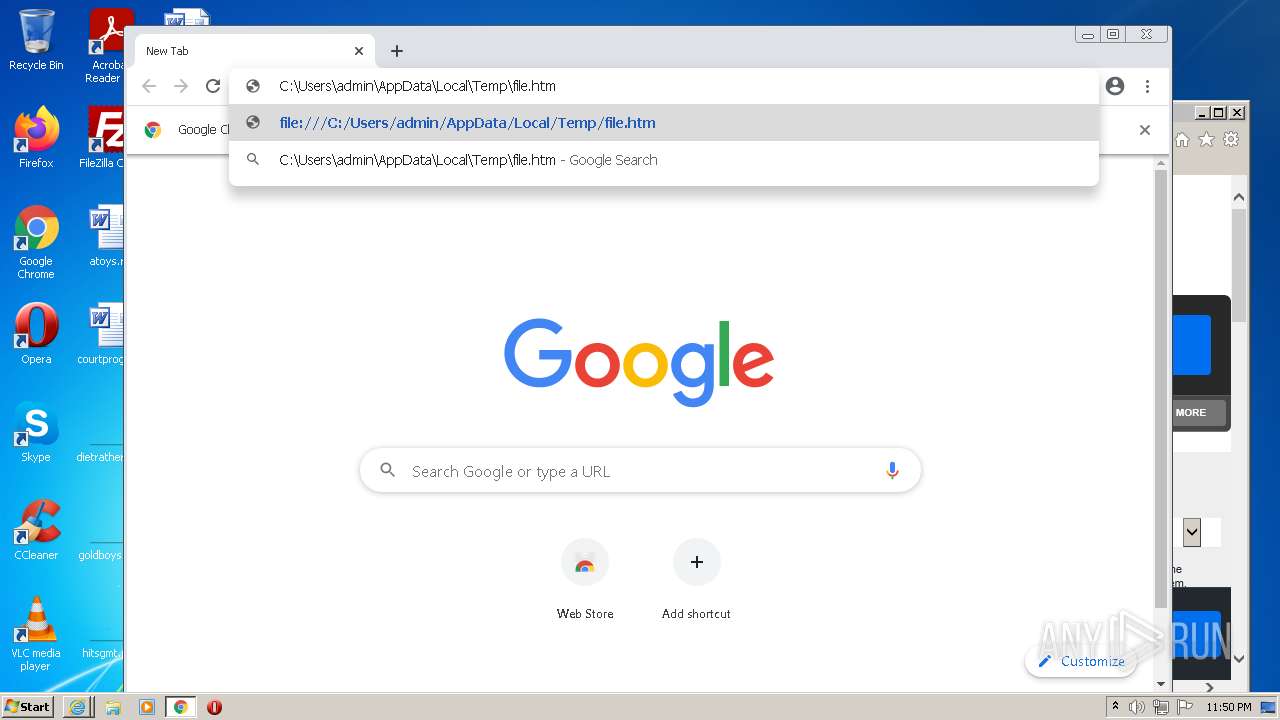
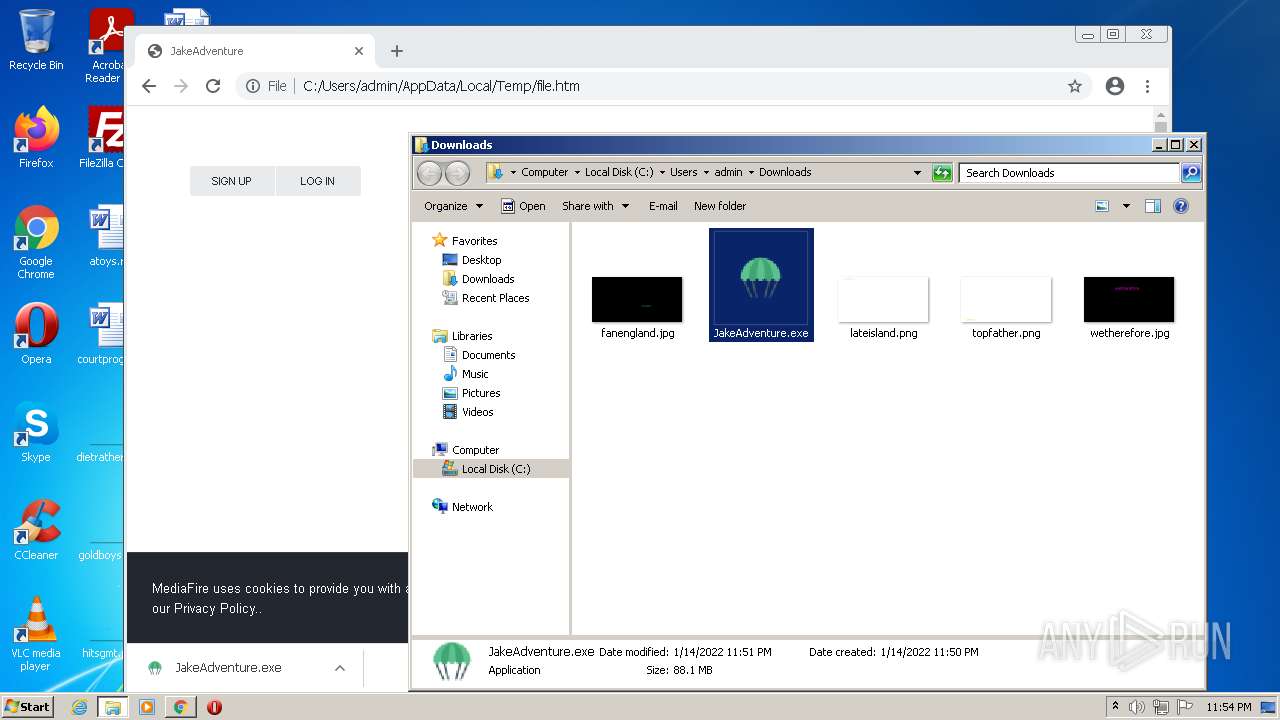
| download: | file |
| Full analysis: | https://app.any.run/tasks/e969010c-27ad-4061-8db1-28b7c490d8b7 |
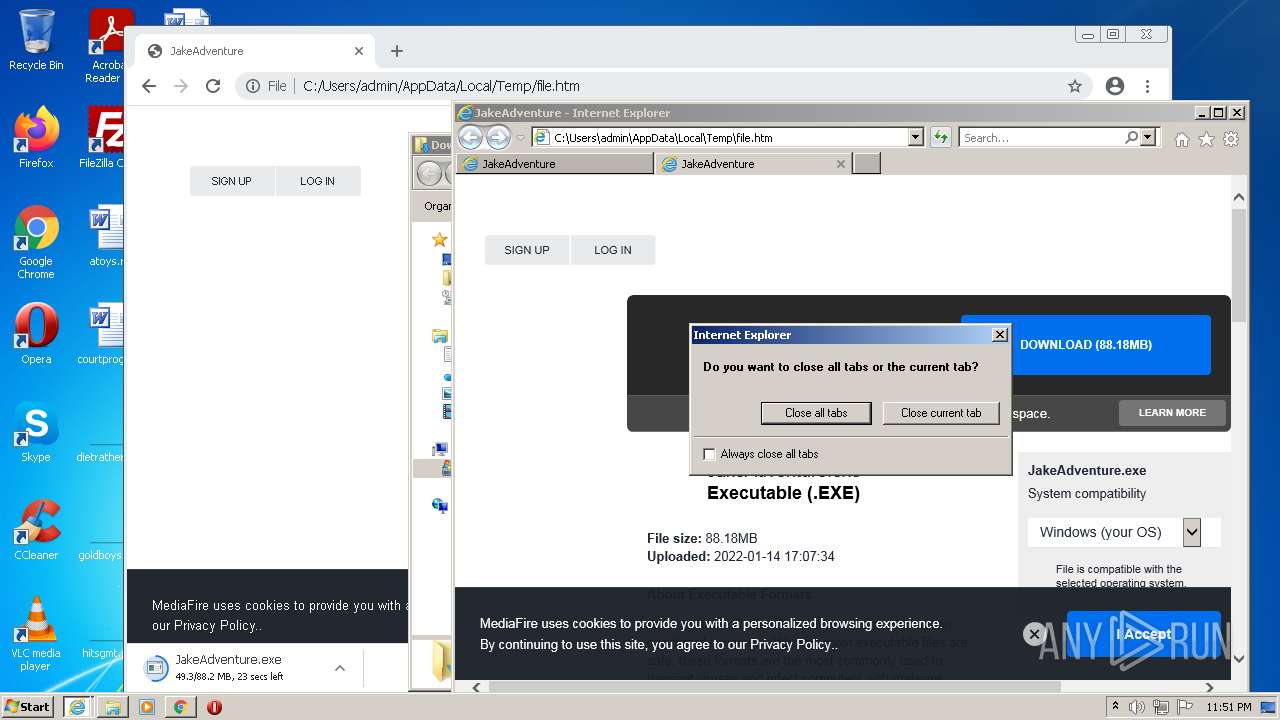
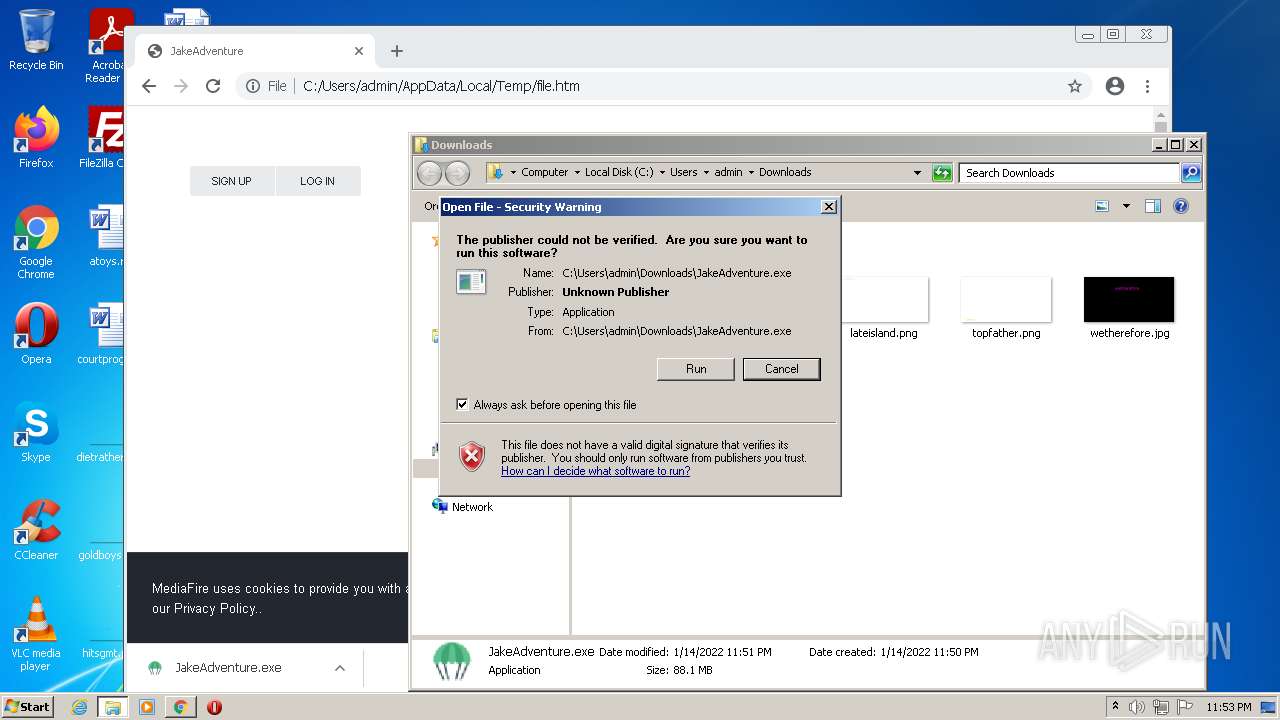
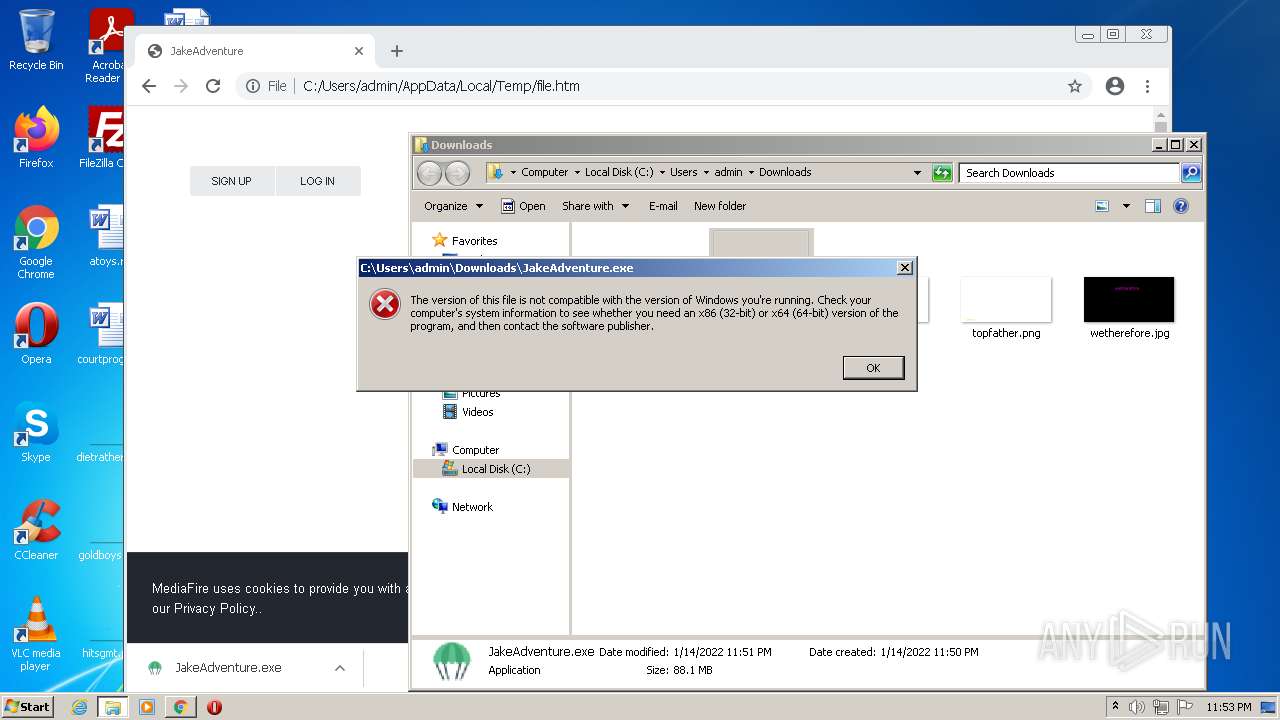
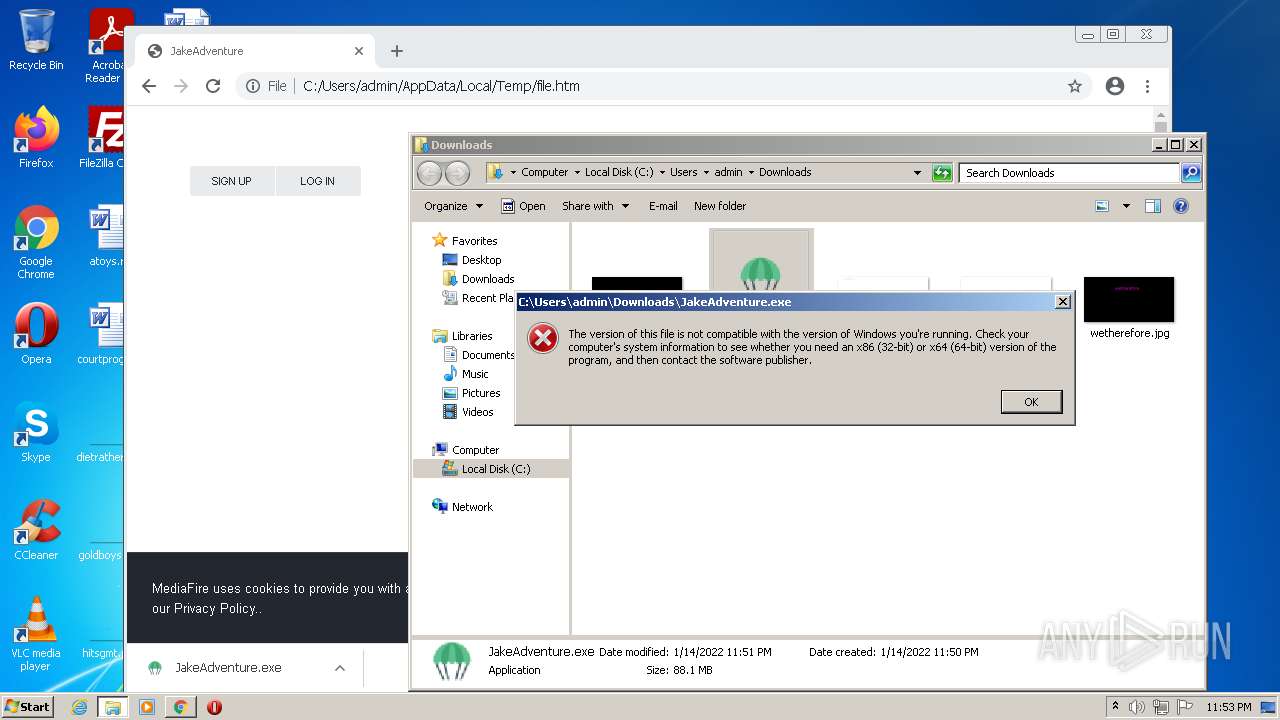
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2022, 23:49:46 |
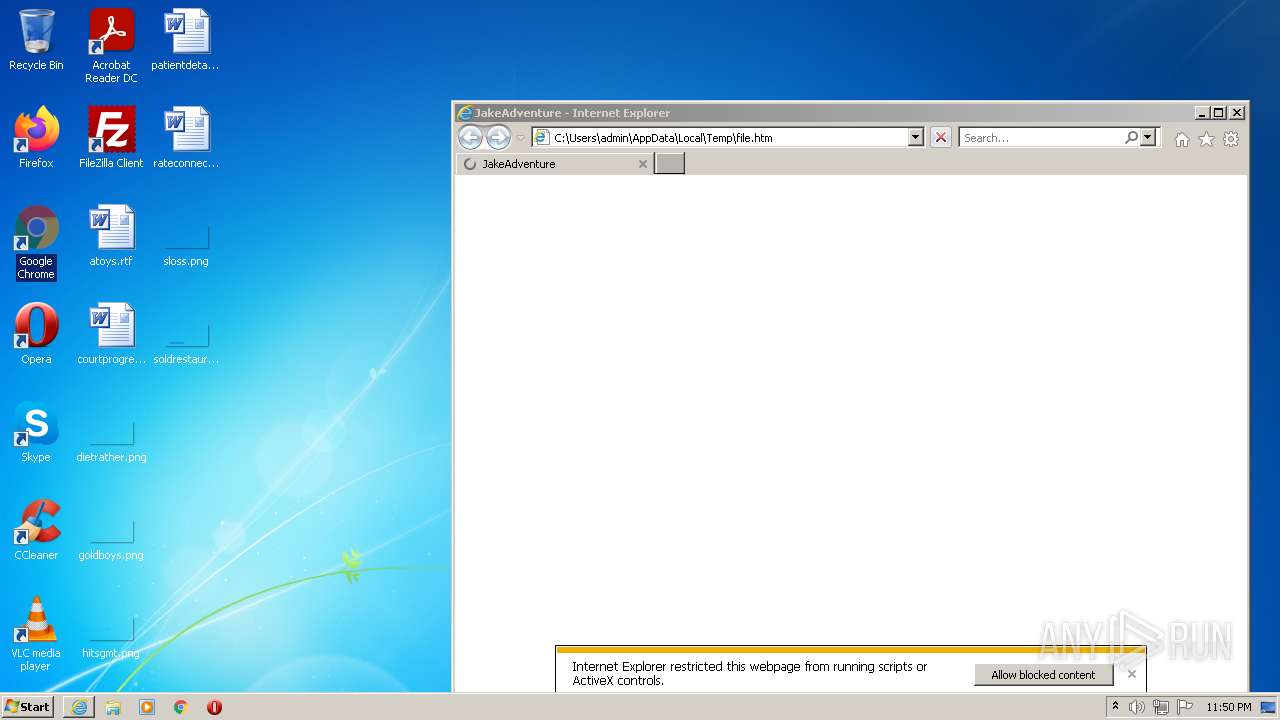
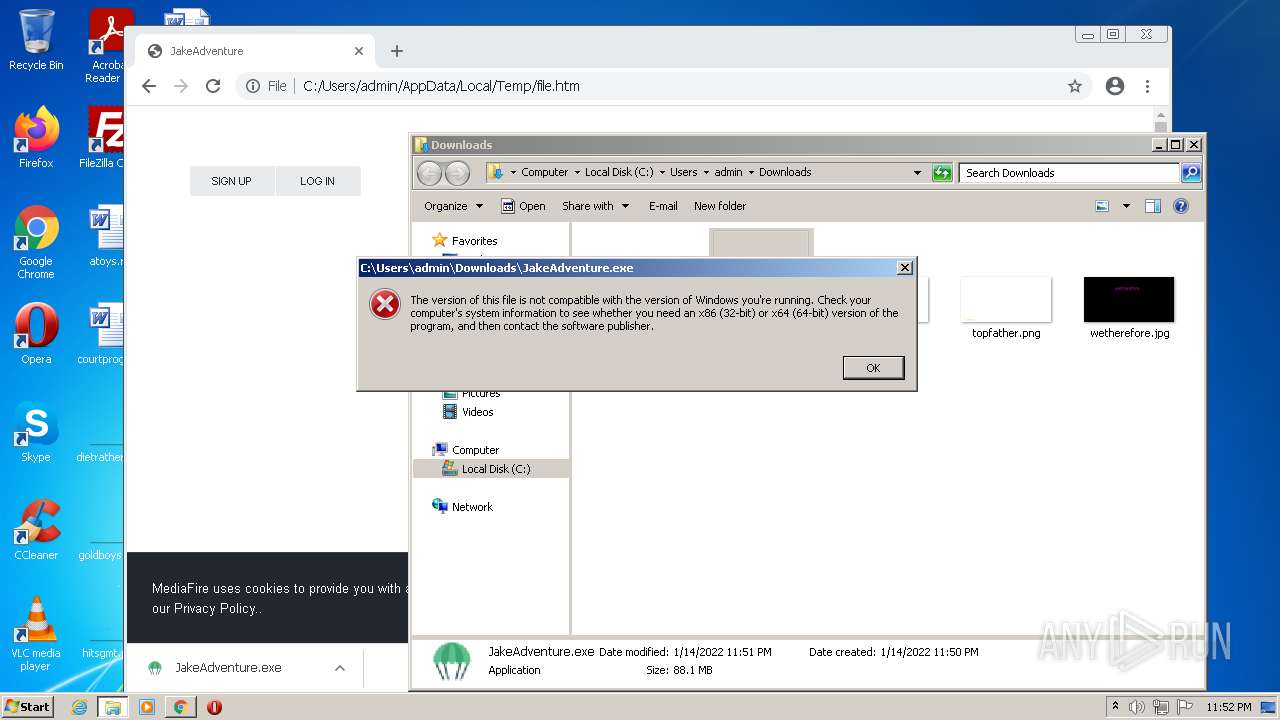
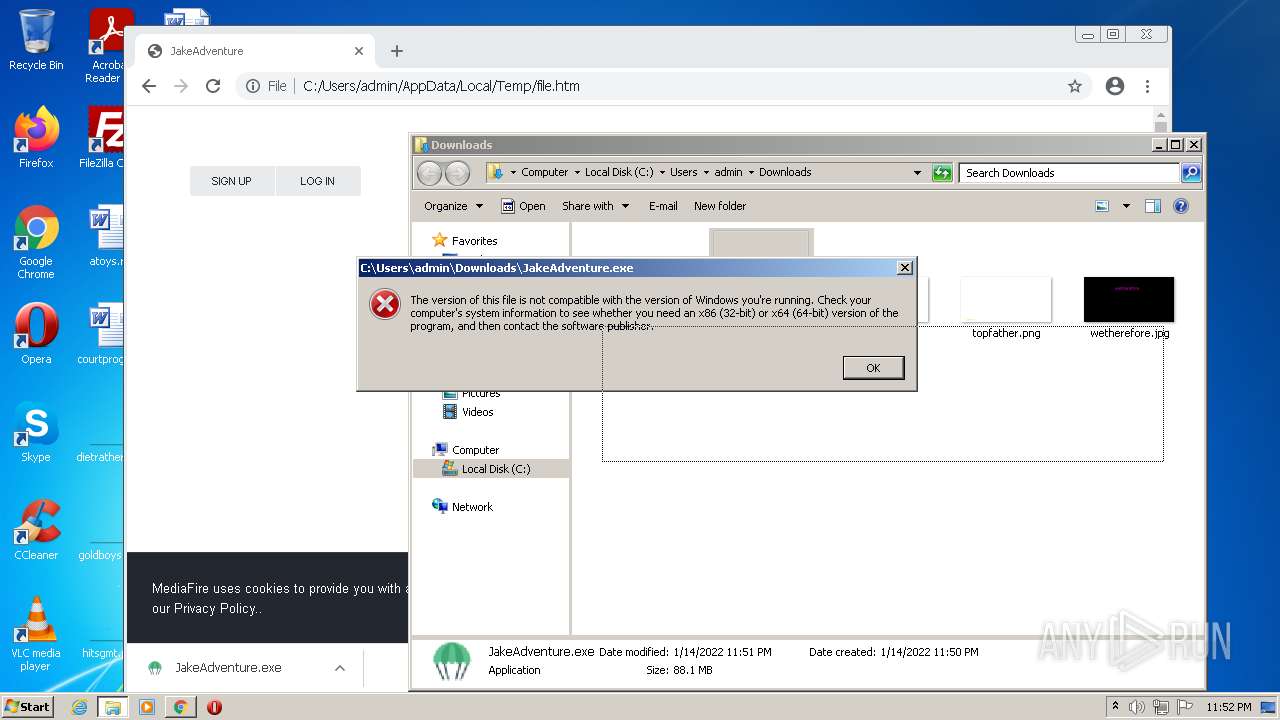
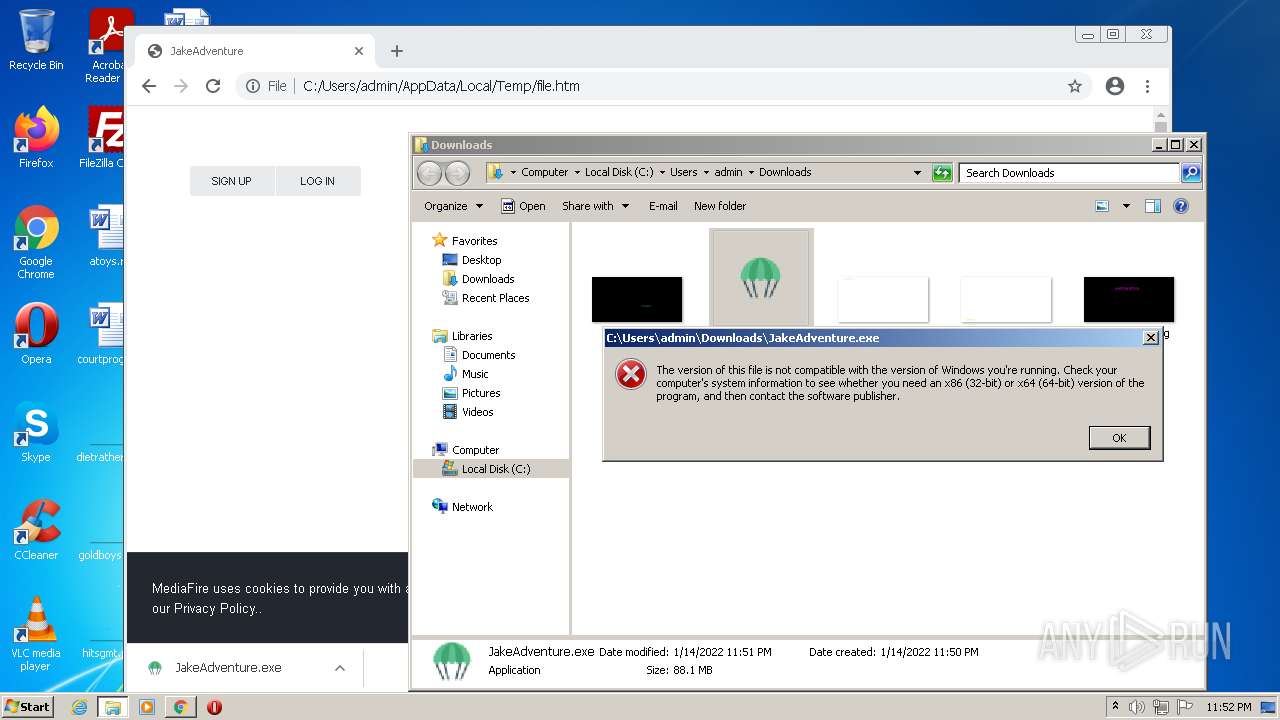
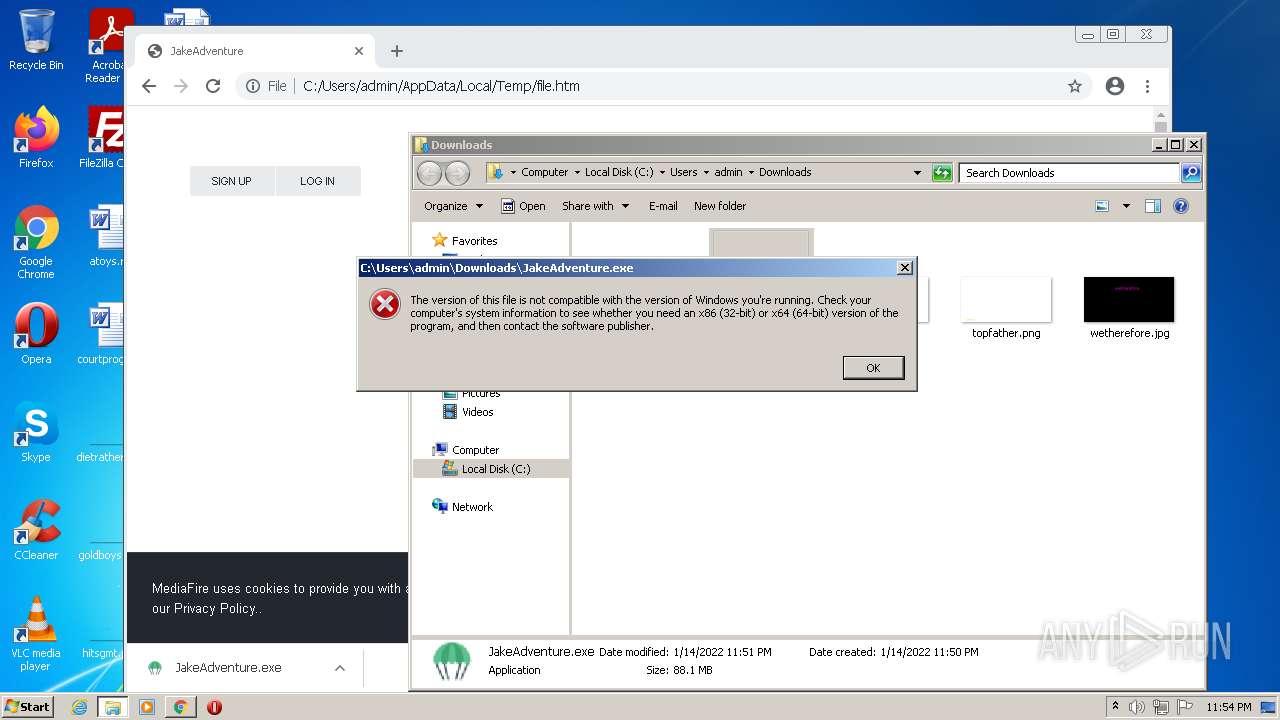
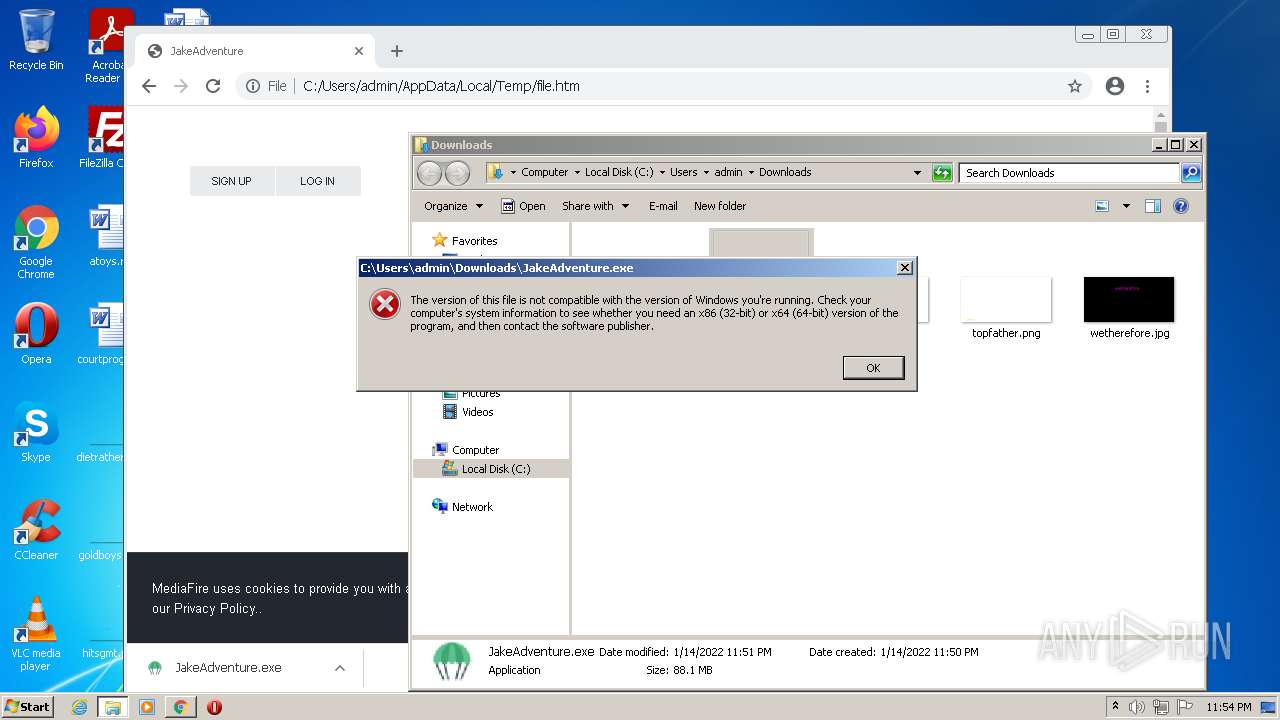
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 94105596910ABC6C746E6CE034583685 |
| SHA1: | 3A2CE2E52944FBADE241EABC2C0AF73F106607A8 |
| SHA256: | 21A76C24ABA2273BB7640351B6B846ECBC510B68754366DD4B40FC109871B7A8 |
| SSDEEP: | 3072:Bi2gAkHnjPhQ6KScOq4oNF5Hw0HilQaW+LN7vxRLlzglKhtTS:bgAkHnjPhQBScOqv9lyQCN7vBht+ |
MALICIOUS
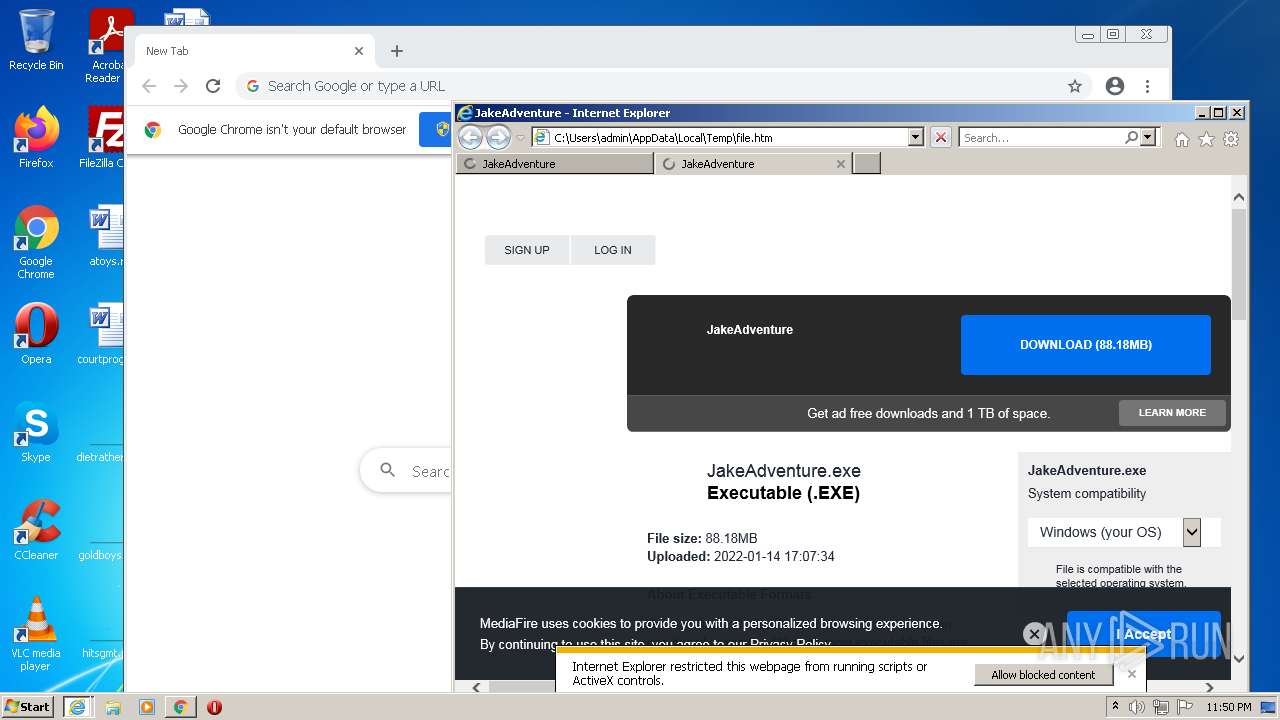
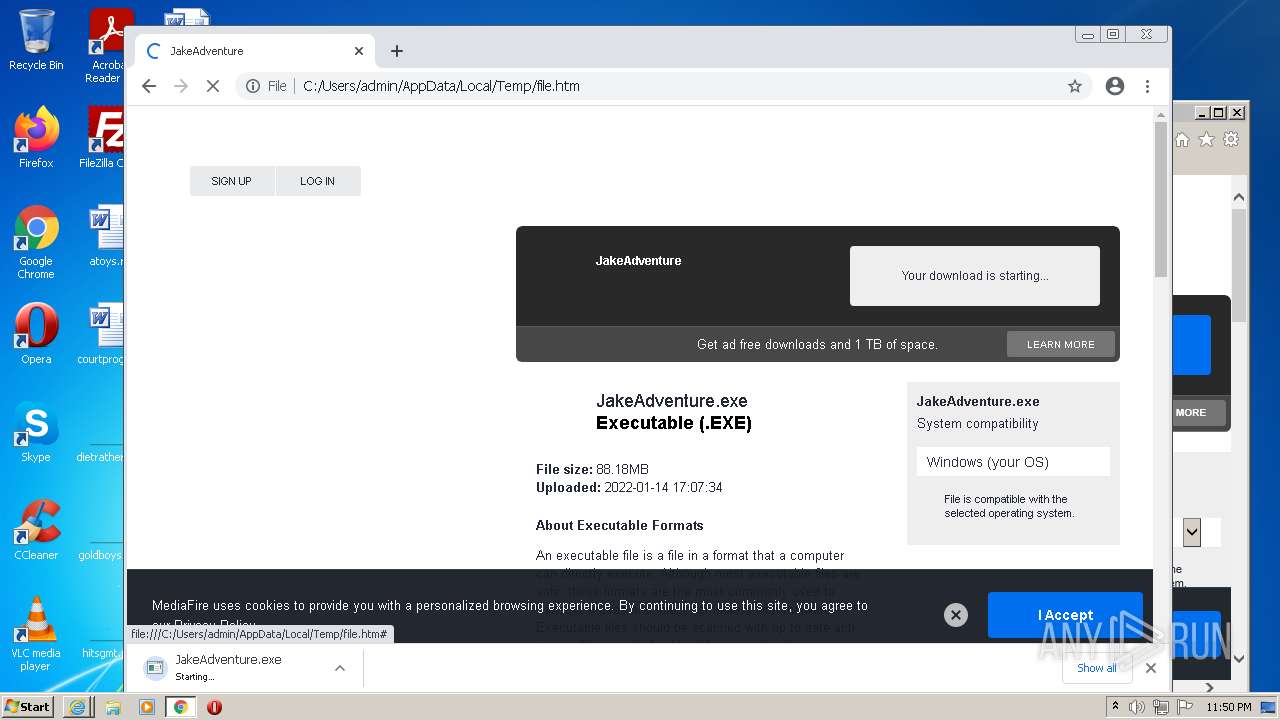
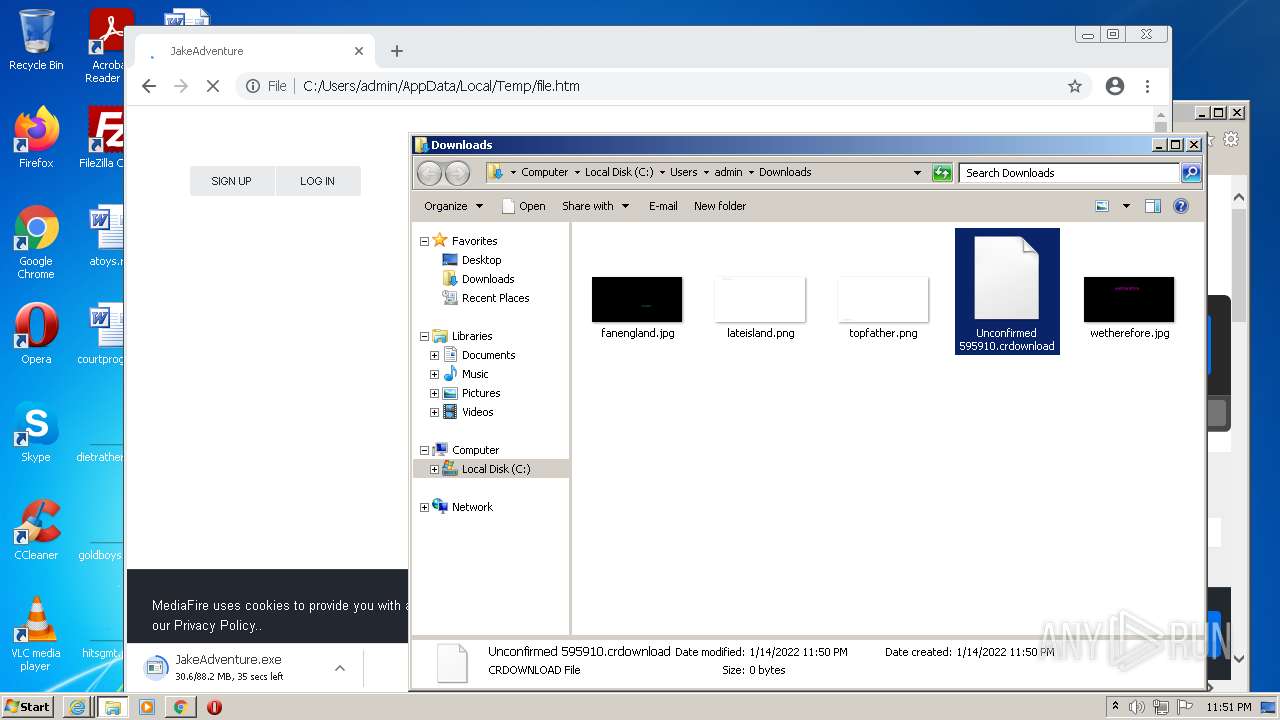
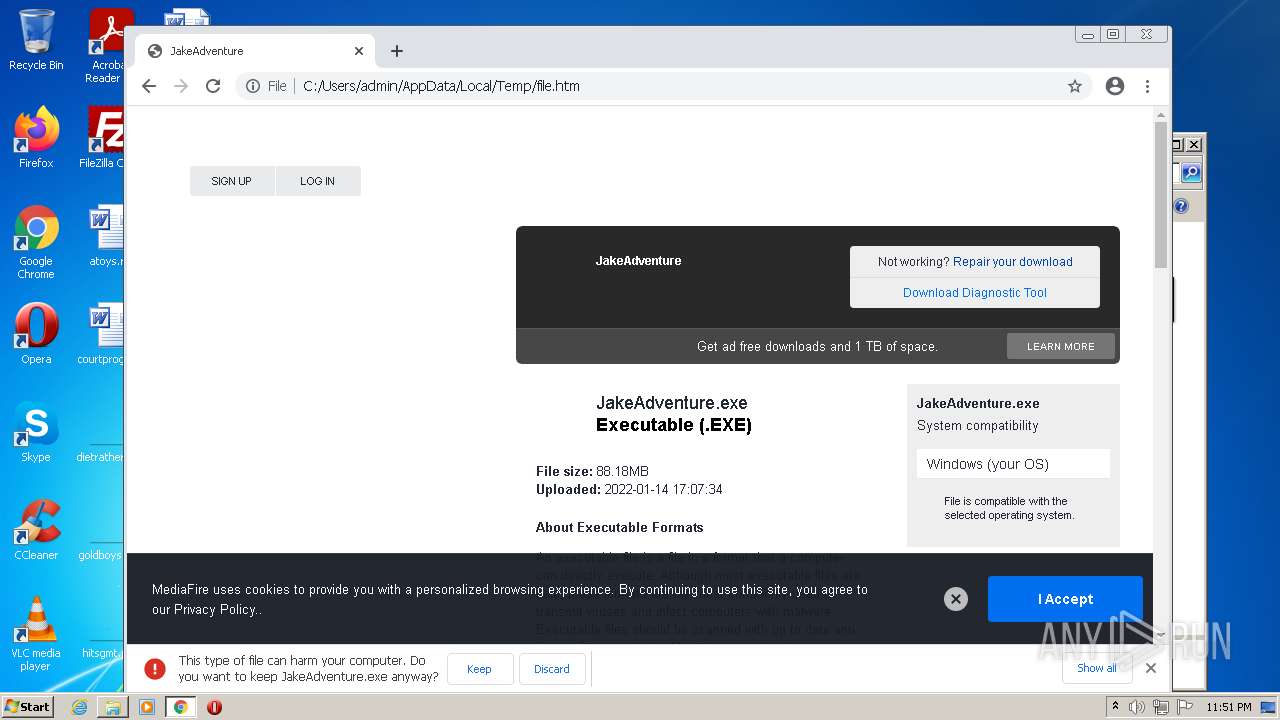
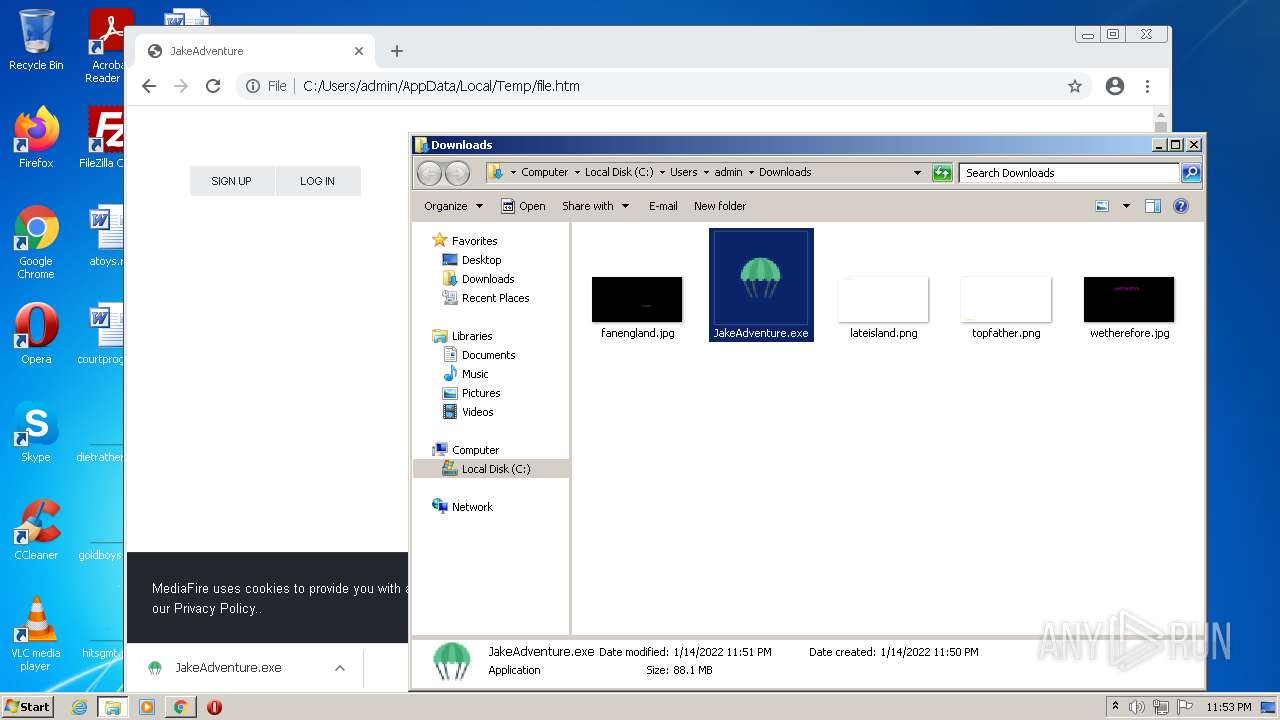
Drops executable file immediately after starts
- chrome.exe (PID: 2464)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3176)
- iexplore.exe (PID: 3752)
Executable content was dropped or overwritten
- chrome.exe (PID: 2464)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2464)
INFO
Reads the computer name
- iexplore.exe (PID: 1324)
- iexplore.exe (PID: 3176)
- chrome.exe (PID: 3896)
- chrome.exe (PID: 1652)
- iexplore.exe (PID: 2460)
- chrome.exe (PID: 1612)
- iexplore.exe (PID: 3752)
- chrome.exe (PID: 1444)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 1800)
- chrome.exe (PID: 3352)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 688)
- chrome.exe (PID: 3588)
- chrome.exe (PID: 3388)
Application launched itself
- iexplore.exe (PID: 1324)
- chrome.exe (PID: 3896)
- iexplore.exe (PID: 3176)
Checks supported languages
- iexplore.exe (PID: 1324)
- iexplore.exe (PID: 3176)
- chrome.exe (PID: 3896)
- chrome.exe (PID: 2852)
- chrome.exe (PID: 1652)
- chrome.exe (PID: 1612)
- chrome.exe (PID: 2184)
- chrome.exe (PID: 1708)
- iexplore.exe (PID: 3752)
- chrome.exe (PID: 2624)
- chrome.exe (PID: 1444)
- iexplore.exe (PID: 2460)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 2176)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 2952)
- chrome.exe (PID: 3352)
- chrome.exe (PID: 1800)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 1272)
- chrome.exe (PID: 2268)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 688)
- chrome.exe (PID: 3588)
- chrome.exe (PID: 628)
- chrome.exe (PID: 292)
- chrome.exe (PID: 3388)
- chrome.exe (PID: 2144)
- chrome.exe (PID: 2496)
- chrome.exe (PID: 1152)
- chrome.exe (PID: 3452)
- chrome.exe (PID: 2464)
- chrome.exe (PID: 492)
- chrome.exe (PID: 2392)
- chrome.exe (PID: 2204)
- chrome.exe (PID: 1128)
- chrome.exe (PID: 748)
- chrome.exe (PID: 3112)
Changes internet zones settings
- iexplore.exe (PID: 1324)
Reads settings of System Certificates
- iexplore.exe (PID: 3176)
- iexplore.exe (PID: 1324)
- chrome.exe (PID: 1612)
- iexplore.exe (PID: 3752)
Checks Windows Trust Settings
- iexplore.exe (PID: 3176)
- iexplore.exe (PID: 1324)
- iexplore.exe (PID: 3752)
- chrome.exe (PID: 3896)
Changes settings of System certificates
- iexplore.exe (PID: 3176)
- iexplore.exe (PID: 3752)
- iexplore.exe (PID: 1324)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3176)
- iexplore.exe (PID: 3752)
- iexplore.exe (PID: 1324)
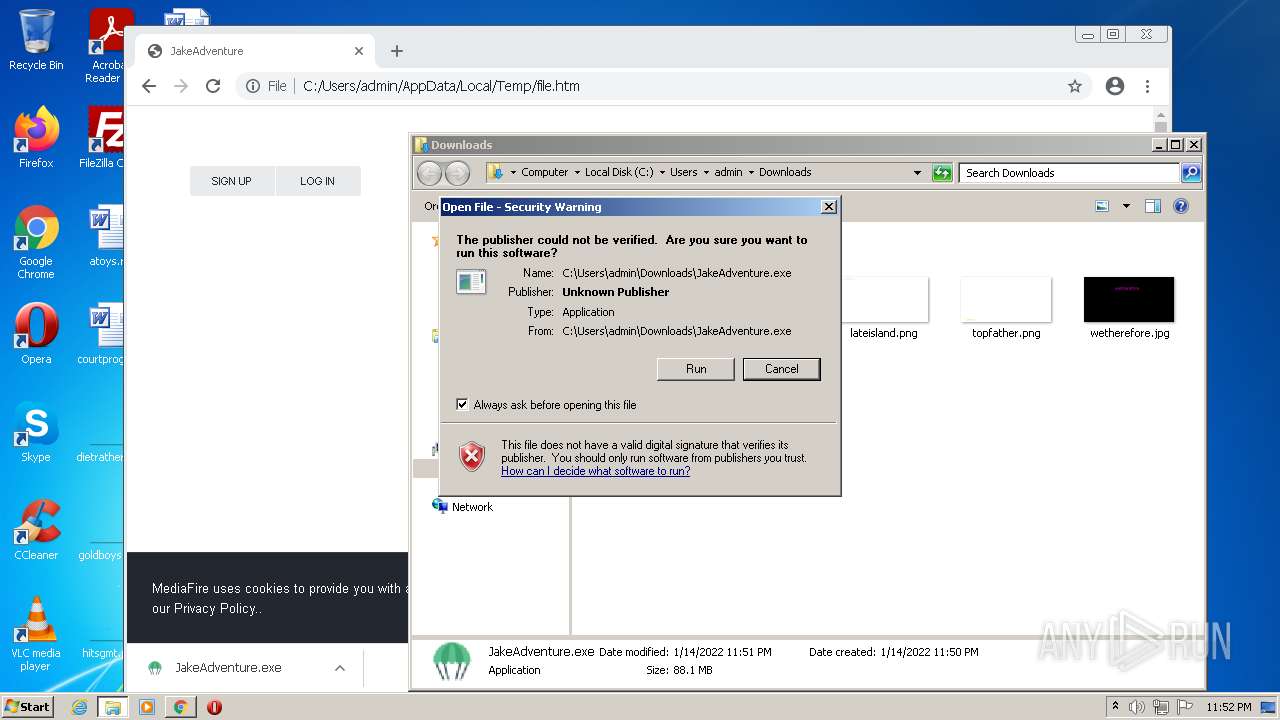
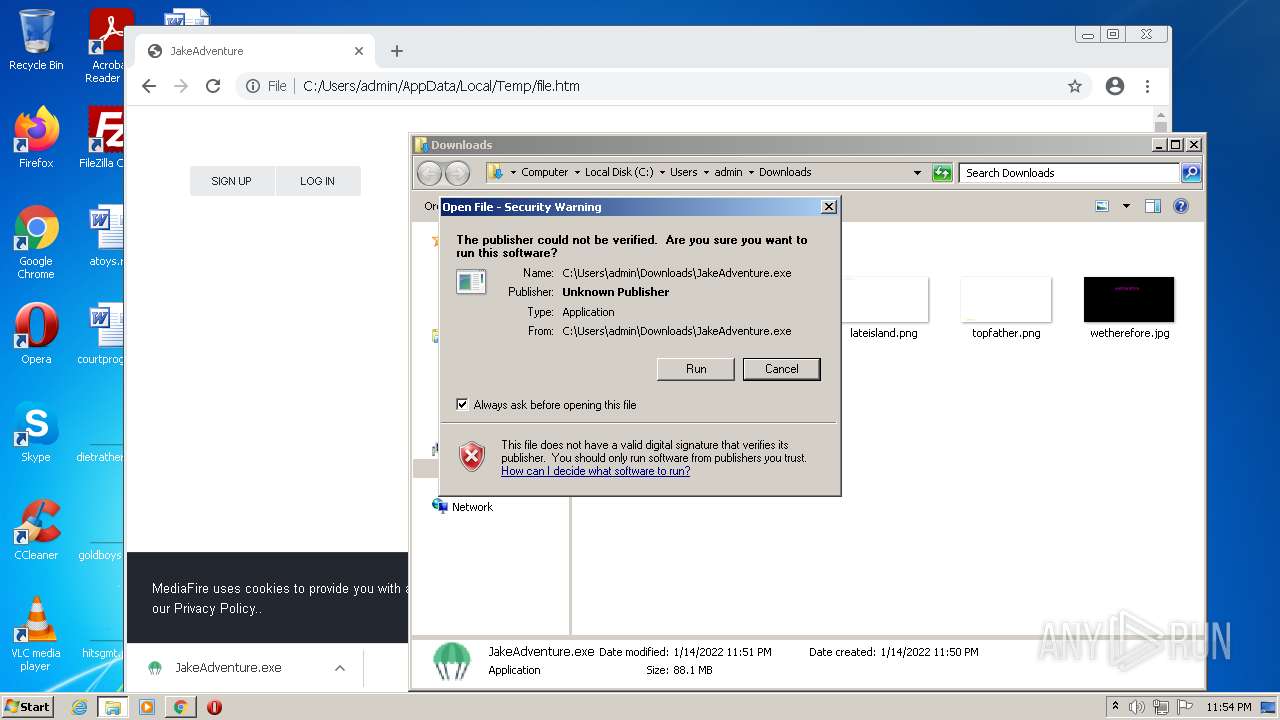
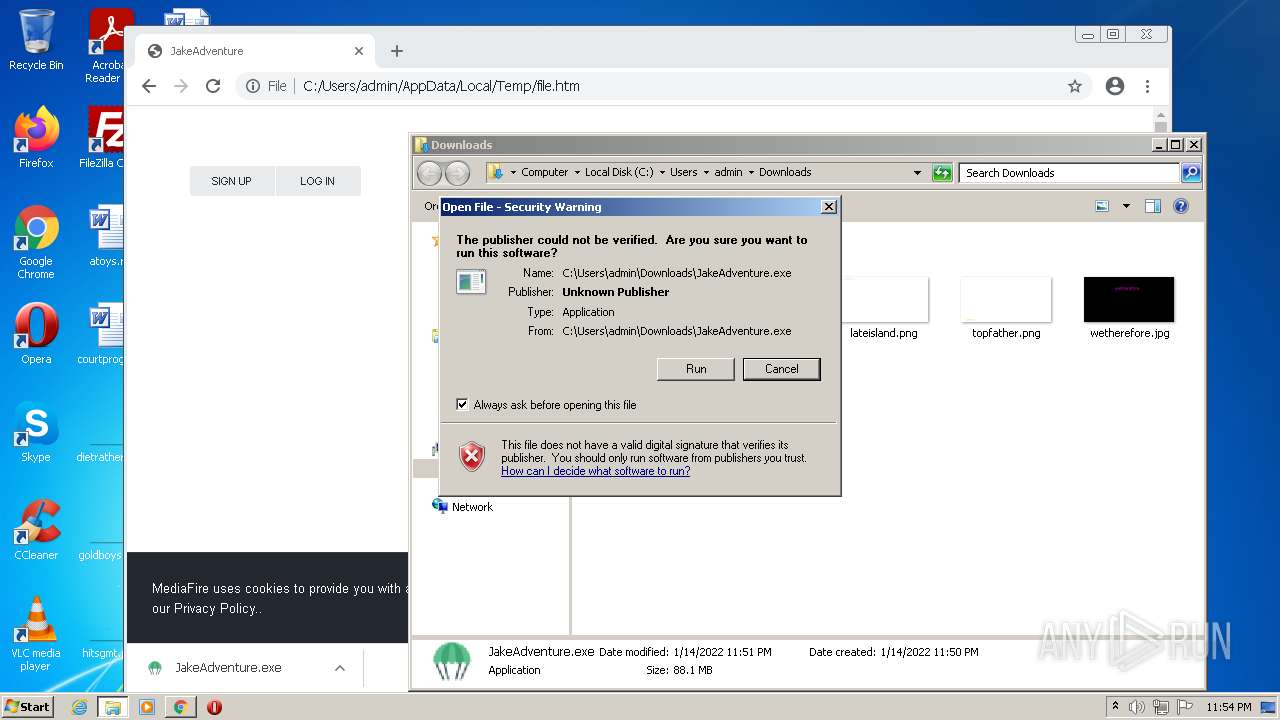
Manual execution by user
- chrome.exe (PID: 3896)
Reads the hosts file
- chrome.exe (PID: 3896)
- chrome.exe (PID: 1612)
Reads internet explorer settings
- iexplore.exe (PID: 3176)
- iexplore.exe (PID: 3752)
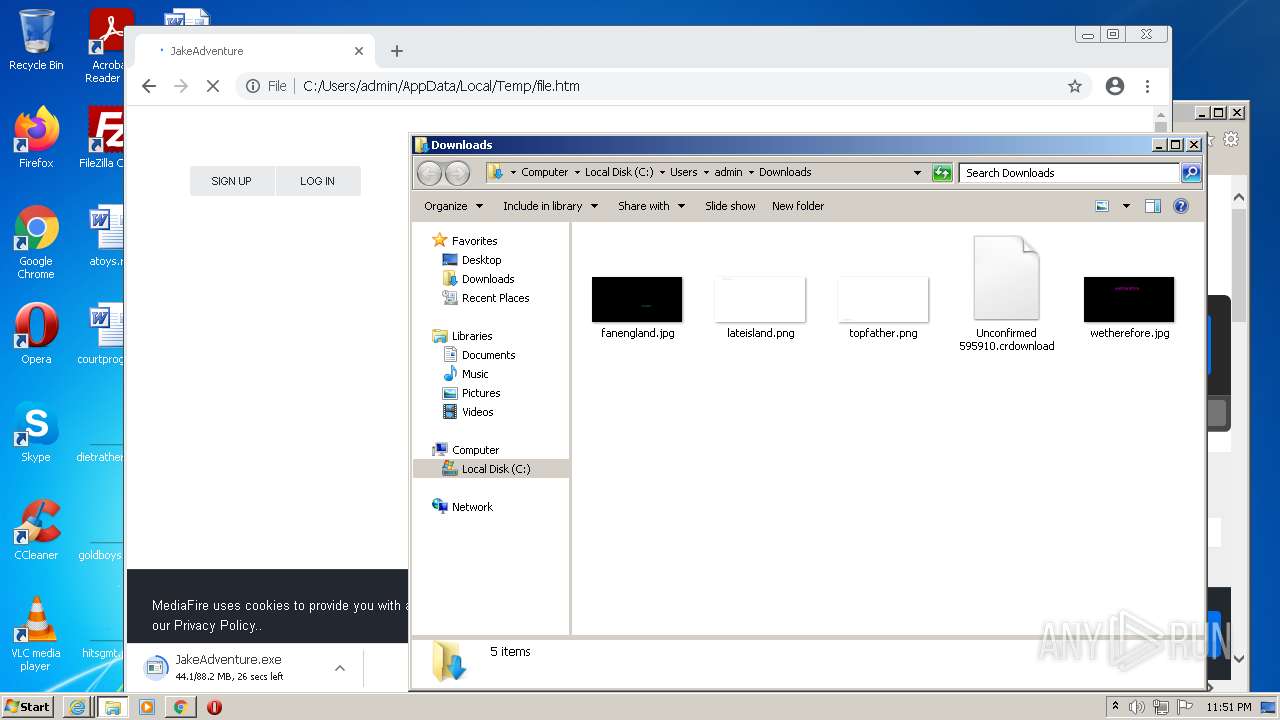
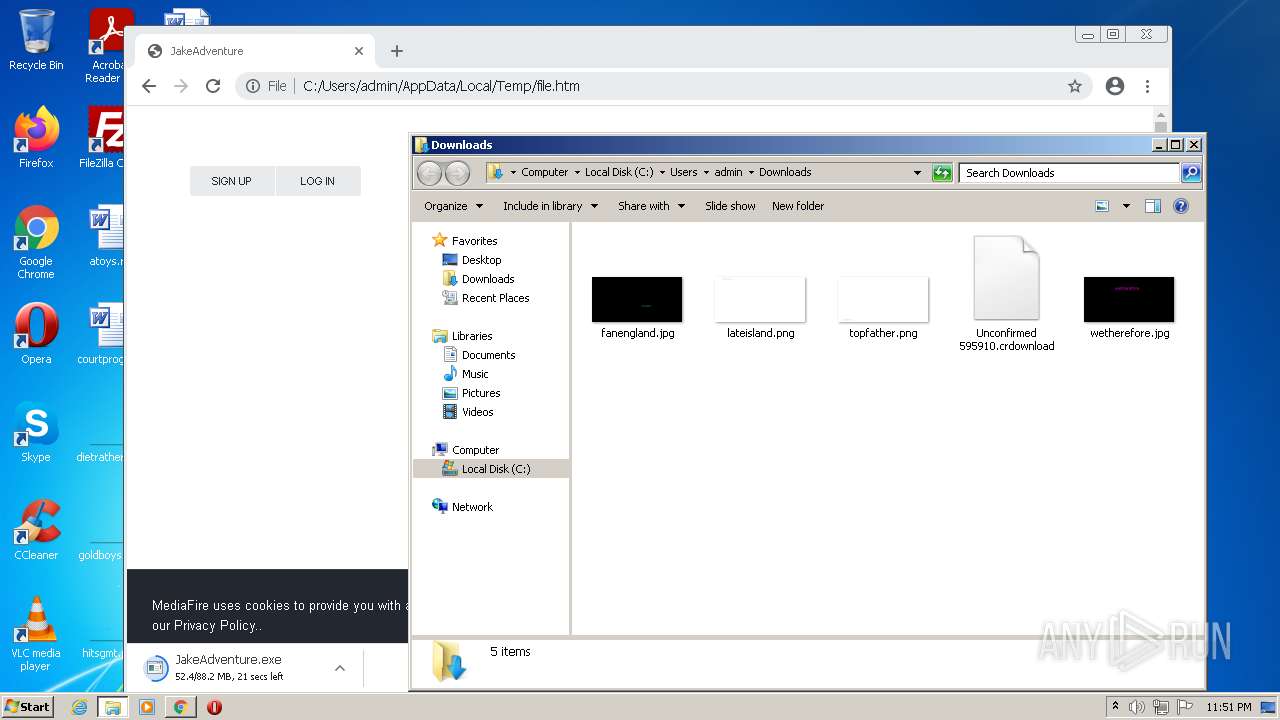
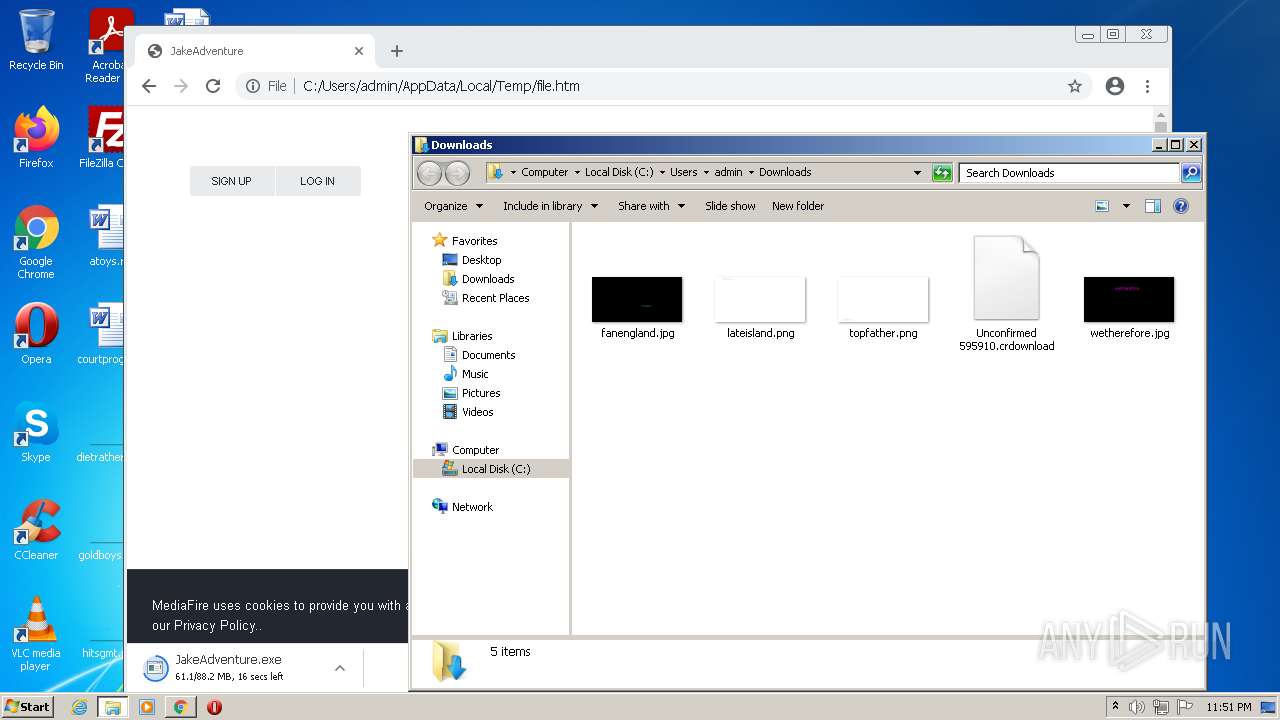
Creates files in the user directory
- iexplore.exe (PID: 3176)
- iexplore.exe (PID: 1324)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1324)
- chrome.exe (PID: 3896)
Reads the date of Windows installation
- chrome.exe (PID: 2616)
- iexplore.exe (PID: 1324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| twitterDescription: | - |
|---|---|
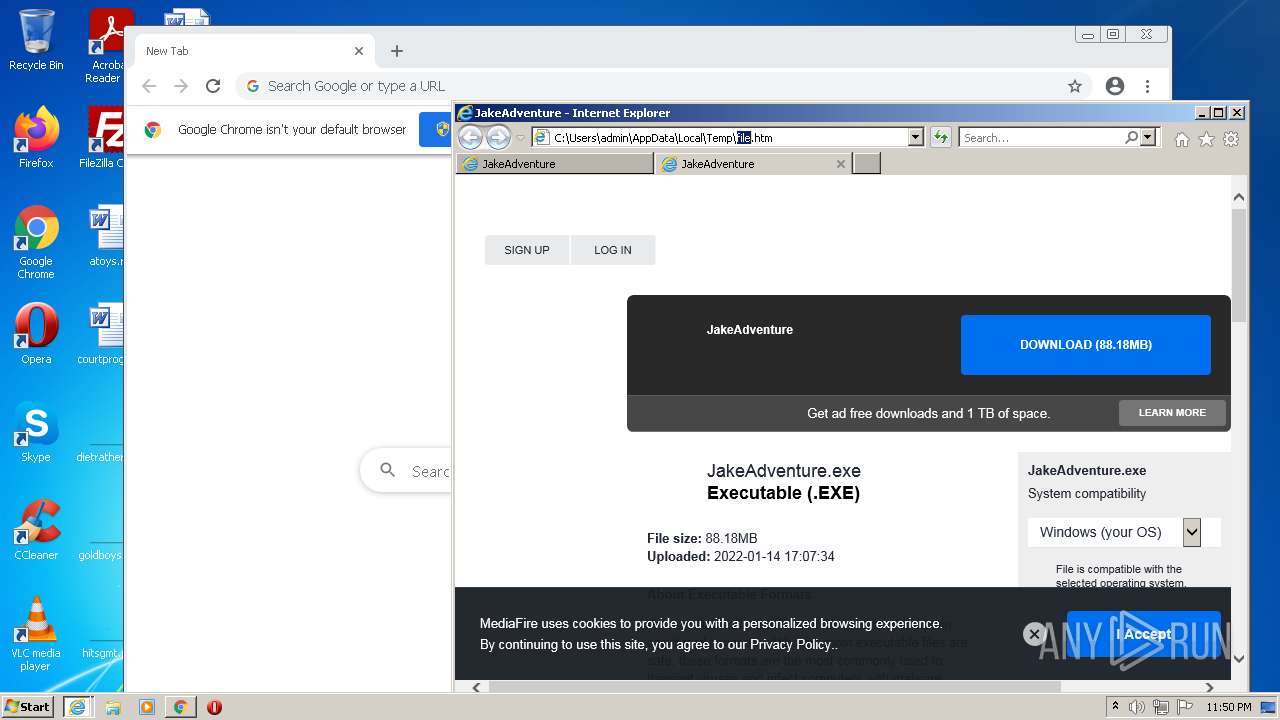
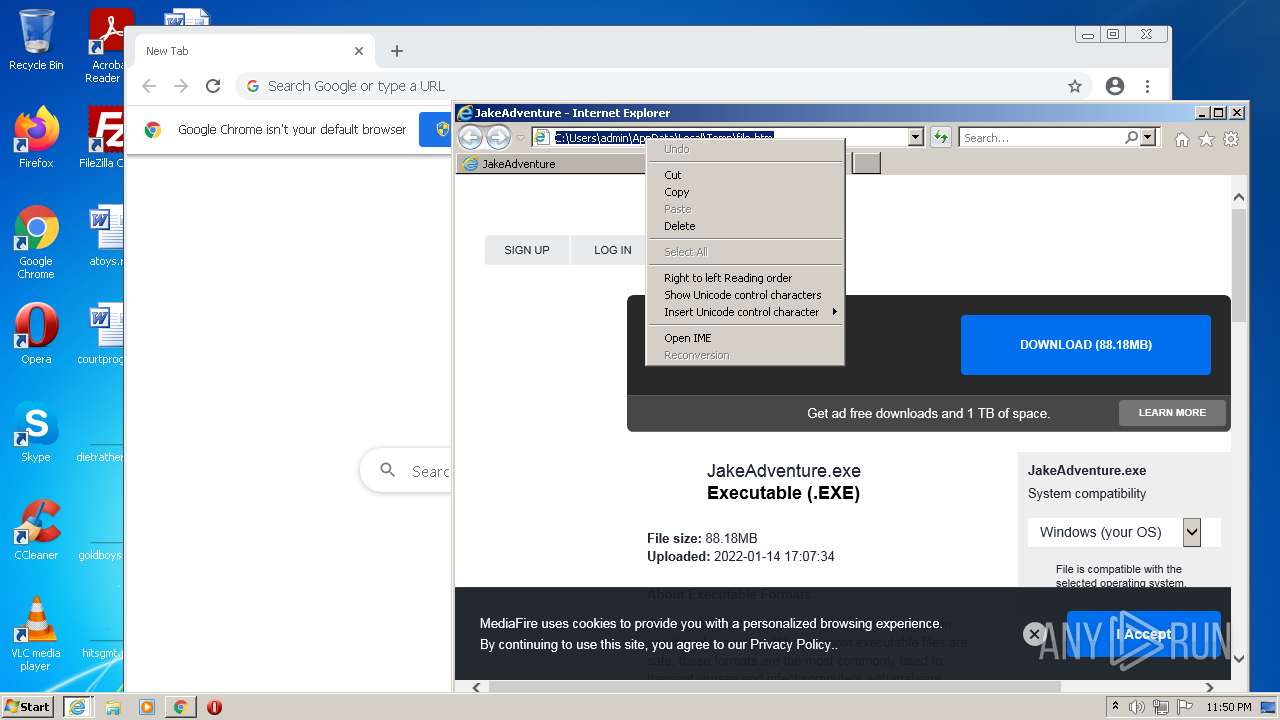
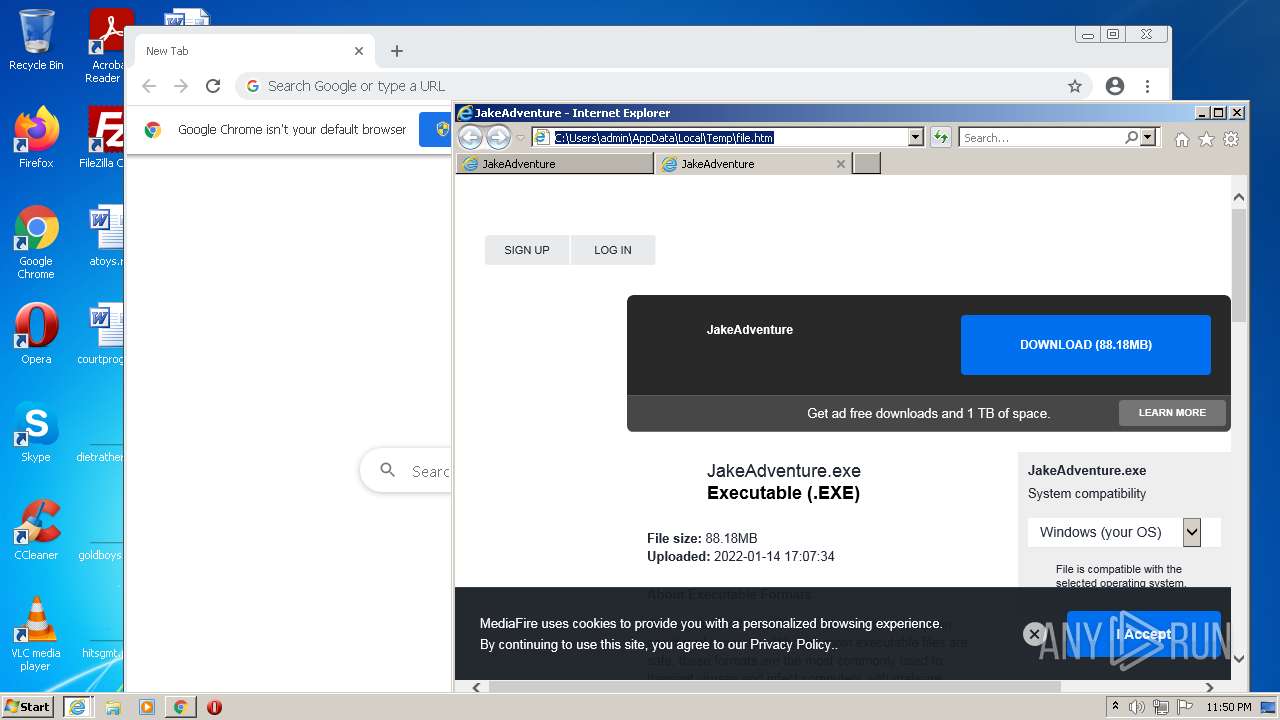
| twitterImage: | https://static.mediafire.com/images/filetype/download/app.jpg |
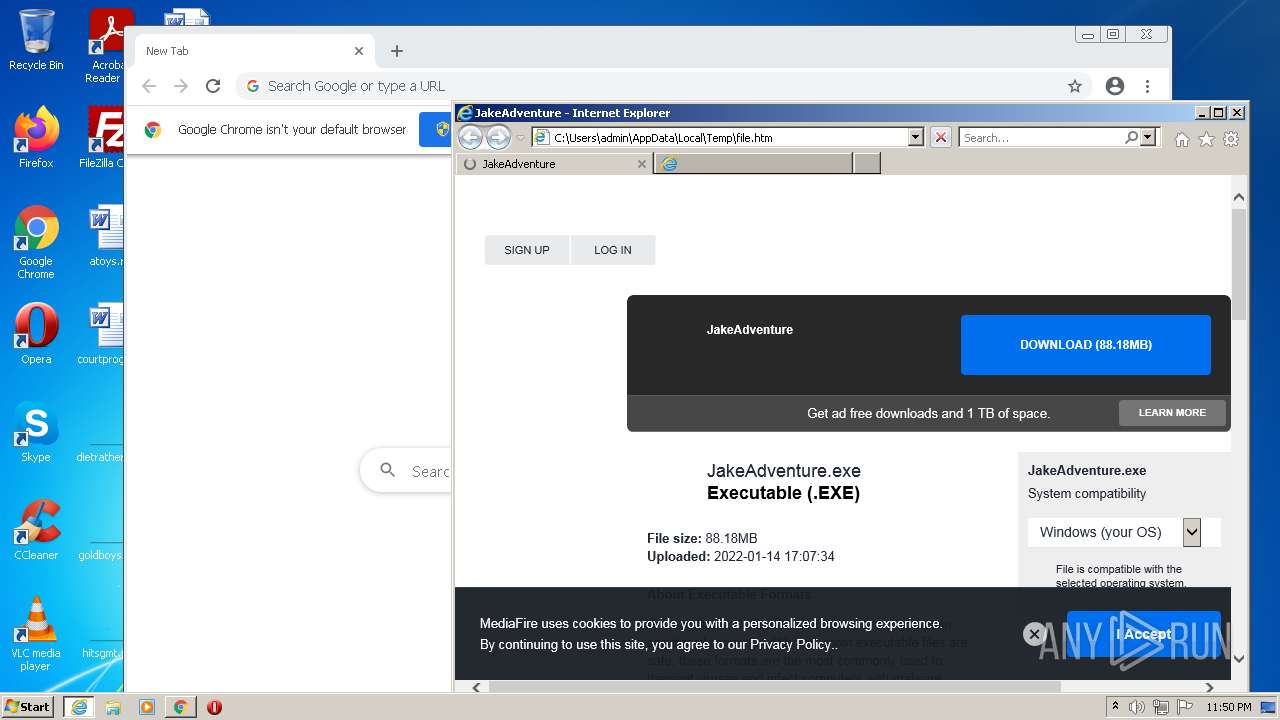
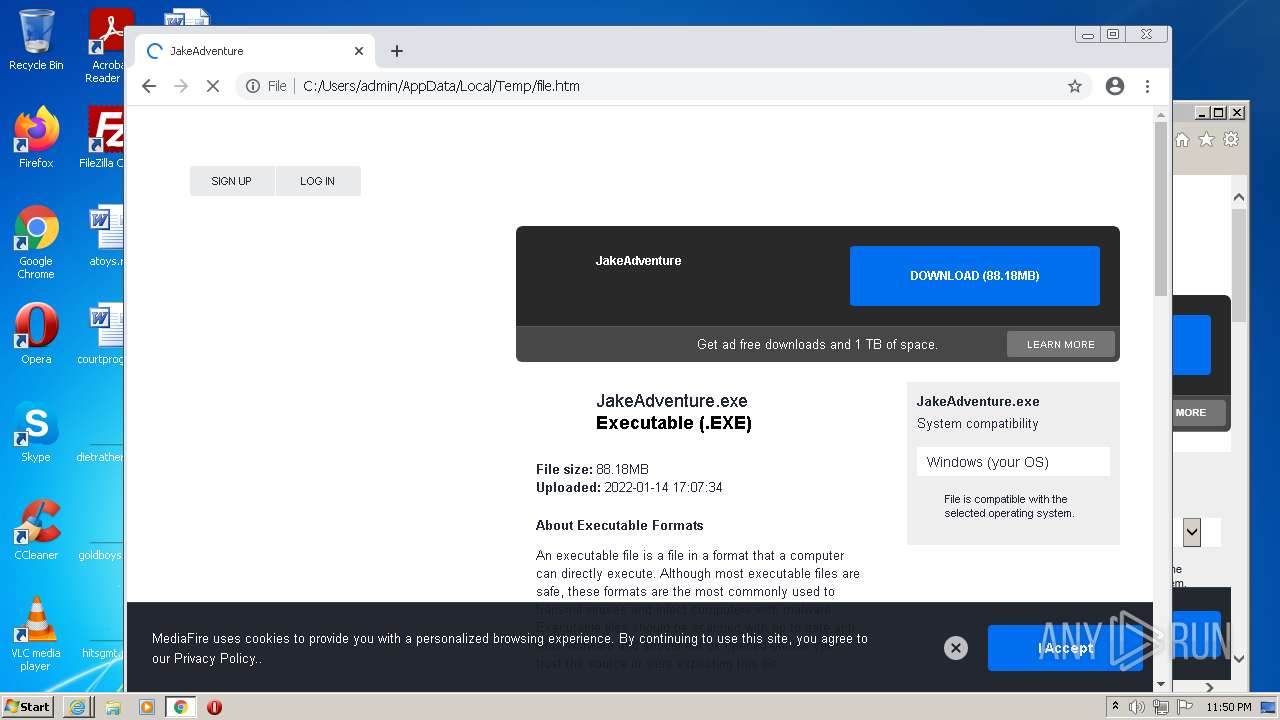
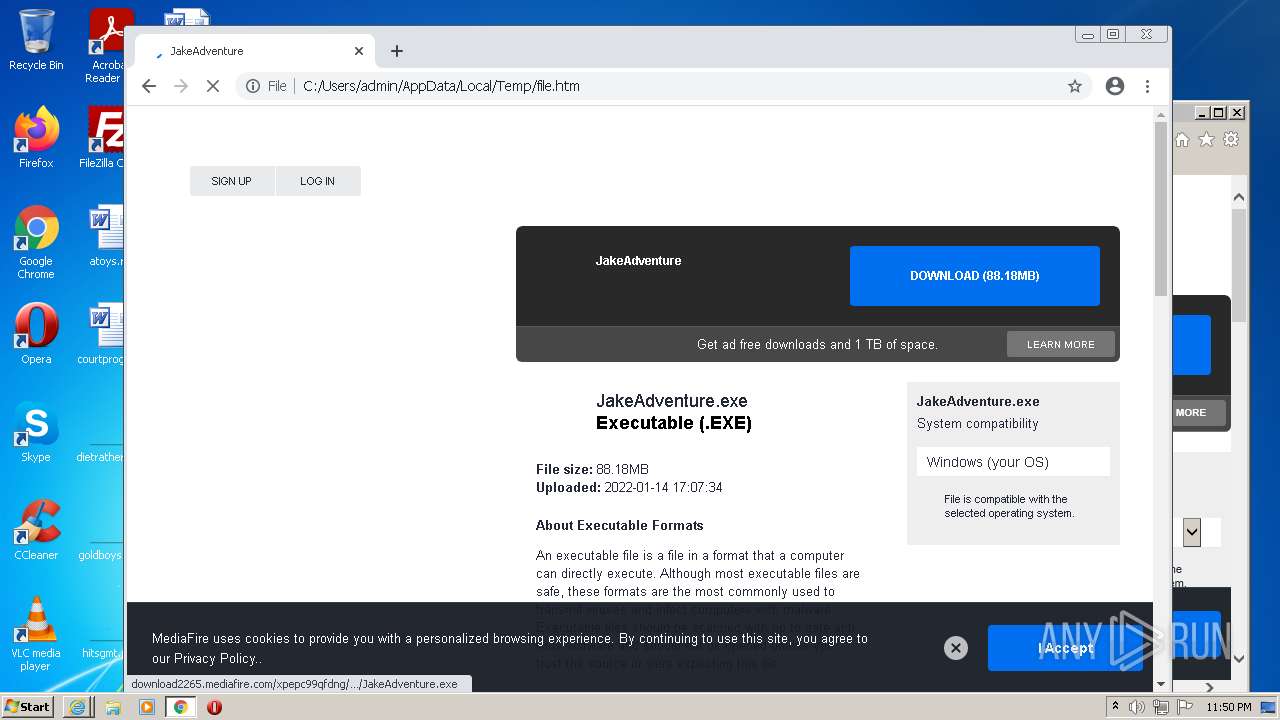
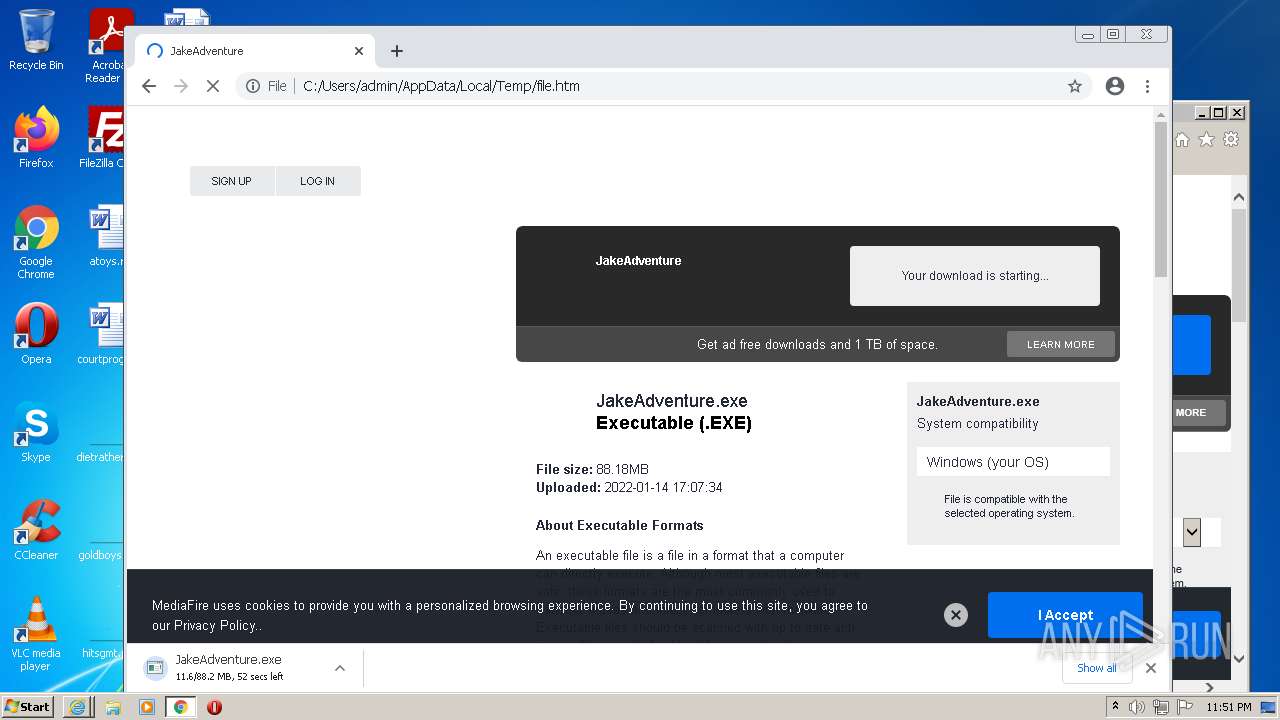
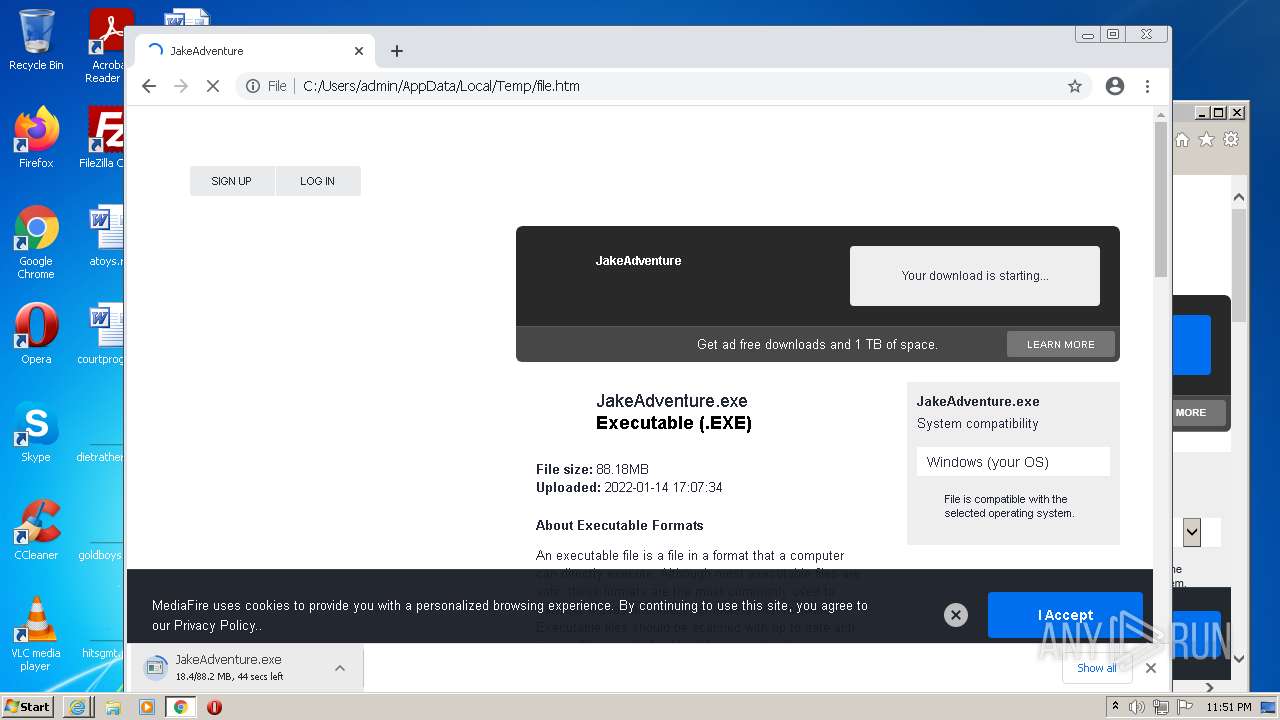
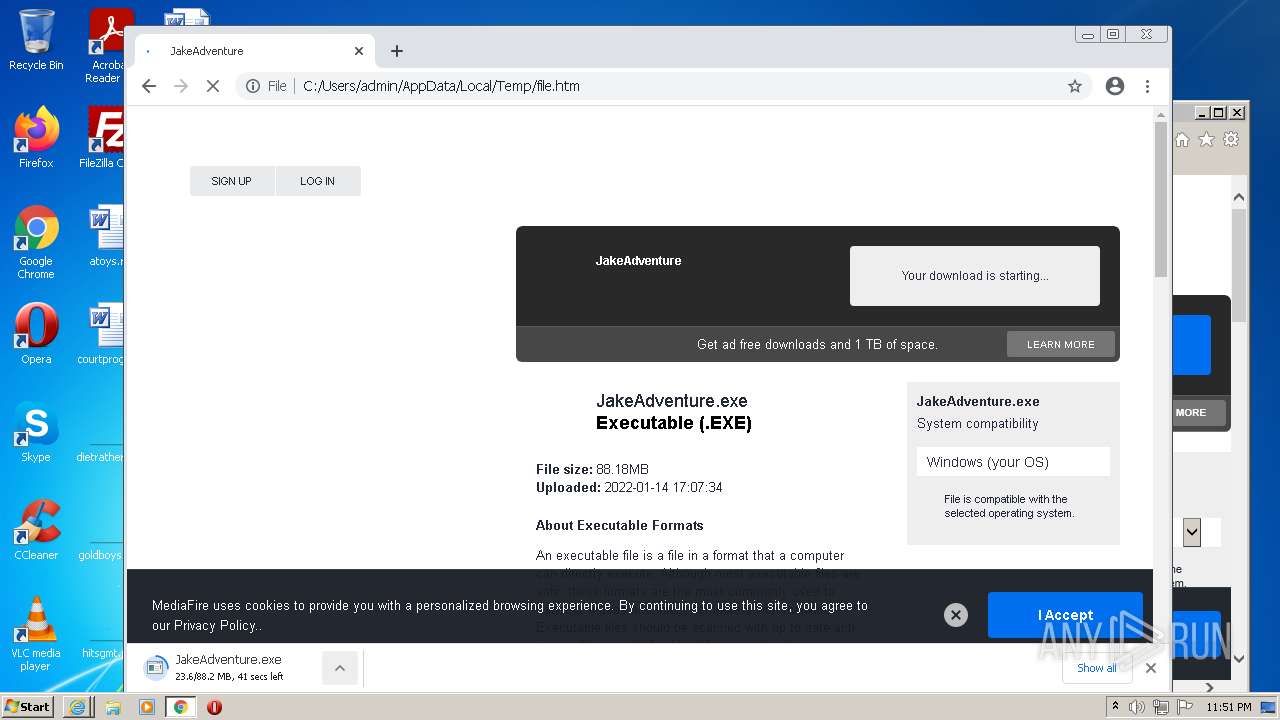
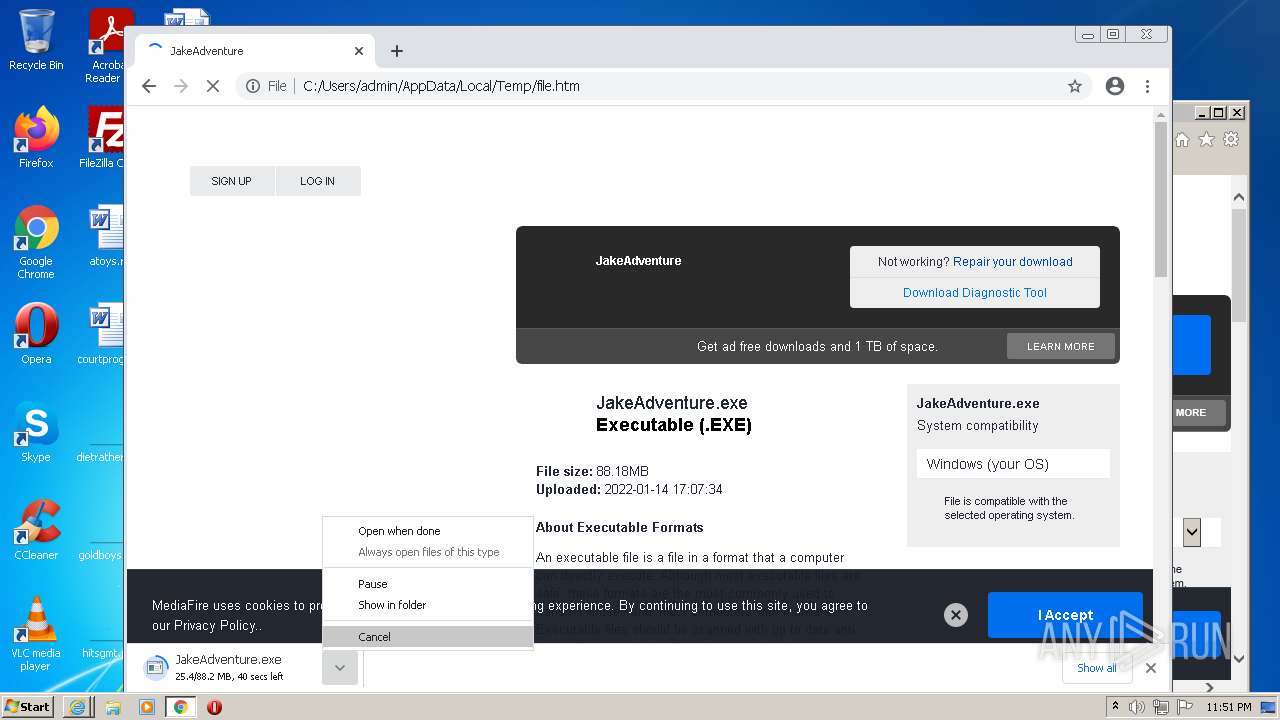
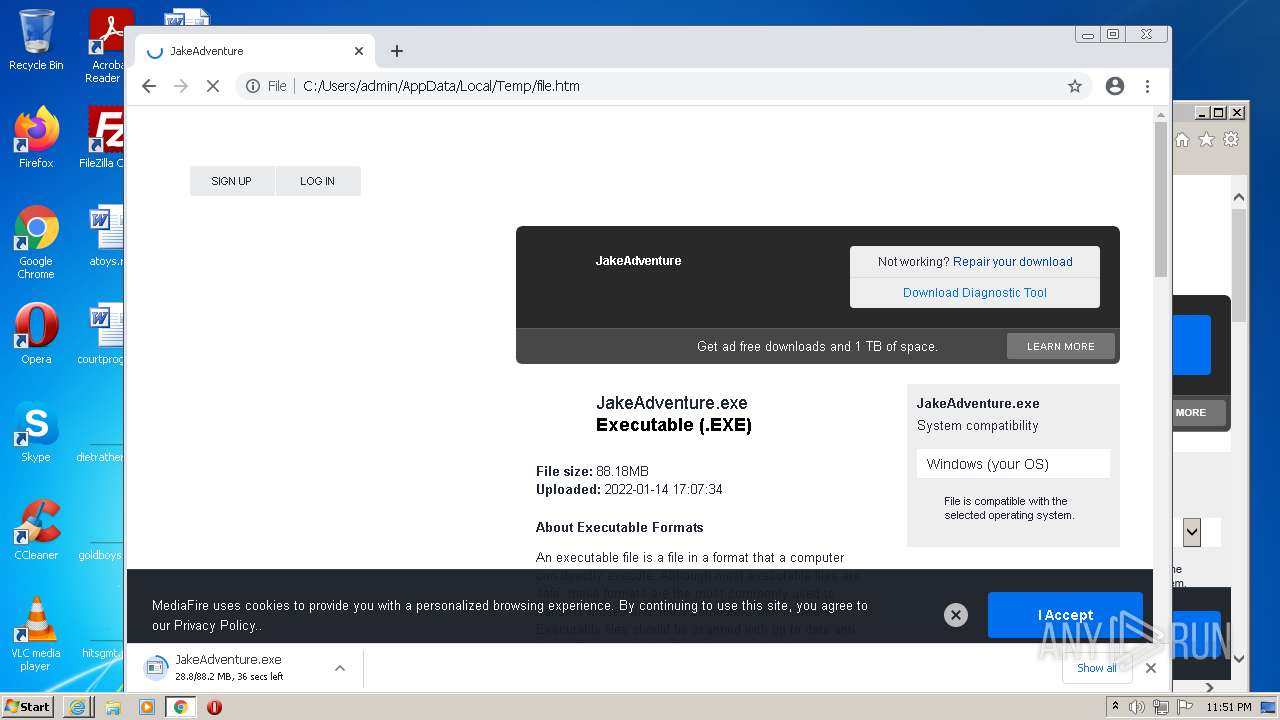
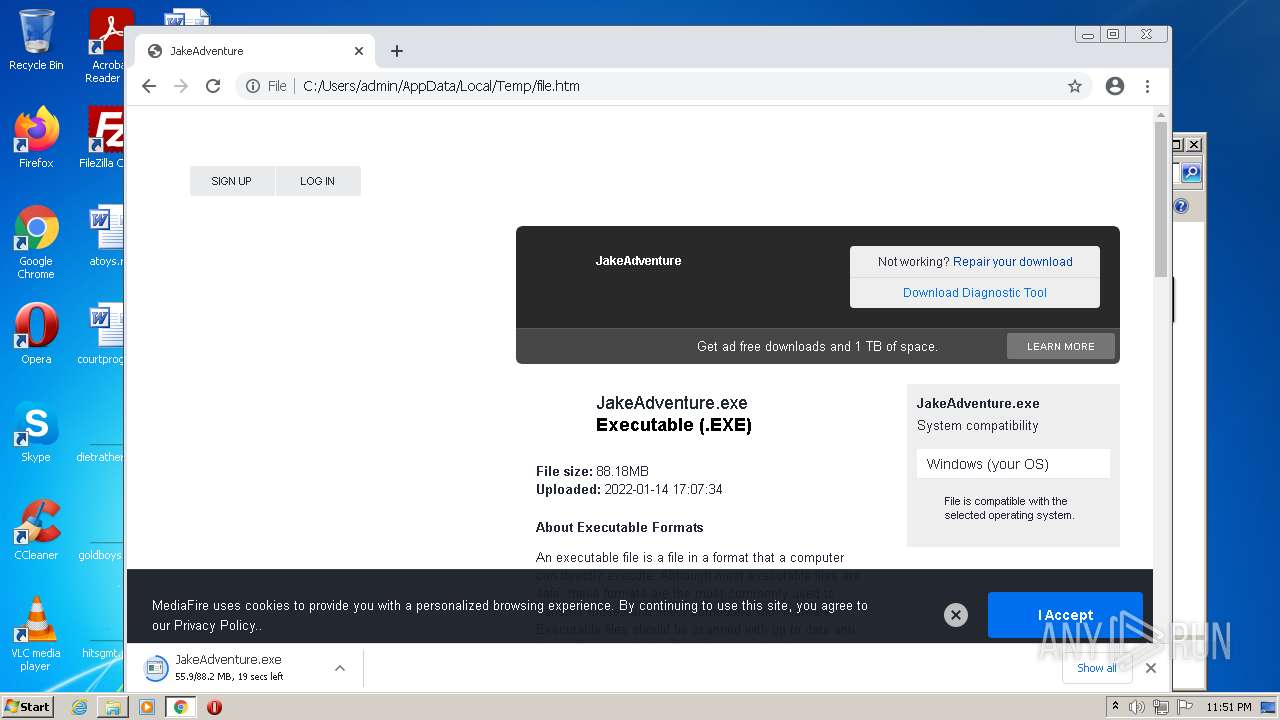
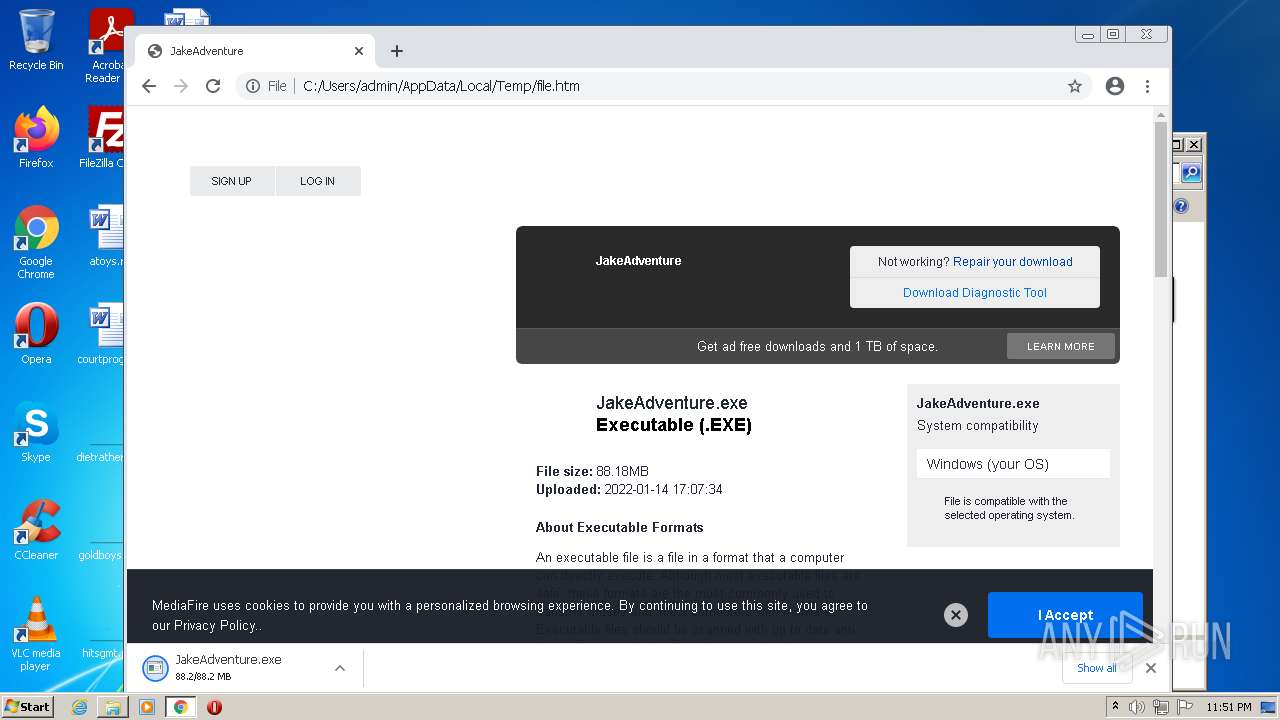
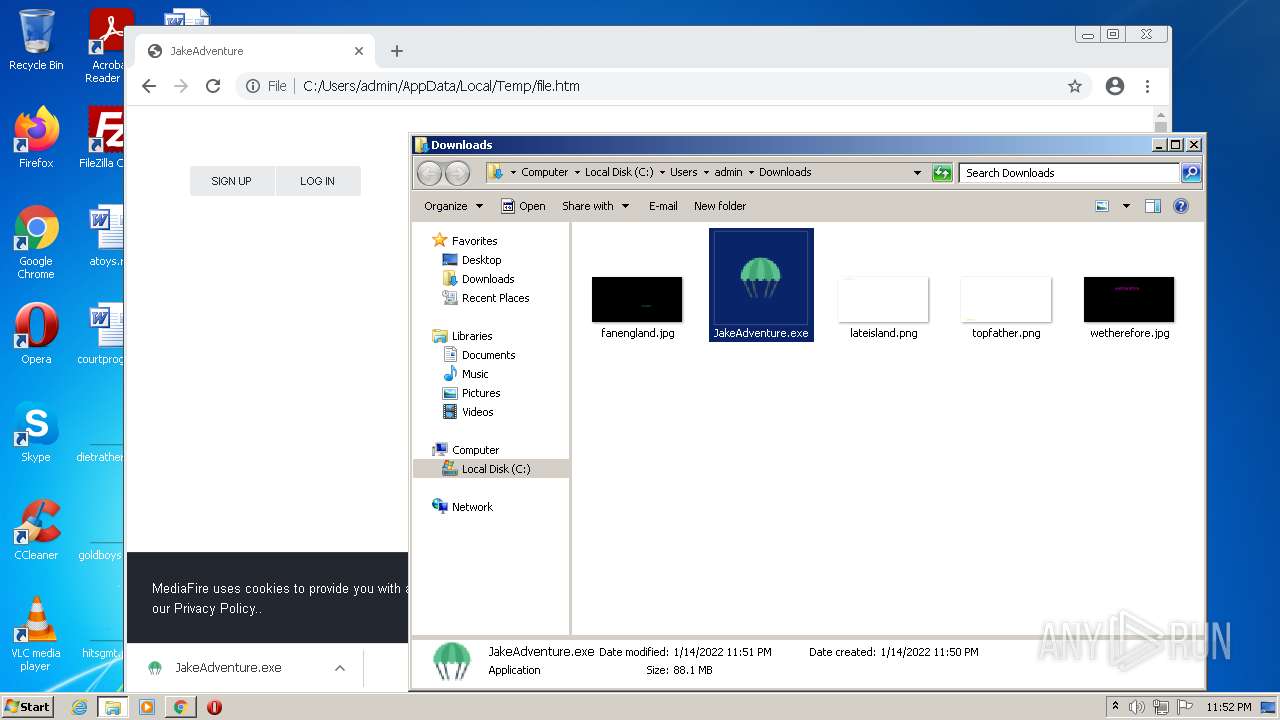
| twitterTitle: | JakeAdventure |
| twitterUrl: | https://www.mediafire.com/file/9j9rfb27z5g6qge/JakeAdventure.exe/file |
| twitterSite: | @MediaFire |
| twitterCard: | summary_large_image |
| googleTranslateCustomization: | 5587c1b0a958bf07-62a8e309de686e87-gc92f61279a2c8524-11 |
| slurp: | noindex,nofollow |
| GoogleBot: | noindex,nofollow |
| Robots: | noindex,nofollow |
| Description: | MediaFire is a simple to use free service that lets you put all your photos, documents, music, and video in a single place so you can access them anywhere and share them everywhere. |
| Keywords: | online storage, free storage, cloud Storage, collaboration, backup file Sharing, share Files, photo backup, photo sharing, ftp replacement, cross platform, remote access, mobile access, send large files, recover files, file versioning, undelete, Windows, PC, Mac, OS X, Linux, iPhone, iPad, Android |
| Title: | JakeAdventure |
| viewport: | width=device-width, initial-scale=1, shrink-to-fit=no |
| HTTPEquivXUaCompatible: | ie=edge |
Total processes
83
Monitored processes
39
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1020,11105468550978731304,7355726273868346124,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3276 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1020,11105468550978731304,7355726273868346124,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3700 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1020,11105468550978731304,7355726273868346124,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1020,11105468550978731304,7355726273868346124,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3196 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1020,11105468550978731304,7355726273868346124,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2852 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1020,11105468550978731304,7355726273868346124,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1688 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1020,11105468550978731304,7355726273868346124,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3780 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1020,11105468550978731304,7355726273868346124,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2852 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Internet Explorer\iexplore.exe" "C:\Users\admin\AppData\Local\Temp\file.htm" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,11105468550978731304,7355726273868346124,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1044 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
43 342
Read events
42 927
Write events
397
Delete events
18
Modification events
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30935457 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30935457 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
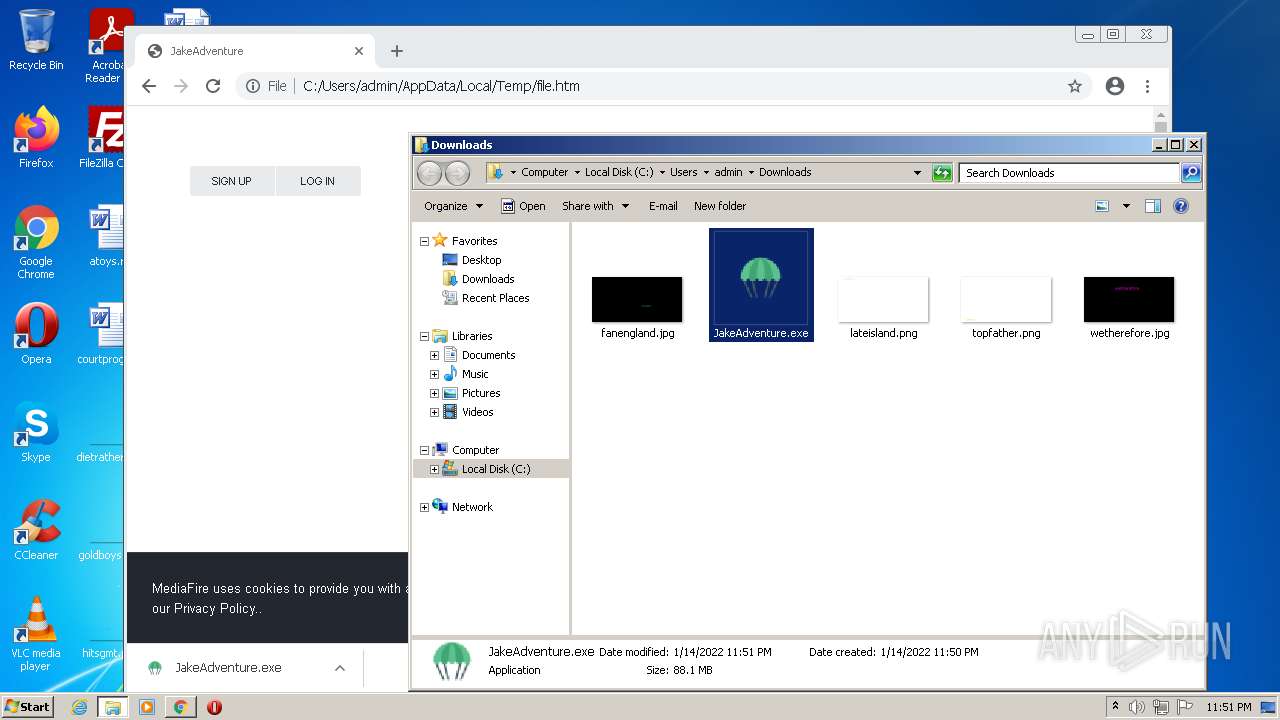
Executable files
1
Suspicious files
107
Text files
169
Unknown types
31
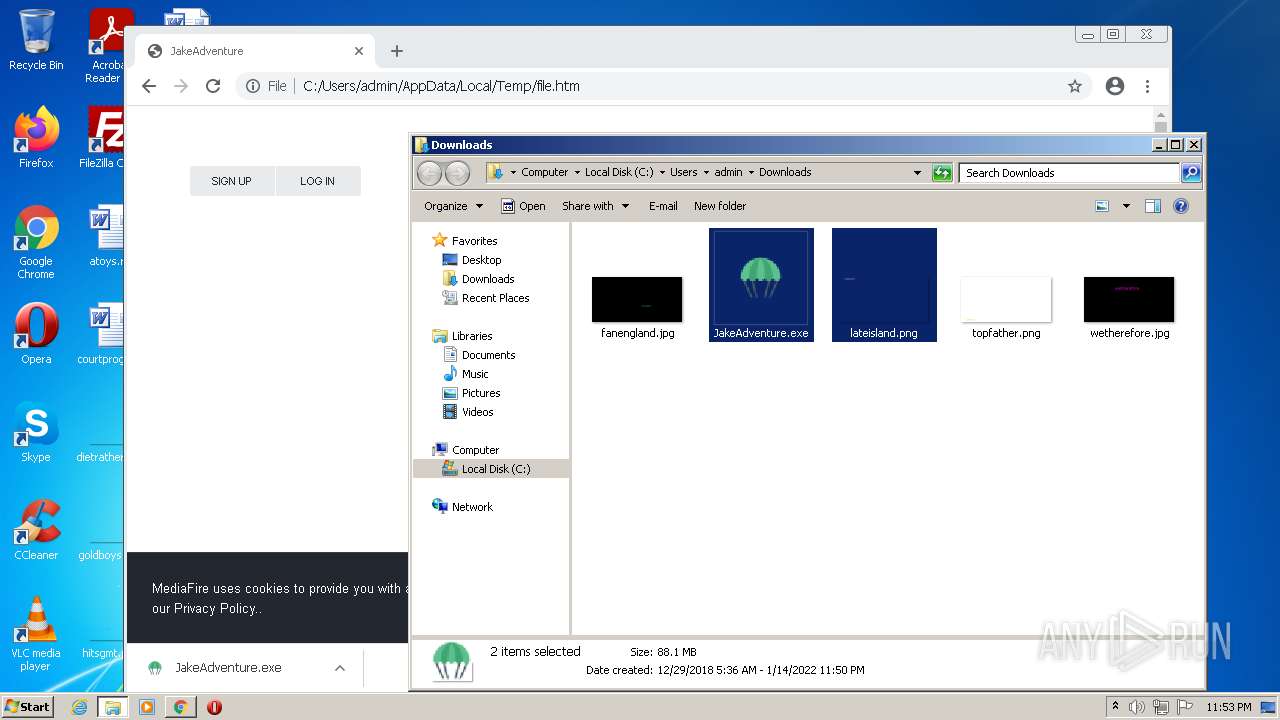
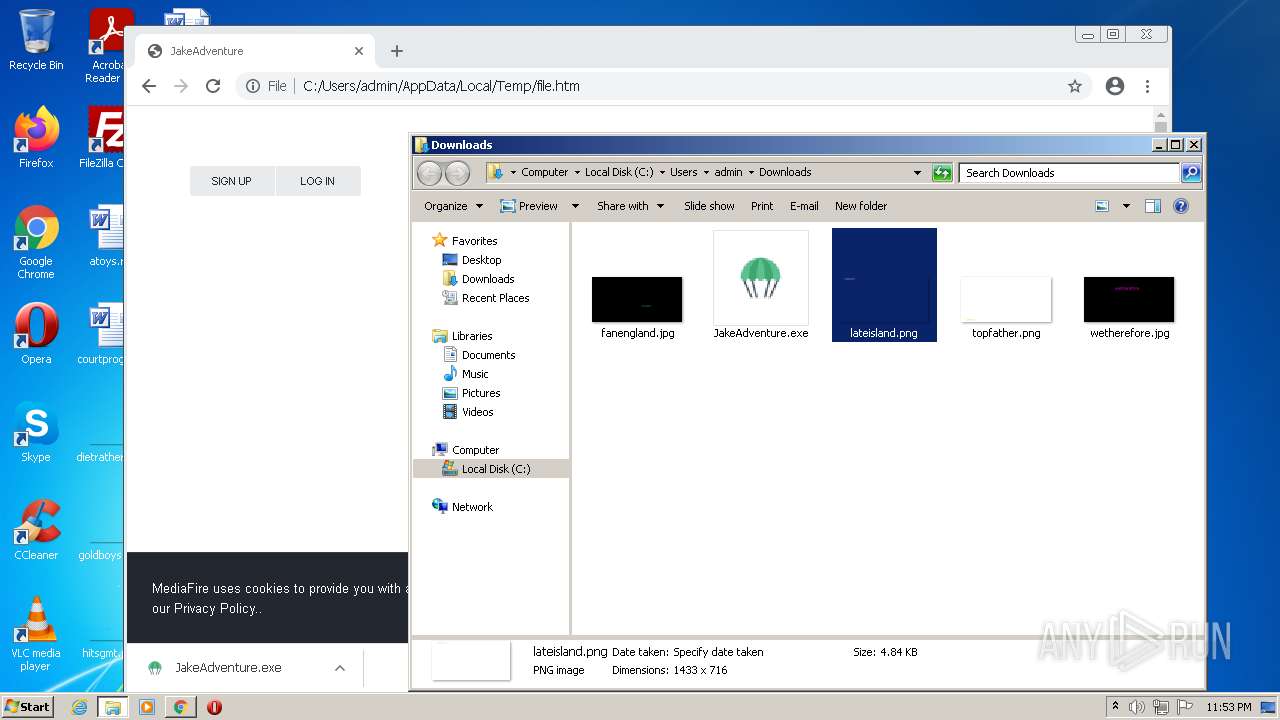
Dropped files
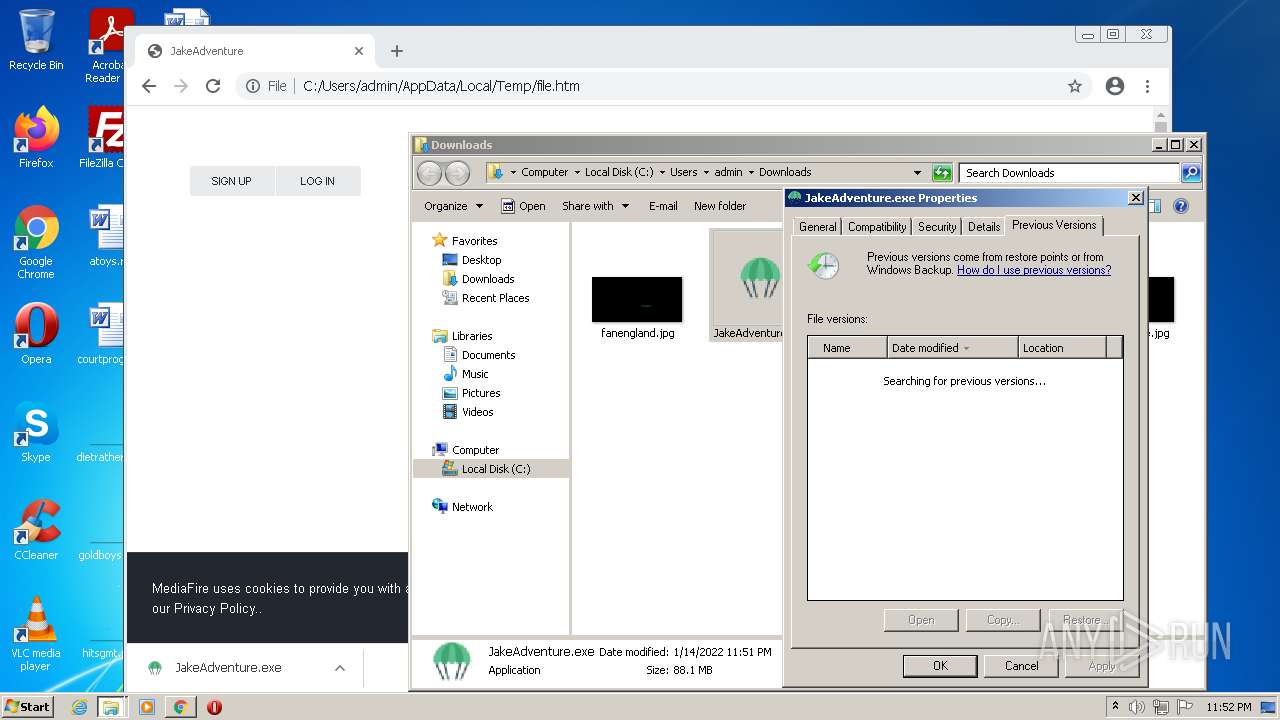
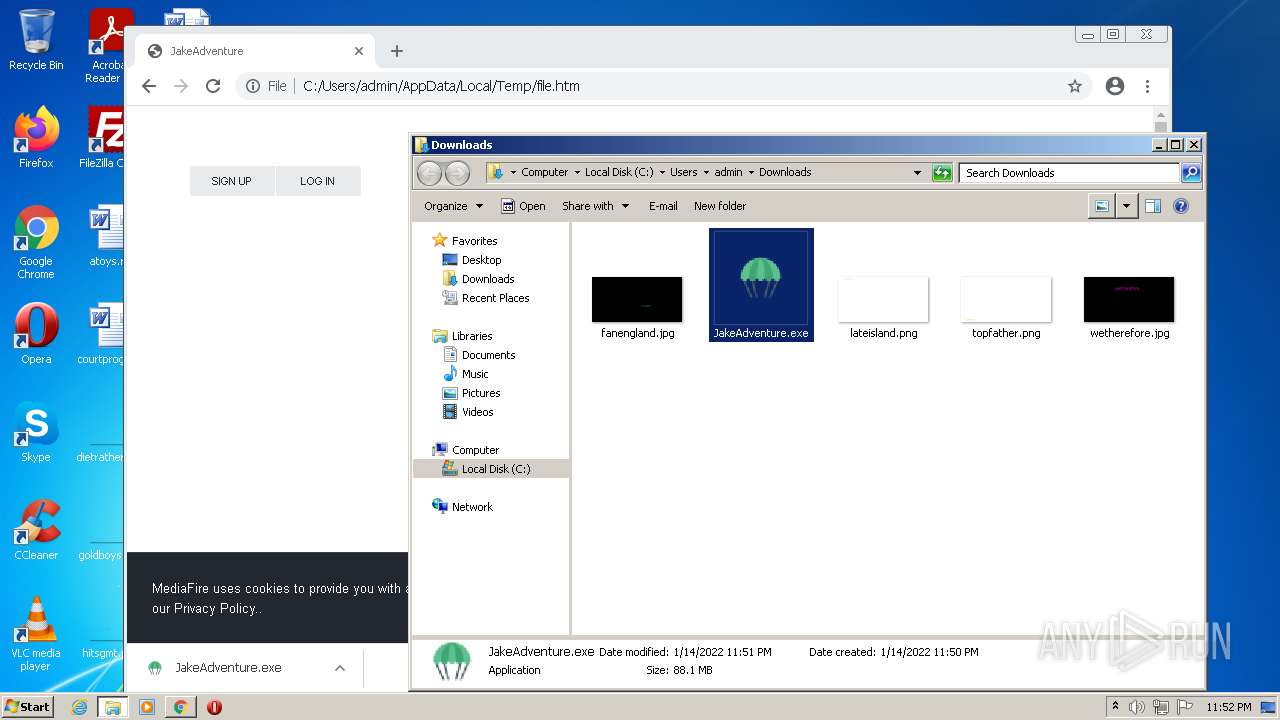
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61E20C33-F38.pma | — | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\tag[1].js | text | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F2DDCD2B5F37625B82E81F4976CEE400_A01EFC9EF87B331821A80D893F4D7FE8 | der | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F2DDCD2B5F37625B82E81F4976CEE400_A01EFC9EF87B331821A80D893F4D7FE8 | binary | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
115
DNS requests
73
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3176 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3176 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3176 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | US | der | 471 b | whitelisted |
3176 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCAnDacZA1UWwoAAAABJ9nq | US | der | 472 b | whitelisted |
3176 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3176 | iexplore.exe | GET | 200 | 18.66.92.210:80 | http://s.ss2.us/r.crl | US | der | 434 b | whitelisted |
3176 | iexplore.exe | GET | 200 | 52.222.250.174:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3176 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | US | der | 727 b | whitelisted |
3176 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR64T7ooMQqLLQoy%2BemBUYZQOKh6QQUkK9qOpRaC9iQ6hJWc99DtDoo2ucCEQDsCXYdUL4EYo7T3qwnuV1j | US | der | 472 b | whitelisted |
1324 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3176 | iexplore.exe | 104.26.7.139:443 | btloader.com | Cloudflare Inc | US | suspicious |
4 | System | 104.16.202.237:445 | static.mediafire.com | Cloudflare Inc | US | unknown |
4 | System | 142.250.186.142:445 | translate.google.com | Google Inc. | US | whitelisted |
3176 | iexplore.exe | 8.248.149.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3176 | iexplore.exe | 216.58.212.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
— | — | 142.250.186.142:139 | translate.google.com | Google Inc. | US | whitelisted |
3176 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 104.16.203.237:139 | static.mediafire.com | Cloudflare Inc | US | unknown |
1324 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1612 | chrome.exe | 142.250.181.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
btloader.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
translate.google.com |
| whitelisted |
static.mediafire.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1612 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
1612 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |