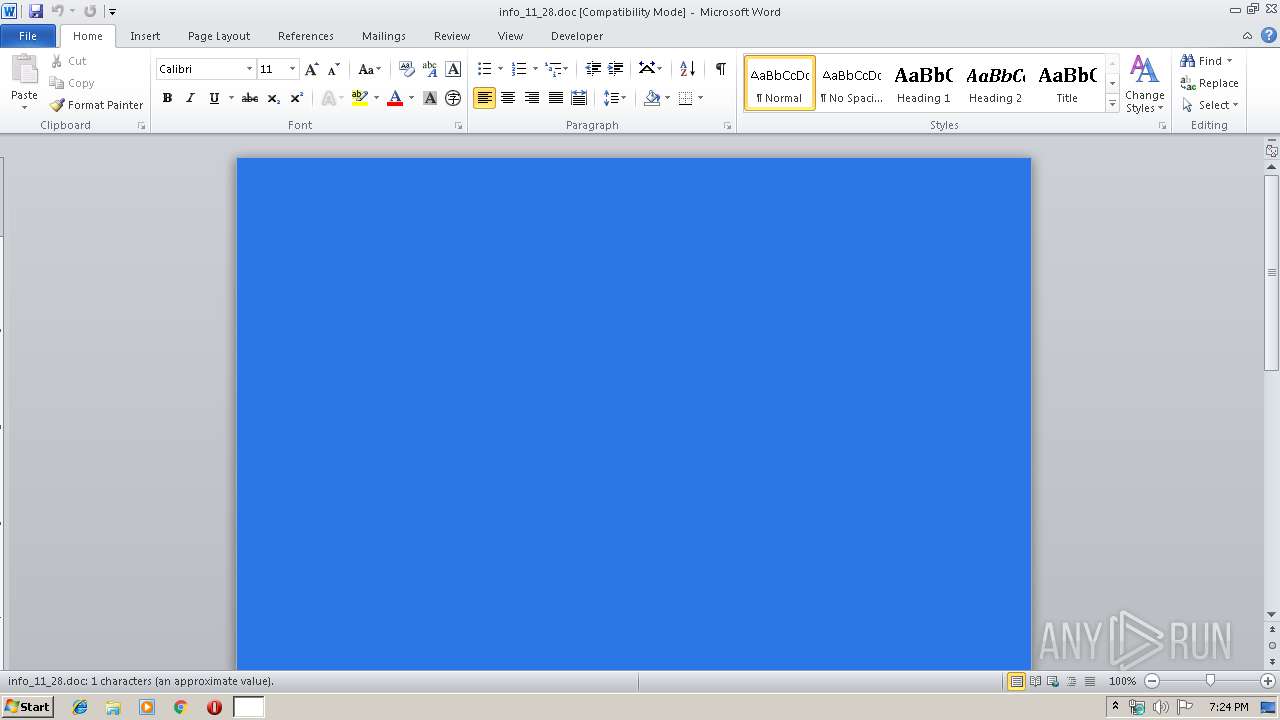
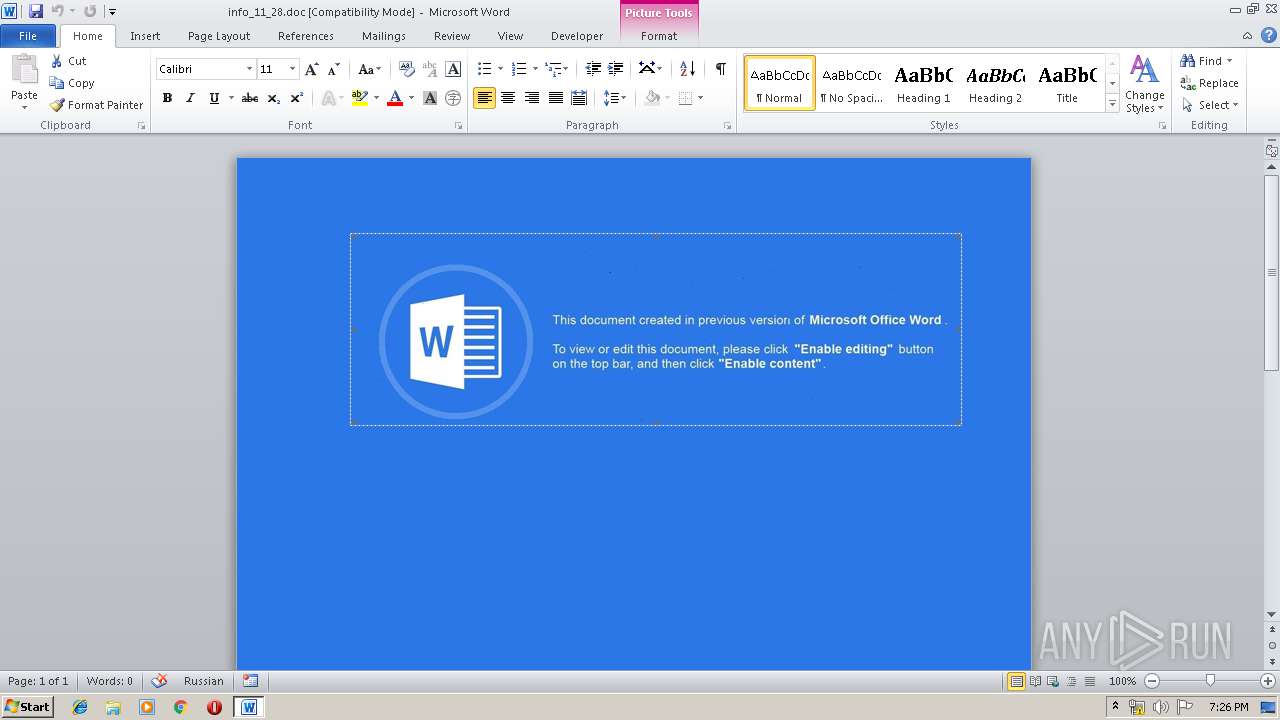
| File name: | info_11_28.doc |
| Full analysis: | https://app.any.run/tasks/611fc9be-404c-430f-88d7-608d106e623e |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 19:24:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1251, Title: Auto Formatter v1.2, Subject: Payslip auto formatter, Author: WAREHOUSECOMP1, Comments: Reference #8966, Template: Normal, Last Saved By: Windows, Revision Number: 7, Name of Creating Application: Microsoft Office Word, Total Editing Time: 01:00, Create Time/Date: Tue Aug 6 10:17:00 2019, Last Saved Time/Date: Thu Nov 28 10:27:00 2019, Number of Pages: 1, Number of Words: 0, Number of Characters: 1, Security: 0 |
| MD5: | C66741A07FEDAE12CD3F1AFE0E13C326 |
| SHA1: | 82C972B568E4B1C66204873478E9BE90AC858E4A |
| SHA256: | 213B38E9597FCB946879DA3FDD8B0725B0EA1F7296D0687F07D7135BFC392C65 |
| SSDEEP: | 3072:6KiQ/A+cup0ljtHY9z+sw5HPHzoT8cXO5yS1ZqRafpv5736WPGRjOK8BlEu6arqX:D/SXqEHkXO5x11ERjsBlENamAniQC |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 4076)
Executes scripts
- WINWORD.EXE (PID: 4076)
SUSPICIOUS
Creates files in the user directory
- WScript.exe (PID: 3380)
Creates files in the Windows directory
- WINWORD.EXE (PID: 4076)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 4076)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Auto Formatter v1.2 |
|---|---|
| Subject: | Payslip auto formatter |
| Author: | WAREHOUSECOMP1 |
| Keywords: | - |
| Comments: | Reference #8966 |
| Template: | Normal |
| LastModifiedBy: | Пользователь Windows |
| RevisionNumber: | 7 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 1.0 minutes |
| CreateDate: | 2019:08:06 09:17:00 |
| ModifyDate: | 2019:11:28 10:27:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Manager: | Lottie Hamill |
| Company: | EasyLease LLC |
| Bytes: | 27648 |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 1 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
39
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3380 | "C:\Windows\System32\WScript.exe" "C:\Windows\Temp\hwaqpsykee.js" | C:\Windows\System32\WScript.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 4076 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\info_11_28.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 747
Read events
919
Write events
675
Delete events
153
Modification events
| (PID) Process: | (4076) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | #c: |
Value: 23633A00EC0F0000010000000000000000000000 | |||
| (PID) Process: | (4076) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (4076) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (4076) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (4076) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (4076) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (4076) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (4076) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (4076) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (4076) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1333919806 | |||
Executable files
0
Suspicious files
0
Text files
6
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4076 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD783.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3380 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@avg[1].txt | — | |
MD5:— | SHA256:— | |||
| 3380 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@bitdefender[1].txt | — | |
MD5:— | SHA256:— | |||
| 4076 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFB89F2726209351C6.TMP | — | |
MD5:— | SHA256:— | |||
| 4076 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF425C2A974E86A4BF.TMP | — | |
MD5:— | SHA256:— | |||
| 4076 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF3462DF2B80DCB3F2.TMP | — | |
MD5:— | SHA256:— | |||
| 4076 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{41170766-DEF0-4919-B829-099BFB6B9268}.tmp | — | |
MD5:— | SHA256:— | |||
| 4076 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF6CB362D9F4312AC6.TMP | — | |
MD5:— | SHA256:— | |||
| 4076 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{ECBDF062-A05B-4FF8-9AF9-9484F850CB7E}.tmp | — | |
MD5:— | SHA256:— | |||
| 4076 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3380 | WScript.exe | GET | 404 | 93.179.69.171:80 | http://mimicaunaw.com/curoix/jotask.php?l=apitzy1.cab | RU | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3380 | WScript.exe | 104.109.85.142:443 | www.avg.com | Akamai International B.V. | NL | whitelisted |
3380 | WScript.exe | 52.21.38.34:443 | www.eset.com | Amazon.com, Inc. | US | unknown |
3380 | WScript.exe | 93.179.69.171:80 | mimicaunaw.com | Fop Iliushenko Volodymyr Olexandrovuch | RU | suspicious |
3380 | WScript.exe | 104.18.169.222:443 | www.bitdefender.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.avg.com |
| whitelisted |
www.bitdefender.com |
| suspicious |
www.eset.com |
| whitelisted |
mimicaunaw.com |
| suspicious |
Threats
1 ETPRO signatures available at the full report