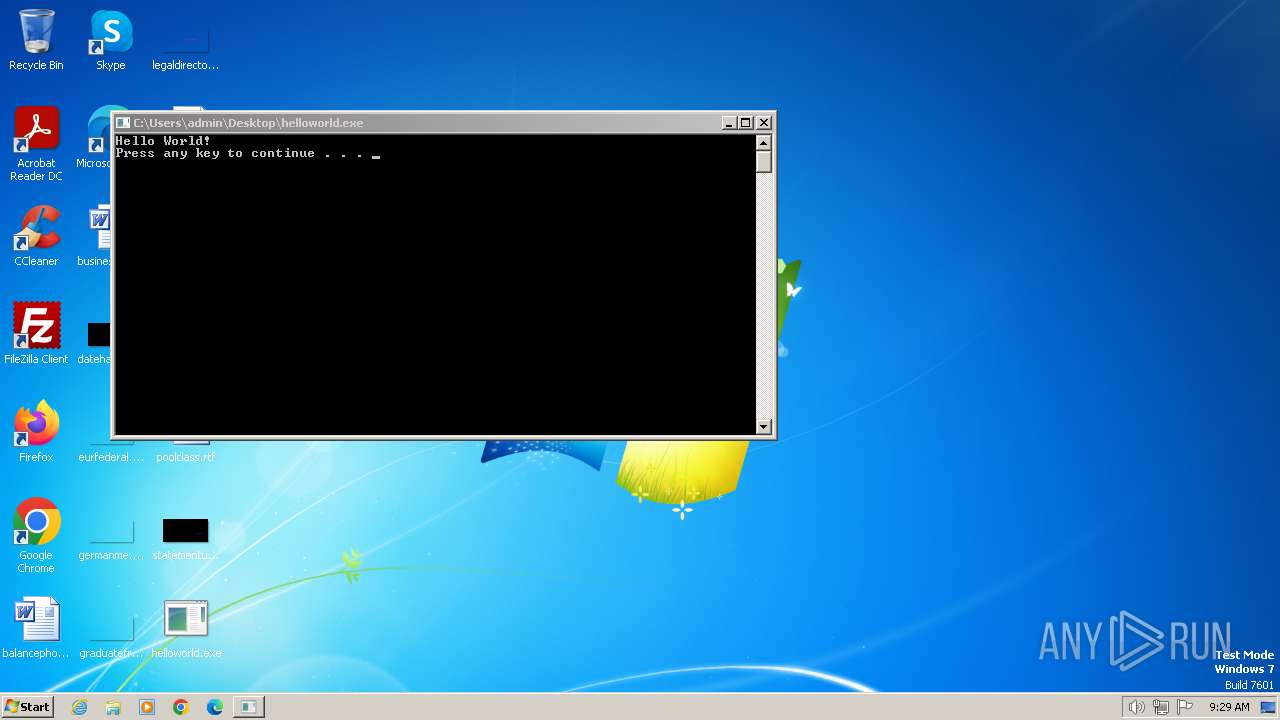
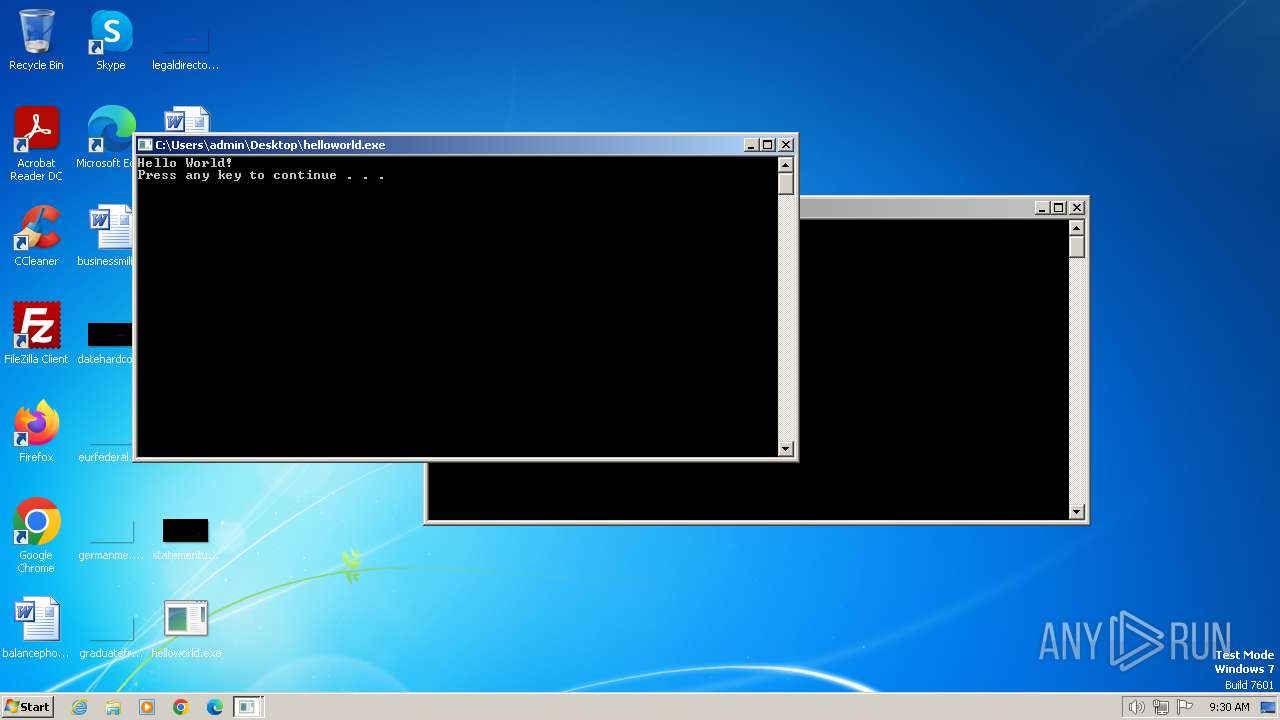
| File name: | helloworld.exe |
| Full analysis: | https://app.any.run/tasks/d78f7c73-bbc9-4ec7-92bb-995c3b9fd3dd |
| Verdict: | Malicious activity |
| Analysis date: | March 04, 2024, 09:27:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 64D94559DE57B1B1ED5F64B0316D5BF5 |
| SHA1: | 9C5573A43259DB0873BB75F0C25A2FBBB9B9B643 |
| SHA256: | 2193B580571CF48BE4C0F90EC497CE2F5D24802ACF2E545FDAAD29320CFE2BE4 |
| SSDEEP: | 3072:dVUJkfiGVLSQJTmcgtzXnIJxShuN+cyQ3cAEkjqfwxRMrM5enXys3g1886XatP:deMiG0JftzXIjS8N+cybAEM28btP |
MALICIOUS
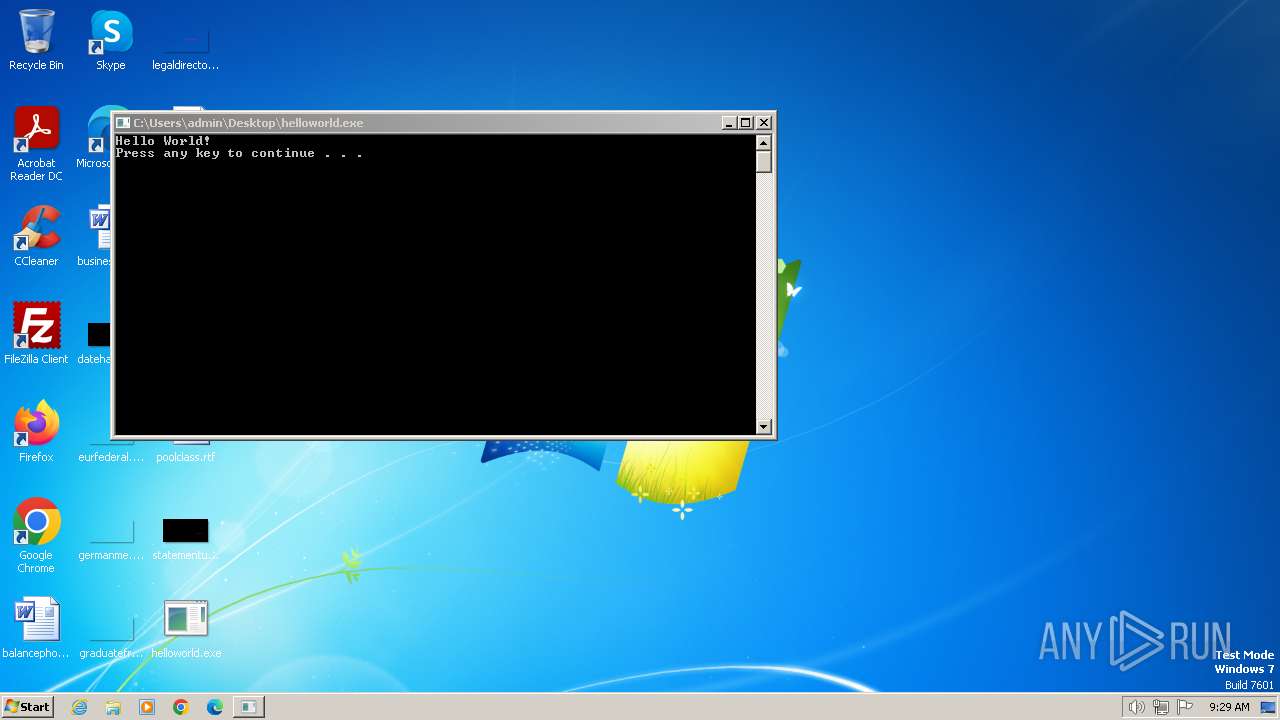
Drops the executable file immediately after the start
- cmd.exe (PID: 3668)
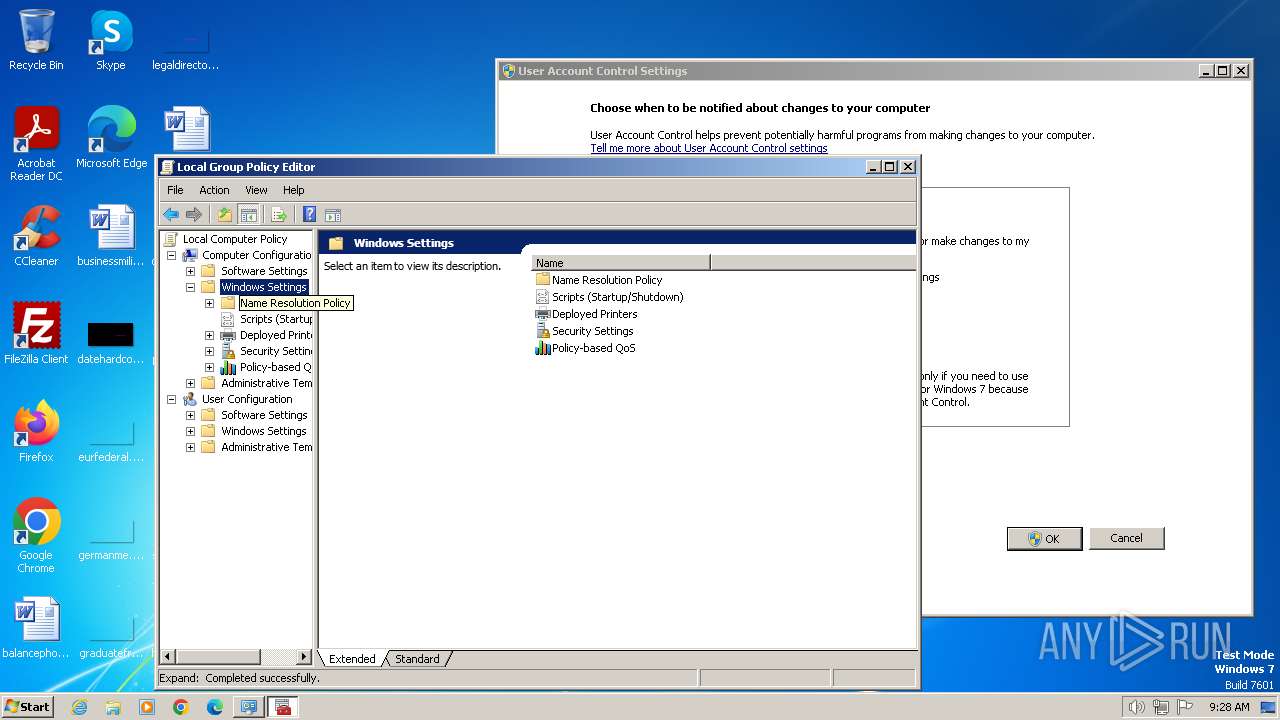
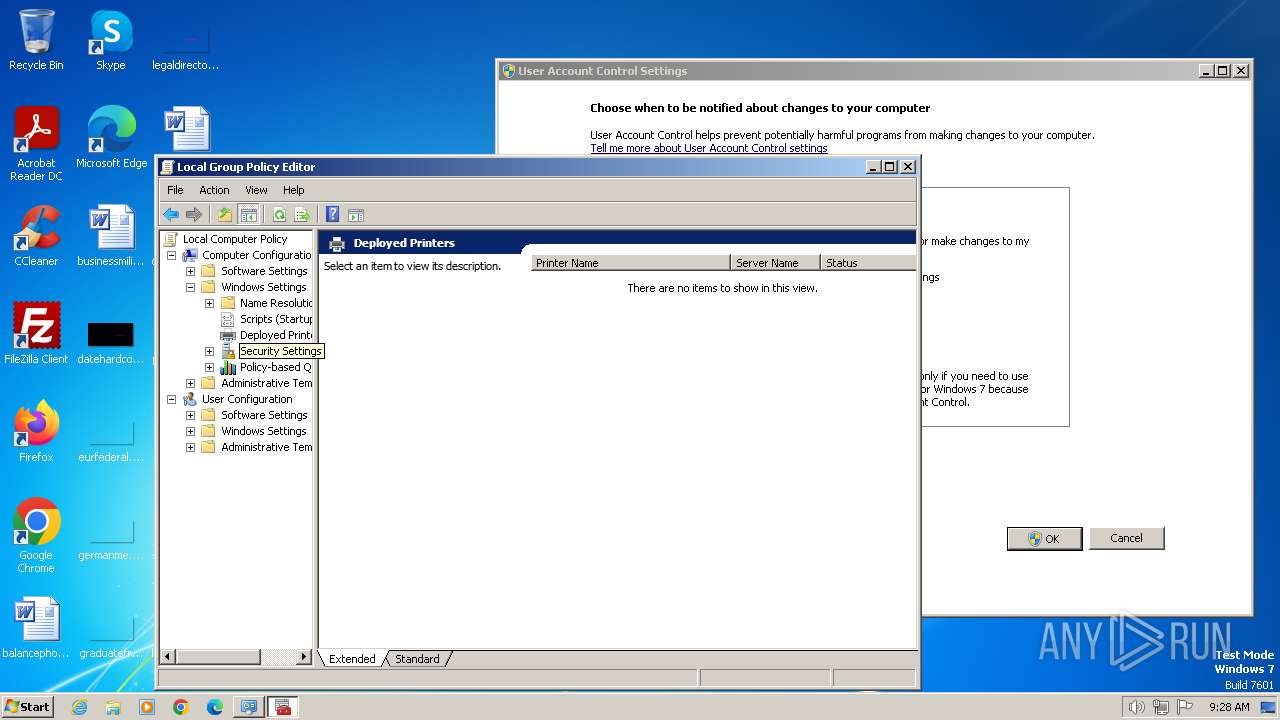
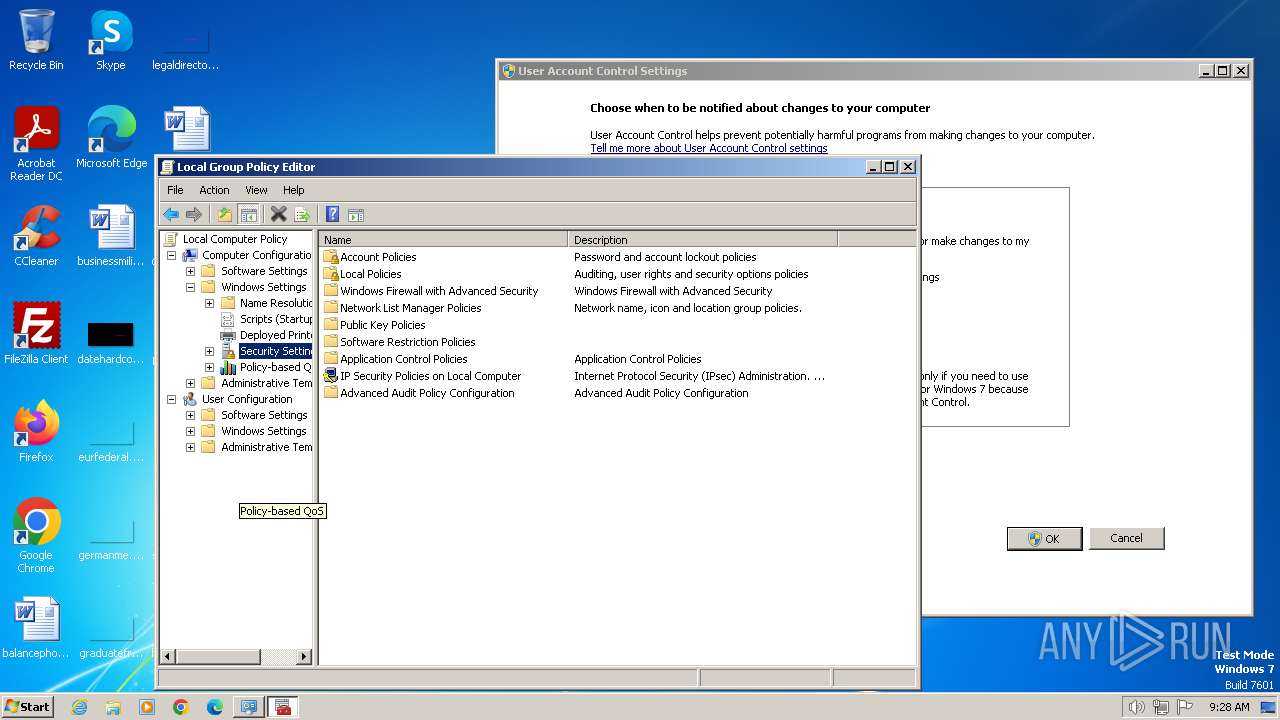
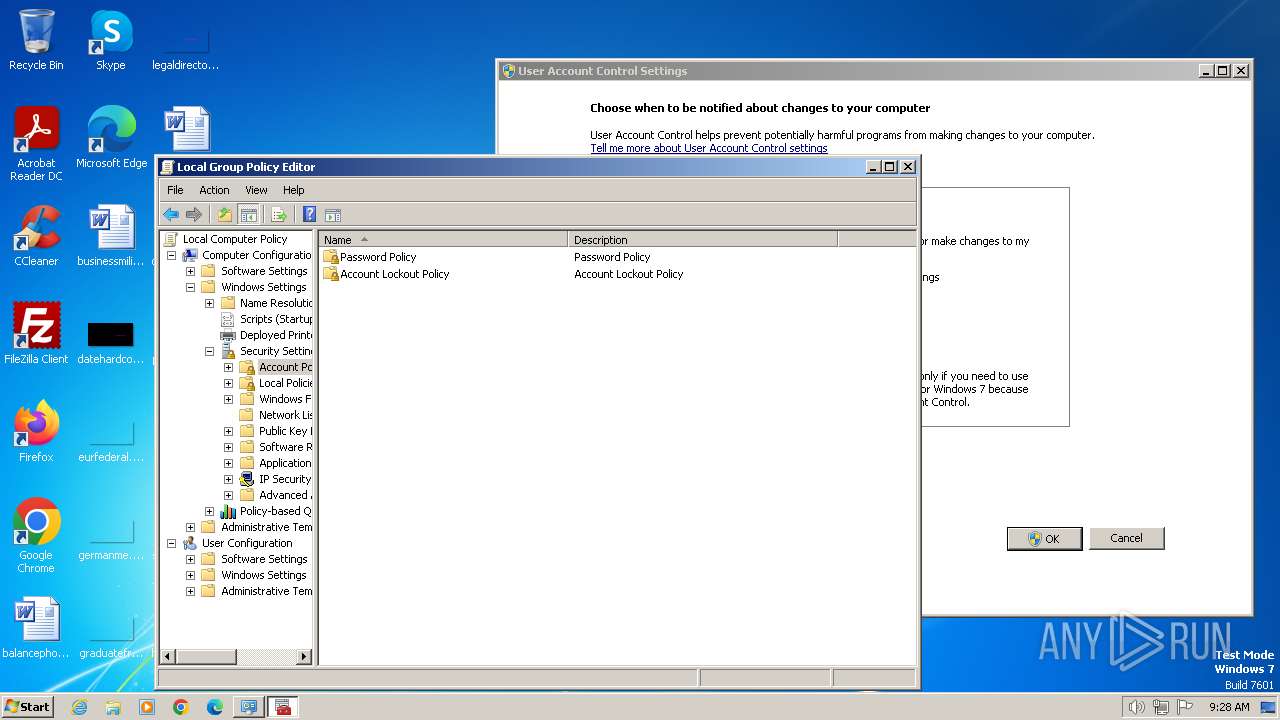
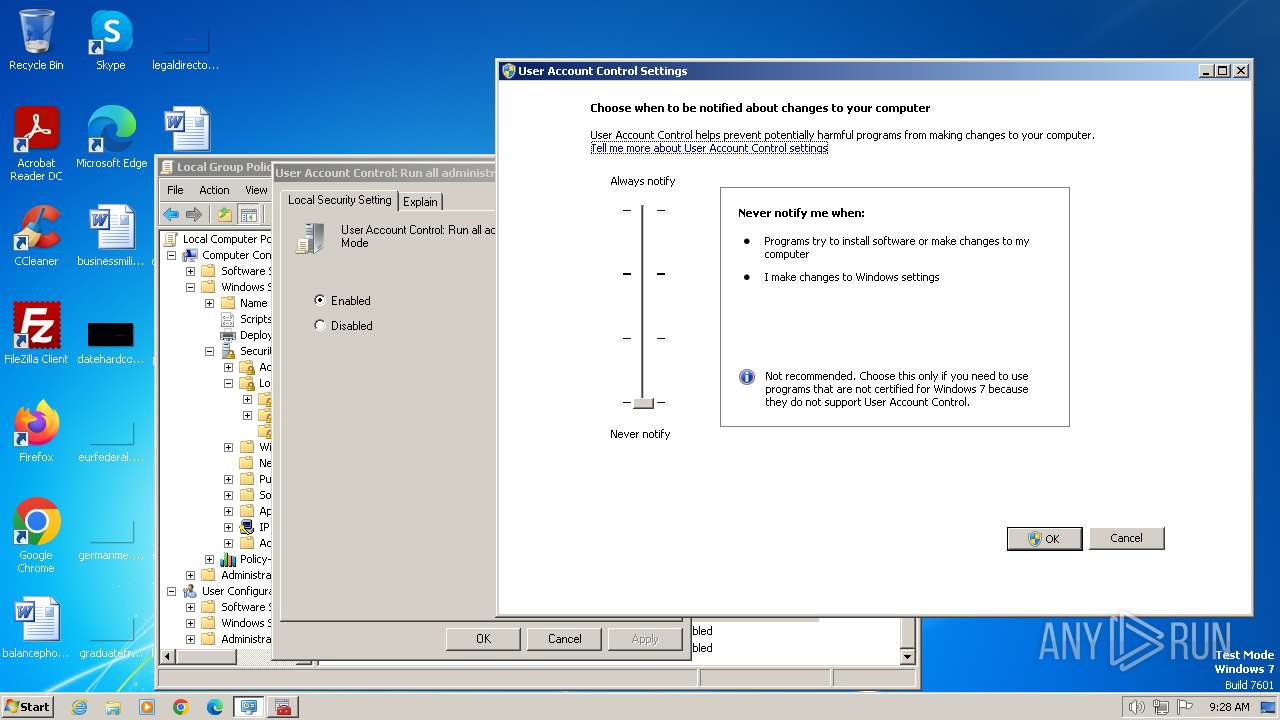
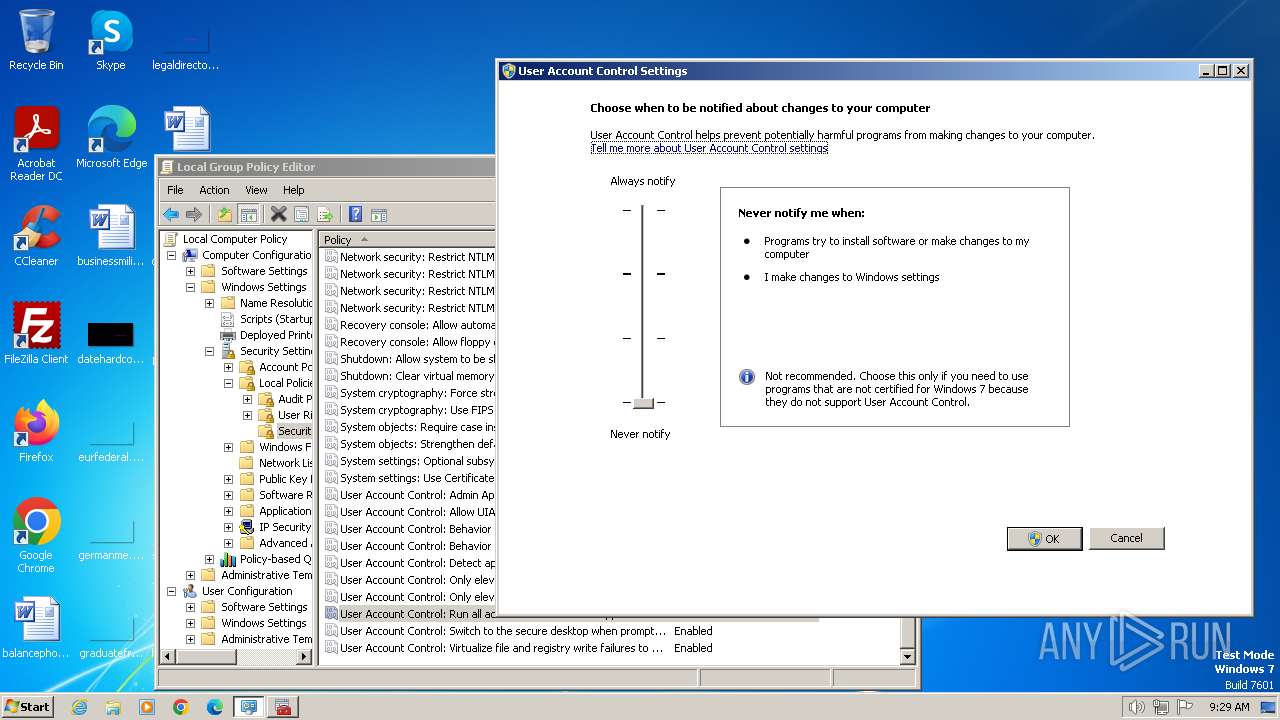
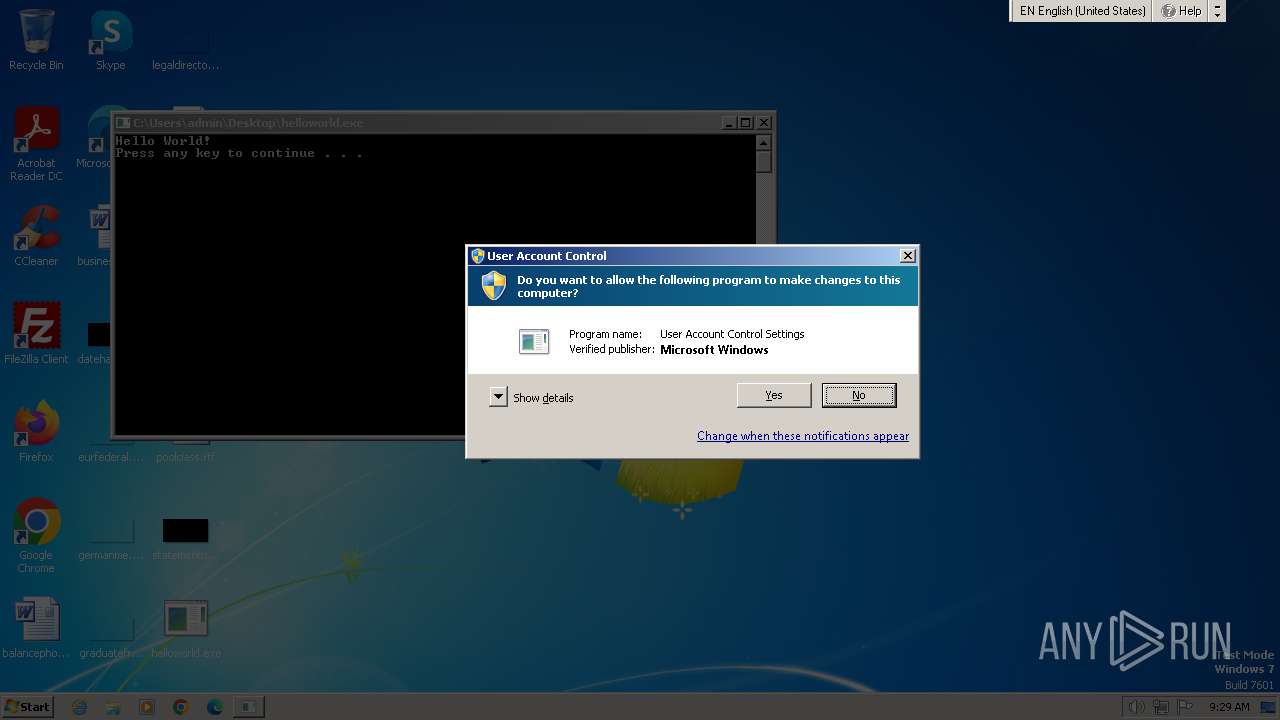
Changes the Windows auto-update feature
- mmc.exe (PID: 3912)
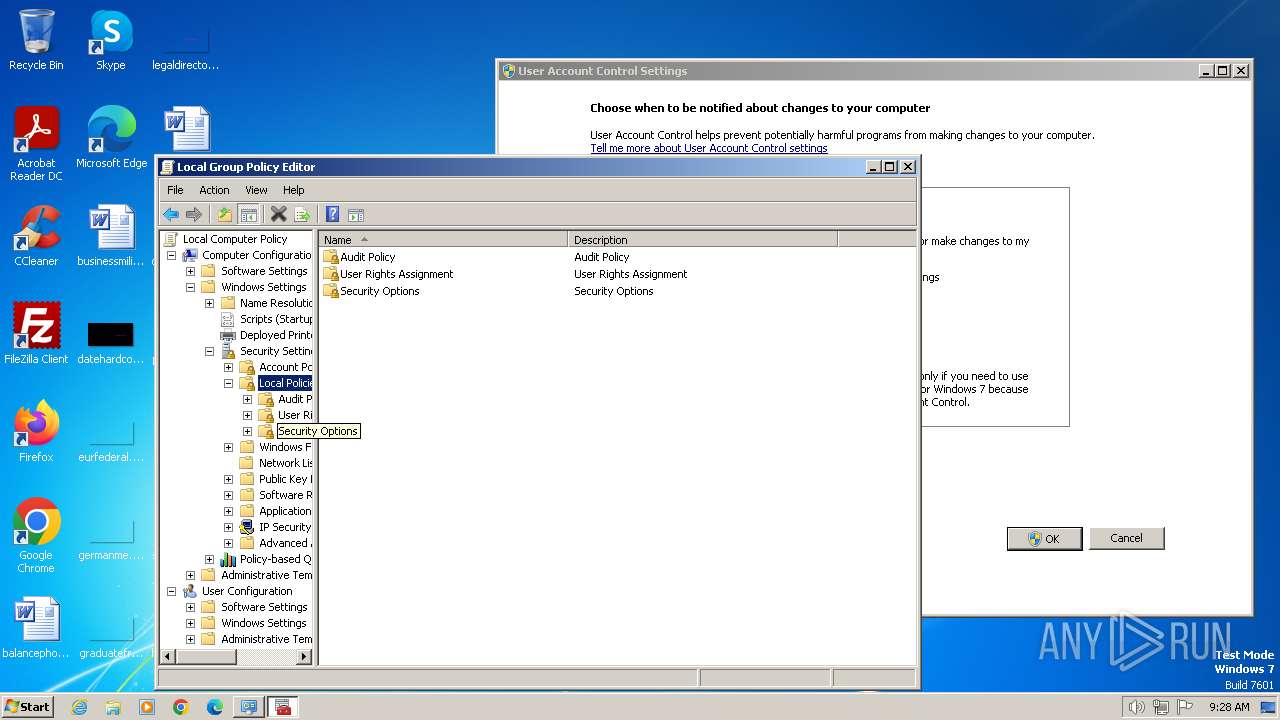
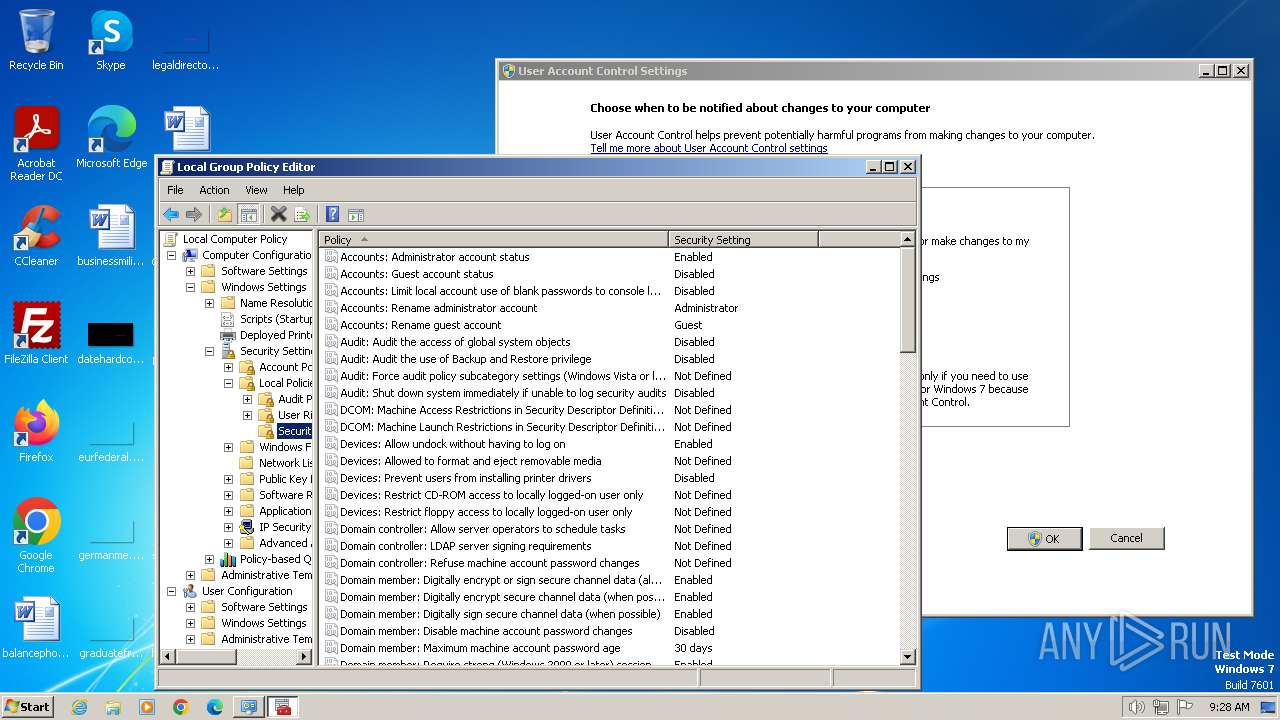
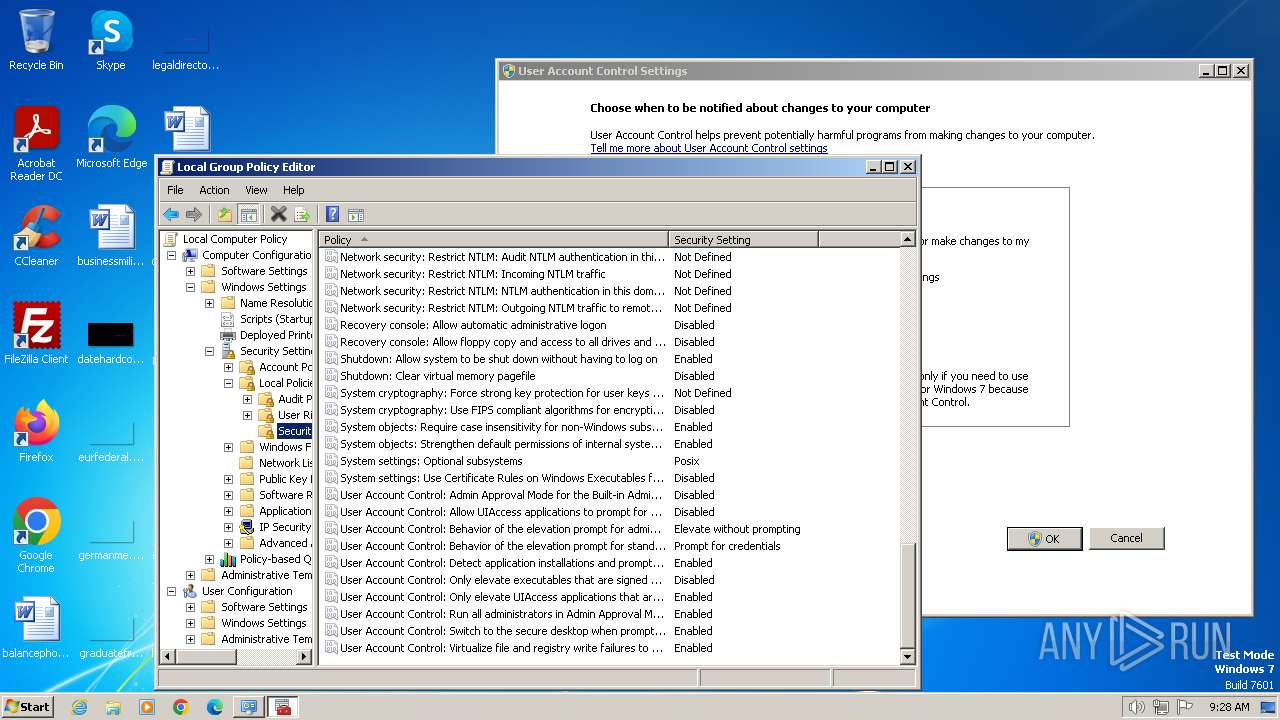
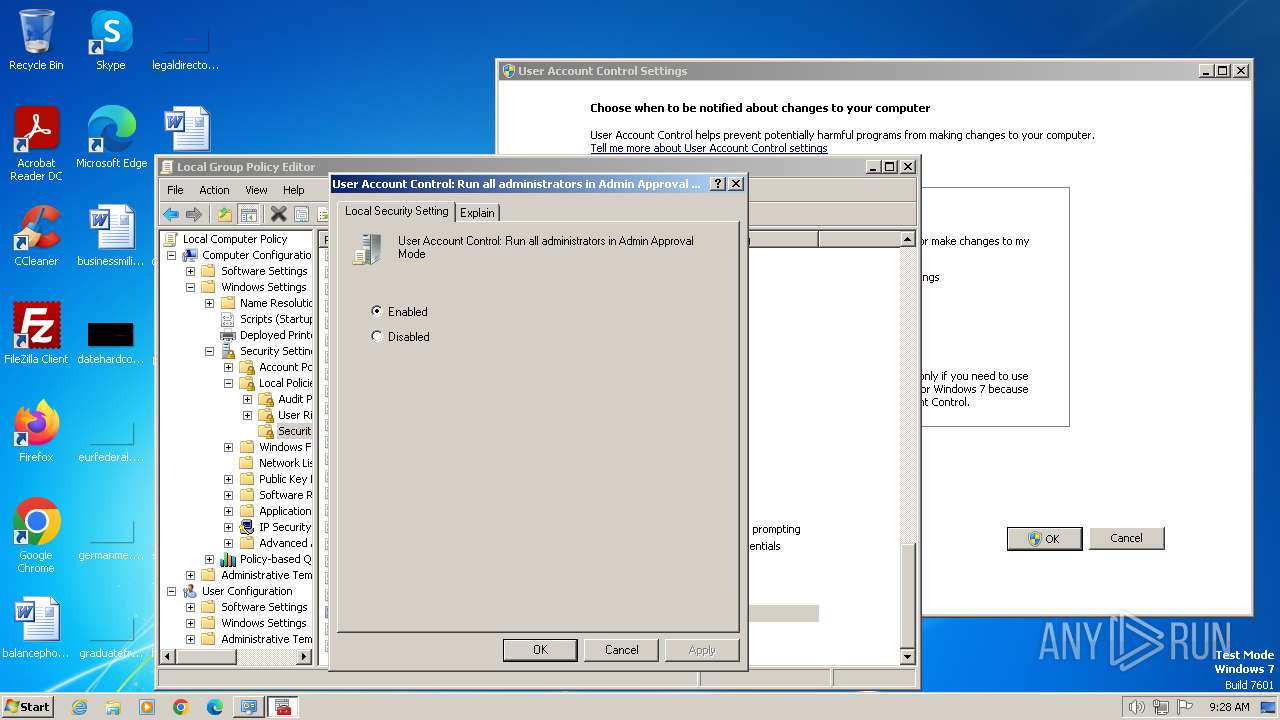
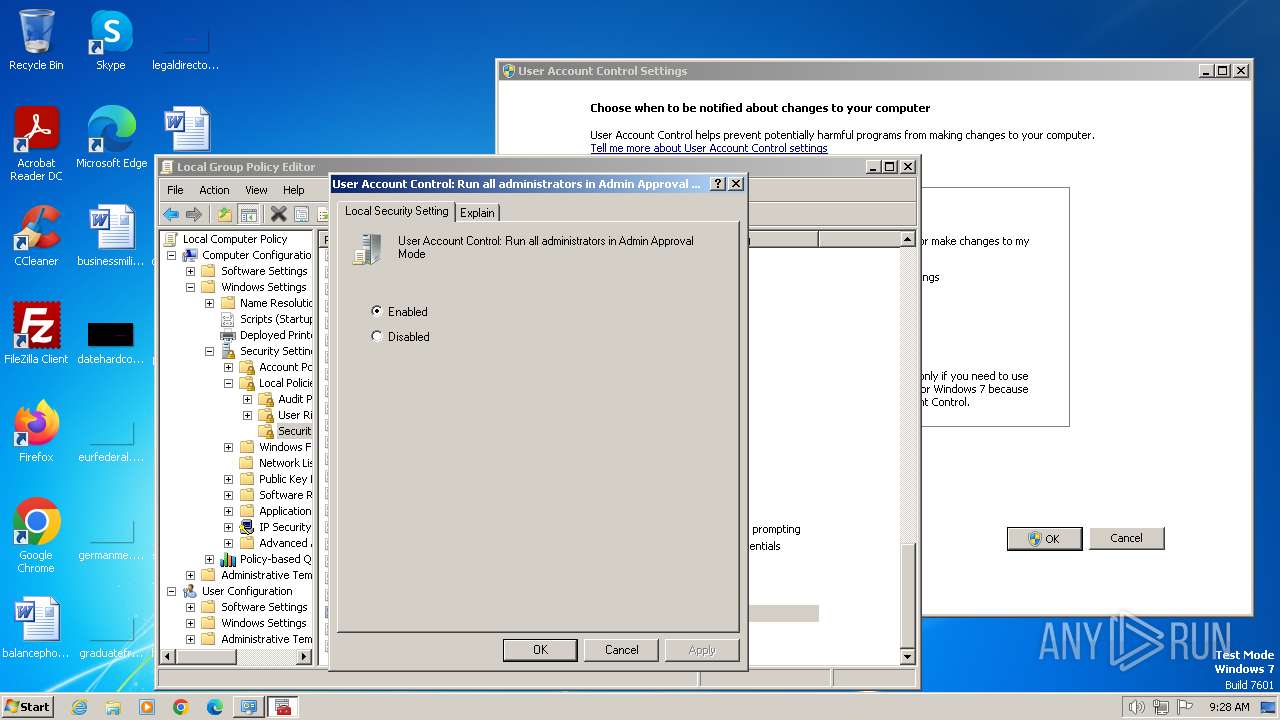
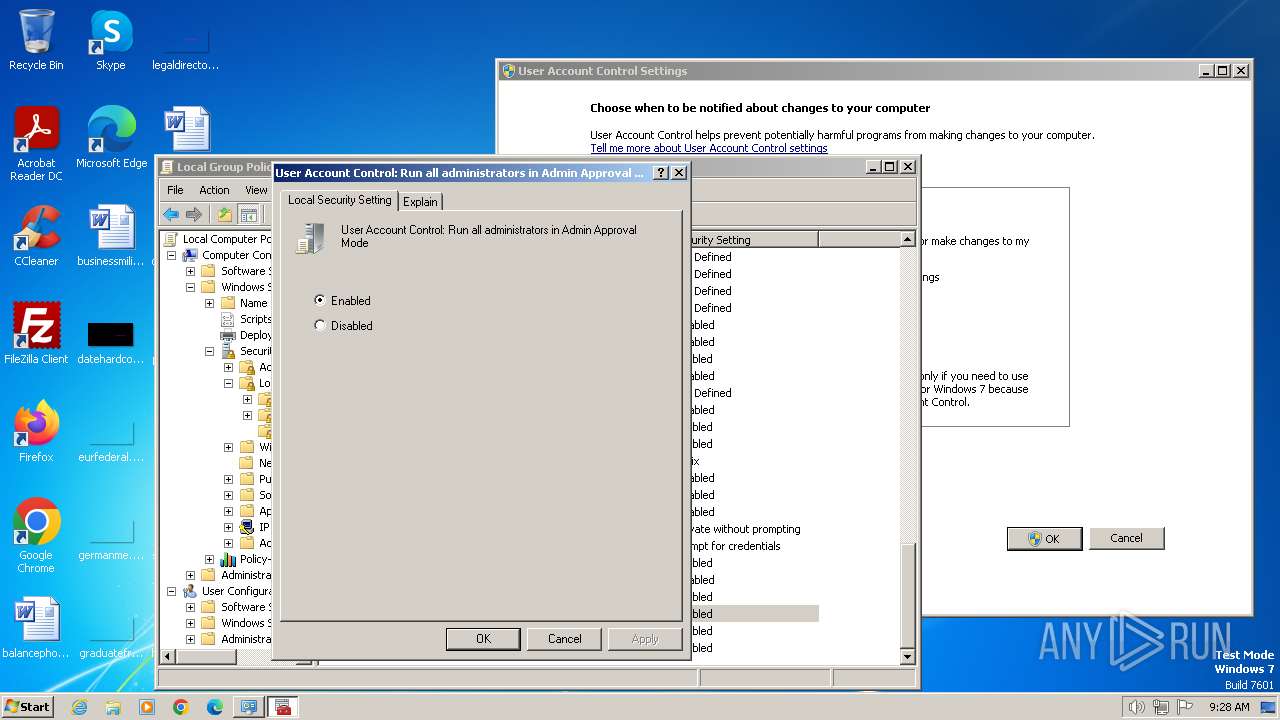
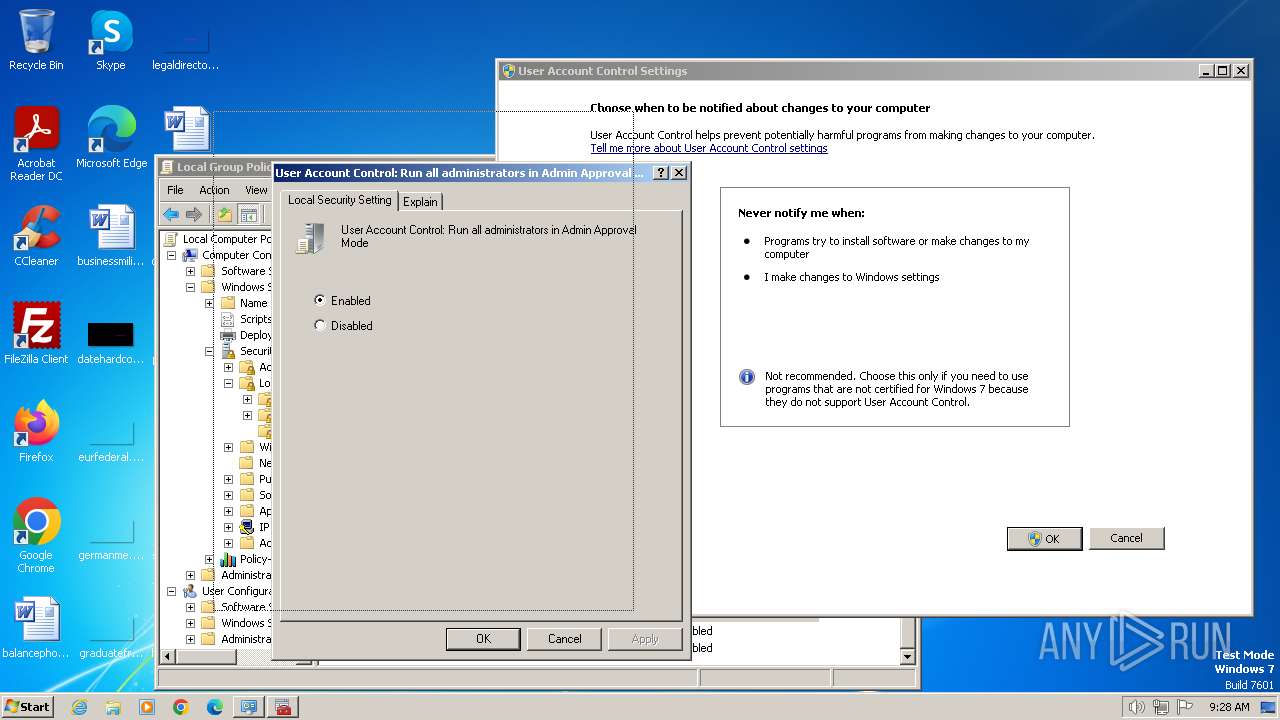
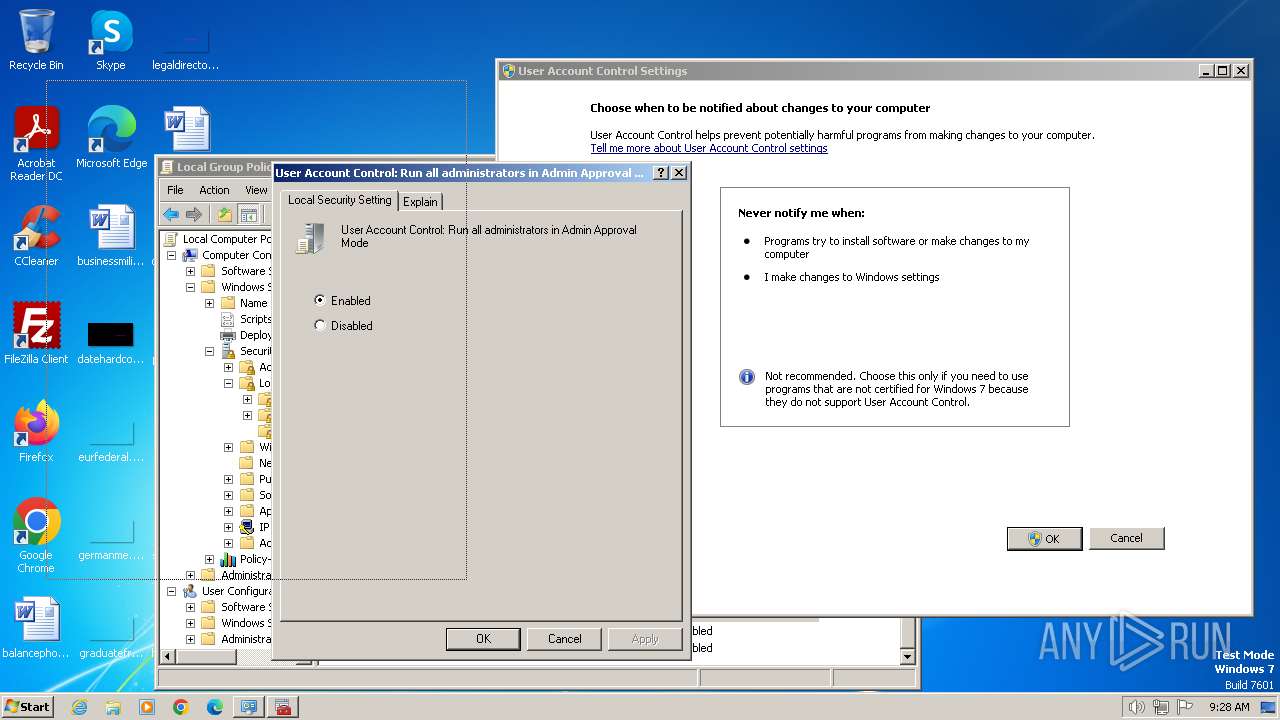
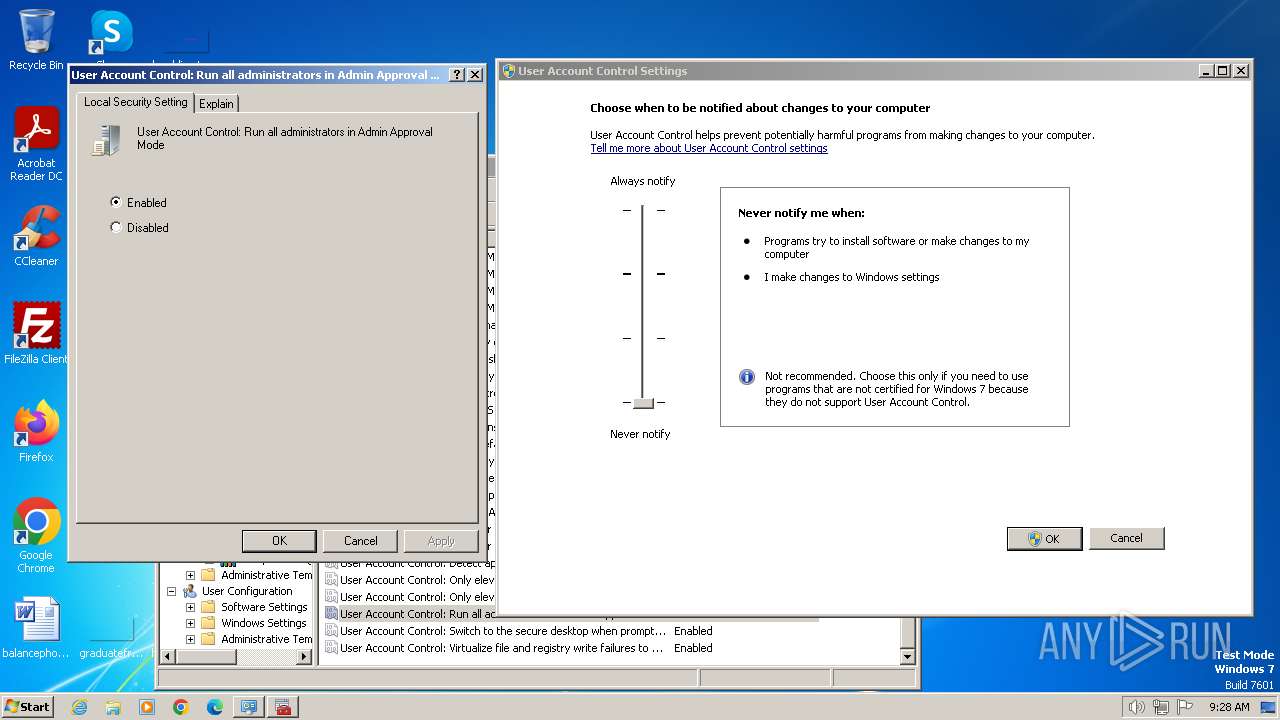
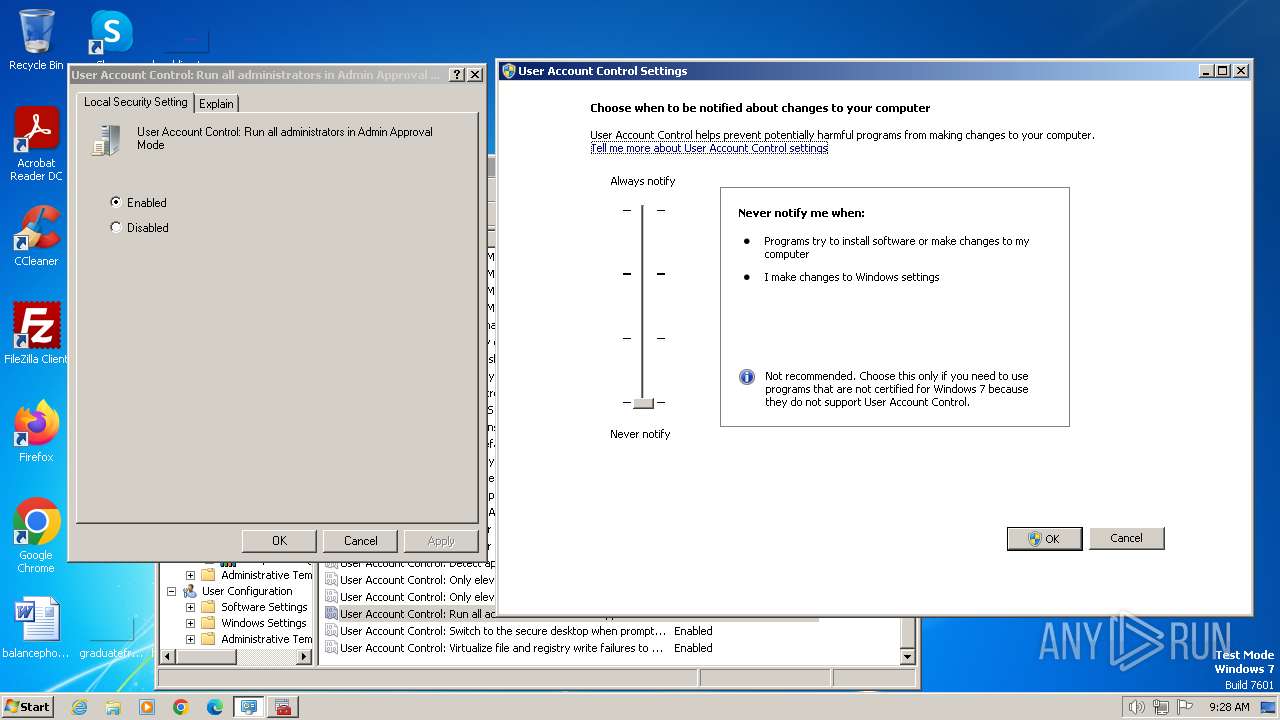
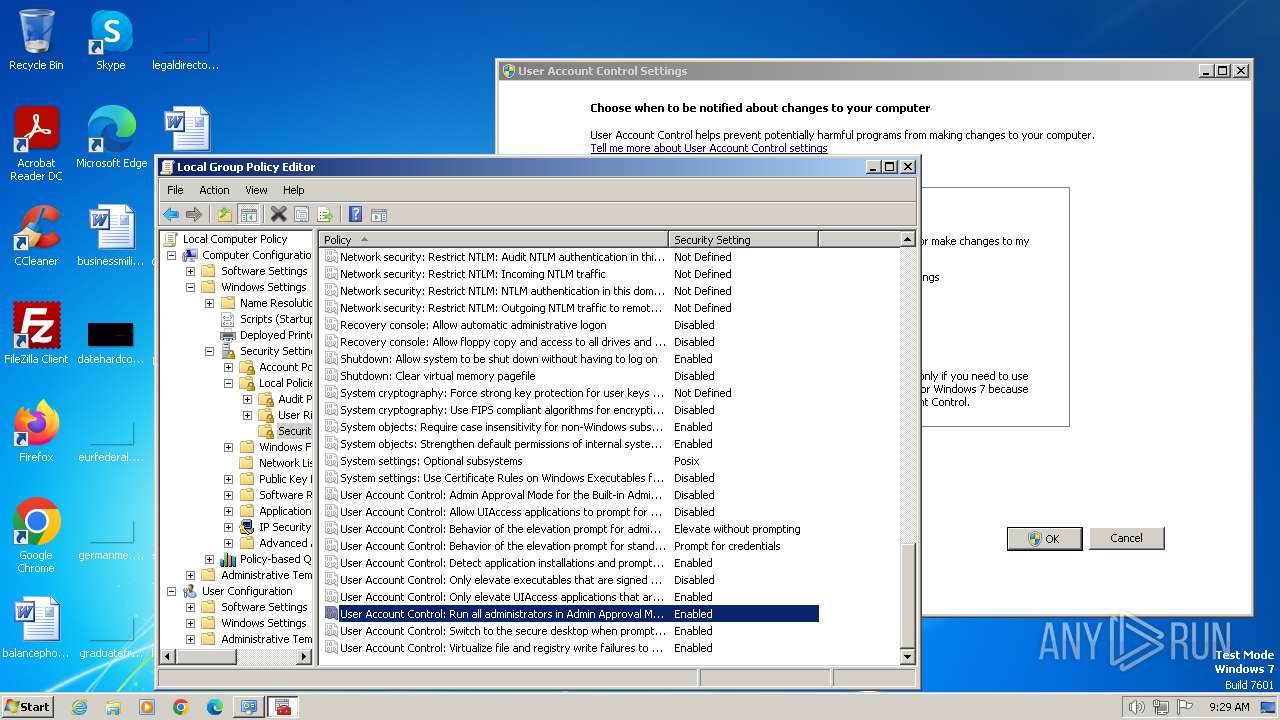
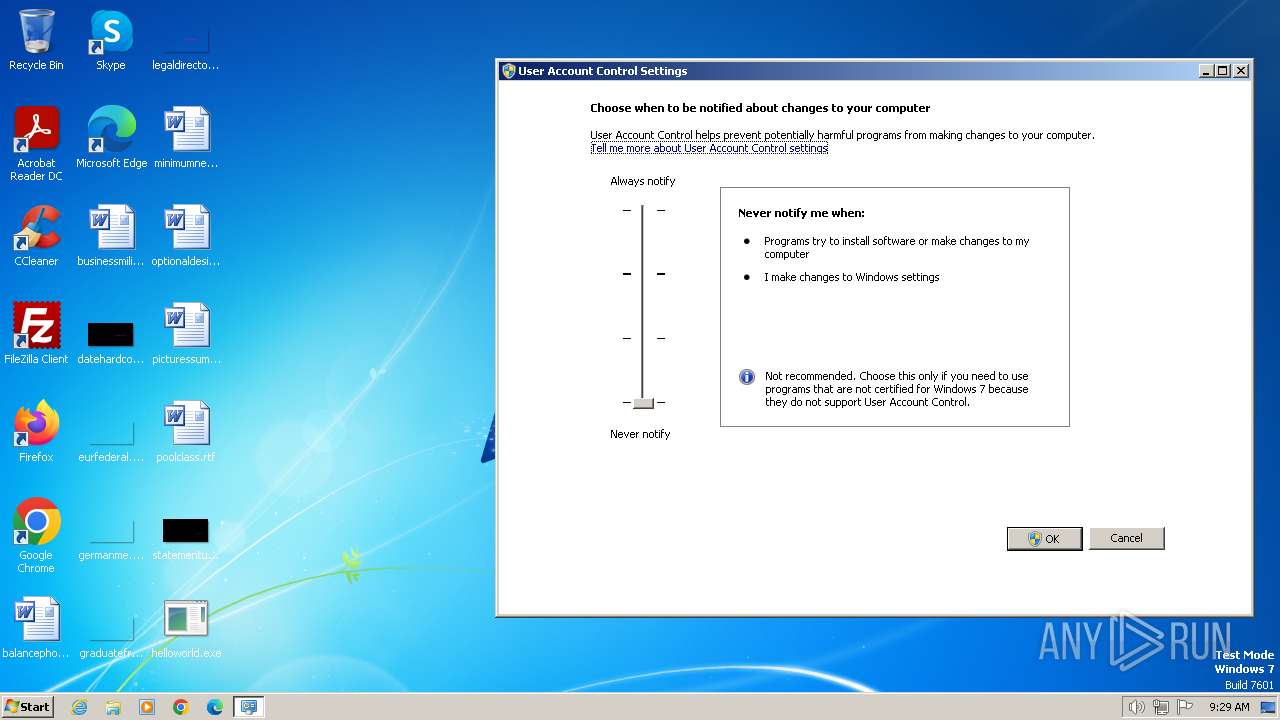
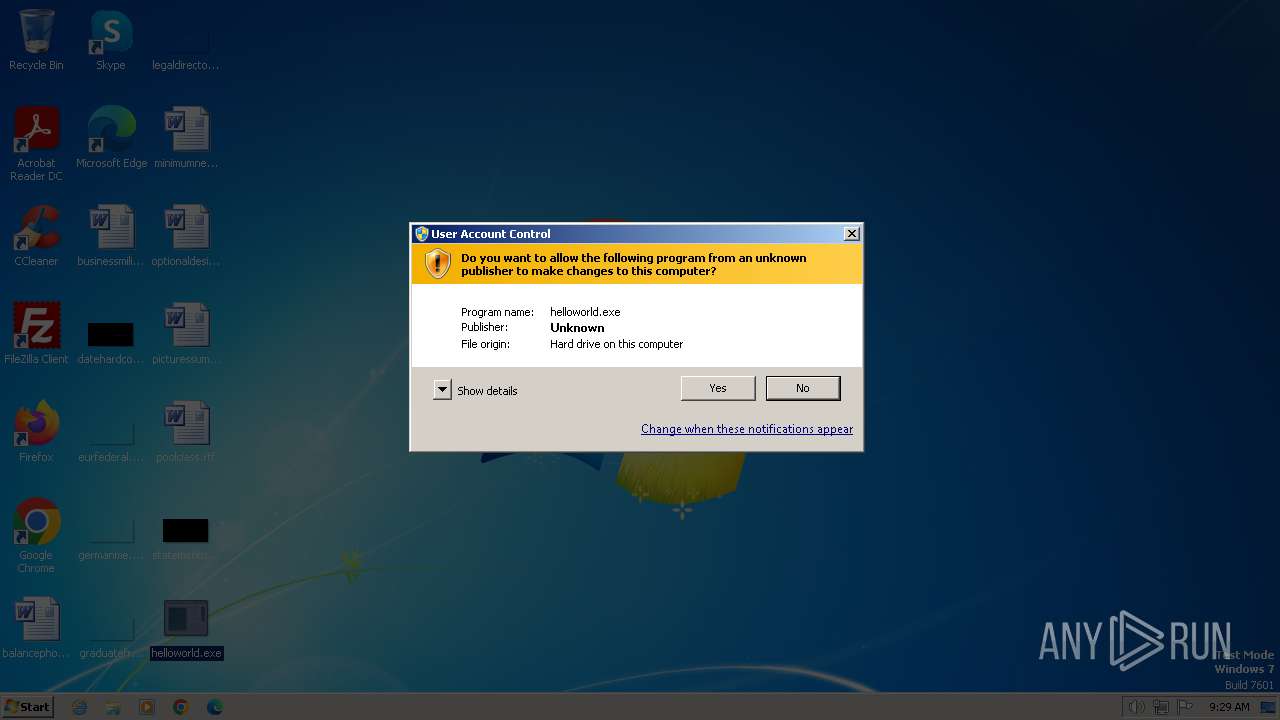
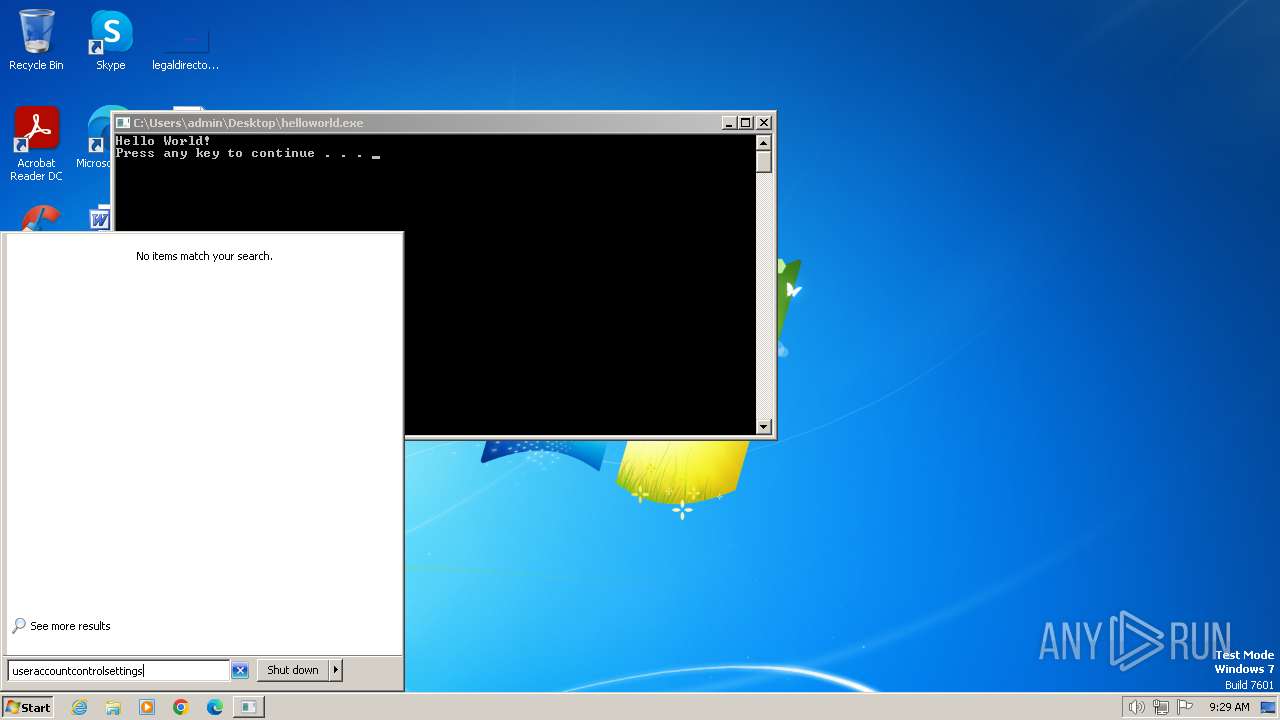
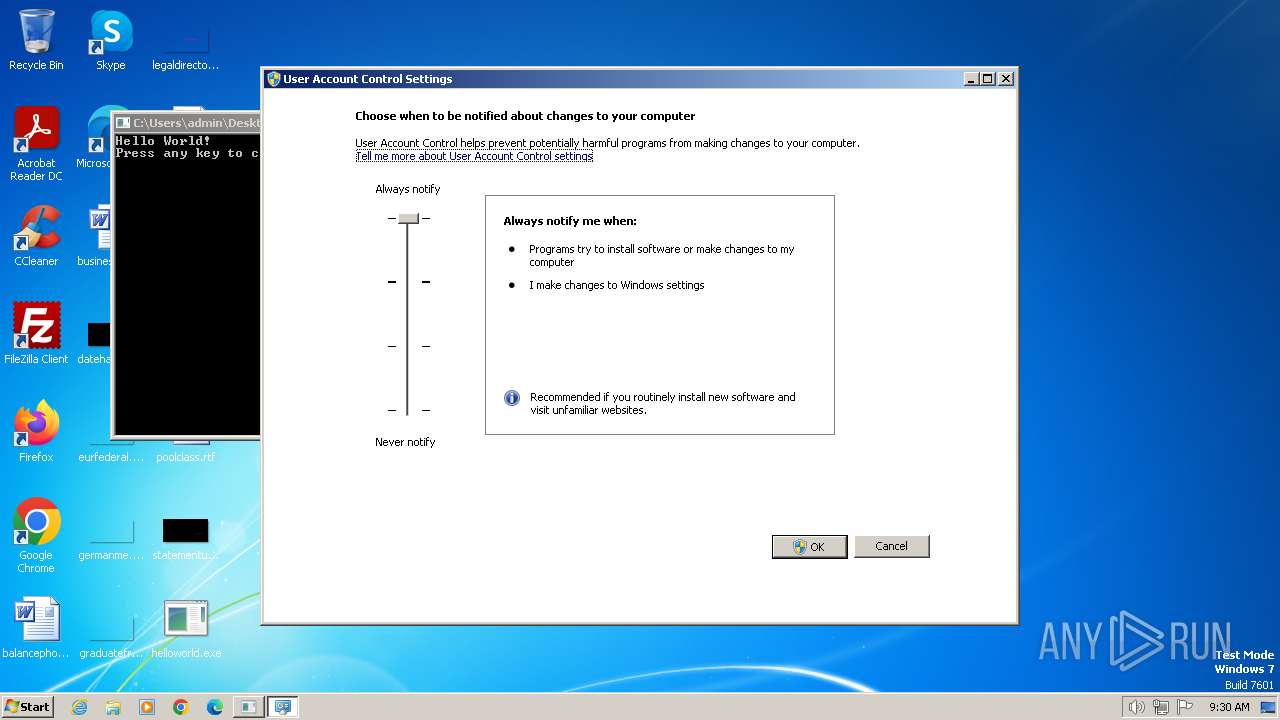
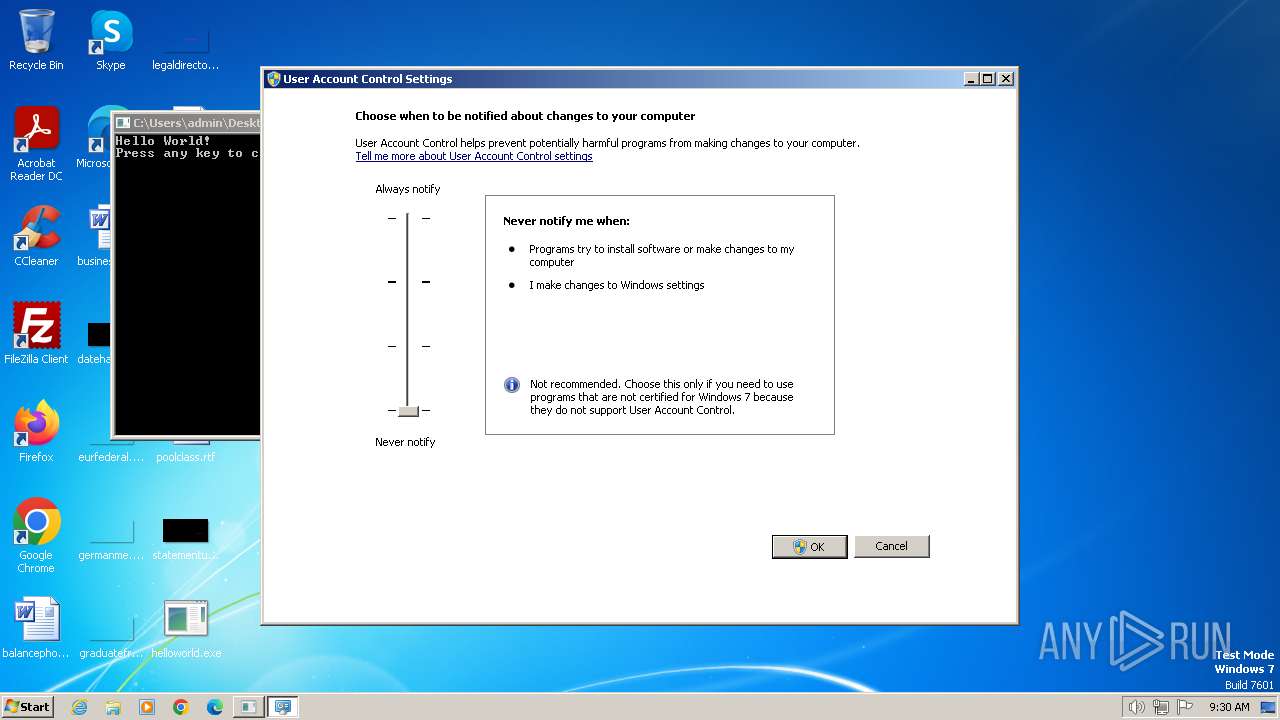
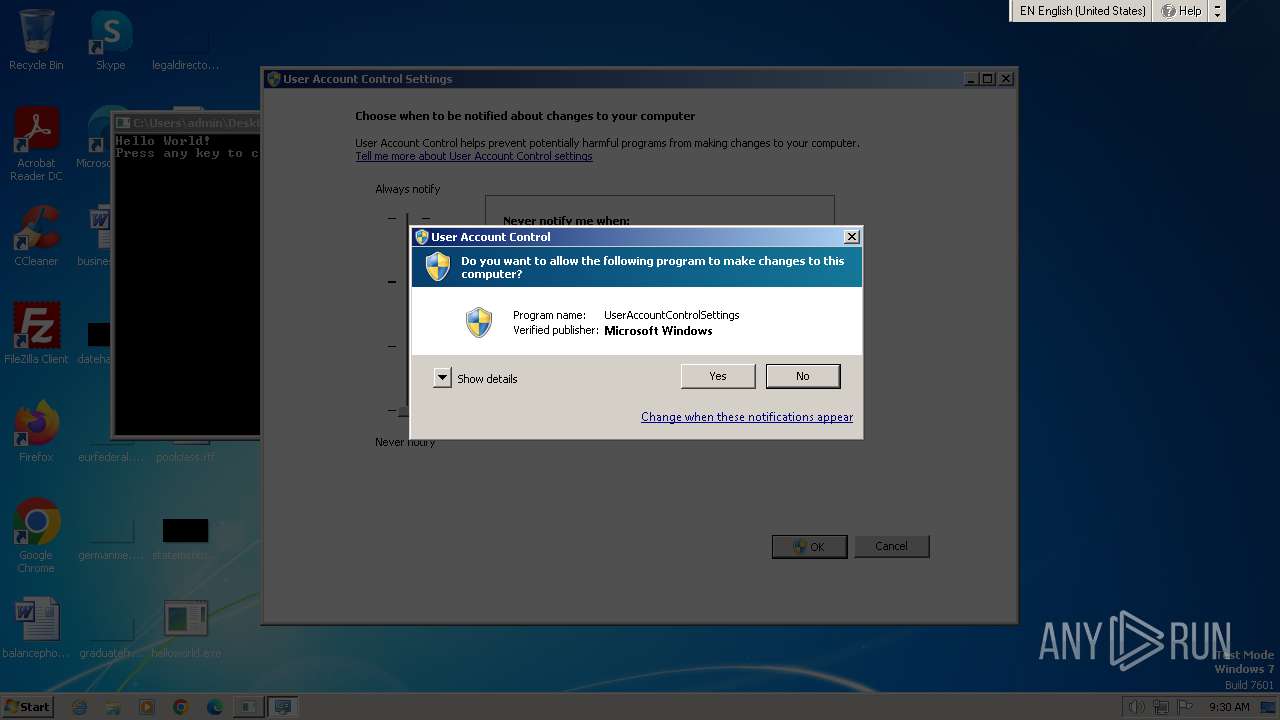
UAC/LUA settings modification
- dllhost.exe (PID: 4020)
- dllhost.exe (PID: 4044)
SUSPICIOUS
Reads the Internet Settings
- mmc.exe (PID: 3912)
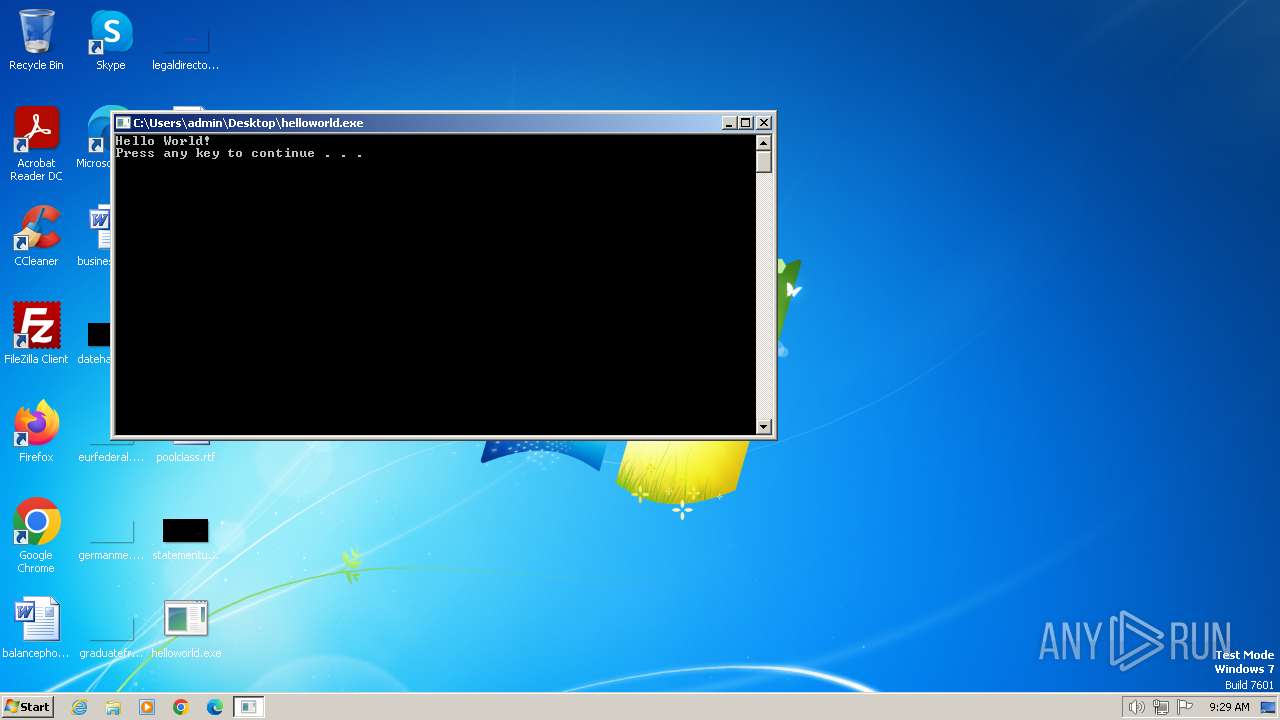
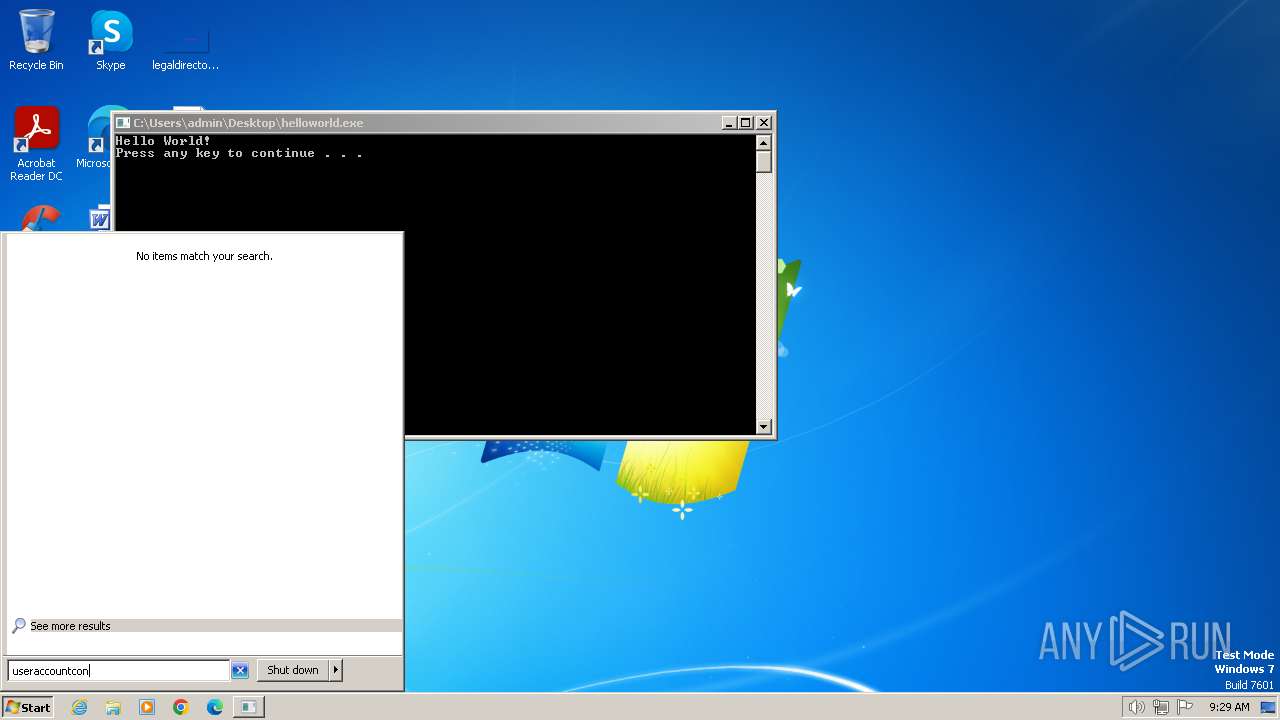
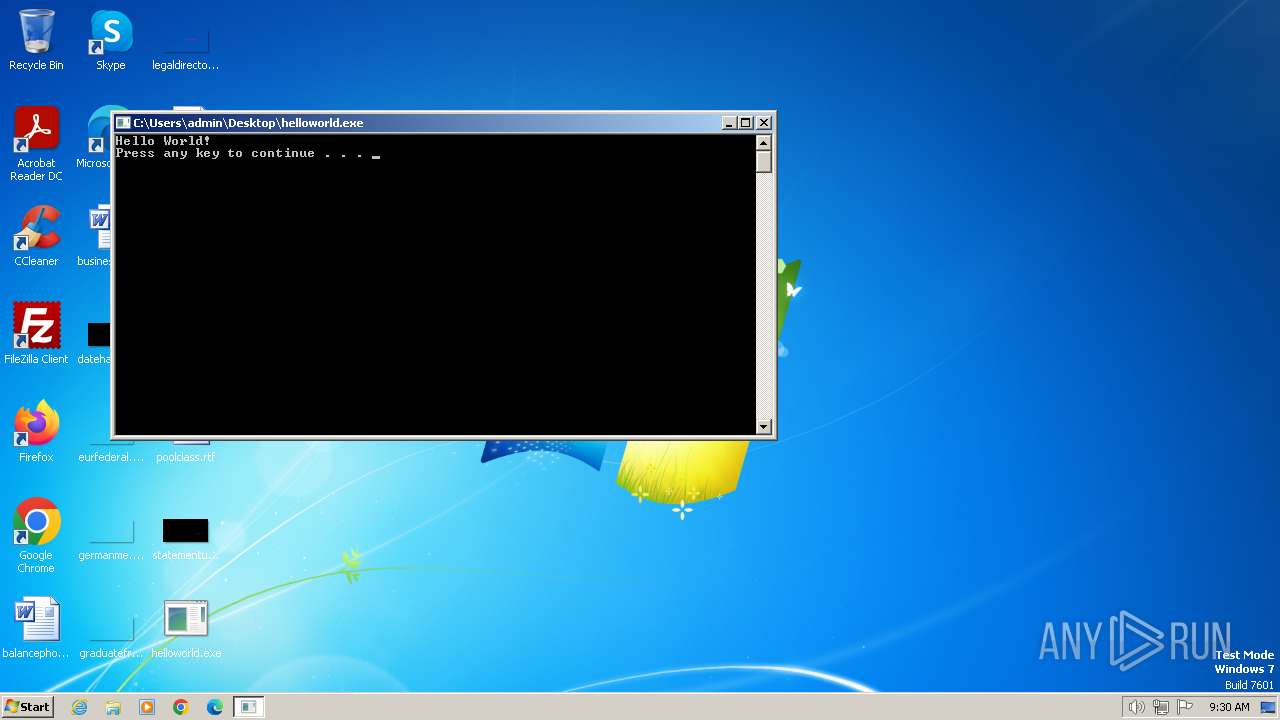
Starts CMD.EXE for commands execution
- helloworld.exe (PID: 3468)
- helloworld.exe (PID: 3684)
Reads Internet Explorer settings
- mmc.exe (PID: 3912)
Reads Microsoft Outlook installation path
- mmc.exe (PID: 3912)
INFO
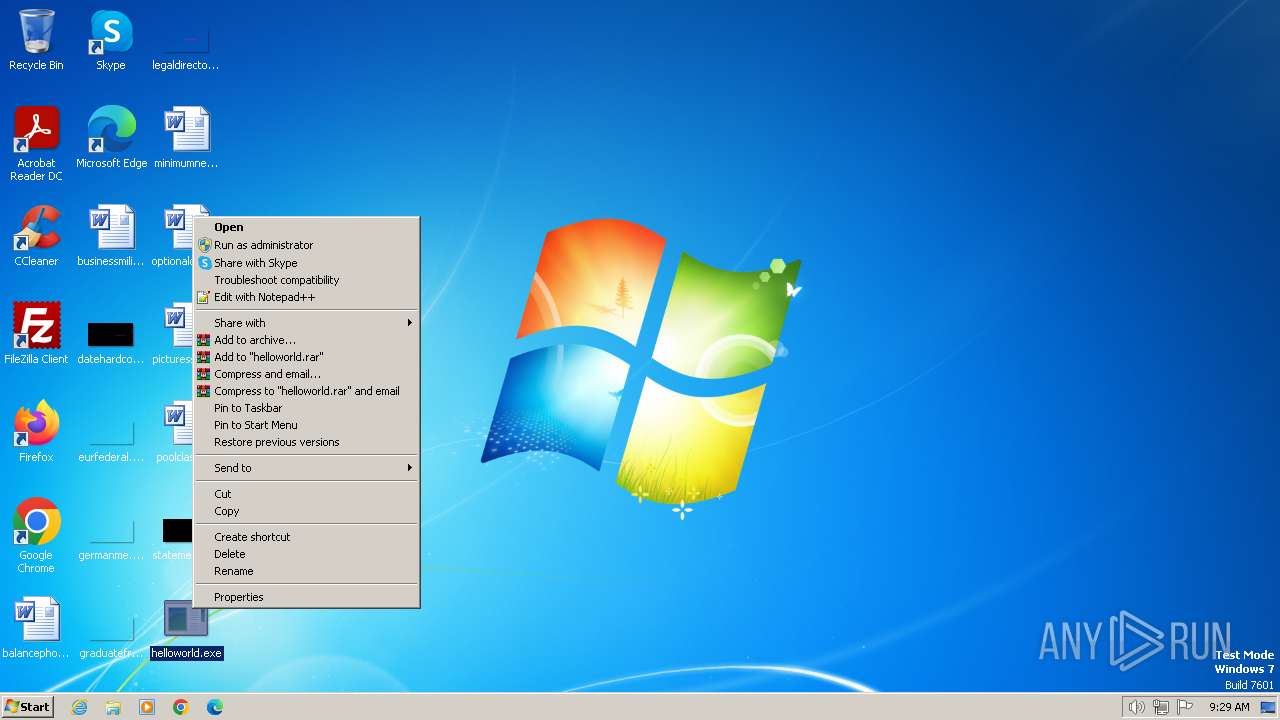
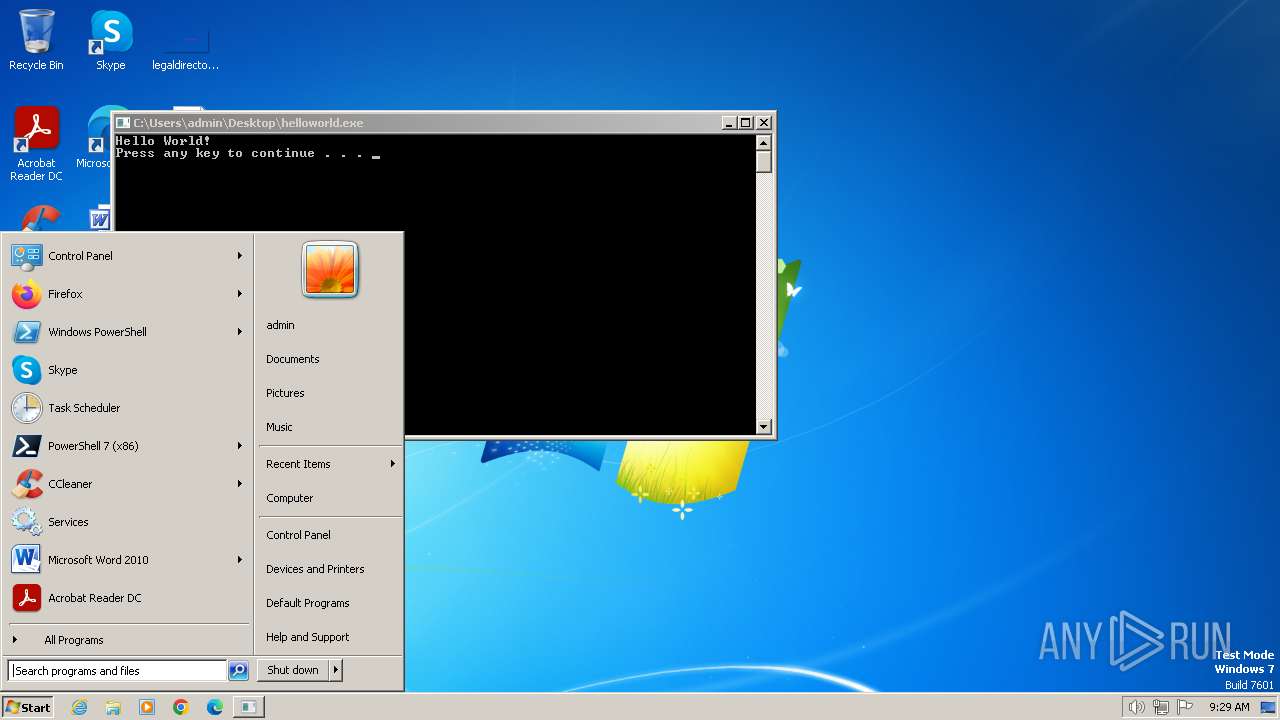
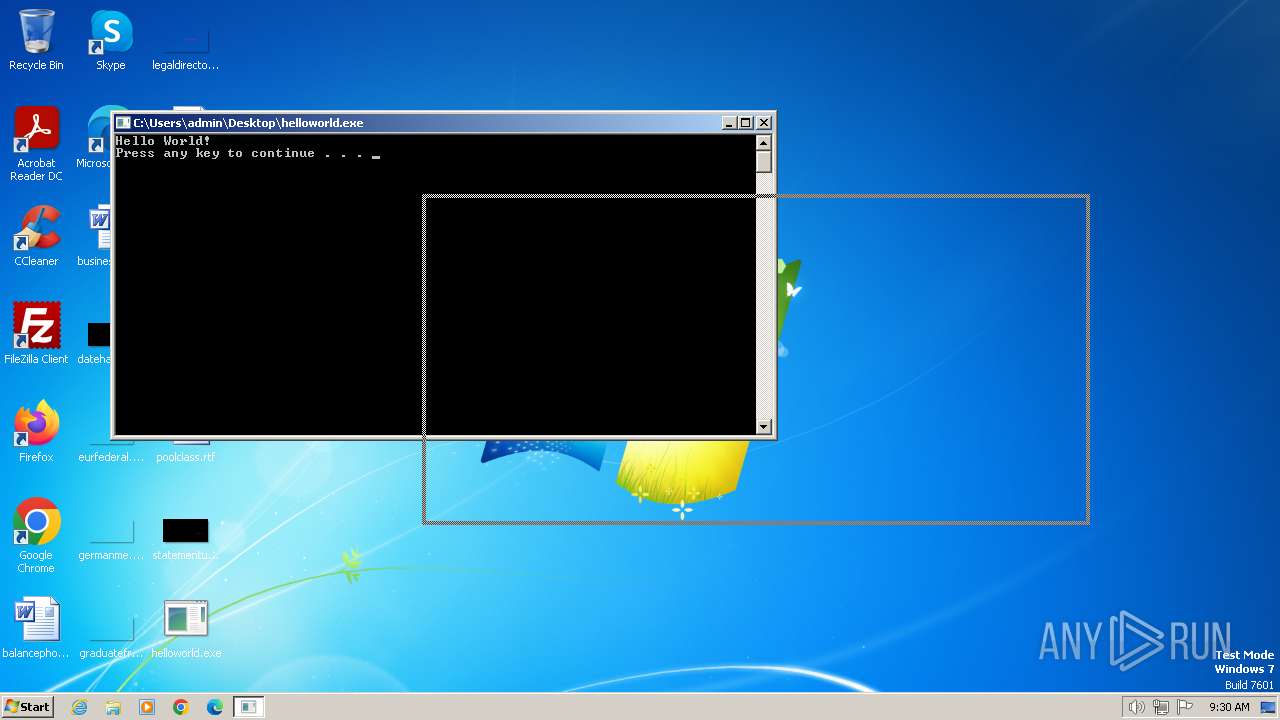
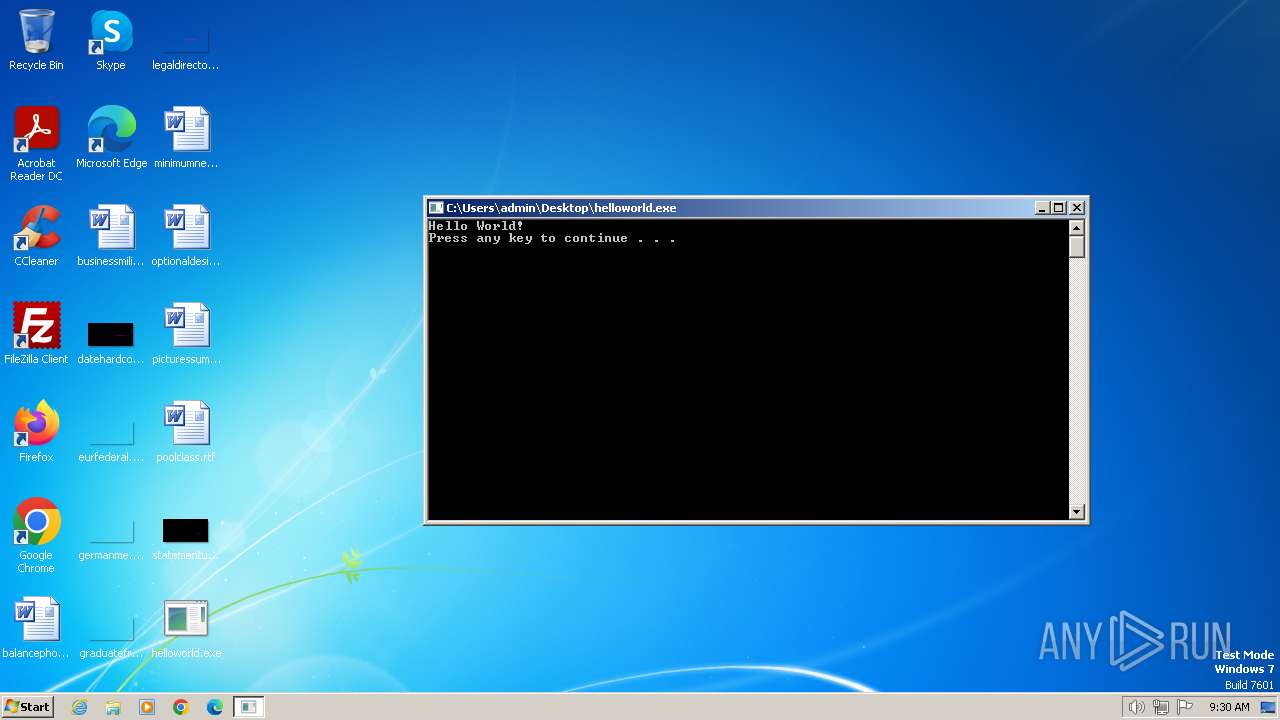
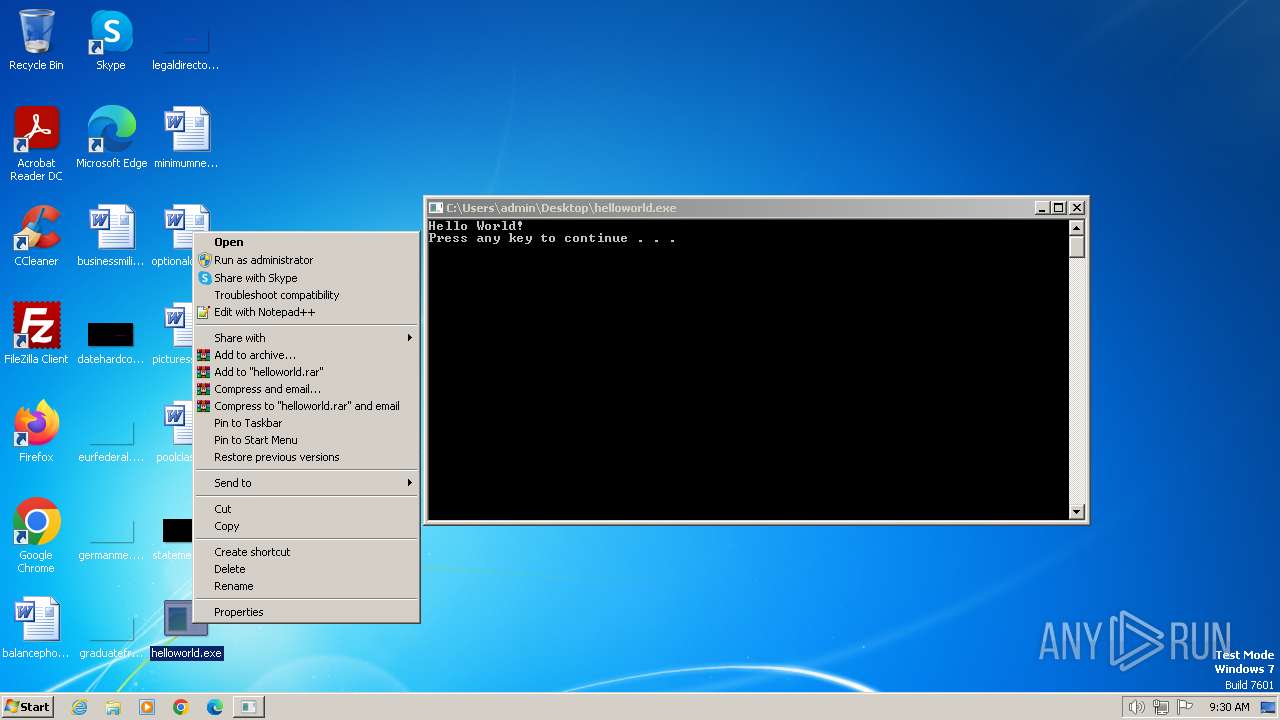
Manual execution by a user
- useraccountcontrolsettings.exe (PID: 2120)
- mmc.exe (PID: 3912)
- helloworld.exe (PID: 3468)
- helloworld.exe (PID: 3684)
- useraccountcontrolsettings.exe (PID: 2836)
- mmc.exe (PID: 2440)
Reads security settings of Internet Explorer
- mmc.exe (PID: 3912)
- dllhost.exe (PID: 2756)
- dllhost.exe (PID: 1388)
Checks supported languages
- helloworld.exe (PID: 3468)
- helloworld.exe (PID: 3684)
Checks transactions between databases Windows and Oracle
- useraccountcontrolsettings.exe (PID: 2836)
- useraccountcontrolsettings.exe (PID: 2120)
Checks proxy server information
- mmc.exe (PID: 3912)
Creates files or folders in the user directory
- mmc.exe (PID: 3912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:11:16 20:07:02+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.37 |
| CodeSize: | 113664 |
| InitializedDataSize: | 52736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4b10 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
73
Monitored processes
15
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Windows\system32\UserAccountControlSettings.exe" /applySettings | C:\Windows\System32\UserAccountControlSettings.exe | dllhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: UserAccountControlSettings Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1216 | "C:\Windows\system32\UserAccountControlSettings.exe" /applySettings | C:\Windows\System32\UserAccountControlSettings.exe | dllhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: UserAccountControlSettings Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1388 | C:\Windows\system32\DllHost.exe /Processid:{06C792F8-6212-4F39-BF70-E8C0AC965C23} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1424 | C:\Windows\system32\cmd.exe /c PAUSE | C:\Windows\System32\cmd.exe | — | helloworld.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2120 | "C:\Windows\system32\useraccountcontrolsettings.exe" | C:\Windows\System32\useraccountcontrolsettings.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: UserAccountControlSettings Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2440 | "C:\Windows\system32\mmc.exe" C:\Windows\system32\gpedit.msc | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2596 | C:\Windows\system32\cmd.exe /c PAUSE | C:\Windows\System32\cmd.exe | — | helloworld.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2756 | C:\Windows\system32\DllHost.exe /Processid:{06C792F8-6212-4F39-BF70-E8C0AC965C23} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2836 | "C:\Windows\system32\useraccountcontrolsettings.exe" | C:\Windows\System32\useraccountcontrolsettings.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: UserAccountControlSettings Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3468 | "C:\Users\admin\Desktop\helloworld.exe" | C:\Users\admin\Desktop\helloworld.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
6 021
Read events
5 605
Write events
394
Delete events
22
Modification events
| (PID) Process: | (3912) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{2F01F9A8-6439-403A-BD15-79613324CDC9}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate\AU |
| Operation: | write | Name: | IncludeRecommendedUpdates |
Value: 0 | |||
| (PID) Process: | (3912) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{2F01F9A8-6439-403A-BD15-79613324CDC9}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate\AU |
| Operation: | write | Name: | AutoInstallMinorUpdates |
Value: 0 | |||
| (PID) Process: | (3912) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{2F01F9A8-6439-403A-BD15-79613324CDC9}Machine\Software\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (3912) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{2F01F9A8-6439-403A-BD15-79613324CDC9}Machine\Software\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableRealtimeMonitoring |
Value: 1 | |||
| (PID) Process: | (3912) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3912) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3912) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3912) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3912) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3912) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3912 | mmc.exe | C:\Windows\System32\GroupPolicy\gpt.ini | text | |
MD5:FED929AE34422010496B5B4A1827A501 | SHA256:2DDA40A266ECA9DDD736701EFA24C6FE186EDD6737DB7BF52BFFE32D614667ED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |