| URL: | http://timestampindia.com/citech/Document/ |
| Full analysis: | https://app.any.run/tasks/8d1404e1-125b-423b-a648-d532e41fd680 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 17:13:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 655DDCA4392674E5387057FA5237932D |
| SHA1: | A439646A6A082CB1E492A5DF1B17AED0A2614A62 |
| SHA256: | 21AEC177786AF1C0690E96D0EFA22E969C436E3F080FD3D8063872B906A35DF5 |
| SSDEEP: | 3:N1KKMZR1xGKrxMyK:CK8R1v0 |
MALICIOUS
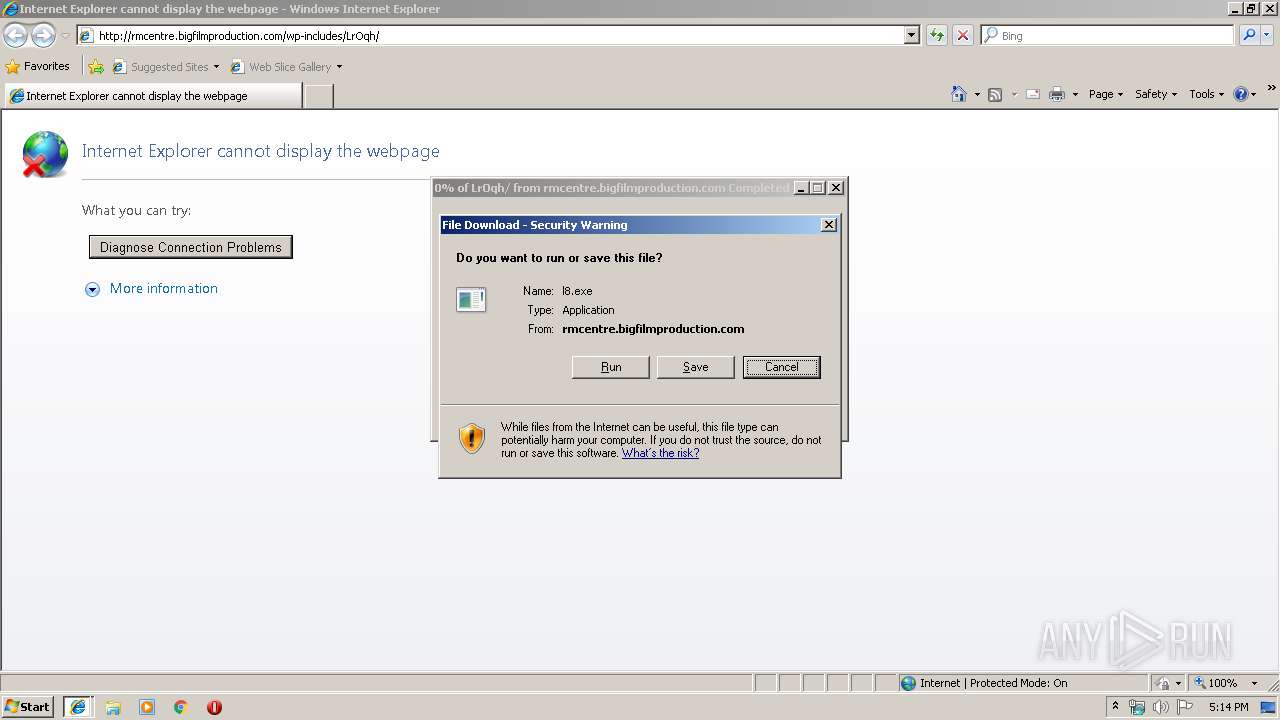
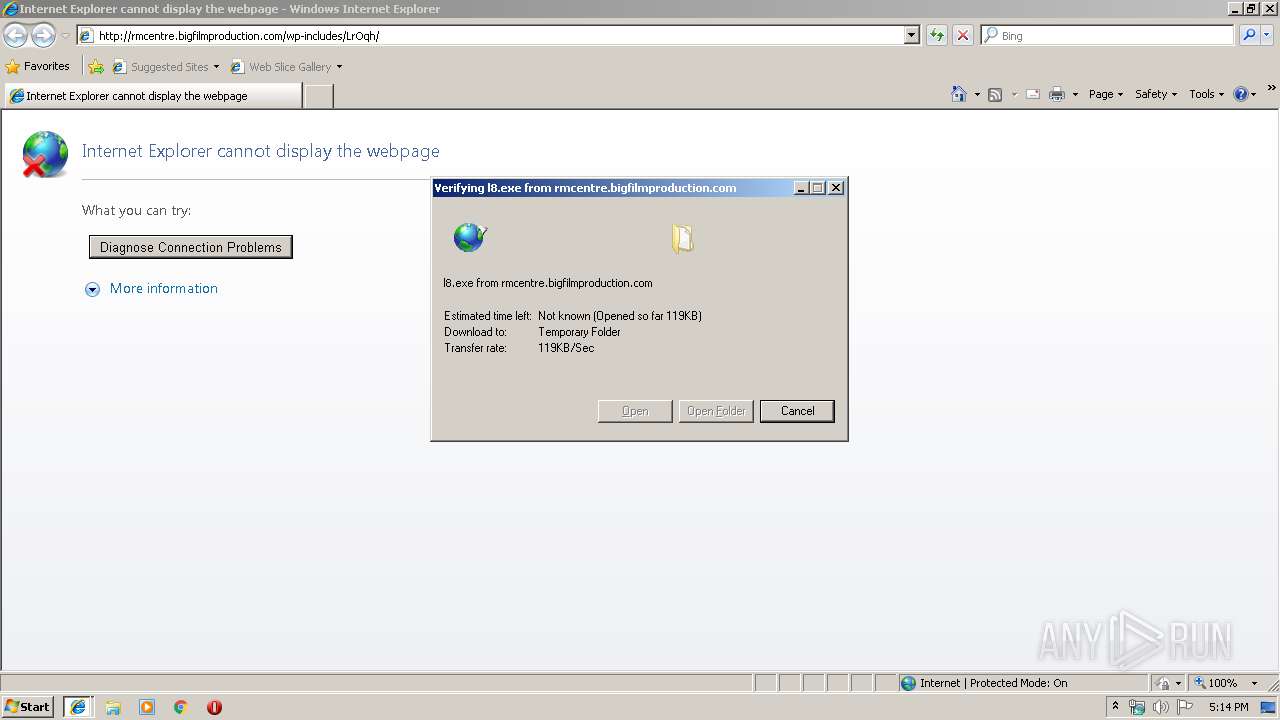
Downloads executable files from the Internet
- iexplore.exe (PID: 2372)
Application was dropped or rewritten from another process
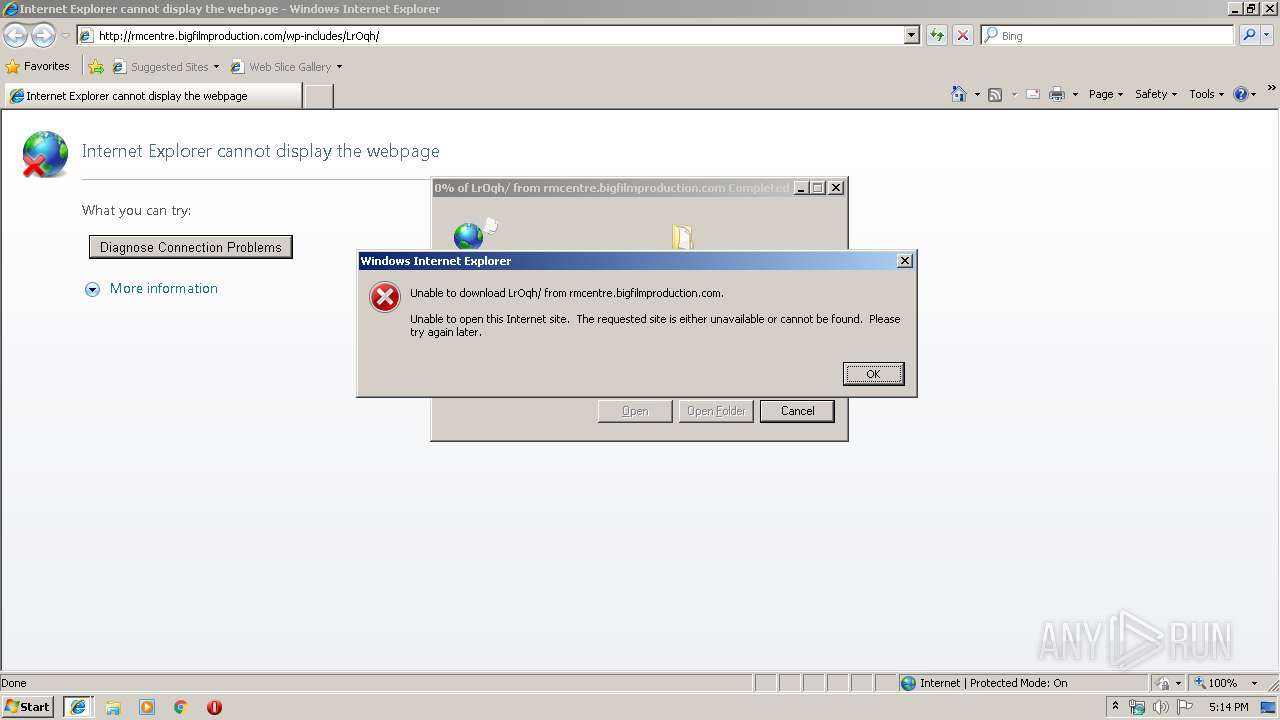
- LrOqh[1].exe (PID: 436)
- LrOqh[1].exe (PID: 3476)
- serialfunc.exe (PID: 2764)
- serialfunc.exe (PID: 3564)
Emotet process was detected
- LrOqh[1].exe (PID: 3476)
EMOTET was detected
- serialfunc.exe (PID: 2764)
Connects to CnC server
- serialfunc.exe (PID: 2764)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 2372)
- LrOqh[1].exe (PID: 3476)
- iexplore.exe (PID: 4000)
Cleans NTFS data-stream (Zone Identifier)
- LrOqh[1].exe (PID: 3476)
Starts itself from another location
- LrOqh[1].exe (PID: 3476)
Application launched itself
- serialfunc.exe (PID: 3564)
Connects to server without host name
- serialfunc.exe (PID: 2764)
INFO
Changes internet zones settings
- iexplore.exe (PID: 4000)
Reads internet explorer settings
- iexplore.exe (PID: 2372)
Application launched itself
- iexplore.exe (PID: 4000)
Reads Internet Cache Settings
- iexplore.exe (PID: 2372)
Creates files in the user directory
- iexplore.exe (PID: 2372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 436 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\LrOqh[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\LrOqh[1].exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4000 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2764 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3476 | --67cb4401 | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\LrOqh[1].exe | LrOqh[1].exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3564 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | LrOqh[1].exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 4000 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://timestampindia.com/citech/Document/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
735
Read events
675
Write events
60
Delete events
0
Modification events
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {C66E0CBD-184B-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070C000500060011000D0035008F00 | |||
Executable files
3
Suspicious files
0
Text files
28
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\1LLZCCW3\httpErrorPagesScripts[1] | text | |
MD5:E7CA76A3C9EE0564471671D500E3F0F3 | SHA256:58268CA71A28973B756A48BBD7C9DC2F6B87B62AE343E582CE067C725275B63C | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\1DUXQ40Q\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\1DUXQ40Q\errorPageStrings[1] | text | |
MD5:1A0563F7FB85A678771450B131ED66FD | SHA256:EB5678DE9D8F29CA6893D4E6CA79BD5AB4F312813820FE4997B009A2B1A1654C | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\9UXVF8AI\ErrorPageTemplate[1] | text | |
MD5:F4FE1CB77E758E1BA56B8A8EC20417C5 | SHA256:8D018639281B33DA8EB3CE0B21D11E1D414E59024C3689F92BE8904EB5779B5F | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\66TUW33G\dnserror[1] | html | |
MD5:68E03ED57EC741A4AFBBCD11FAB1BDBE | SHA256:1FF3334C3EB27033F8F37029FD72F648EDD4551FCE85FC1F5159FEAEA1439630 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
19
DNS requests
3
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2372 | iexplore.exe | GET | 301 | 103.117.180.4:80 | http://timestampindia.com/citech/Document/ | unknown | html | 251 b | suspicious |
2372 | iexplore.exe | GET | 301 | 103.117.180.4:80 | http://timestampindia.com/citech/Document/ | unknown | html | 251 b | suspicious |
2764 | serialfunc.exe | POST | — | 12.229.155.122:80 | http://12.229.155.122/nDveaAINp9vjZ10p4nM | US | — | — | malicious |
2764 | serialfunc.exe | POST | — | 107.2.2.28:80 | http://107.2.2.28/U67eF | US | — | — | malicious |
2764 | serialfunc.exe | POST | — | 108.191.2.72:80 | http://108.191.2.72/T6CPzaDd5kUvjON | US | — | — | malicious |
2764 | serialfunc.exe | POST | — | 108.179.206.219:8080 | http://108.179.206.219:8080/iUjGM5tBa5k5rAi | US | — | — | malicious |
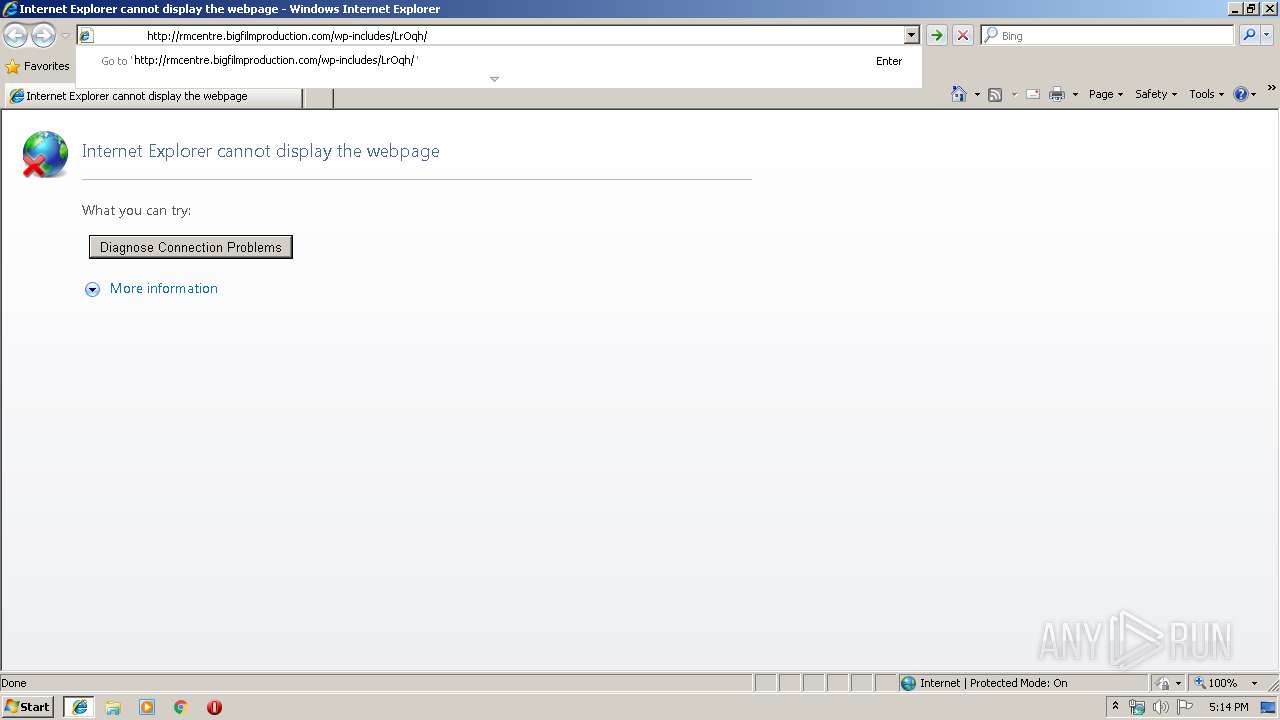
2372 | iexplore.exe | GET | 200 | 206.221.182.74:80 | http://rmcentre.bigfilmproduction.com/wp-includes/LrOqh/ | US | executable | 492 Kb | malicious |
2372 | iexplore.exe | GET | 200 | 206.221.182.74:80 | http://rmcentre.bigfilmproduction.com/wp-includes/LrOqh/ | US | executable | 492 Kb | malicious |
2764 | serialfunc.exe | POST | — | 59.110.18.236:443 | http://59.110.18.236:443/dms1RIeQsq3yvHHkTL | CN | — | — | malicious |
4000 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2372 | iexplore.exe | 206.221.182.74:80 | rmcentre.bigfilmproduction.com | Choopa, LLC | US | malicious |
2764 | serialfunc.exe | 12.229.155.122:80 | — | AT&T Services, Inc. | US | malicious |
2764 | serialfunc.exe | 59.110.18.236:443 | — | Hangzhou Alibaba Advertising Co.,Ltd. | CN | malicious |
2764 | serialfunc.exe | 108.179.206.219:8080 | — | CyrusOne LLC | US | malicious |
2764 | serialfunc.exe | 45.56.88.91:443 | — | Linode, LLC | US | malicious |
4000 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2372 | iexplore.exe | 103.117.180.4:443 | timestampindia.com | — | — | suspicious |
2764 | serialfunc.exe | 108.191.2.72:80 | — | BRIGHT HOUSE NETWORKS, LLC | US | malicious |
2372 | iexplore.exe | 103.117.180.4:80 | timestampindia.com | — | — | suspicious |
2764 | serialfunc.exe | 107.2.2.28:80 | — | Comcast Cable Communications, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
timestampindia.com |
| suspicious |
www.bing.com |
| whitelisted |
rmcentre.bigfilmproduction.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2372 | iexplore.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
2372 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2372 | iexplore.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2372 | iexplore.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
2372 | iexplore.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
2372 | iexplore.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2372 | iexplore.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
2764 | serialfunc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 2 |
2764 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
2764 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |