| File name: | dc4e4ada96a6ec485683a71096930dab.exe |
| Full analysis: | https://app.any.run/tasks/0bfe4c3e-cbbb-4449-a03b-ac24885dd18b |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 13:58:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | DC4E4ADA96A6EC485683A71096930DAB |
| SHA1: | 6CFC07BAAE07F5FA7E66B454DB47CB770B686431 |
| SHA256: | 21BAB9F86ACB800C9D684DEE7015E45D6E005E09FFE8C57FDFA98FB3A20FE245 |
| SSDEEP: | 98304:Oyi35icoKogj0YjbdDXayrZryYCUVUZ/f9Mj2tikcazgDoY0291uQ4+zqkUxSd2Z:lgBkzai |
MALICIOUS
Adds path to the Windows Defender exclusion list
- NSudoLG.exe (PID: 4108)
Changes Windows Defender settings
- NSudoLG.exe (PID: 4108)
SUSPICIOUS
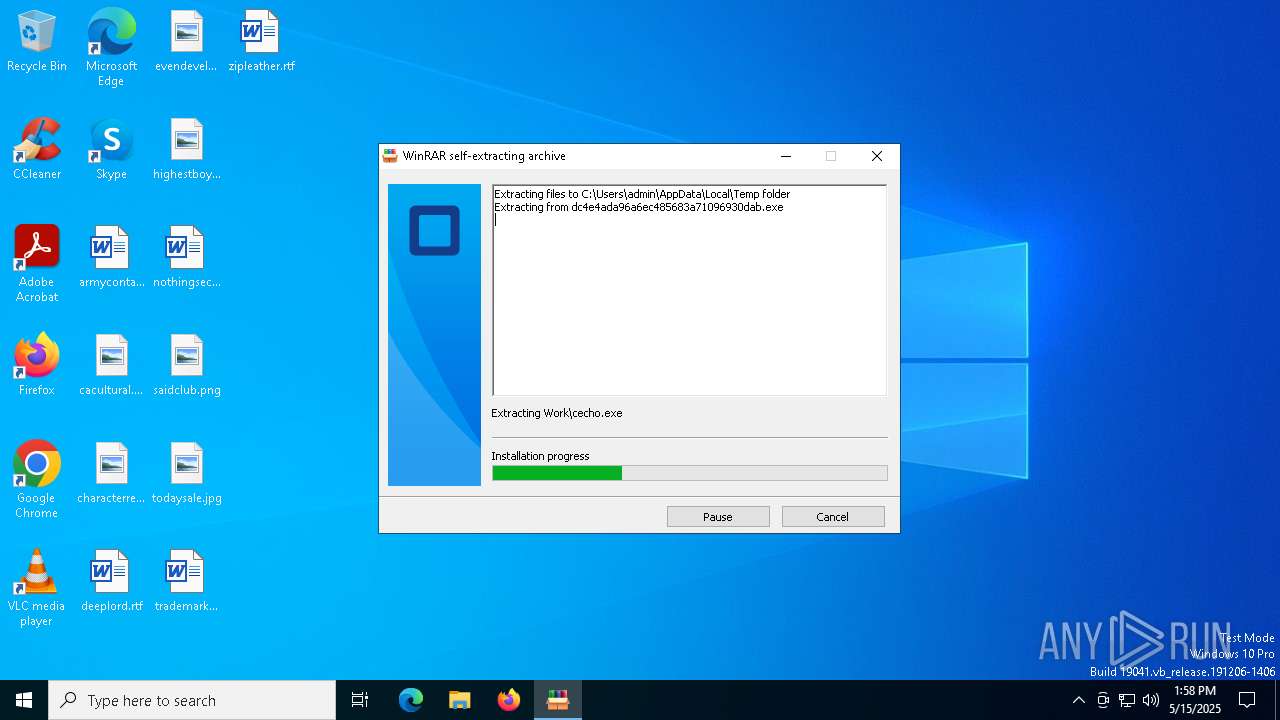
Drops 7-zip archiver for unpacking
- dc4e4ada96a6ec485683a71096930dab.exe (PID: 5072)
Executable content was dropped or overwritten
- dc4e4ada96a6ec485683a71096930dab.exe (PID: 5072)
- 7z.exe (PID: 7444)
- Unlocker.exe (PID: 7924)
The process creates files with name similar to system file names
- dc4e4ada96a6ec485683a71096930dab.exe (PID: 5072)
Executing commands from a ".bat" file
- dc4e4ada96a6ec485683a71096930dab.exe (PID: 5072)
Reads security settings of Internet Explorer
- dc4e4ada96a6ec485683a71096930dab.exe (PID: 5072)
- Unlocker.exe (PID: 7468)
- Unlocker.exe (PID: 7924)
- Unlocker.exe (PID: 8160)
Starts CMD.EXE for commands execution
- dc4e4ada96a6ec485683a71096930dab.exe (PID: 5072)
- Unlocker.exe (PID: 7468)
- Unlocker.exe (PID: 7924)
- Unlocker.exe (PID: 8160)
The executable file from the user directory is run by the CMD process
- NSudoLG.exe (PID: 4108)
- 7z.exe (PID: 7444)
- Unlocker.exe (PID: 7468)
- Unlocker.exe (PID: 7924)
- Unlocker.exe (PID: 8160)
Starts POWERSHELL.EXE for commands execution
- NSudoLG.exe (PID: 4108)
Script adds exclusion path to Windows Defender
- NSudoLG.exe (PID: 4108)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 6964)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7620)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 1096)
Reads the date of Windows installation
- Unlocker.exe (PID: 7468)
- Unlocker.exe (PID: 7924)
- Unlocker.exe (PID: 8160)
Starts SC.EXE for service management
- cmd.exe (PID: 7540)
- cmd.exe (PID: 8024)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 7316)
Windows service management via SC.EXE
- sc.exe (PID: 7592)
- sc.exe (PID: 8080)
- sc.exe (PID: 4000)
- sc.exe (PID: 4068)
Drops a system driver (possible attempt to evade defenses)
- Unlocker.exe (PID: 7924)
Creates or modifies Windows services
- Unlocker.exe (PID: 7924)
Stops a currently running service
- sc.exe (PID: 1328)
INFO
Reads the computer name
- dc4e4ada96a6ec485683a71096930dab.exe (PID: 5072)
- NSudoLG.exe (PID: 4108)
- 7z.exe (PID: 7444)
- Unlocker.exe (PID: 7468)
- IObitUnlocker.exe (PID: 8116)
- IObitUnlocker.exe (PID: 7224)
- Unlocker.exe (PID: 7924)
- Unlocker.exe (PID: 8160)
Create files in a temporary directory
- dc4e4ada96a6ec485683a71096930dab.exe (PID: 5072)
- 7z.exe (PID: 7444)
Checks supported languages
- dc4e4ada96a6ec485683a71096930dab.exe (PID: 5072)
- NSudoLG.exe (PID: 4108)
- 7z.exe (PID: 7444)
- Unlocker.exe (PID: 7468)
- IObitUnlocker.exe (PID: 8116)
- IObitUnlocker.exe (PID: 7224)
- Unlocker.exe (PID: 7924)
- Unlocker.exe (PID: 8160)
Process checks computer location settings
- dc4e4ada96a6ec485683a71096930dab.exe (PID: 5072)
The sample compiled with english language support
- dc4e4ada96a6ec485683a71096930dab.exe (PID: 5072)
- Unlocker.exe (PID: 7924)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6964)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6964)
Reads the machine GUID from the registry
- Unlocker.exe (PID: 7468)
- Unlocker.exe (PID: 7924)
- Unlocker.exe (PID: 8160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:03:03 13:15:57+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.3 |
| CodeSize: | 203776 |
| InitializedDataSize: | 261632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1f530 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
293
Monitored processes
37
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1012 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | "C:\Windows\System32\cmd.exe" /c taskkill /f /pid "7924" | C:\Windows\System32\cmd.exe | — | Unlocker.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 1300 | "C:\Windows\System32\cmd.exe" /c taskkill /f /pid "8160" | C:\Windows\System32\cmd.exe | — | Unlocker.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | sc stop IObitUnlocker | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | taskkill /f /pid "7924" | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Terminates Processes Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3020 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4000 | sc query IObitUnlocker | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4008 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 493
Read events
8 487
Write events
5
Delete events
1
Modification events
| (PID) Process: | (7468) Unlocker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\DK |
| Operation: | write | Name: | CurrentDiskSize |
Value: 228911710208 | |||
| (PID) Process: | (7924) Unlocker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\IObitUnlocker |
| Operation: | write | Name: | Type |
Value: 1 | |||
| (PID) Process: | (7924) Unlocker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\IObitUnlocker |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (7924) Unlocker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\IObitUnlocker |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
| (PID) Process: | (7924) Unlocker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\IObitUnlocker |
| Operation: | write | Name: | ImagePath |
Value: C:\WINDOWS\TEMP\IObitUnlocker\IObitUnlocker.sys | |||
| (PID) Process: | (8160) Unlocker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\DK |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
8
Suspicious files
3
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5072 | dc4e4ada96a6ec485683a71096930dab.exe | C:\Users\admin\AppData\Local\Temp\Work\7z.exe | executable | |
MD5:426CCB645E50A3143811CFA0E42E2BA6 | SHA256:CF878BFBD9ED93DC551AC038AFF8A8BBA4C935DDF8D48E62122BDDFDB3E08567 | |||
| 6964 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_d544hjrz.3wf.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6964 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_r1xxedvc.53r.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7924 | Unlocker.exe | C:\Windows\Temp\IObitUnlocker\IObitUnlocker.exe | executable | |
MD5:2541290195FFE29716EBBC7AAC76D82F | SHA256:EAA9DC1C9DC8620549FEE54D81399488292349D2C8767B58B7D0396564FB43E7 | |||
| 6964 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:4F25CE1D261E11CEDE00B9C73F00F30B | SHA256:5AC9E76564F3F9ED1D0B6C8CC60D41A676607B33783D08D21A353842F4FF76D7 | |||
| 7924 | Unlocker.exe | C:\Windows\Temp\IObitUnlocker\IObitUnlocker.dll | executable | |
MD5:2C6233C8DBC560027EE1427F5413E4B1 | SHA256:37D2A1626DC205D60F0BEC8746AB256569267E4EF2F8F84DFF4D9D792AA3AF30 | |||
| 5072 | dc4e4ada96a6ec485683a71096930dab.exe | C:\Users\admin\AppData\Local\Temp\Work\cecho.exe | executable | |
MD5:E783BC59D0ED6CFBD8891F94AE23D1B3 | SHA256:5C1211559DDA10592CFEDD57681F18F4A702410816D36EDA95AEE6C74E3C6A47 | |||
| 5072 | dc4e4ada96a6ec485683a71096930dab.exe | C:\Users\admin\AppData\Local\Temp\b0Y19sD.bat | text | |
MD5:350D172630B12F10564C78EEF37E3F95 | SHA256:73BC1BD40DCB68AC6DBF25FFB5E0B708F43FD4CA8A17D08647EEB89641B37062 | |||
| 5072 | dc4e4ada96a6ec485683a71096930dab.exe | C:\Users\admin\AppData\Local\Temp\Work\DKTolz.zip | compressed | |
MD5:6B617C0196FE449E27C84532EC2C38E7 | SHA256:E3528C57765074D5D73021F747B26EDEFA15227D0F1A3B80A6CDEF21322C99CA | |||
| 5072 | dc4e4ada96a6ec485683a71096930dab.exe | C:\Users\admin\AppData\Local\Temp\Work\nircmd.exe | executable | |
MD5:4A9DA765FD91E80DECFD2C9FE221E842 | SHA256:2E81E048AB419FDC6E5F4336A951BD282ED6B740048DC38D7673678EE3490CDA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
21
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1128 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1128 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |