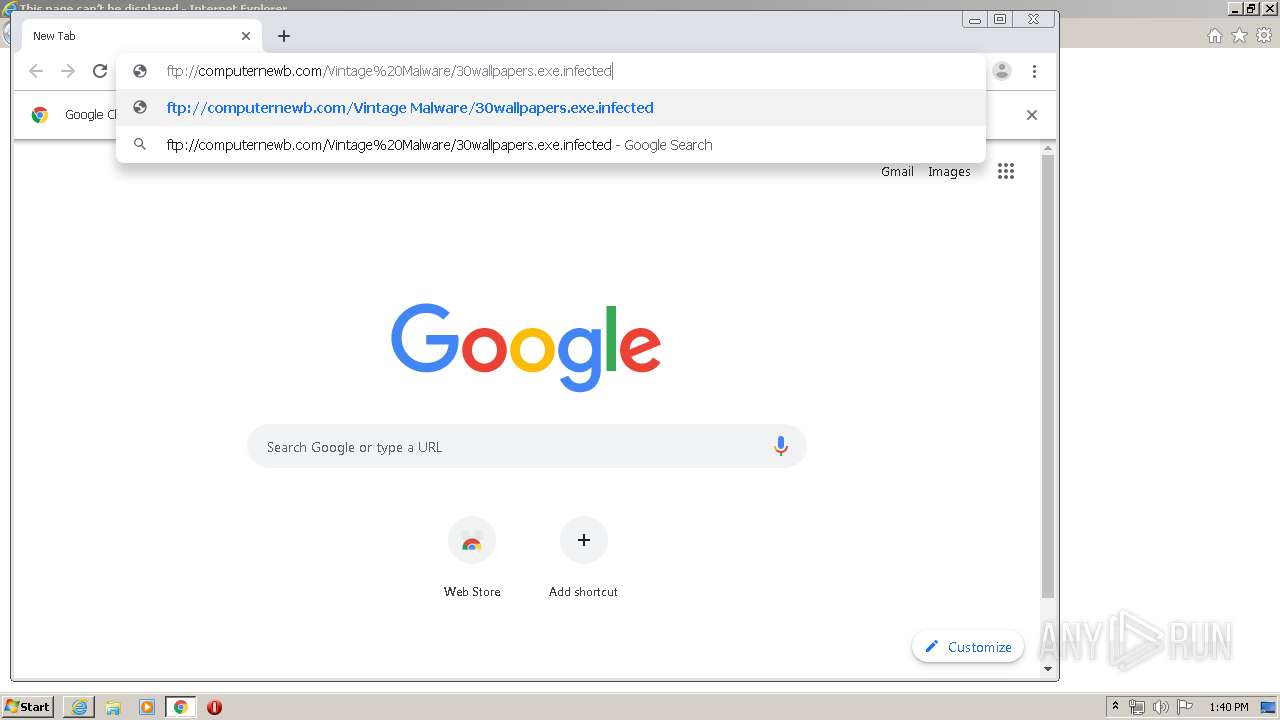
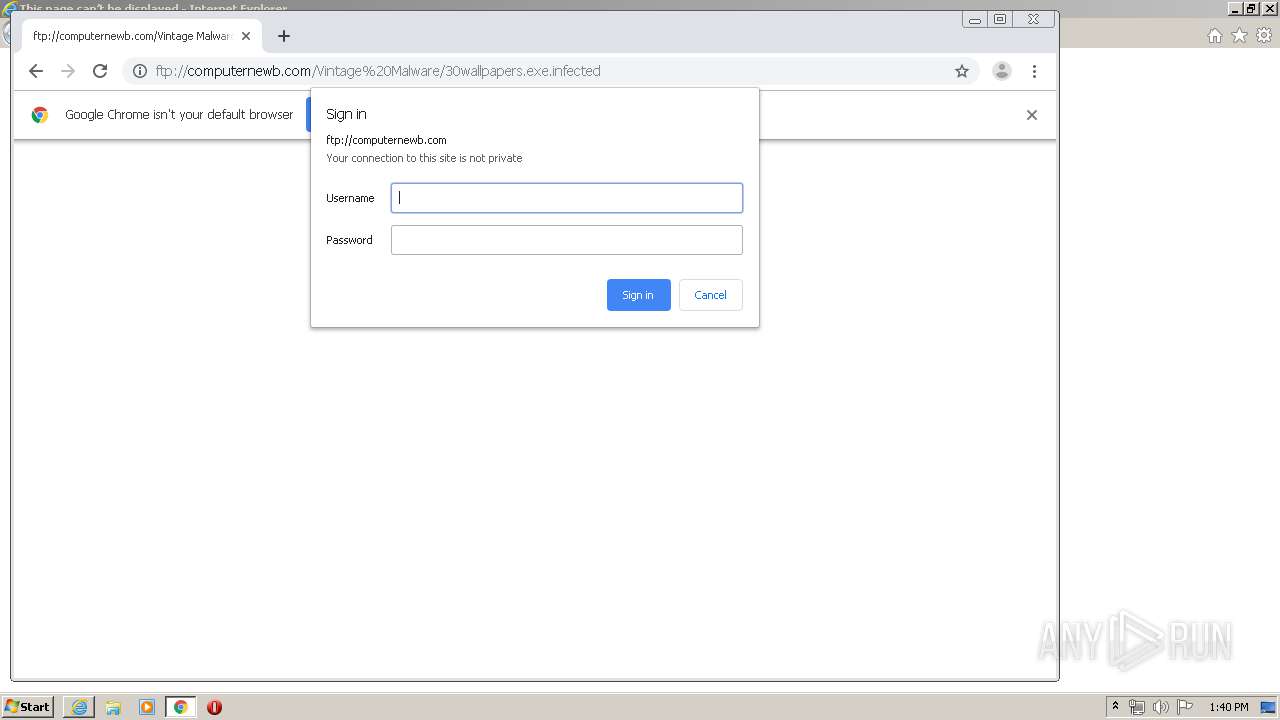
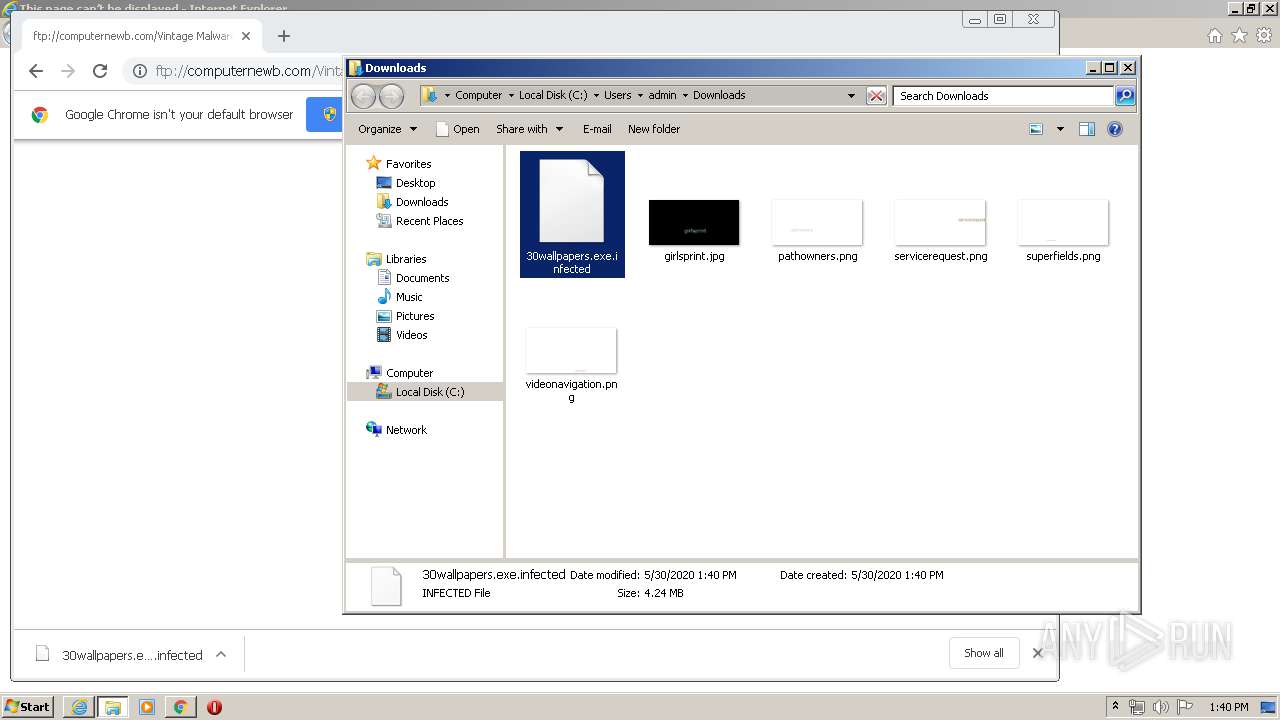
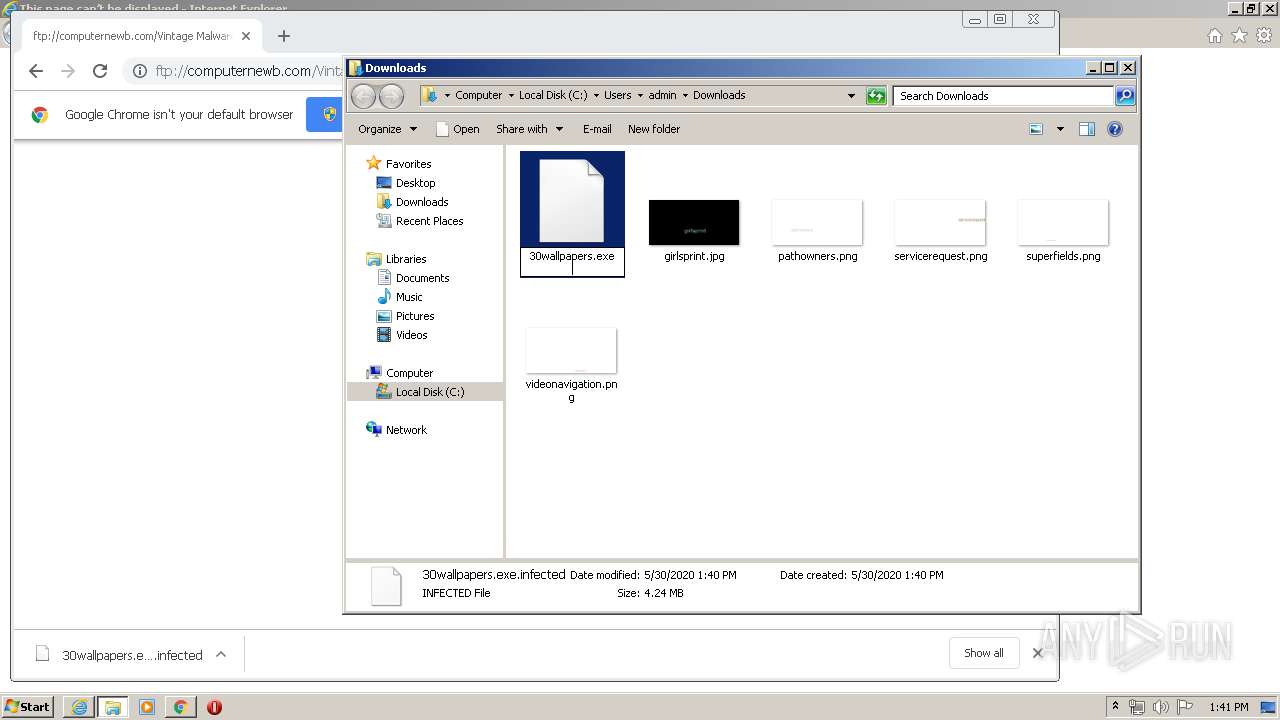
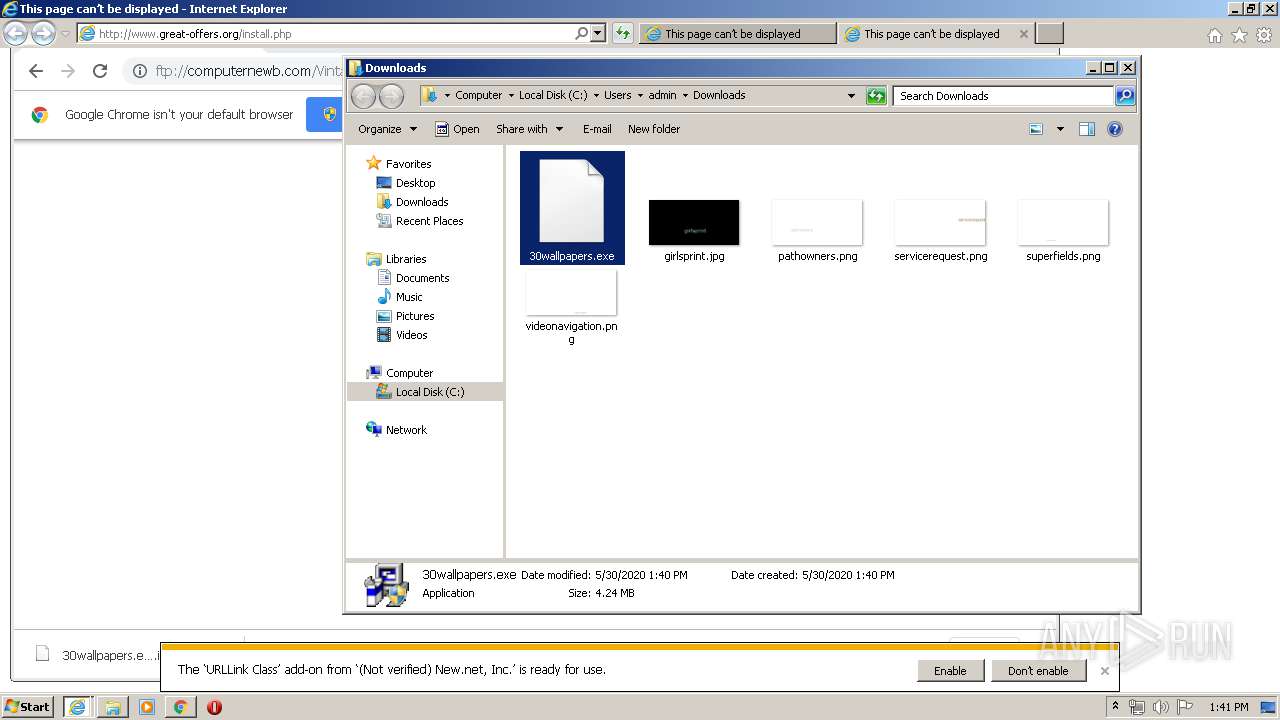
| URL: | ftp://computernewb.com/Vintage%20Malware/30wallpapers.exe.infected |
| Full analysis: | https://app.any.run/tasks/fdafcbbf-86b0-41c6-bf64-e4a4b39c2ab5 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 12:39:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0E5727AFC2CE28FE6E8885DA174D7F6C |
| SHA1: | 331114A6EB200EED5DF769D0601DDC5C273A93D5 |
| SHA256: | 21BDB38BBC6DFF3284DF23D2FEFCD931B977D86D8DA877F4F0828ADC15895733 |
| SSDEEP: | 3:HidKI6mt3gCAMEqJJV8yoG2:CII643gCAFeOR |
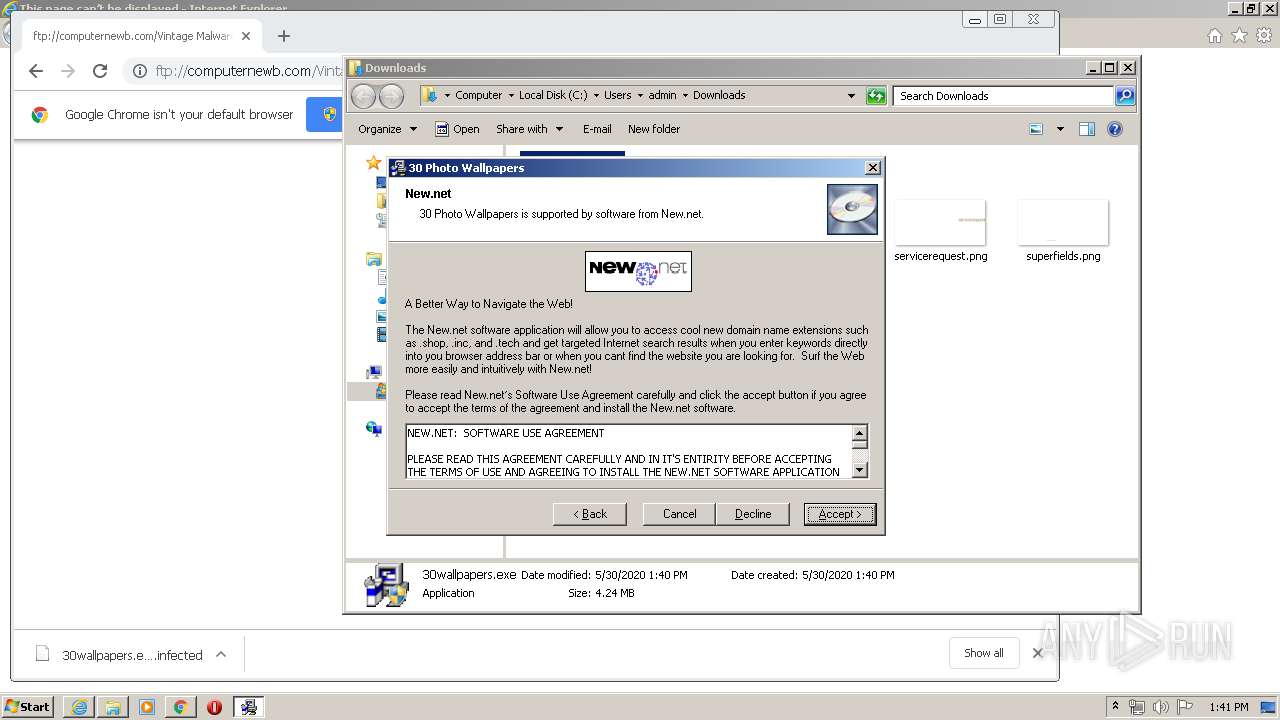
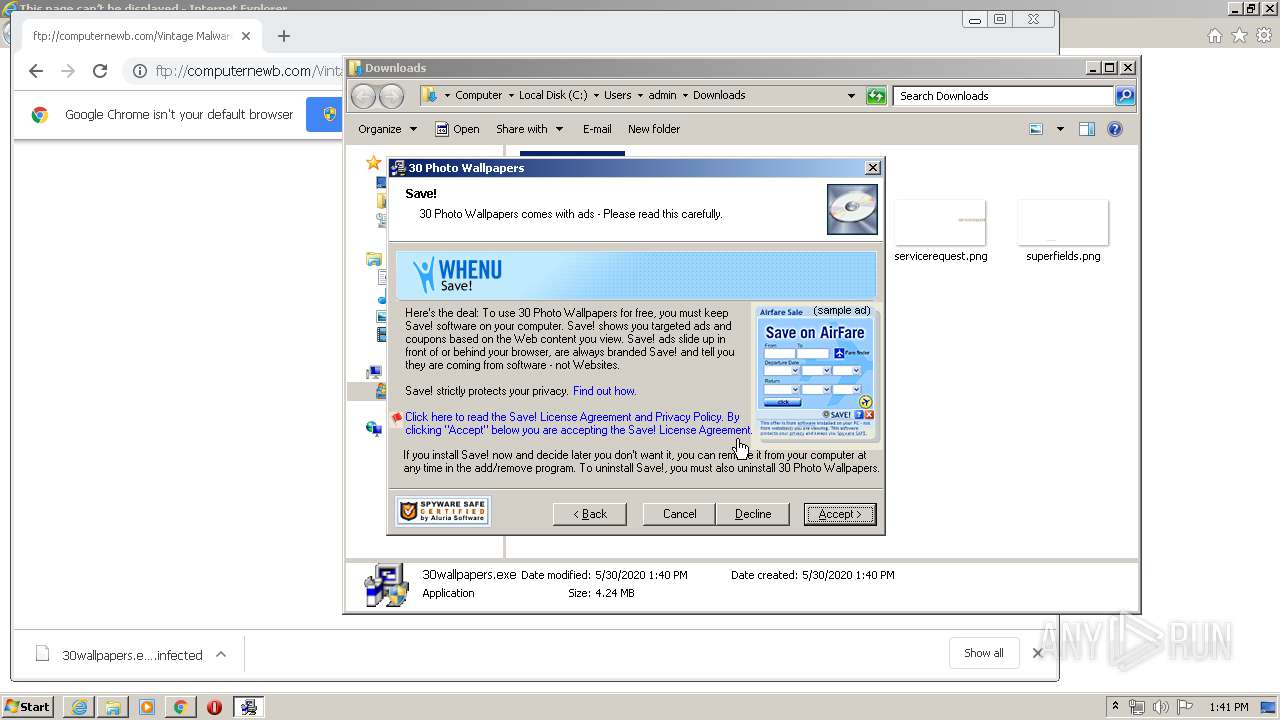
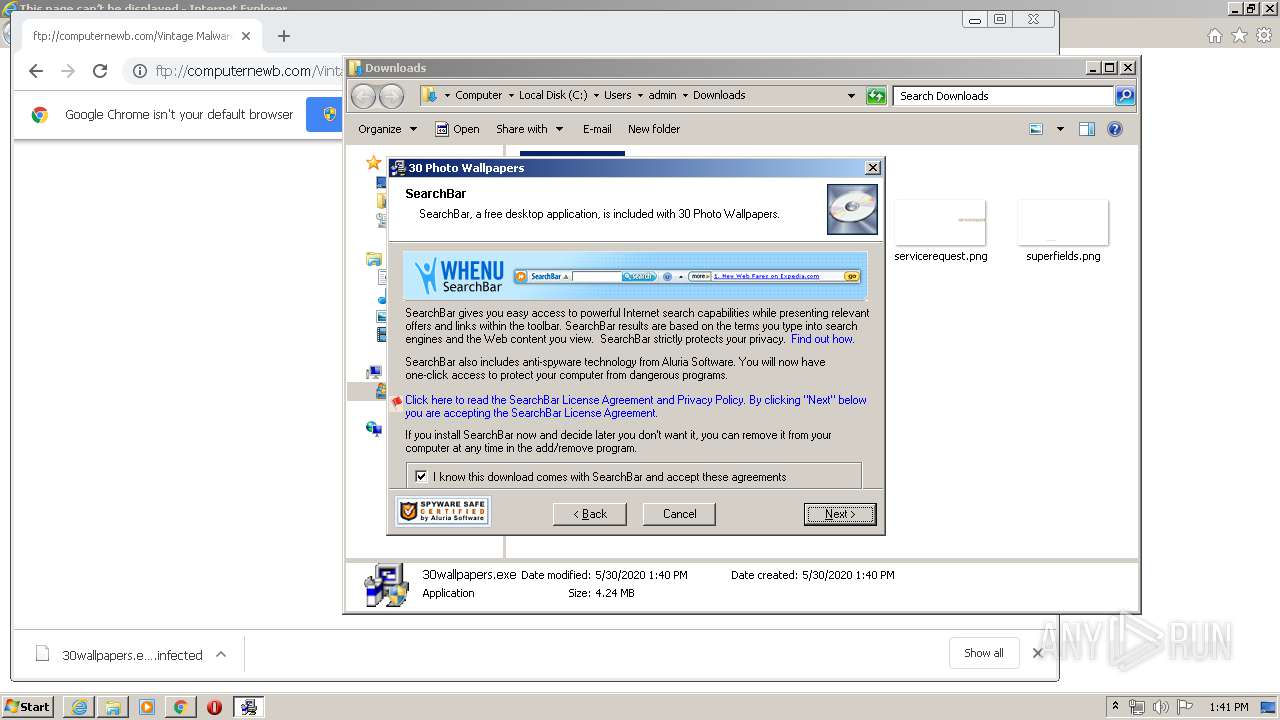
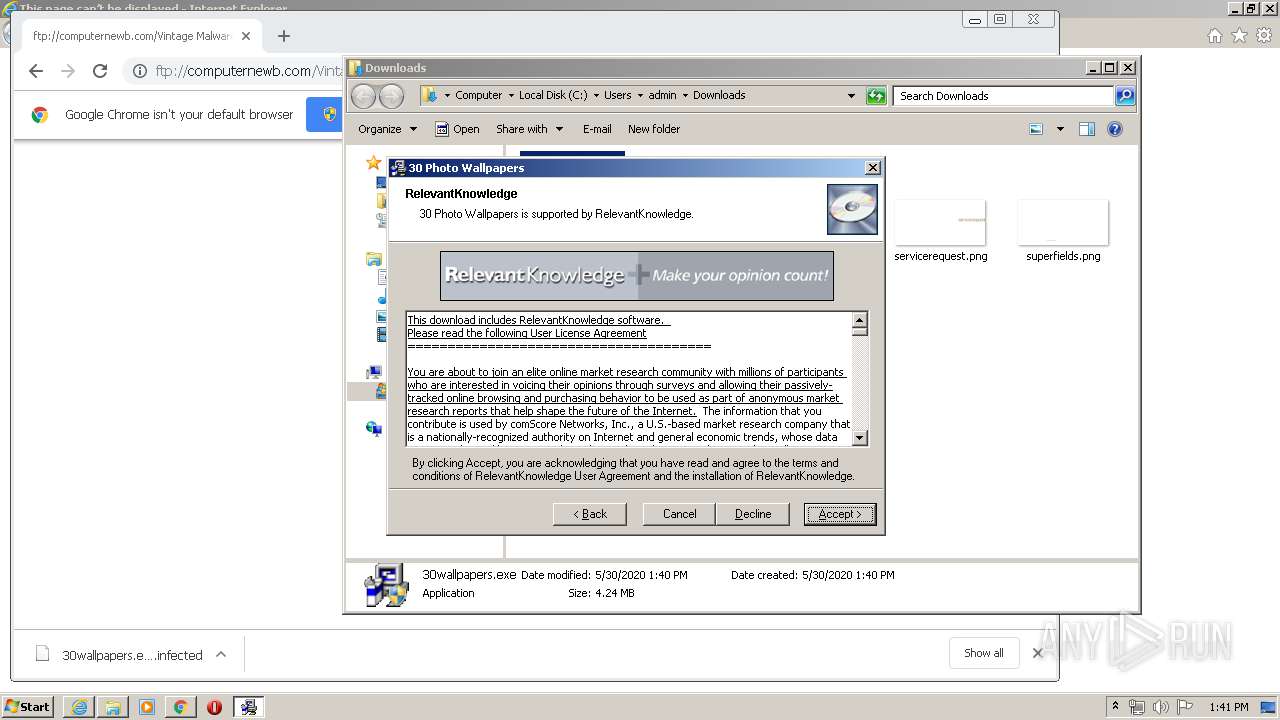
MALICIOUS
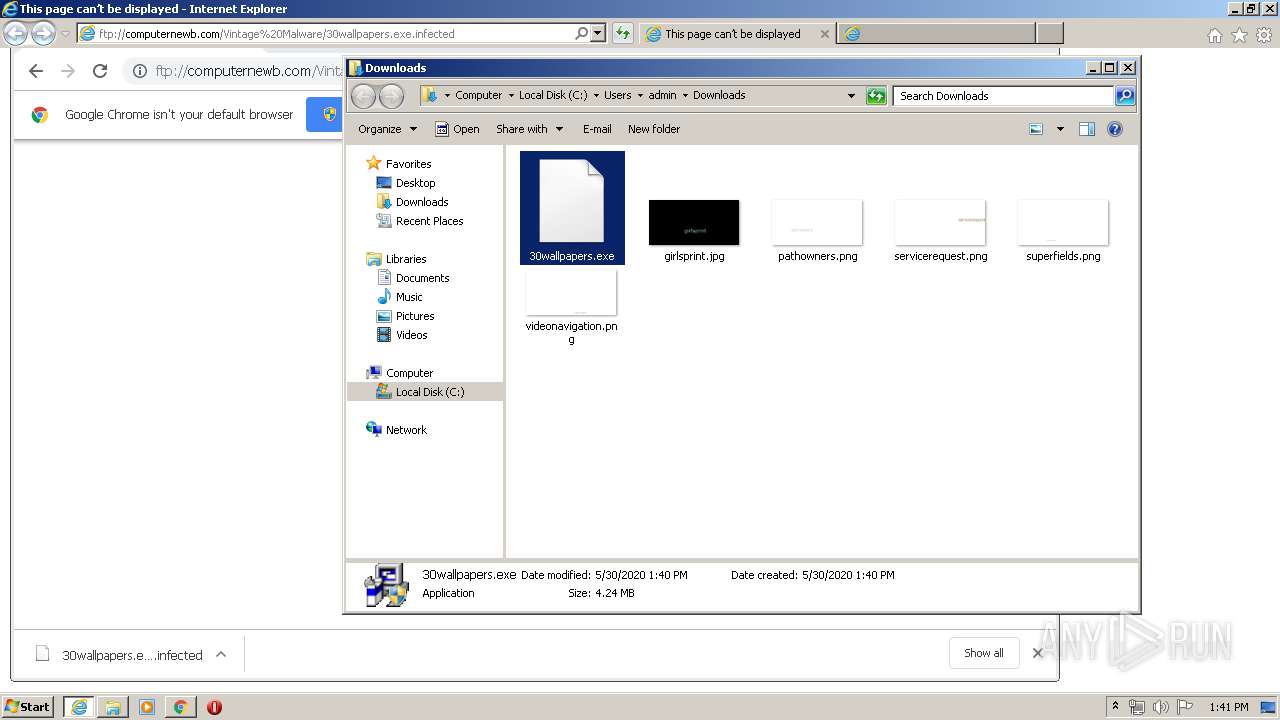
Application was dropped or rewritten from another process
- 30wallpapers.exe (PID: 1484)
- 30wallpapers.exe (PID: 1948)
- VVSNInst.exe (PID: 840)
- NNADFS~1.EXE (PID: 3336)
- VVSN.exe (PID: 2228)
- rk.exe (PID: 3676)
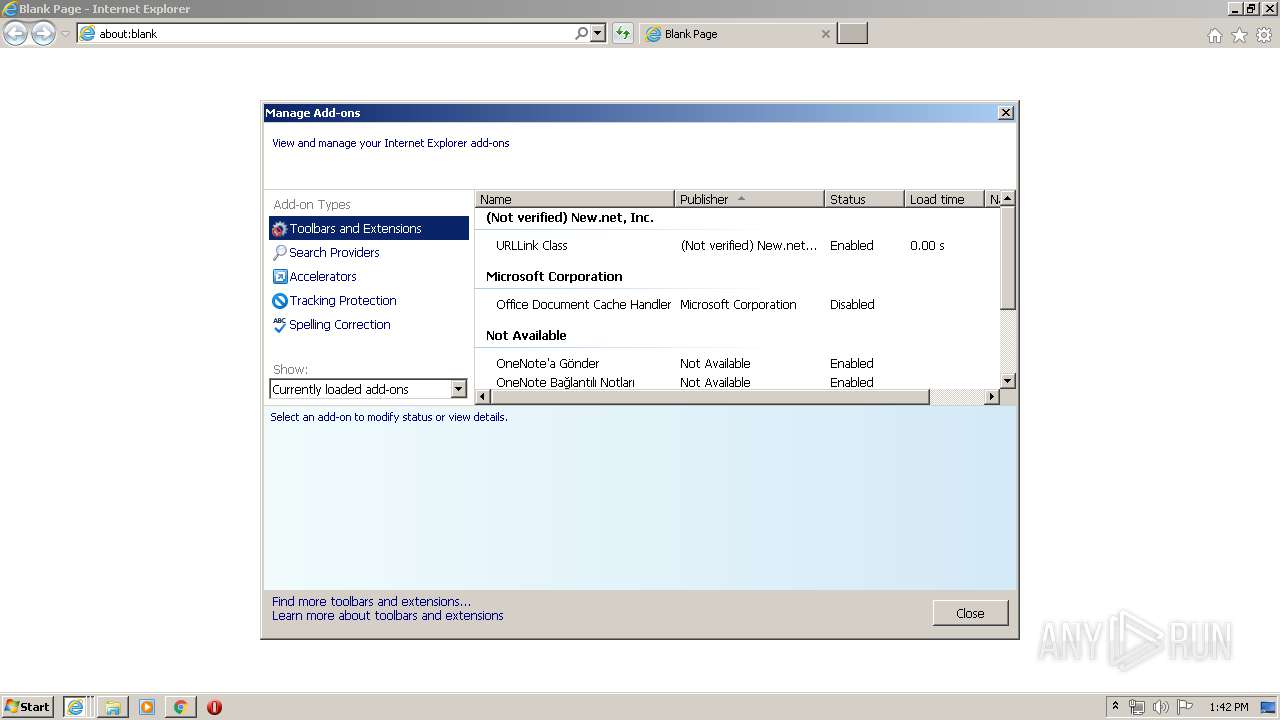
Loads dropped or rewritten executable
- 30wallpapers.exe (PID: 1948)
- NNADFS~1.EXE (PID: 3336)
- VVSN.exe (PID: 2228)
- iexplore.exe (PID: 2532)
- rundll32.exe (PID: 2792)
- chrome.exe (PID: 2160)
- iexplore.exe (PID: 356)
- iexplore.exe (PID: 2388)
- rk.exe (PID: 3676)
- iexplore.exe (PID: 576)
- chrome.exe (PID: 2000)
- explorer.exe (PID: 396)
- svchost.exe (PID: 872)
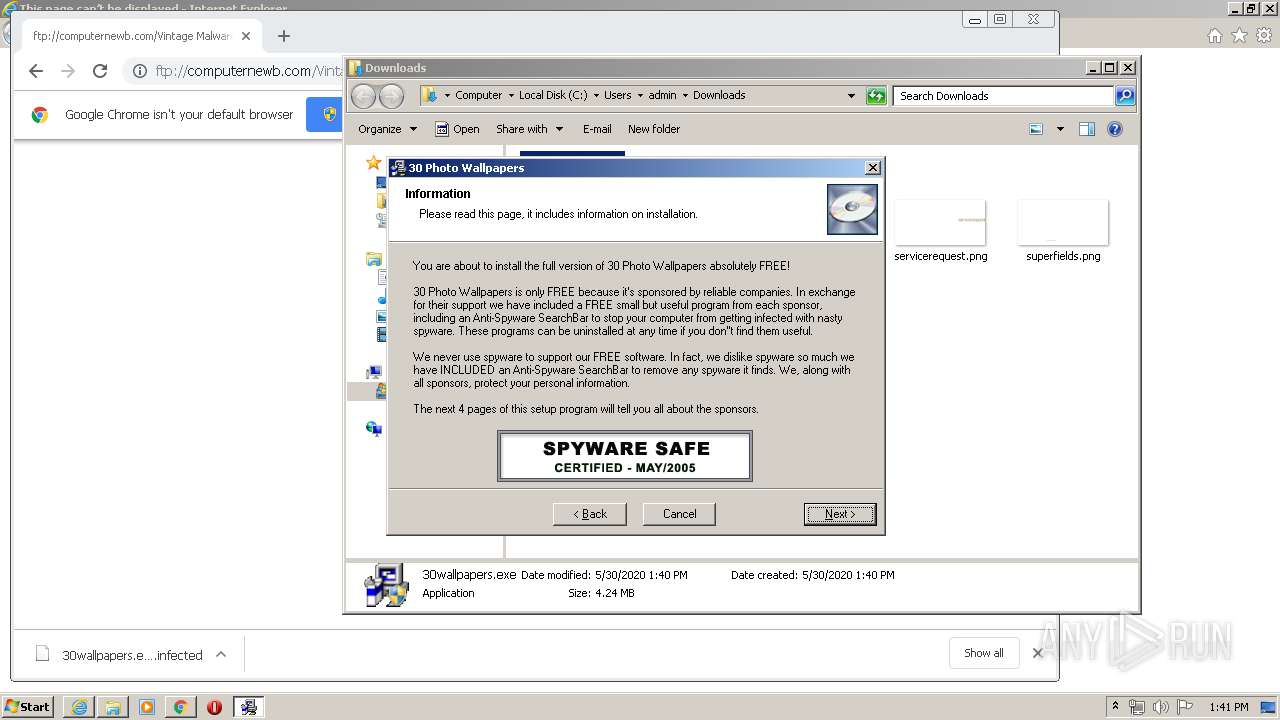
Actions looks like stealing of personal data
- VVSNInst.exe (PID: 840)
- svchost.exe (PID: 872)
- explorer.exe (PID: 396)
Changes the autorun value in the registry
- NNADFS~1.EXE (PID: 3336)
- VVSN.exe (PID: 2228)
- rk.exe (PID: 3676)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2000)
- NNADFS~1.EXE (PID: 3336)
- VVSNInst.exe (PID: 840)
- 30wallpapers.exe (PID: 1948)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2000)
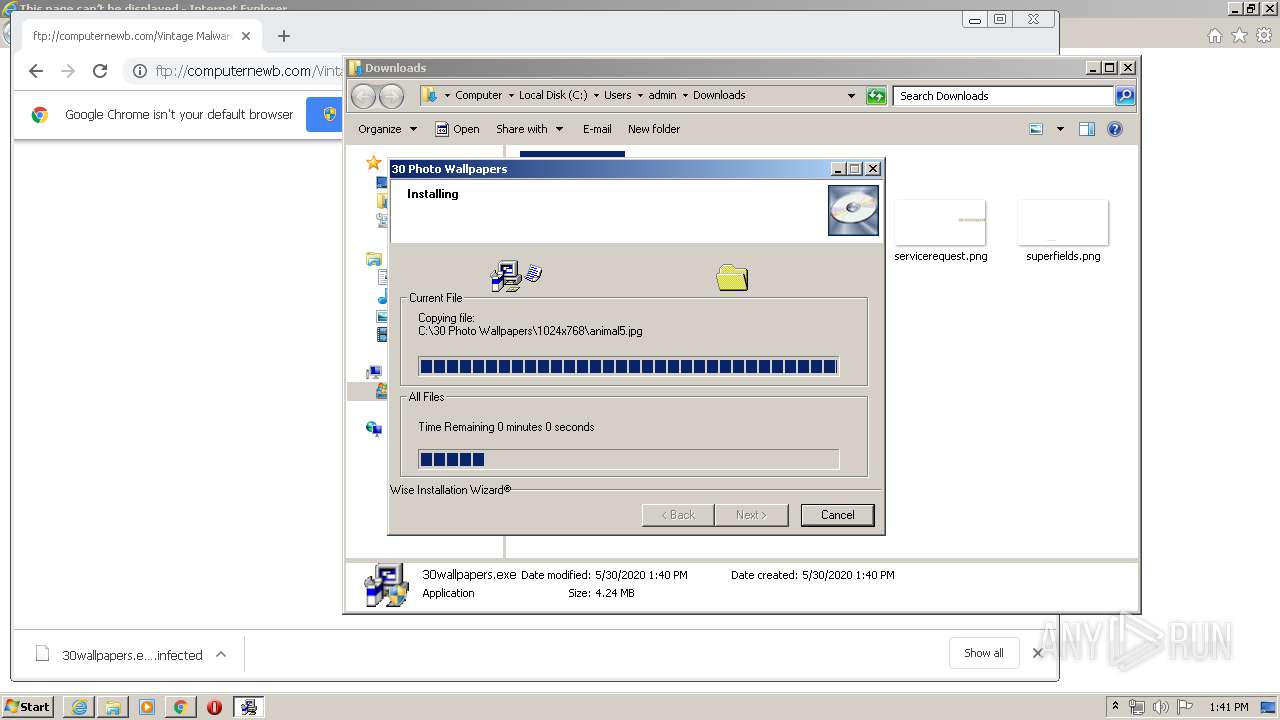
Creates files in the Windows directory
- 30wallpapers.exe (PID: 1948)
- NNADFS~1.EXE (PID: 3336)
Creates files in the program directory
- VVSNInst.exe (PID: 840)
- NNADFS~1.EXE (PID: 3336)
- VVSN.exe (PID: 2228)
Removes files from Windows directory
- 30wallpapers.exe (PID: 1948)
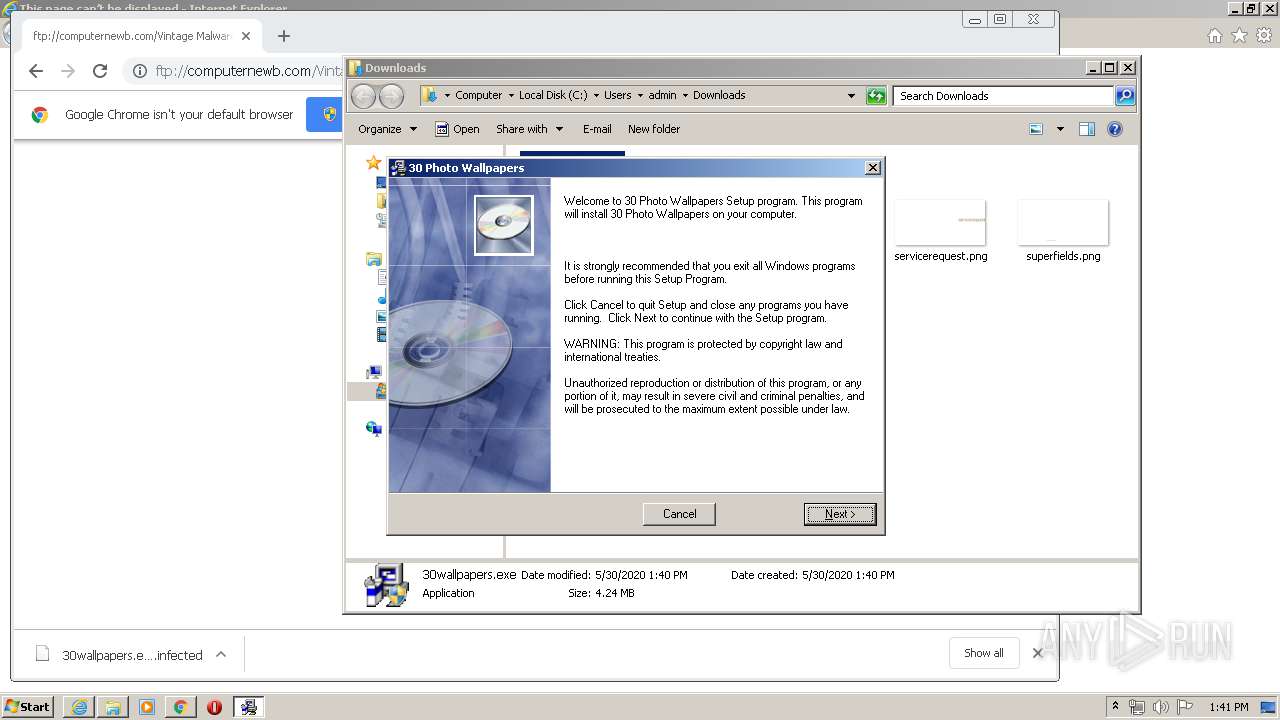
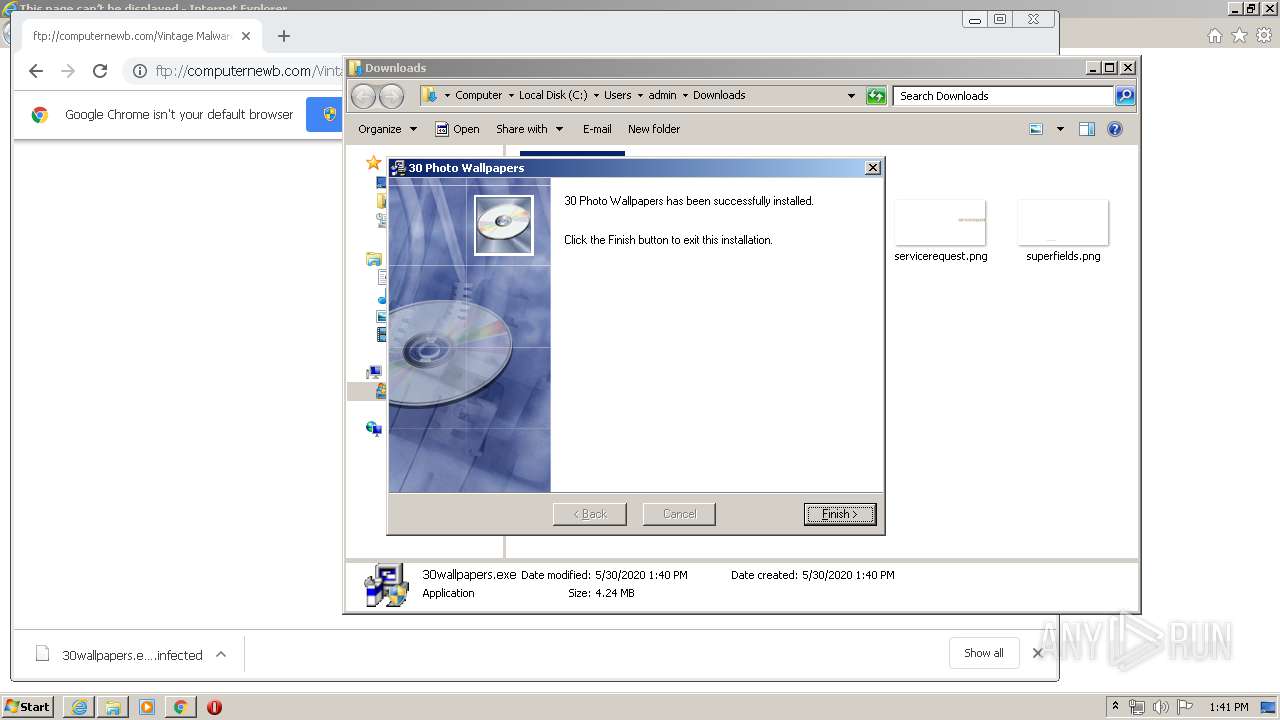
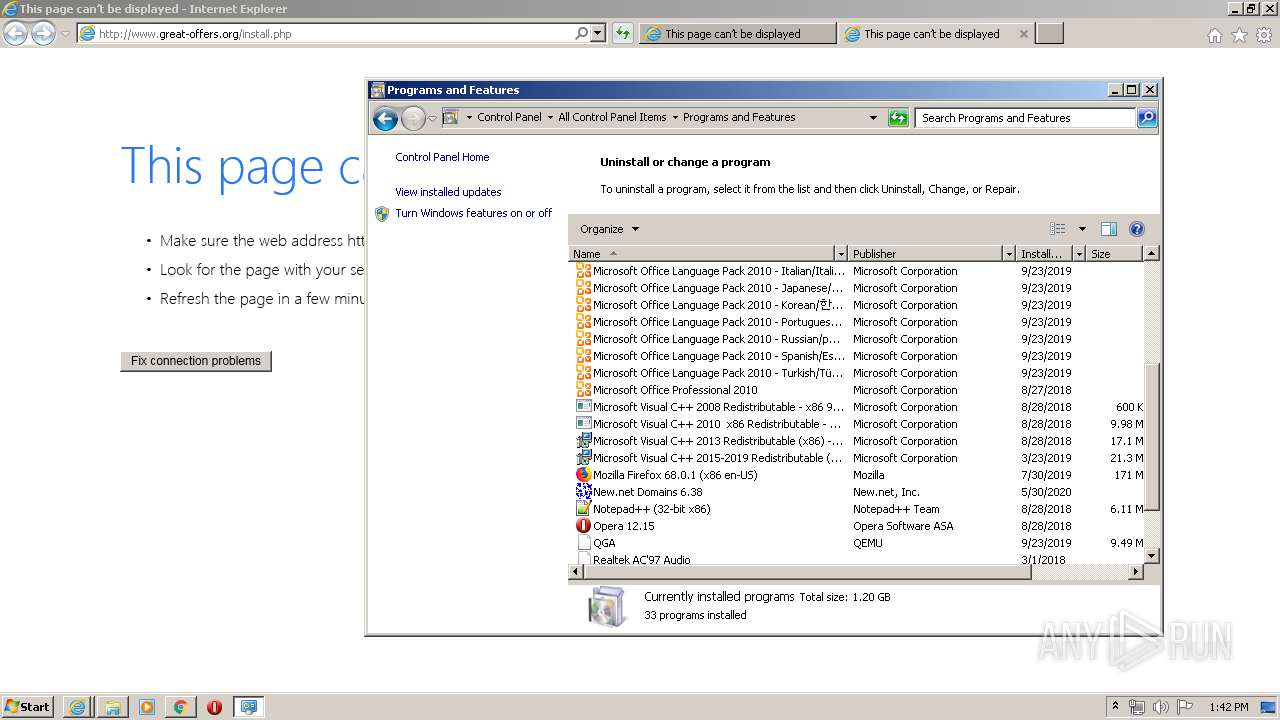
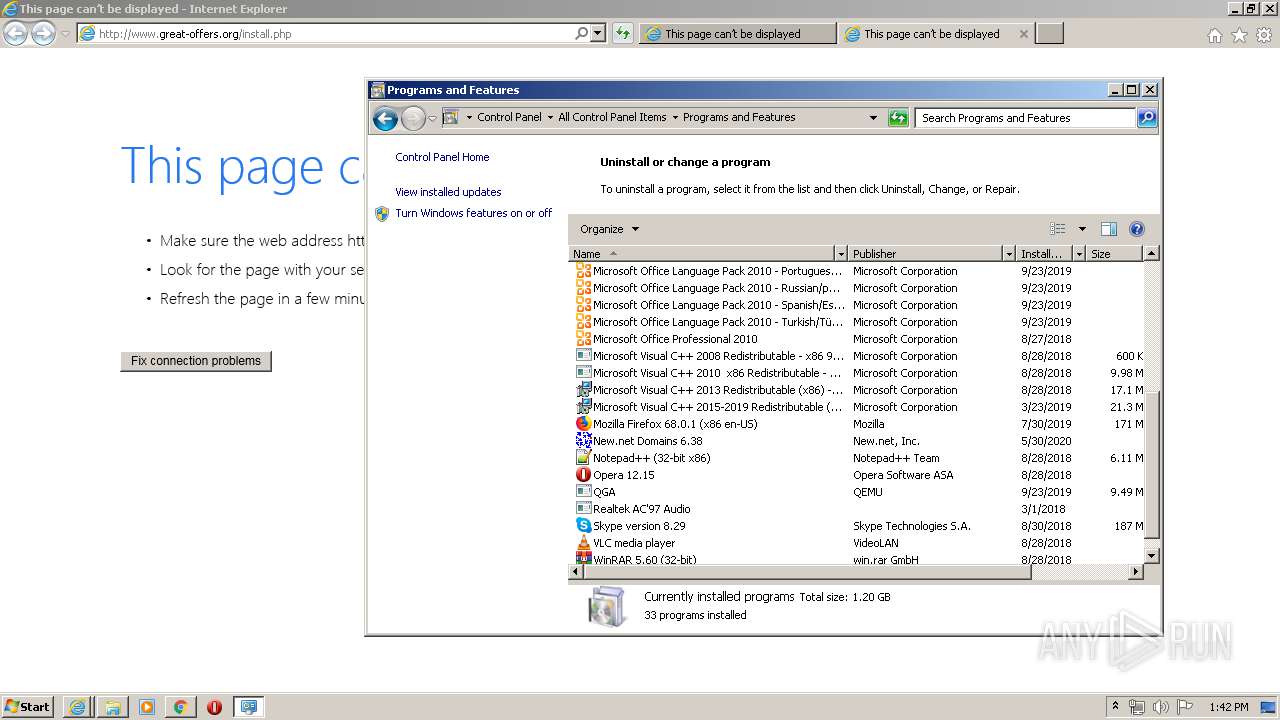
Creates a software uninstall entry
- 30wallpapers.exe (PID: 1948)
- NNADFS~1.EXE (PID: 3336)
- rk.exe (PID: 3676)
Uses NETSH.EXE for network configuration
- rk.exe (PID: 3676)
Creates COM task schedule object
- NNADFS~1.EXE (PID: 3336)
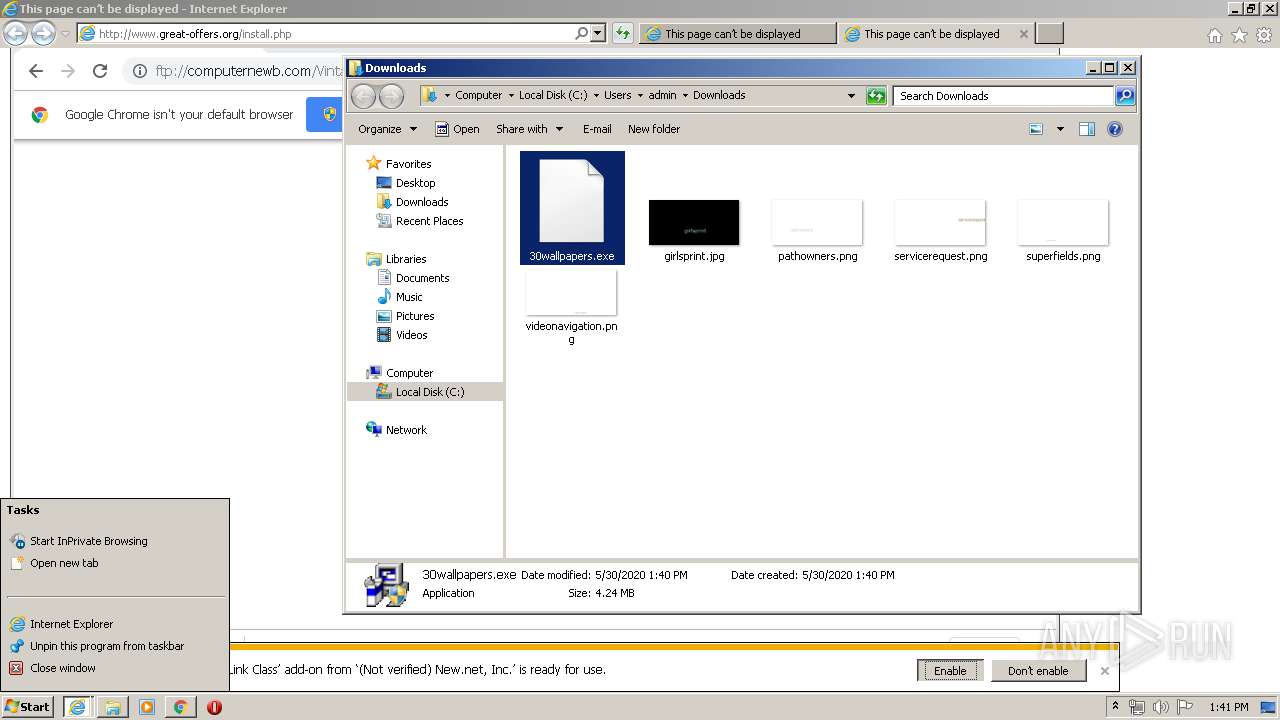
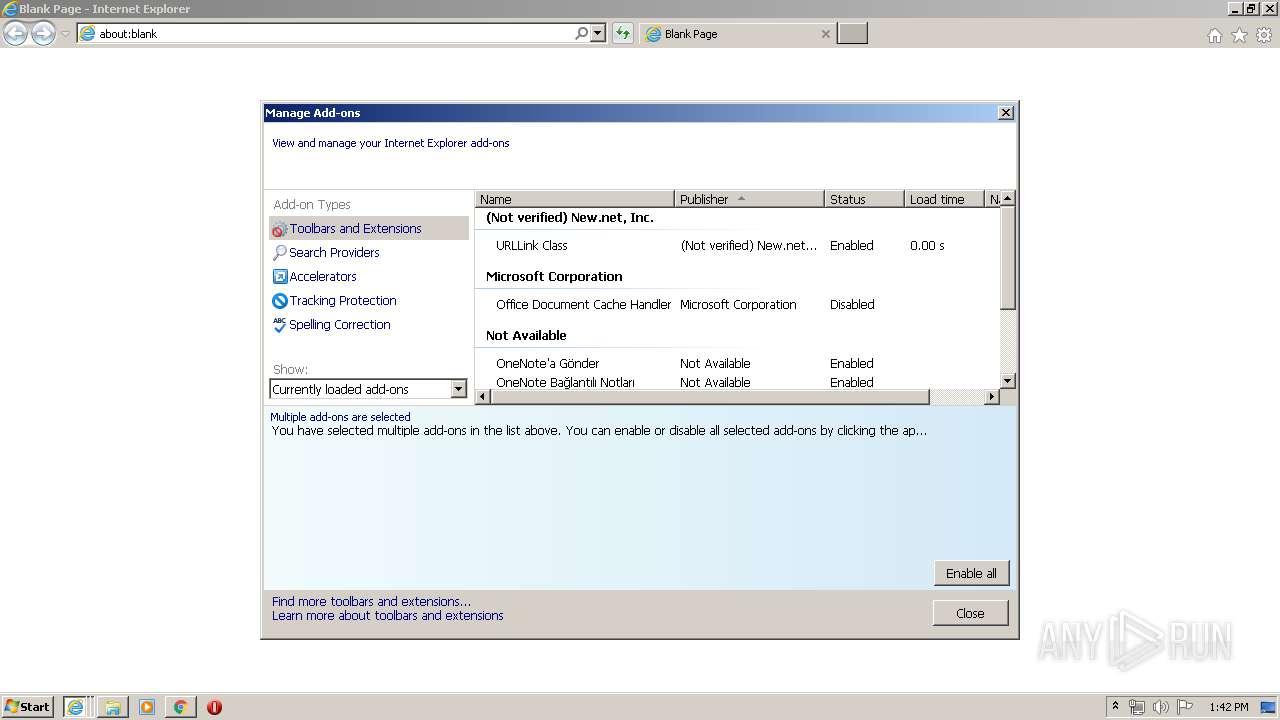
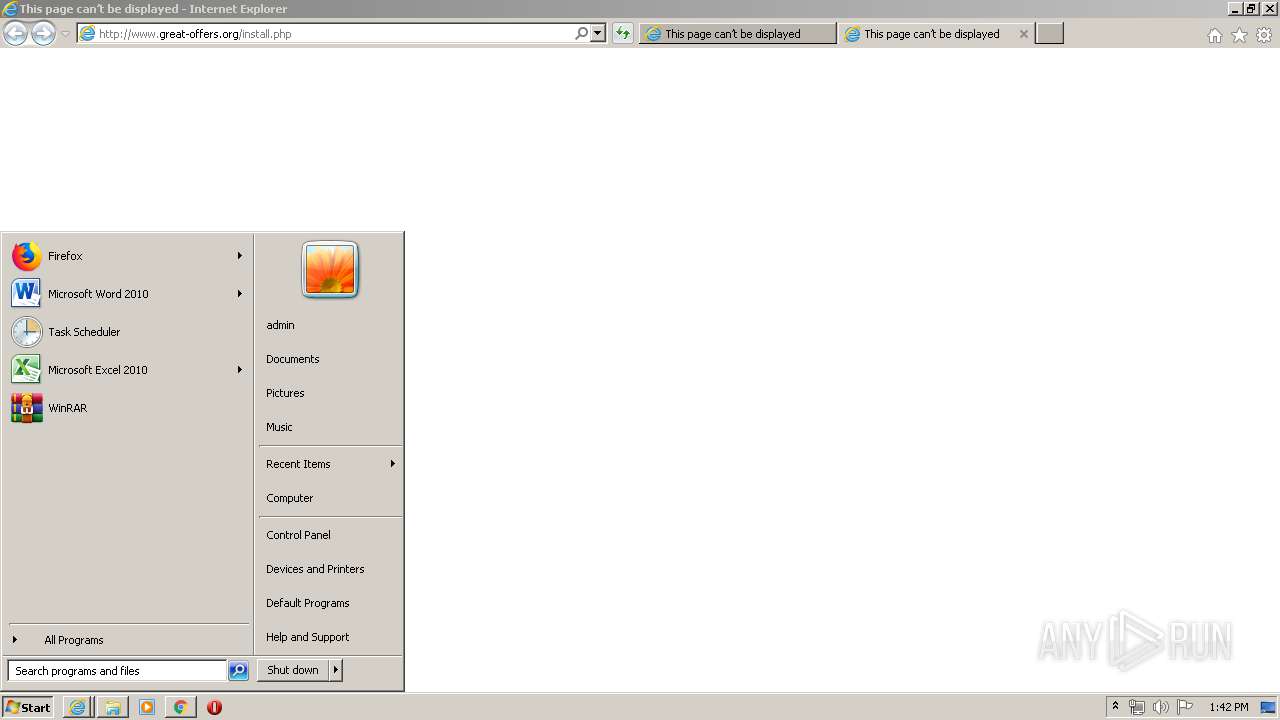
Starts Internet Explorer
- explorer.exe (PID: 396)
Reads Internet Cache Settings
- VVSN.exe (PID: 2228)
- rk.exe (PID: 3676)
Uses RUNDLL32.EXE to load library
- NNADFS~1.EXE (PID: 3336)
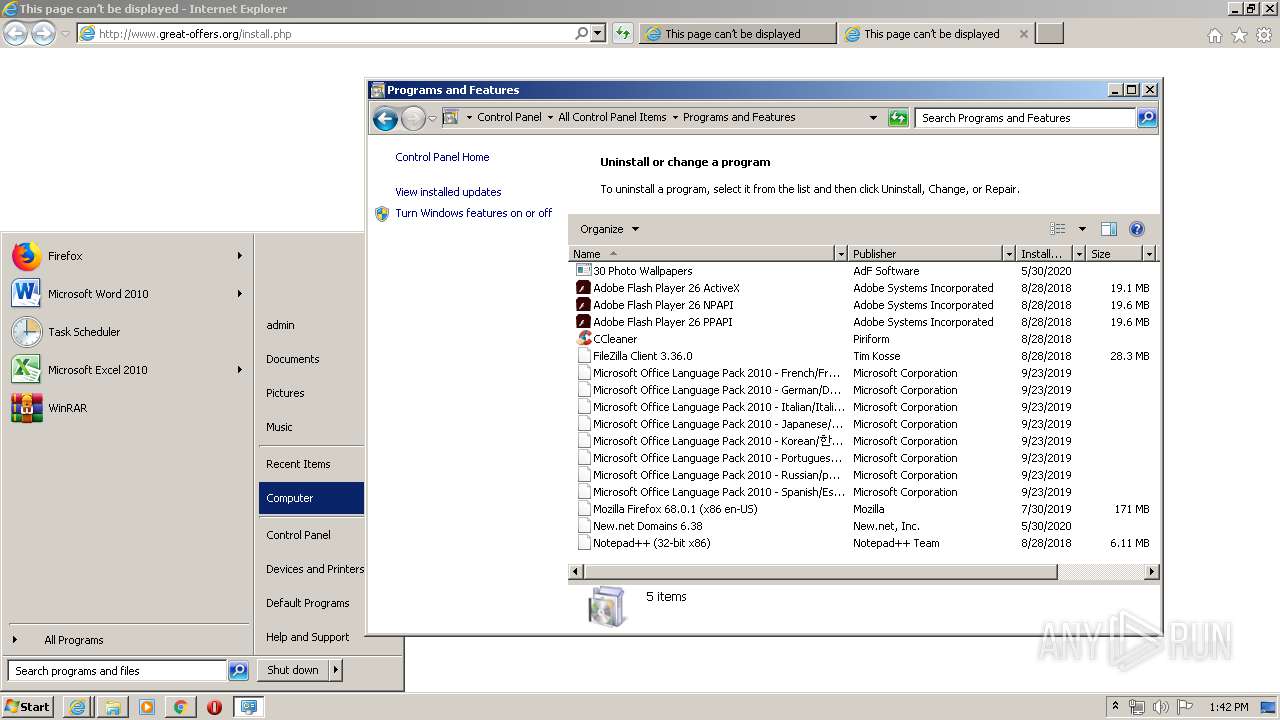
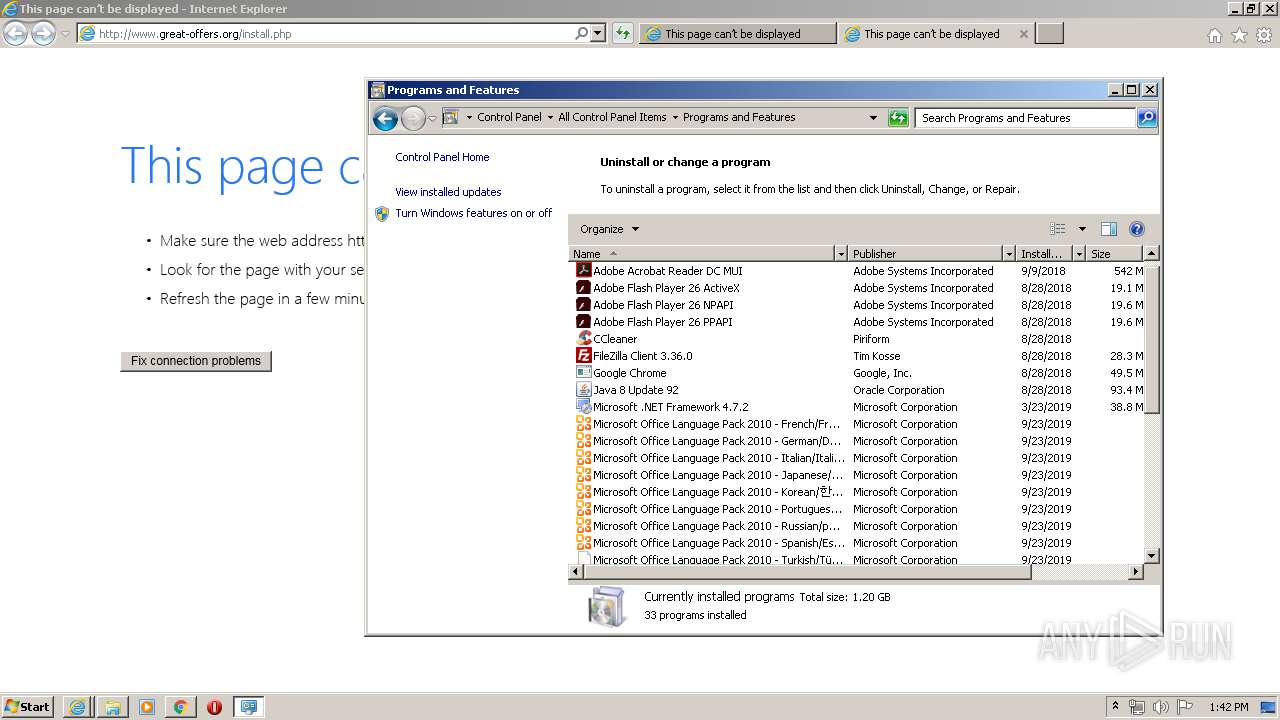
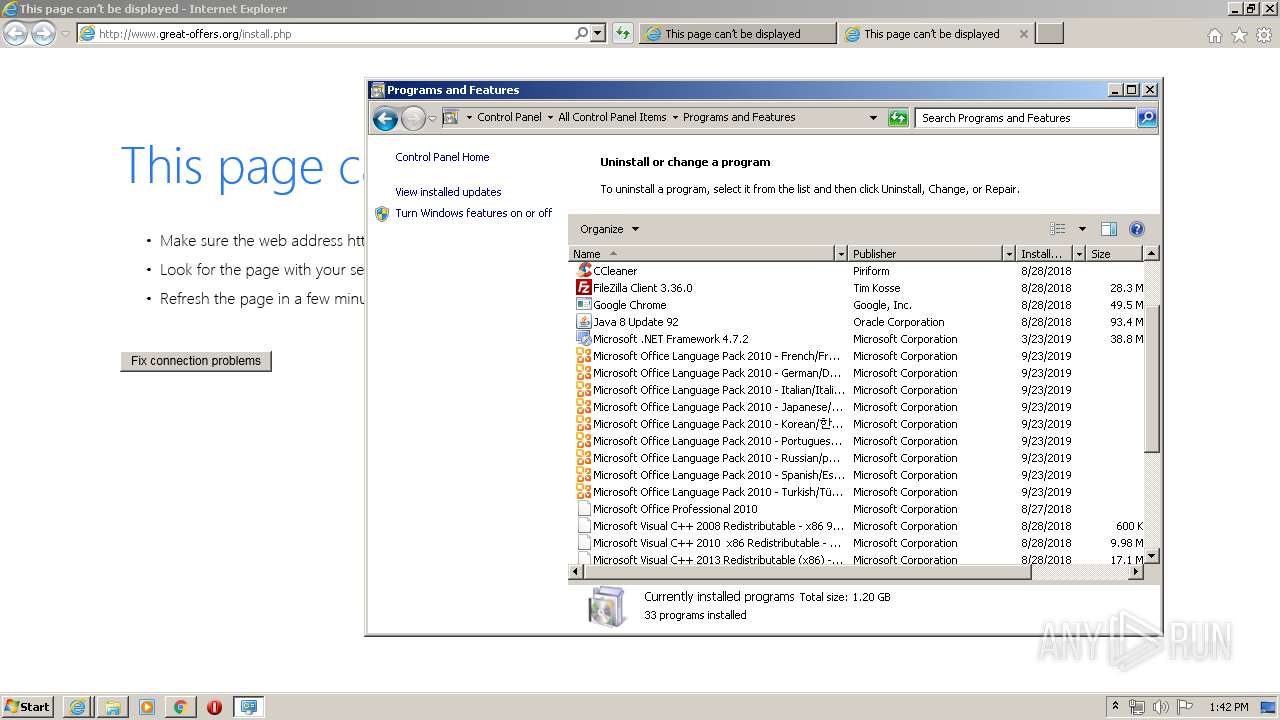
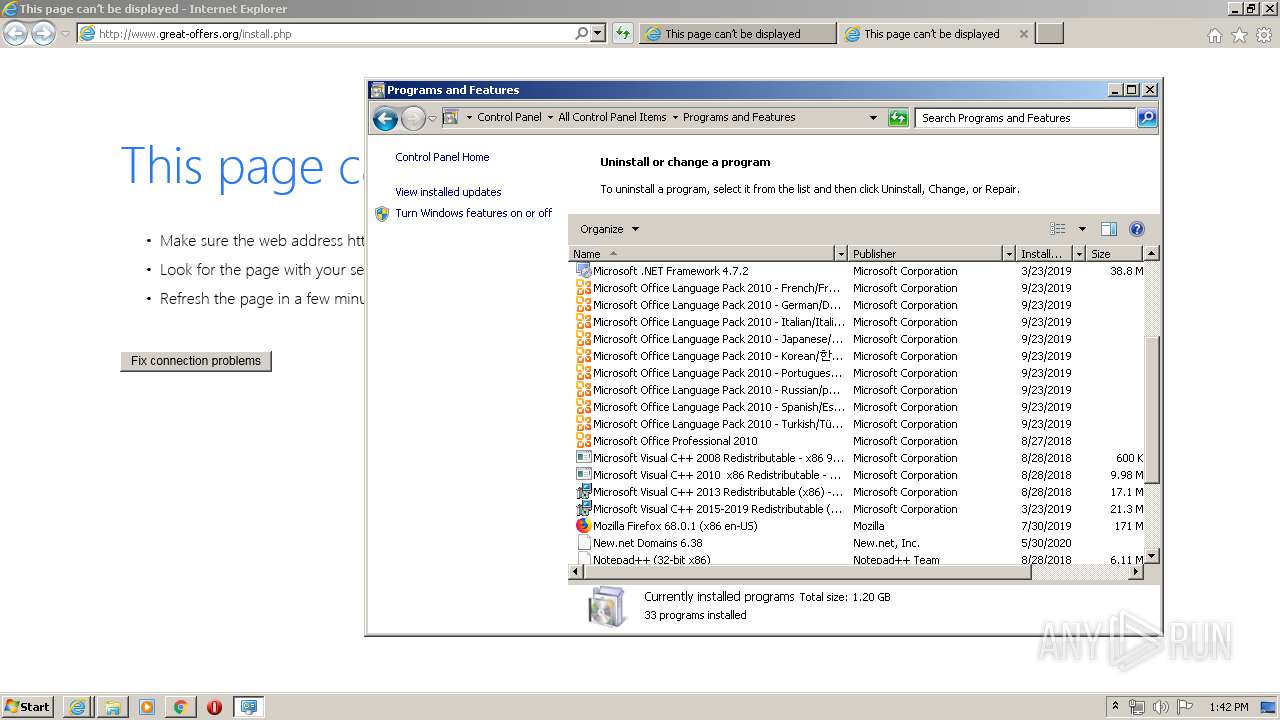
Searches for installed software
- explorer.exe (PID: 396)
INFO
Reads the hosts file
- chrome.exe (PID: 2000)
- chrome.exe (PID: 2160)
Reads Internet Cache Settings
- iexplore.exe (PID: 2532)
- iexplore.exe (PID: 2388)
- chrome.exe (PID: 2000)
- iexplore.exe (PID: 356)
- iexplore.exe (PID: 576)
Application launched itself
- iexplore.exe (PID: 2532)
- chrome.exe (PID: 2000)
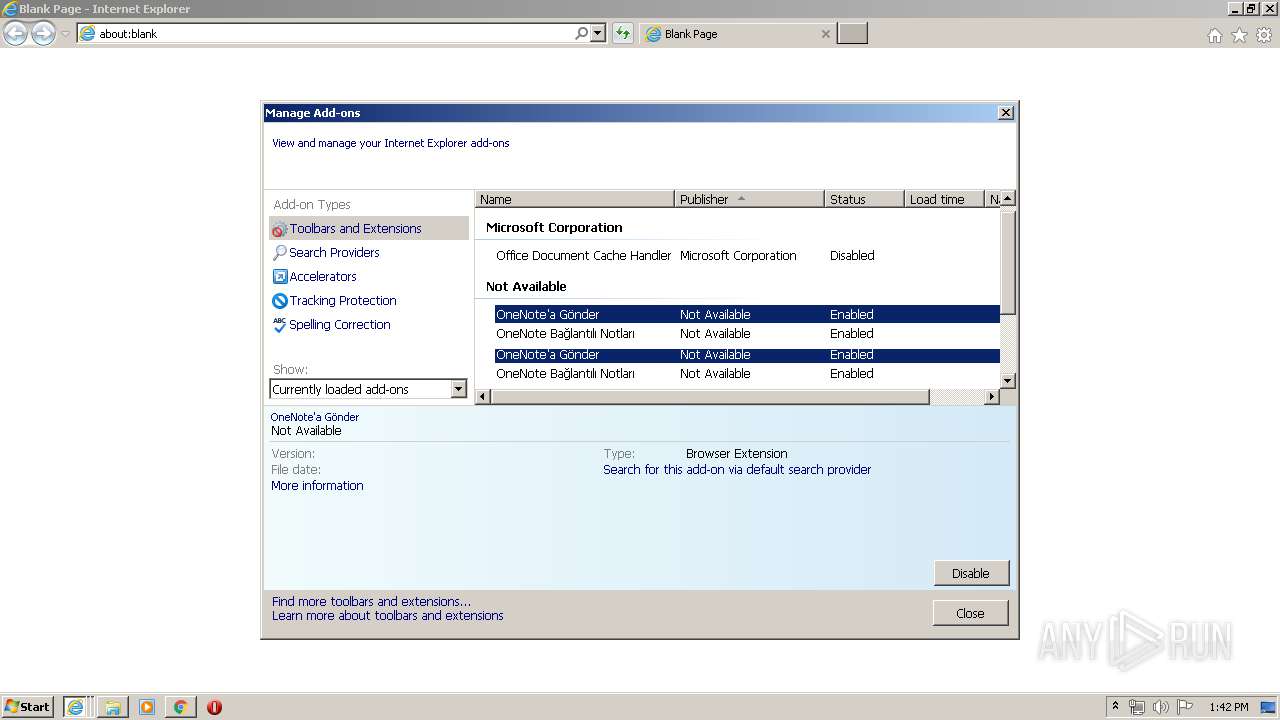
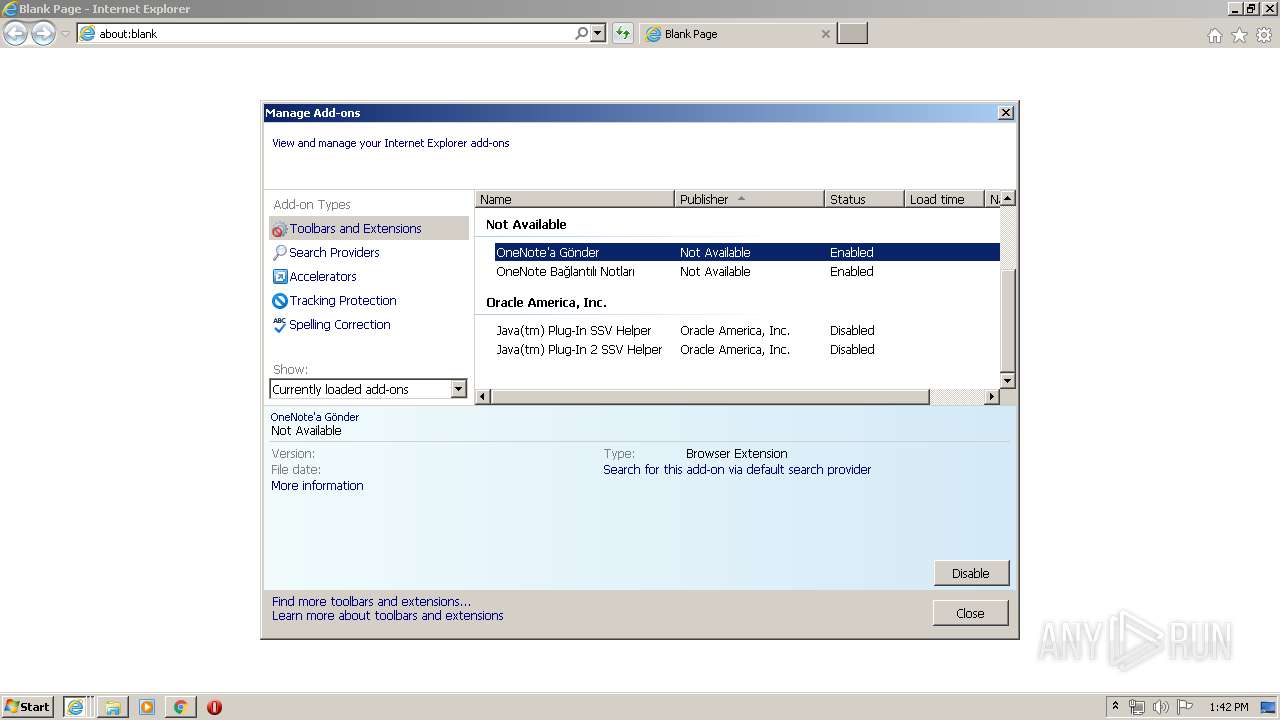
Changes internet zones settings
- iexplore.exe (PID: 2532)
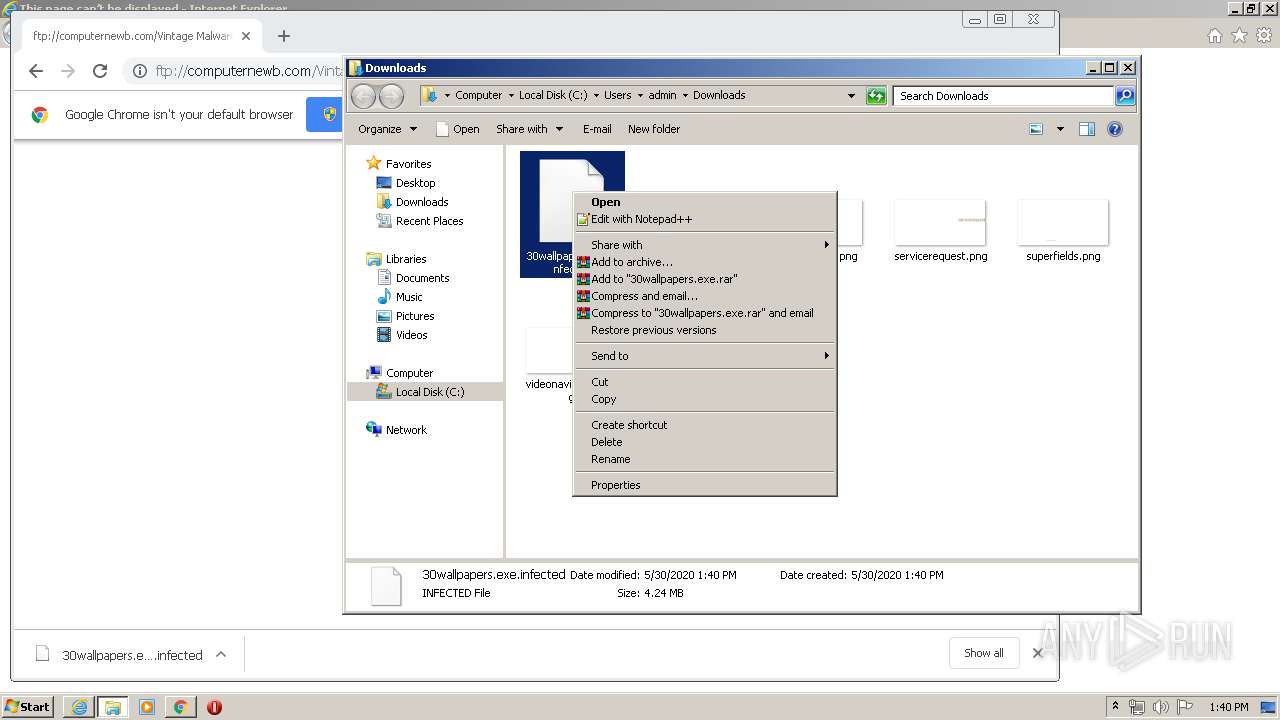
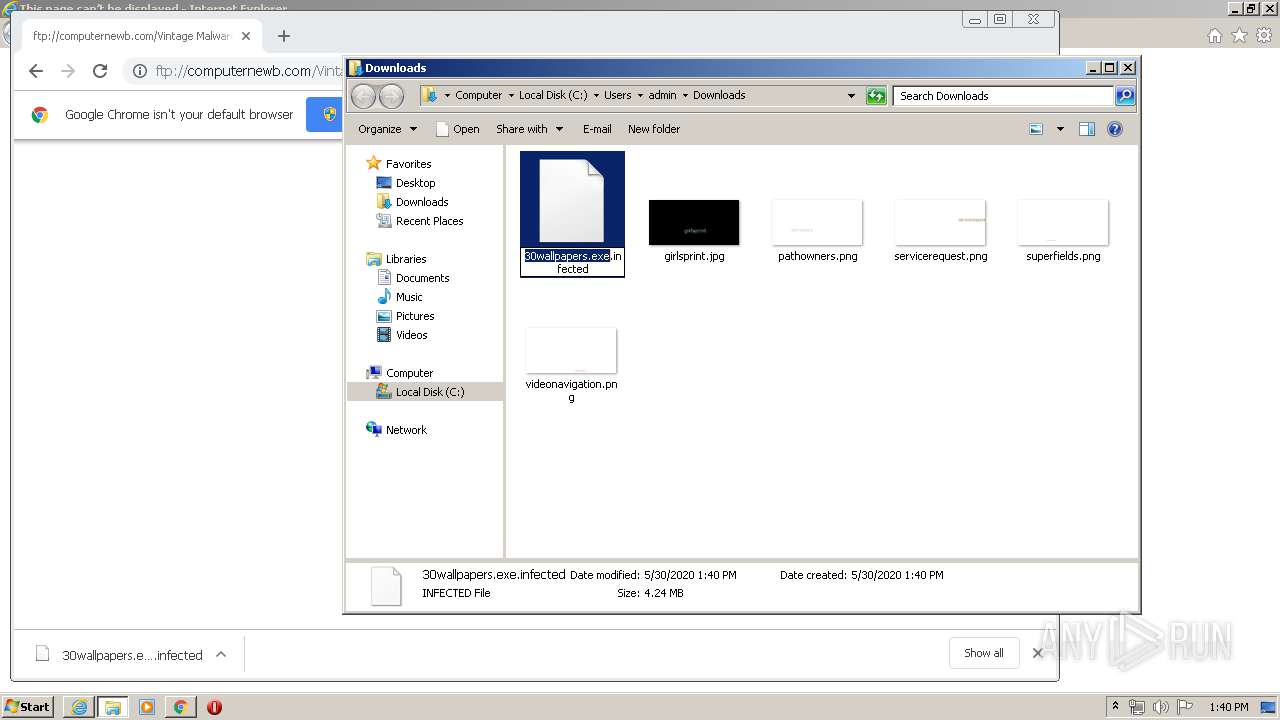
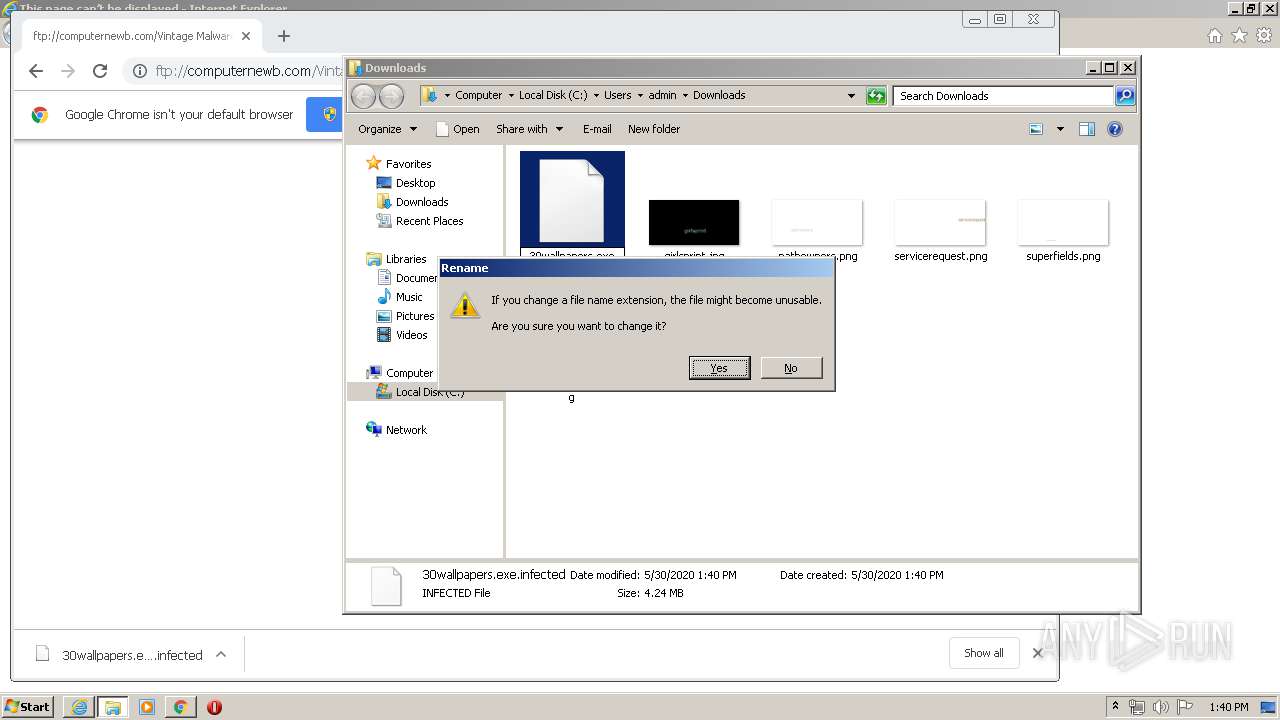
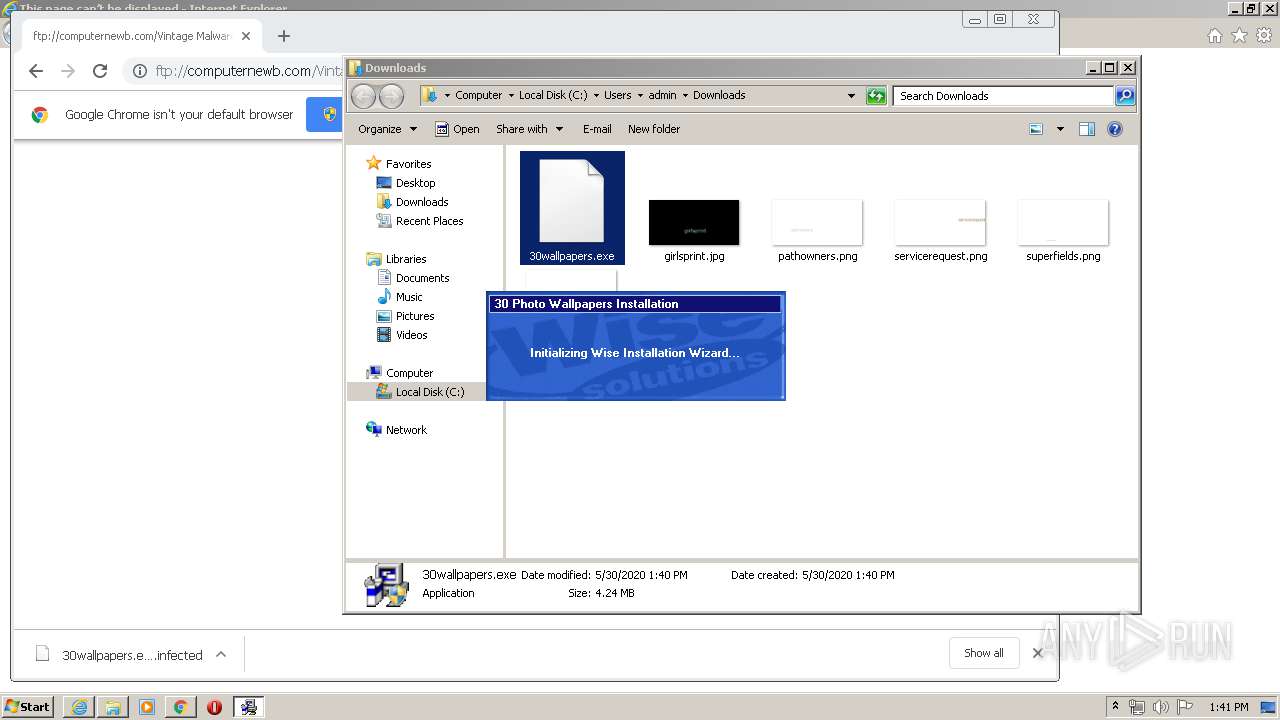
Manual execution by user
- chrome.exe (PID: 2000)
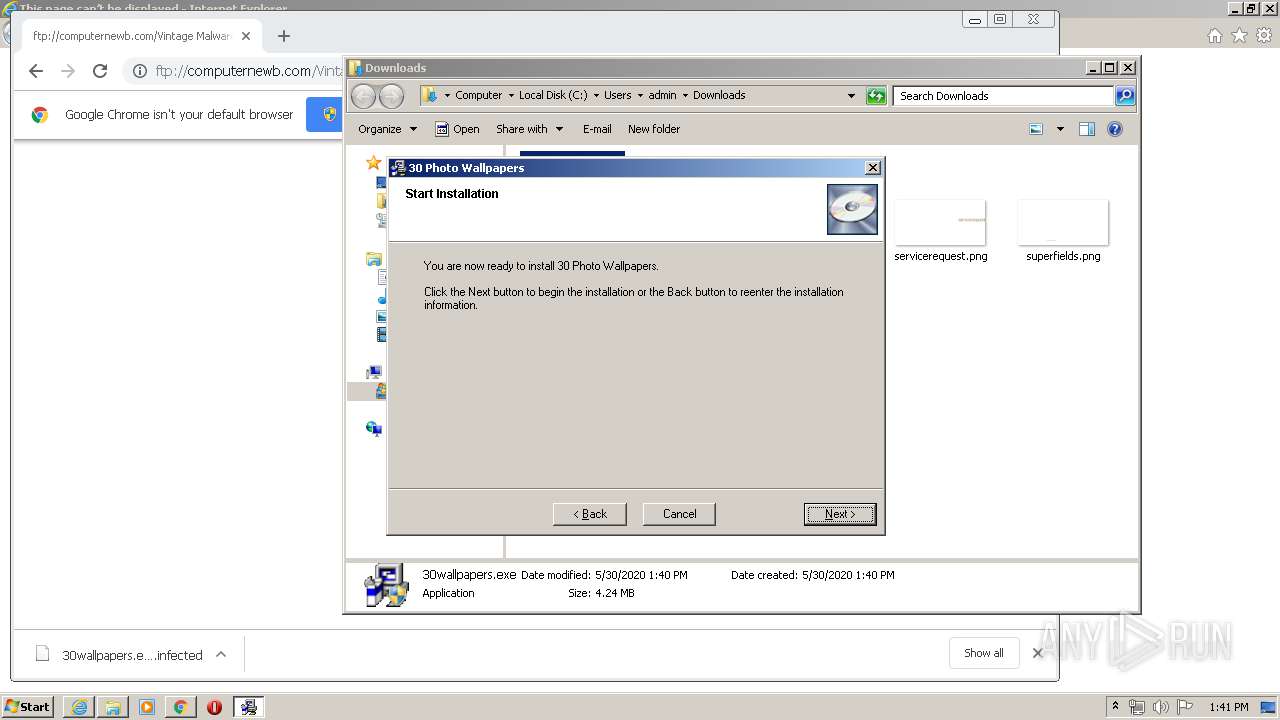
- 30wallpapers.exe (PID: 1484)
- 30wallpapers.exe (PID: 1948)
Creates files in the user directory
- iexplore.exe (PID: 2532)
Reads settings of System Certificates
- chrome.exe (PID: 2160)
- iexplore.exe (PID: 2532)
Reads internet explorer settings
- iexplore.exe (PID: 2388)
- iexplore.exe (PID: 356)
- iexplore.exe (PID: 576)
Dropped object may contain Bitcoin addresses
- VVSN.exe (PID: 2228)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2532)
Changes settings of System certificates
- iexplore.exe (PID: 2532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
91
Monitored processes
47
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2532 CREDAT:988436 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 396 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2532 CREDAT:2692367 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1860 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 708 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 840 | "C:\30PHOT~1\VVSNInst.exe" /cfg:ADFS030501 /d"30 Photo Wallpapers" /f"C:\30 Photo Wallpapers\License.txt" /whenu:1 /tADFS0305010003 | C:\30PHOT~1\VVSNInst.exe | 30wallpapers.exe | ||||||||||||
User: admin Company: WhenU.com, Inc Integrity Level: HIGH Description: UInstall Application Exit code: 0 Version: 1, 0, 1, 2 Modules
| |||||||||||||||
| 872 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,2139140531979121364,14448150295278423697,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11265182561334578755 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2448 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,2139140531979121364,14448150295278423697,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8172420624984002116 --mojo-platform-channel-handle=3724 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,2139140531979121364,14448150295278423697,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17764150783425255924 --mojo-platform-channel-handle=5004 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
16 021
Read events
8 094
Write events
5 522
Delete events
2 405
Modification events
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2079122684 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30815871 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
18
Suspicious files
40
Text files
283
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5ED25429-7D0.pma | — | |
MD5:— | SHA256:— | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\67e73b67-a53b-4dd3-8c4c-8a4747283055.tmp | — | |
MD5:— | SHA256:— | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF10da54.TMP | text | |
MD5:— | SHA256:— | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF10dae1.TMP | — | |
MD5:— | SHA256:— | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF10da16.TMP | text | |
MD5:— | SHA256:— | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF10da93.TMP | text | |
MD5:— | SHA256:— | |||
| 2000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
39
DNS requests
43
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2160 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
2532 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2160 | chrome.exe | GET | 200 | 173.194.191.135:80 | http://r2---sn-q4fl6ns7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=85.203.20.11&mm=28&mn=sn-q4fl6ns7&ms=nvh&mt=1590842288&mv=u&mvi=1&pl=25&shardbypass=yes | US | crx | 816 Kb | whitelisted |
2160 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
2532 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2532 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2532 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2160 | chrome.exe | GET | 200 | 173.194.141.235:80 | http://r5---sn-q4f7sn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=85.203.20.11&mm=28&mn=sn-q4f7sn7k&ms=nvh&mt=1590842288&mv=u&mvi=4&pl=25&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2388 | iexplore.exe | 104.219.234.138:21 | computernewb.com | DataWagon LLC | US | suspicious |
2532 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2160 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2160 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2160 | chrome.exe | 172.217.16.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
— | — | 216.58.210.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
— | — | 216.58.206.14:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
— | — | 216.58.206.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.16.174:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
computernewb.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2388 | iexplore.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2388 | iexplore.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2160 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2160 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |