| URL: | https://anonfiles.com/P5ec9fs9yb/s4_Yahoo_Checker_rar |
| Full analysis: | https://app.any.run/tasks/af48cfa0-4376-4ca2-a4f3-d7722bf13acf |
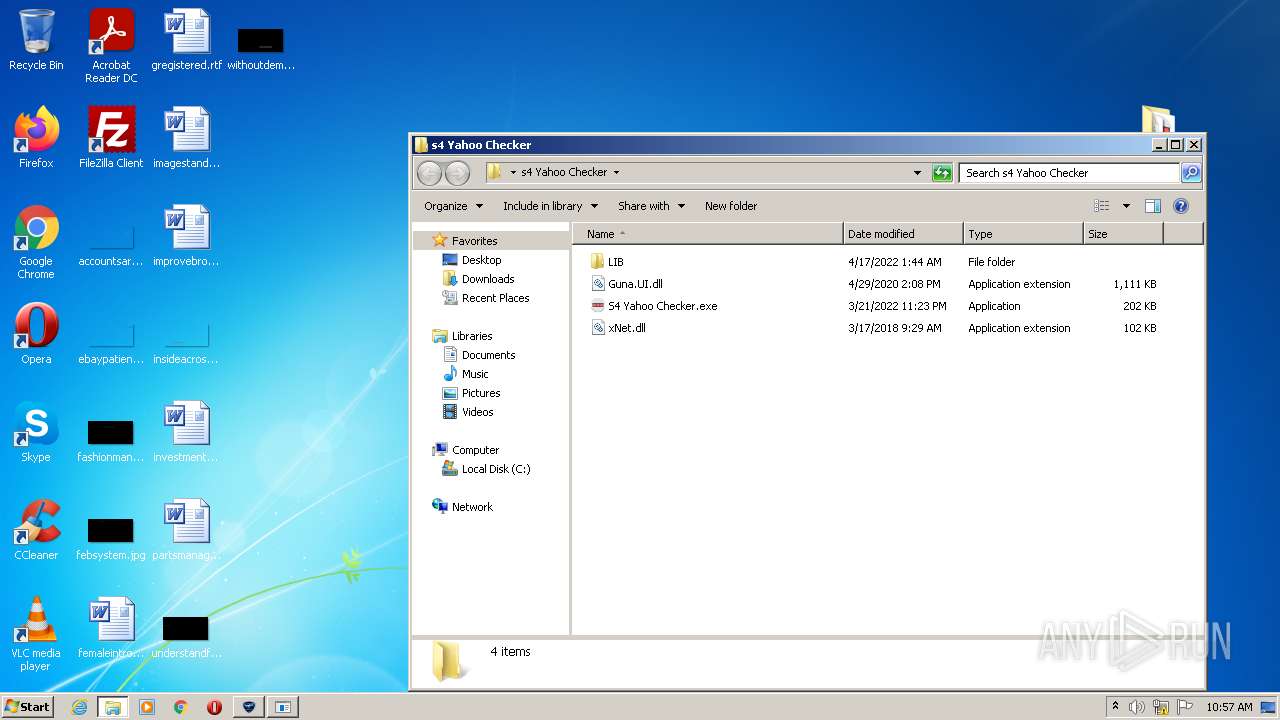
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 09:56:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8BCF126D81938AF6B9C7AE33DED2F568 |
| SHA1: | 1D0FDC5CDE01424567933E57EA150FD4EBCEA349 |
| SHA256: | 21272ED66F94B396B99B25D441FAC44896406D5ECC72ED37F019E0C831FF222A |
| SSDEEP: | 3:N8M2brHNR68EYKNEc:2M2brHm8Eqc |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3000)
- Launcher.exe (PID: 2660)
- ldm.exe (PID: 2736)
Drops executable file immediately after starts
- WinRAR.exe (PID: 2572)
- Launcher.exe (PID: 2660)
Application was dropped or rewritten from another process
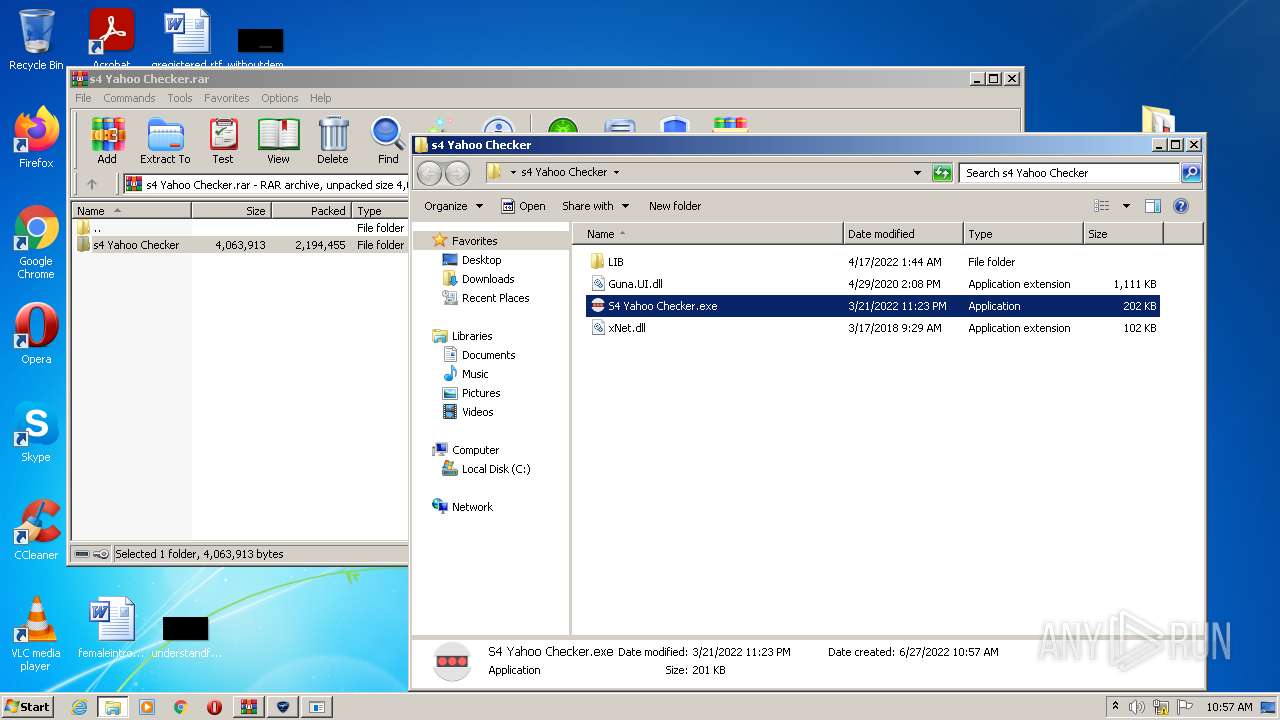
- S4 Yahoo Checker.exe (PID: 1092)
- Launcher.exe (PID: 2660)
- ldm.exe (PID: 2736)
- Secure System Shell.exe (PID: 2592)
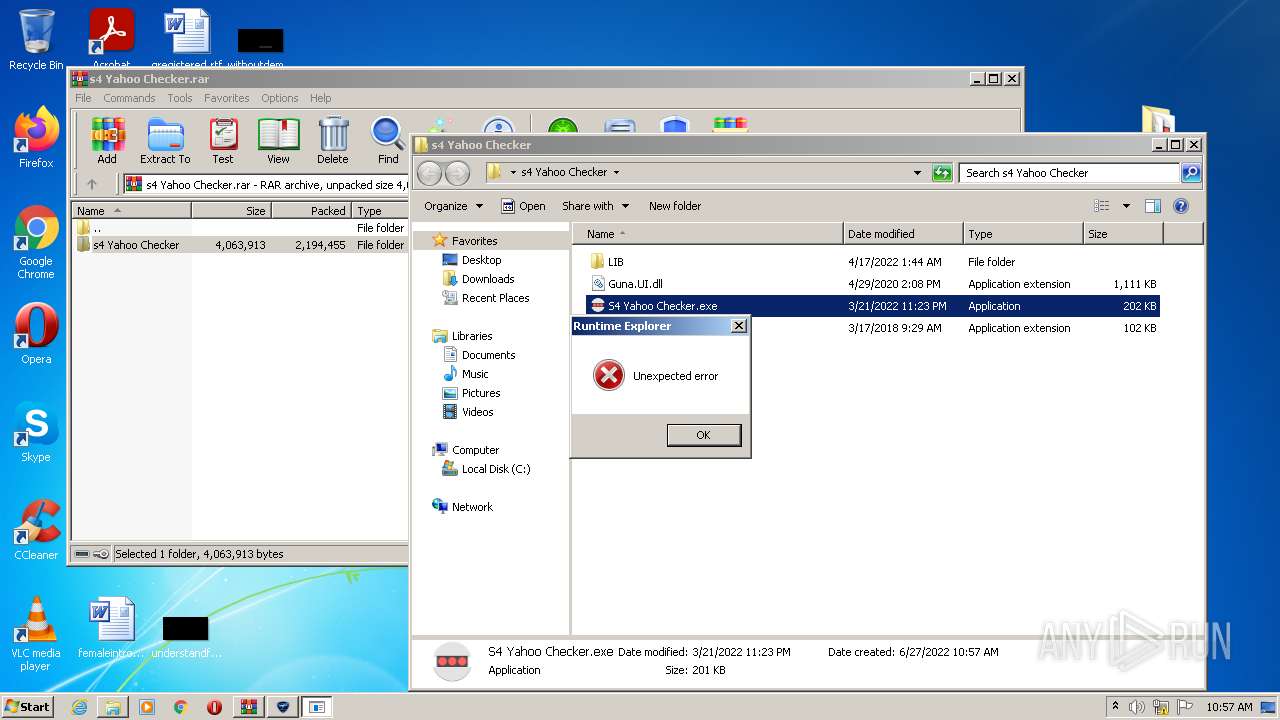
- Runtime Explorer.exe (PID: 396)
- Runtime Explorer.exe (PID: 892)
- Windows Services.exe (PID: 840)
Writes to a start menu file
- Launcher.exe (PID: 2660)
Changes the autorun value in the registry
- Launcher.exe (PID: 2660)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2572)
- S4 Yahoo Checker.exe (PID: 1092)
- Launcher.exe (PID: 2660)
- powershell.exe (PID: 2356)
- ldm.exe (PID: 2736)
- Secure System Shell.exe (PID: 2592)
- Windows Services.exe (PID: 840)
- Runtime Explorer.exe (PID: 892)
- Runtime Explorer.exe (PID: 396)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2864)
Reads the computer name
- WinRAR.exe (PID: 2572)
- S4 Yahoo Checker.exe (PID: 1092)
- Launcher.exe (PID: 2660)
- powershell.exe (PID: 2356)
- ldm.exe (PID: 2736)
- Windows Services.exe (PID: 840)
- Secure System Shell.exe (PID: 2592)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2572)
- Launcher.exe (PID: 2660)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2572)
- Launcher.exe (PID: 2660)
Executes PowerShell scripts
- Launcher.exe (PID: 2660)
Creates files in the user directory
- Launcher.exe (PID: 2660)
Creates files in the Windows directory
- Launcher.exe (PID: 2660)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2568)
Reads the computer name
- iexplore.exe (PID: 2568)
- iexplore.exe (PID: 2864)
Checks supported languages
- iexplore.exe (PID: 2568)
- iexplore.exe (PID: 2864)
Reads settings of System Certificates
- iexplore.exe (PID: 2864)
- iexplore.exe (PID: 2568)
- powershell.exe (PID: 2356)
Application launched itself
- iexplore.exe (PID: 2568)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2568)
Reads the date of Windows installation
- iexplore.exe (PID: 2568)
Checks Windows Trust Settings
- iexplore.exe (PID: 2864)
- iexplore.exe (PID: 2568)
- powershell.exe (PID: 2356)
Reads internet explorer settings
- iexplore.exe (PID: 2864)
Manual execution by user
- S4 Yahoo Checker.exe (PID: 1092)
Dropped object may contain Bitcoin addresses
- Launcher.exe (PID: 2660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
12
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | "C:\Windows\IMF\Runtime Explorer.exe" | C:\Windows\IMF\Runtime Explorer.exe | — | Windows Services.exe | |||||||||||
User: admin Company: Microsoft Windows Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 840 | "C:\Windows\IMF\Windows Services.exe" {Arguments If Needed} | C:\Windows\IMF\Windows Services.exe | — | Launcher.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Windows Services Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 892 | "C:\Windows\IMF\Runtime Explorer.exe" | C:\Windows\IMF\Runtime Explorer.exe | — | Windows Services.exe | |||||||||||
User: admin Company: Microsoft Windows Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
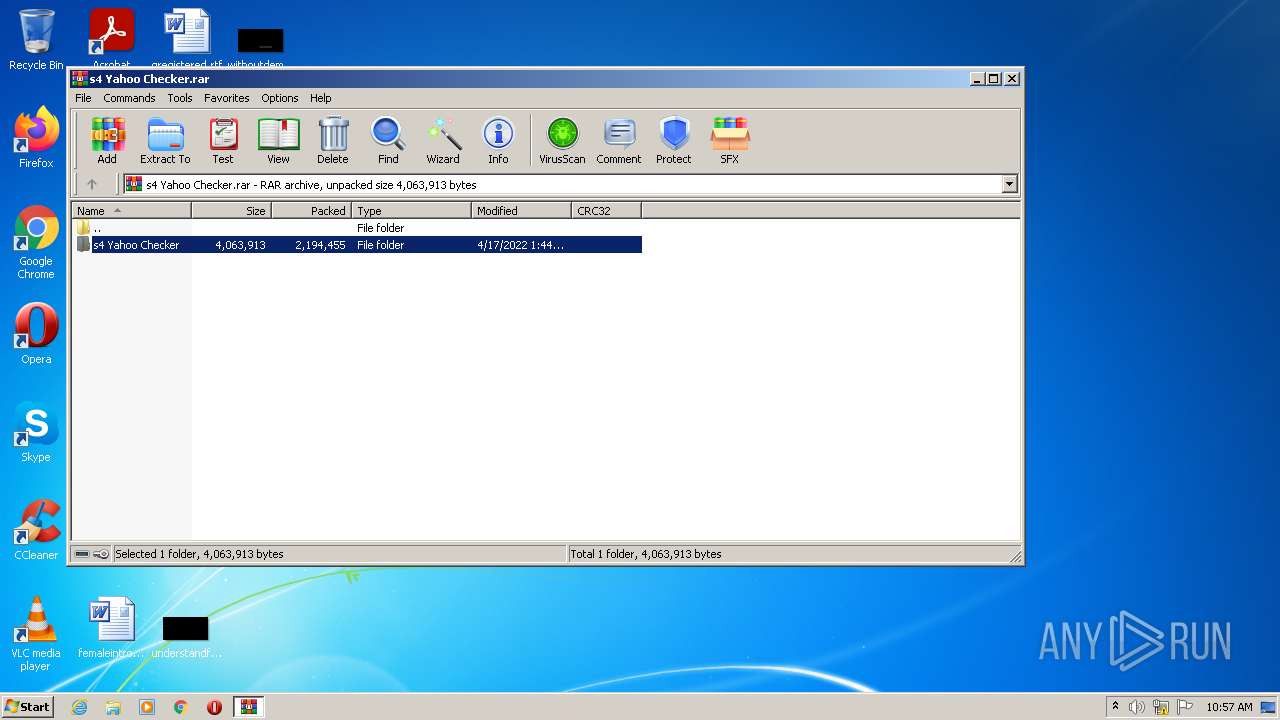
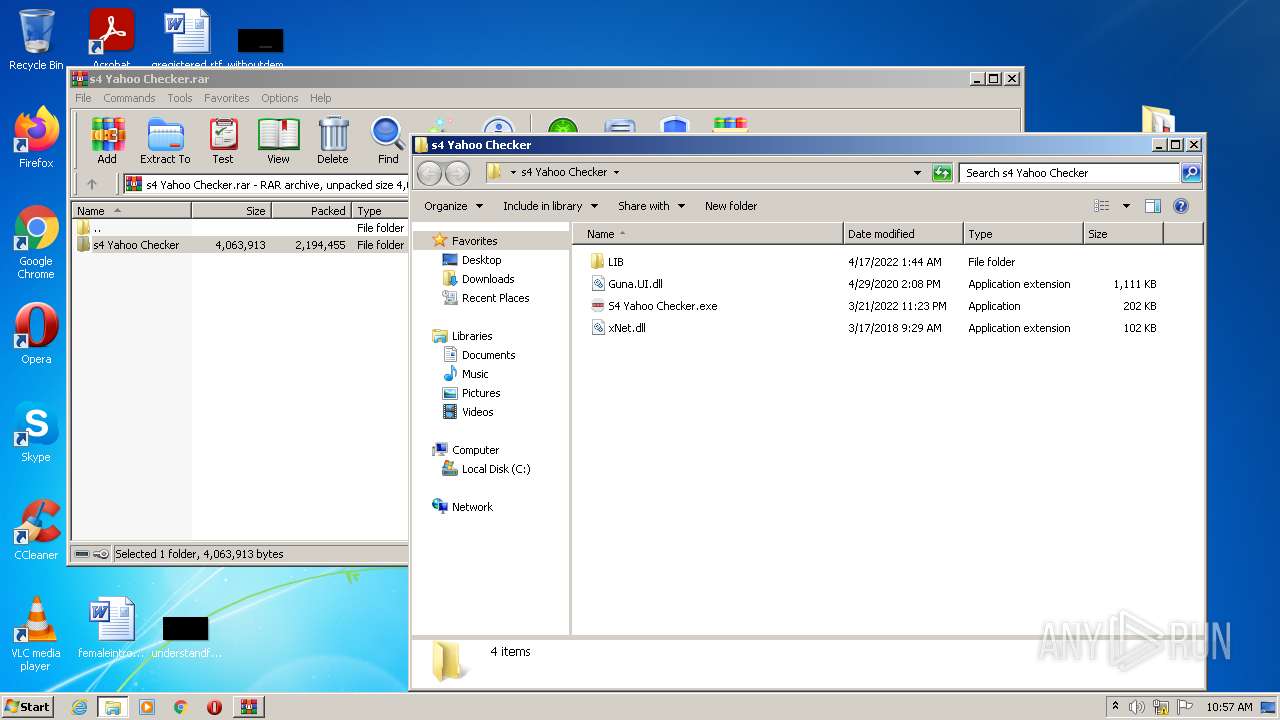
| 1092 | "C:\Users\admin\Desktop\s4 Yahoo Checker\S4 Yahoo Checker.exe" | C:\Users\admin\Desktop\s4 Yahoo Checker\S4 Yahoo Checker.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: Launcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2356 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" add-mppreference -exclusionpath C:\Windows\IMF\ | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://anonfiles.com/P5ec9fs9yb/s4_Yahoo_Checker_rar" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
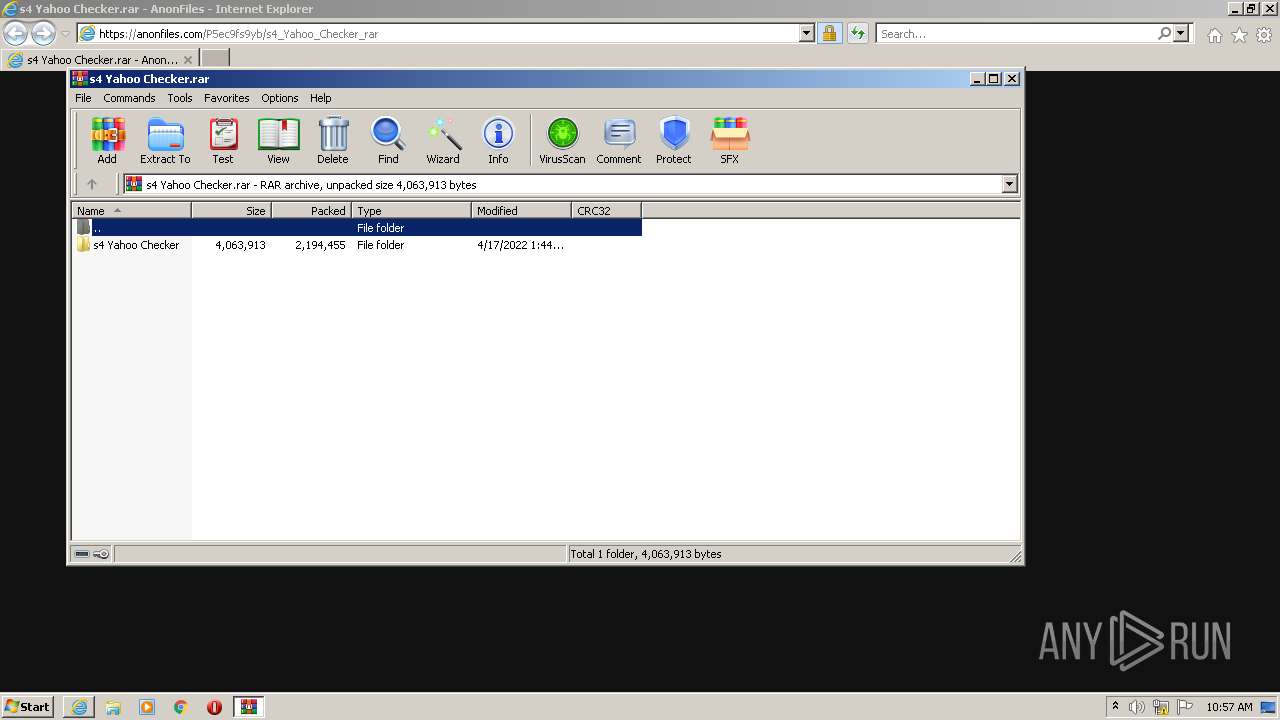
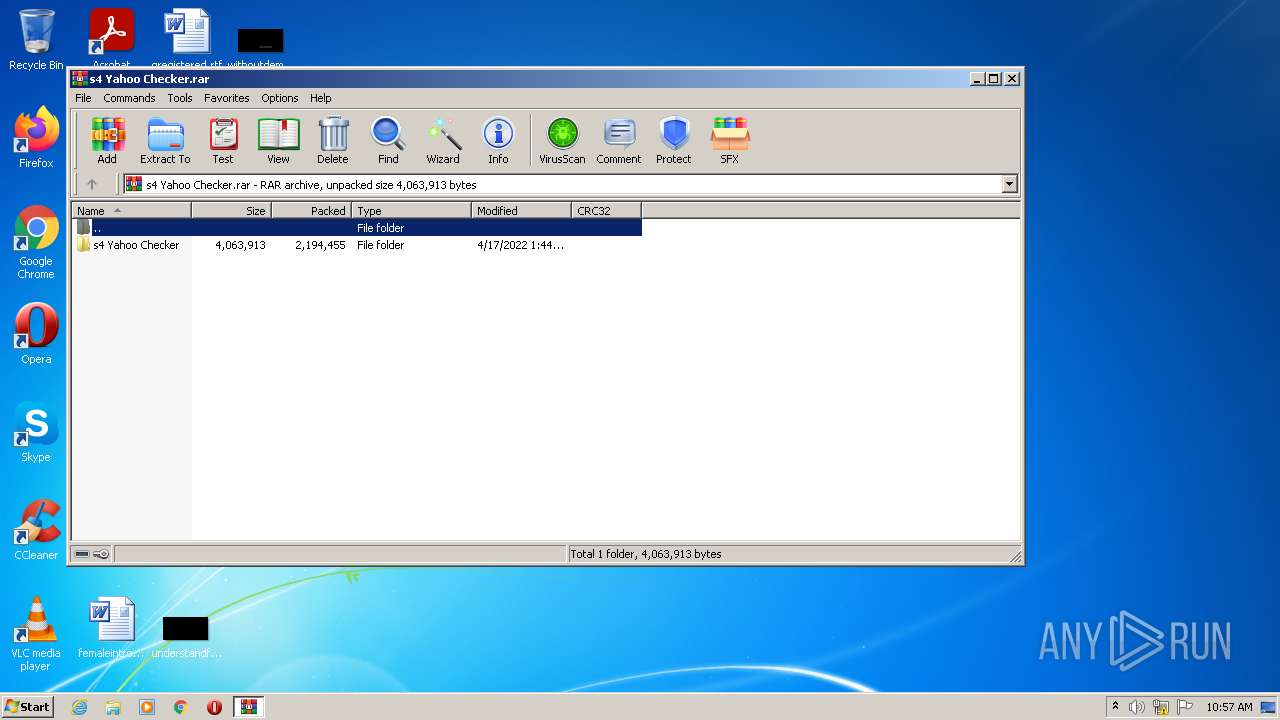
| 2572 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\s4 Yahoo Checker.rar" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2592 | "C:\Windows\IMF\Secure System Shell.exe" | C:\Windows\IMF\Secure System Shell.exe | — | Windows Services.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Secure System Shell Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2660 | "C:\Users\admin\Desktop\s4 Yahoo Checker\LIB\Launcher.exe" | C:\Users\admin\Desktop\s4 Yahoo Checker\LIB\Launcher.exe | S4 Yahoo Checker.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Launcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2736 | "C:\Users\admin\Desktop\s4 Yahoo Checker\LIB\ldm.exe" | C:\Users\admin\Desktop\s4 Yahoo Checker\LIB\ldm.exe | S4 Yahoo Checker.exe | ||||||||||||
User: admin Company: S4 Integrity Level: HIGH Description: S4 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
18 305
Read events
18 122
Write events
182
Delete events
1
Modification events
| (PID) Process: | (2568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 887309728 | |||
| (PID) Process: | (2568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30968332 | |||
| (PID) Process: | (2568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30968332 | |||
| (PID) Process: | (2568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
14
Suspicious files
24
Text files
26
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 2568 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab618F.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2568 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\anonfiles[1].css | text | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\ABE5BEA86CDF3A91EBC3F9F946566003 | der | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\ABE5BEA86CDF3A91EBC3F9F946566003 | binary | |
MD5:— | SHA256:— | |||
| 2864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\s4_Yahoo_Checker_rar[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
27
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2864 | iexplore.exe | GET | 200 | 188.114.99.173:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHophRq39F1meVBmQbb%2F1x0%3D | US | der | 1.40 Kb | whitelisted |
2864 | iexplore.exe | GET | 200 | 18.66.242.155:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
2864 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?9bd51c455daa7161 | US | compressed | 60.0 Kb | whitelisted |
2568 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2864 | iexplore.exe | GET | 200 | 18.66.137.173:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2864 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f1e602415c584d2e | US | compressed | 4.70 Kb | whitelisted |
2864 | iexplore.exe | GET | 200 | 184.24.77.67:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMKkbL8LAFVsPfjhHUkFjxBXA%3D%3D | US | der | 503 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2864 | iexplore.exe | 45.154.253.152:443 | anonfiles.com | — | — | suspicious |
2864 | iexplore.exe | 96.16.145.230:80 | x1.c.lencr.org | Akamai Technologies, Inc. | US | suspicious |
2568 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2568 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2864 | iexplore.exe | 184.24.77.67:80 | r3.o.lencr.org | Time Warner Cable Internet LLC | US | unknown |
2864 | iexplore.exe | 151.101.2.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
2864 | iexplore.exe | 143.204.101.138:443 | djv99sxoqpv11.cloudfront.net | — | US | unknown |
2864 | iexplore.exe | 188.114.99.173:80 | ocsp2.globalsign.com | Cloudflare Inc | US | unknown |
2864 | iexplore.exe | 195.96.151.42:443 | cdn-148.anonfiles.com | Archway S.r.l | IQ | suspicious |
2864 | iexplore.exe | 18.66.242.155:80 | ocsp.rootg2.amazontrust.com | Massachusetts Institute of Technology | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfiles.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r3.o.lencr.org |
| shared |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
ocsp2.globalsign.com |
| whitelisted |