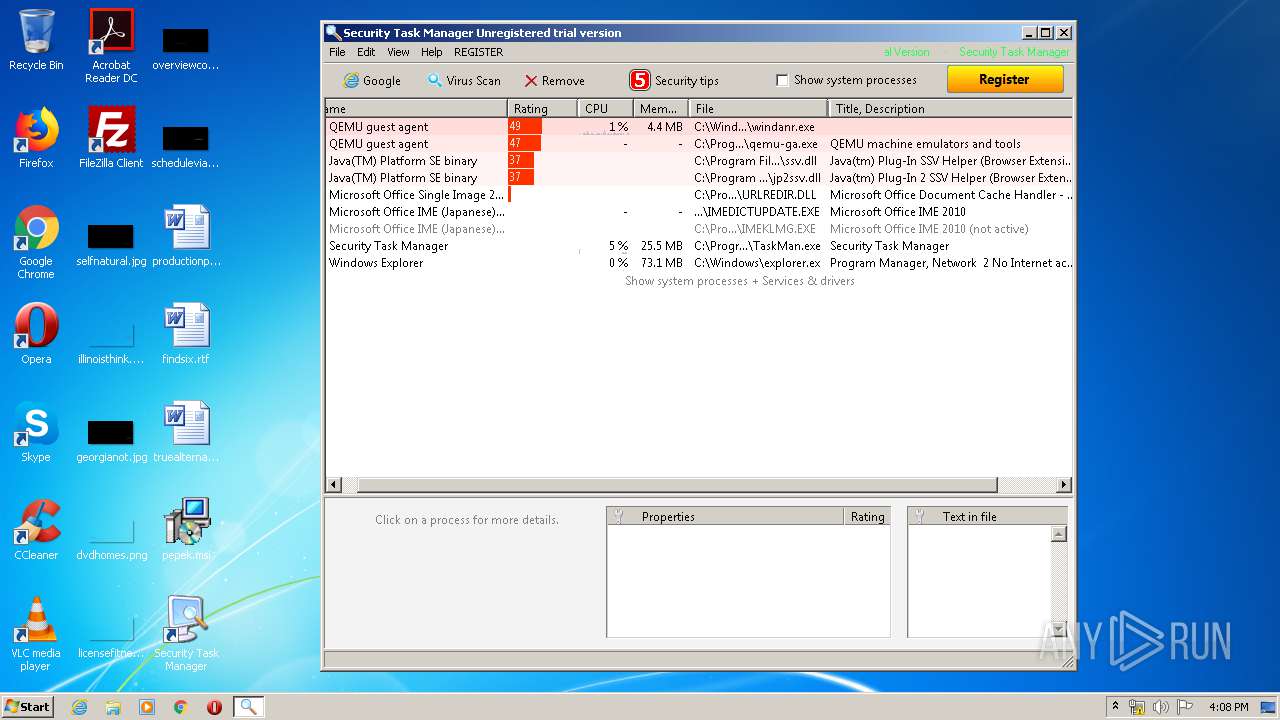
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\SecurityTaskManager_Setup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\SecurityTaskManager_Setup.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 652 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 680 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 984 | ".\setup.exe" | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\setup.exe | SecurityTaskManager_Setup.exe | ||||||||||||
User: admin Company: Neuber Software Integrity Level: HIGH Description: Setup program Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1016 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\Desktop\pepek.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1748 | C:\Windows\system32\MsiExec.exe -Embedding 4D5EB274C085B6E9F32218DCC02CA39F | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2628 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\Desktop\pepek.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3368 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\SecurityTaskManager_Setup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\SecurityTaskManager_Setup.exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
9 426
Read events
5 371
Write events
2 823
Delete events
1 232
Modification events
| (PID) Process: | (680) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: A8020000B49FF58E6300D601 | |||
| (PID) Process: | (680) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 605E8E3114A4BA02B61DA6FB03386E73185E163946B7083C2C2F9E21382B197D | |||
| (PID) Process: | (680) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1748) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | tqndfvenof |
Value: C:\Windows\System32\cmd.exe /k cd\ & cd C:\o64vondqz10hqjf64j3t465wj & c:\windows\system32\rundll32.exe uga640tfzgwyh8ntn1baoxy09.jpg e | |||
| (PID) Process: | (1748) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1748) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1748) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1748) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1748) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1748) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
20
Suspicious files
358
Text files
129
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 680 | msiexec.exe | C:\Windows\Installer\MSI6D39.tmp | — | |
MD5:— | SHA256:— | |||
| 680 | msiexec.exe | C:\Windows\Installer\MSI6DB7.tmp | — | |
MD5:— | SHA256:— | |||
| 680 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFC50D4BA41F7022BE.TMP | — | |
MD5:— | SHA256:— | |||
| 680 | msiexec.exe | C:\Windows\Installer\MSI6E64.tmp | — | |
MD5:— | SHA256:— | |||
| 680 | msiexec.exe | C:\Config.Msi\a66ca0.rbs | — | |
MD5:— | SHA256:— | |||
| 680 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFA34C09226E782977.TMP | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab7F2.tmp | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar7F3.tmp | — | |
MD5:— | SHA256:— | |||
| 1536 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\SecurityTaskManager_Setup[1].exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
6
DNS requests
6
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3892 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
1536 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3892 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3892 | iexplore.exe | 104.26.2.236:443 | www.neuber.com | Cloudflare Inc | US | unknown |
3892 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1536 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
module.servebeer.com |
| unknown |
www.neuber.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.servebeer .com |