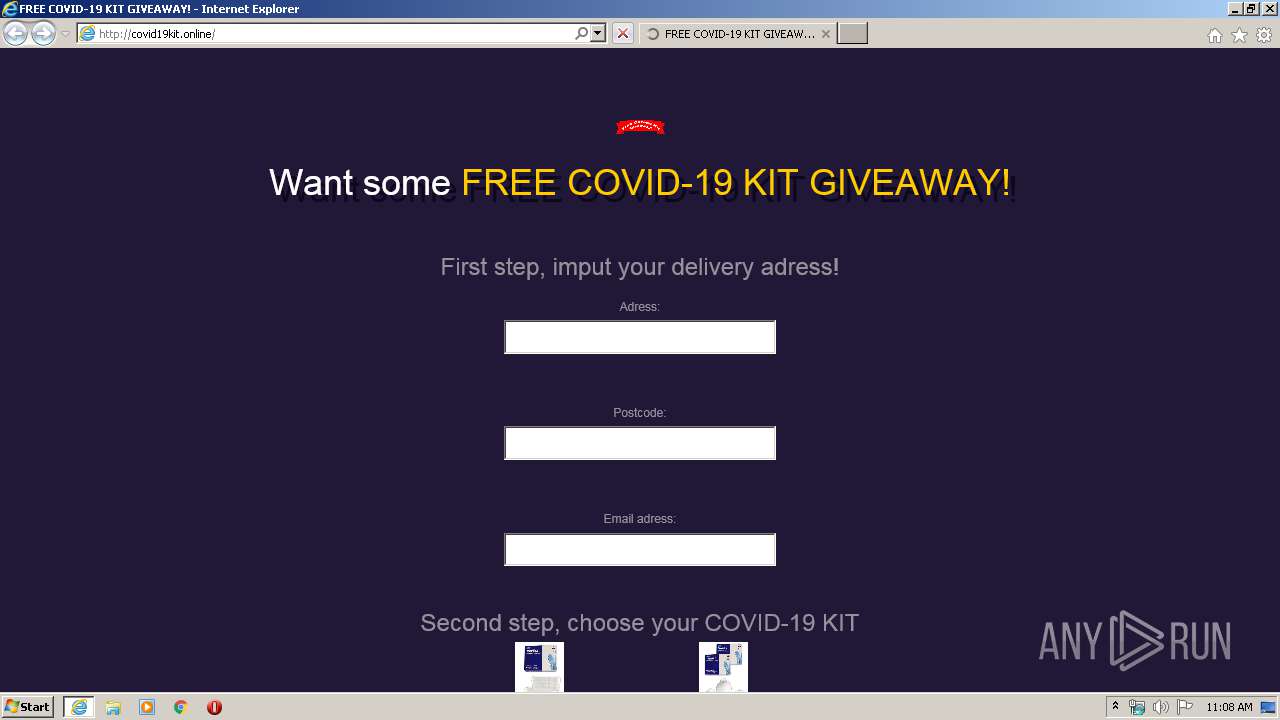
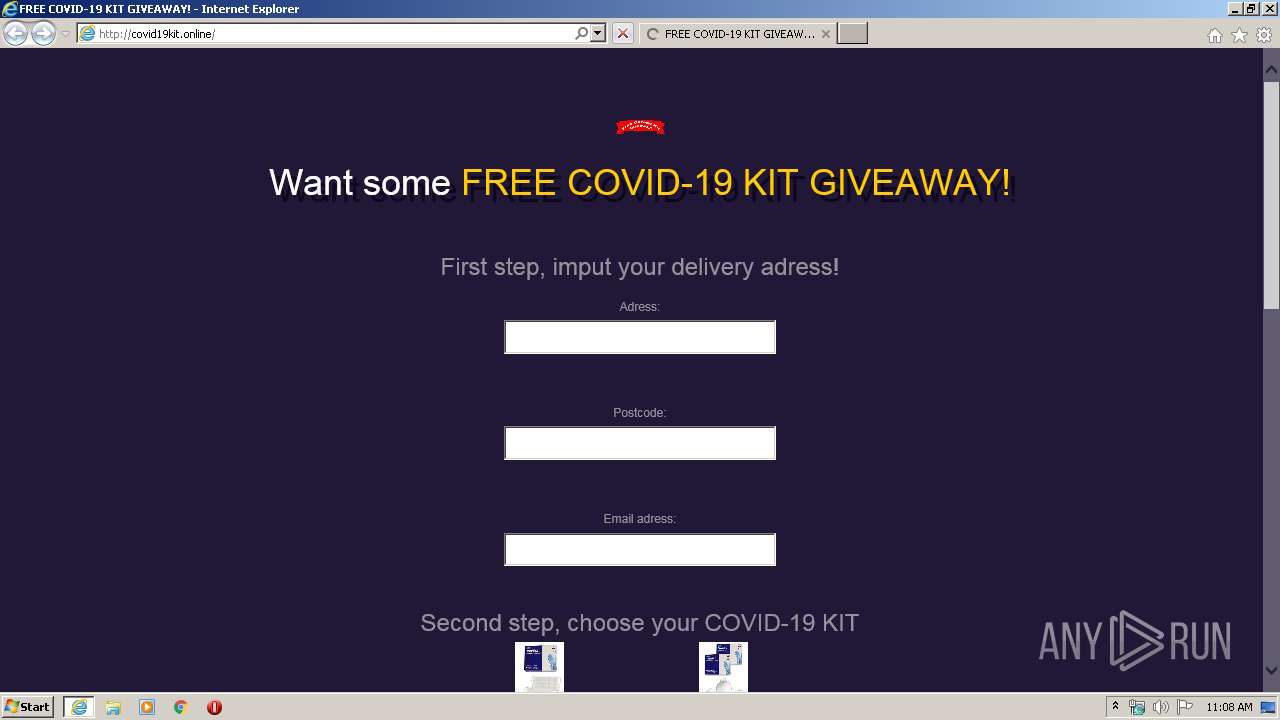
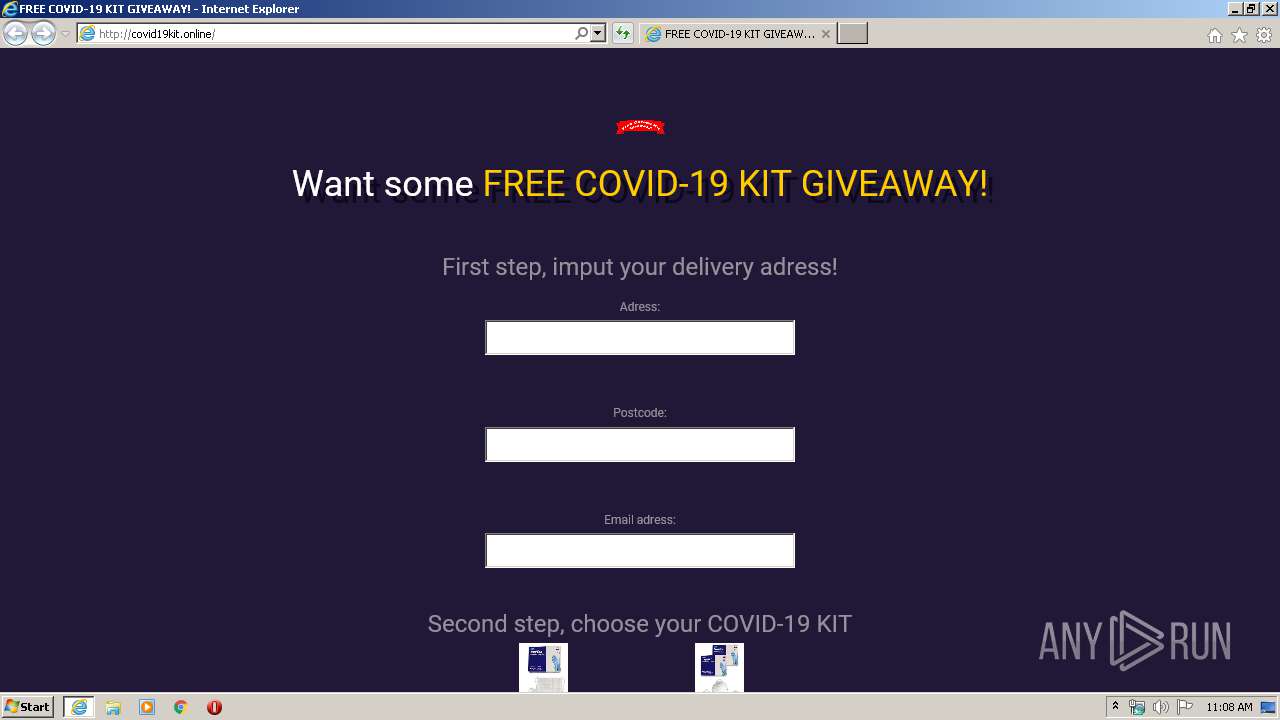
| URL: | http://covid19kit.online |
| Full analysis: | https://app.any.run/tasks/3bef02c4-f8b7-42c1-96db-ab8ea18e20bf |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 10:07:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D78A209C633193C4B832CBC2D87EE035 |
| SHA1: | 38E88E964948DD8B5178AB3825551A1EA7A8172C |
| SHA256: | 21C1CDBB65D364EDE54EAE6F73C935D5D5AF44CFEEDED4C6B8FFEAAFADD2DA27 |
| SSDEEP: | 3:N1KdKTA1T0n:CIkm |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2876)
- iexplore.exe (PID: 3956)
Drops Coronavirus (possible) decoy
- iexplore.exe (PID: 3956)
- iexplore.exe (PID: 2876)
Reads internet explorer settings
- iexplore.exe (PID: 3956)
Changes internet zones settings
- iexplore.exe (PID: 2876)
Reads settings of System Certificates
- iexplore.exe (PID: 3956)
- iexplore.exe (PID: 2876)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2876)
Changes settings of System certificates
- iexplore.exe (PID: 2876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2876 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://covid19kit.online" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3956 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2876 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
5 916
Read events
734
Write events
3 467
Delete events
1 715
Modification events
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1385644870 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30803780 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2876) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
29
Text files
22
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3956 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab7DC3.tmp | — | |
MD5:— | SHA256:— | |||
| 3956 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar7DC4.tmp | — | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\HWYJH8NS.htm | html | |
MD5:— | SHA256:— | |||
| 3956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 3956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\photo[1].jpg | image | |
MD5:— | SHA256:— | |||
| 3956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\bootstrap.superhero[1].css | text | |
MD5:— | SHA256:— | |||
| 3956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\1[1].png | image | |
MD5:— | SHA256:— | |||
| 3956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\2[1].png | image | |
MD5:— | SHA256:— | |||
| 3956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BE8B021F9E811DFC8C8A28572A17C05A_F8C660BDA0A15C43A0E97ADAD6819DBB | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
61
DNS requests
24
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3956 | iexplore.exe | GET | — | 23.254.226.226:80 | http://covid19kit.online/p0kec0ins.com/ais/o.png | US | — | — | suspicious |
3956 | iexplore.exe | GET | — | 23.254.226.226:80 | http://covid19kit.online/p0kec0ins.com/ais/cs.png | US | — | — | suspicious |
3956 | iexplore.exe | GET | 200 | 172.217.16.193:80 | http://lh6.googleusercontent.com/-uhaO6GGOzQU/AAAAAAAAAAI/AAAAAAAAAA8/kbqlfgjbwkU/w48-c-h48-rw/photo.jpg | US | image | 1.01 Kb | whitelisted |
3956 | iexplore.exe | GET | 200 | 2.20.190.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
3956 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEAUI1xTz%2FIA59ca8CEavehY%3D | US | der | 280 b | whitelisted |
3956 | iexplore.exe | GET | 200 | 2.20.190.17:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgPA9lFBhuWacMXW1P2pNreH0A%3D%3D | unknown | der | 527 b | whitelisted |
2876 | iexplore.exe | GET | 500 | 23.254.226.226:80 | http://covid19kit.online/favicon.ico | US | html | 688 b | suspicious |
3956 | iexplore.exe | GET | 200 | 2.20.190.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
3956 | iexplore.exe | GET | 200 | 23.254.226.226:80 | http://covid19kit.online/1.png | US | image | 151 Kb | suspicious |
3956 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3956 | iexplore.exe | 23.254.226.226:80 | covid19kit.online | Hostwinds LLC. | US | suspicious |
3956 | iexplore.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3956 | iexplore.exe | 172.217.22.33:80 | lh3.googleusercontent.com | Google Inc. | US | whitelisted |
3956 | iexplore.exe | 172.217.16.193:80 | lh5.googleusercontent.com | Google Inc. | US | whitelisted |
3956 | iexplore.exe | 78.142.29.171:80 | p0kec0ins.com | BlueAngelHost Pvt. Ltd | BG | unknown |
3956 | iexplore.exe | 34.225.254.242:80 | loader.ogstats.com | Amazon.com, Inc. | US | unknown |
3956 | iexplore.exe | 172.217.18.106:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2876 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3956 | iexplore.exe | 172.217.23.163:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3956 | iexplore.exe | 172.217.23.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
covid19kit.online |
| suspicious |
api.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
lh3.googleusercontent.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |
lh4.googleusercontent.com |
| whitelisted |
lh6.googleusercontent.com |
| whitelisted |
p0kec0ins.com |
| unknown |
loader.ogstats.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M1 |
3956 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 Domain M1 |
3956 | iexplore.exe | A Network Trojan was detected | ET INFO Possible Phish - Mirrored Website Comment Observed |
3956 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 Domain M1 |
3956 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 Domain M1 |
3956 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 Domain M1 |
3956 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 Domain M1 |
3956 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 Domain M1 |
3956 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 Domain M1 |
3956 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M2 |