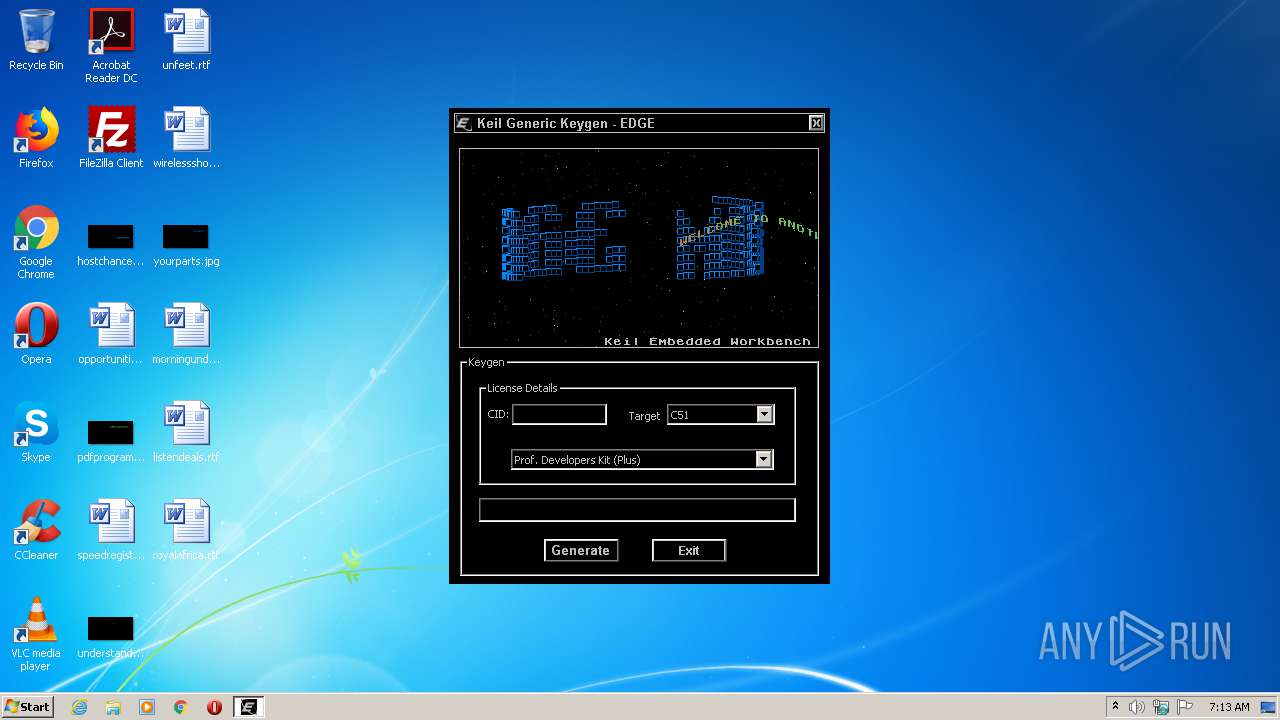
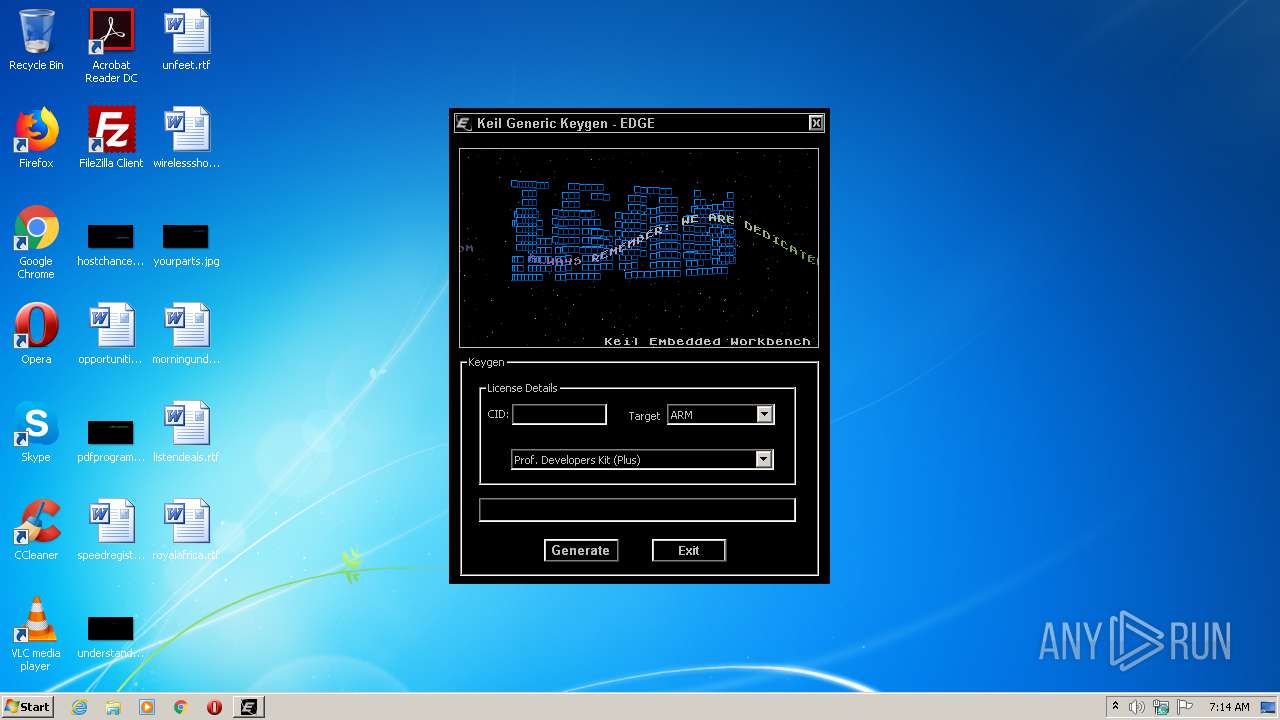
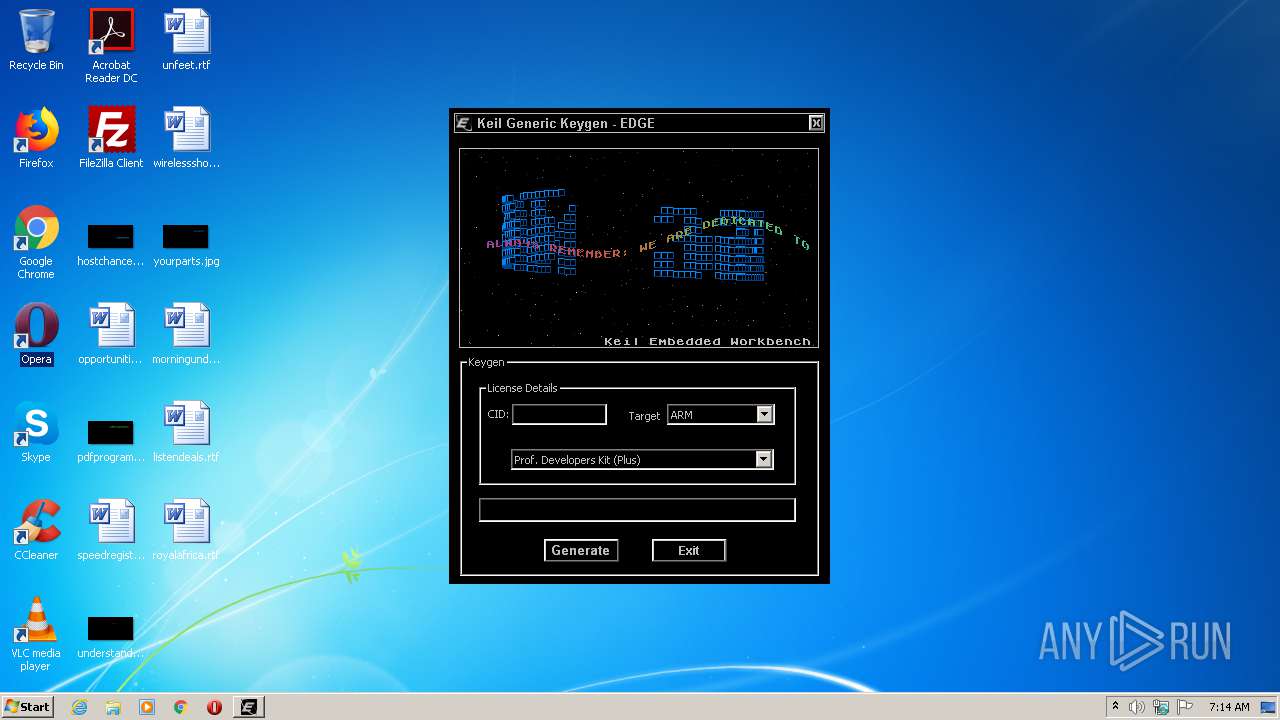
| File name: | KeilMDK5Keygen.exe |
| Full analysis: | https://app.any.run/tasks/6e337313-0eab-44dd-98c8-f3c55406eac1 |
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2021, 07:13:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable |
| MD5: | B71CAB36BDFE1D4EE5B548673AA3D739 |
| SHA1: | C768E4928B6CEA182FD33593899A53B643FF18BC |
| SHA256: | 216E34266FB0FA44A596C1624ECEF633D67E6CB9F522C44C7EE36D0A14DA7806 |
| SSDEEP: | 768:VOF1iS4MUkh19ZrhhjZLTXarlebViVPe76fTi+jDKR:xmvlnp |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
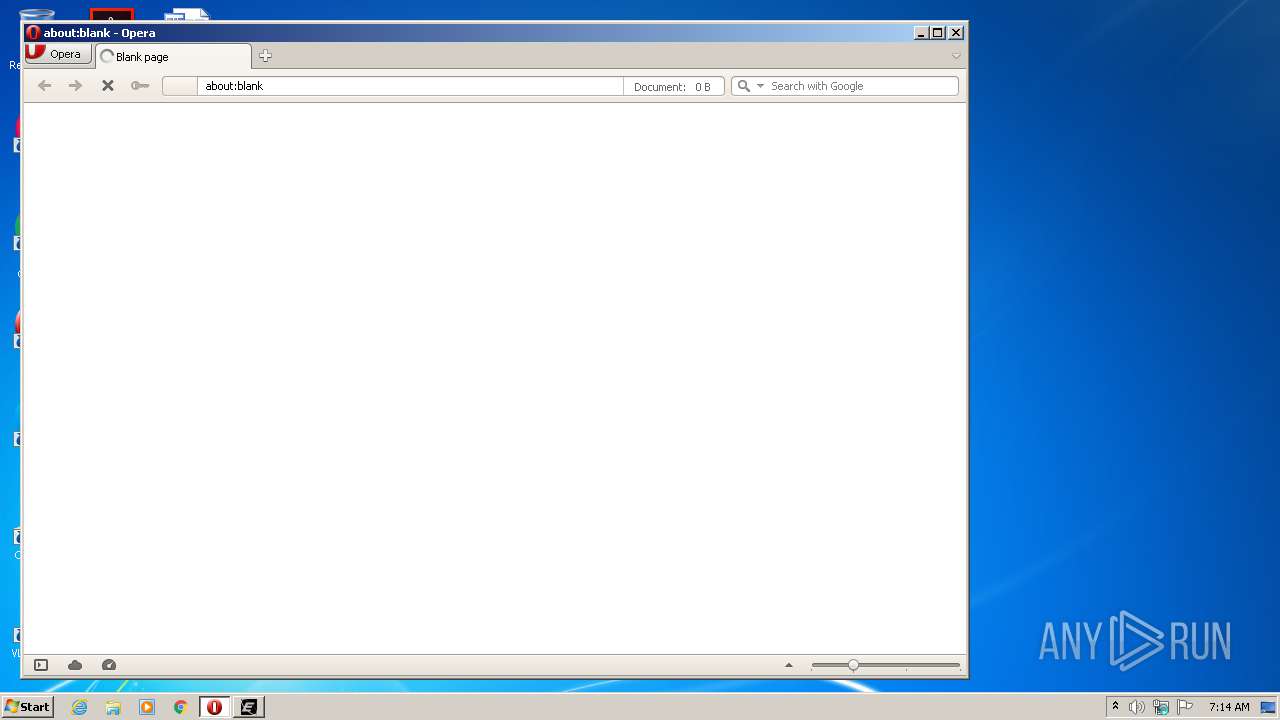
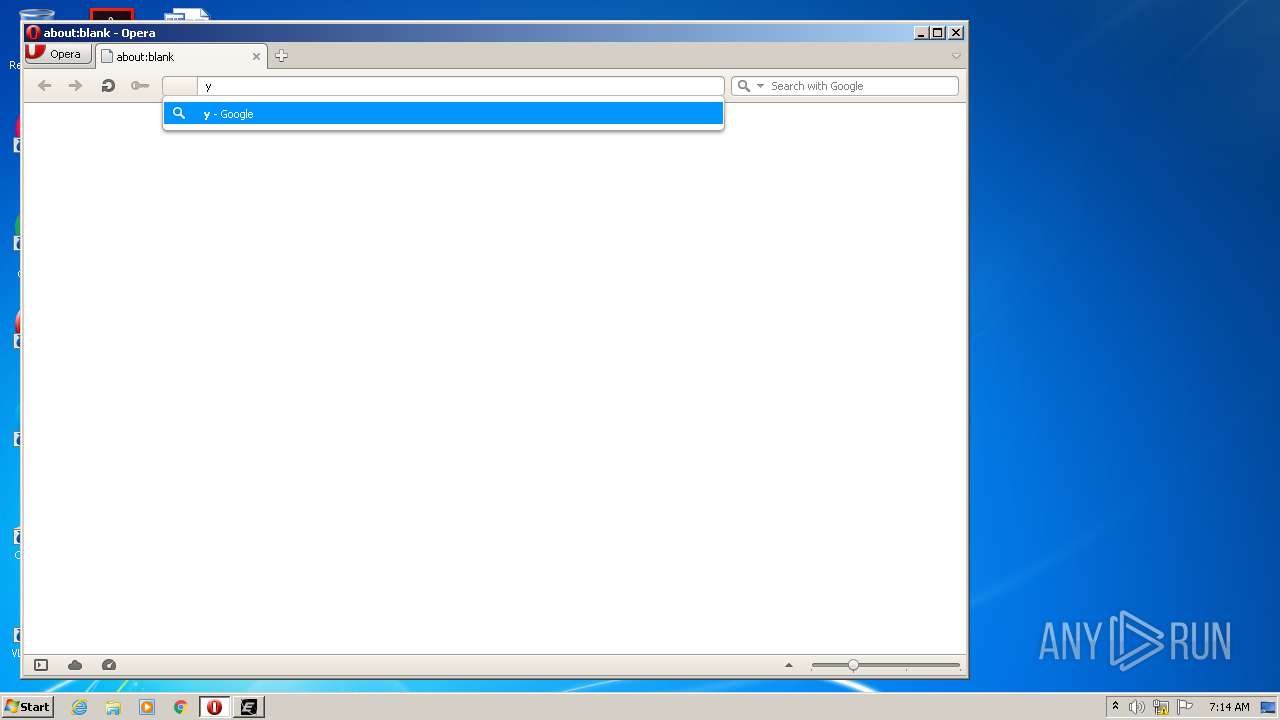
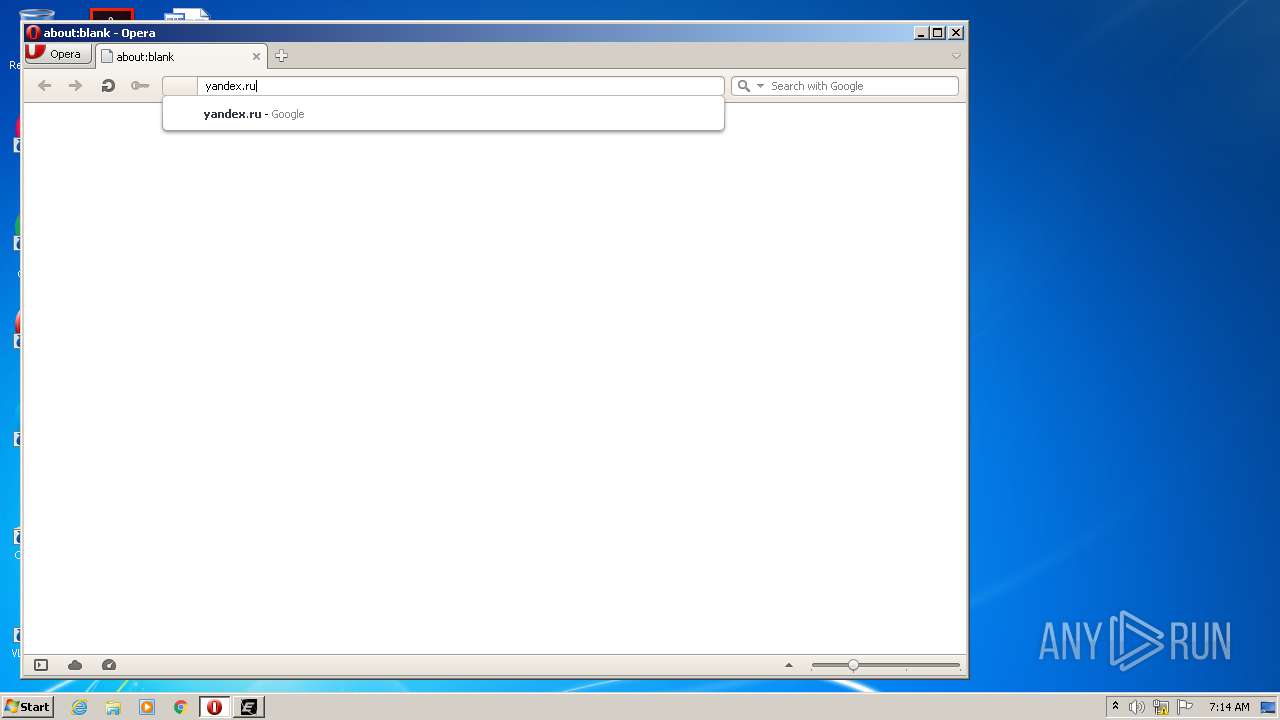
Manual execution by user
- opera.exe (PID: 3264)
Creates files in the user directory
- opera.exe (PID: 3264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2008:02:27 18:42:26+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 20480 |
| InitializedDataSize: | 487424 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5526 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Feb-2008 17:42:26 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x6166 |
| Pages in file: | 0x6272 |
| Relocations: | 0x6172 |
| Size of header: | 0x7375 |
| Min extra paragraphs: | 0x6863 |
| Max extra paragraphs: | 0x4550 |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x014C |
| Checksum: | 0x0001 |
| Initial IP value: | 0xA102 |
| Initial CS value: | 0x47C5 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x010B |
| OEM information: | 0x0006 |
| Address of NE header: | 0x0000000C |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 1 |
| Time date stamp: | 27-Feb-2008 17:42:26 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00080C19 | 0x0007B687 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.86667 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.90871 | 744 | UNKNOWN | Portuguese - Portugal | RT_ICON |
2 | 4.01501 | 296 | UNKNOWN | Portuguese - Portugal | RT_ICON |
105 | 2.16096 | 20 | UNKNOWN | Portuguese - Portugal | RT_GROUP_ICON |
107 | 2.07507 | 20 | UNKNOWN | Portuguese - Portugal | RT_GROUP_ICON |
110 | 2.3961 | 200 | UNKNOWN | Portuguese - Portugal | RT_BITMAP |
111 | 0.988461 | 2510 | UNKNOWN | Portuguese - Portugal | RT_BITMAP |
112 | 0.533073 | 1922 | UNKNOWN | Portuguese - Portugal | RT_BITMAP |
KEYGEN | 3.27919 | 556 | UNKNOWN | Portuguese - Portugal | RT_DIALOG |
TUNE | 4.39558 | 9902 | UNKNOWN | Portuguese - Portugal | RT_RCDATA |
Imports
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
USER32.dll |
WINMM.dll |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Users\admin\AppData\Local\Temp\KeilMDK5Keygen.exe" | C:\Users\admin\AppData\Local\Temp\KeilMDK5Keygen.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3264 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
Total events
205
Read events
147
Write events
58
Delete events
0
Modification events
| (PID) Process: | (3264) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (3264) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
7
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3264 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr5ED5.tmp | — | |
MD5:— | SHA256:— | |||
| 3264 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr5F14.tmp | — | |
MD5:— | SHA256:— | |||
| 3264 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\O3VJMR3MWM0IK4QDMJE4.temp | — | |
MD5:— | SHA256:— | |||
| 3264 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 3264 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3264 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 3264 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
| 3264 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms~RFe6a2f.TMP | binary | |
MD5:— | SHA256:— | |||
| 3264 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\CACHEDIR.TAG | text | |
MD5:E717F92FA29AE97DBE4F6F5C04B7A3D9 | SHA256:5BBD5DCBF87FD8CD7544C522BADF22A2951CF010AD9F25C40F9726F09EA2B552 | |||
| 3264 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opicacrt6.dat | binary | |
MD5:82F1A2B1176A5ECC457D32301E2AD833 | SHA256:A783052804DD4C232BE2ED3DC00C430CB67A20370890E235562ED2B27B5A602E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
11
DNS requests
4
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3264 | opera.exe | GET | — | 77.88.55.77:80 | http://yandex.ru/ | RU | — | — | whitelisted |
3264 | opera.exe | GET | 200 | 216.58.208.110:80 | http://clients1.google.com/complete/search?q=yandex&client=opera-suggest-omnibox&hl=de | US | text | 101 b | whitelisted |
3264 | opera.exe | GET | 200 | 216.58.208.110:80 | http://clients1.google.com/complete/search?q=yan&client=opera-suggest-omnibox&hl=de | US | text | 118 b | whitelisted |
3264 | opera.exe | GET | 200 | 216.58.208.110:80 | http://clients1.google.com/complete/search?q=yand&client=opera-suggest-omnibox&hl=de | US | text | 109 b | whitelisted |
3264 | opera.exe | GET | 400 | 82.145.216.16:80 | http://sitecheck2.opera.com/?host=yandex.ru&hdn=eH1ae1xR%2ByqwDNtlH/6FeQ== | unknown | html | 150 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3264 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3264 | opera.exe | 216.58.208.110:80 | clients1.google.com | Google Inc. | US | whitelisted |
— | — | 77.88.55.77:80 | yandex.ru | YANDEX LLC | RU | whitelisted |
— | — | 82.145.216.16:80 | sitecheck2.opera.com | Opera Software AS | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
clients1.google.com |
| whitelisted |
yandex.ru |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3264 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3264 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3264 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3264 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
— | — | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
— | — | Potentially Bad Traffic | ET INFO TLS Handshake Failure |