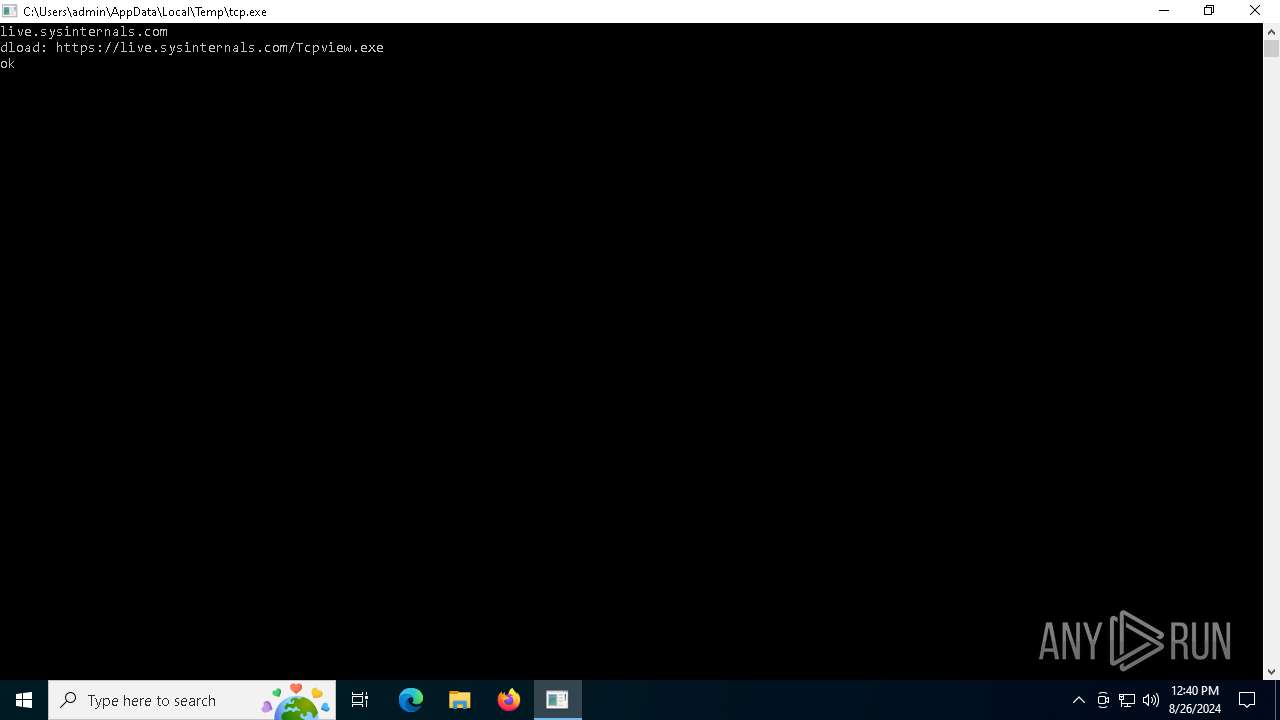
| File name: | tcp.exe |
| Full analysis: | https://app.any.run/tasks/838891fd-8714-48a7-8a95-beec6c91de65 |
| Verdict: | Malicious activity |
| Analysis date: | August 26, 2024, 12:39:49 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | 7FFCB08AECA5423C52FF38270748EE99 |
| SHA1: | 0A446FBB0280C9E9478820C32C71013C723BF0A1 |
| SHA256: | 21E836E4AB04DD5018D3628C0761ACA2BE3CD0C54989758D2F676507CA8C79FF |
| SSDEEP: | 24576:n1UeJFhG/Kznc/D6q+z1WQEkyyydGLc+Ec0xMki8UsU3AohT0qDtZnkNt6:1UeJFhGCznc/DaodwT0qDtZnQt6 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops the executable file immediately after the start
- tcp.exe (PID: 5264)
Reads security settings of Internet Explorer
- tcp.exe (PID: 5264)
Reads the date of Windows installation
- tcp.exe (PID: 5264)
Executable content was dropped or overwritten
- tcp.exe (PID: 5264)
Checks Windows Trust Settings
- tcp.exe (PID: 5264)
INFO
Checks proxy server information
- tcp.exe (PID: 5264)
Reads the computer name
- tcp.exe (PID: 5264)
Creates files or folders in the user directory
- tcp.exe (PID: 5264)
- ggc.exe (PID: 7084)
Checks supported languages
- tcp.exe (PID: 5264)
- ggc.exe (PID: 7084)
Reads the time zone
- ggc.exe (PID: 7084)
Create files in a temporary directory
- tcp.exe (PID: 5264)
Reads the software policy settings
- tcp.exe (PID: 5264)
Process checks computer location settings
- tcp.exe (PID: 5264)
Reads CPU info
- ggc.exe (PID: 7084)
Reads the machine GUID from the registry
- tcp.exe (PID: 5264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:08:26 12:38:54+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 2.42 |
| CodeSize: | 866304 |
| InitializedDataSize: | 1091584 |
| UninitializedDataSize: | 3584 |
| EntryPoint: | 0x13f0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
130
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4252 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tcp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
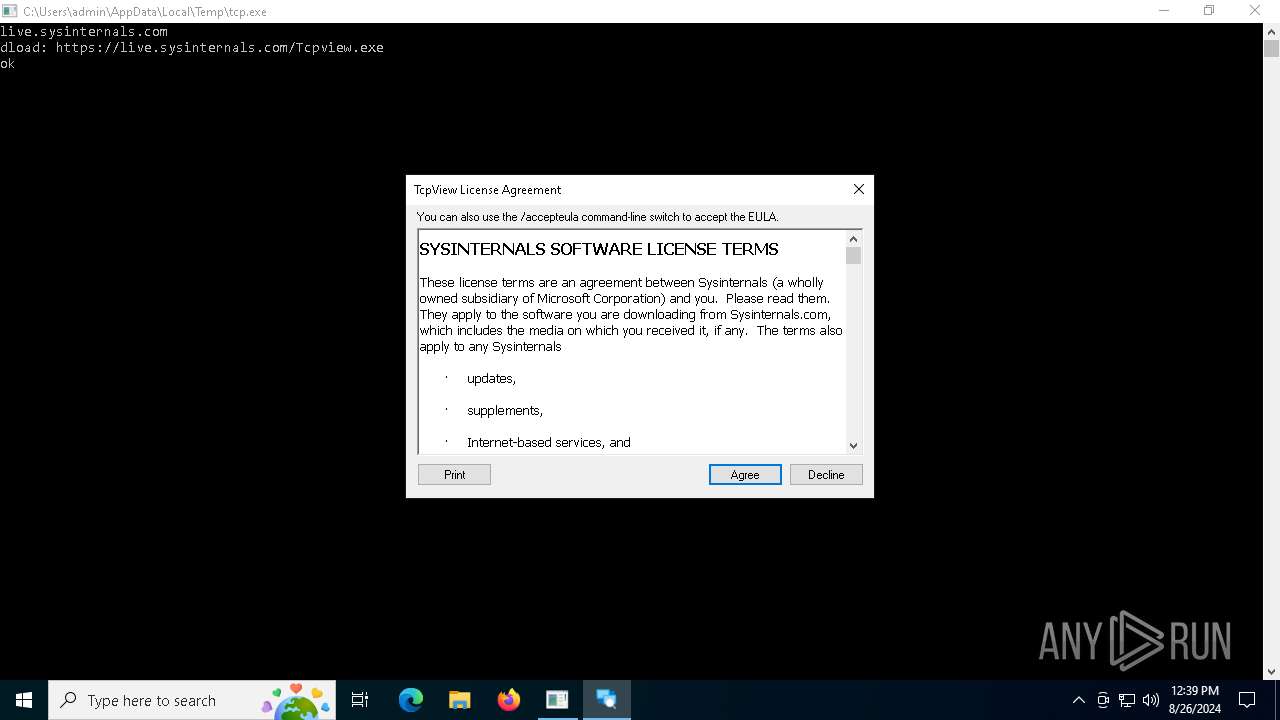
| 5264 | "C:\Users\admin\AppData\Local\Temp\tcp.exe" | C:\Users\admin\AppData\Local\Temp\tcp.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
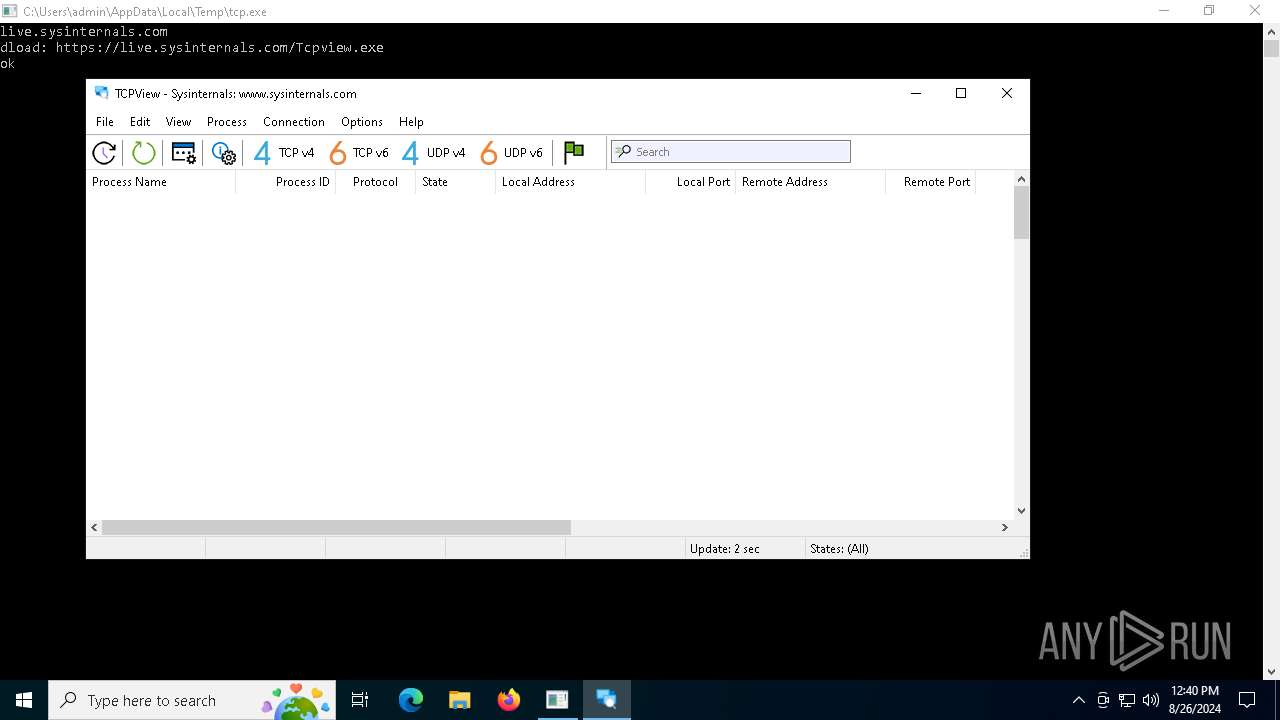
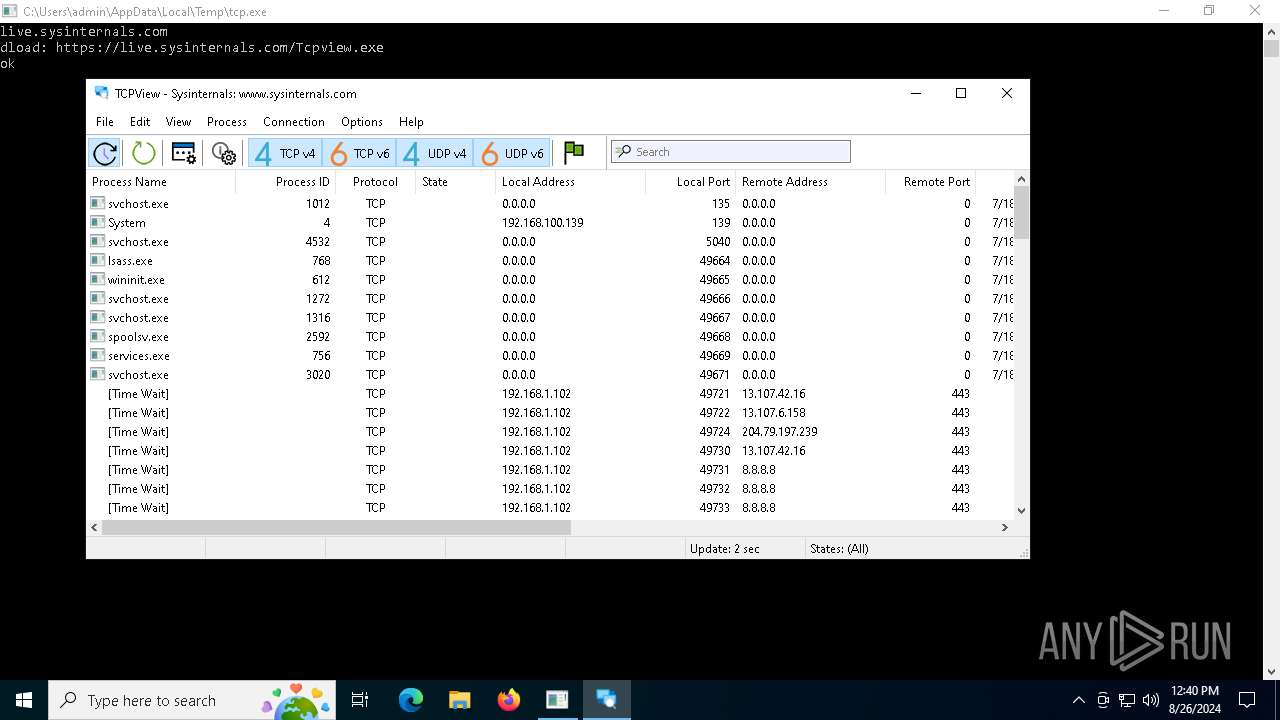
| 7084 | "C:\Users\admin\AppData\Local\Temp\ggc.exe" | C:\Users\admin\AppData\Local\Temp\ggc.exe | tcp.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: HIGH Description: Sysinternals TcpView Exit code: 1 Version: 4.19 Modules
| |||||||||||||||
Total events
4 991
Read events
4 979
Write events
12
Delete events
0
Modification events
| (PID) Process: | (5264) tcp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5264) tcp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5264) tcp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5264) tcp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (5264) tcp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5264) tcp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5264) tcp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7084) ggc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Sysinternals\TcpView |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
Executable files
2
Suspicious files
8
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5264 | tcp.exe | C:\Users\admin\AppData\Local\Temp\ggc.exe | executable | |
MD5:7CE89829F9FB955DC377529C461852FD | SHA256:9775B4BBE23B8EB93727EFE0A6D0B160AE5132A10B223F43200499CF0051A18F | |||
| 5264 | tcp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | der | |
MD5:36328FCA0A5D4B62657E7079A86FD60A | SHA256:7DE93512310A1C538F5A7FEB7AD81F517DF9E76C13A2714108AF3304FBAB0283 | |||
| 5264 | tcp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\87D78C45136644DE48CA5BE9C7B7FB9E_BB00108E24CF7C583AE5C1D9CA671CA3 | binary | |
MD5:00E3CE9E05ACC3AEE792AB98EE629272 | SHA256:244EB7FE8CDFB07E960E9CD6E89D899ADF91FD15EA3F83149AA535D41ED0CDEC | |||
| 5264 | tcp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_0C4CF5196B6676C60436CD17DE56BD63 | binary | |
MD5:4061F619AF54985CEF306E8B17C45CD4 | SHA256:1773CD5D0EDC7B46DA01DA0D783E253F829217A0EB8F6AE1BD35FCE6471565A5 | |||
| 5264 | tcp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7EF516642261549A23D49DB36FFE5F3F_AB4C88B69AAA8544C9741089B80A11F8 | der | |
MD5:021213833A4B11D654E5A5915ADA3D11 | SHA256:70F778ED34304BCDF940FF5AC6AA3FE3311DBB70988E25A9D6CE8EB751387D90 | |||
| 5264 | tcp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7EF516642261549A23D49DB36FFE5F3F_AB4C88B69AAA8544C9741089B80A11F8 | binary | |
MD5:05741AB18CF9A360815F59045632954F | SHA256:E0FD7C46F94539CEB389B892F27B0C77C65BB56997C08C9B255DAADD7E9F61F0 | |||
| 5264 | tcp.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\Tcpview[1].exe | executable | |
MD5:7CE89829F9FB955DC377529C461852FD | SHA256:9775B4BBE23B8EB93727EFE0A6D0B160AE5132A10B223F43200499CF0051A18F | |||
| 5264 | tcp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\87D78C45136644DE48CA5BE9C7B7FB9E_BB00108E24CF7C583AE5C1D9CA671CA3 | der | |
MD5:364111EBF40E4C239481CB67E80CD6CA | SHA256:BA0AC38762BCDB01D0DE29C9704D6773B95AC8E3E918F350E0425E55233A0CF1 | |||
| 5264 | tcp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:3DFCA46E00FFA4795C72A41375F159D3 | SHA256:DCBA1A505396539BAC40A7253C9F5DCCF06CBB79957E21D56305E1FC3AF5F40E | |||
| 7084 | ggc.exe | C:\Users\admin\AppData\Local\Sysinternals\tcpview.ini | text | |
MD5:E6E13068EB68236EE7CC3294CA81DAB6 | SHA256:05EED57A075E24137A64D2789CBAF423EDDD1409D85F17A163B7AF254400CBF6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
42
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5264 | tcp.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBTkdQGdwyPiJnQdbEA5B5X5BZZGLgQUO3DRU%2Bl2JZ1gqMpmD8abrm9UFmoCEzMAb%2FqyLHLS8MWfWfgAAABv%2BrI%3D | unknown | — | — | whitelisted |
5264 | tcp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5264 | tcp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEA7y5dg2gVICVeksYI%2B8L%2FQ%3D | unknown | — | — | whitelisted |
5264 | tcp.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSQXI0BX8IeiVGTBY3Wzmndxh3q4gQUrVQdA1Rxxi9e1lsYWM5uJMXWogoCEzMAAARgUJNB7iYCa%2BgAAAAABGA%3D | unknown | — | — | whitelisted |
1780 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1020 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1020 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2968 | svchost.exe | GET | 304 | 2.18.161.41:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7128 | svchost.exe | 52.185.211.133:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5644 | RUXIMICS.exe | 52.185.211.133:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 52.185.211.133:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4324 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5264 | tcp.exe | 20.76.201.171:443 | sysinternals.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5264 | tcp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5264 | tcp.exe | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
sysinternals.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
docs.microsoft.com |
| whitelisted |
learn.microsoft.com |
| whitelisted |
live.sysinternals.com |
| whitelisted |
login.live.com |
| whitelisted |