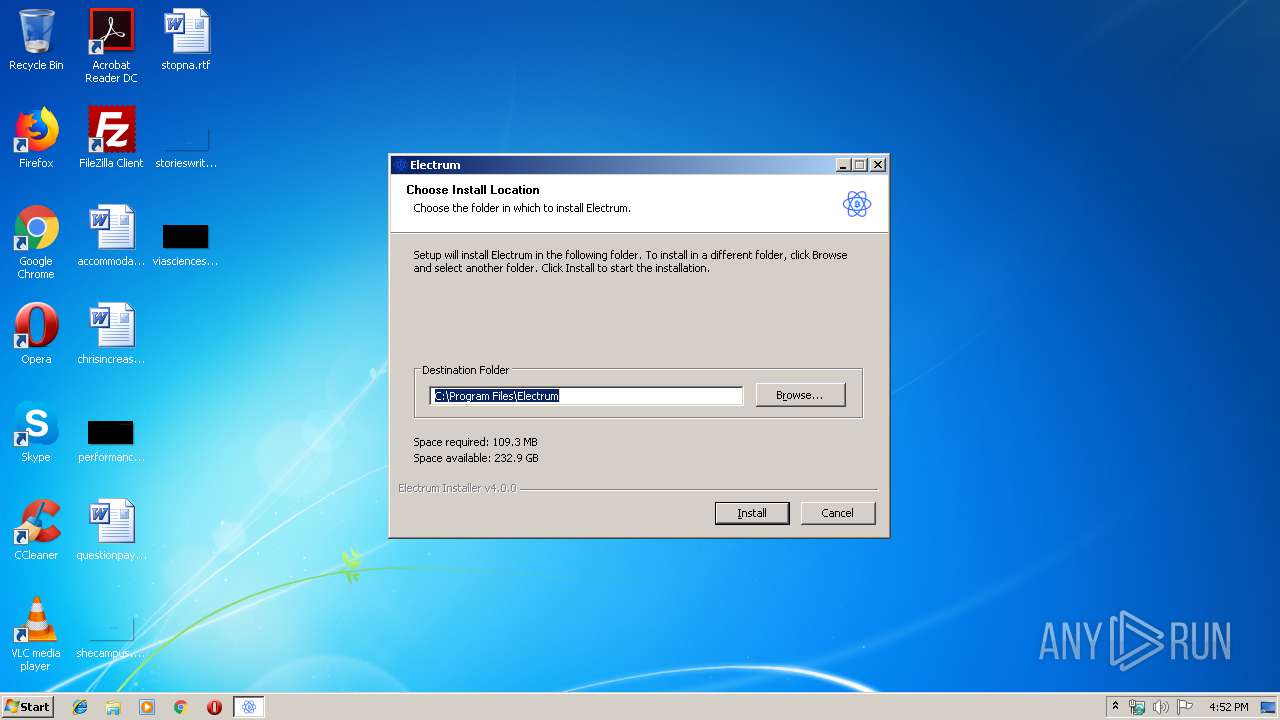
| download: | electrum-4.0.0-setup.exe |
| Full analysis: | https://app.any.run/tasks/bec55617-666b-488f-9634-6223640cfe55 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 15:51:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | CEAAB266DFCC571A00A4944BE14A174A |
| SHA1: | C166DF3FD344D3AD1BB3C2213C18D7AB9859C685 |
| SHA256: | 21B90EF6BA6EC6445495F287DA640F749ED0B2E43DD566ACD5B894527BE199E8 |
| SSDEEP: | 786432:rCMK0TS7SbH4y2EdI4h8AFo/LD5ckUKSWhQnhiAbZA:uN0TS7SbHj5IKQzD55U4WLq |
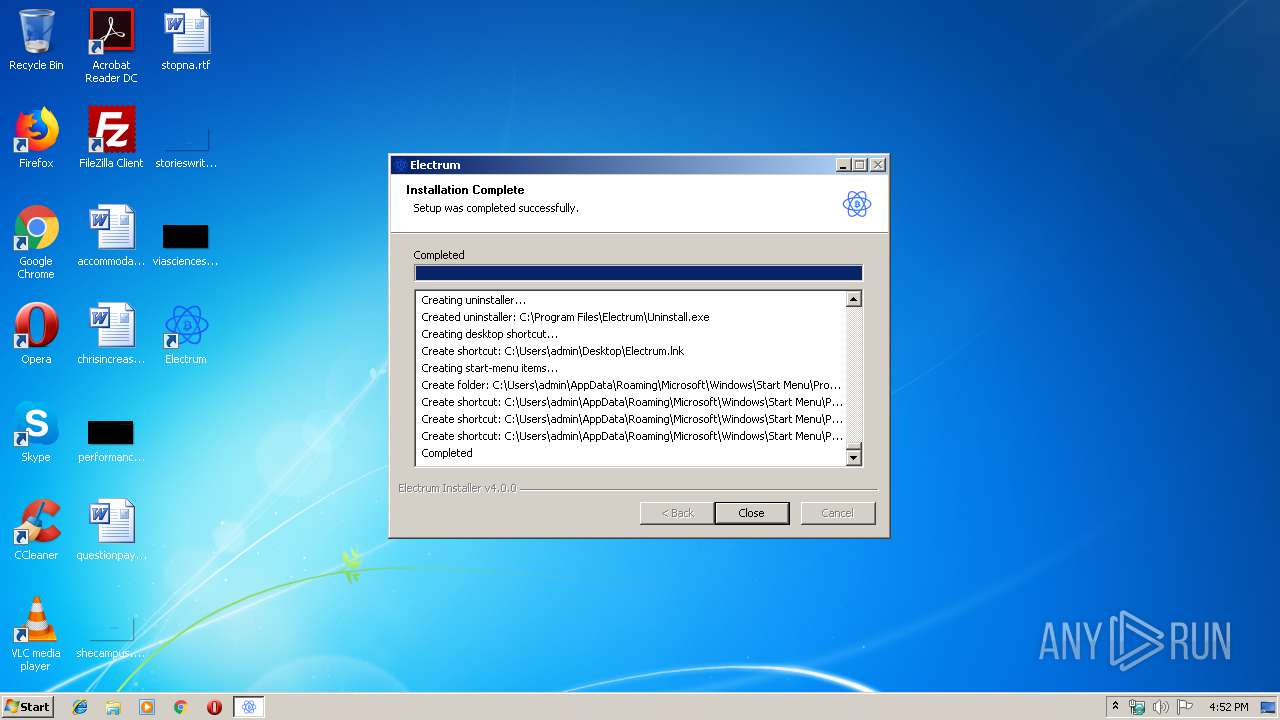
MALICIOUS
Loads dropped or rewritten executable
- electrum-4.0.0-setup.exe (PID: 3824)
SUSPICIOUS
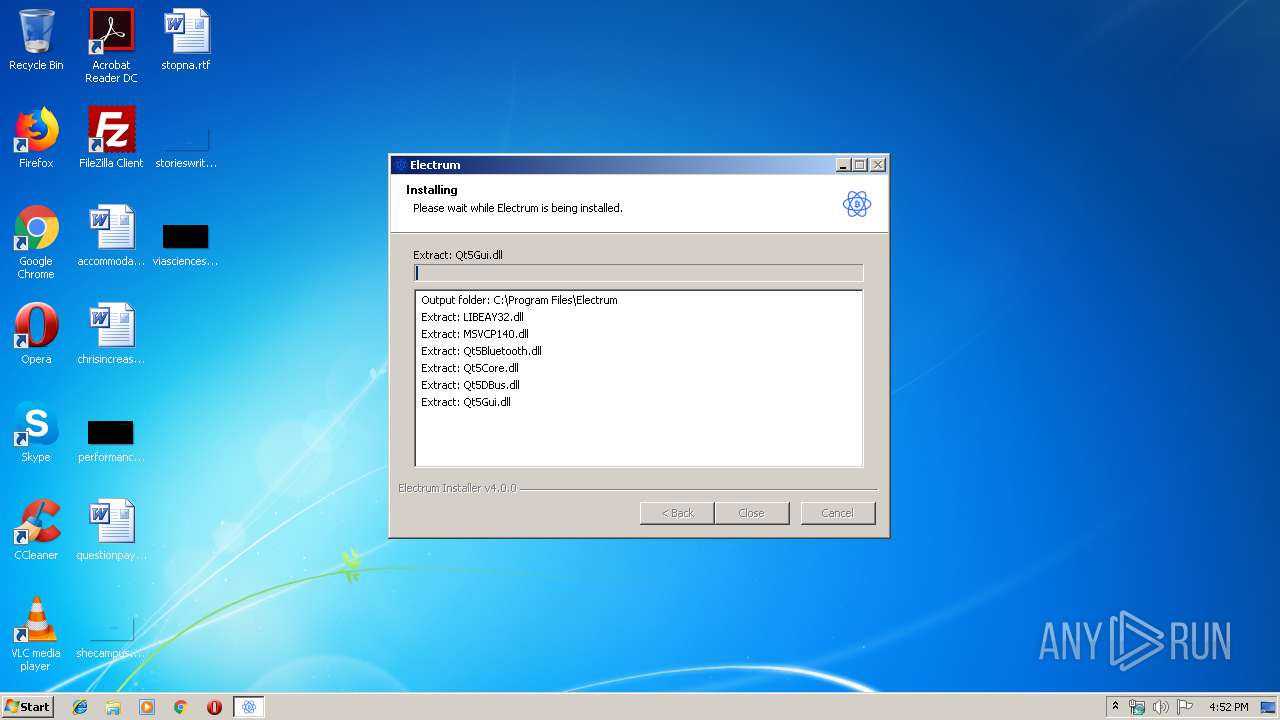
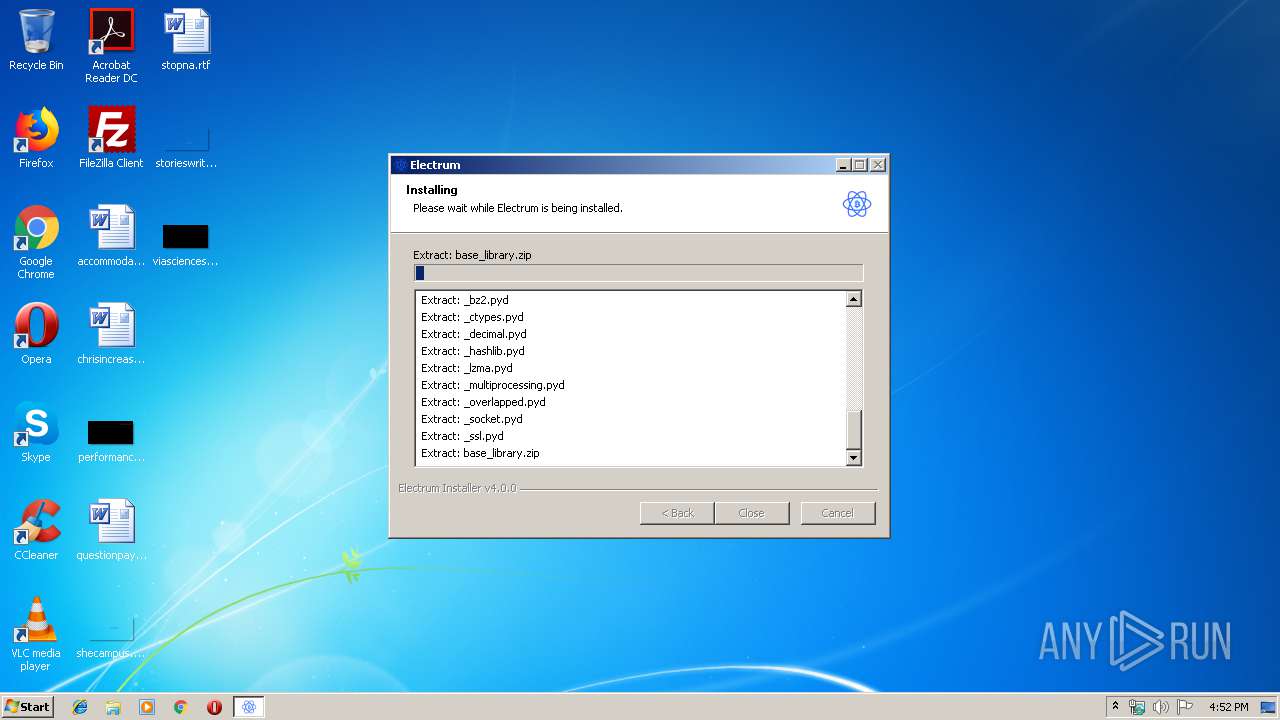
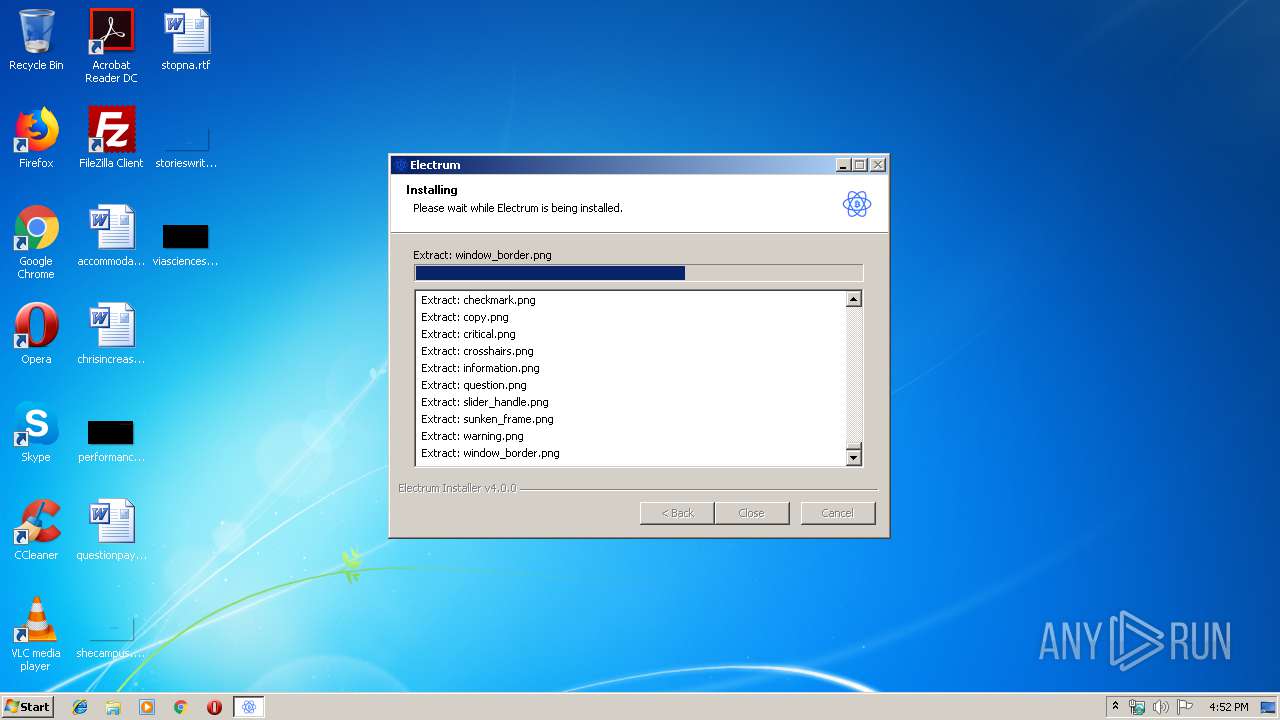
Executable content was dropped or overwritten
- electrum-4.0.0-setup.exe (PID: 3824)
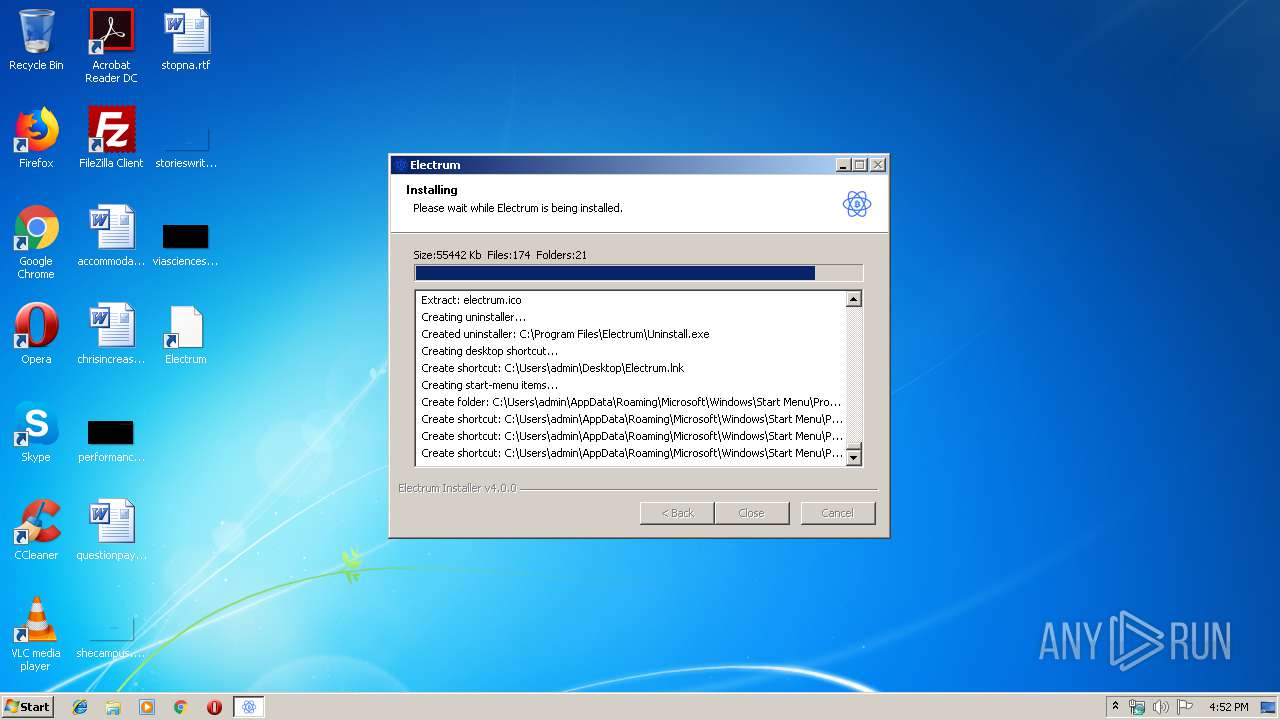
Creates files in the user directory
- electrum-4.0.0-setup.exe (PID: 3824)
Creates a software uninstall entry
- electrum-4.0.0-setup.exe (PID: 3824)
Modifies the open verb of a shell class
- electrum-4.0.0-setup.exe (PID: 3824)
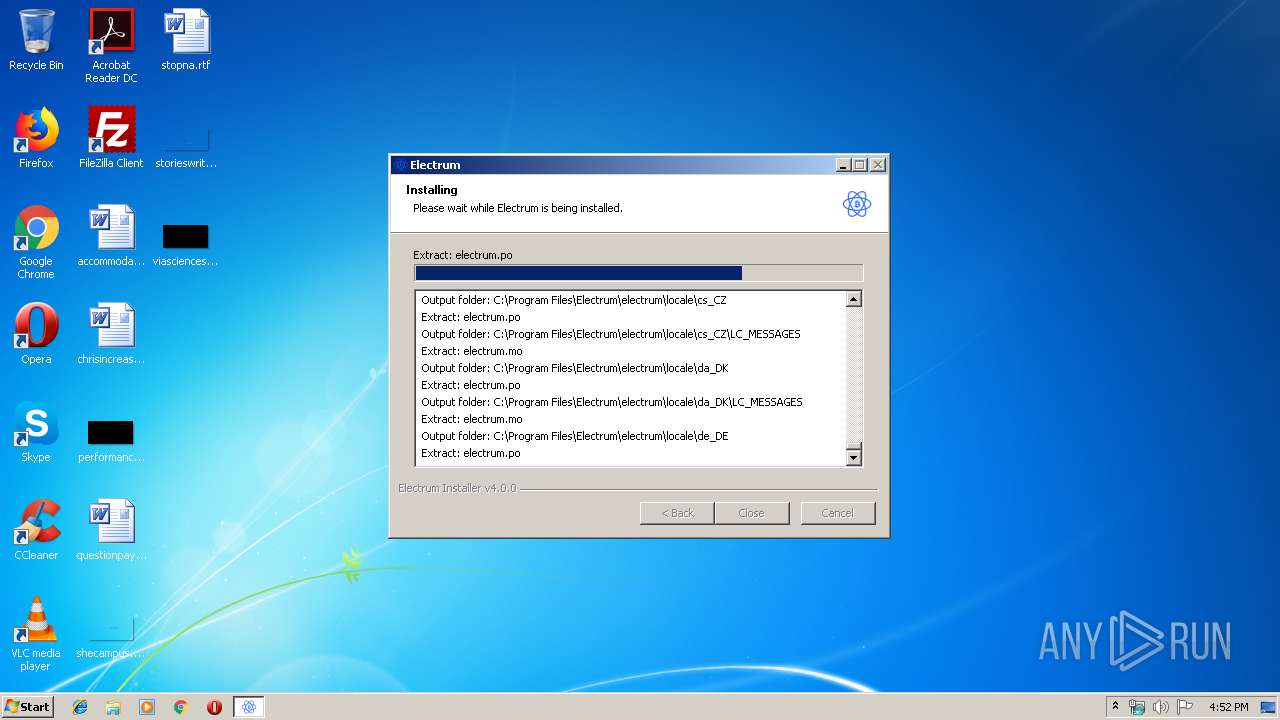
Creates files in the program directory
- electrum-4.0.0-setup.exe (PID: 3824)
INFO
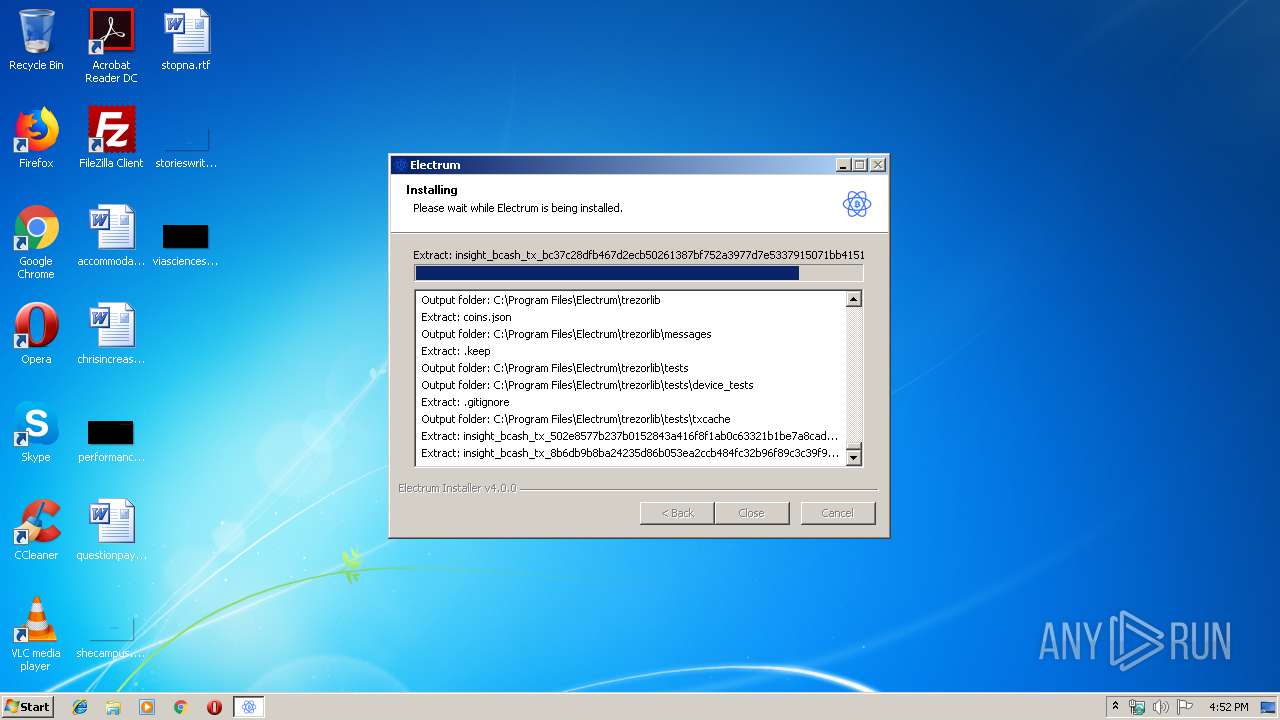
Dropped object may contain Bitcoin addresses
- electrum-4.0.0-setup.exe (PID: 3824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 04:57:38+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3328 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | The installer for Electrum |
| CompanyName: | Electrum |
| FileDescription: | Electrum Installer |
| FileVersion: | 4.0.0 |
| InternalName: | Electrum Installer |
| LegalCopyright: | 2013-2018 Electrum Technologies GmbH |
| LegalTrademarks: | Electrum is a trademark of Electrum Technologies GmbH |
| OriginalFileName: | Electrum.exe |
| ProductName: | Electrum Installer |
| ProductVersion: | 4.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2018 03:57:38 |
| Detected languages: |
|
| Comments: | The installer for Electrum |
| CompanyName: | Electrum |
| FileDescription: | Electrum Installer |
| FileVersion: | 4.0.0 |
| InternalName: | Electrum Installer |
| LegalCopyright: | 2013-2018 Electrum Technologies GmbH |
| LegalTrademarks: | Electrum is a trademark of Electrum Technologies GmbH |
| OriginalFilename: | Electrum.exe |
| ProductName: | Electrum Installer |
| ProductVersion: | 4.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jan-2018 03:57:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006077 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40397 |
.rdata | 0x00008000 | 0x00001248 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04426 |
.data | 0x0000A000 | 0x0001A838 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.22445 |
.ndata | 0x00025000 | 0x0000F000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00034000 | 0x0000DB58 | 0x0000DC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.07447 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28813 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.20642 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 3.52336 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 2.80722 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 2.47831 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 2.66811 | 1640 | UNKNOWN | English - United States | RT_ICON |
7 | 1.15935 | 1384 | UNKNOWN | English - United States | RT_ICON |
8 | 4.17452 | 1128 | UNKNOWN | English - United States | RT_ICON |
9 | 2.65167 | 744 | UNKNOWN | English - United States | RT_ICON |
10 | 1.734 | 296 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
41
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
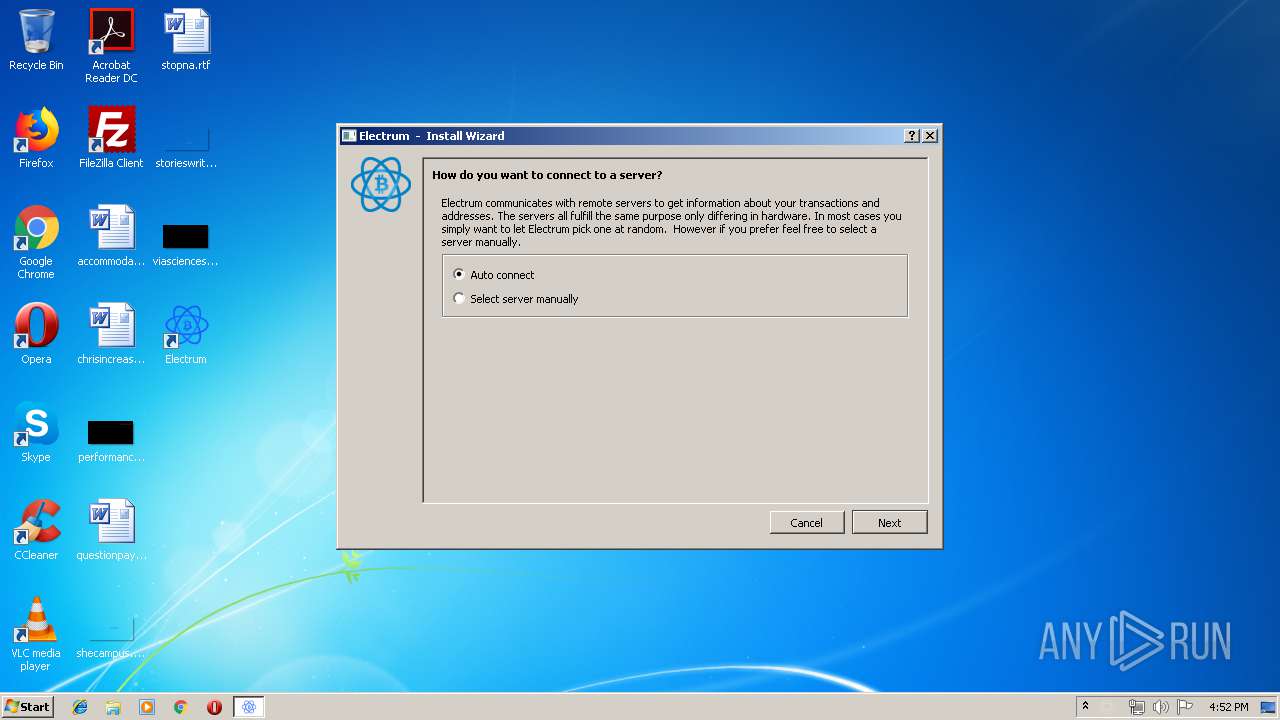
| 1744 | "C:\Program Files\Electrum\electrum-4.0.0.exe" | C:\Program Files\Electrum\electrum-4.0.0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 | |||||||||||||||
| 2976 | C:\Windows\system32\cmd.exe /c fsutil sparse setflag "C:\Users\admin\AppData\Roaming\Electrum\blockchain_headers" 1 | C:\Windows\system32\cmd.exe | — | electrum-4.0.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | |||||||||||||||
| 3508 | "C:\Users\admin\AppData\Local\Temp\electrum-4.0.0-setup.exe" | C:\Users\admin\AppData\Local\Temp\electrum-4.0.0-setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Electrum Integrity Level: MEDIUM Description: Electrum Installer Exit code: 3221226540 Version: 4.0.0 Modules
| |||||||||||||||
| 3824 | "C:\Users\admin\AppData\Local\Temp\electrum-4.0.0-setup.exe" | C:\Users\admin\AppData\Local\Temp\electrum-4.0.0-setup.exe | explorer.exe | ||||||||||||
User: admin Company: Electrum Integrity Level: HIGH Description: Electrum Installer Exit code: 0 Version: 4.0.0 Modules
| |||||||||||||||
| 4016 | fsutil sparse setflag "C:\Users\admin\AppData\Roaming\Electrum\blockchain_headers" 1 | C:\Windows\system32\fsutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: fsutil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
Total events
353
Read events
342
Write events
11
Delete events
0
Modification events
| (PID) Process: | (3824) electrum-4.0.0-setup.exe | Key: | HKEY_CURRENT_USER\Software\Electrum |
| Operation: | write | Name: | |
Value: C:\Program Files\Electrum | |||
| (PID) Process: | (3824) electrum-4.0.0-setup.exe | Key: | HKEY_CLASSES_ROOT\bitcoin |
| Operation: | write | Name: | |
Value: URL:bitcoin Protocol | |||
| (PID) Process: | (3824) electrum-4.0.0-setup.exe | Key: | HKEY_CLASSES_ROOT\bitcoin |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (3824) electrum-4.0.0-setup.exe | Key: | HKEY_CLASSES_ROOT\bitcoin |
| Operation: | write | Name: | DefaultIcon |
Value: "C:\Program Files\Electrum\electrum.ico, 0" | |||
| (PID) Process: | (3824) electrum-4.0.0-setup.exe | Key: | HKEY_CLASSES_ROOT\bitcoin\shell\open\command |
| Operation: | write | Name: | |
Value: "C:\Program Files\Electrum\electrum-4.0.0.exe" "%1" | |||
| (PID) Process: | (3824) electrum-4.0.0-setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Electrum |
| Operation: | write | Name: | DisplayName |
Value: Electrum | |||
| (PID) Process: | (3824) electrum-4.0.0-setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Electrum |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Electrum\Uninstall.exe | |||
| (PID) Process: | (3824) electrum-4.0.0-setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Electrum |
| Operation: | write | Name: | DisplayVersion |
Value: 4.0.0 | |||
| (PID) Process: | (3824) electrum-4.0.0-setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Electrum |
| Operation: | write | Name: | URLInfoAbout |
Value: https://github.com/spesmilo/electrum | |||
| (PID) Process: | (3824) electrum-4.0.0-setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Electrum |
| Operation: | write | Name: | Publisher |
Value: Electrum Technologies GmbH | |||
Executable files
40
Suspicious files
1
Text files
13
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3824 | electrum-4.0.0-setup.exe | C:\Program Files\Electrum\Qt5DBus.dll | executable | |
MD5:— | SHA256:— | |||
| 3824 | electrum-4.0.0-setup.exe | C:\Program Files\Electrum\Qt5MultimediaWidgets.dll | executable | |
MD5:— | SHA256:— | |||
| 3824 | electrum-4.0.0-setup.exe | C:\Program Files\Electrum\Qt5SerialPort.dll | executable | |
MD5:— | SHA256:— | |||
| 3824 | electrum-4.0.0-setup.exe | C:\Program Files\Electrum\Qt5Help.dll | executable | |
MD5:— | SHA256:— | |||
| 3824 | electrum-4.0.0-setup.exe | C:\Program Files\Electrum\Qt5OpenGL.dll | executable | |
MD5:— | SHA256:— | |||
| 3824 | electrum-4.0.0-setup.exe | C:\Program Files\Electrum\Qt5NetworkAuth.dll | executable | |
MD5:— | SHA256:— | |||
| 3824 | electrum-4.0.0-setup.exe | C:\Program Files\Electrum\Qt5Bluetooth.dll | executable | |
MD5:— | SHA256:— | |||
| 3824 | electrum-4.0.0-setup.exe | C:\Program Files\Electrum\LIBEAY32.dll | executable | |
MD5:— | SHA256:— | |||
| 3824 | electrum-4.0.0-setup.exe | C:\Program Files\Electrum\Qt5Nfc.dll | executable | |
MD5:— | SHA256:— | |||
| 3824 | electrum-4.0.0-setup.exe | C:\Program Files\Electrum\Qt5PositioningQuick.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
30
DNS requests
44
Threats
104
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 111.90.159.213:50002 | electrum.esrv.one | Shinjiru Technology Sdn Bhd | MY | malicious |
— | — | 46.227.71.110:50002 | electrum.txid.pw | Obenetwork AB | SE | malicious |
— | — | 46.227.71.109:50002 | electrum.lightspeed.tel | Obenetwork AB | SE | malicious |
— | — | 27.102.129.56:50002 | electrum.livex.biz | DAOU TECHNOLOGY | KR | malicious |
— | — | 46.227.71.108:50002 | electrum.xs500.net | Obenetwork AB | SE | malicious |
— | — | 85.206.160.91:50002 | electrum.elastics.info | Informacines sistemos ir technologijos, UAB | LT | unknown |
— | — | 46.166.160.164:50002 | electrum.ssrv.info | UAB Cherry Servers | LT | malicious |
— | — | 185.25.48.104:50002 | electrum.rollerco.xyz | Informacines sistemos ir technologijos, UAB | LT | malicious |
— | — | 185.25.48.36:50002 | electrum.tnsfr.link | Informacines sistemos ir technologijos, UAB | LT | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
electrum.esrv.one |
| unknown |
bitcoin3nqy3db7c.onion |
| unknown |
wsw6tua3xl24gsmi264zaep6seppjyrkyucpsmuxnjzyt3f3j6swshad.onion |
| unknown |
hsmiths4fyqlw5xw.onion |
| unknown |
electrum.txid.pw |
| malicious |
bauerjda5hnedjam.onion |
| unknown |
electrum.tnsfr.link |
| malicious |
electrum.lightspeed.tel |
| malicious |
electrum.livex.biz |
| malicious |
ozahtqwp25chjdjd.onion |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
— | — | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |