| File name: | 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe |
| Full analysis: | https://app.any.run/tasks/922abde8-ff13-4d84-9ec0-a6f3c7c0c412 |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2025, 06:00:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | A543BDFDDD783EA0A4D592B914EDC667 |
| SHA1: | FEB59CB4FFB4DEC87D61A05D3651F48E5160959E |
| SHA256: | 21F8191117DF5F58D24EA288D35F2D2225B0B1FE90A98C1C0AA1536CB22FDF2C |
| SSDEEP: | 3072:bgJI3jRVNgsdR1NCD1AU88tEOt8YzX3aRMAMMCeSqgXAsNKSqo:cW3FVNgsdR1NCD1AU8dYj3aRMPMCeSqS |
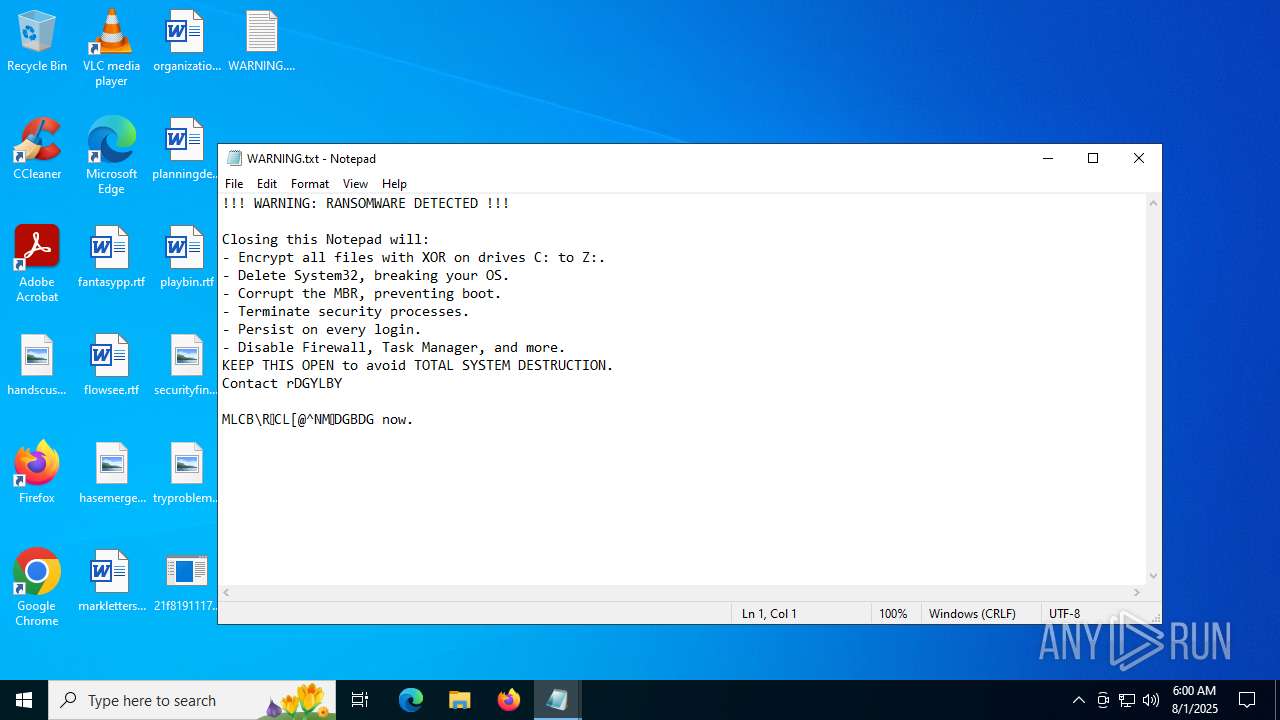
MALICIOUS
Changes the autorun value in the registry
- 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe (PID: 5764)
- 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe (PID: 1156)
SUSPICIOUS
Starts CMD.EXE for commands execution
- 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe (PID: 5764)
- 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe (PID: 1156)
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 6948)
- cmd.exe (PID: 5768)
- cmd.exe (PID: 3740)
- cmd.exe (PID: 4168)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2348)
- cmd.exe (PID: 2632)
Executes application which crashes
- 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe (PID: 5764)
- 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe (PID: 1156)
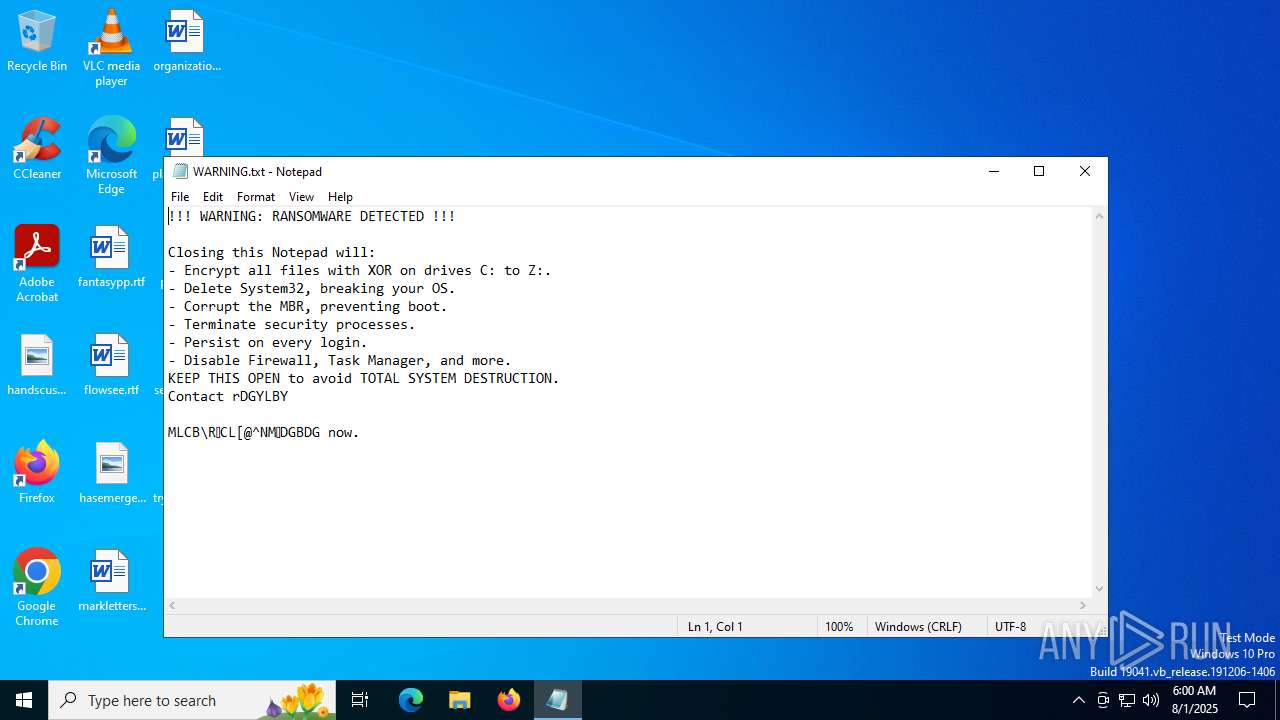
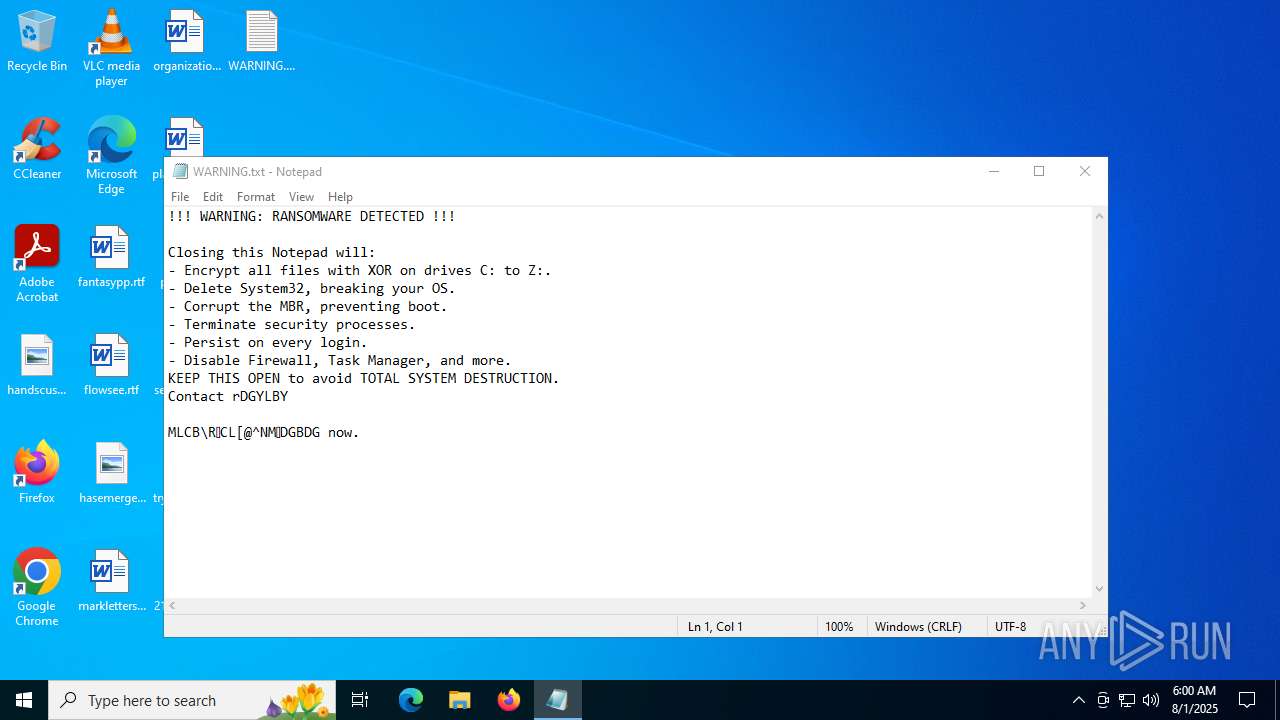
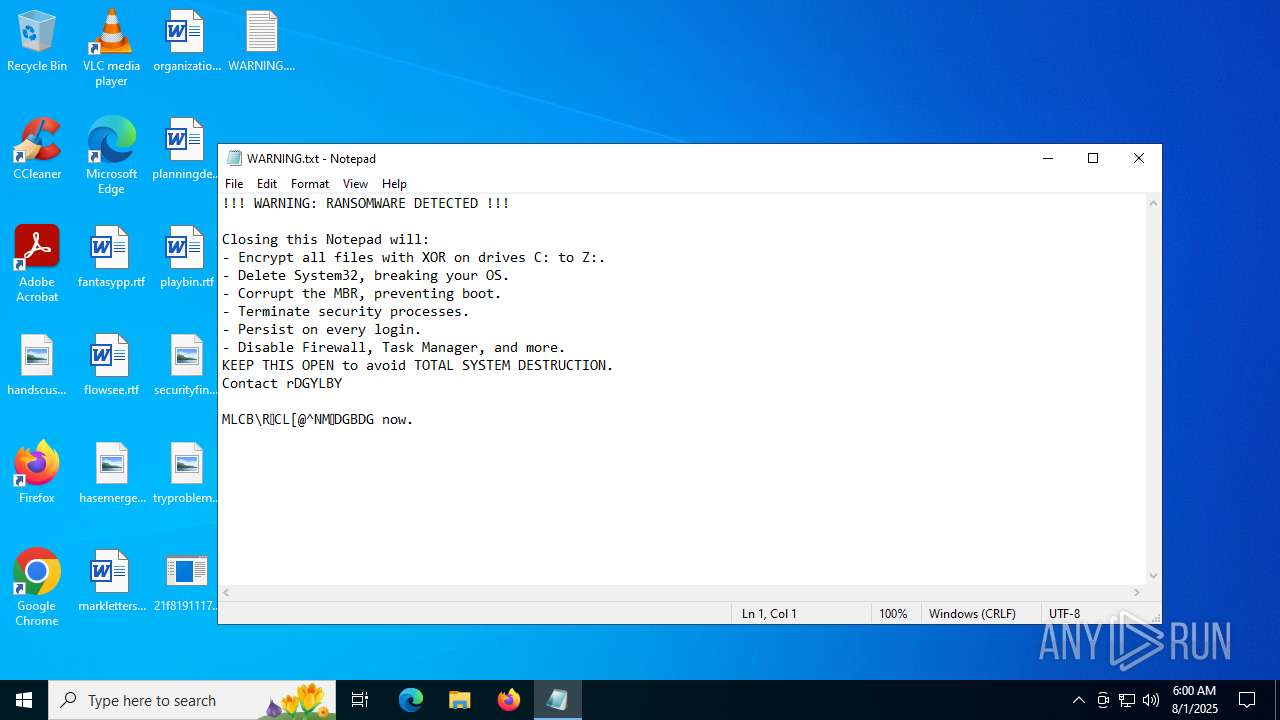
There is functionality for taking screenshot (YARA)
- notepad.exe (PID: 4644)
INFO
Checks supported languages
- 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe (PID: 5764)
- 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe (PID: 1156)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 1192)
- WMIC.exe (PID: 640)
- notepad.exe (PID: 4644)
- WMIC.exe (PID: 1872)
- WMIC.exe (PID: 3636)
- notepad.exe (PID: 5988)
Launching a file from a Registry key
- 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe (PID: 5764)
- 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe (PID: 1156)
Checks proxy server information
- WerFault.exe (PID: 1668)
- WerFault.exe (PID: 3400)
- slui.exe (PID: 1468)
Creates files or folders in the user directory
- WerFault.exe (PID: 1668)
- WerFault.exe (PID: 3400)
Reads the software policy settings
- WerFault.exe (PID: 1668)
- WerFault.exe (PID: 3400)
- slui.exe (PID: 1468)
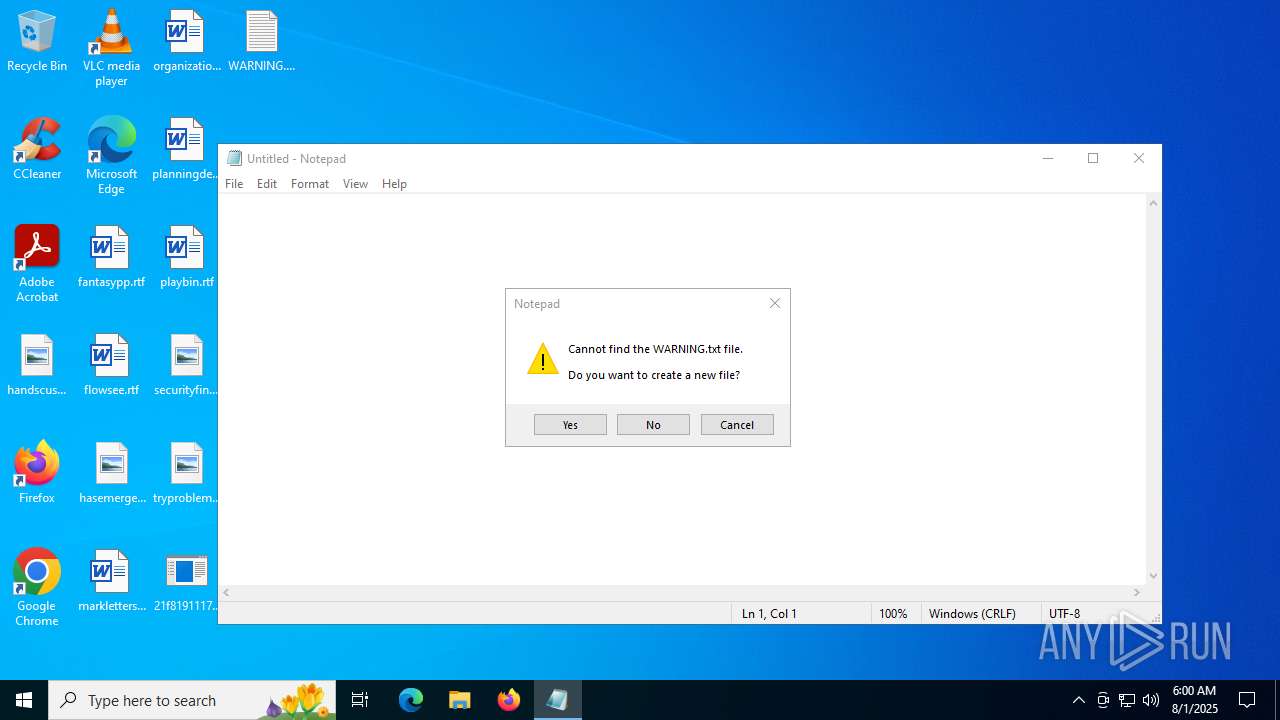
Manual execution by a user
- notepad.exe (PID: 5988)
- 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe (PID: 1156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:07:31 19:57:27+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.44 |
| CodeSize: | 69120 |
| InitializedDataSize: | 46080 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x10528 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
167
Monitored processes
28
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | wmic bios get serialnumber | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | C:\Users\admin\Desktop\21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe | C:\Users\admin\Desktop\21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226505 Modules
| |||||||||||||||
| 1192 | wmic bios get serialnumber | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1468 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1508 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1668 | C:\WINDOWS\system32\WerFault.exe -u -p 5764 -s 728 | C:\Windows\System32\WerFault.exe | 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1872 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1872 | wmic bios get serialnumber | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2348 | cmd.exe /c reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\System32\cmd.exe | — | 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2632 | cmd.exe /c reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\System32\cmd.exe | — | 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 499
Read events
8 493
Write events
6
Delete events
0
Modification events
| (PID) Process: | (5764) 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | SystemUpdate |
Value: C:\Users\admin\Desktop\21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe | |||
| (PID) Process: | (4644) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 210 | |||
| (PID) Process: | (4644) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 143 | |||
| (PID) Process: | (4644) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (4644) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 489 | |||
| (PID) Process: | (1156) 21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | SystemUpdate |
Value: C:\Users\admin\Desktop\21f8191117df5f58d24ea288d35f2d2225b0b1fe90a98c1c0aa1536cb22fdf2c.exe | |||
Executable files
0
Suspicious files
3
Text files
4
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3400 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_21f8191117df5f58_eaf75f2dc2ed3f12ac513fee9dd9f662a1f7e_46898e9a_59b0c77e-59ac-4827-8472-90925c0320f0\Report.wer | — | |
MD5:— | SHA256:— | |||
| 1668 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_21f8191117df5f58_eaf75f2dc2ed3f12ac513fee9dd9f662a1f7e_46898e9a_bbf30c69-a0ab-446e-94b1-50b41473b59c\Report.wer | — | |
MD5:— | SHA256:— | |||
| 1668 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERCDF9.tmp.dmp | dmp | |
MD5:4FA674BE365BA99ADD31369900501B57 | SHA256:D9754DB7E47B218B83D8EE8041C82DAC22C41C2299633DA264008BC3074BA5AD | |||
| 1668 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | der | |
MD5:D310523737A0D4D05066857AC157F458 | SHA256:0A0520D498306689AFA3CAC09ACE82E09229108FC9FABA5A906291D077004484 | |||
| 1668 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERCE78.tmp.xml | xml | |
MD5:5103FCA6A3CEAF808C72FC099364439C | SHA256:C8F00CC801A02DD3D989AC9A60345D520CE84EA5CFBAC46C8B67AA48AF877A48 | |||
| 1668 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:CAAF51CB8FF699D5670CA755BE2EED6B | SHA256:A99033AD7570076AA1082D332C5F414C11463770DC564220ED40A1351E31635D | |||
| 1668 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:4B6B626DB5156E82C87909A62B1DE87A | SHA256:353BA0AAE33C8A7C621139CE213359D8857745F163E394AEFA1882B2A7EA4D48 | |||
| 1668 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERCE58.tmp.WERInternalMetadata.xml | xml | |
MD5:6F75CE1557006CBBB37397299A349A0E | SHA256:2B38441EC62CCF06D2220AF941A8B55DE0F5E80C9BB869439FBADAF5A7F3473A | |||
| 3400 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER4240.tmp.WERInternalMetadata.xml | xml | |
MD5:4CE93501C70A13183045183E9914760C | SHA256:D0858354018ACC3F1F22710EDB5D87CEA45C2F2354905CE5EB0EDFCB2405EEF6 | |||
| 3400 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER41E1.tmp.dmp | dmp | |
MD5:E271DFD9690940014B60769F4DD1E97F | SHA256:F296F01BEF1F9F2669B74260CF61A3E8BC96051790349FA95828AA1990C81591 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
27
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1668 | WerFault.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1668 | WerFault.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
3944 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
5988 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
5988 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | DE | binary | 734 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5528 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1668 | WerFault.exe | 172.178.240.161:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | DE | whitelisted |
1668 | WerFault.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1668 | WerFault.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3944 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3944 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |