| download: | europe-middle-east-africa-emea |
| Full analysis: | https://app.any.run/tasks/b1e845ea-67d1-47b4-b30b-78db14e2ee07 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 20:10:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | 0E031F1CB31235B3C7A0EA0772A55C04 |
| SHA1: | 4723B09900E47DBEA9FAF11BA07BF998898073BB |
| SHA256: | 219CC8485BFB02638D037CE53FDC1C0F369E3DE021D179A64F134D61012D7B22 |
| SSDEEP: | 3072:EHGEbWT/d5zG0J2cTBRArTMqXJOphsRgve81Hr0HK4kH7pqHNgdH0hHKnEHWdH2x:EHDcTBRArTMqXJOphsRgG74xqz |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 1556)
Reads internet explorer settings
- iexplore.exe (PID: 2504)
Reads settings of System Certificates
- iexplore.exe (PID: 2504)
Reads Internet Cache Settings
- iexplore.exe (PID: 2504)
Changes internet zones settings
- iexplore.exe (PID: 1556)
Creates files in the user directory
- iexplore.exe (PID: 2504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
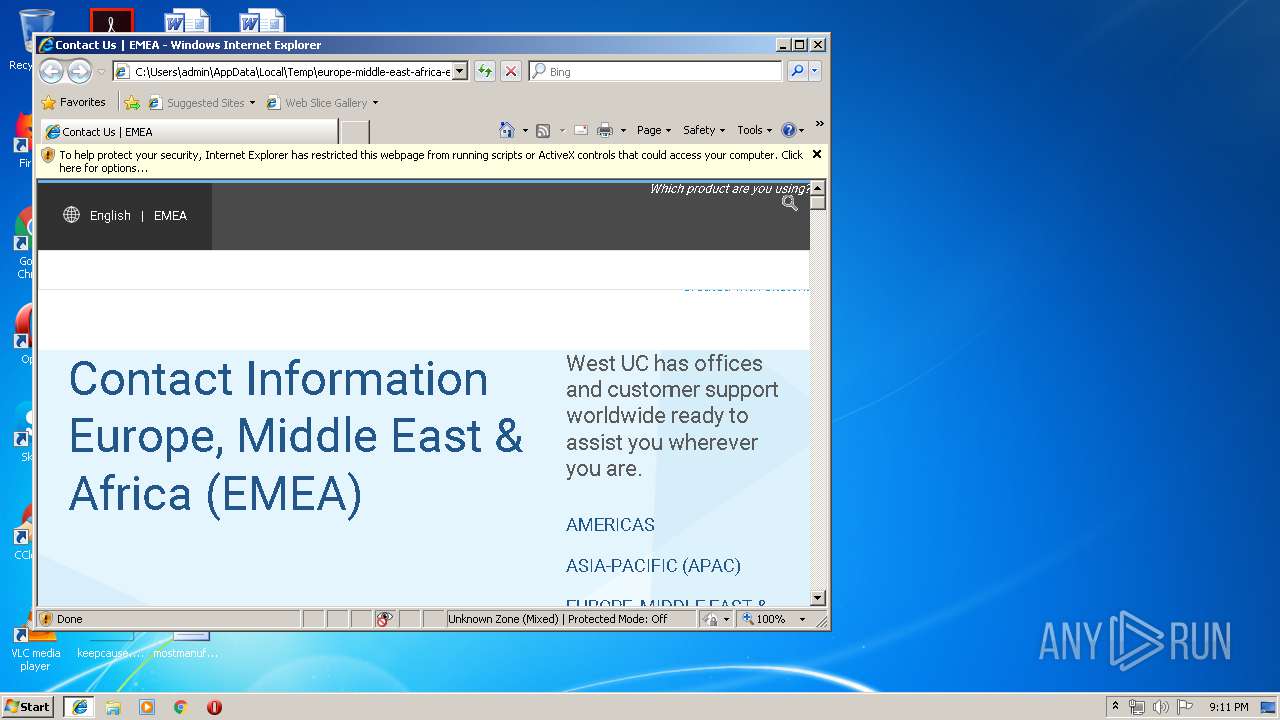
| Description: | Contact West Unified Communications Services offices in Europe, Middle East and Africa (EMEA). |
|---|---|
| Generator: | Drupal 7 (http://drupal.org) |
| msvalidate01: | 9C75077AE08E824E7CC3F3A25F8D182D |
| googleSiteVerification: | 9j8qiOTQ0iAaETPkP7_yL0-dg0PDQL0qW3DPvwPlvXg |
| Title: | Contact Us | EMEA |
| MobileOptimized: | width |
| HandheldFriendly: | |
| viewport: | width=device-width,initial-scale=1.0,minimum-scale=1.0,maximum-scale=1.0,user-scalable=no |
| HTTPEquivCleartype: | on |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1556 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\europe-middle-east-africa-emea.htm | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1556 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
399
Read events
322
Write events
76
Delete events
1
Modification events
| (PID) Process: | (1556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070A0001000E0014000A0017006402 | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | LoadTime |
Value: 8 | |||
Executable files
0
Suspicious files
0
Text files
35
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\css_Bb2UQwhX0P7AS13cRxramAccdjVZ8_JWvk9HT8Xn7AI[1].css | text | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\css_nCfBclPckLay7fV70jgH9WLLinjDPQ2HFmWO3M7vOaE[1].css | text | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\js_ocUCH5KDyoO03OHo8ucOMoLEPMowmCkg0mUP9EHm8pQ[1].js | text | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\css_9YJ6Kpp9ROwGz_vqBpCBgk30a5INlGiLJS9IjquK13k[1].css | text | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\globe[1].svg | — | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\caret-down[1].svg | — | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\js_-9-t5t3cxgBM0qlyUvU_F3LDJA0oEpwRLCkDl8ZEGmw[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
29
DNS requests
9
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2504 | iexplore.exe | OPTIONS | 400 | 172.217.21.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
2504 | iexplore.exe | OPTIONS | 400 | 172.217.21.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
2504 | iexplore.exe | OPTIONS | 400 | 172.217.21.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
2504 | iexplore.exe | OPTIONS | 400 | 172.217.21.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
2504 | iexplore.exe | OPTIONS | 400 | 172.217.21.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
2504 | iexplore.exe | OPTIONS | 400 | 172.217.21.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
2504 | iexplore.exe | OPTIONS | 400 | 172.217.21.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
1556 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2504 | iexplore.exe | OPTIONS | 400 | 172.217.21.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
2504 | iexplore.exe | OPTIONS | 400 | 172.217.21.232:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1556 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2504 | iexplore.exe | 104.20.38.125:443 | www.westuc.com | Cloudflare Inc | US | shared |
2504 | iexplore.exe | 104.20.39.125:443 | www.westuc.com | Cloudflare Inc | US | shared |
2504 | iexplore.exe | 172.217.18.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2504 | iexplore.exe | 172.217.23.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2504 | iexplore.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
2504 | iexplore.exe | 172.217.23.106:443 | maps.googleapis.com | Google Inc. | US | whitelisted |
2504 | iexplore.exe | 136.147.110.2:443 | c.la4-c2-dfw.salesforceliveagent.com | Salesforce.com, Inc. | US | unknown |
4 | System | 172.217.21.232:139 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2504 | iexplore.exe | 172.217.21.232:80 | www.googletagmanager.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.westuc.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
maps.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
c.la4-c2-dfw.salesforceliveagent.com |
| whitelisted |
Threats
10 ETPRO signatures available at the full report