| File name: | 2217 |
| Full analysis: | https://app.any.run/tasks/474e8d55-6335-482c-9219-4d9fa2b4e2e4 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 10:55:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 158B38F0E34E41C59B72BBCFF1AD04A3 |
| SHA1: | 5BCC81A0581394834C5B468CAF18F4FBCBE68C4E |
| SHA256: | 2217B88ED7FA8C7491F61FA8212D17B3E10B481366F9F717779DD245716CAE49 |
| SSDEEP: | 49152:HxbbTJcgaM1qZzIXFVjKE8sojZ+VJhtOuOYN2mqux0ktszsr+Rlm0:Rb3JcEqZsXFRLojZdu9Em7xPeICRlm0 |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2356)
- cmd.exe (PID: 1504)
Loads dropped or rewritten executable
- 2217.exe (PID: 3392)
- 2217.exe (PID: 3332)
- svchost.exe (PID: 664)
Application was dropped or rewritten from another process
- reap.exe (PID: 480)
Creates or modifies windows services
- reg.exe (PID: 3192)
Starts NET.EXE to view/change users group
- powershell.exe (PID: 252)
SUSPICIOUS
Executable content was dropped or overwritten
- 2217.exe (PID: 3392)
- powershell.exe (PID: 3696)
- powershell.exe (PID: 252)
Starts CMD.EXE for commands execution
- 2217.exe (PID: 3392)
- wscript.exe (PID: 2752)
- 2217.exe (PID: 3332)
- wscript.exe (PID: 2844)
- svchost.exe (PID: 664)
- powershell.exe (PID: 252)
Executes scripts
- cmd.exe (PID: 2324)
- cmd.exe (PID: 2424)
Creates files in the user directory
- powershell.exe (PID: 3696)
- powershell.exe (PID: 252)
Executed via COM
- DllHost.exe (PID: 2900)
- DllHost.exe (PID: 3408)
Creates files in the Windows directory
- powershell.exe (PID: 252)
Uses ICACLS.EXE to modify access control list
- powershell.exe (PID: 252)
Uses REG.EXE to modify Windows registry
- powershell.exe (PID: 252)
INFO
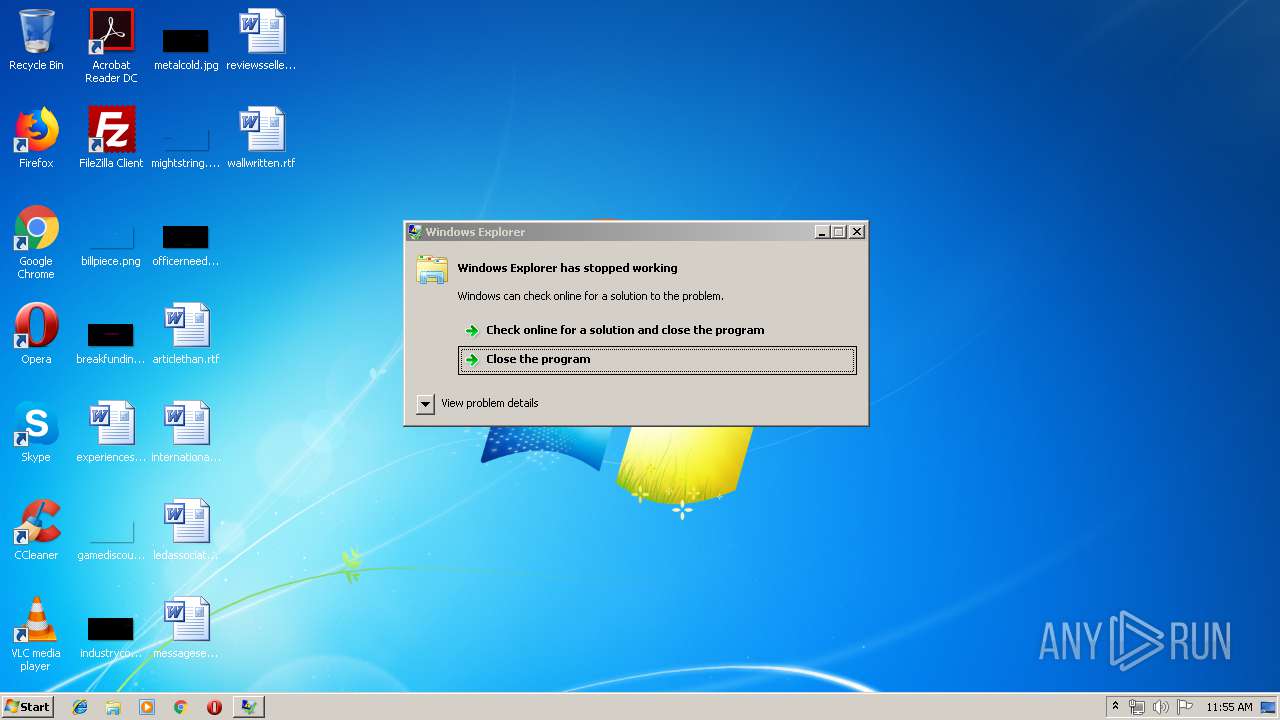
Application was crashed
- reap.exe (PID: 480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:32+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3328 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.1 |
| ProductVersionNumber: | 2.0.0.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | portable |
| CompanyName: | portable company |
| FileDescription: | portable Application |
| FileVersion: | 2.0.0.1 |
| LegalCopyright: | Copyright portable company |
| LegalTrademarks: | portable is a trademark of portable company |
| ProductName: | portable |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:32 |
| Detected languages: |
|
| Comments: | portable |
| CompanyName: | portable company |
| FileDescription: | portable Application |
| FileVersion: | 2.0.0.1 |
| LegalCopyright: | Copyright portable company |
| LegalTrademarks: | portable is a trademark of portable company |
| ProductName: | portable |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006077 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40386 |
.rdata | 0x00008000 | 0x00001250 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04481 |
.data | 0x0000A000 | 0x0001A838 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.22445 |
.ndata | 0x00025000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002E000 | 0x000112B8 | 0x00011400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.13236 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2992 | 830 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.98048 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
77
Monitored processes
26
Malicious processes
11
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | powershell.exe -ep bypass -f C:\Users\admin\AppData\Local\Temp\portable.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 480 | "C:\Users\admin\AppData\Local\Temp\reap.exe" 43 "C:\Users\admin\AppData\Local\Temp\2217.exe" | C:\Users\admin\AppData\Local\Temp\reap.exe | powershell.exe | ||||||||||||
User: admin Company: loihhs Integrity Level: MEDIUM Description: loihhs Exit code: 0 Version: 3.1.2 Modules
| |||||||||||||||
| 664 | C:\Windows\System32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1352 | "C:\Windows\system32\takeown.exe" /A /F rfxvmt.dll | C:\Windows\system32\takeown.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1504 | "C:\Windows\System32\cmd.exe" /c rename C:\Users\admin\AppData\Local\Temp\portable.txt portable.ps1& powershell.exe -ep bypass -f C:\Users\admin\AppData\Local\Temp\portable.ps1 | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1652 | "C:\Windows\system32\net.exe" localgroup Administrators "NT AUTHORITY\NETWORK SERVICE" /add | C:\Windows\system32\net.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1904 | "C:\Windows\system32\icacls.exe" rfxvmt.dll /grant "NT AUTHORITY\SYSTEM:RX" | C:\Windows\system32\icacls.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2324 | "cmd.exe" /c wscript C:\Users\admin\AppData\Local\Temp\portable.vbs | C:\Windows\system32\cmd.exe | — | 2217.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2356 | "C:\Windows\System32\cmd.exe" /c rename C:\Users\admin\AppData\Local\Temp\portable.txt portable.ps1& powershell.exe -ep bypass -f C:\Users\admin\AppData\Local\Temp\portable.ps1 | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2424 | "cmd.exe" /c wscript C:\Users\admin\AppData\Local\Temp\portable.vbs | C:\Windows\system32\cmd.exe | — | 2217.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 589
Read events
1 461
Write events
128
Delete events
0
Modification events
| (PID) Process: | (2752) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2752) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3696) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3696) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3696) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3408) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3408) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2900) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ICM\Calibration |
| Operation: | write | Name: | DisplayCalibrator |
Value: C:\Users\admin\AppData\Local\Temp\2217.exe | |||
| (PID) Process: | (2844) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2844) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
5
Suspicious files
4
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3392 | 2217.exe | C:\Users\admin\AppData\Local\Temp\nsr4182.tmp | — | |
MD5:— | SHA256:— | |||
| 3696 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\GVQDPVCESHVWCX42EN2I.temp | — | |
MD5:— | SHA256:— | |||
| 3332 | 2217.exe | C:\Users\admin\AppData\Local\Temp\nsw4DB8.tmp\System.dll | — | |
MD5:— | SHA256:— | |||
| 3332 | 2217.exe | C:\Users\admin\AppData\Local\Temp\nsq4CFB.tmp | — | |
MD5:— | SHA256:— | |||
| 252 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8MV6B7TMVLM3YZFJ5TVS.temp | — | |
MD5:— | SHA256:— | |||
| 3392 | 2217.exe | C:\Users\admin\AppData\Local\Temp\portable.txt | text | |
MD5:— | SHA256:— | |||
| 3392 | 2217.exe | C:\Users\admin\AppData\Local\Temp\log_4043.txt | text | |
MD5:— | SHA256:— | |||
| 2356 | cmd.exe | C:\Users\admin\AppData\Local\Temp\portable.ps1 | text | |
MD5:— | SHA256:— | |||
| 3392 | 2217.exe | C:\Users\admin\AppData\Local\Temp\readme_88755.txt | text | |
MD5:— | SHA256:— | |||
| 3392 | 2217.exe | C:\Users\admin\AppData\Local\Temp\terminal.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
6
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3100 | powershell.exe | GET | 301 | 151.101.2.219:80 | http://www.speedtest.net/speedtest-config.php | US | — | — | whitelisted |
3100 | powershell.exe | GET | 301 | 151.101.2.219:80 | http://www.speedtest.net/speedtest-servers.php | US | — | — | whitelisted |
3100 | powershell.exe | GET | — | 200.108.52.2:5060 | http://speedmovil1.movistar.com.pa:5060/speedtest/random2000x2000.jpg | PA | — | — | unknown |
3100 | powershell.exe | GET | 200 | 151.101.2.219:80 | http://c.speedtest.net/speedtest-servers-static.php | US | xml | 1.88 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3100 | powershell.exe | 151.101.0.133:443 | raw.githubusercontent.com | Fastly | US | malicious |
3100 | powershell.exe | 151.101.2.219:80 | www.speedtest.net | Fastly | US | suspicious |
— | — | 151.101.2.219:443 | www.speedtest.net | Fastly | US | suspicious |
— | — | 151.101.2.219:80 | www.speedtest.net | Fastly | US | suspicious |
3100 | powershell.exe | 200.108.52.2:5060 | speedmovil1.movistar.com.pa | Telefonica Moviles Panama S.A. | PA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
raw.githubusercontent.com |
| shared |
www.speedtest.net |
| whitelisted |
c.speedtest.net |
| whitelisted |
speedmovil1.movistar.com.pa |
| unknown |
Threats
1 ETPRO signatures available at the full report