| File name: | iBUixhq.png |
| Full analysis: | https://app.any.run/tasks/818d6581-7e4b-4884-92bc-7de88ec2012c |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 14:13:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | image/png |
| File info: | PNG image data, 957 x 622, 8-bit/color RGBA, non-interlaced |
| MD5: | B0CEEA3C3E29EFDFFA398EB393BDDA0B |
| SHA1: | 61033F719658FD2265BF266C1B181230EC8F0144 |
| SHA256: | 21C8E2E481CDFF3A9C86427AA7B4A98F06114F5C528CF5D5D4A0049966631204 |
| SSDEEP: | 12288:tzge9OF25eQd+lRraK6rl+jLigP8AxaeCa+4fsDMGFDxjhOiyPk71TnC1QT+wFo:Oe9K25VdApLPXxC48x1DFCi6Mo |
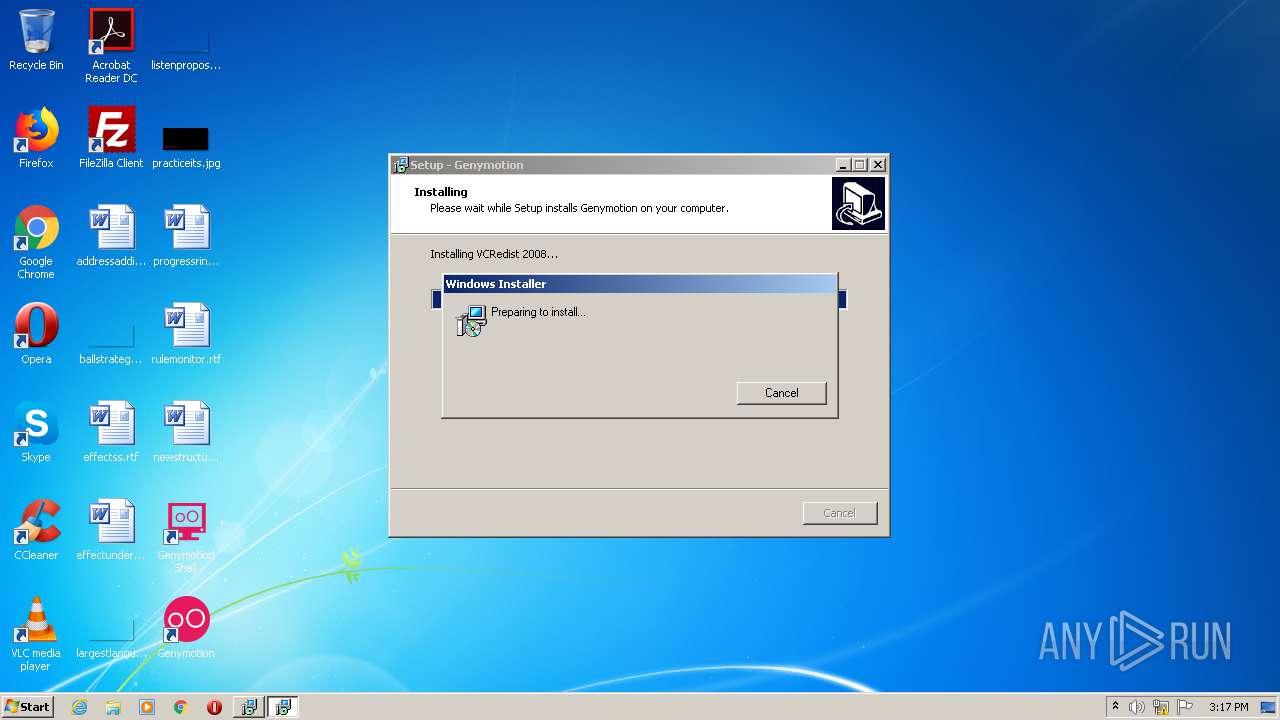
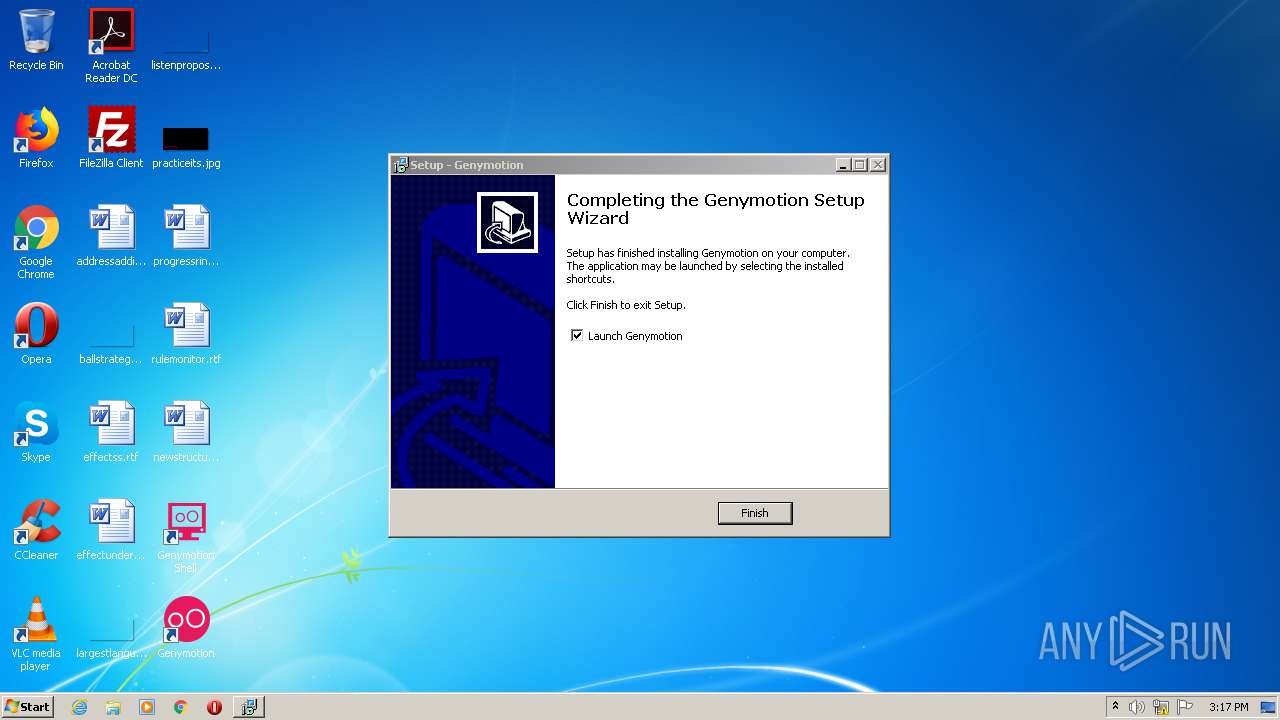
MALICIOUS
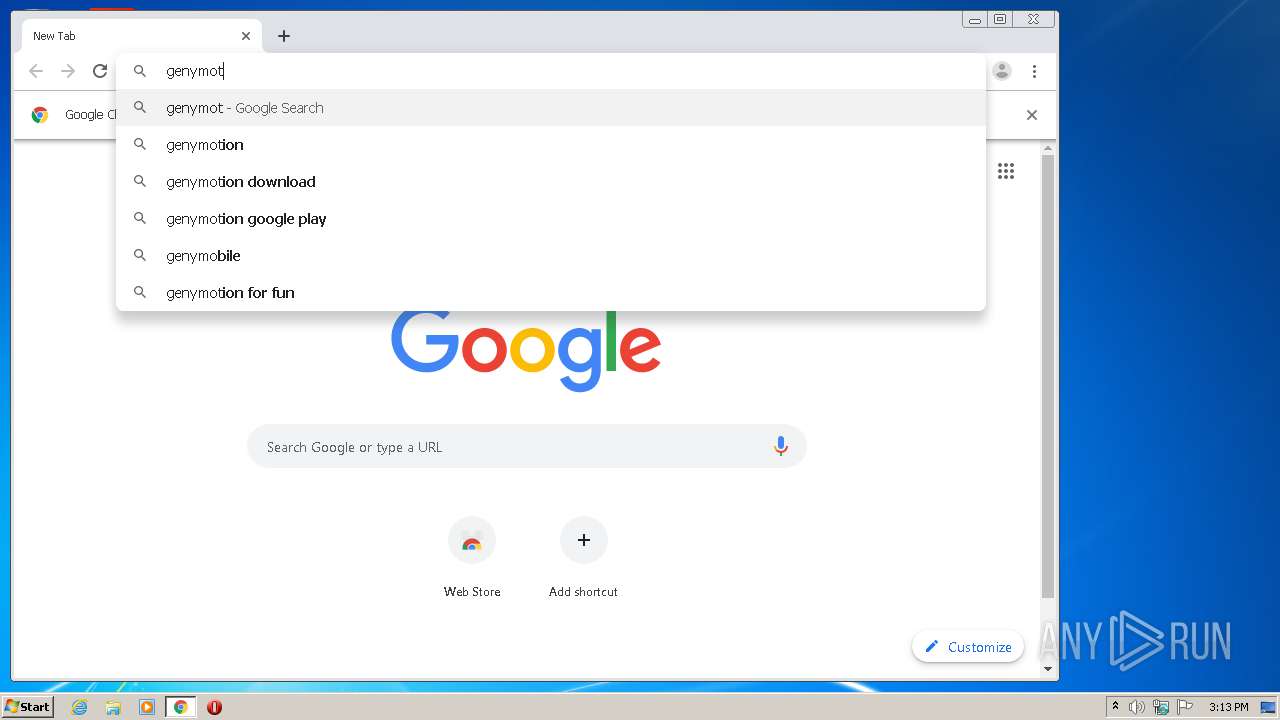
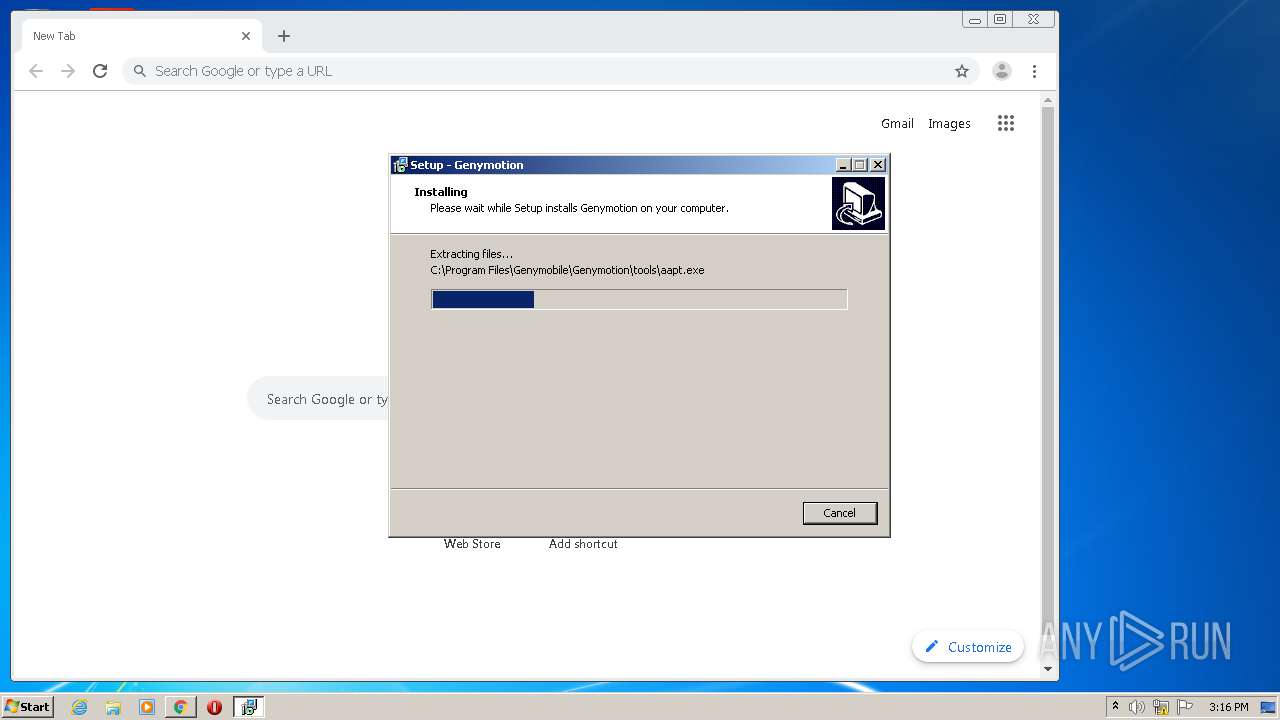
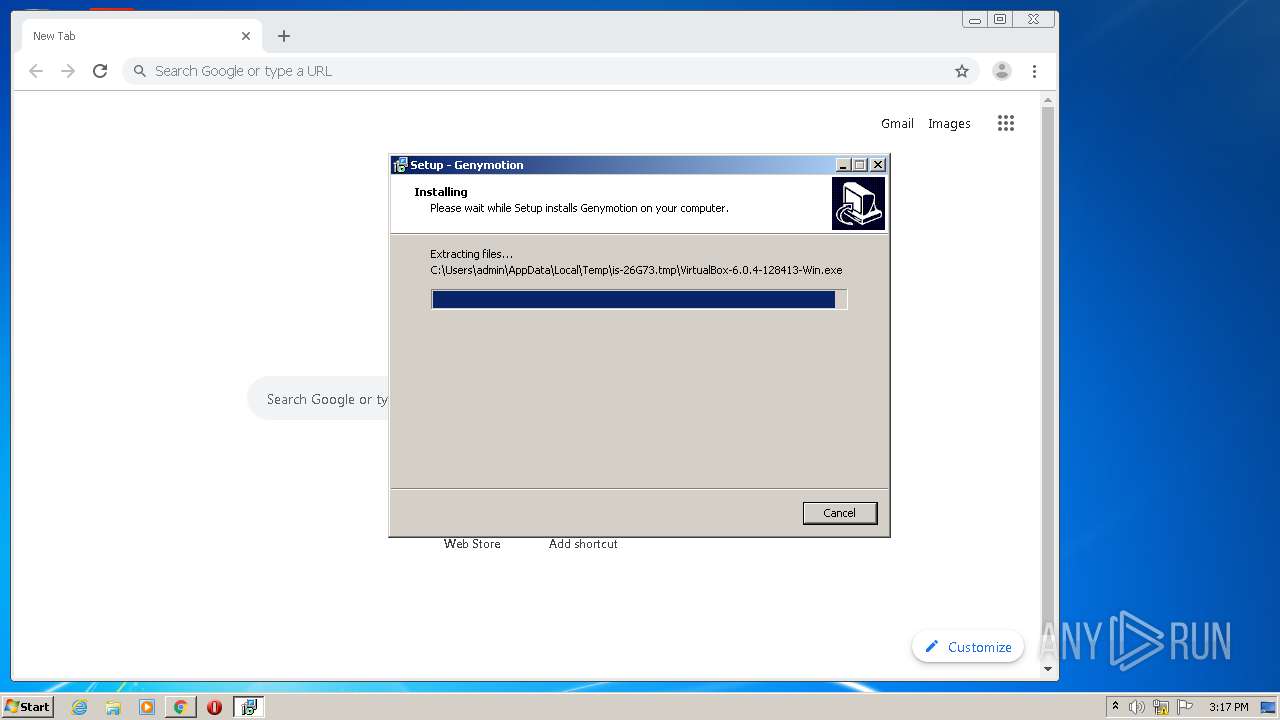
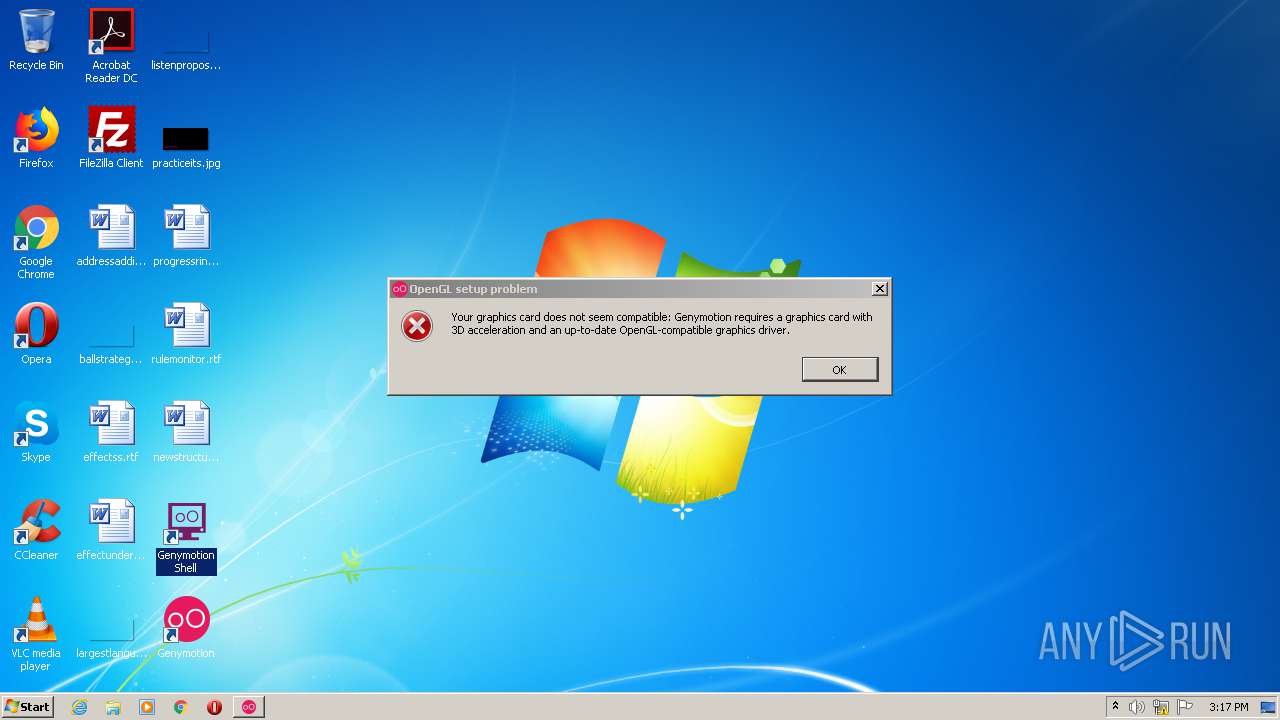
Application was dropped or rewritten from another process
- genymotion-3.1.0-vbox.exe (PID: 3376)
- genymotion-3.1.0-vbox.exe (PID: 3272)
- adb.exe (PID: 1260)
- install.exe (PID: 2068)
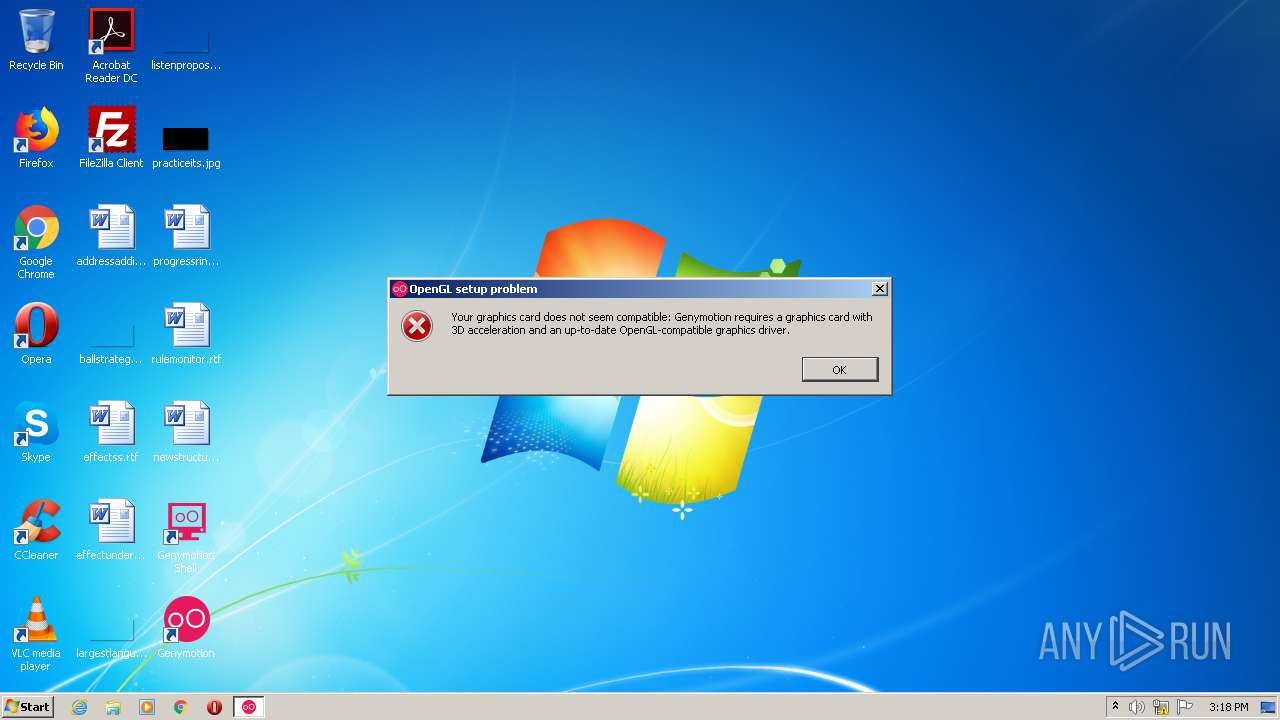
- genymotion.exe (PID: 3216)
- genymotion.exe (PID: 2160)
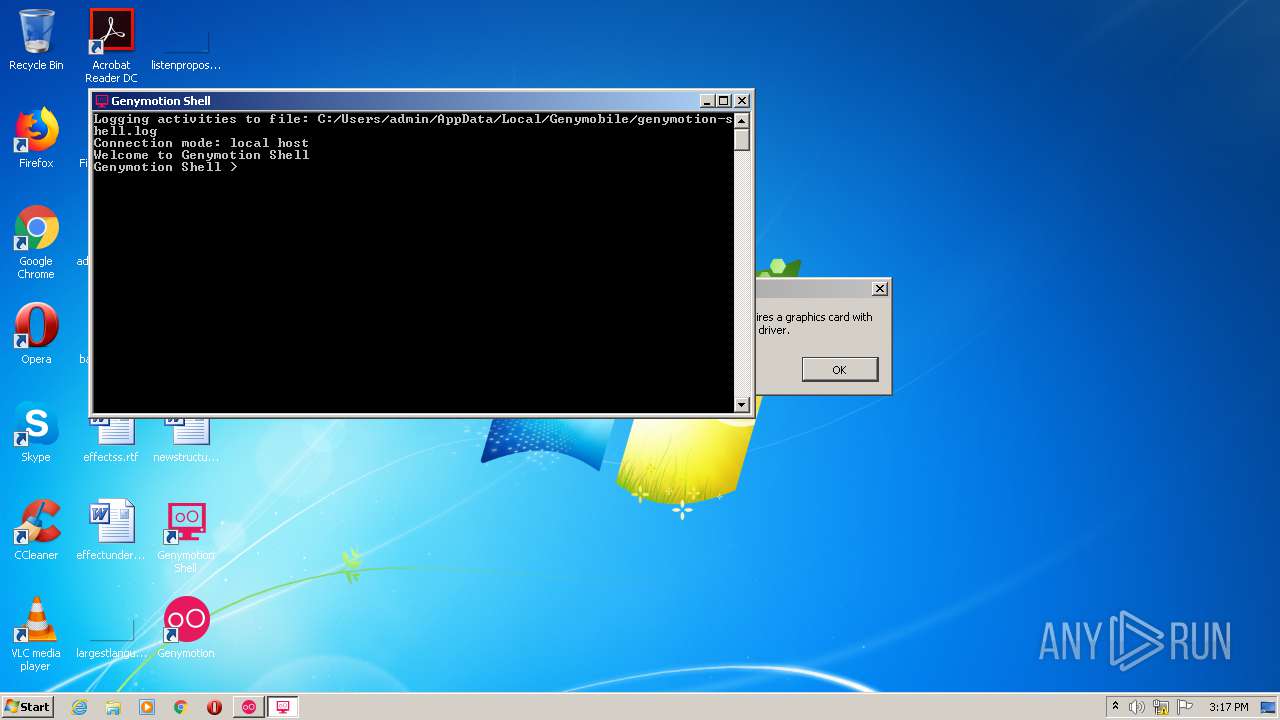
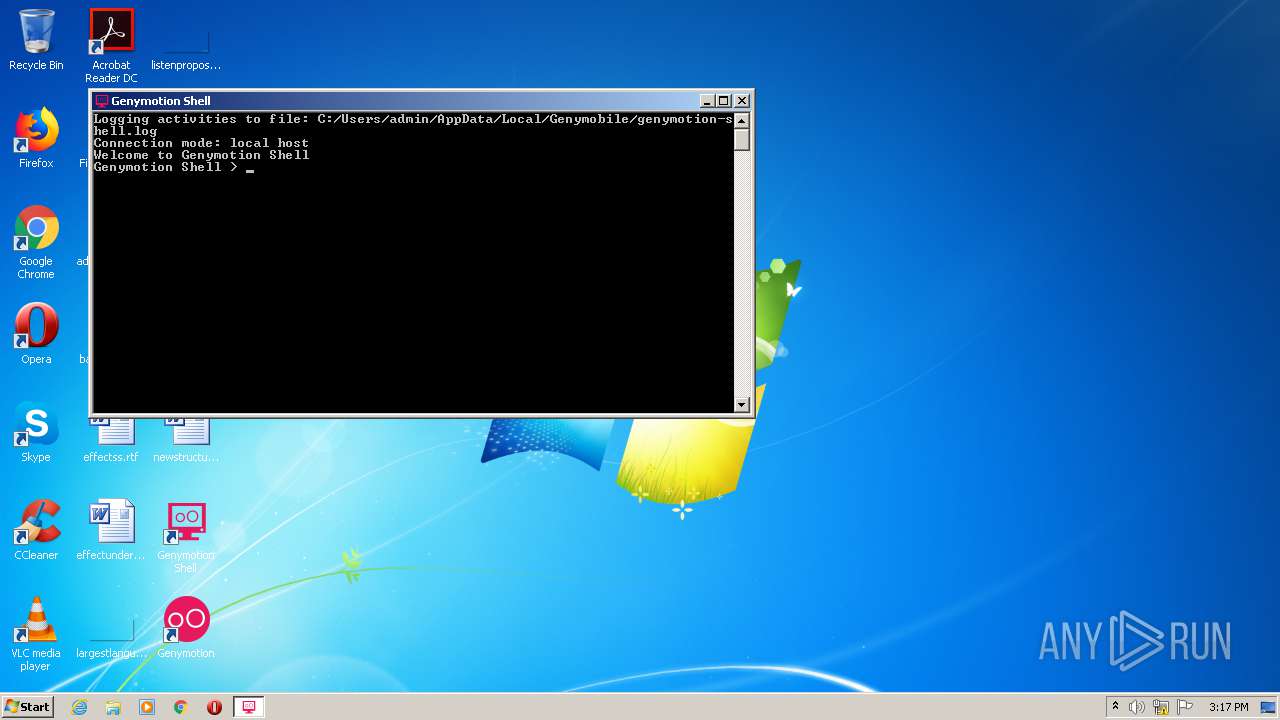
- genyshell.exe (PID: 1764)
- genymotion.exe (PID: 1636)
Loads dropped or rewritten executable
- adb.exe (PID: 1260)
- install.exe (PID: 2068)
- genymotion.exe (PID: 2160)
- genymotion.exe (PID: 3216)
- genyshell.exe (PID: 1764)
- genymotion.exe (PID: 1636)
Changes settings of System certificates
- msiexec.exe (PID: 3816)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2656)
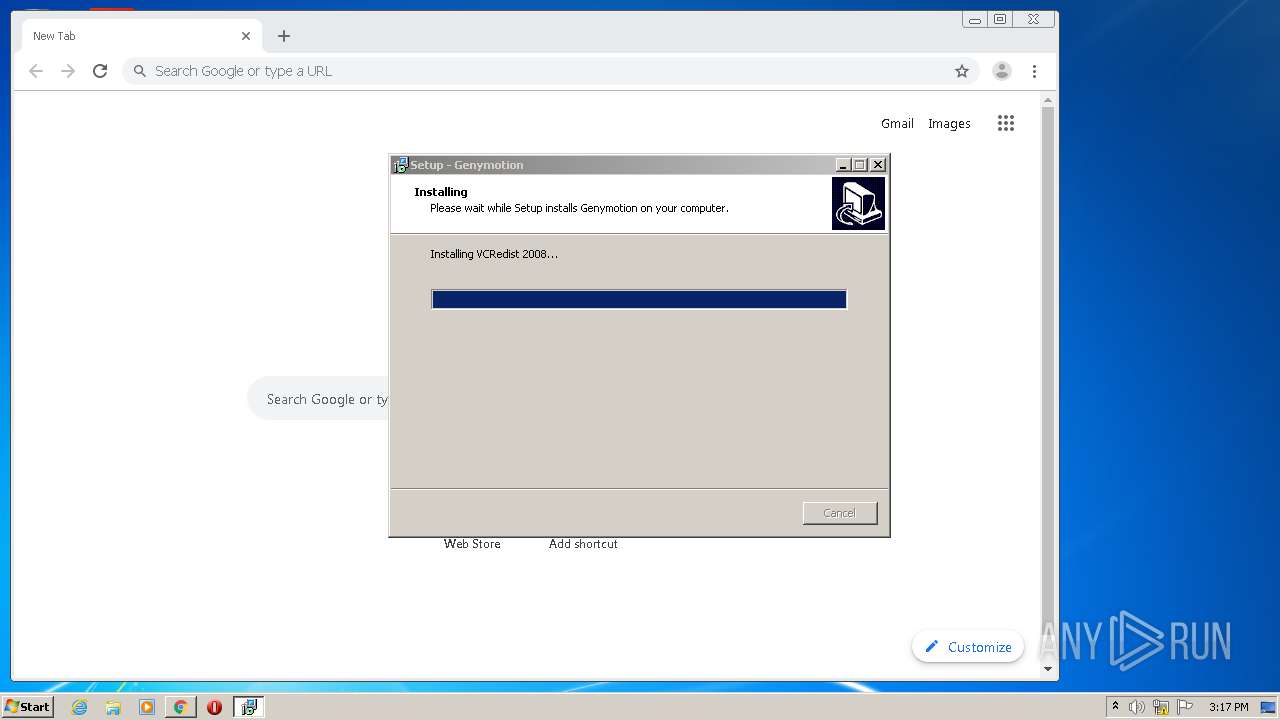
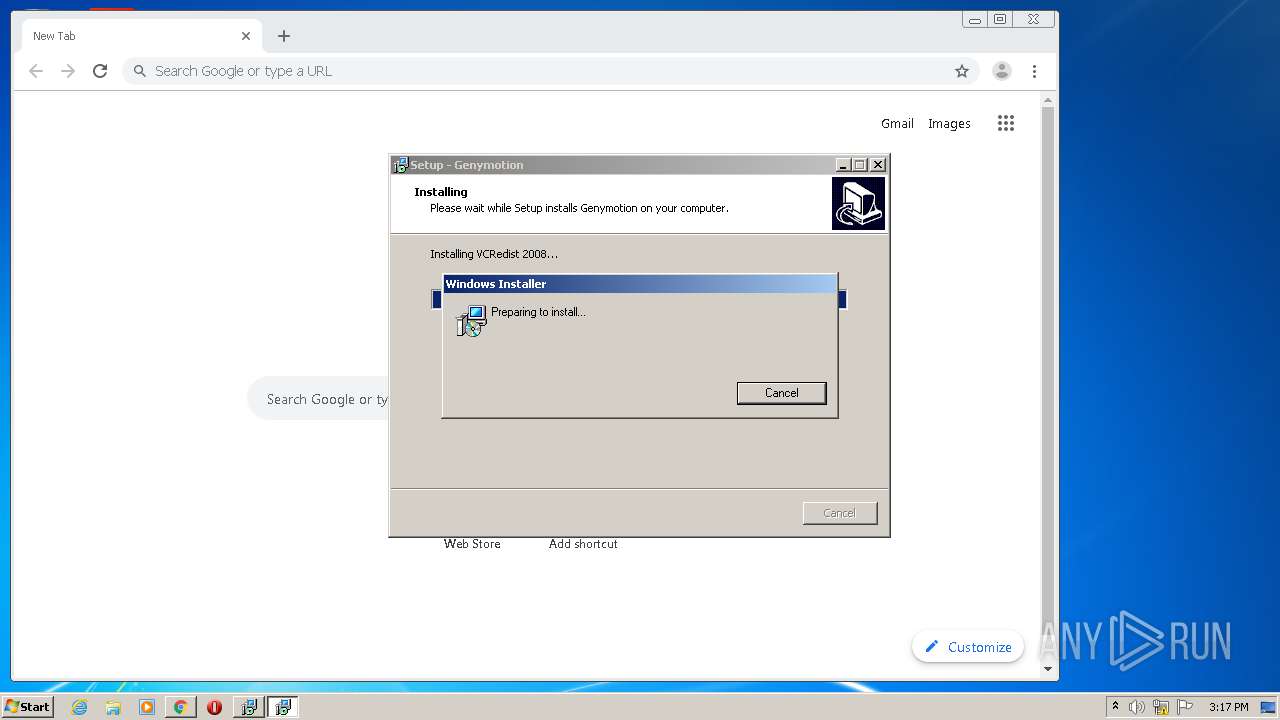
Executable content was dropped or overwritten
- chrome.exe (PID: 2656)
- genymotion-3.1.0-vbox.exe (PID: 3376)
- genymotion-3.1.0-vbox.exe (PID: 3272)
- genymotion-3.1.0-vbox.tmp (PID: 868)
- vcredist.exe (PID: 2700)
- msiexec.exe (PID: 3816)
Executed as Windows Service
- vssvc.exe (PID: 3488)
Creates files in the Windows directory
- msiexec.exe (PID: 3816)
Removes files from Windows directory
- msiexec.exe (PID: 3816)
Adds / modifies Windows certificates
- msiexec.exe (PID: 3816)
INFO
Reads the hosts file
- chrome.exe (PID: 1360)
- chrome.exe (PID: 2656)
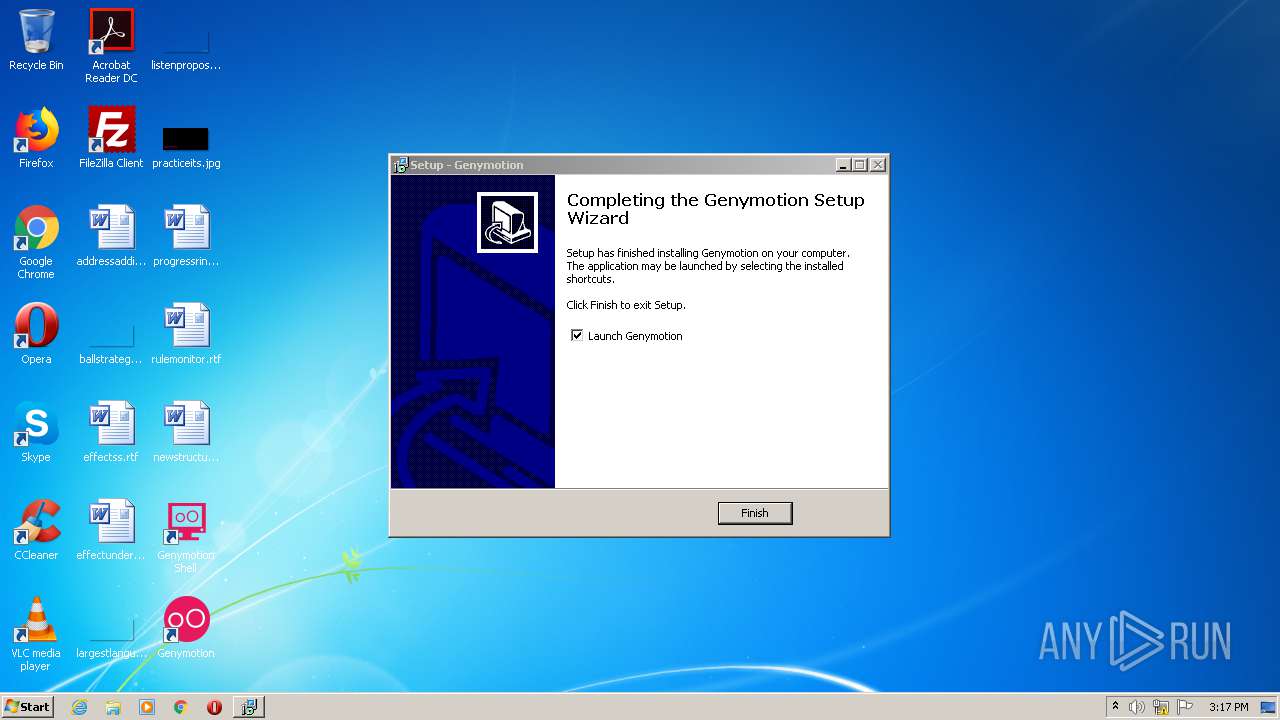
Manual execution by user
- chrome.exe (PID: 2656)
- genymotion.exe (PID: 2160)
- genyshell.exe (PID: 1764)
- genymotion.exe (PID: 1636)
Reads settings of System Certificates
- chrome.exe (PID: 2656)
- msiexec.exe (PID: 3816)
- chrome.exe (PID: 1360)
Application was dropped or rewritten from another process
- genymotion-3.1.0-vbox.tmp (PID: 1744)
- genymotion-3.1.0-vbox.tmp (PID: 868)
- vcredist.exe (PID: 2700)
Application launched itself
- chrome.exe (PID: 2656)
Reads Internet Cache Settings
- chrome.exe (PID: 2656)
Dropped object may contain Bitcoin addresses
- genymotion-3.1.0-vbox.tmp (PID: 868)
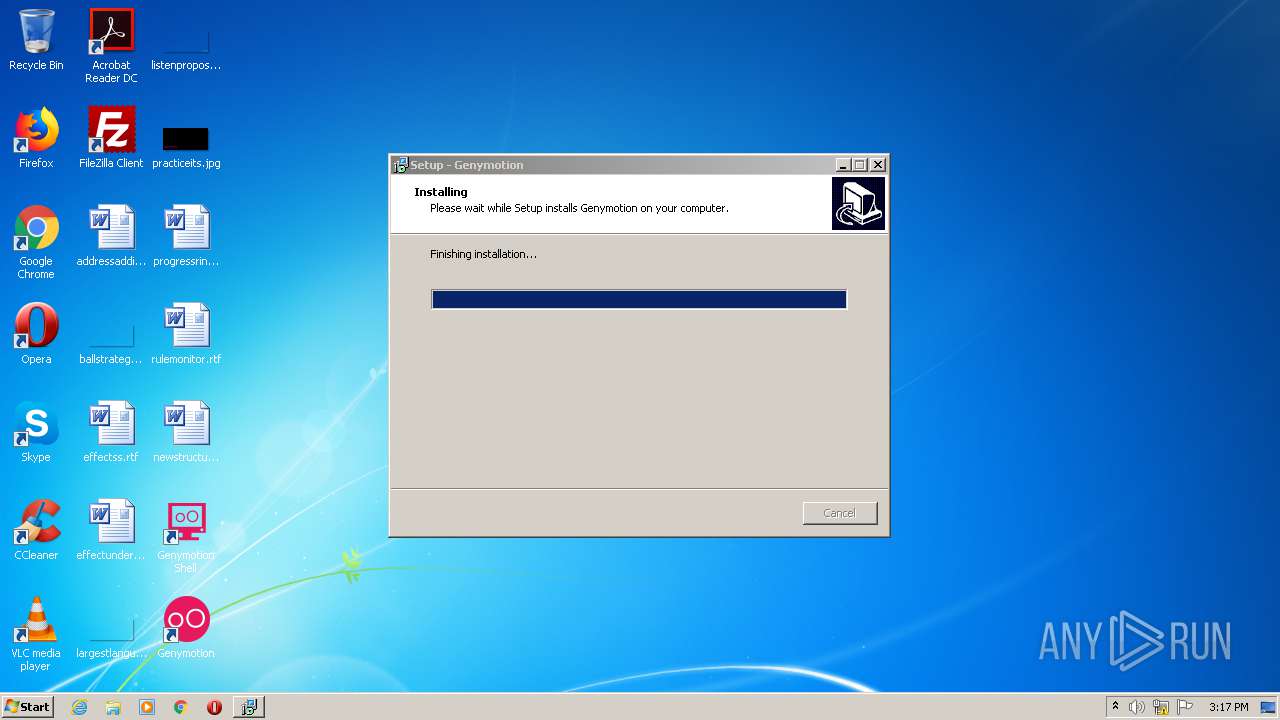
Creates a software uninstall entry
- genymotion-3.1.0-vbox.tmp (PID: 868)
- msiexec.exe (PID: 3816)
Searches for installed software
- msiexec.exe (PID: 3816)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3488)
Creates files in the program directory
- genymotion-3.1.0-vbox.tmp (PID: 868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .png | | | Portable Network Graphics (100) |
|---|
EXIF
PNG
| ImageWidth: | 957 |
|---|---|
| ImageHeight: | 622 |
| BitDepth: | 8 |
| ColorType: | RGB with Alpha |
| Compression: | Deflate/Inflate |
| Filter: | Adaptive |
| Interlace: | Noninterlaced |
| SRGBRendering: | Perceptual |
| Gamma: | 2.2 |
Composite
| ImageSize: | 957x622 |
|---|---|
| Megapixels: | 0.595 |
Total processes
103
Monitored processes
57
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,15077161354090932547,10694151386962842214,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1385994604574199516 --mojo-platform-channel-handle=2076 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,15077161354090932547,10694151386962842214,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15917827663518079912 --mojo-platform-channel-handle=5040 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,15077161354090932547,10694151386962842214,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11278354866000900518 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,15077161354090932547,10694151386962842214,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7752019912193805603 --mojo-platform-channel-handle=3280 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,15077161354090932547,10694151386962842214,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5530513428727283990 --mojo-platform-channel-handle=5276 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,15077161354090932547,10694151386962842214,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10034827476445168949 --mojo-platform-channel-handle=5236 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | "C:\Windows\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\AppData\Local\Temp\iBUixhq.png | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 868 | "C:\Users\admin\AppData\Local\Temp\is-4LRVM.tmp\genymotion-3.1.0-vbox.tmp" /SL5="$40146,253703463,57856,C:\Users\admin\Downloads\genymotion-3.1.0-vbox.exe" /SPAWNWND=$3014A /NOTIFYWND=$40136 | C:\Users\admin\AppData\Local\Temp\is-4LRVM.tmp\genymotion-3.1.0-vbox.tmp | genymotion-3.1.0-vbox.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Genymobile\Genymotion\tools\adb.exe" kill-server | C:\Program Files\Genymobile\Genymotion\tools\adb.exe | genymotion-3.1.0-vbox.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,15077161354090932547,10694151386962842214,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=14626866162307584848 --mojo-platform-channel-handle=1568 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 057
Read events
2 385
Write events
1 650
Delete events
22
Modification events
| (PID) Process: | (836) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: rundll32.exe | |||
| (PID) Process: | (836) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
| (PID) Process: | (2232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2656-13239036822709375 |
Value: 259 | |||
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
Executable files
111
Suspicious files
531
Text files
866
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0B1A97-A60.pma | — | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\82c4427f-6a7e-41ef-8f0d-51bbe6234d91.tmp | — | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFf836f.TMP | text | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFf8553.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
62
DNS requests
46
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
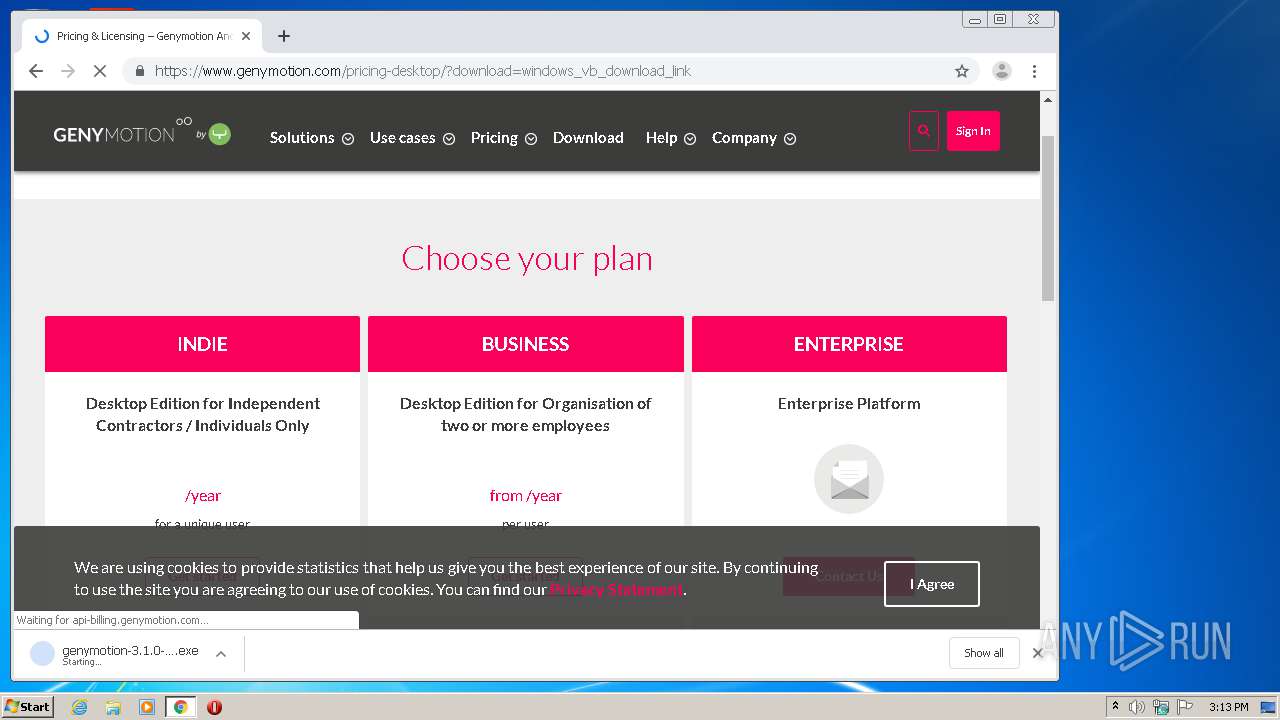
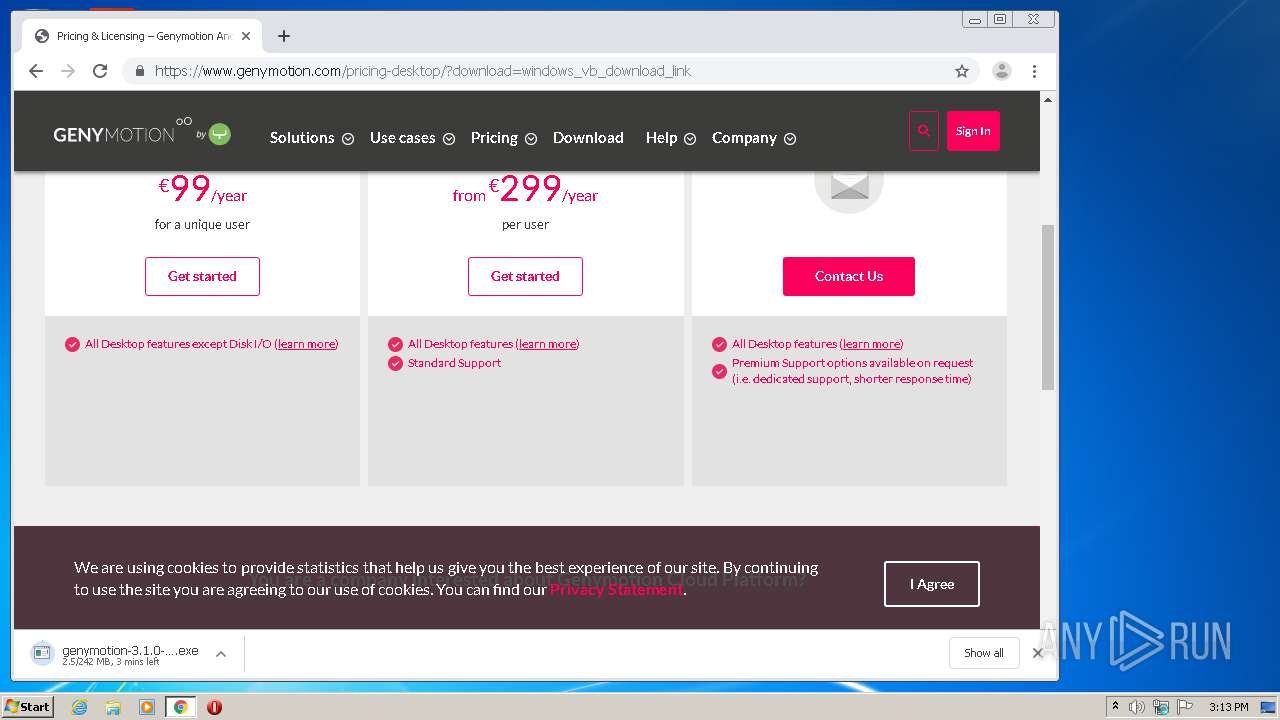
1360 | chrome.exe | GET | 302 | 216.58.207.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
1360 | chrome.exe | GET | 302 | 216.58.207.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
1360 | chrome.exe | GET | 200 | 185.48.9.15:80 | http://r4---sn-x2pm-3uf6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=84.17.55.74&mm=28&mn=sn-x2pm-3uf6&ms=nvh&mt=1594563138&mv=m&mvi=4&pl=23&shardbypass=yes | PL | crx | 823 Kb | whitelisted |
1360 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
1360 | chrome.exe | GET | 200 | 176.126.58.204:80 | http://r1---sn-x2pm-3ufk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=84.17.55.74&mm=28&mn=sn-x2pm-3ufk&ms=nvh&mt=1594563138&mv=m&mvi=1&pl=23&shardbypass=yes | PL | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1360 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1360 | chrome.exe | 172.217.18.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1360 | chrome.exe | 216.58.212.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1360 | chrome.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1360 | chrome.exe | 216.58.207.46:443 | apis.google.com | Google Inc. | US | whitelisted |
1360 | chrome.exe | 172.217.16.142:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
1360 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
1360 | chrome.exe | 172.217.22.14:443 | consent.google.com | Google Inc. | US | whitelisted |
1360 | chrome.exe | 172.217.18.106:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
1360 | chrome.exe | 172.217.18.14:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
consent.google.com |
| shared |