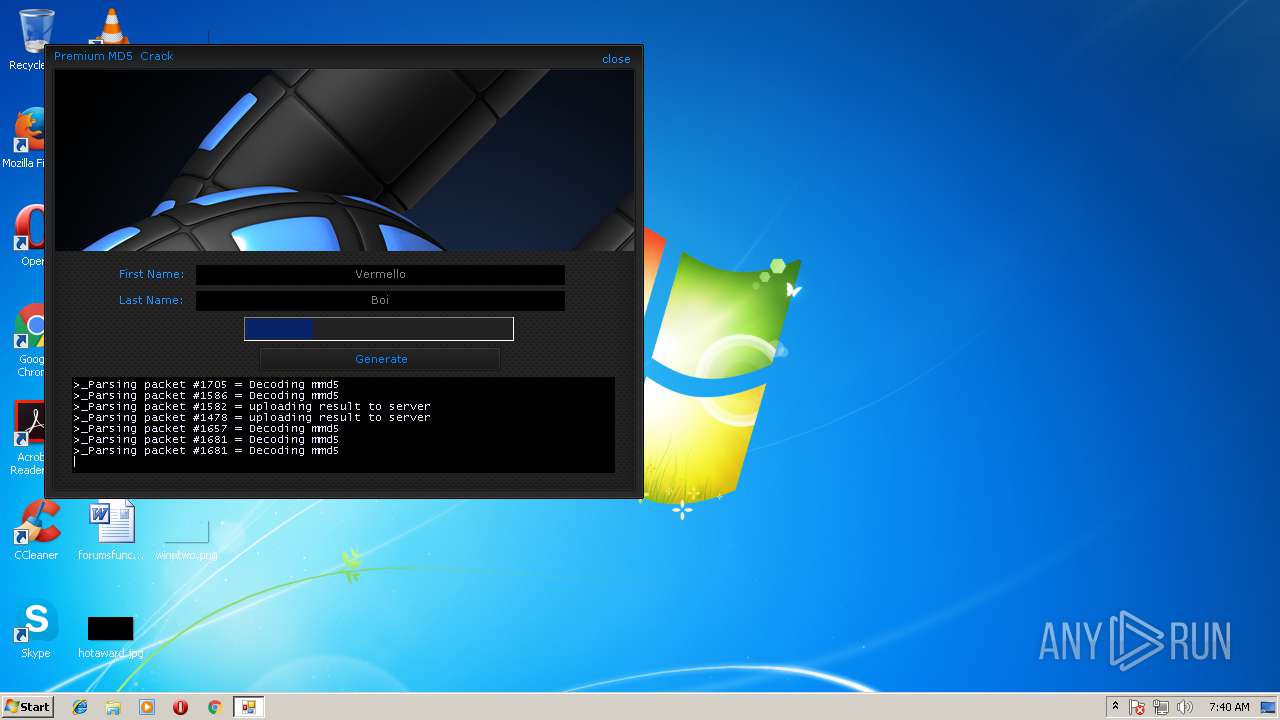
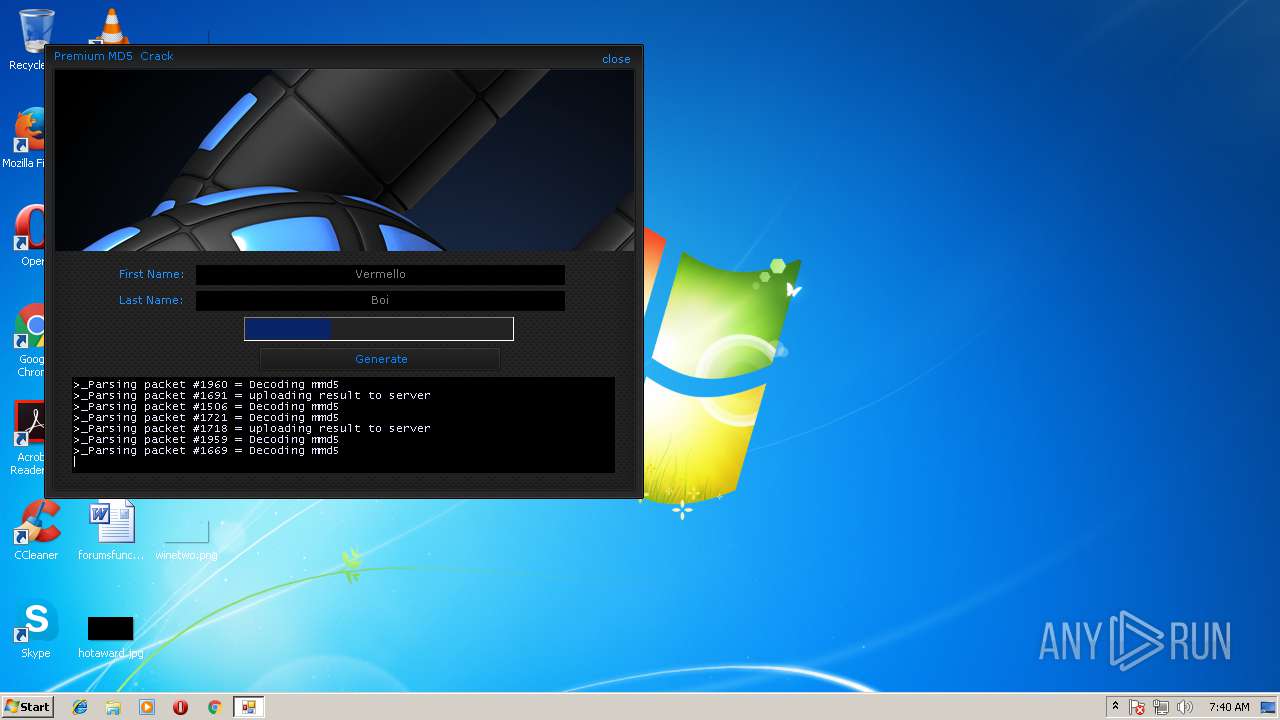
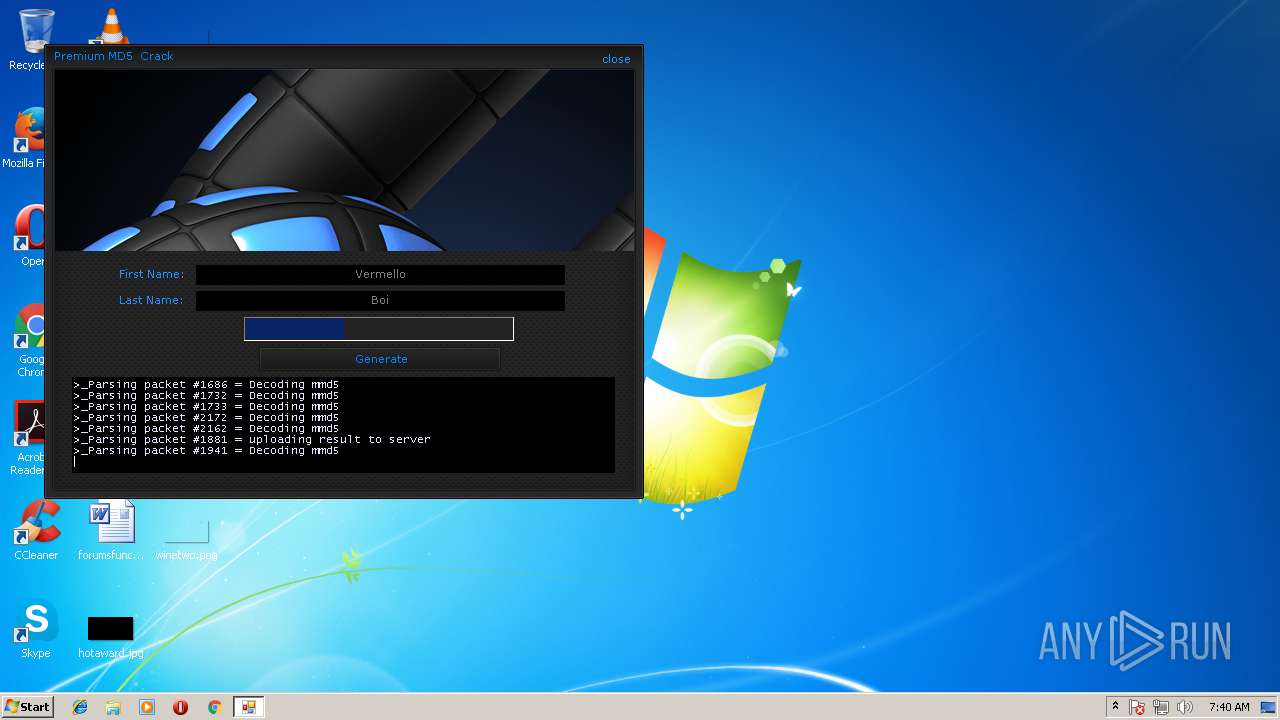
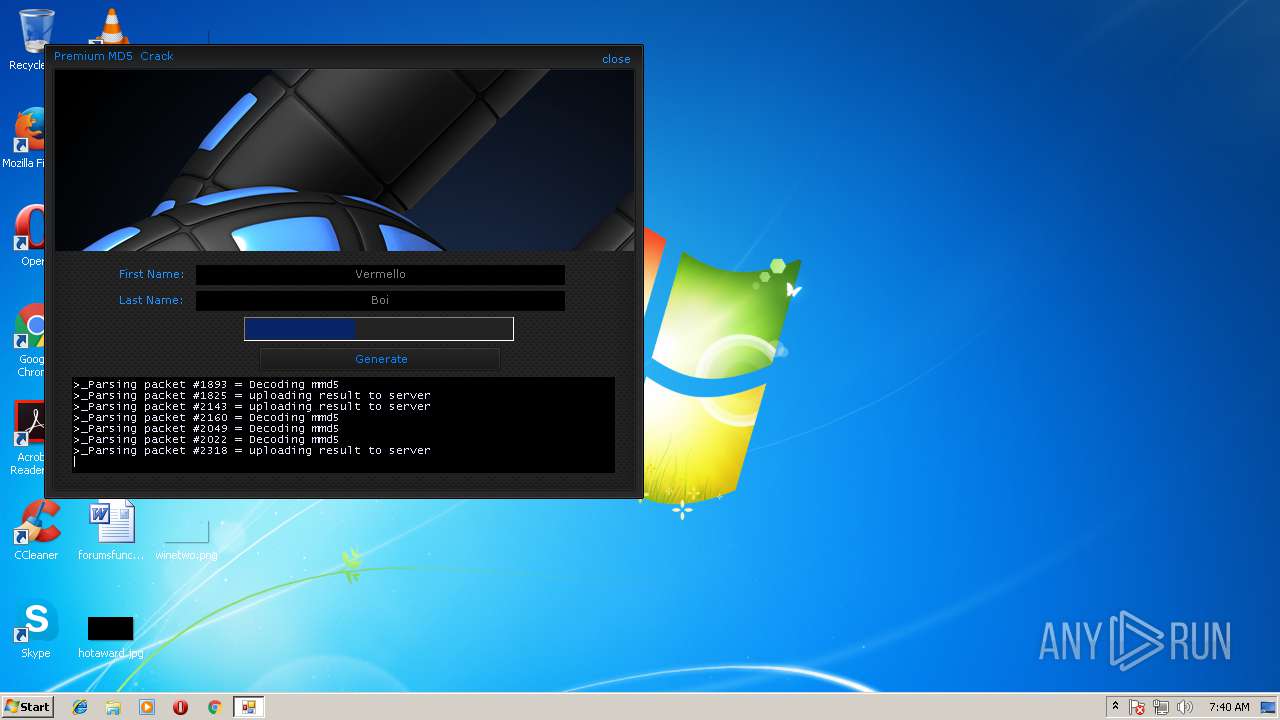
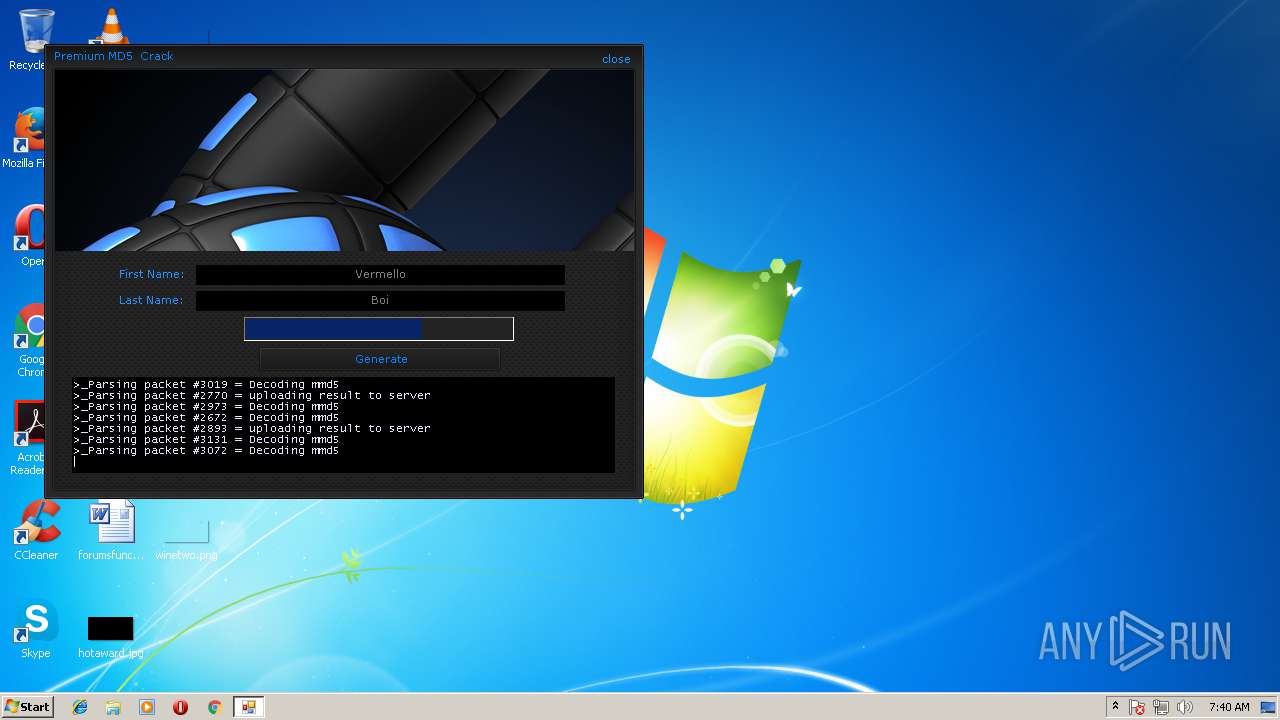
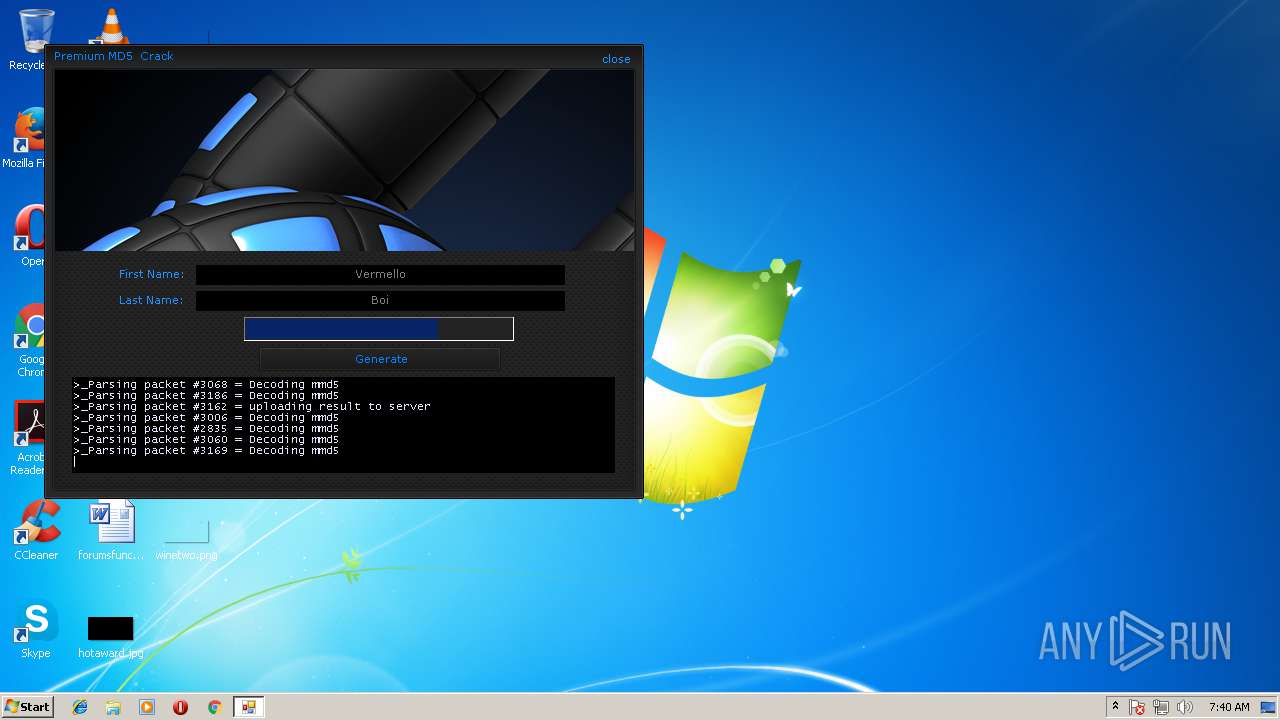
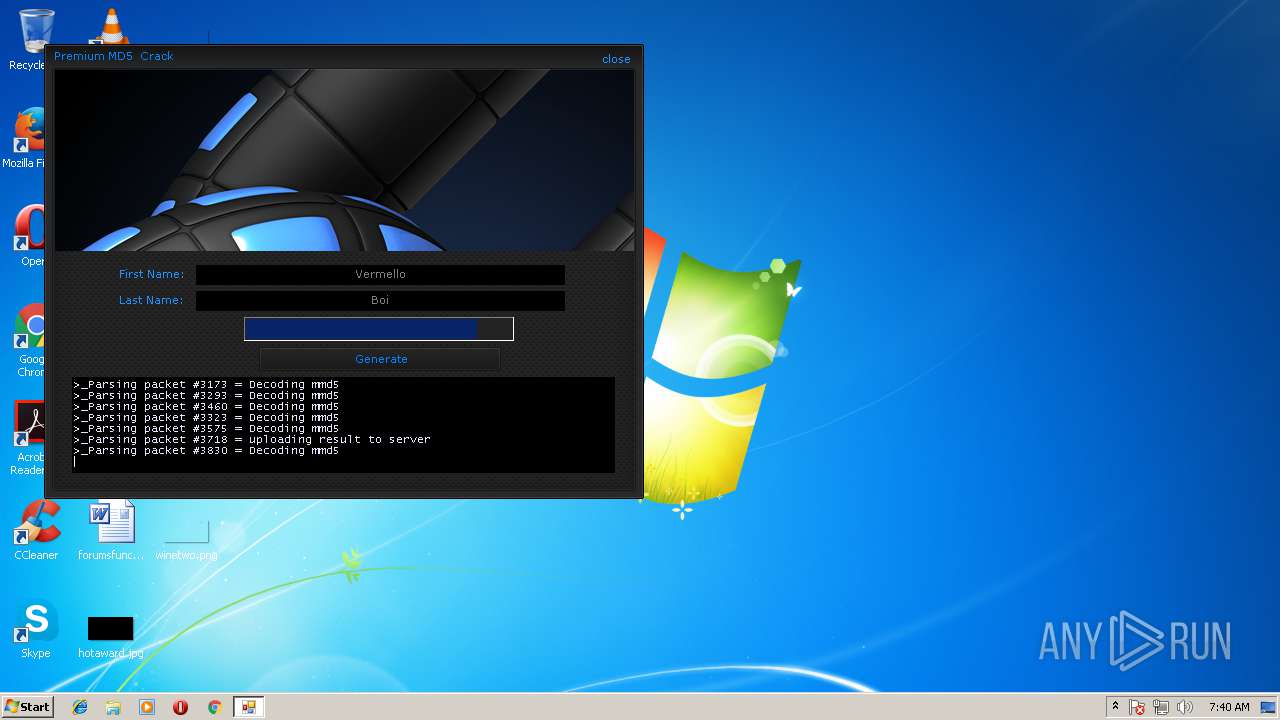
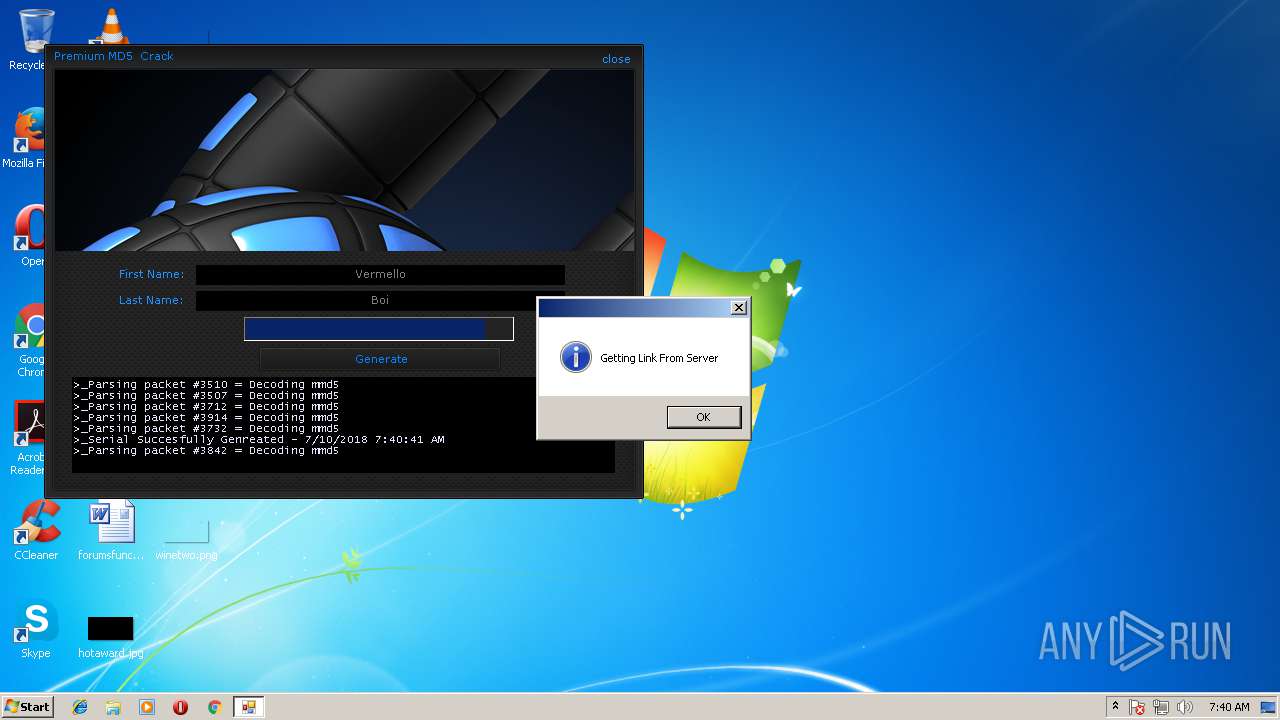
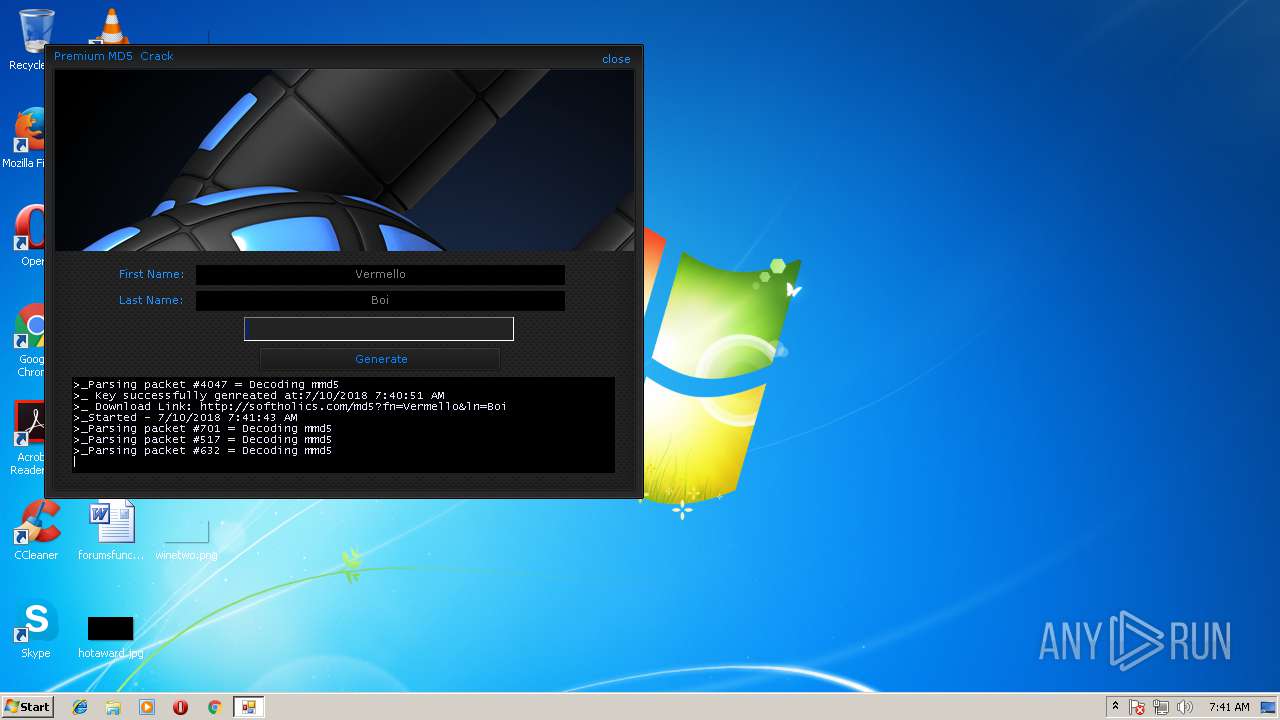
| File name: | md5crack.exe |
| Full analysis: | https://app.any.run/tasks/16e4af0a-2dac-401e-9560-0dd209b73ac0 |
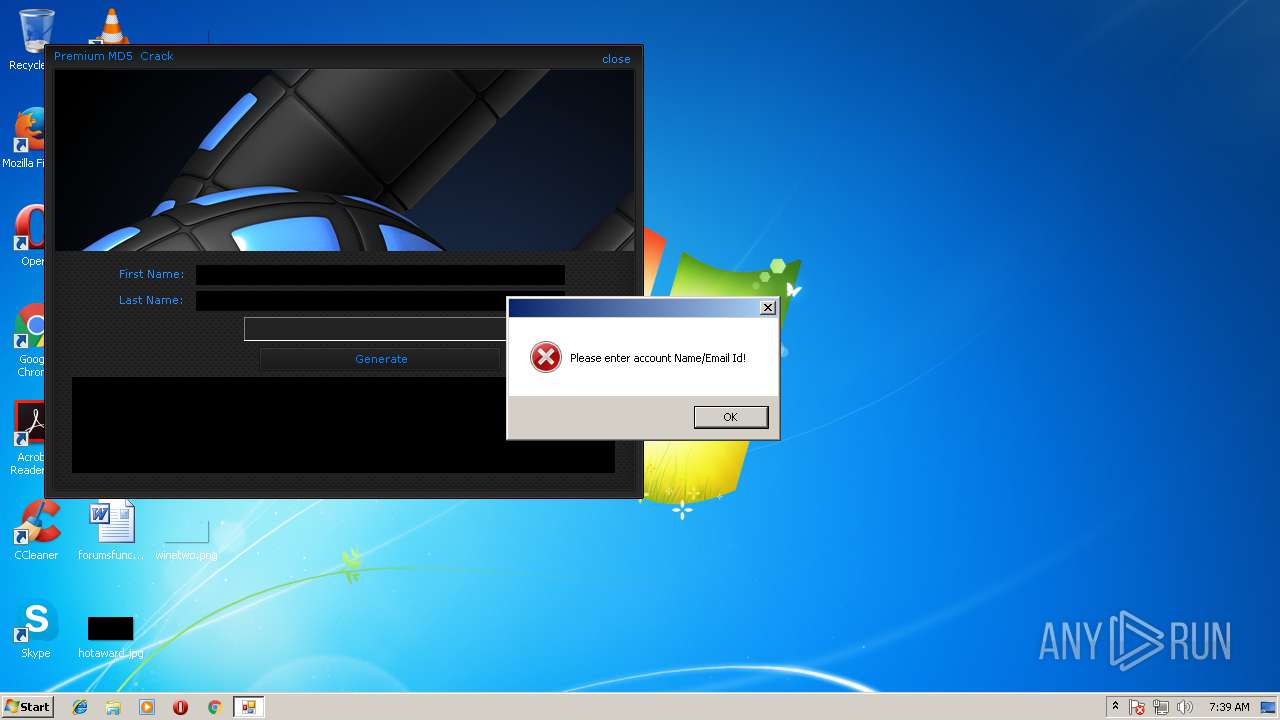
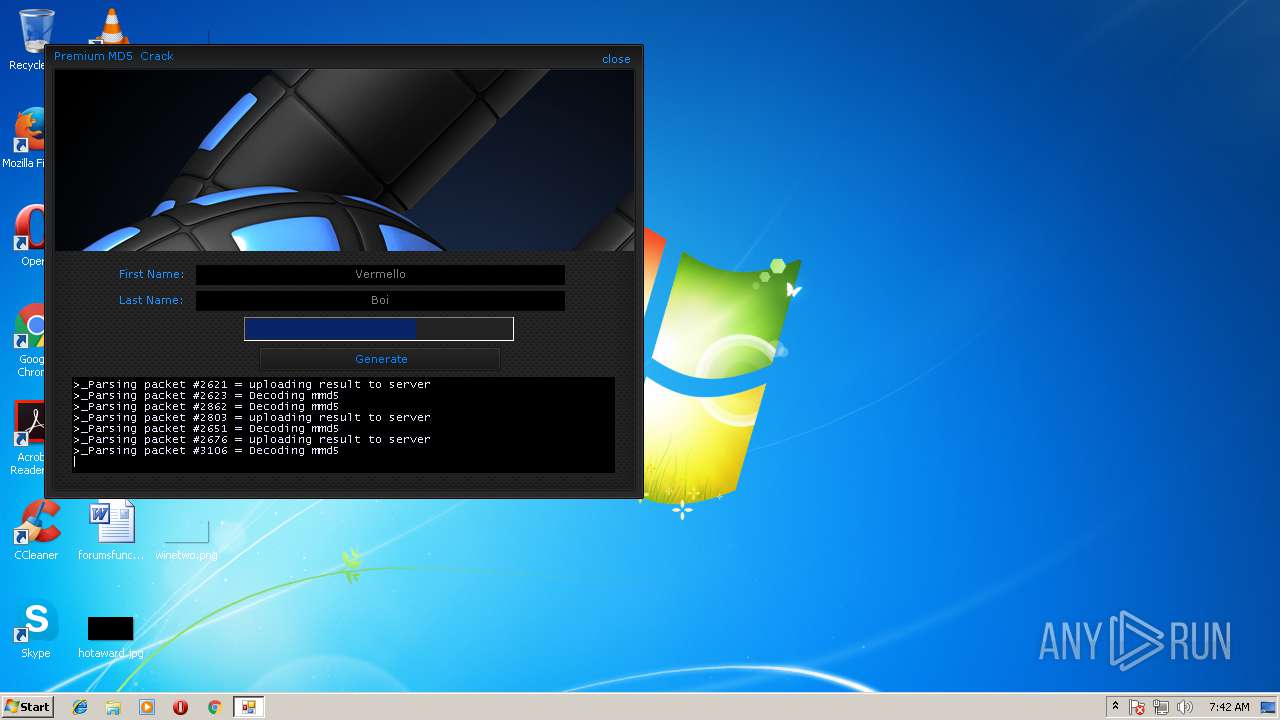
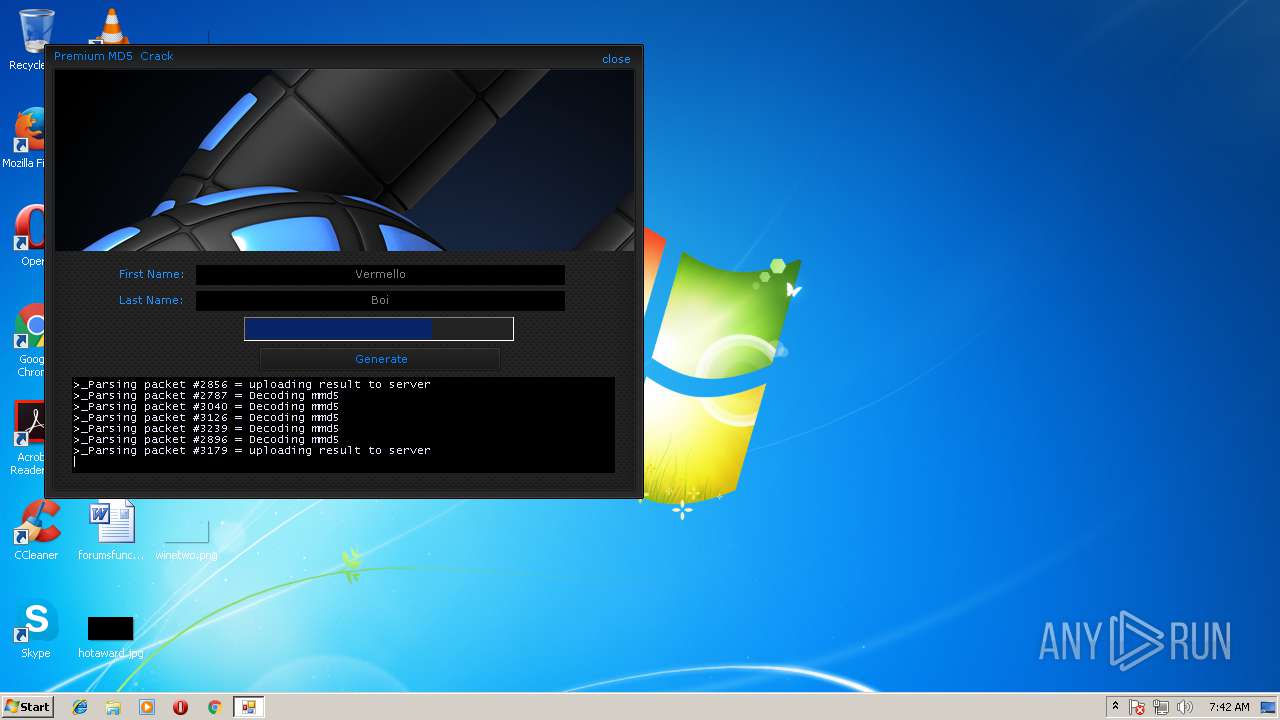
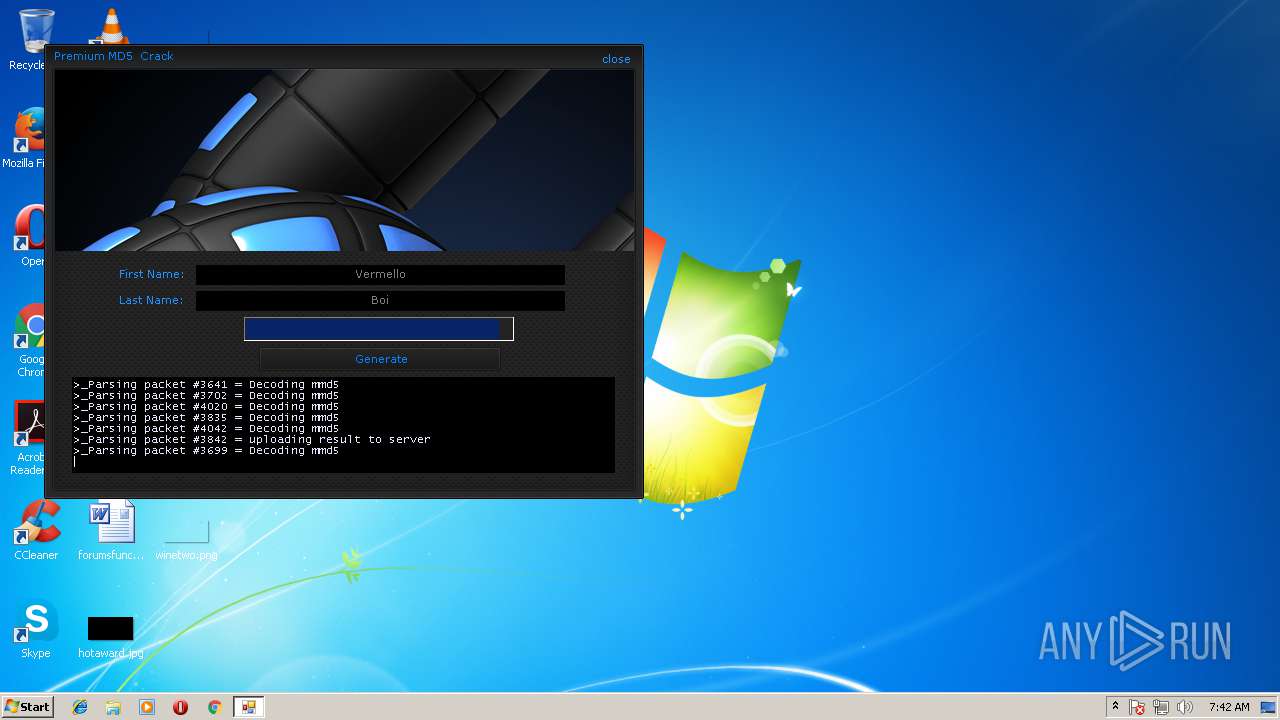
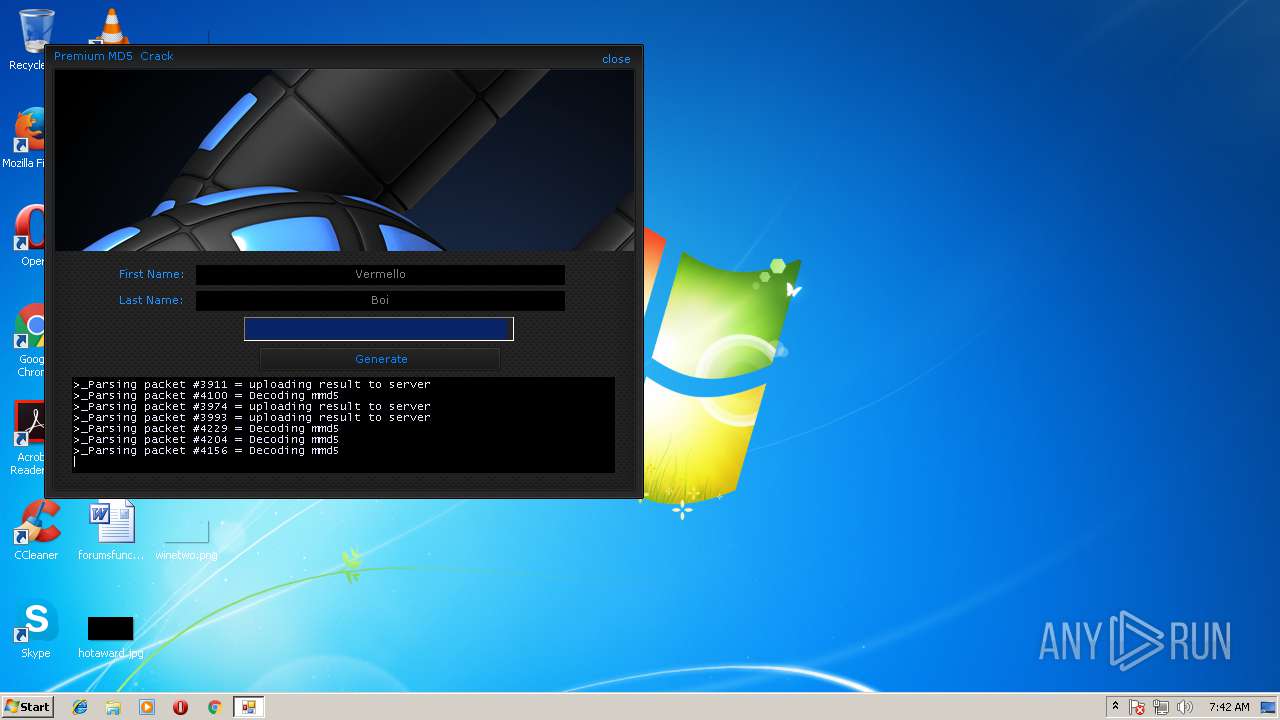
| Verdict: | Suspicious activity |
| Analysis date: | July 10, 2018, 06:39:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | EB37C7C84910DDB8D0F7FB185D742867 |
| SHA1: | D7E6D06DDBDF629339A5951AC1ECDB3AFE4AC388 |
| SHA256: | 21F7DB5D937CBCFF03FC0D23E021775F8B709DD814EC8B31B262A82A47904376 |
| SSDEEP: | 12288:UicZbFisWtHSf6CRZuVJhvye2x3g/6OA04D8mVtlqKClYAu8gg:VmhisWdbNvswiI4D8YCvg |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
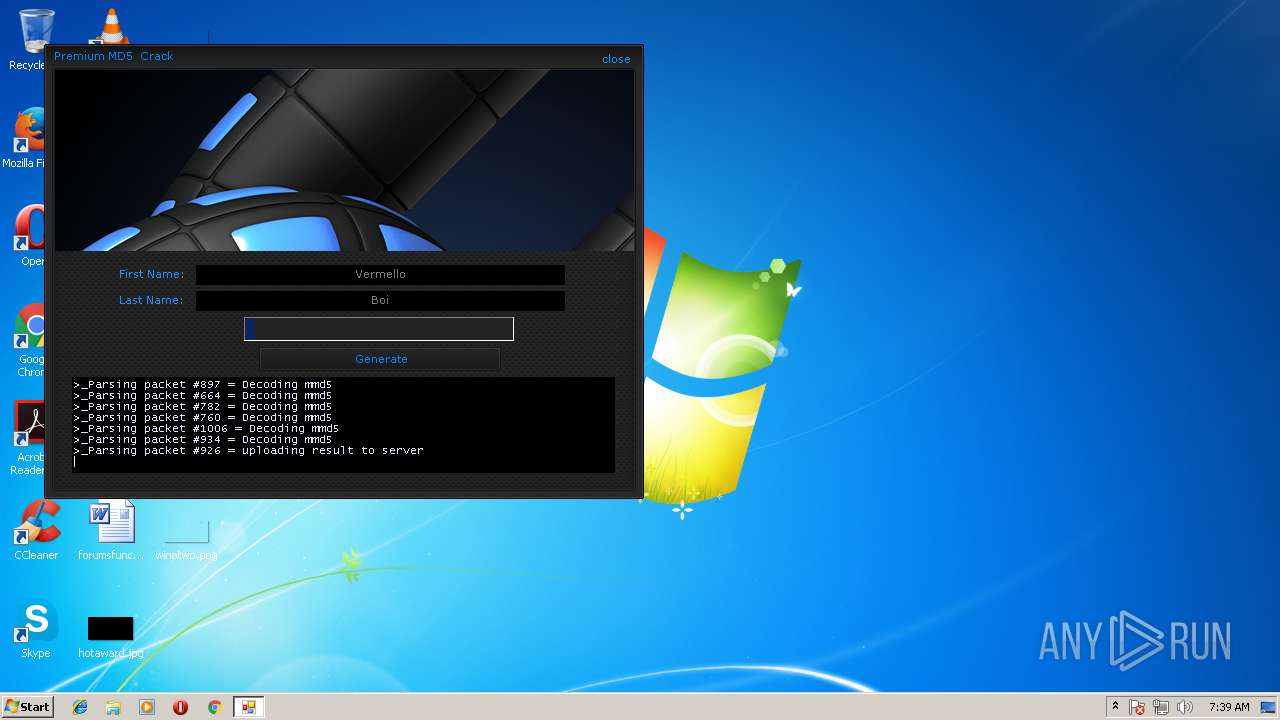
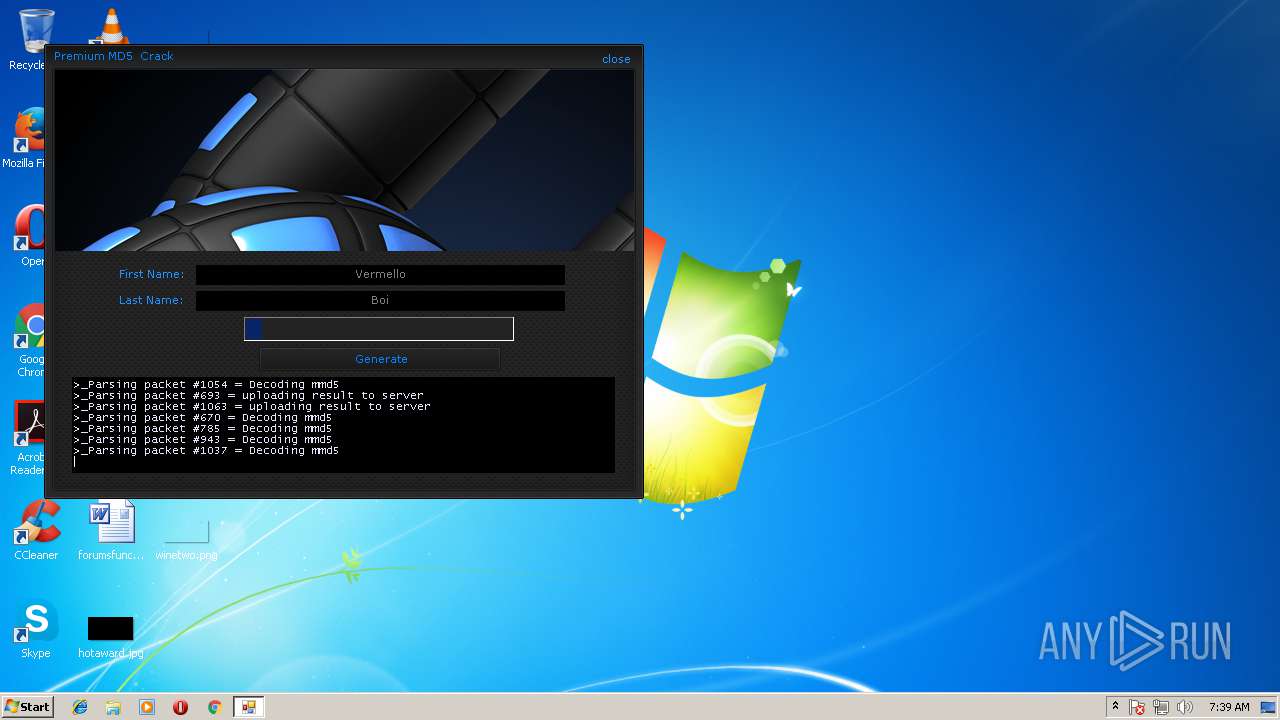
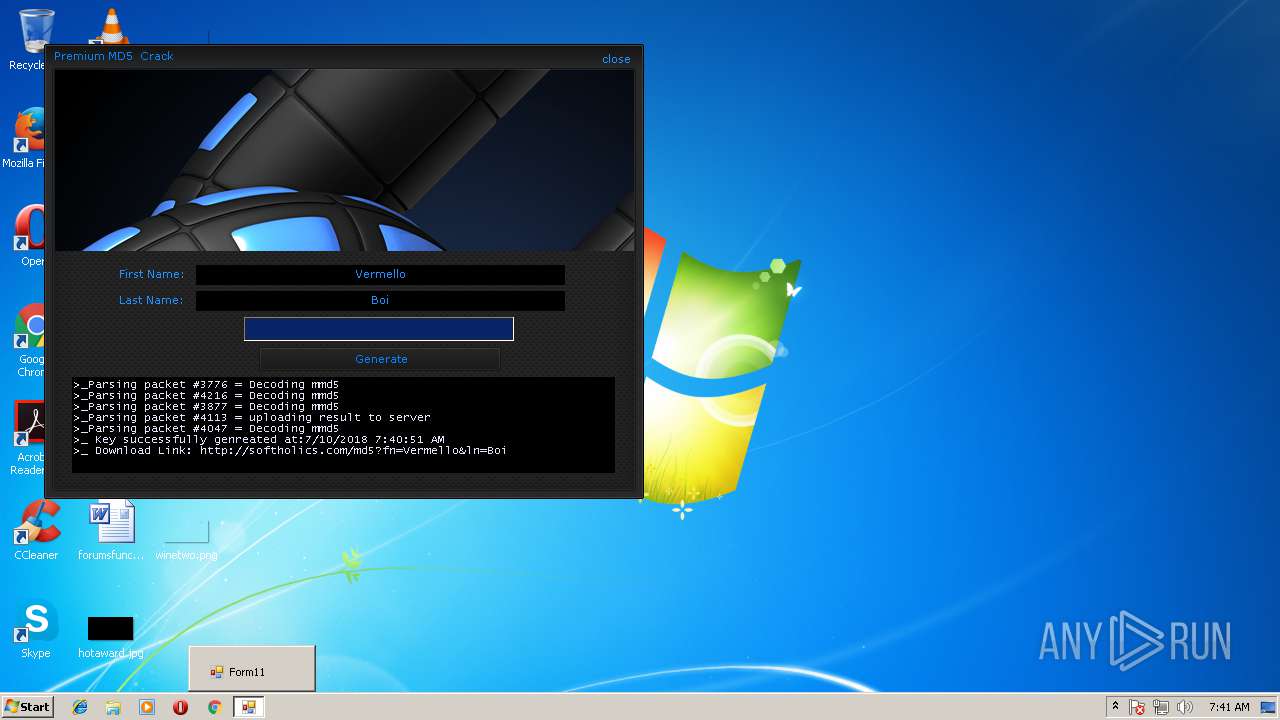
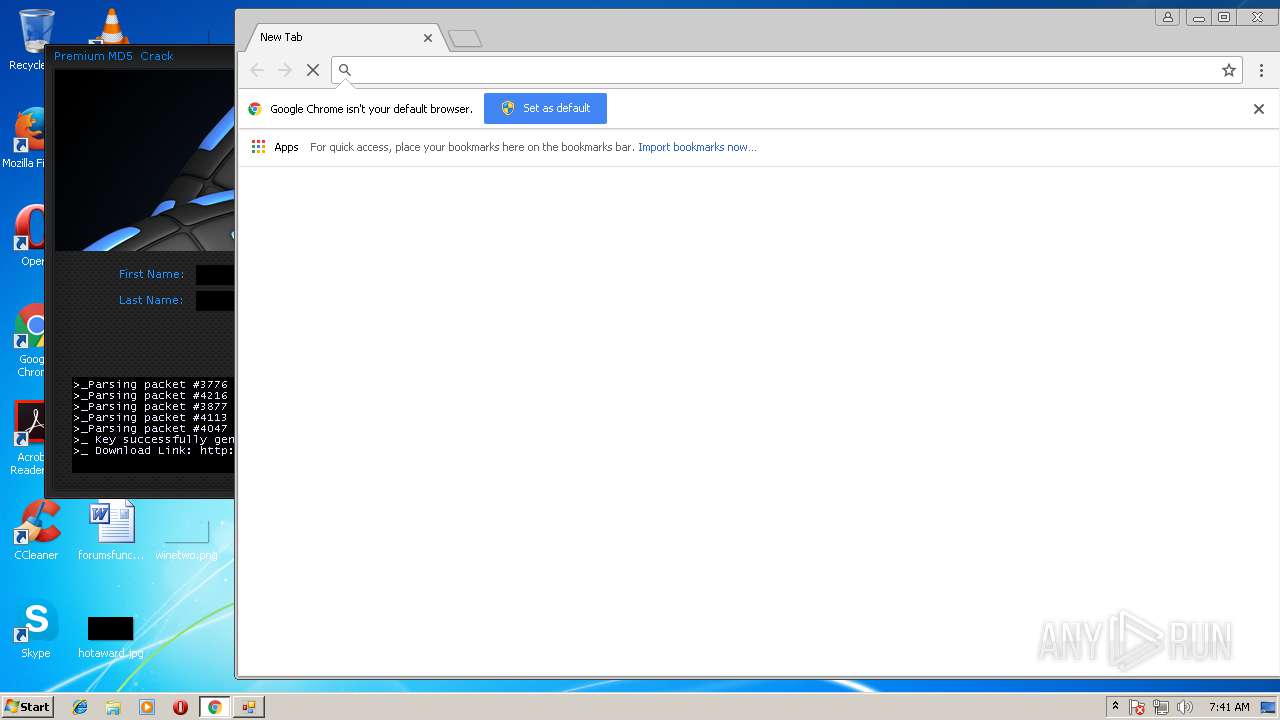
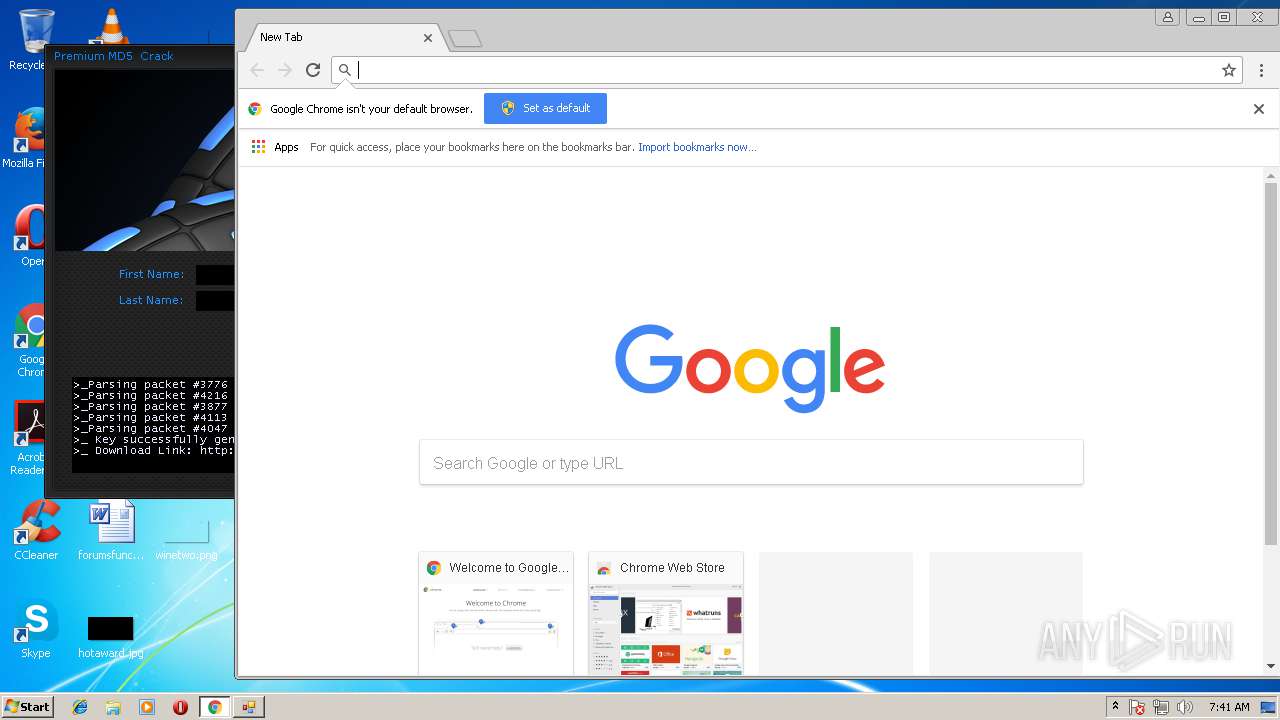
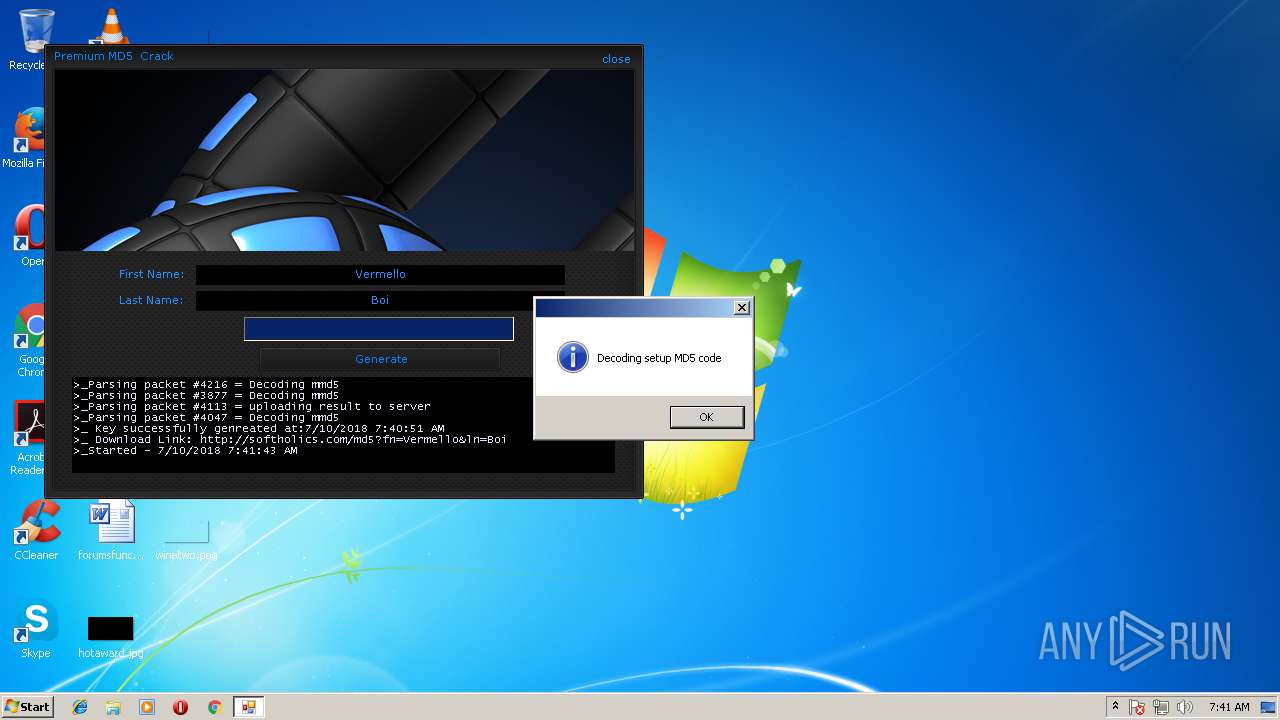
Application launched itself
- chrome.exe (PID: 2752)
Loads the Task Scheduler COM API
- software_reporter_tool.exe (PID: 2724)
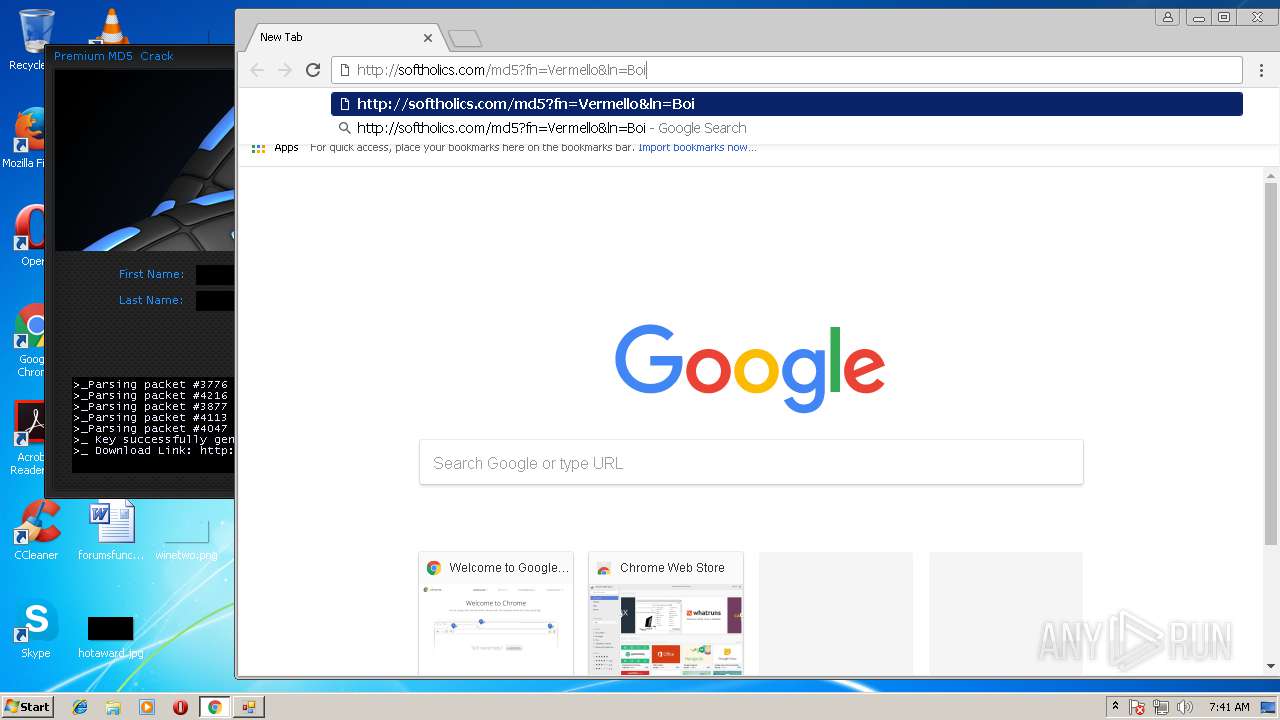
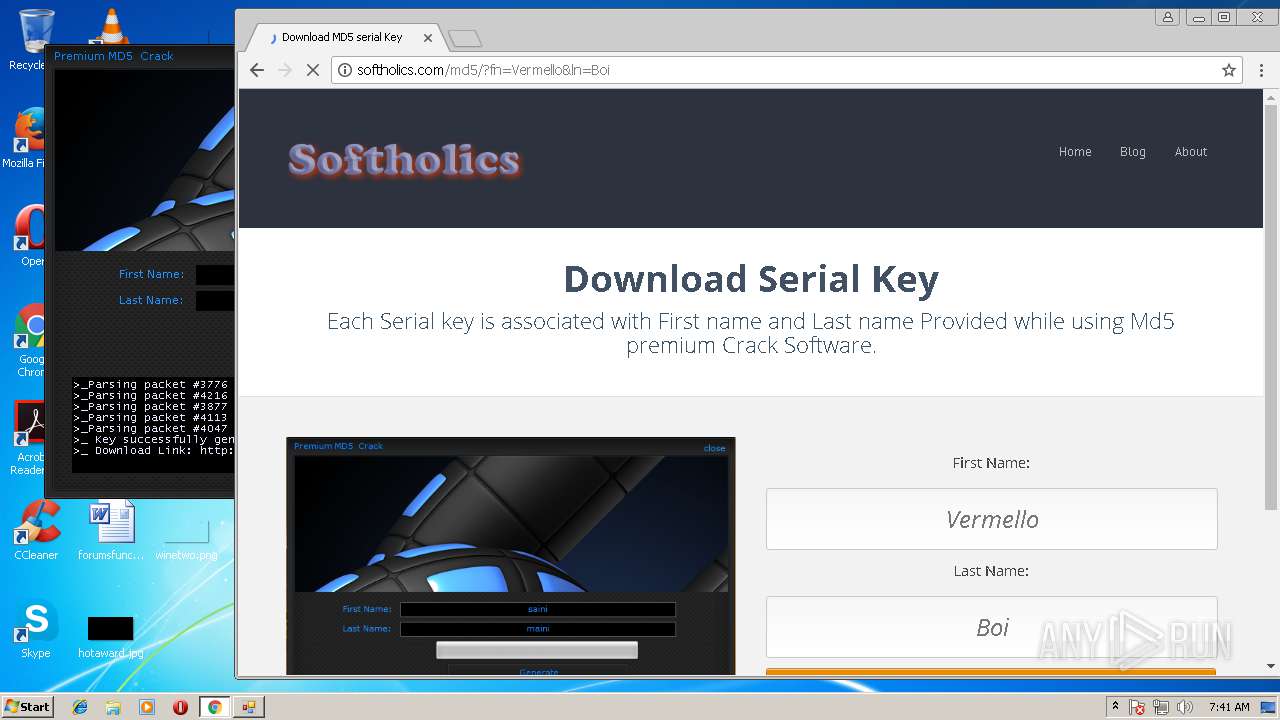
Dropped object may contain URL's
- chrome.exe (PID: 2752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (55.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21) |
| .scr | | | Windows screen saver (9.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | minecraft_vb |
| OriginalFileName: | minecraft_vb.exe |
| LegalCopyright: | Copyright © 2012 |
| InternalName: | minecraft_vb.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | minecraft_vb |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0xa139e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 13312 |
| CodeSize: | 652288 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| TimeStamp: | 2014:03:24 07:41:25+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Mar-2014 06:41:25 |
| Debug artifacts: |
|
| FileDescription: | minecraft_vb |
| FileVersion: | 1.0.0.0 |
| InternalName: | minecraft_vb.exe |
| LegalCopyright: | Copyright © 2012 |
| OriginalFilename: | minecraft_vb.exe |
| ProductName: | minecraft_vb |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 24-Mar-2014 06:41:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0009F3A4 | 0x0009F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.88621 |
.sdata | 0x000A2000 | 0x00000138 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.38075 |
.rsrc | 0x000A4000 | 0x00002E70 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.3033 |
.reloc | 0x000A8000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 2.0843 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 1.04772 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 2.76148 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 1.71396 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 1.72071 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 2.72257 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.71964 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
42
Monitored processes
10
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=61.0.3163.100 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6d9e7d7c,0x6d9e7da4,0x6d9e7d8c | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 1332 | "C:\Users\admin\AppData\Local\Temp\md5crack.exe" | C:\Users\admin\AppData\Local\Temp\md5crack.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: minecraft_vb Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1596,1256774741295478357,3661948408010834954,131072 --service-pipe-token=C8EED57FFF16A4AE2E49B8E38467283B --lang=en-US --disable-client-side-phishing-detection --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=C8EED57FFF16A4AE2E49B8E38467283B --renderer-client-id=5 --mojo-platform-channel-handle=3260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1596,1256774741295478357,3661948408010834954,131072 --service-pipe-token=6DF03EA5FF85F1107ACD06EF905BF934 --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=6DF03EA5FF85F1107ACD06EF905BF934 --renderer-client-id=6 --mojo-platform-channel-handle=3584 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1596,1256774741295478357,3661948408010834954,131072 --service-pipe-token=8973CEDBDA4CF8BFFD1D2D3F7EA7849F --lang=en-US --extension-process --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=8973CEDBDA4CF8BFFD1D2D3F7EA7849F --renderer-client-id=2 --mojo-platform-channel-handle=1288 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2724 | "C:\Users\admin\AppData\Local\Google\Chrome\User Data\SwReporter\23.129.0\software_reporter_tool.exe" --session-id=/J2djG66DWsa/SC+5EUWkGL6+c7FrZwKcE3cAR0y | C:\Users\admin\AppData\Local\Google\Chrome\User Data\SwReporter\23.129.0\software_reporter_tool.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Integrity Level: MEDIUM Description: Software Reporter Tool Exit code: 2 Version: 23.129.0 Modules
| |||||||||||||||
| 2752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2904 | "c:\users\admin\appdata\local\google\chrome\user data\swreporter\23.129.0\software_reporter_tool.exe" --crash-handler "--database=c:\users\admin\appdata\local\Google\Software Reporter Tool" --url=https://clients2.google.com/cr/report --annotation=plat=Win32 --annotation=prod=ChromeFoil --annotation=ver=23.129.0 --initial-client-data=0xe4,0xec,0xf0,0xe8,0xf4,0x104c42c,0x104c43c,0x104c44c | c:\users\admin\appdata\local\google\chrome\user data\swreporter\23.129.0\software_reporter_tool.exe | — | software_reporter_tool.exe | |||||||||||
User: admin Company: Google Integrity Level: MEDIUM Description: Software Reporter Tool Exit code: 0 Version: 23.129.0 Modules
| |||||||||||||||
| 3508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1768 --on-initialized-event-handle=296 --parent-handle=300 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 3524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1596,1256774741295478357,3661948408010834954,131072 --service-pipe-token=B0F9795EC1C0581373A2AB7C2D5B0510 --lang=en-US --disable-client-side-phishing-detection --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=B0F9795EC1C0581373A2AB7C2D5B0510 --renderer-client-id=4 --mojo-platform-channel-handle=1608 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
Total events
491
Read events
222
Write events
258
Delete events
11
Modification events
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2752-13175678463593617 |
Value: 259 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3708-13168704147815429 |
Value: 0 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2752-13175678463593617 |
Value: 259 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
49
Text files
57
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000040.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\38b42205-3259-4e3c-be67-0a5e1e50e82b.tmp | — | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\IndexedDB\https_www.google.ru_0.indexeddb.leveldb\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1c0f98.TMP | text | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RF1c1295.TMP | text | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\f_000001 | compressed | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
32
DNS requests
13
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
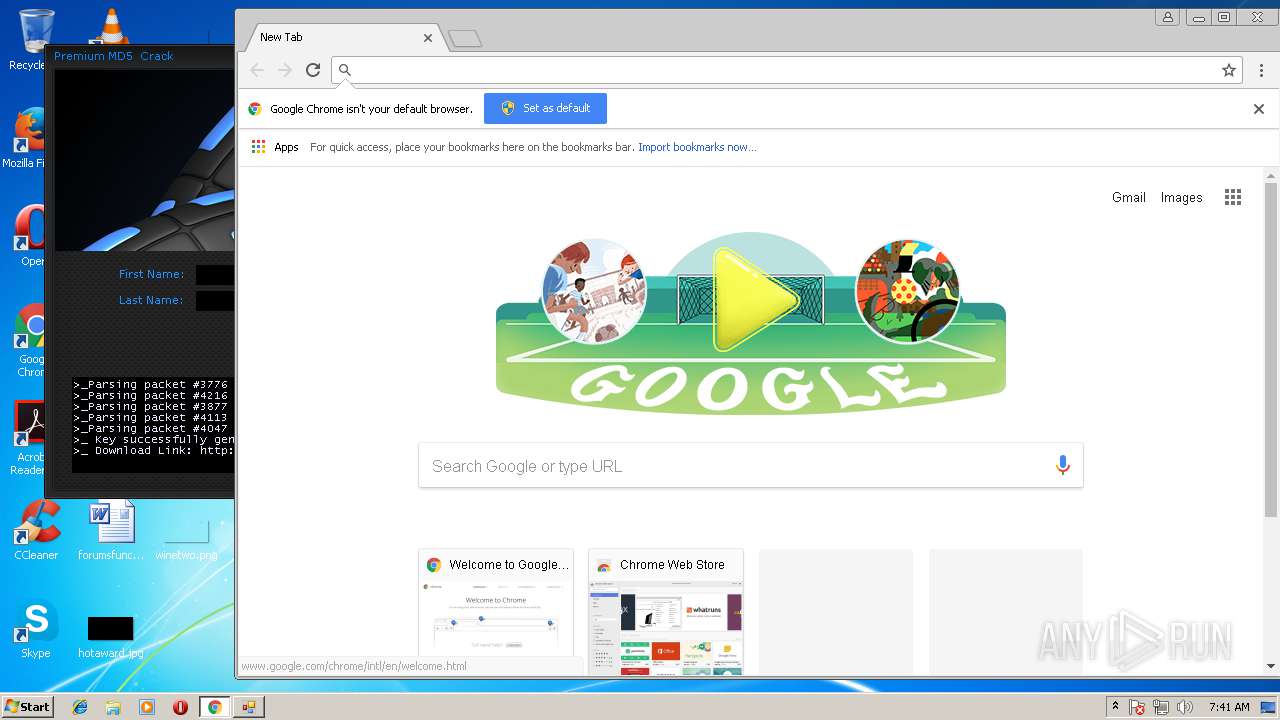
2752 | chrome.exe | GET | 200 | 31.220.3.21:80 | http://softholics.com/md5/wp-content/plugins/wordpress-notification-bar/inc/css/seed_wnba560.css?ver=3.9.1 | BZ | text | 422 b | malicious |
2752 | chrome.exe | GET | 200 | 31.220.3.21:80 | http://softholics.com/md5/wp-content/plugins/optimizePressPlugin/lib/assets/default.min1e06.css?ver=2.1.10.1 | BZ | text | 61.7 Kb | malicious |
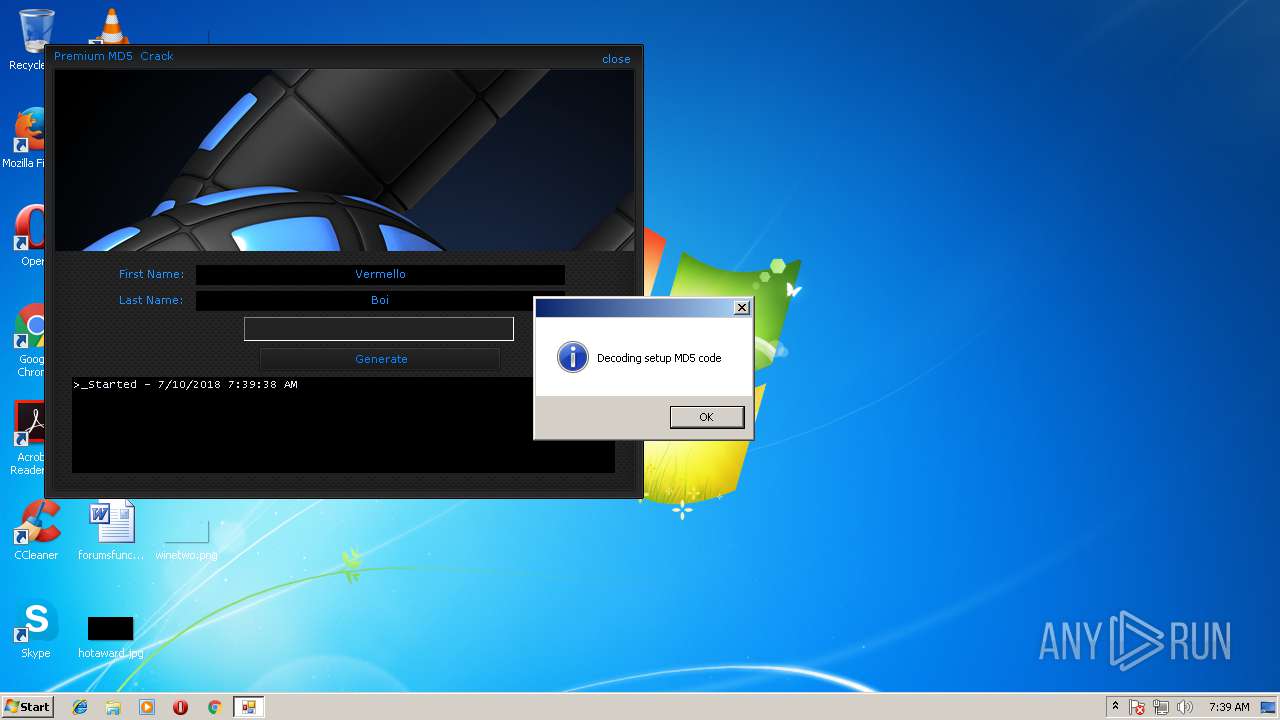
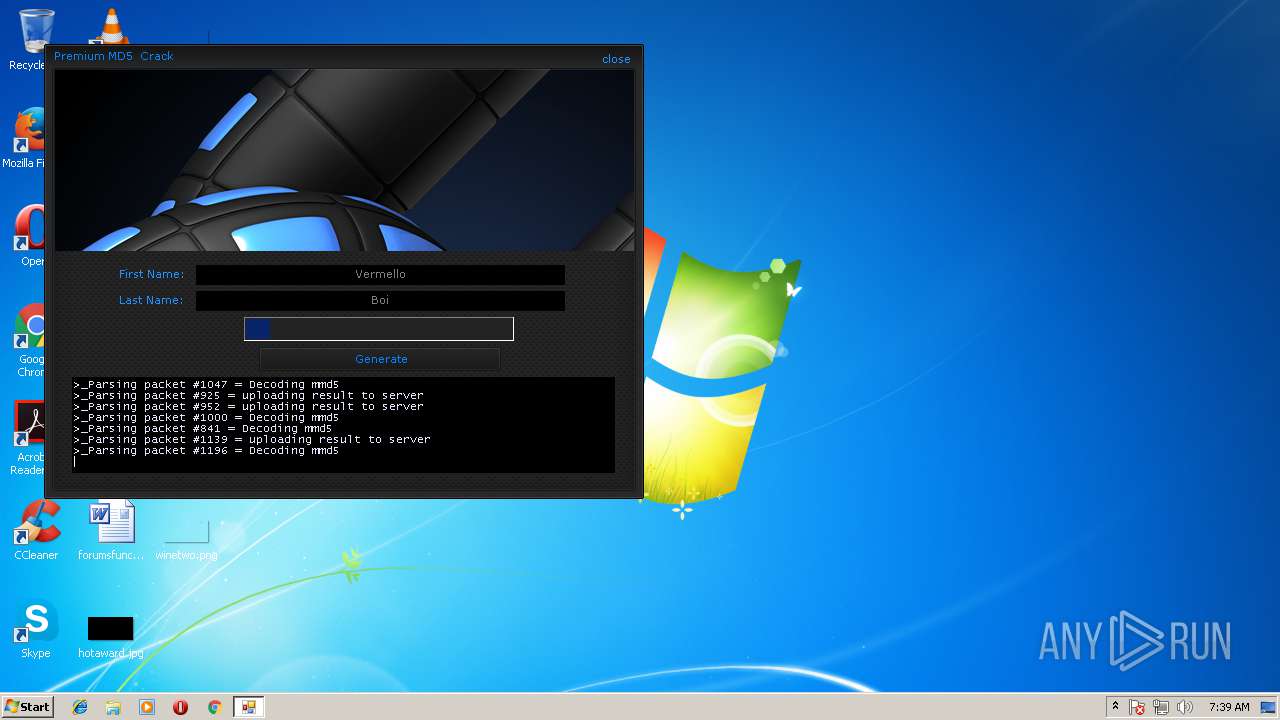
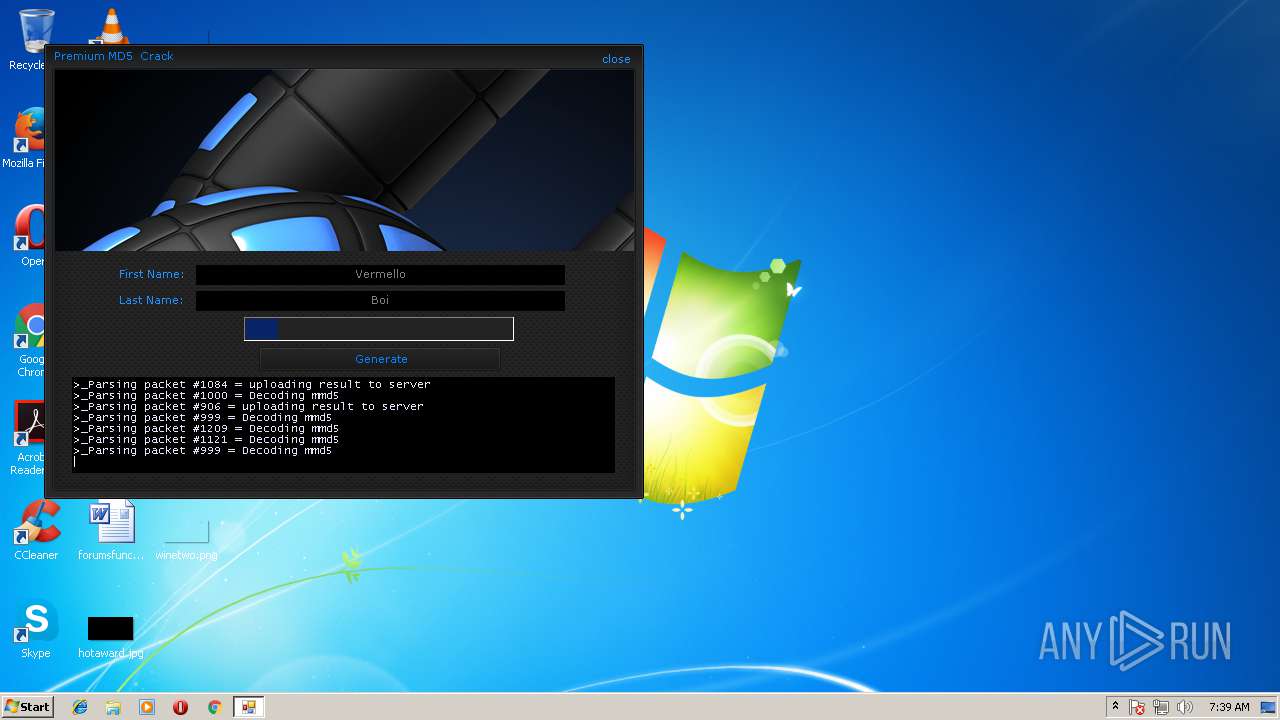
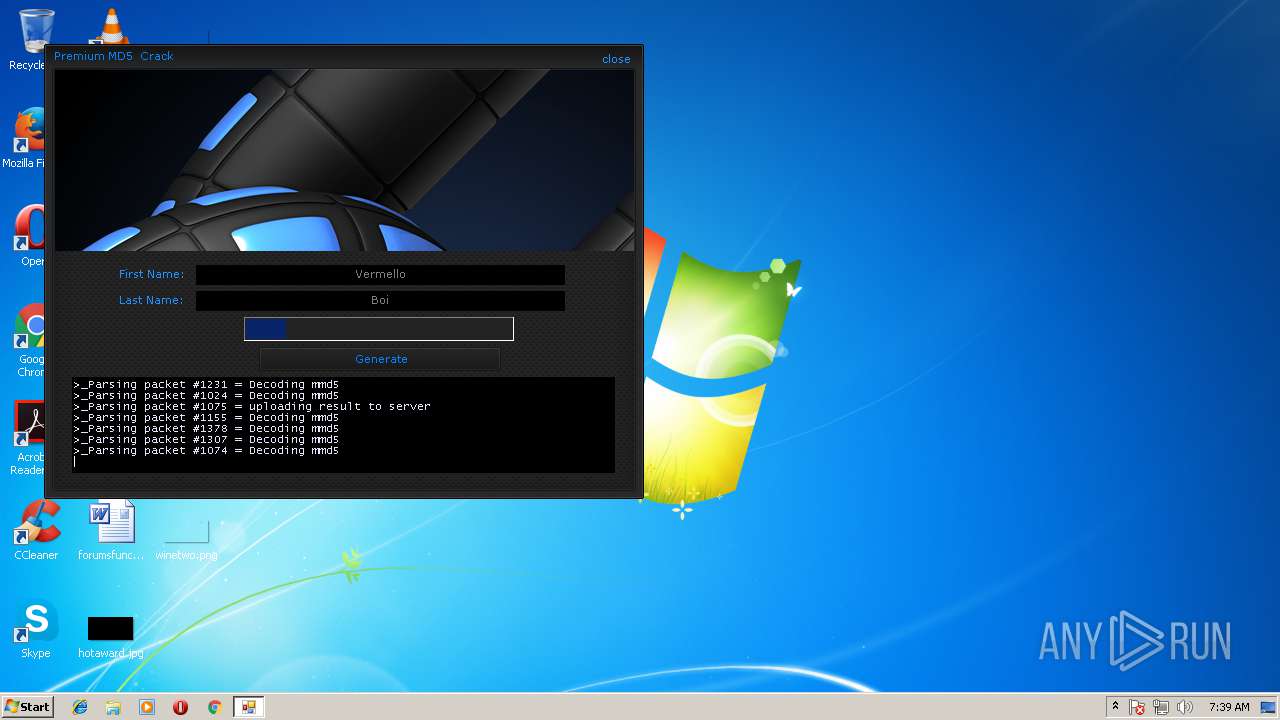
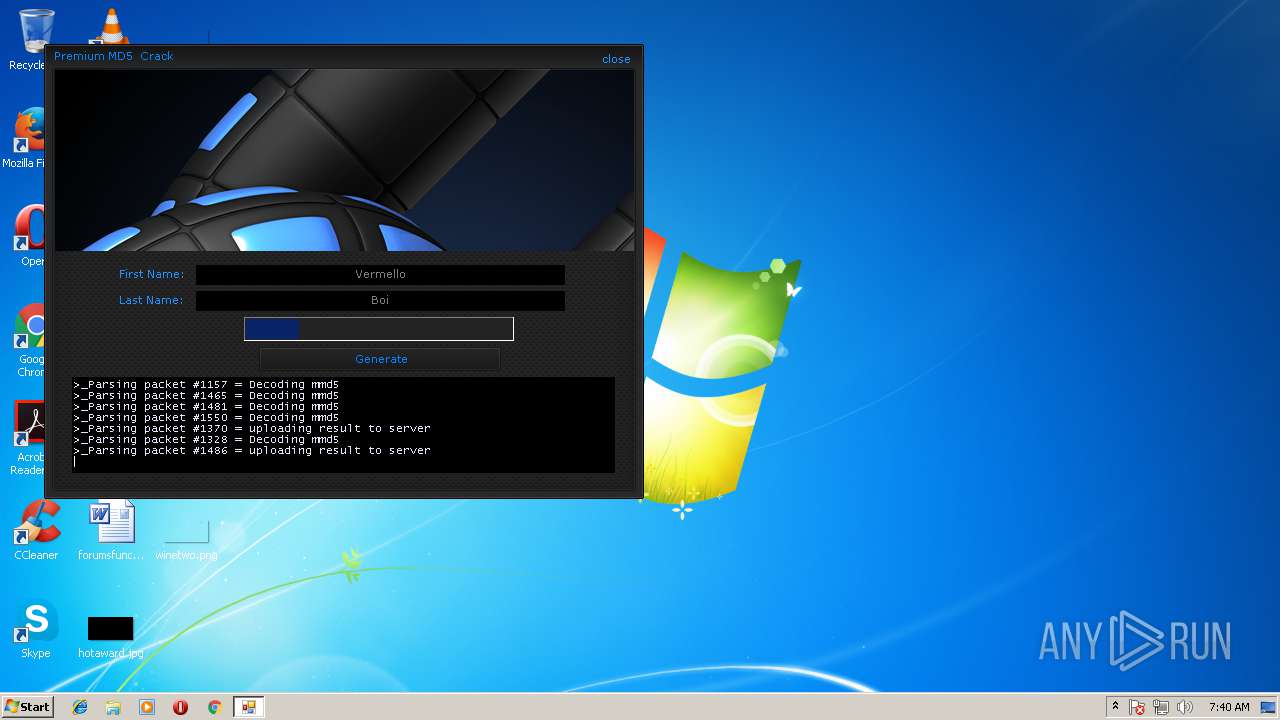
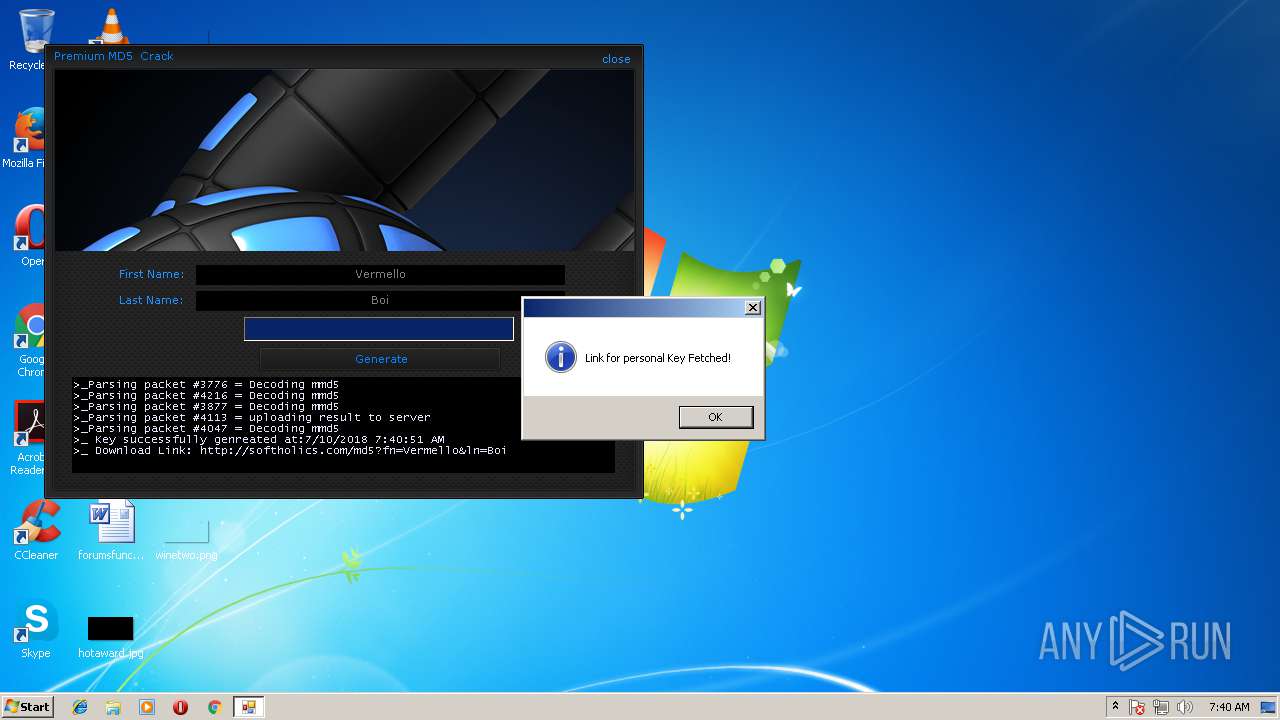
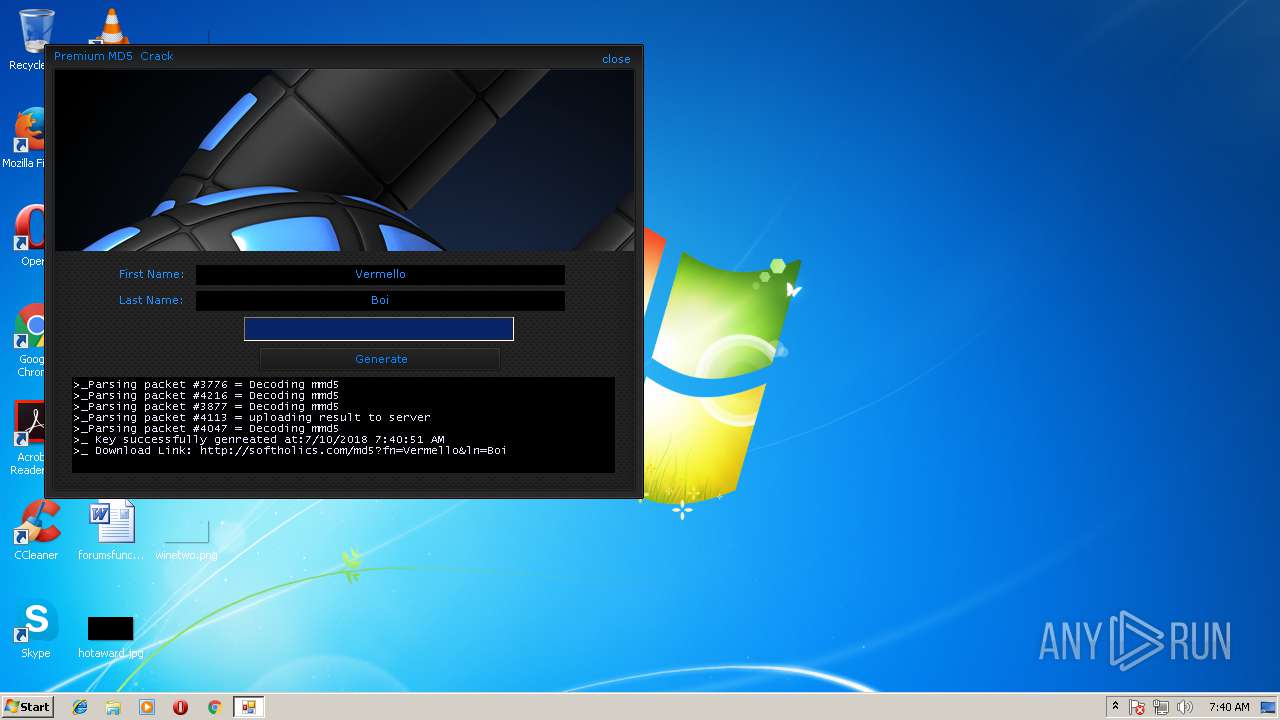
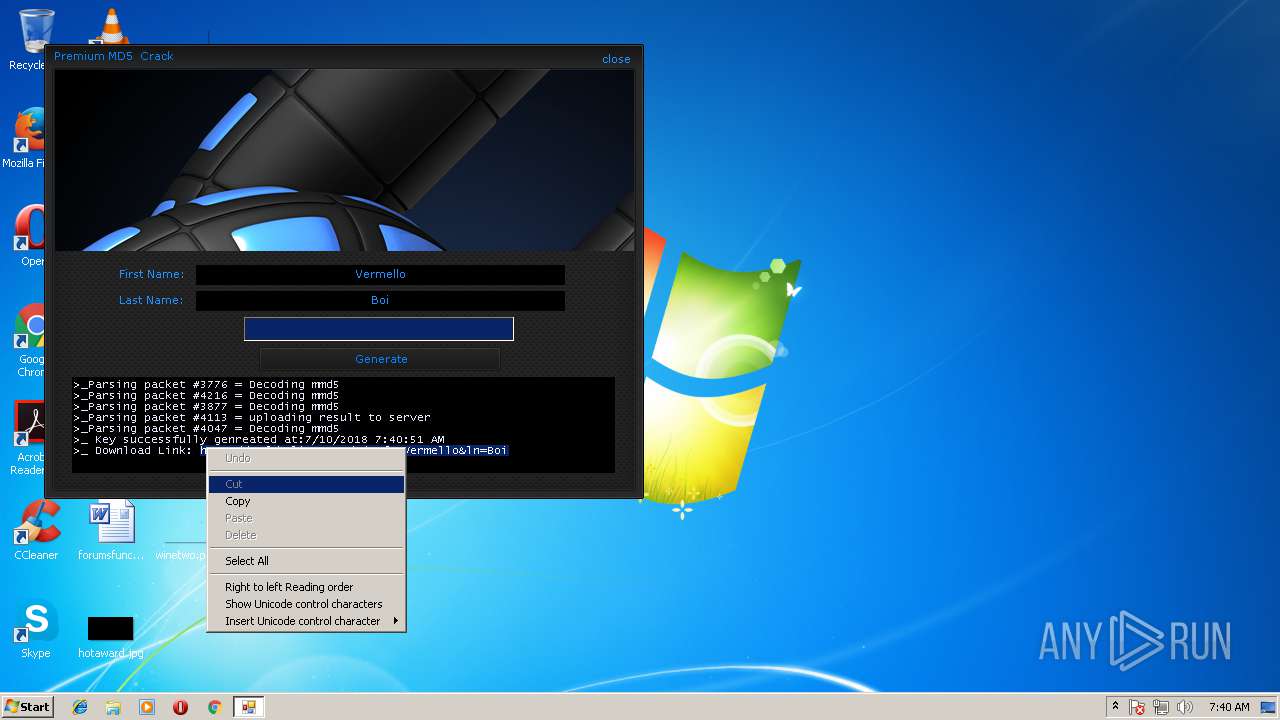
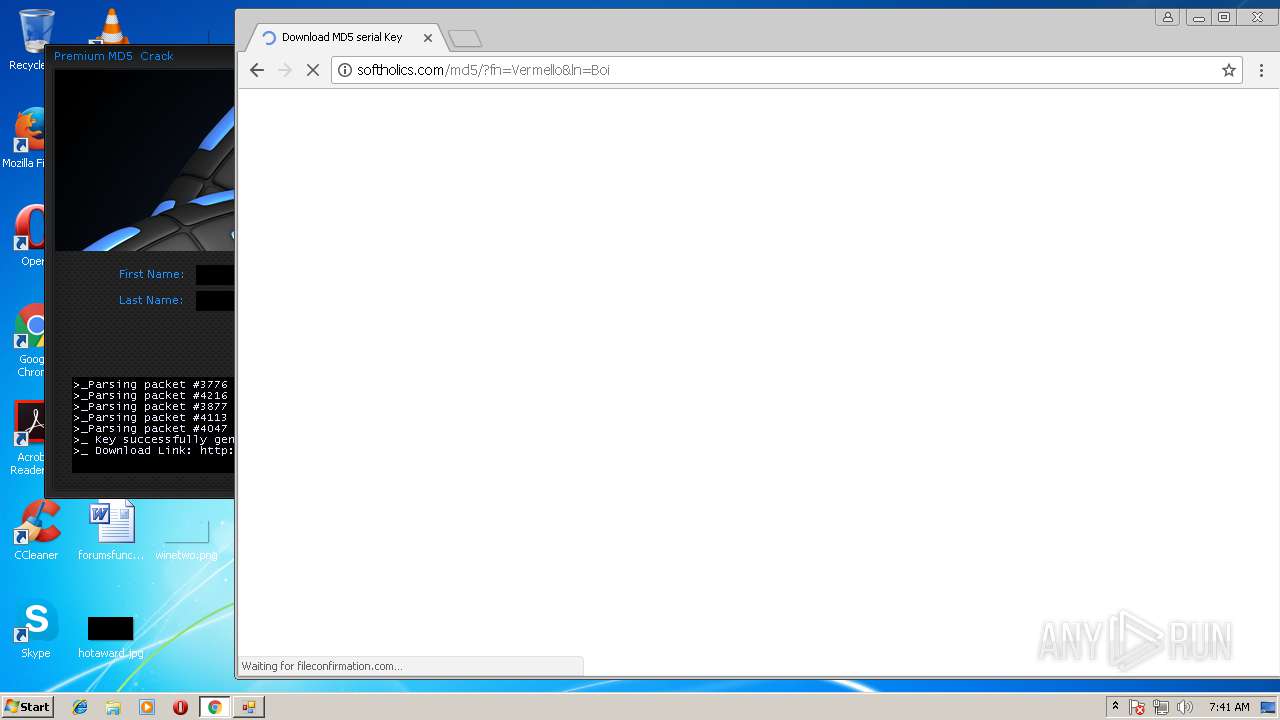
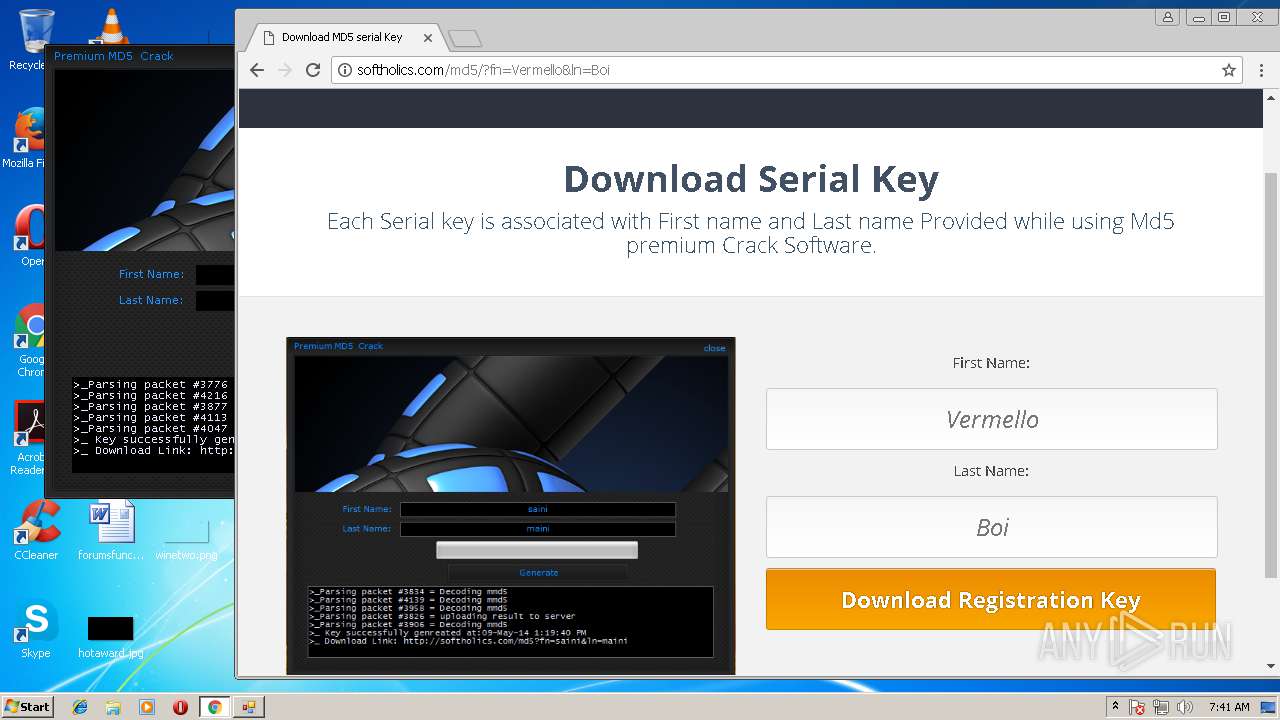
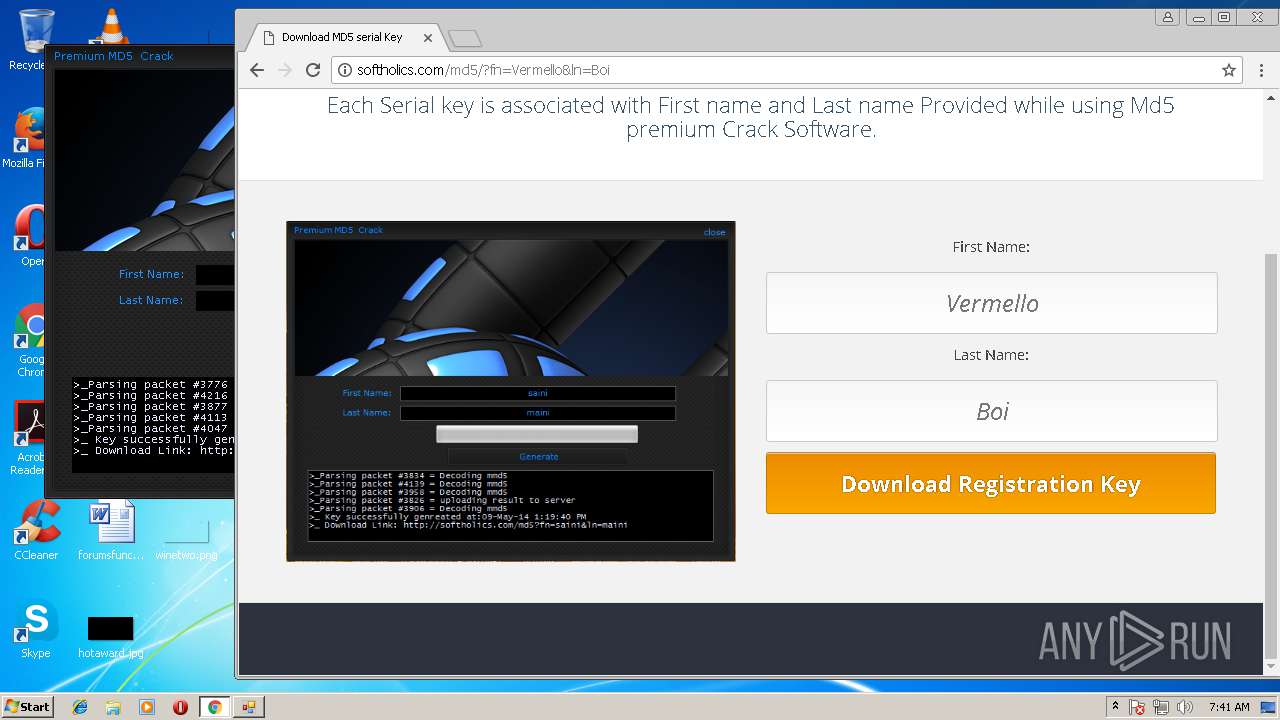
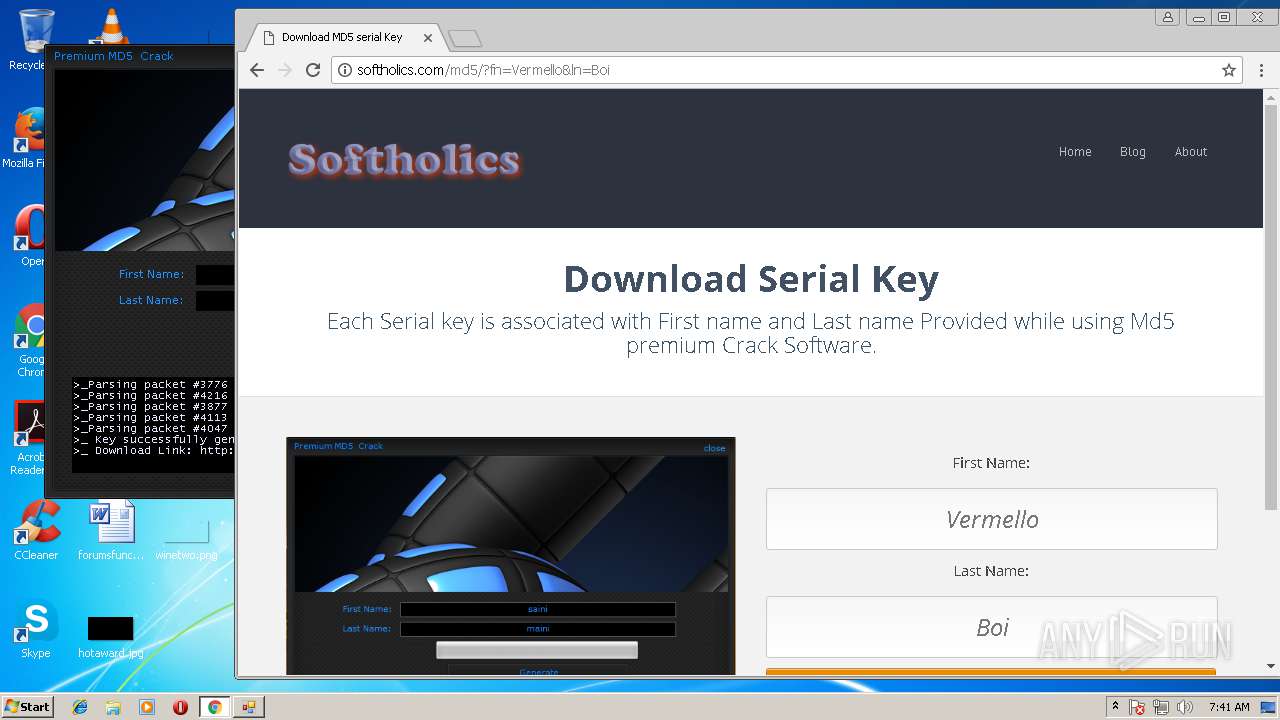
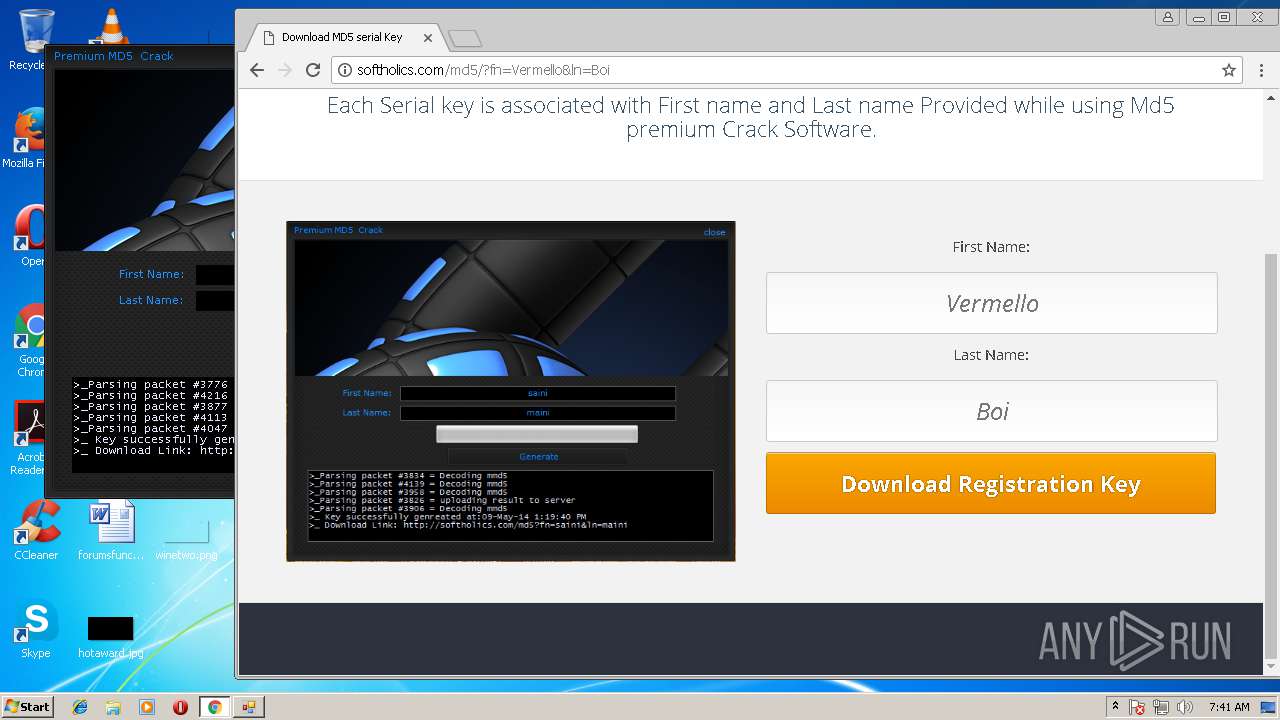
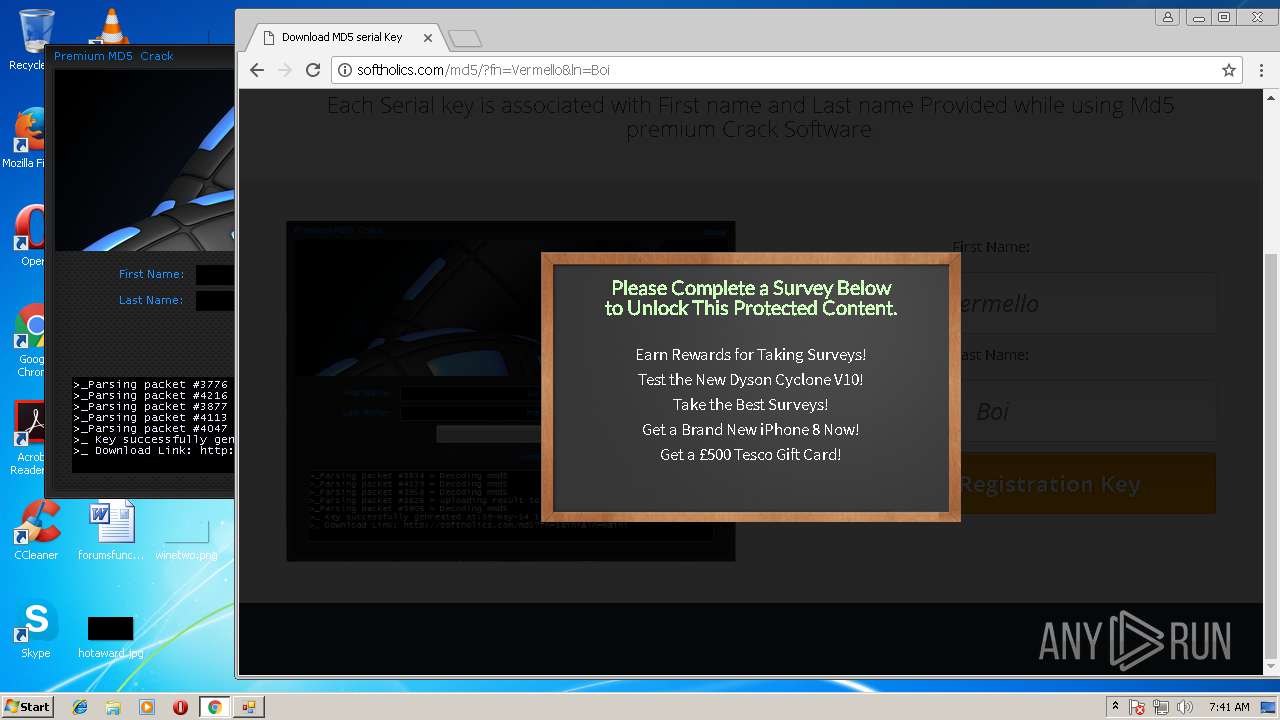
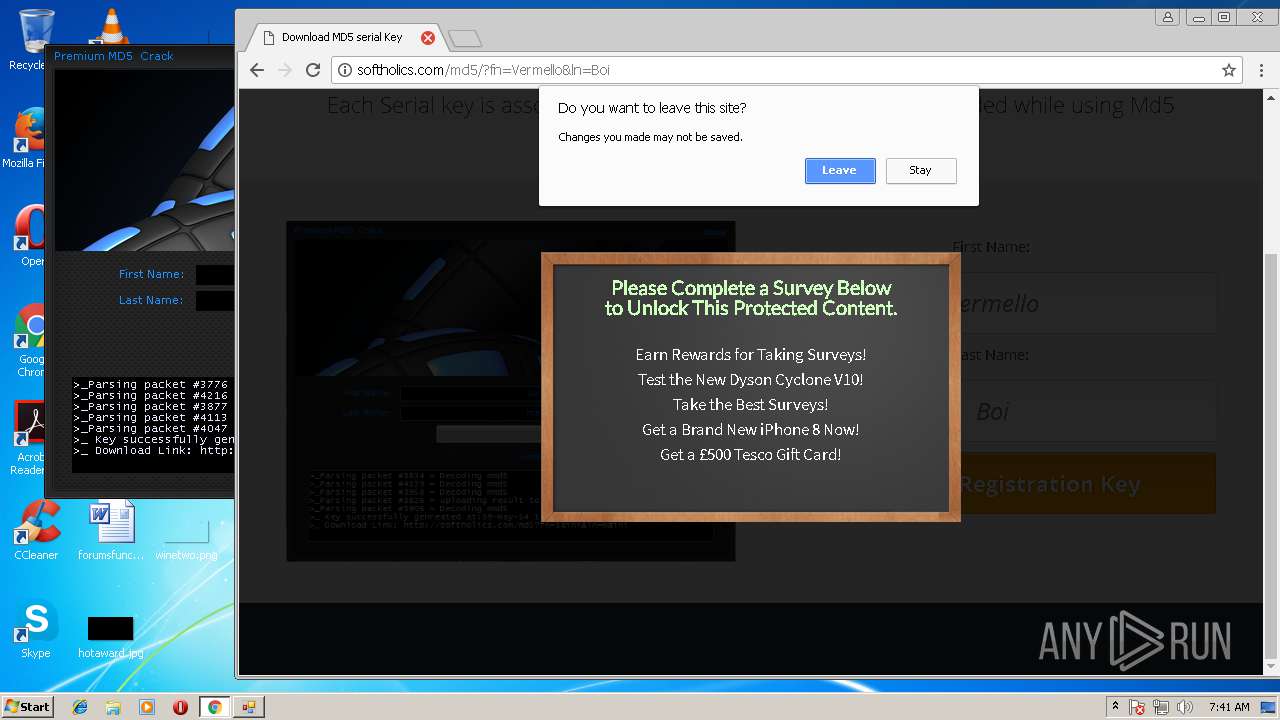
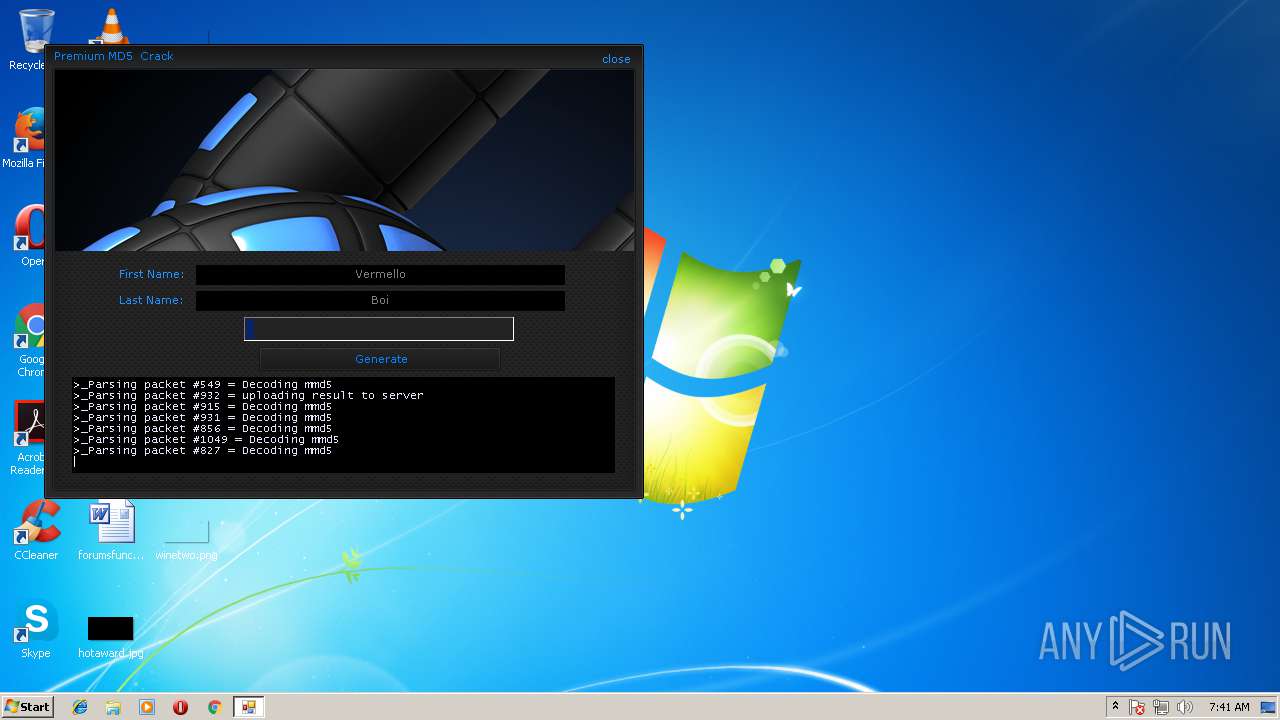
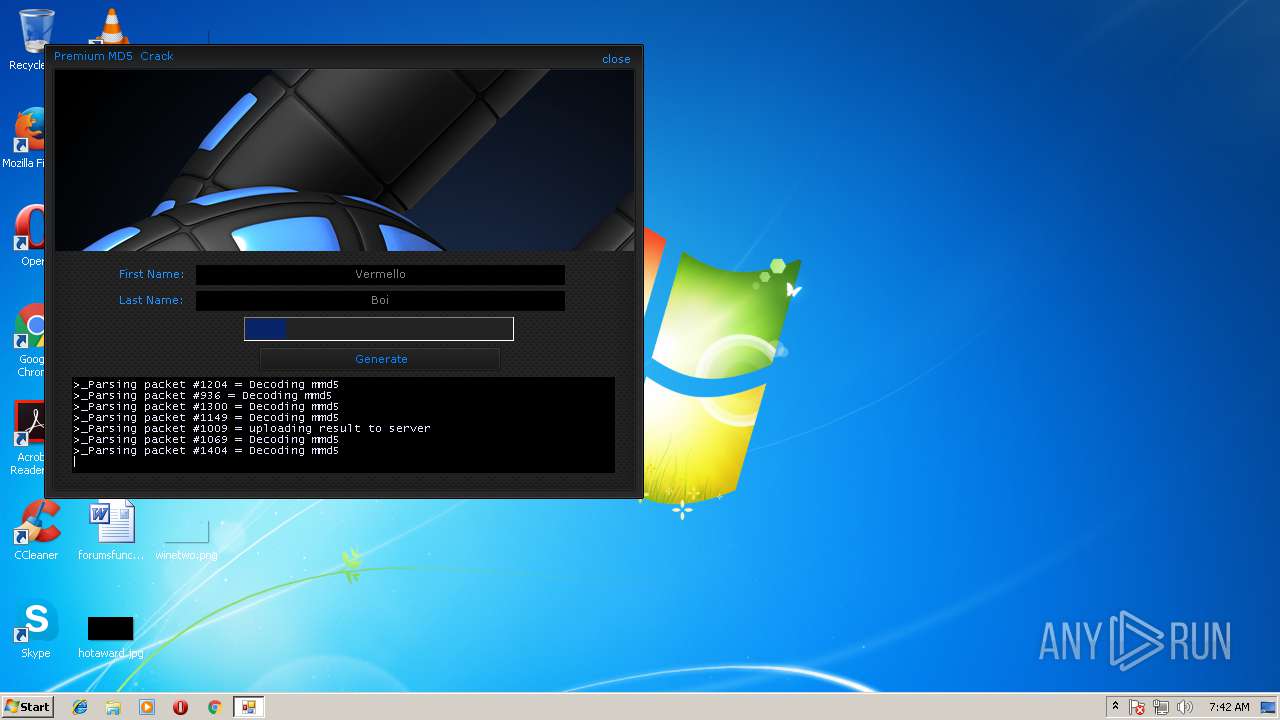
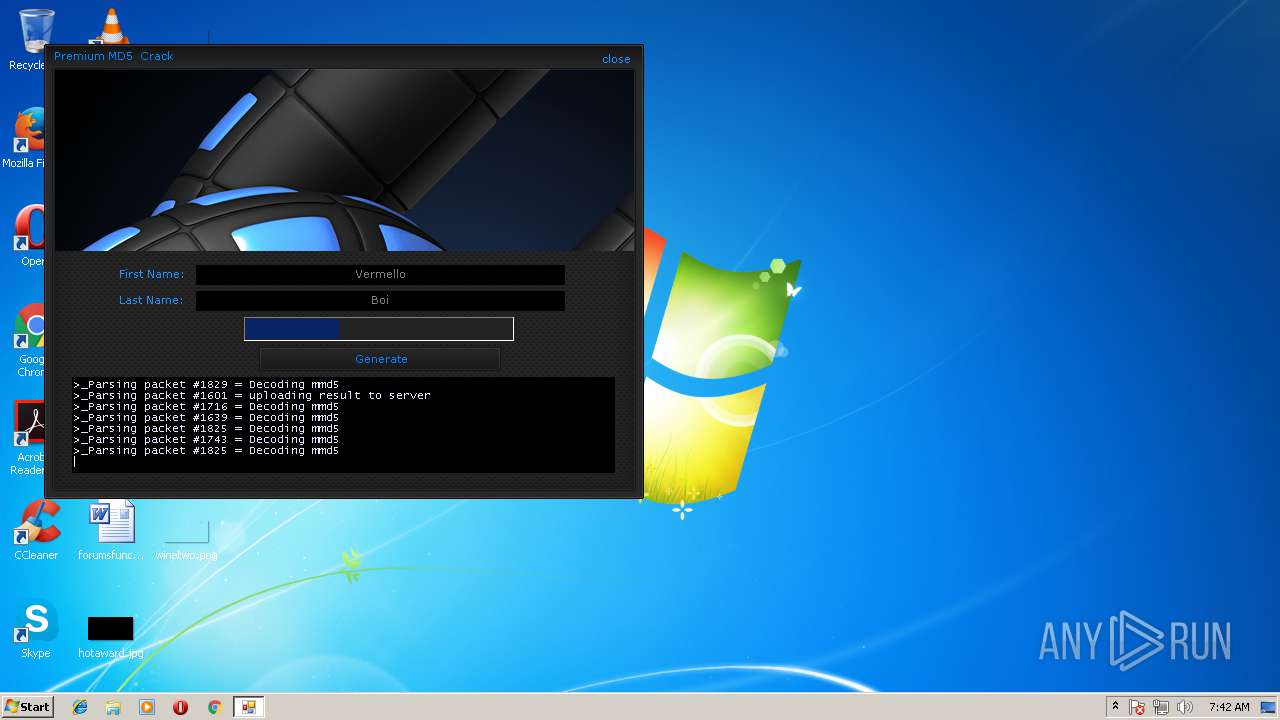
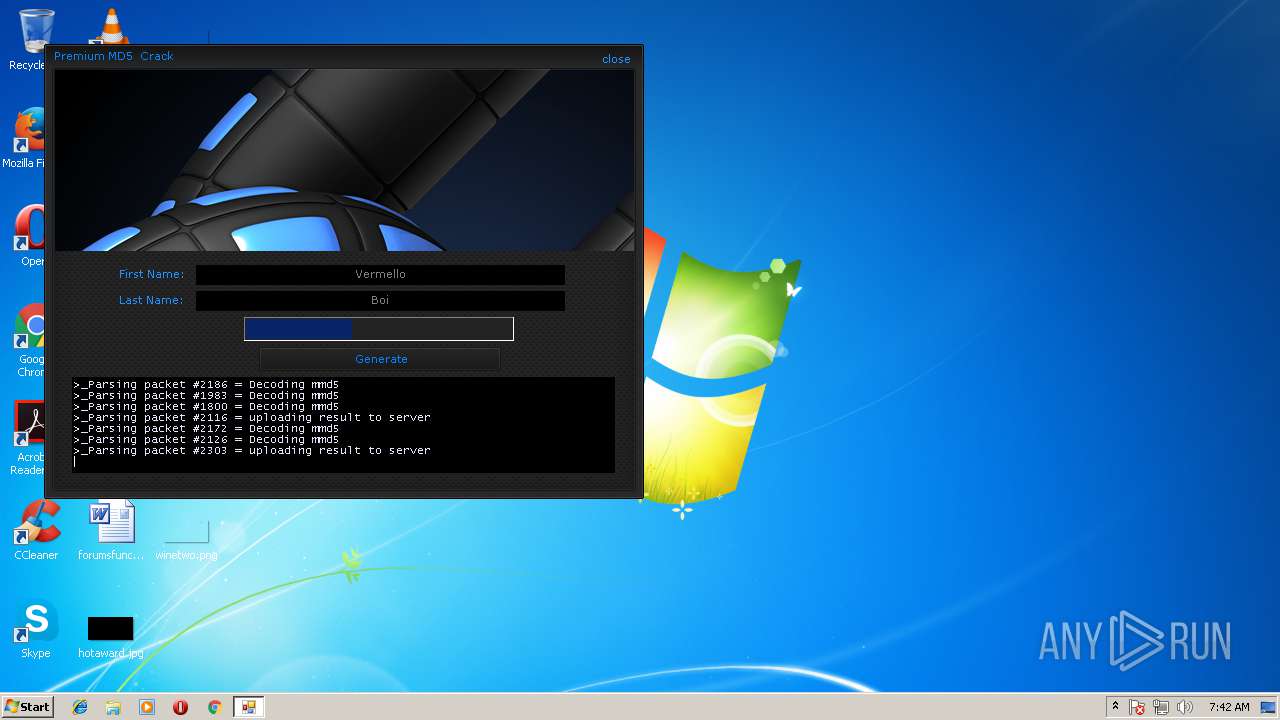
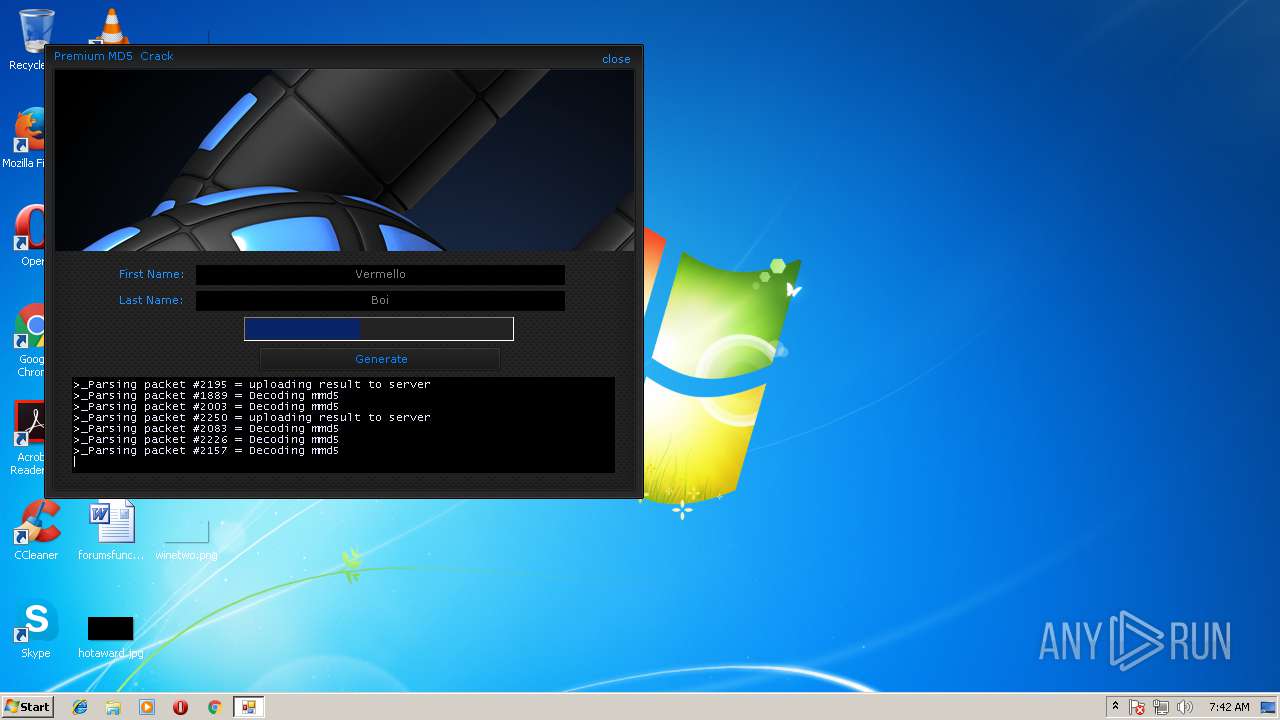
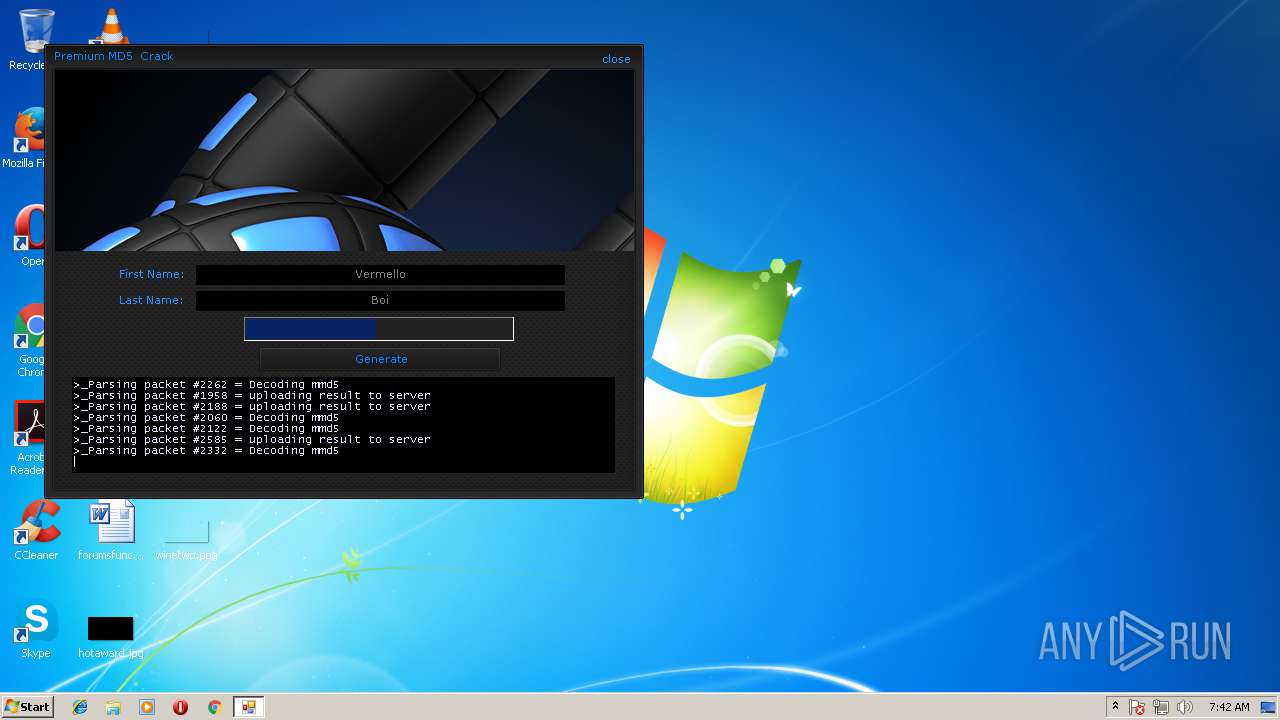
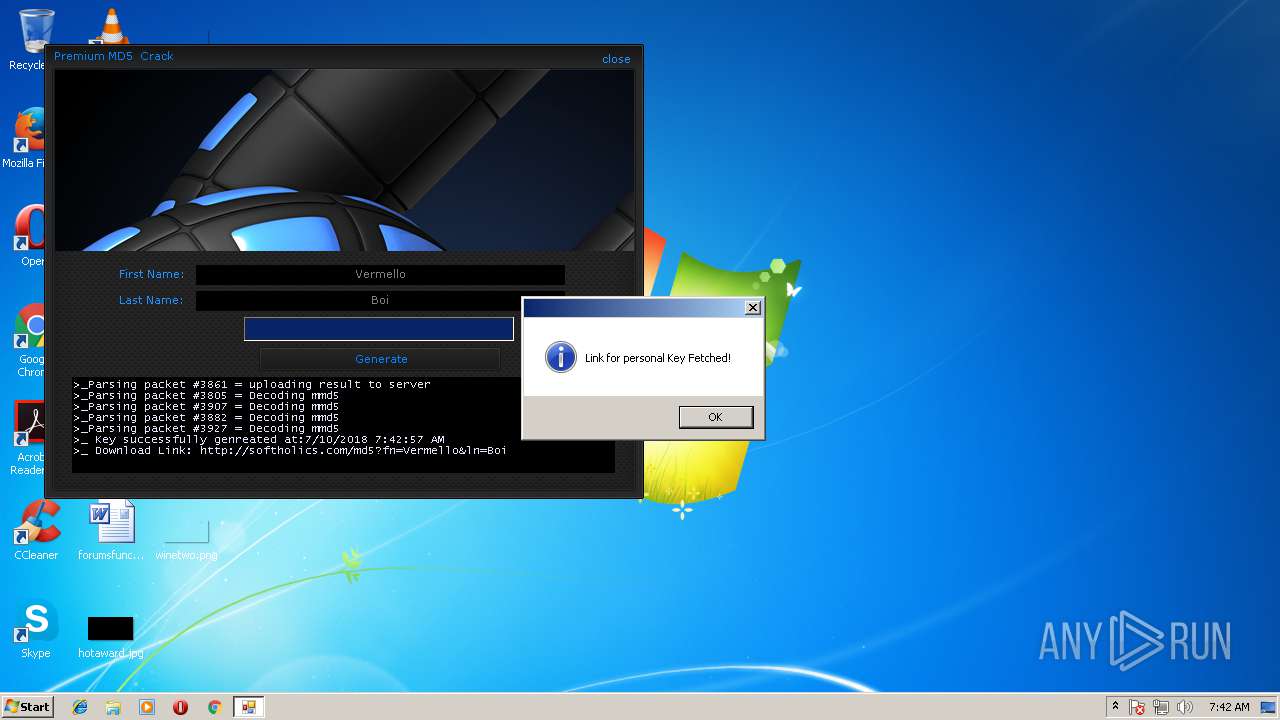
2752 | chrome.exe | GET | 200 | 31.220.3.21:80 | http://softholics.com/md5/?fn=Vermello&ln=Boi | BZ | html | 5.28 Kb | malicious |
2752 | chrome.exe | GET | 200 | 172.217.18.10:80 | http://fonts.googleapis.com/css?family=Open+Sans:400italic,700italic,400,700&subset=latin,latin-ext | US | text | 792 b | whitelisted |
2752 | chrome.exe | GET | 200 | 31.220.3.21:80 | http://softholics.com/md5/wp-content/plugins/optimizePressPlugin/lib/js/jquery/jquery.noconflict.min1e06.js?ver=2.1.10.1 | BZ | text | 546 b | malicious |
2752 | chrome.exe | GET | 200 | 31.220.3.21:80 | http://softholics.com/md5/wp-content/themes/twentytwelve/stylea560.css?ver=3.9.1 | BZ | text | 9.54 Kb | malicious |
2752 | chrome.exe | GET | 200 | 172.217.18.10:80 | http://fonts.googleapis.com/css?family=Open%20Sans:300,r,b,i,bi|Source%20Sans%20Pro:300,r,i,b,bi|Montserrat:r | US | text | 1.36 Kb | whitelisted |
2752 | chrome.exe | GET | 200 | 172.217.18.10:80 | http://fonts.googleapis.com/css?family=PT%20Sans:r,b,i,bi | US | text | 629 b | whitelisted |
2752 | chrome.exe | GET | 200 | 31.220.3.21:80 | http://softholics.com/md5/wp-content/plugins/optimizePressPlugin/lib/js/validation.min1e06.js?ver=2.1.10.1 | BZ | text | 300 b | malicious |
2752 | chrome.exe | GET | 200 | 172.217.18.10:80 | http://fonts.googleapis.com/css?family=Source%20Sans%20Pro:300,r,i,b,bi | US | text | 873 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2752 | chrome.exe | 216.58.215.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 172.217.168.46:443 | apis.google.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 172.217.18.196:443 | www.google.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 31.220.3.21:80 | softholics.com | Amarutu Technology Ltd | BZ | suspicious |
2752 | chrome.exe | 172.217.18.10:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 104.16.220.10:443 | fileconfirmation.com | Cloudflare Inc | US | shared |
2752 | chrome.exe | 70.32.68.202:80 | opdemo.com | Media Temple, Inc. | US | unknown |
2752 | chrome.exe | 216.58.207.67:443 | www.google.ru | Google Inc. | US | whitelisted |
2752 | chrome.exe | 216.58.215.227:80 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.ru |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
softholics.com |
| malicious |
fileconfirmation.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
opdemo.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
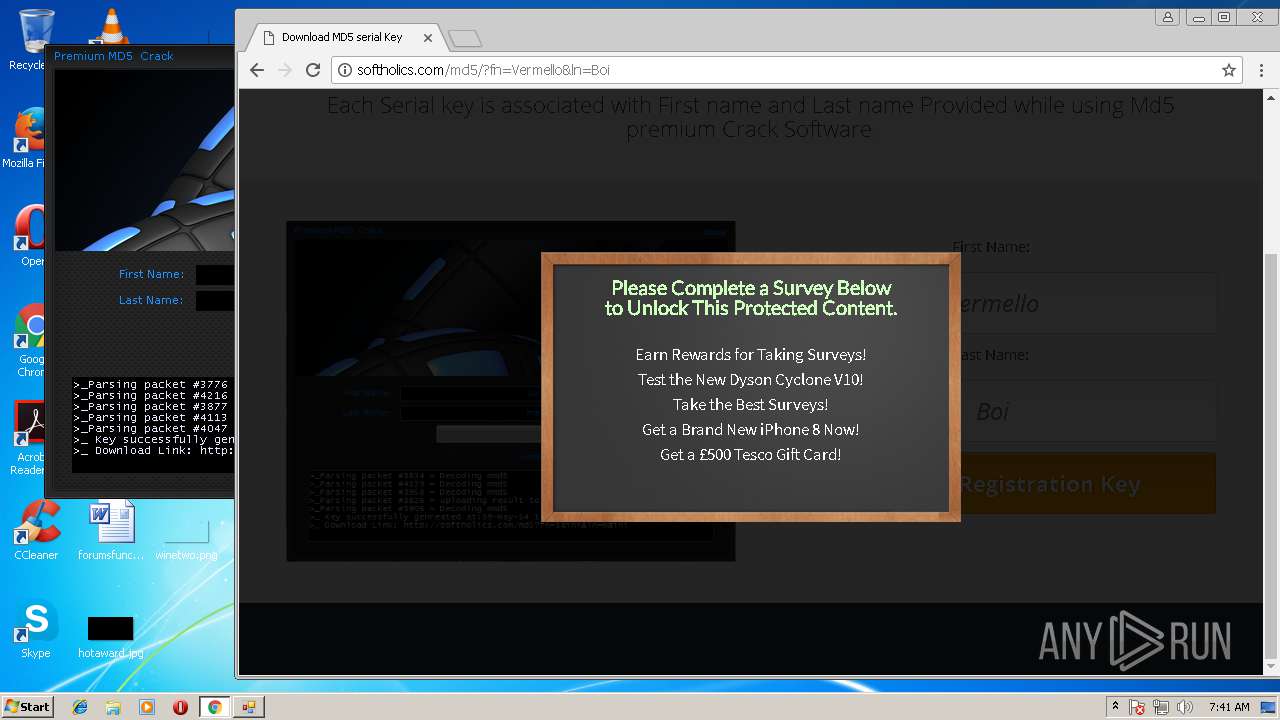
2752 | chrome.exe | A Network Trojan was detected | ET INFO Possible Phish - Mirrored Website Comment Observed |