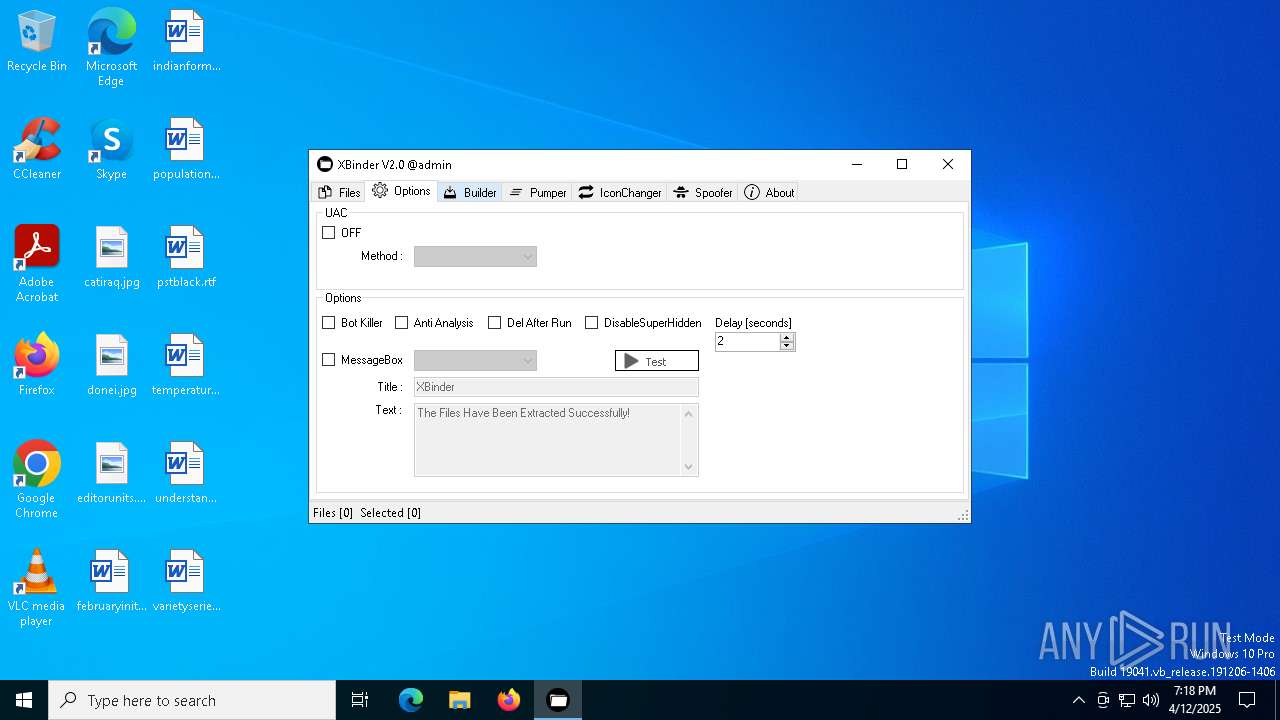
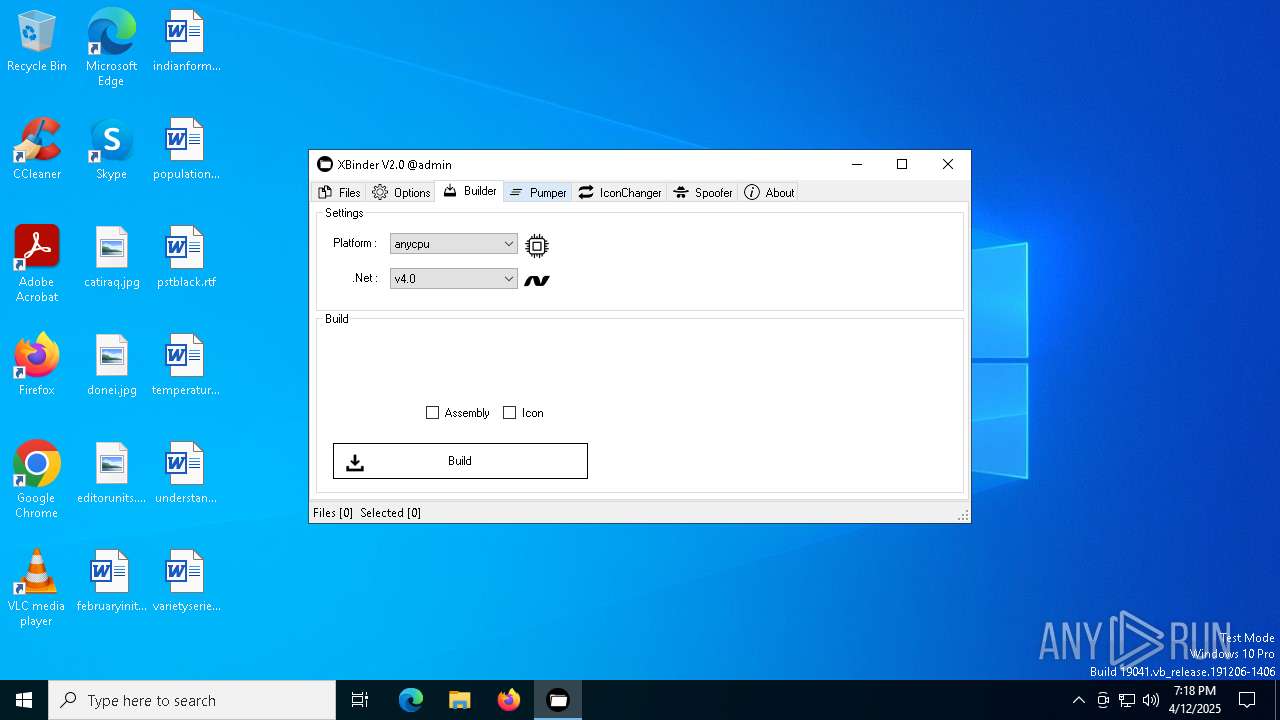
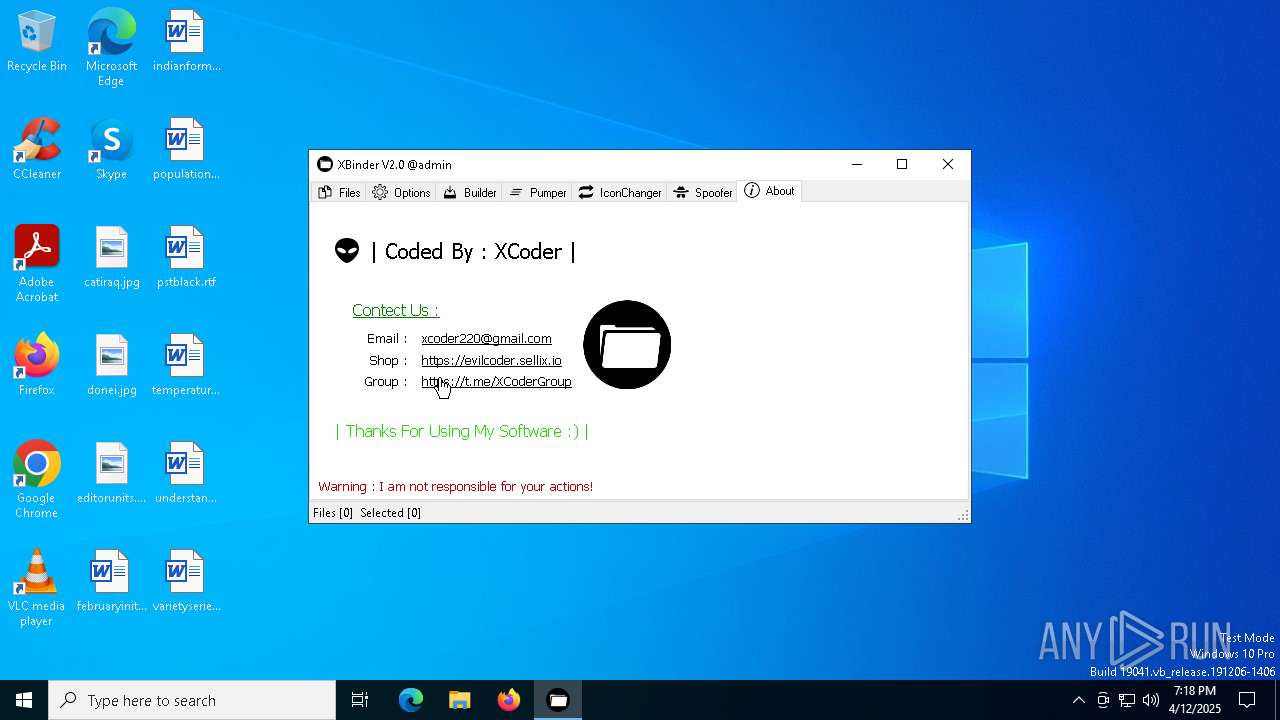
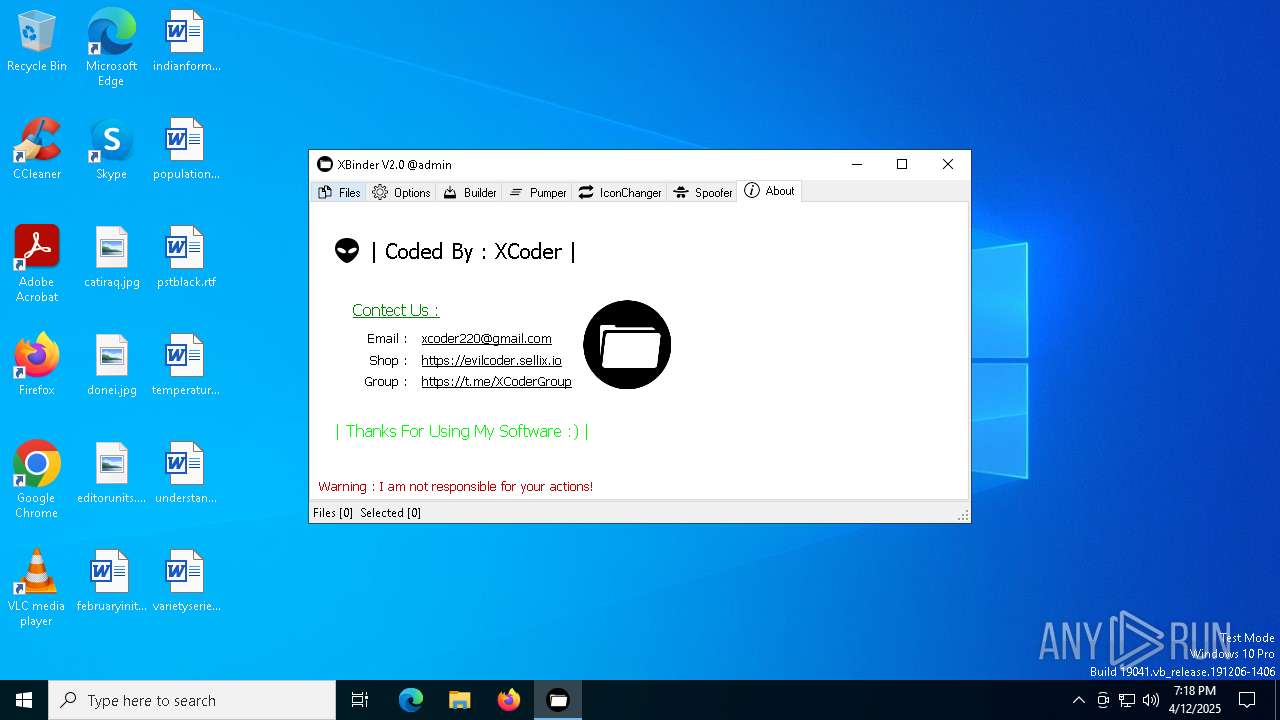
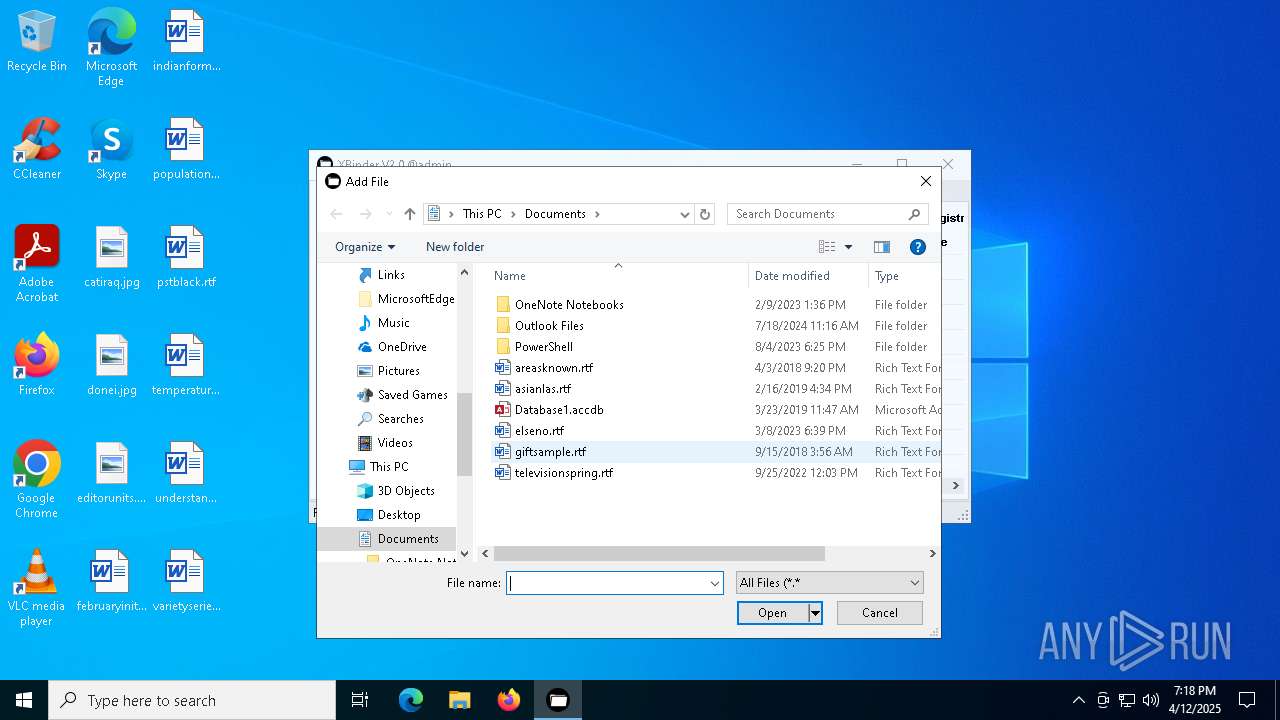
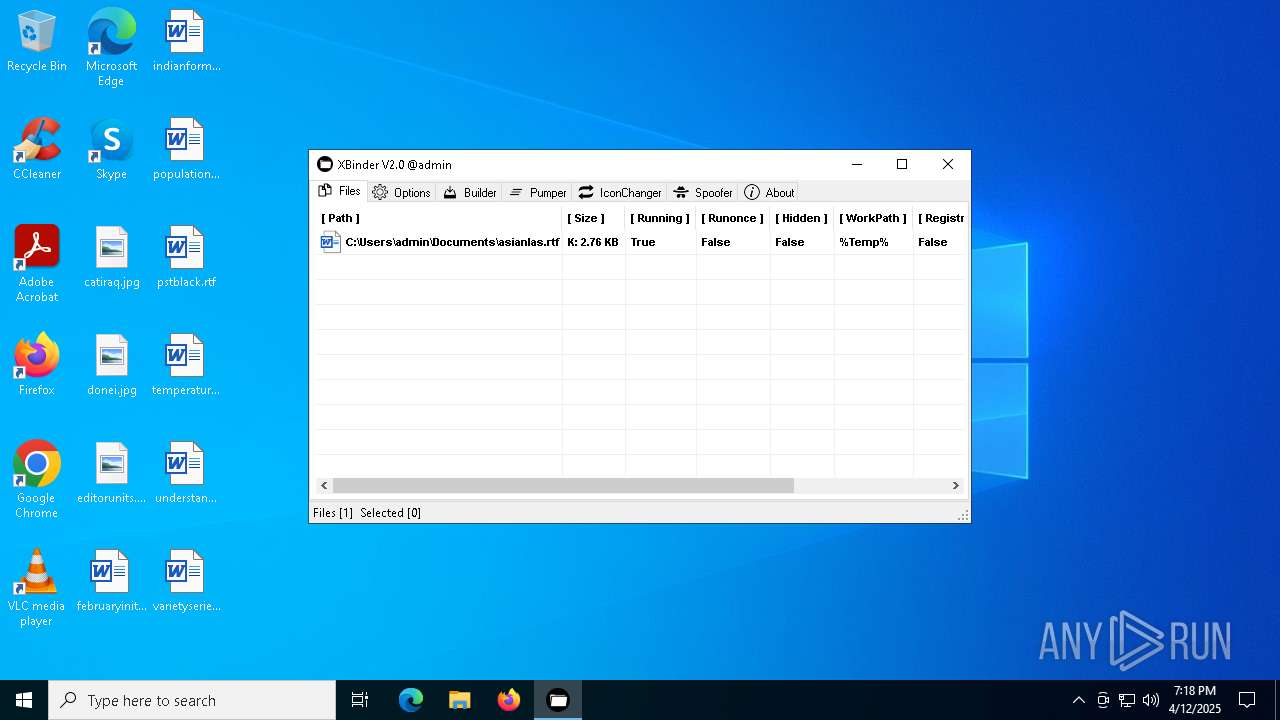
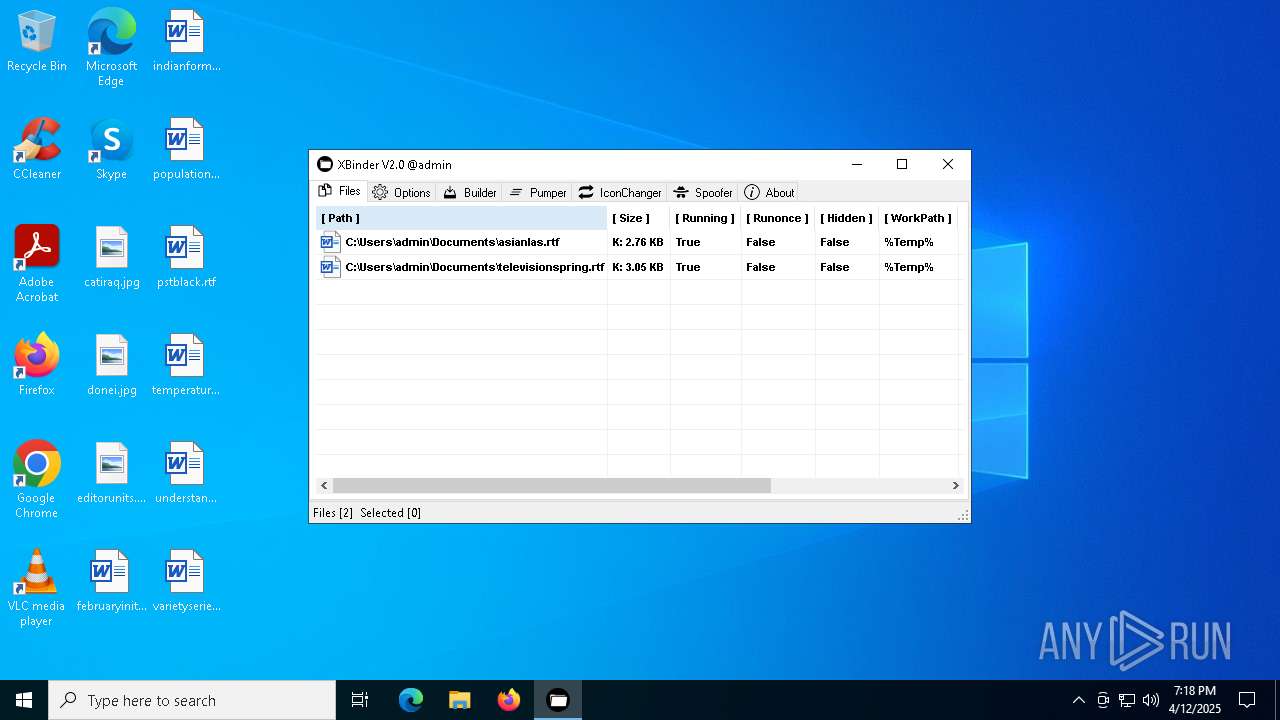
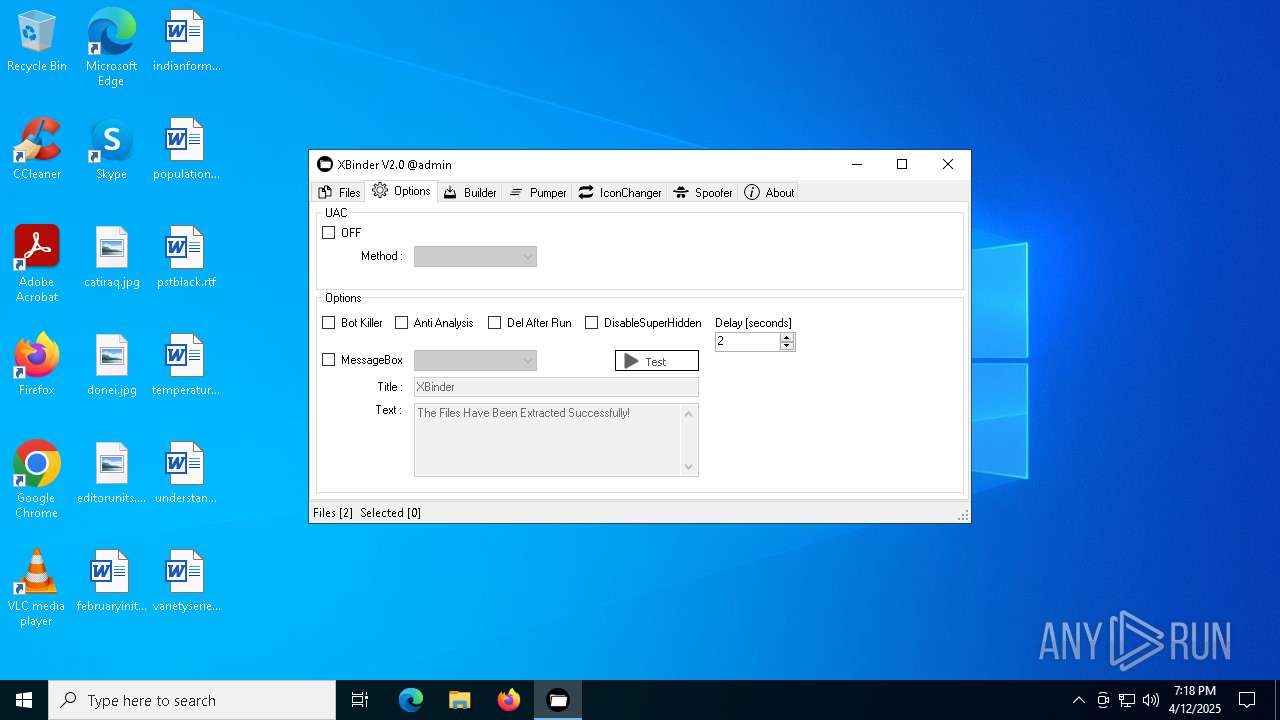
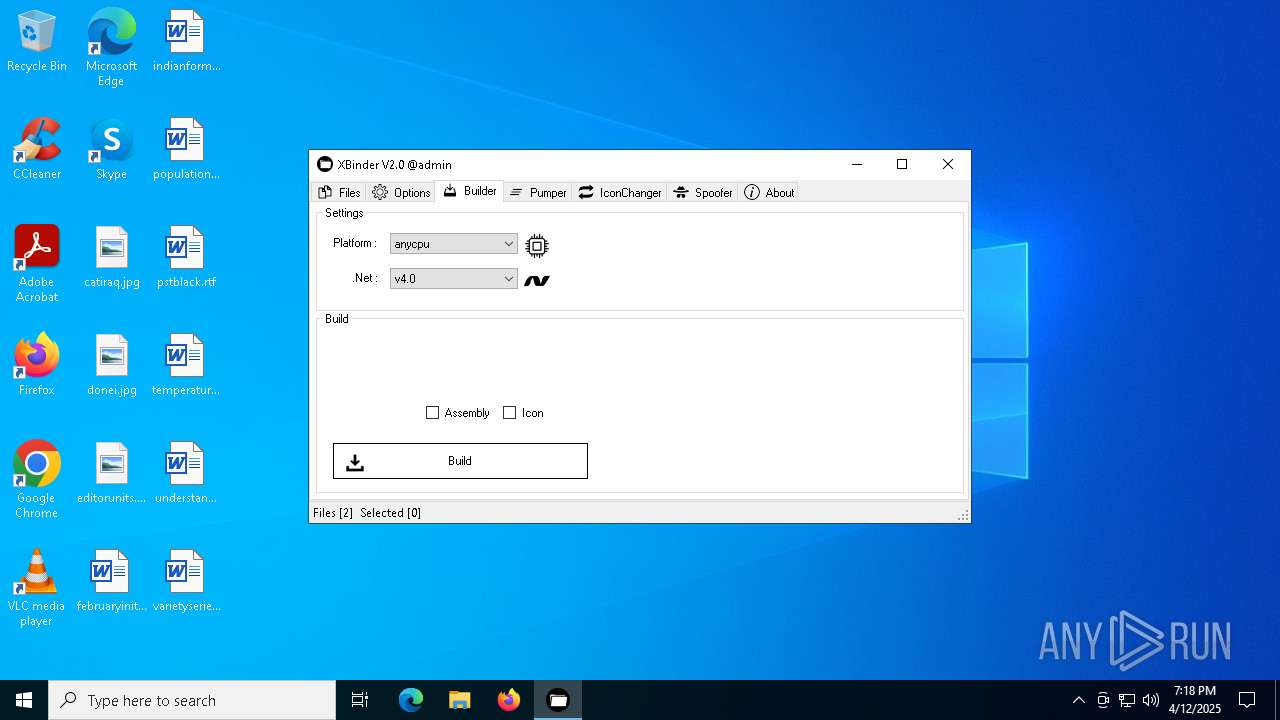
| File name: | XBinder v2.exe |
| Full analysis: | https://app.any.run/tasks/c2af95e0-49c0-487b-ba15-5fdab080c12a |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2025, 19:18:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | A98358EB7F4953AA6D60015CCD8506CE |
| SHA1: | D9BE0C9D6D968C1BAEF11027A7ACE6A0E869E75A |
| SHA256: | 21E0CC9EF715CC2147B9EC481B3FB876DBAE8A4491367B478513128D7F7B8555 |
| SSDEEP: | 24576:yxxxSxWxx7xxxxbfWfkNmePfTwjBZMt7+NI+6Vrw7id7:t8NmePfM66+d7 |
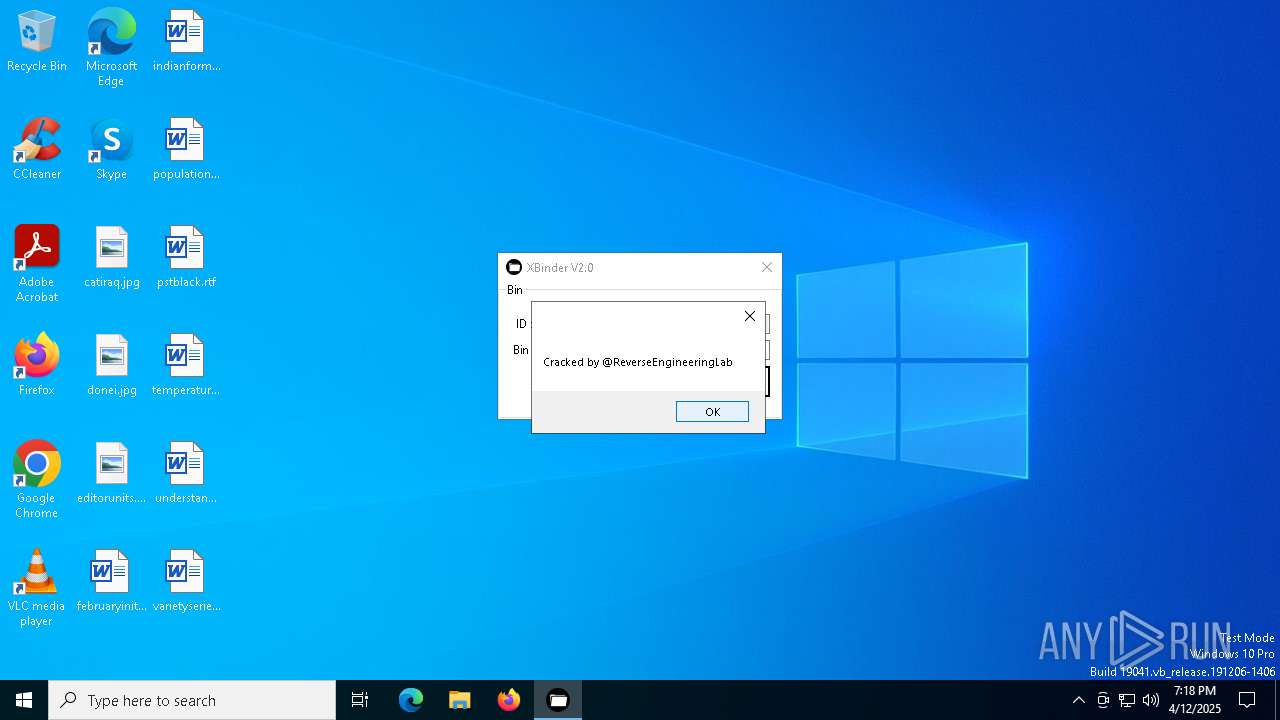
MALICIOUS
XORed URL has been found (YARA)
- XBinder v2.exe (PID: 1244)
SUSPICIOUS
There is functionality for capture public ip (YARA)
- XBinder v2.exe (PID: 1244)
Reads security settings of Internet Explorer
- XBinder v2.exe (PID: 1244)
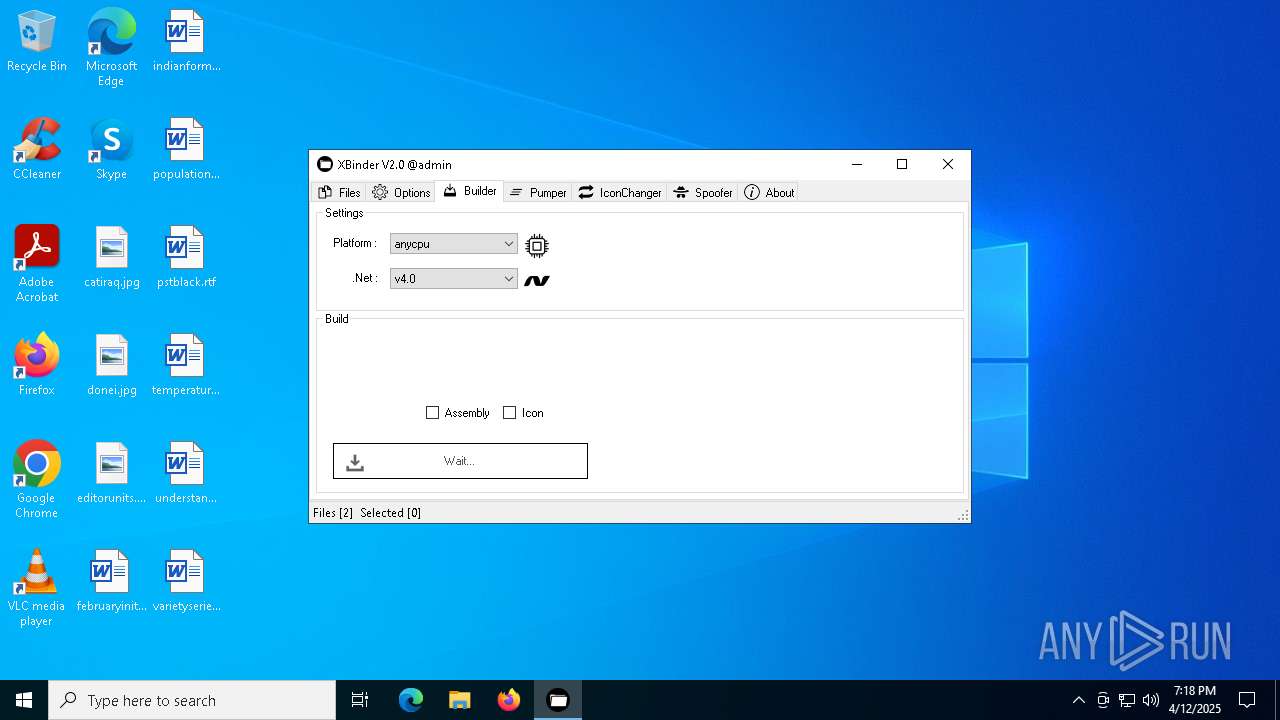
Executable content was dropped or overwritten
- vbc.exe (PID: 1328)
INFO
Reads the machine GUID from the registry
- XBinder v2.exe (PID: 1244)
- vbc.exe (PID: 1328)
Reads the computer name
- XBinder v2.exe (PID: 1244)
Checks supported languages
- XBinder v2.exe (PID: 1244)
- vbc.exe (PID: 1328)
- cvtres.exe (PID: 4188)
Create files in a temporary directory
- vbc.exe (PID: 1328)
- cvtres.exe (PID: 4188)
- XBinder v2.exe (PID: 1244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2022:09:15 00:32:03+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 48 |
| CodeSize: | 3605504 |
| InitializedDataSize: | 106496 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
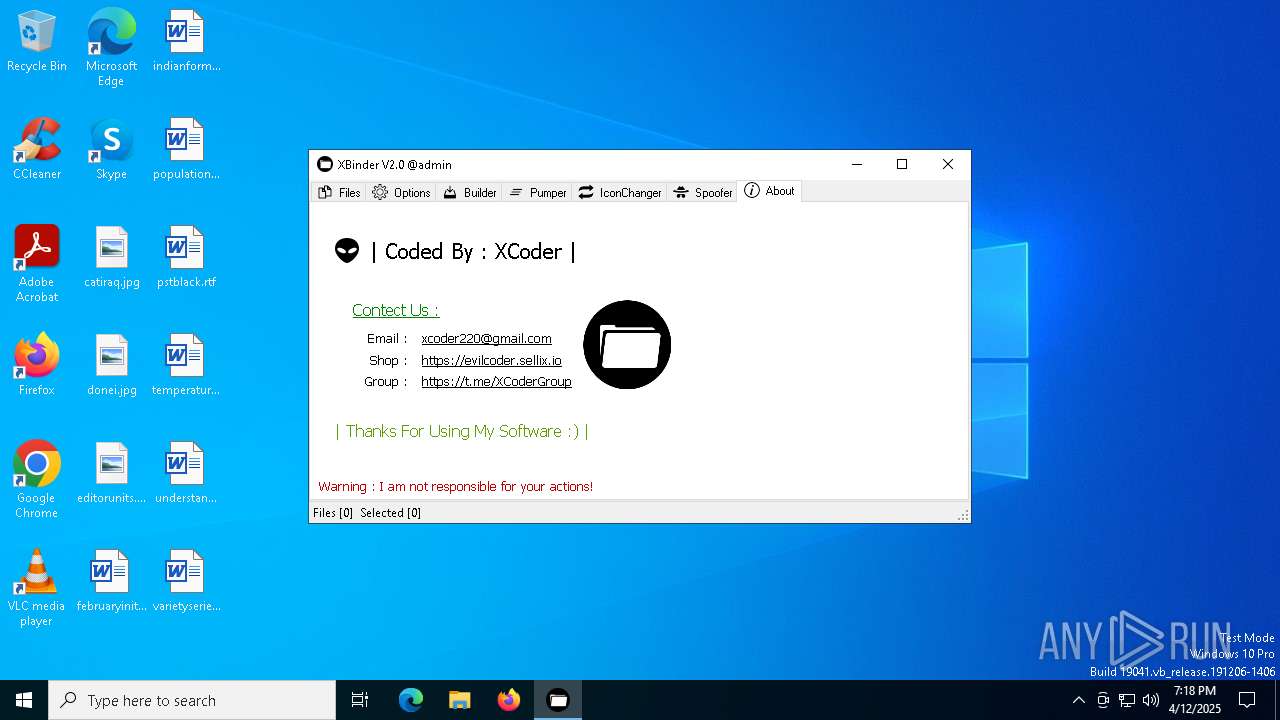
| Comments: | XCoder |
| CompanyName: | - |
| FileDescription: | XBinder |
| FileVersion: | 2.0.0.0 |
| InternalName: | XBinder.exe |
| LegalCopyright: | Copyright © 2022 |
| LegalTrademarks: | - |
| OriginalFileName: | XBinder.exe |
| ProductName: | XBinder |
| ProductVersion: | 2.0.0.0 |
| AssemblyVersion: | 2.0.0.0 |
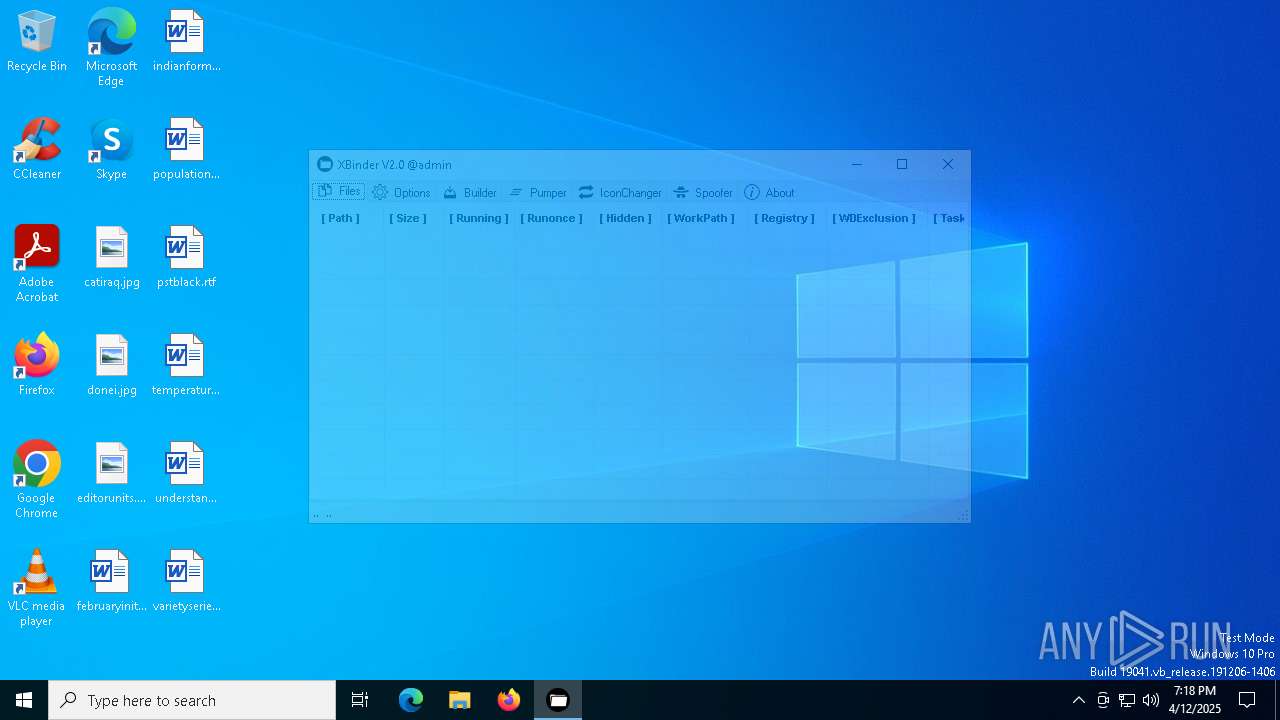
Total processes
131
Monitored processes
6
Malicious processes
1
Suspicious processes
0
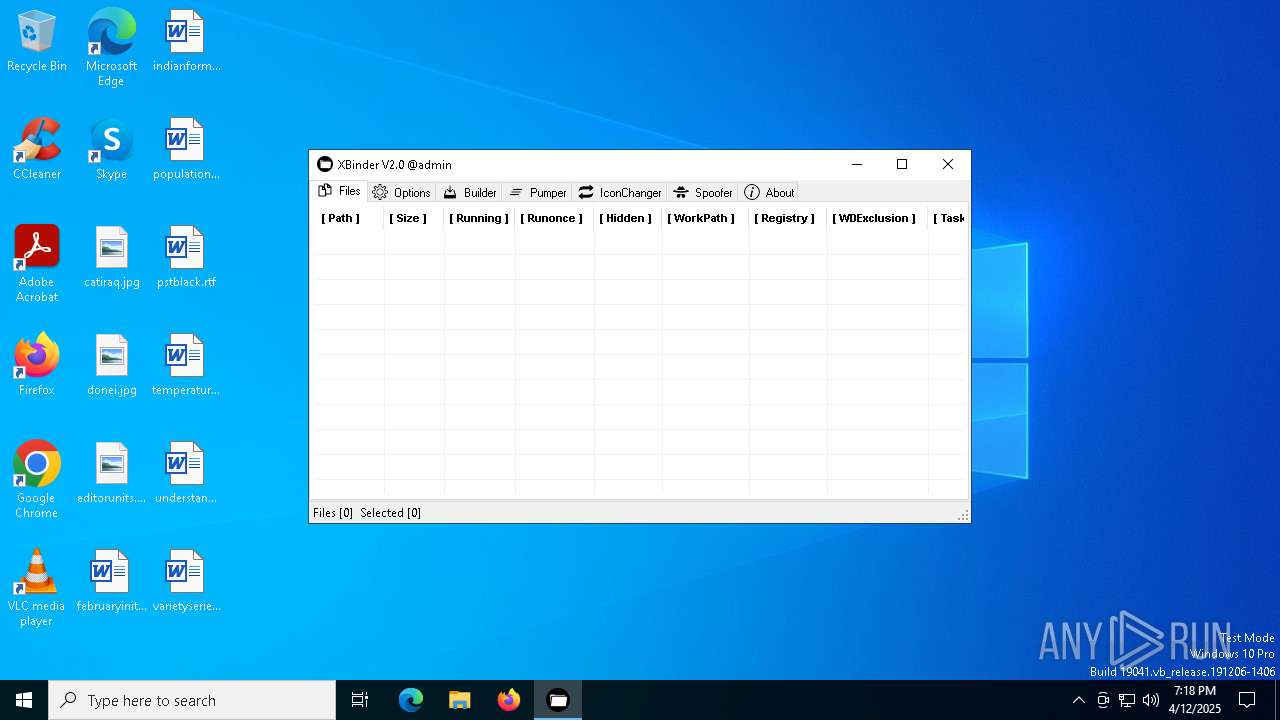
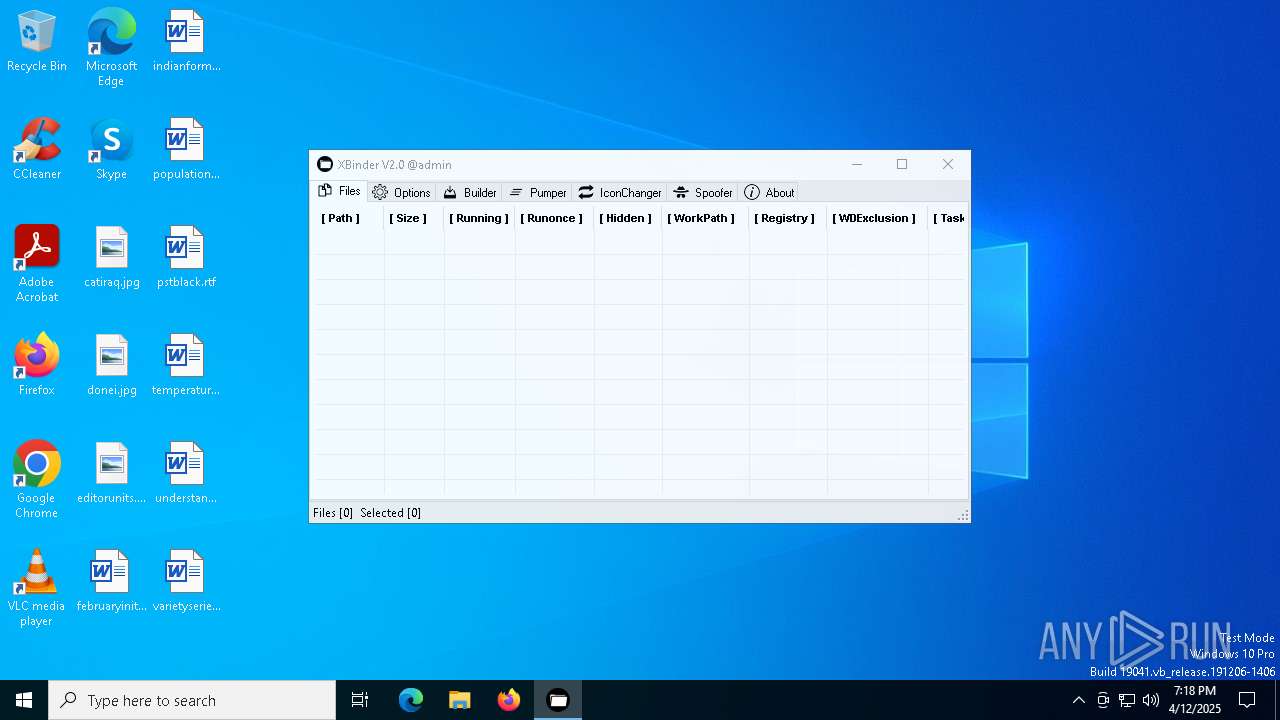
Behavior graph
Click at the process to see the details
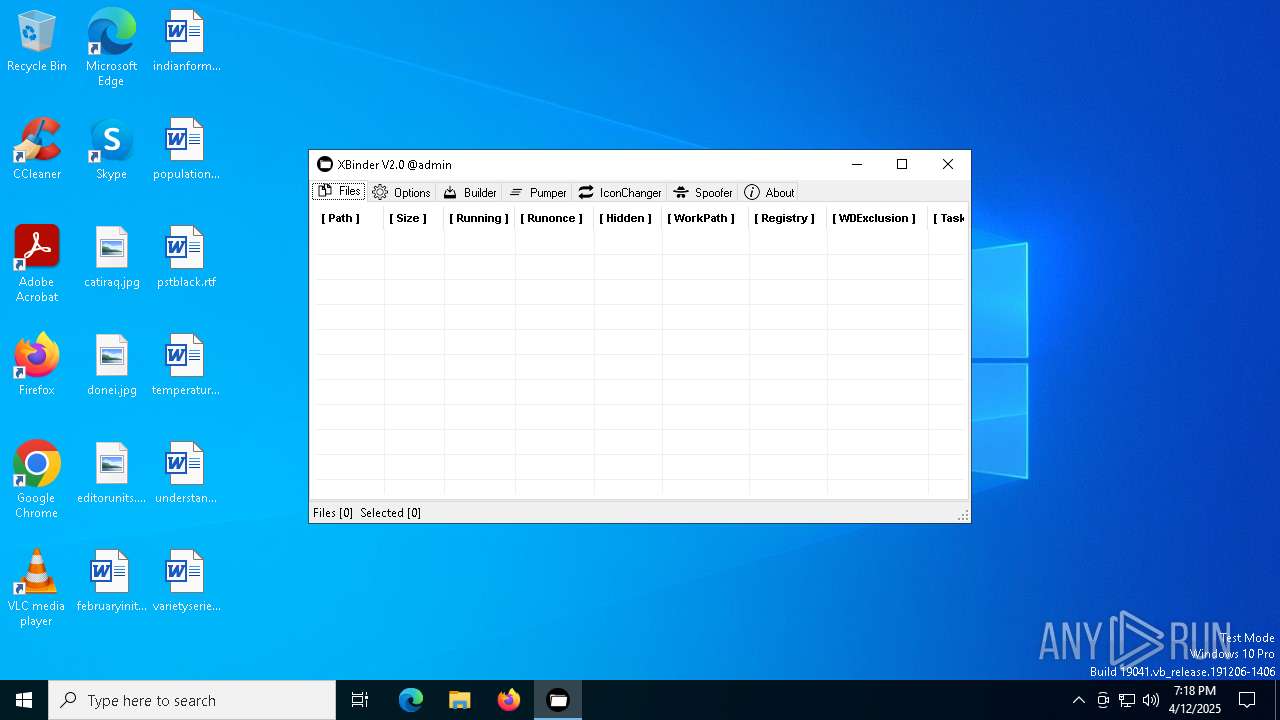
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1244 | "C:\Users\admin\AppData\Local\Temp\XBinder v2.exe" | C:\Users\admin\AppData\Local\Temp\XBinder v2.exe | explorer.exe | ||||||||||||
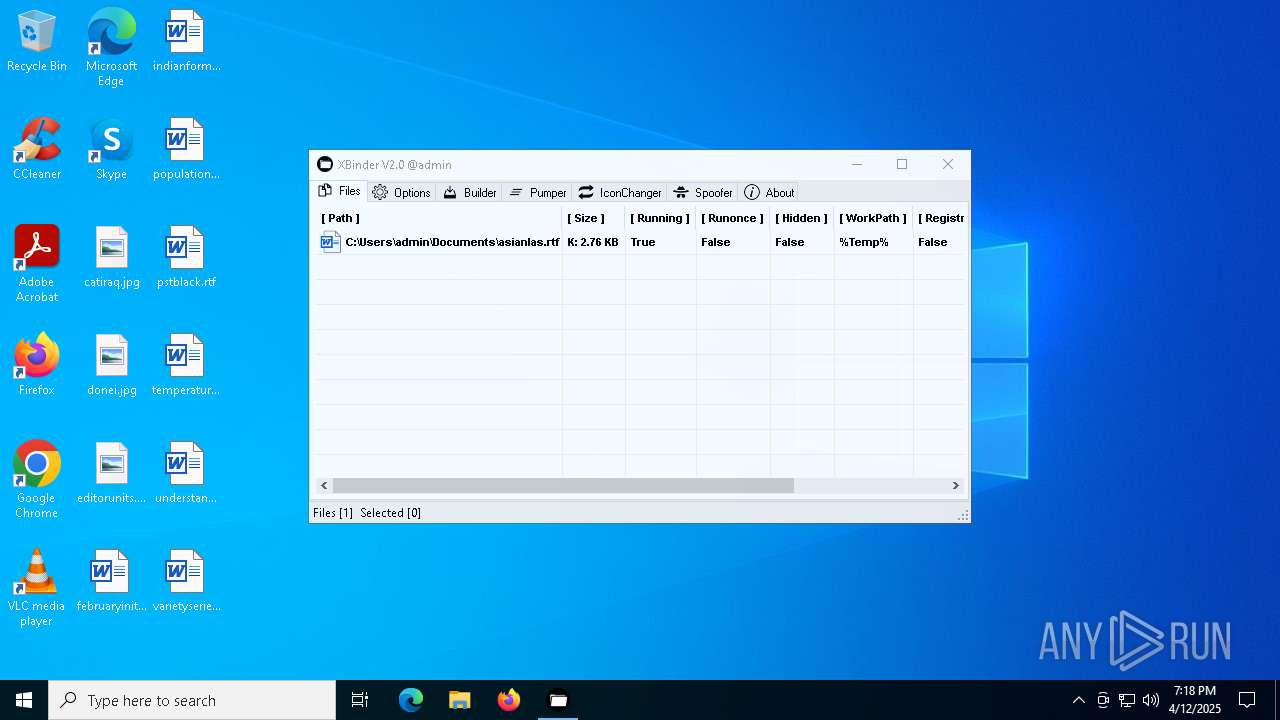
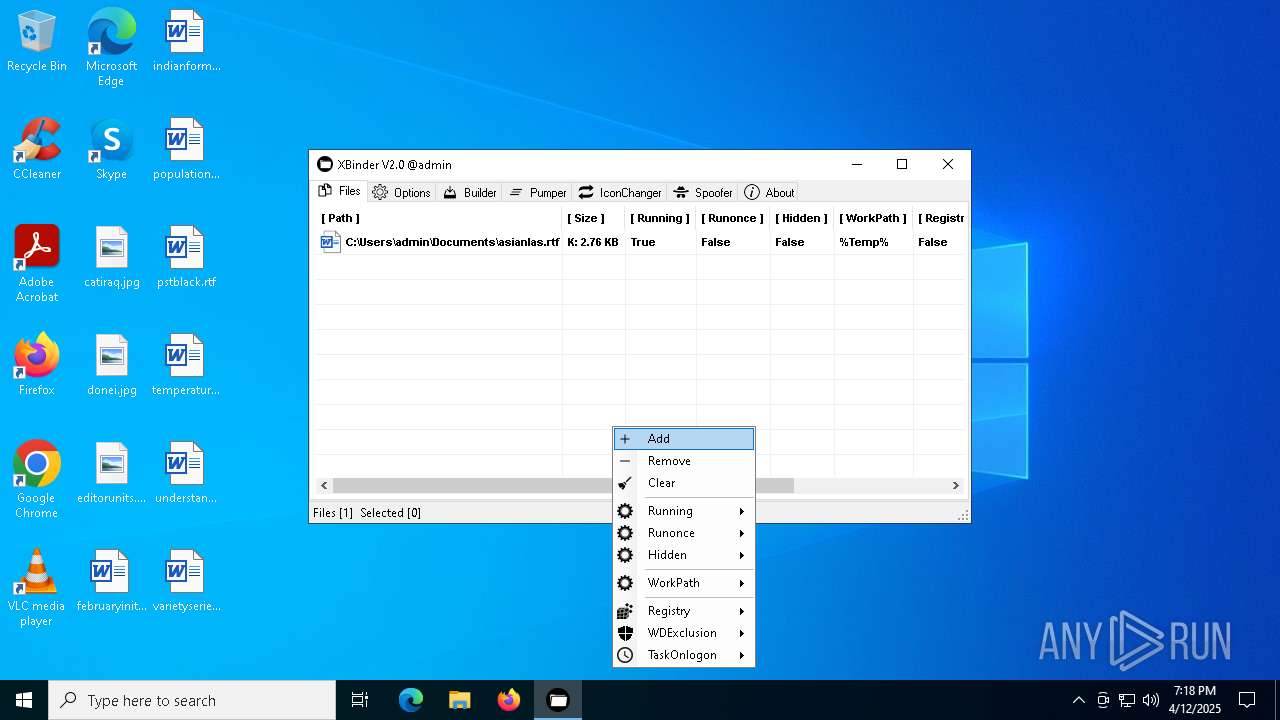
User: admin Integrity Level: MEDIUM Description: XBinder Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 1328 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\vbc.exe" /noconfig @"C:\Users\admin\AppData\Local\Temp\ucu4hfch.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\vbc.exe | XBinder v2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 14.8.9037.0 Modules
| |||||||||||||||
| 2268 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | vbc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4040 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4188 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES4A73.tmp" "C:\Users\admin\AppData\Local\Temp\vbcF1F10CD9CBF7408F9BEC611A1F6D65.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | vbc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
Total events
14 278
Read events
14 186
Write events
88
Delete events
4
Modification events
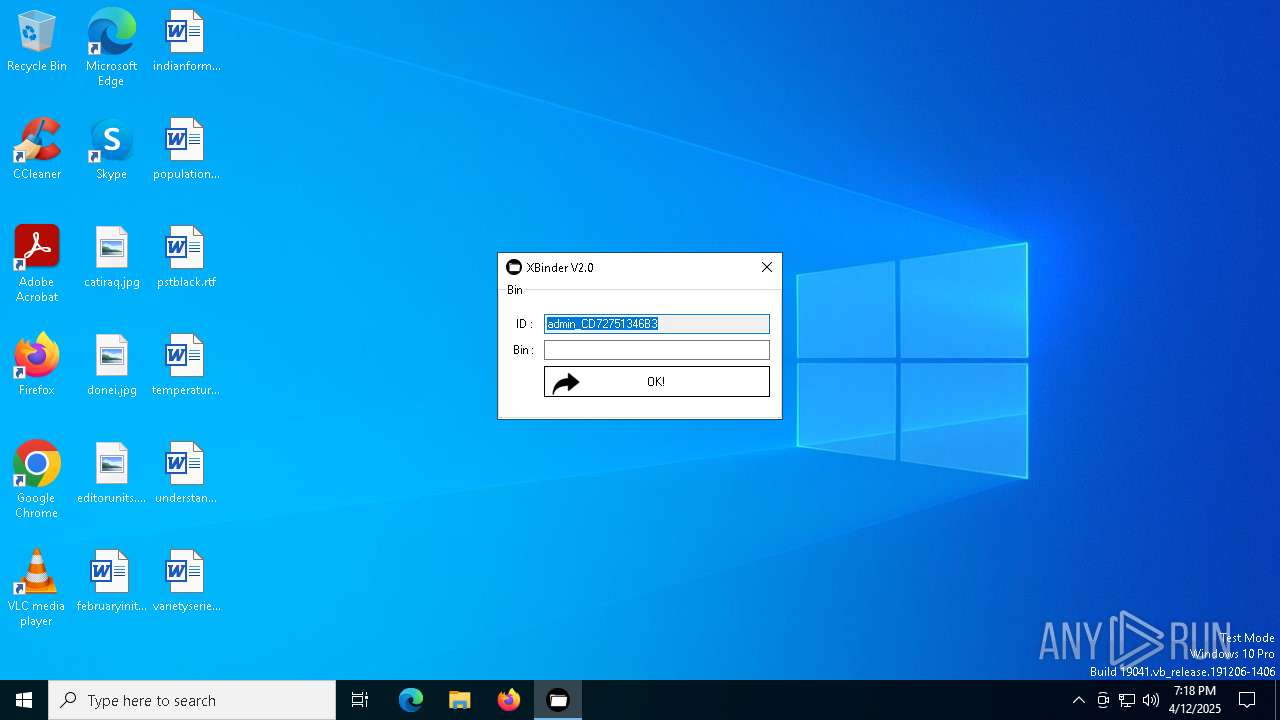
| (PID) Process: | (1244) XBinder v2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\XBinder |
| Operation: | write | Name: | License |
Value: | |||
| (PID) Process: | (1244) XBinder v2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Documents | |||
| (PID) Process: | (1244) XBinder v2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1244) XBinder v2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 04000000030000000E00000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (1244) XBinder v2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 040000000000000005000000020000000100000003000000FFFFFFFF | |||
| (PID) Process: | (1244) XBinder v2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 114 | |||
| (PID) Process: | (1244) XBinder v2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 91BCFA6700000000 | |||
| (PID) Process: | (1244) XBinder v2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Modules\NavPane |
| Operation: | write | Name: | ExpandedState |
Value: 12000000160014001F80CB859F6720028040B29B5540CC05AAB60000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000FFFF00000000000000000000160014001F60983FFBB4EAC18D42A78AD1F5659CBA930000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000FFFF00000000000000000000160014001F7840F05F6481501B109F0800AA002F954E0000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000000000000000000000000000160014001F706806EE260AA0D7449371BEB064C986830000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000FFFF00000000000000000000160014001F580D1A2CF021BE504388B07367FC96EF3C0000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000000000000000000000000000160014001F5425481E03947BC34DB131E946B44C8DD50000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000000000000000000000000000160014001F50E04FD020EA3A6910A2D808002B30309D0000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000FFFF000000000000000000003C003A001F44471A0359723FA74489C55595FE6B30EE260001002600EFBE1000000034E9025AA9B7D80155EC262BAAB7D8018F3827B5B0B7D80114000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000FFFF000000000000000000003C003A001F42665C8D01334507439B53224DE2ED1FE6260001002600EFBE11000000A1C1E0E0AF27D301F77F6305B0B7D8019F22F307B0B7D80114000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000000000000000000000000000940092003200000080004658D1892000474F4F474C457E312E5A49500000760009000400EFBE4658D1894658D1892E000000F55D05000000090000000000000000000000000000001F47700047006F006F0067006C0065004300680072006F006D00650045006E0074006500720070007200690073006500420075006E0064006C006500360034002E007A006900700000001C000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B0000000000000000000000000000005C005A00320099030000F2588C582000657874312E7A69700000420009000400EFBEF2588C58F2588C582E000000A70D00000000160000000000000000000000000000003A91F90065007800740031002E007A0069007000000018000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B00000000000000000000000000000050004E00310000000000F258CE5810006578743100003A0009000400EFBEF258CE58F258CE582E000000DE0200000000170000000000000000000000000000001CB7E9006500780074003100000014000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000FFFF000000000000000000006E006C0032001EEC0500F258826620005052454645527E312E5A49500000500009000400EFBEF2588266F25882662E00000028D4000000001900000000000000000000000000000005A1250050007200650066006500720065006E006300650073002E007A006900700000001C000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B0000000000000000000000000000005800560032007E0D0000F258866620006578742E7A697000400009000400EFBEF2588666F25886662E0000002AD4000000001E0000000000000000000000000000005498DF006500780074002E007A0069007000000016000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B00000000000000000000000000000062006000310000000000F2588D6610005052454645527E310000480009000400EFBEF2588D66F2588F662E0000002E2F0100000017000000000000000000000000000000CF57130150007200650066006500720065006E00630065007300000018000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B0000000000000000000000000000004C004A00310000000000F2589066100065787400380009000400EFBEF2589066F25890662E000000E88D0100000007000000000000000000000000000000DE8B4100650078007400000012000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000000000000000000000000000780076003200C1862C03F258957920004F4D4E495F327E312E5A495000005A0009000400EFBEF258E578F25895792E0000007C600500000039000000000000000000000000000000DE6FED006F006D006E0069005F00320033005F00310030005F0032003000320034005F002E007A006900700000001C000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B00000000000000000000000000000070006E0032007E0D0000F2587B7920004348524F4D497E312E5A49500000520009000400EFBEF2587B79F2587B792E000000C260050000001800000000000000000000000000000028F586006300680072006F006D00690075006D005F006500780074002E007A006900700000001C000000010000004D0000001C00000031535053A66A63283D95D211B5D600C04FD918D0000000002D00000031535053357EC777E31B5043A48C7563D727776D1100000002000000000B000000000000000000000000000000 | |||
| (PID) Process: | (1244) XBinder v2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\rtf |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (1244) XBinder v2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\rtf |
| Operation: | write | Name: | 0 |
Value: 14001F50E04FD020EA3A6910A2D808002B30309D14002E80922B16D365937A46956B92703ACA08AF660032000D0B0000504E4E842000617369616E6C61732E72746600004A0009000400EFBE504E4E843F5A8D512E000000E25D050000000D00000000000000000000000000000080C7420061007300690061006E006C00610073002E0072007400660000001C000000 | |||
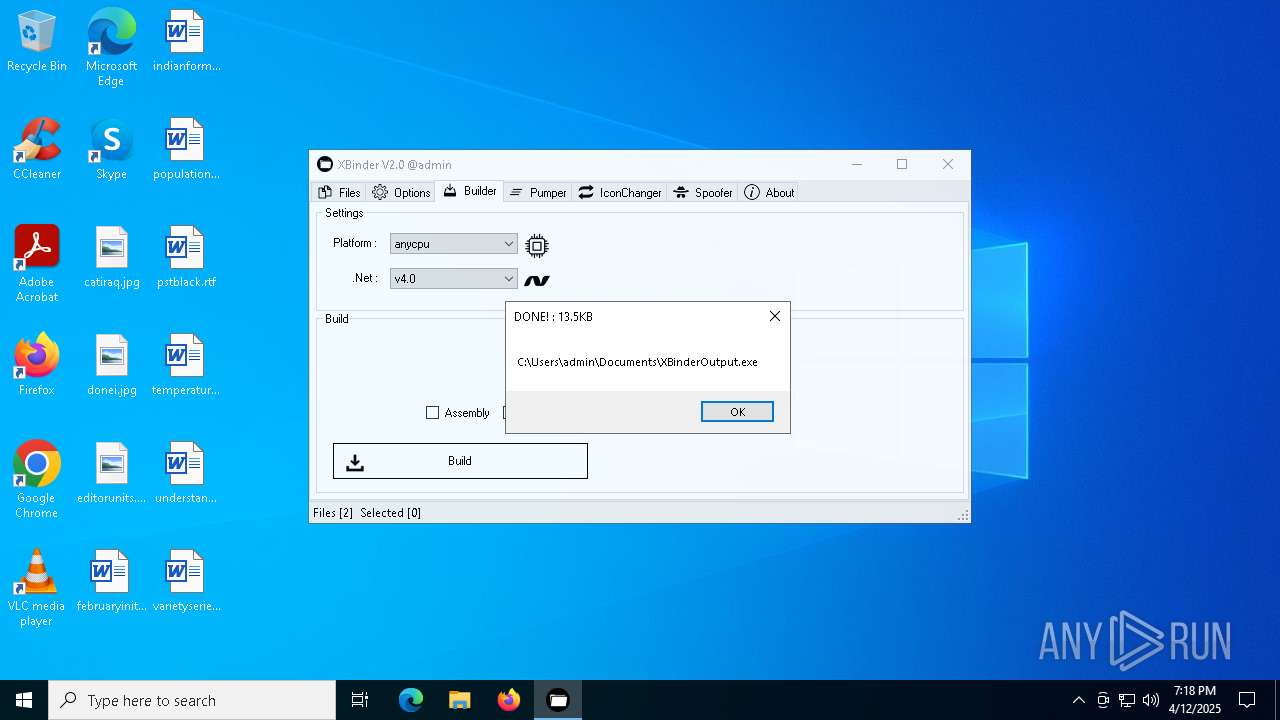
Executable files
1
Suspicious files
5
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1244 | XBinder v2.exe | C:\Users\admin\AppData\Local\Temp\tmp48DD.tmp | binary | |
MD5:CD10C64E9E602425B492C2CA49FE5875 | SHA256:E10580C824C214F67BAC130E572CC4D647C8DAD7B5F6E3CC965FE1C041AAD281 | |||
| 1244 | XBinder v2.exe | C:\Users\admin\AppData\Local\Temp\ucu4hfch.cmdline | text | |
MD5:D53B8C2FD34BDBFE3E2A35A05A114328 | SHA256:B28F8241A19D72D544789E2FBBBFE30313D3069653CAA2218DBD646E14D55BCC | |||
| 1244 | XBinder v2.exe | C:\Users\admin\AppData\Local\Temp\juxhfohm.Resources | binary | |
MD5:D391282CFA5D8904A245549155DE73C3 | SHA256:AAD4CBBB360296AA66D81CECD3C2F855B5ADD17967850E7B769F0BF345FEAA3E | |||
| 1328 | vbc.exe | C:\Users\admin\AppData\Local\Temp\vbc37000D17A28C498AAE9EF9C1A71FFBB.TMP | binary | |
MD5:F07B3CC9BCAF18C11F55737A9B84A835 | SHA256:881C320366D6C57ED9F20E3F223153CC15F7C5D59376182EBCE66CD512B88CC0 | |||
| 1328 | vbc.exe | C:\Users\admin\AppData\Local\Temp\vbcF1F10CD9CBF7408F9BEC611A1F6D65.TMP | binary | |
MD5:CE7EE761D5F0A9CCC4E37A527ACE11D6 | SHA256:D8DB9A7547590C3AFDB024EA67EC9026F367DC18C4D944F4980397628036108E | |||
| 1244 | XBinder v2.exe | C:\Users\admin\AppData\Local\Temp\ucu4hfch.0.vb | text | |
MD5:A0D9A687C9ED98D4F271BBB912D5CDA0 | SHA256:6522C78BACB8123E0D8C45B1066C6572E30F6F2DD5EDC46E882B70F593E746CA | |||
| 1328 | vbc.exe | C:\Users\admin\AppData\Local\Temp\ucu4hfch.out | text | |
MD5:6B56283BC73F26FABF4186FAF5CF8BBC | SHA256:E69B52A99D73A625DEE63B44C379DD84801F1FF66474C18EBBCC39D738CFA240 | |||
| 4188 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES4A73.tmp | binary | |
MD5:4F4AEE930CEDD6B03A8A8F036AAB6A9B | SHA256:5B1397E3E693A6EB9C6B043B11B57B51CA9A2D61ECBF1273D42EA054474CCB52 | |||
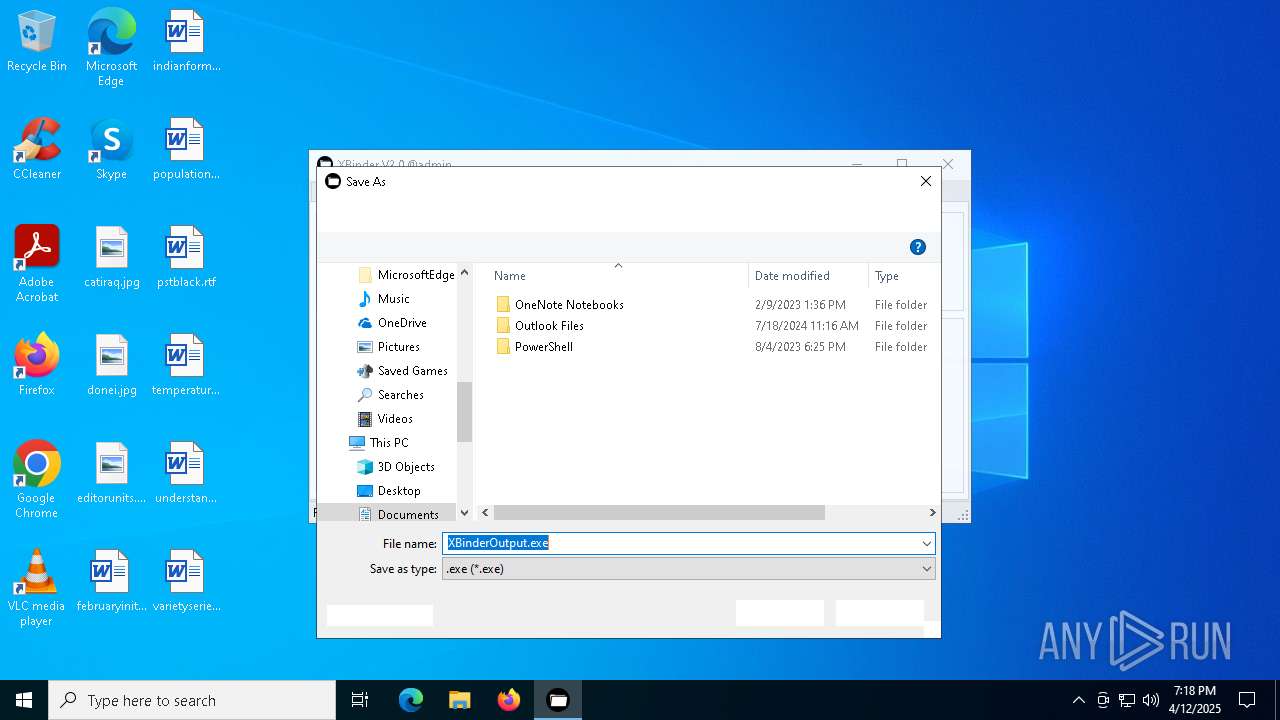
| 1328 | vbc.exe | C:\Users\admin\Documents\XBinderOutput.exe | executable | |
MD5:E53355E14AAA2D6AD8B81A7AFE0B7A75 | SHA256:A2AF35D3020A3ECC7DFDE8BC0A3A78542DF6AC383FD38FC923771EEE5F960309 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
17
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4436 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4436 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.18:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4436 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4436 | SIHClient.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |