| File name: | openme.exe |
| Full analysis: | https://app.any.run/tasks/d11ff2e6-ed75-4cc2-b9e6-078520fc46b3 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2018, 10:19:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E3B3E285390C0E2F7D04BD040BEC790D |
| SHA1: | DBEE71535E9F1FB23B3F01E25989D22D51237E68 |
| SHA256: | 21A0201874AF80436DC0A36E5CBAF7DA9B75217B3E39B712F3850729CF47DEB6 |
| SSDEEP: | 6144:C9dswuuW1sVyO6x5x6bQ5PJIgNdsalkFrgikCxEwdrDY2AotYSNlx4:CtuuiswO696bQXIqSa2FjJG0Y2AotYW4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
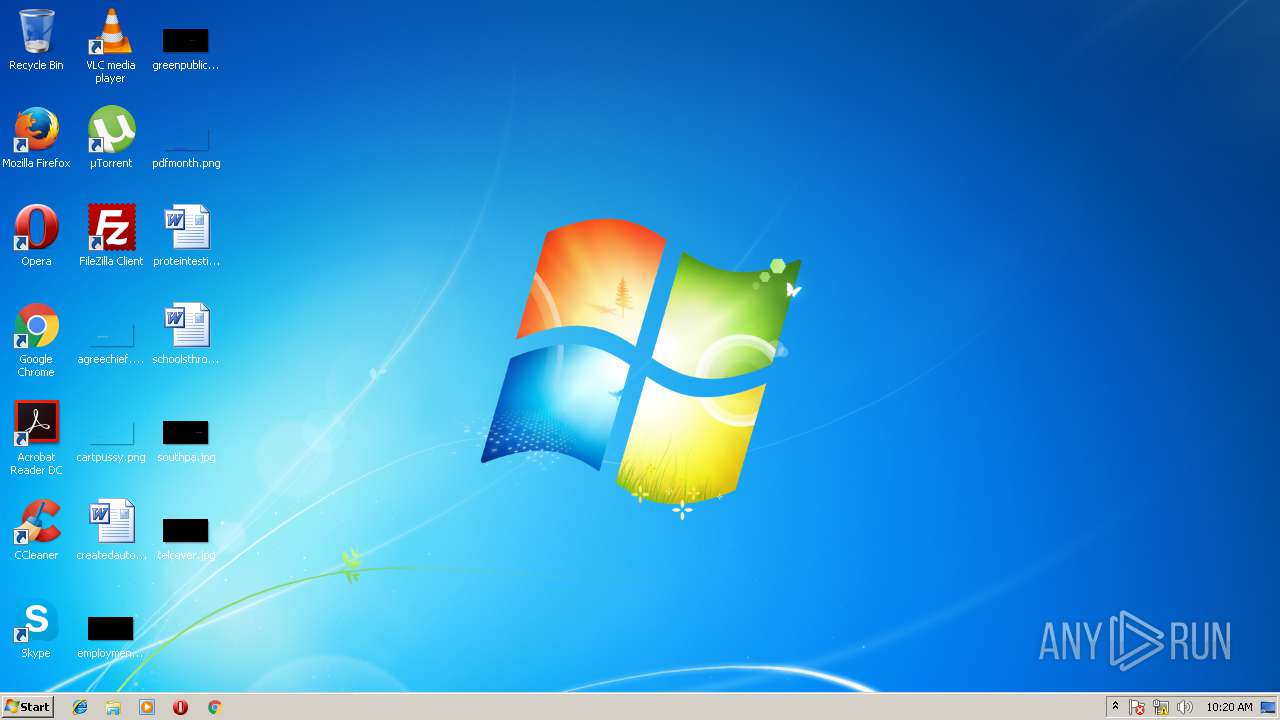
Starts Internet Explorer
- openme.exe (PID: 2872)
Changes the desktop background image
- openme.exe (PID: 2872)
Creates files in the program directory
- openme.exe (PID: 2872)
Starts CMD.EXE for commands execution
- openme.exe (PID: 2872)
INFO
Creates files in the user directory
- iexplore.exe (PID: 3588)
Changes internet zones settings
- iexplore.exe (PID: 3360)
Reads Internet Cache Settings
- iexplore.exe (PID: 3588)
- iexplore.exe (PID: 3360)
Application launched itself
- iexplore.exe (PID: 3360)
Reads internet explorer settings
- iexplore.exe (PID: 2916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:02:19 18:56:19+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 118784 |
| InitializedDataSize: | 261632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9b26 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.3.5.7 |
| ProductVersionNumber: | 6.3.5.7 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileVersion: | 6.3.5.7 |
| Comments: | We've Lqtm |
| FileDescription: | We've Lqtm |
| CompanyName: | Lavasoft |
| OriginalFileName: | Withhold |
| LegalCopyright: | Copyright (c) 2006-2014 Lavasoft |
| ProductName: | Withhold |
| ProductVersion: | 6.3.5.7 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Feb-2017 17:56:19 |
| Detected languages: |
|
| FileVersion: | 6.3.5.7 |
| Comments: | We've Lqtm |
| FileDescription: | We've Lqtm |
| CompanyName: | Lavasoft |
| OriginalFilename: | Withhold |
| LegalCopyright: | Copyright (c) 2006-2014 Lavasoft |
| ProductName: | Withhold |
| ProductVersion: | 6.3.5.7 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 19-Feb-2017 17:56:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001CE05 | 0x0001D000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65105 |
.rdata | 0x0001E000 | 0x00008592 | 0x00008600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.08658 |
.data | 0x00027000 | 0x000032E4 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.28379 |
.tls | 0x0002B000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002C000 | 0x00035EF8 | 0x00036000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.60097 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.0479 | 634 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 7.90987 | 15089 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.03869 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.08344 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.36189 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
105 | 2.60986 | 76 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
357 | 7.97603 | 13848 | Latin 1 / Western European | English - United States | RCDATA |
488 | 7.97594 | 12131 | Latin 1 / Western European | English - United States | RCDATA |
560 | 2.01924 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_CURSOR |
597 | 3.29584 | 344 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
AVICAP32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
NETAPI32.dll |
ODBC32.dll |
OLEAUT32.dll |
Total processes
39
Monitored processes
6
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2872 | "C:\Users\admin\AppData\Local\Temp\openme.exe" | C:\Users\admin\AppData\Local\Temp\openme.exe | — | explorer.exe | |||||||||||
User: admin Company: Lavasoft Integrity Level: MEDIUM Description: We've Lqtm Exit code: 0 Version: 6.3.5.7 Modules
| |||||||||||||||
| 2916 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3360 CREDAT:14337 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3360 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | — | openme.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3556 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3588 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3360 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3676 | cmd.exe /C del /Q /F "C:\Users\admin\AppData\Local\Temp\openme.exe" | C:\Windows\system32\cmd.exe | — | openme.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 177
Read events
1 072
Write events
105
Delete events
0
Modification events
| (PID) Process: | (2872) openme.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\openme_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2872) openme.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\openme_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2872) openme.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\openme_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2872) openme.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\openme_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2872) openme.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\openme_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2872) openme.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\openme_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2872) openme.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\openme_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2872) openme.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\openme_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2872) openme.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\openme_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2872) openme.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\openme_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
38
Text files
25
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2872 | openme.exe | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 2872 | openme.exe | C:\Users\admin\Documents\OneNote Notebooks\Personal\Open Notebook.onetoc2 | — | |
MD5:— | SHA256:— | |||
| 2872 | openme.exe | C:\Users\admin\Documents\Outlook Files\Outlook.pst | — | |
MD5:— | SHA256:— | |||
| 2872 | openme.exe | C:\Users\admin\Desktop\createdauto.rtf | — | |
MD5:— | SHA256:— | |||
| 2872 | openme.exe | C:\Users\admin\Documents\thisany.rtf | — | |
MD5:— | SHA256:— | |||
| 2872 | openme.exe | C:\Users\admin\Desktop\schoolsthrough.rtf | — | |
MD5:— | SHA256:— | |||
| 2872 | openme.exe | C:\Users\admin\Documents\unitcharles.rtf | — | |
MD5:— | SHA256:— | |||
| 2872 | openme.exe | C:\Users\admin\Desktop\proteintesting.rtf | — | |
MD5:— | SHA256:— | |||
| 2872 | openme.exe | C:\Users\admin\Documents\chatonline.rtf | — | |
MD5:— | SHA256:— | |||
| 2872 | openme.exe | C:\Users\admin\Documents\factorstips.rtf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
1
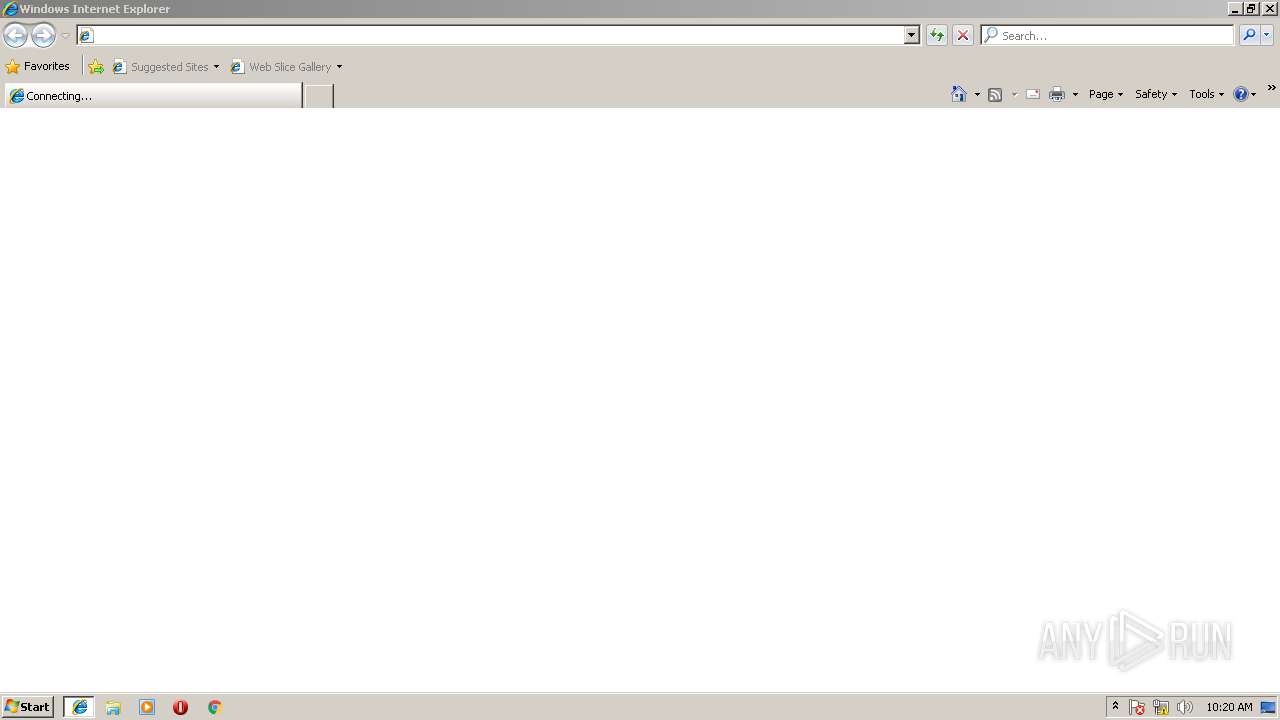
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | — | 81.177.27.36:80 | http://81.177.27.36/checkupdate | RU | — | — | malicious |
— | — | POST | — | 81.177.27.36:80 | http://81.177.27.36/checkupdate | RU | — | — | malicious |
— | — | POST | — | 81.177.27.36:80 | http://81.177.27.36/checkupdate | RU | — | — | malicious |
— | — | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 81.177.27.36:80 | — | JSC RTComm.RU | RU | malicious |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET CNC Ransomware Tracker Reported CnC Server group 99 |