| download: | index.html |
| Full analysis: | https://app.any.run/tasks/175dc6af-8846-4e6a-8e61-d75355c83567 |
| Verdict: | No threats detected |
| Analysis date: | October 28, 2019, 17:21:37 |
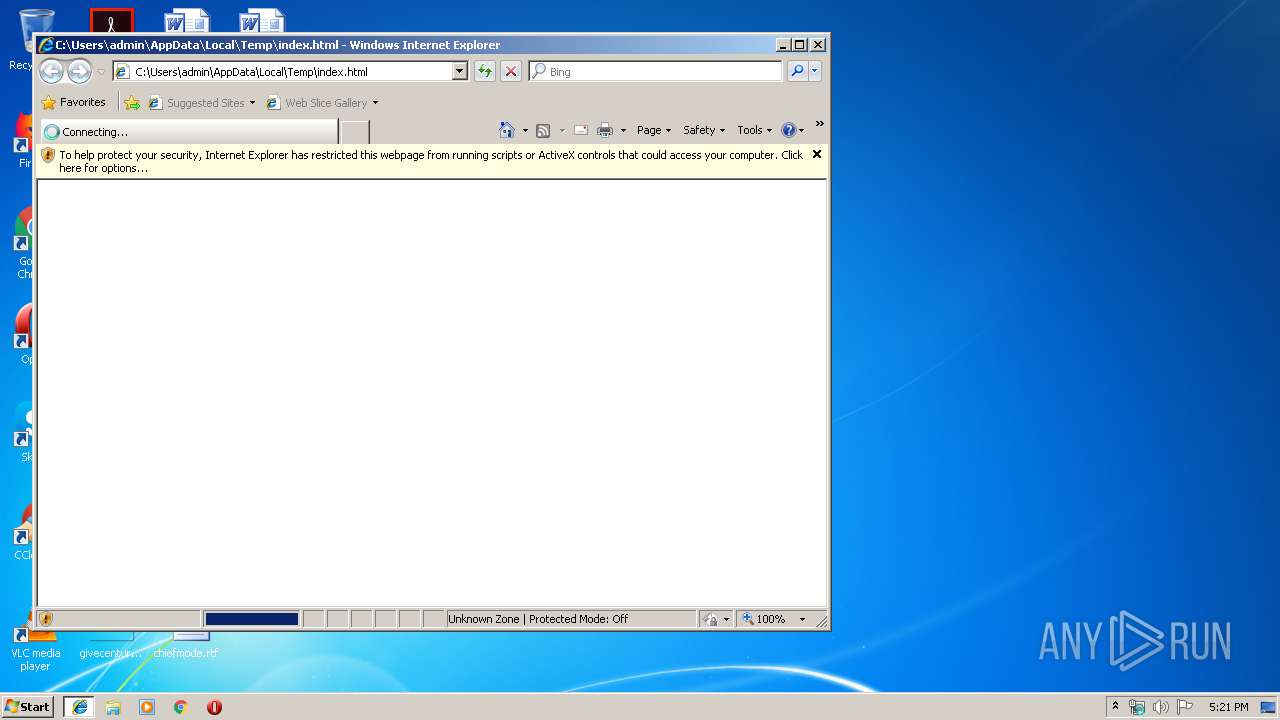
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with CRLF, LF line terminators |
| MD5: | 4C7B954924F497F5E61772EB24D18652 |
| SHA1: | D0DAA9113D32918B437F04E26C1094740BB95861 |
| SHA256: | 215C59F4F005DB579D96FE3739491FFDF27DD1955DC4ACCEF58798178A6F104B |
| SSDEEP: | 768:9VvxpLrJbm0e1/+IawSCztlAxqEa7N5JRVV4mvgdCuPtmgveCfXsGevLEKwceVKd:9bm0e1/MwSalpES5fVV4mvo7PtmgvFfY |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
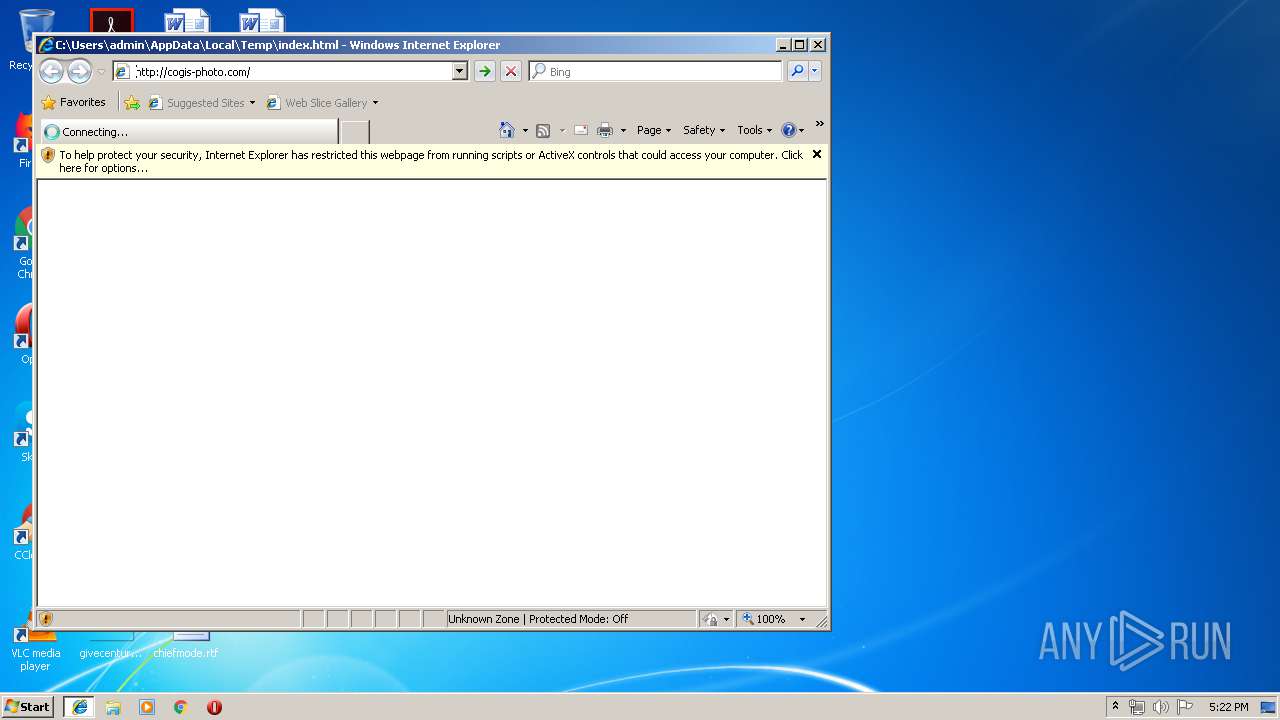
Changes internet zones settings
- iexplore.exe (PID: 2784)
Application launched itself
- iexplore.exe (PID: 2784)
Reads Internet Cache Settings
- iexplore.exe (PID: 2856)
Reads internet explorer settings
- iexplore.exe (PID: 2856)
- iexplore.exe (PID: 2364)
Creates files in the user directory
- iexplore.exe (PID: 2784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| HTTPEquivXUACompatible: | IE=edge,chrome=1 |
|---|---|
| viewport: | width=device-width, initial-scale=1 |
| appleMobileWebAppCapable: | yes |
| appleMobileWebAppStatusBarStyle: | black |
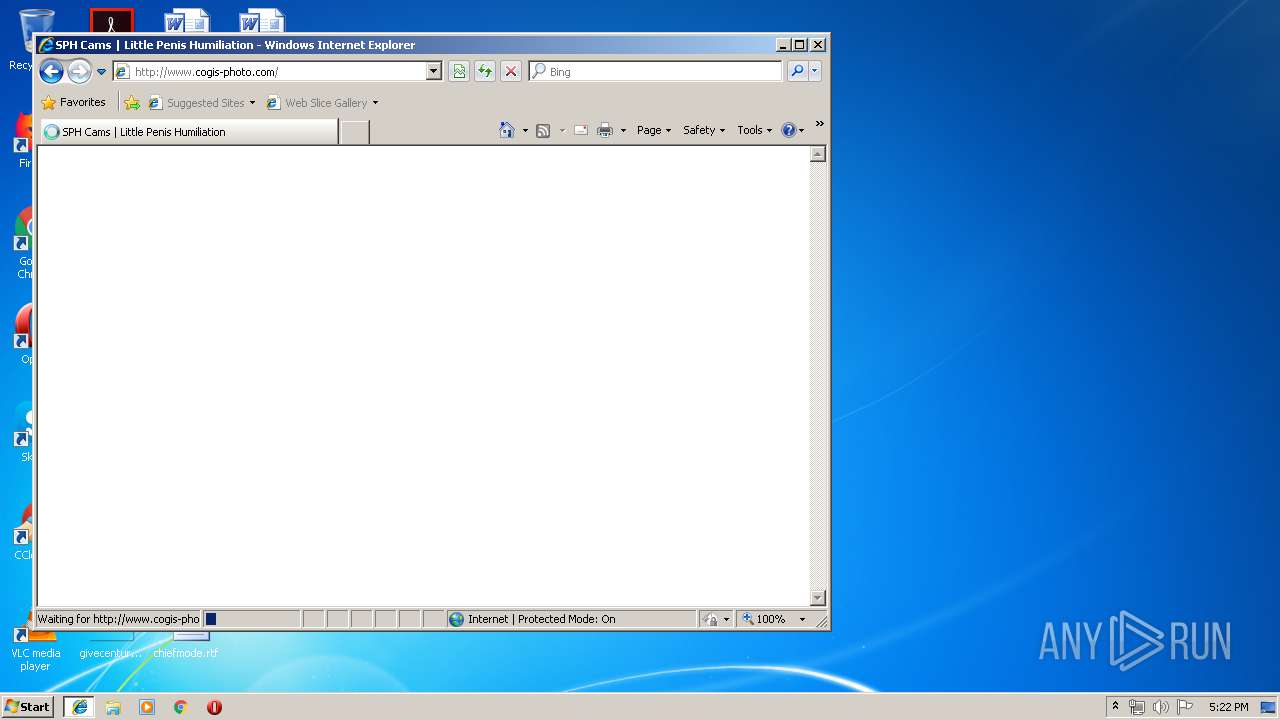
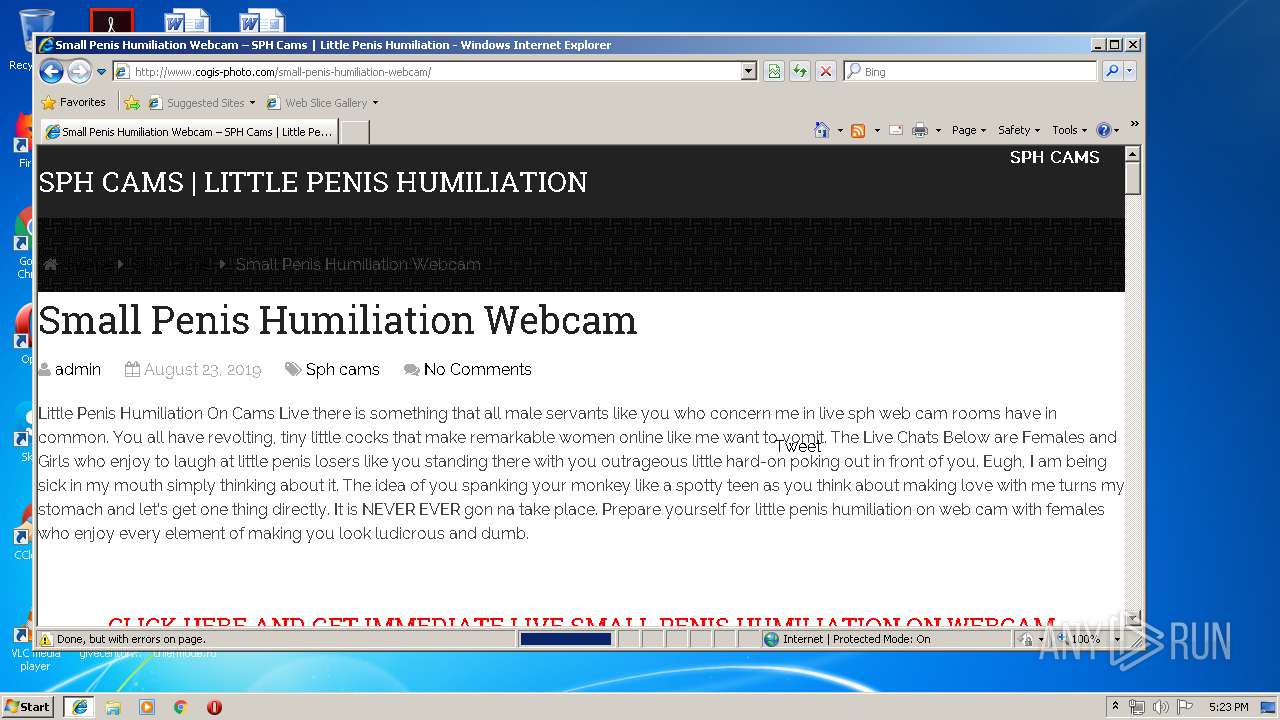
| Title: | SPH Cams | Little Penis Humiliation |
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2364 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2784 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2784 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2856 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2784 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
589
Read events
489
Write events
97
Delete events
3
Modification events
| (PID) Process: | (2784) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2784) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2784) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2784) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2784) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2784) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2784) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {7018DAC7-F9A7-11E9-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2784) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2784) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2784) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070A0001001C00110015003800BC00 | |||
Executable files
0
Suspicious files
6
Text files
52
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2784 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2784 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2784 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF53BA0C5FC54DCF0A.TMP | — | |
MD5:— | SHA256:— | |||
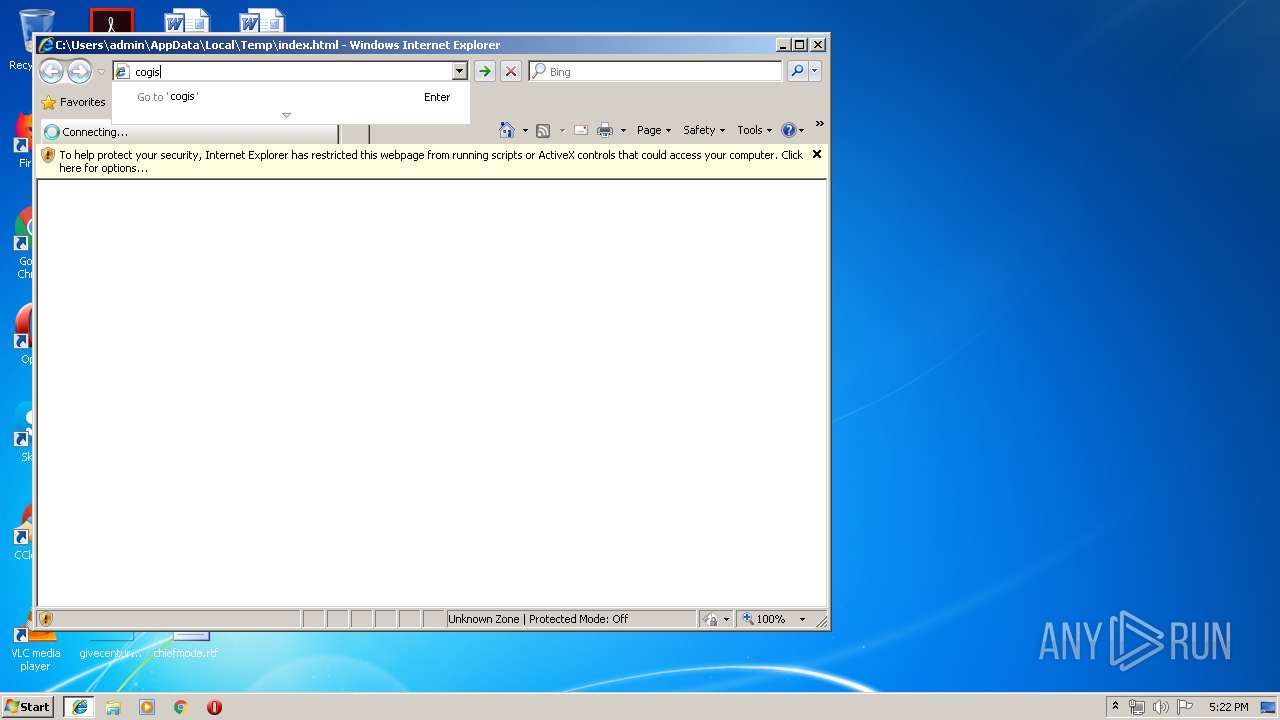
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\AKAD0I72\cogis-photo_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 2784 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:9FF5AF3A97ACFC207936369F20267CF2 | SHA256:A06C65CA4C53B115F04D574B01F1474FC30E79F1D40DC1B5F4B5FD680B1970D1 | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:D0299A54947FE57FDFCC8ED27A2E48B3 | SHA256:9B0FDC4BFBDF077C700A52605594318C7922E9998FE417837A2FA486E37534C1 | |||
| 2784 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{7018DAC8-F9A7-11E9-AB41-5254004A04AF}.dat | binary | |
MD5:9D7149F95652F323C788C9069D8929CC | SHA256:97C8EE930C68D03DB7963BC5C01336C2FB9DB87D9BB4FEDFCE9B4045D2711794 | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\AKAD0I72\cogis-photo_com[1].htm | html | |
MD5:22D4ECA3F389A37124AC90F00EEBA8F8 | SHA256:EDD81960DF6C35376E54CE0D61D082B18F62D7AEFB1255CC03FA716D0C66EF81 | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\AKAD0I72\css[1].txt | text | |
MD5:2D4CF00CF77DC0A205ECC1E5F7ABEC1E | SHA256:9D5C7479262EA7E2D125EA40659B35A23362DF5F2B2EC5F02D225051FF71DE19 | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\AKAD0I72\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
28
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2856 | iexplore.exe | GET | 200 | 143.95.39.117:80 | http://www.cogis-photo.com/ | US | html | 7.82 Kb | unknown |
2856 | iexplore.exe | GET | 200 | 143.95.39.117:80 | http://www.cogis-photo.com/wp-includes/css/dist/block-library/style.min.css | US | text | 5.76 Kb | unknown |
2856 | iexplore.exe | GET | 200 | 143.95.39.117:80 | http://www.cogis-photo.com/wp-content/themes/mts_schema/fonts/fontawesome-webfont.eot? | US | eot | 67.2 Kb | unknown |
2856 | iexplore.exe | GET | 200 | 143.95.39.117:80 | http://www.cogis-photo.com/wp-content/uploads/2019/07/serious-small-dick-humiliation-online-domme-300x200.jpg | US | image | 13.8 Kb | unknown |
2856 | iexplore.exe | GET | 200 | 143.95.39.117:80 | http://www.cogis-photo.com/wp-content/uploads/2019/10/little-penis-humiliation-web-cam-queen-will-humiliate-little-pricks-immediately-300x200.jpg | US | image | 10.3 Kb | unknown |
2856 | iexplore.exe | GET | 200 | 143.95.39.117:80 | http://www.cogis-photo.com/wp-includes/js/wp-emoji-release.min.js | US | text | 5.10 Kb | unknown |
2856 | iexplore.exe | GET | 200 | 143.95.39.117:80 | http://www.cogis-photo.com/wp-content/uploads/2019/08/small-penis-humiliation-webcam-300x200.jpg | US | image | 12.6 Kb | unknown |
2856 | iexplore.exe | GET | 200 | 143.95.39.117:80 | http://www.cogis-photo.com/wp-content/uploads/2019/08/alexastevens-small-cock-humiliation-on-cams-300x200.jpg | US | image | 10.9 Kb | unknown |
2856 | iexplore.exe | GET | 301 | 213.152.244.159:80 | http://www.camsense.com/live/iframe.html?siteID=24&c=7&content=1&ref=1371679&bg=000000&link=FFFFFF&hover=FF0000&newwindow=1&rows=10&cols=1&pictureSize=2&isGeo=0&adult=0 | GB | — | — | unknown |
2856 | iexplore.exe | GET | 200 | 143.95.39.117:80 | http://www.cogis-photo.com/wp-content/uploads/2019/06/busty-and-wonderfully-kinky-bbw-camgirl-belladonna-sph-webcam-300x200.jpg | US | image | 9.97 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2784 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4 | System | 173.194.76.82:445 | html5shim.googlecode.com | Google Inc. | US | whitelisted |
4 | System | 173.194.76.82:139 | html5shim.googlecode.com | Google Inc. | US | whitelisted |
4 | System | 172.217.23.106:445 | fonts.googleapis.com | Google Inc. | US | whitelisted |
4 | System | 172.217.23.106:139 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 173.194.76.82:80 | html5shim.googlecode.com | Google Inc. | US | whitelisted |
2856 | iexplore.exe | 143.95.39.117:80 | www.cogis-photo.com | Colo4, LLC | US | unknown |
2856 | iexplore.exe | 172.217.23.106:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2856 | iexplore.exe | 172.217.22.99:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2856 | iexplore.exe | 213.152.244.159:80 | www.camsense.com | CC Network Inc | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cogis-photo.com |
| unknown |
www.bing.com |
| whitelisted |
html5shim.googlecode.com |
| whitelisted |
dns.msftncsi.com |
| shared |
fonts.googleapis.com |
| whitelisted |
cogis-photo.com |
| unknown |
fonts.gstatic.com |
| whitelisted |
www.camsense.com |
| unknown |