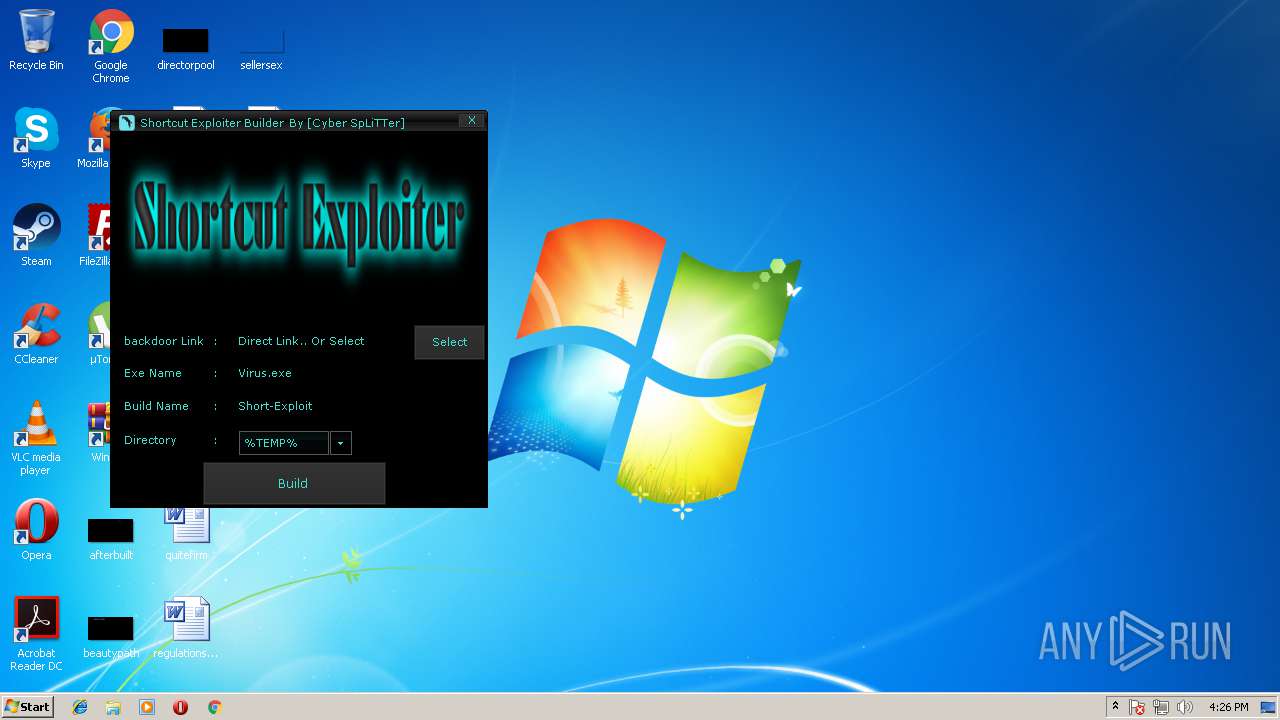
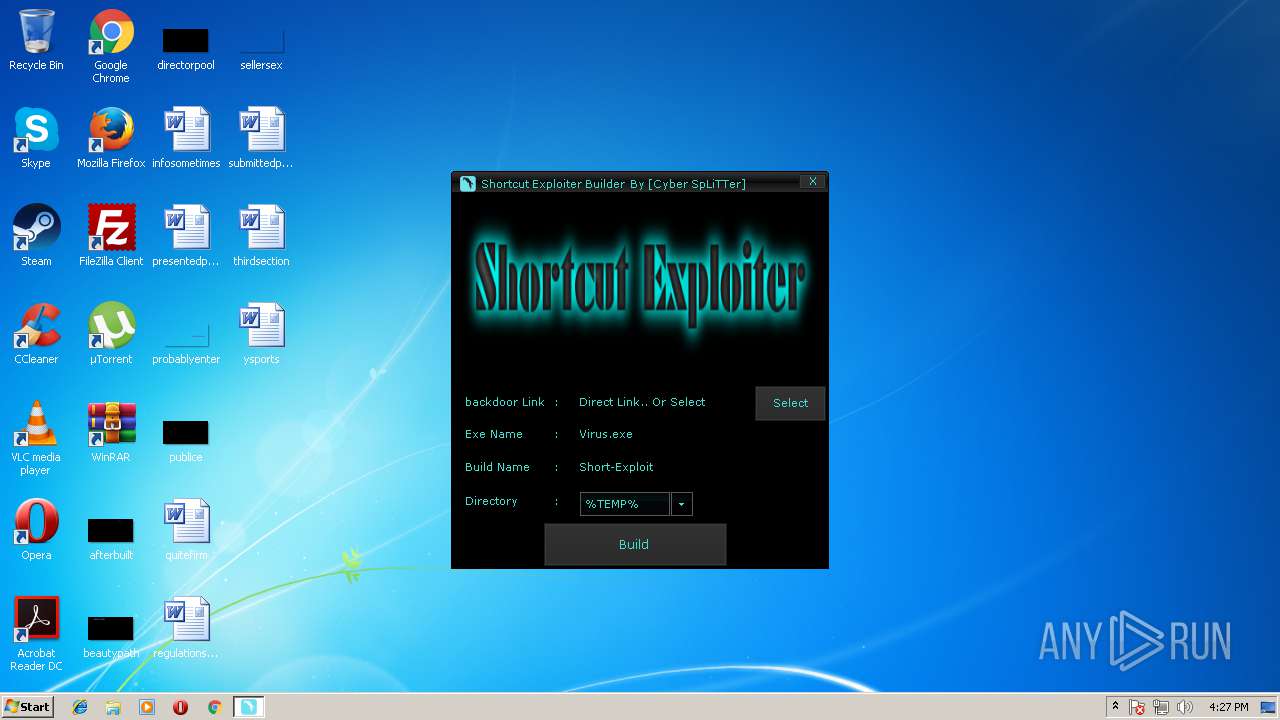
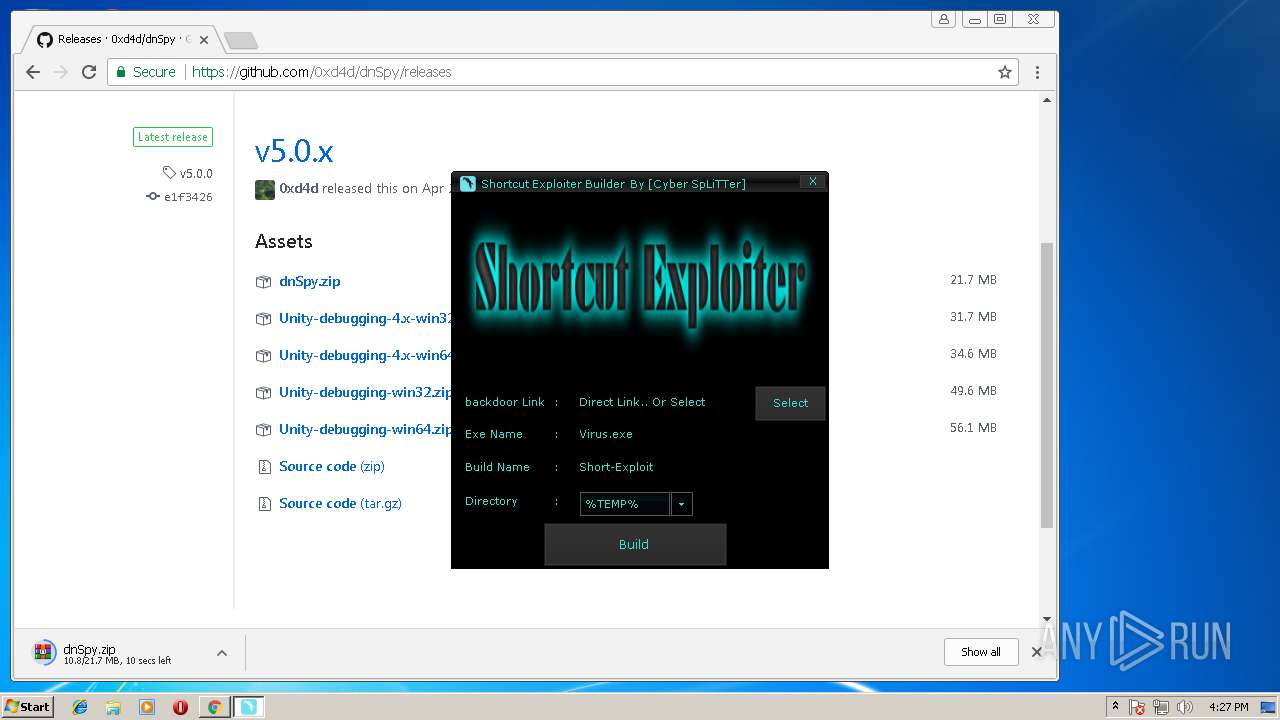
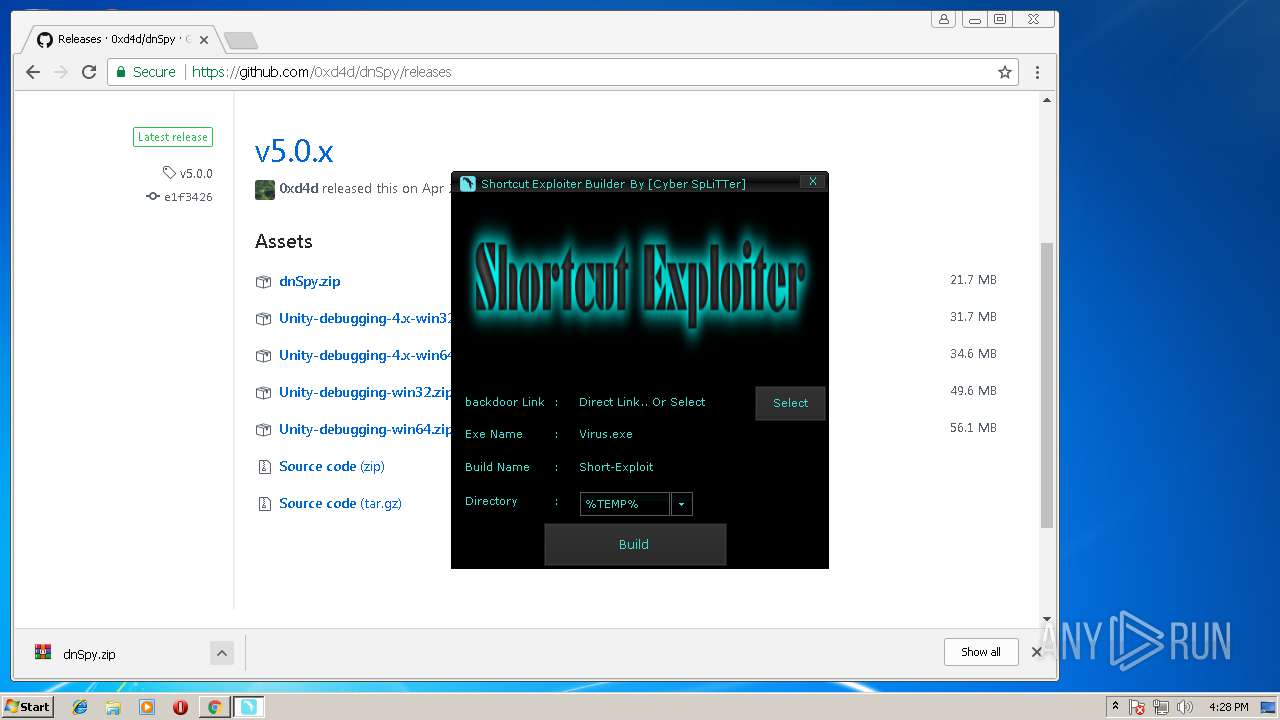
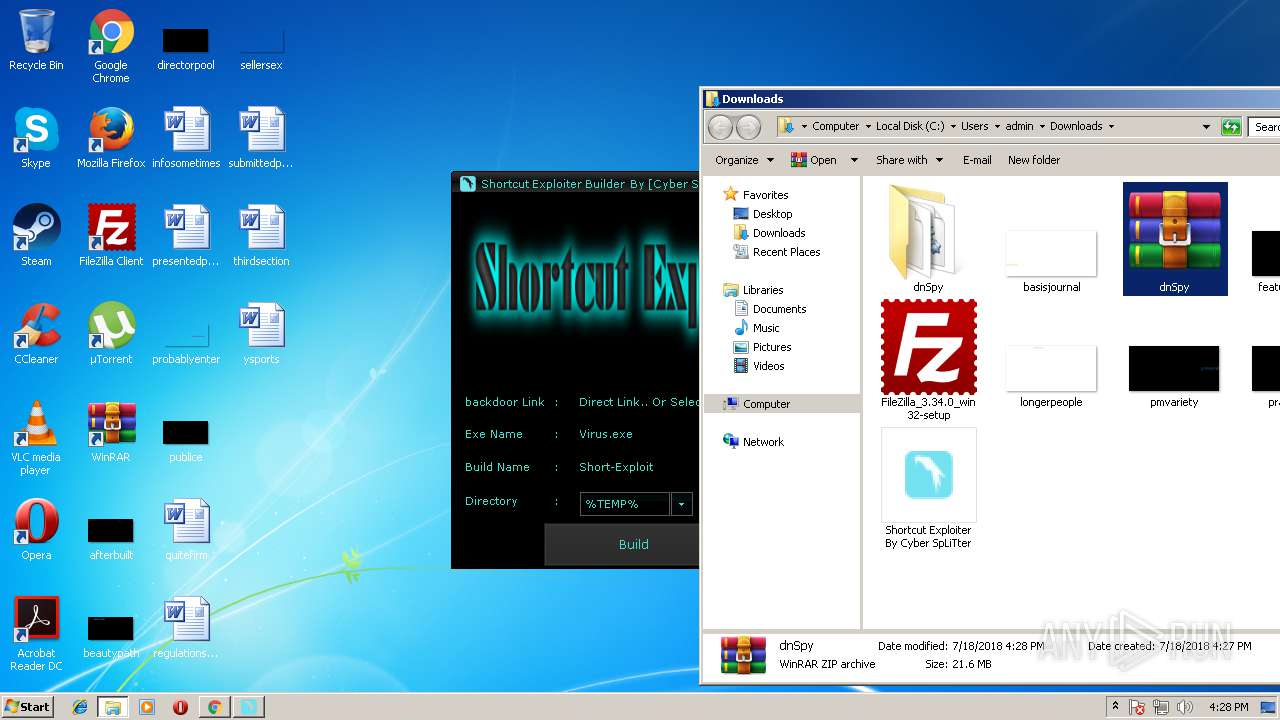
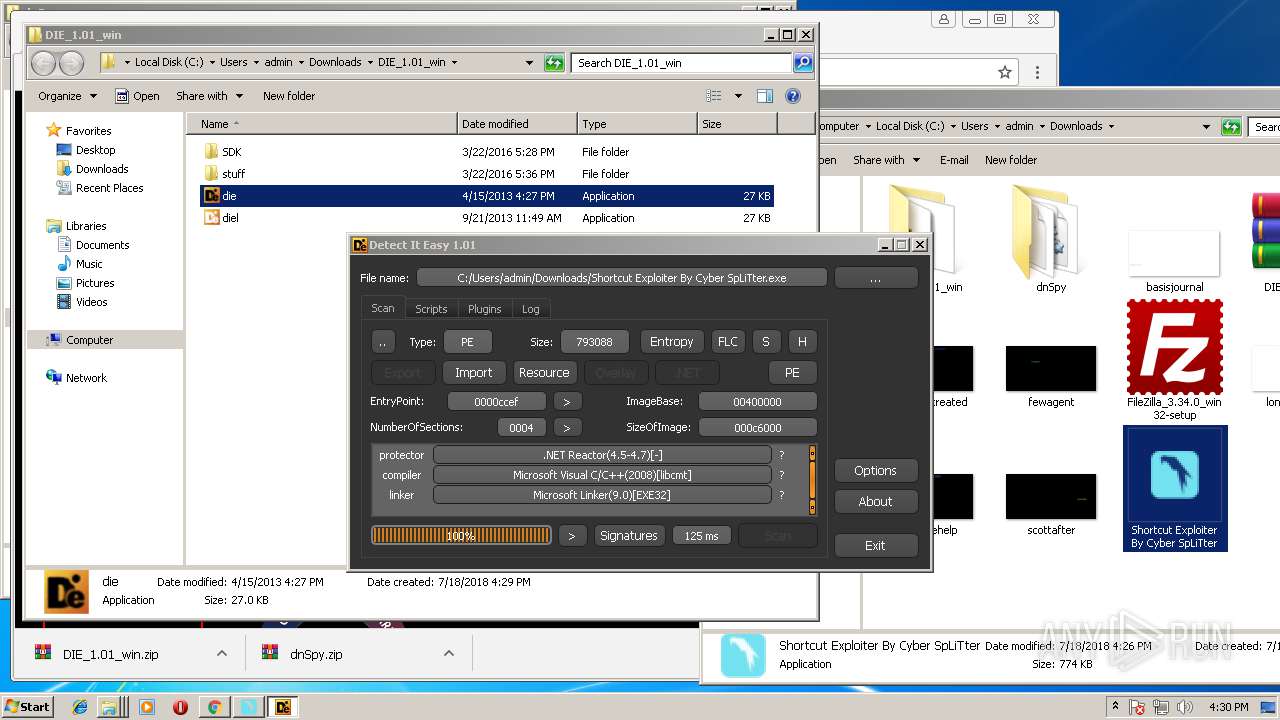
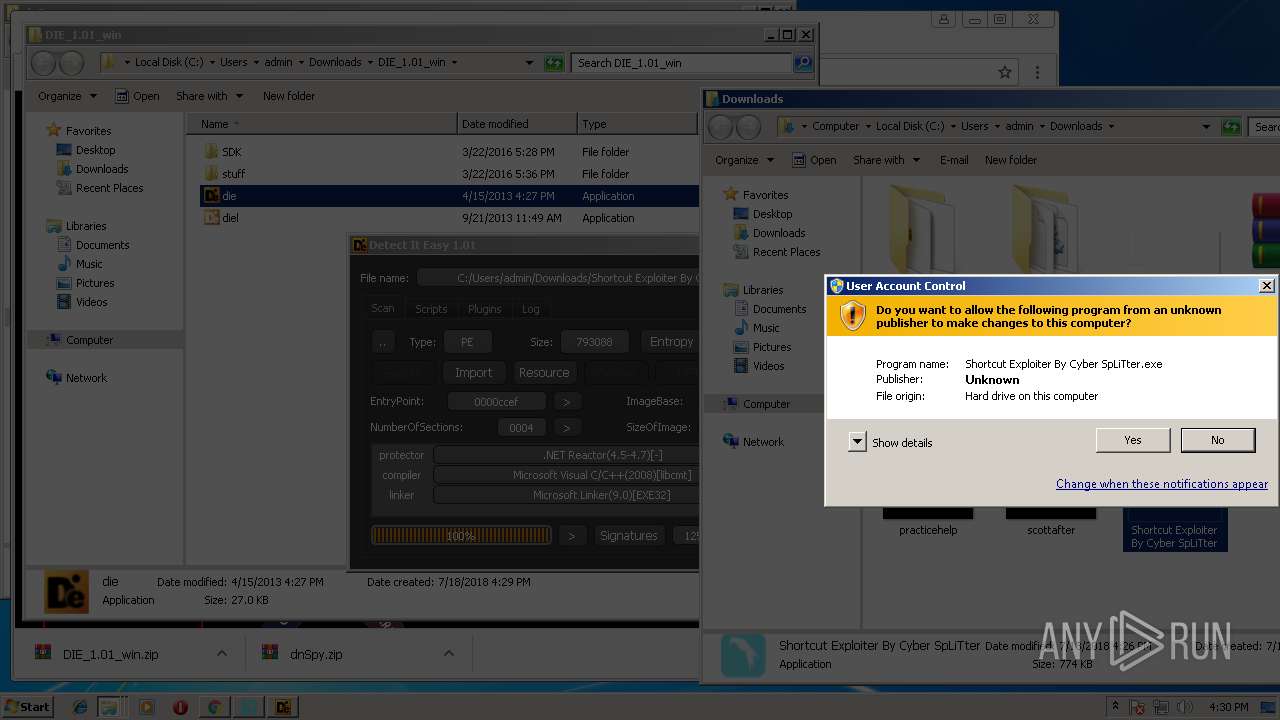
| File name: | Shortcut Exploiter By Cyber SpLiTter.exe |
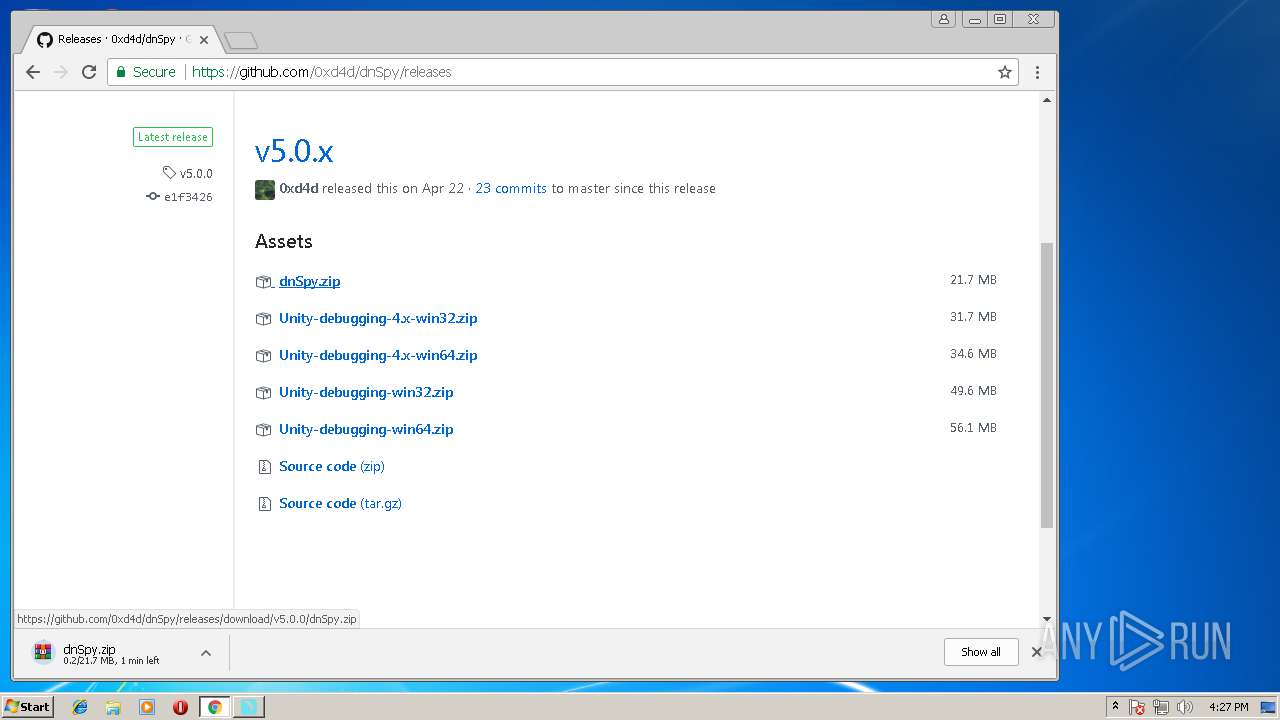
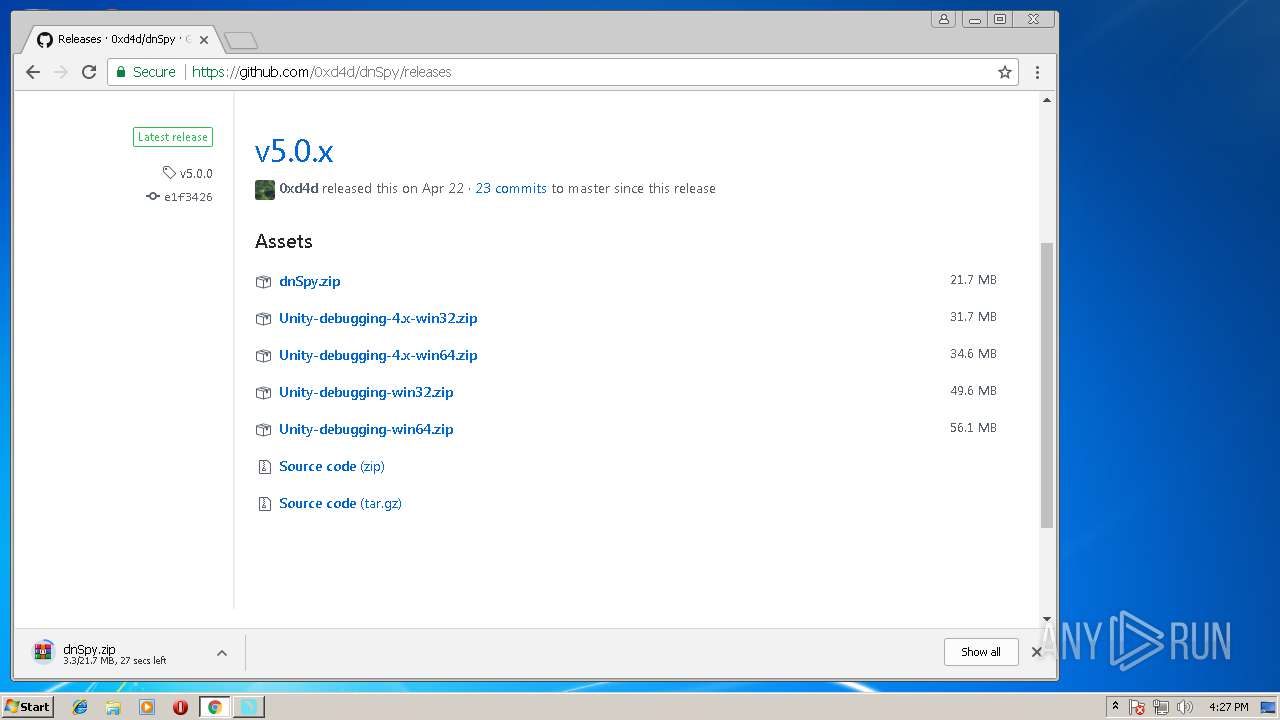
| Full analysis: | https://app.any.run/tasks/344e921c-5ac0-412f-aadf-038a18b9479b |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2018, 15:26:30 |
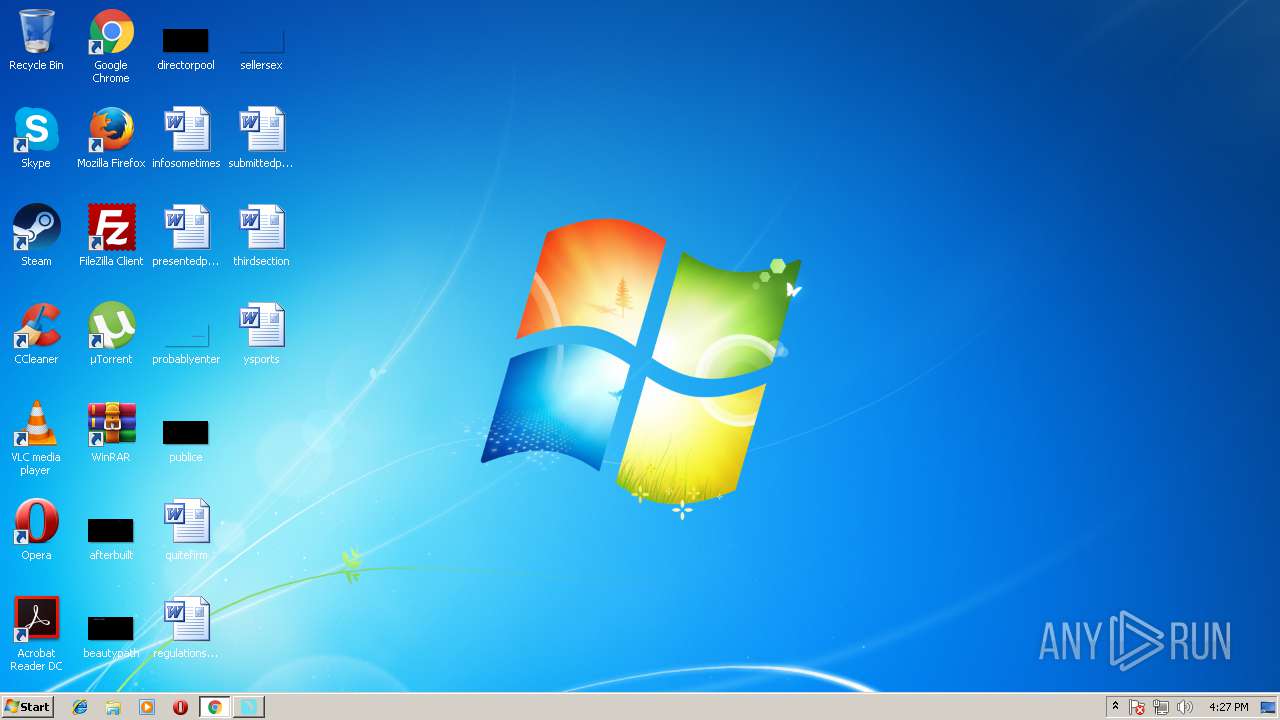
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0ACDA173D7CA24BEEB42557143E0F163 |
| SHA1: | B372E90A8387B9244EF02F64E3ECCFC235CC1D9D |
| SHA256: | 21182584AF3D1B333FF6C540903D74A02ADE8BDF78911ABED89B5C6BD6037C9D |
| SSDEEP: | 24576:rwnU4TDLWRhTLhmUsWp74Xd566hwkjsRiZX:UntTXuhlRsWp7K5ThwXy |
MALICIOUS
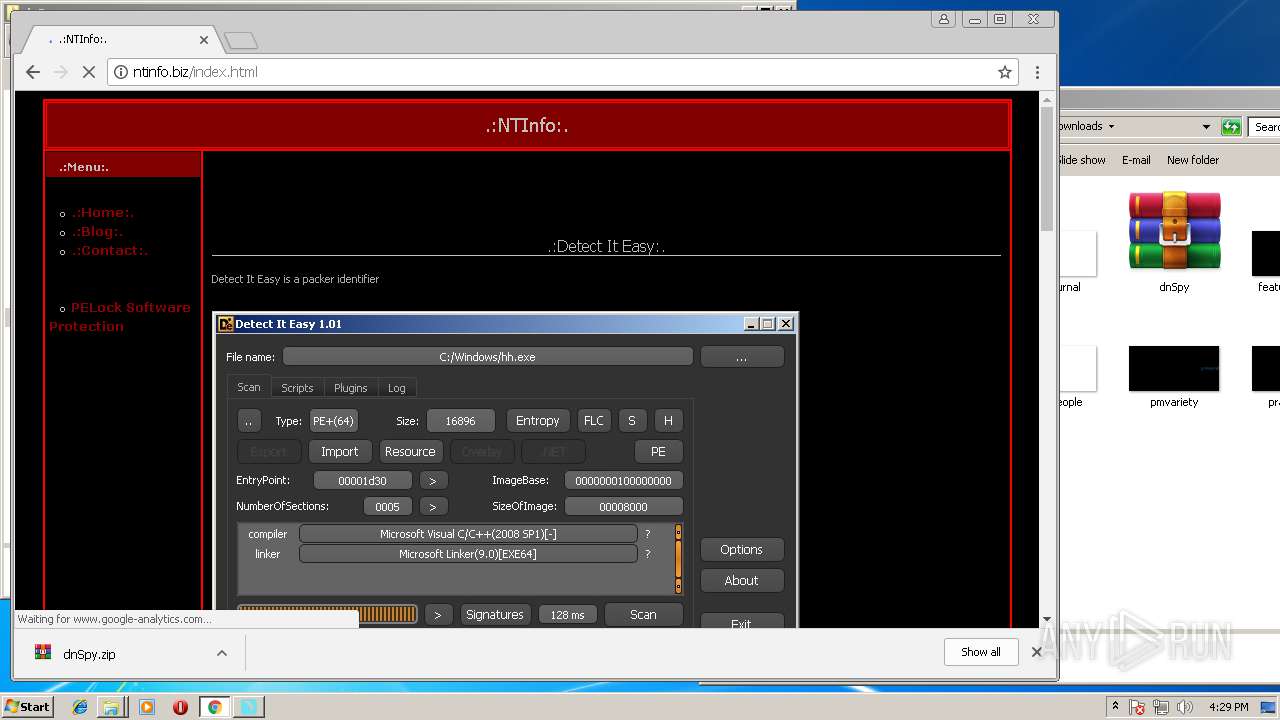
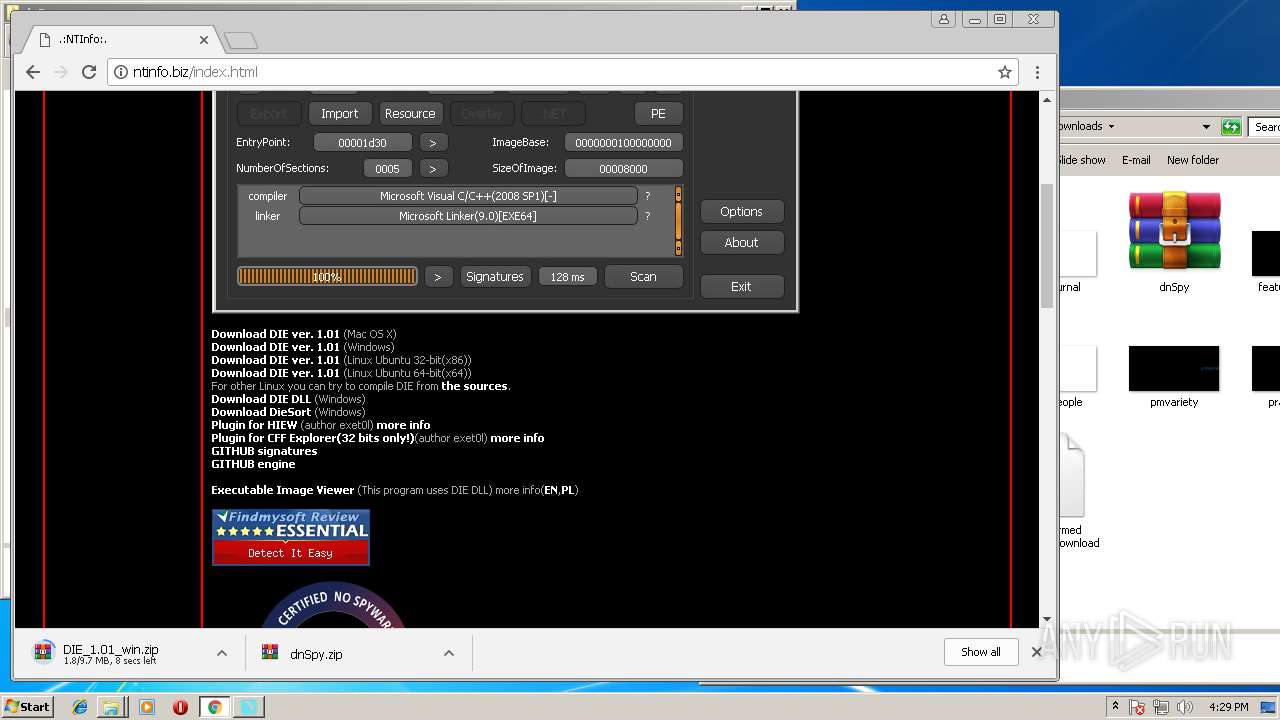
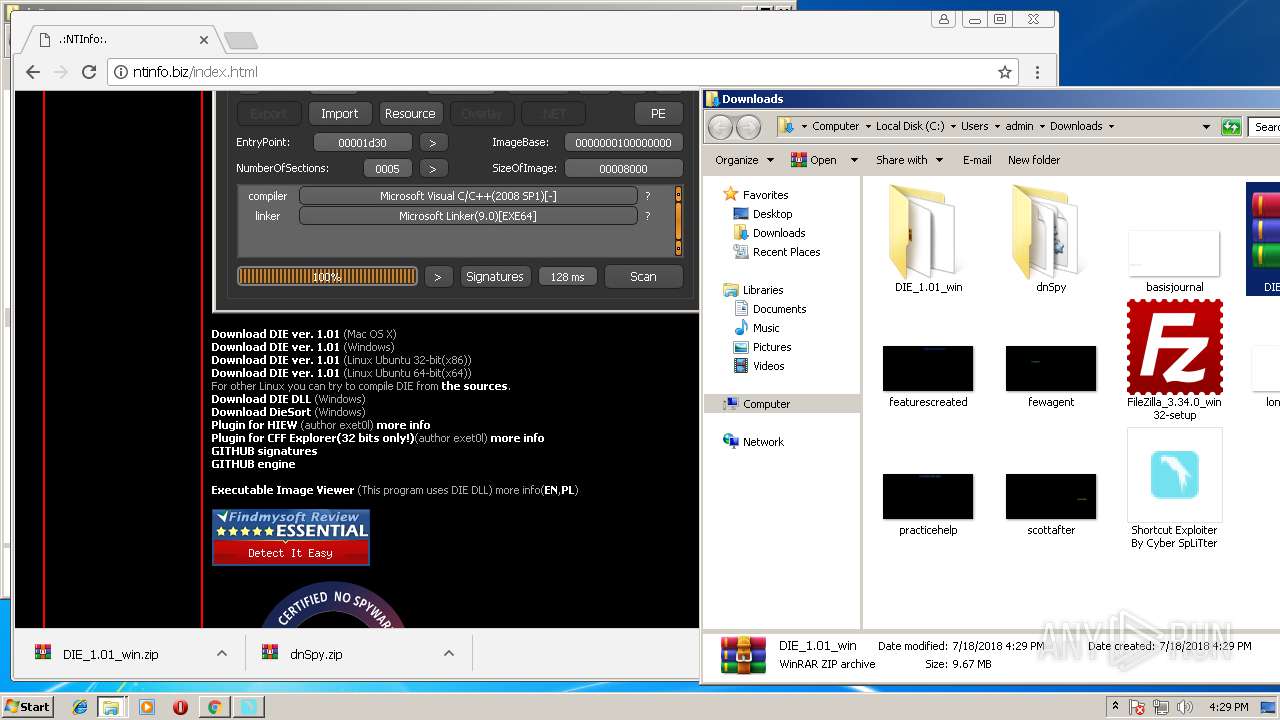
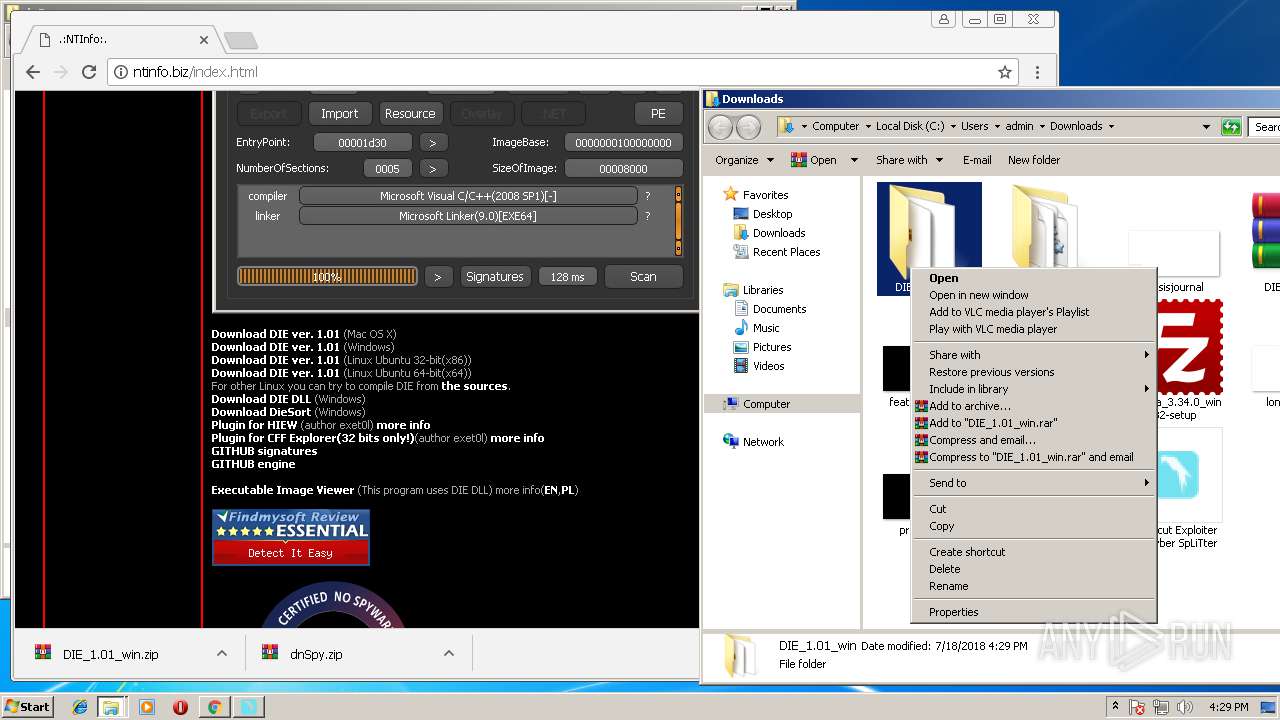
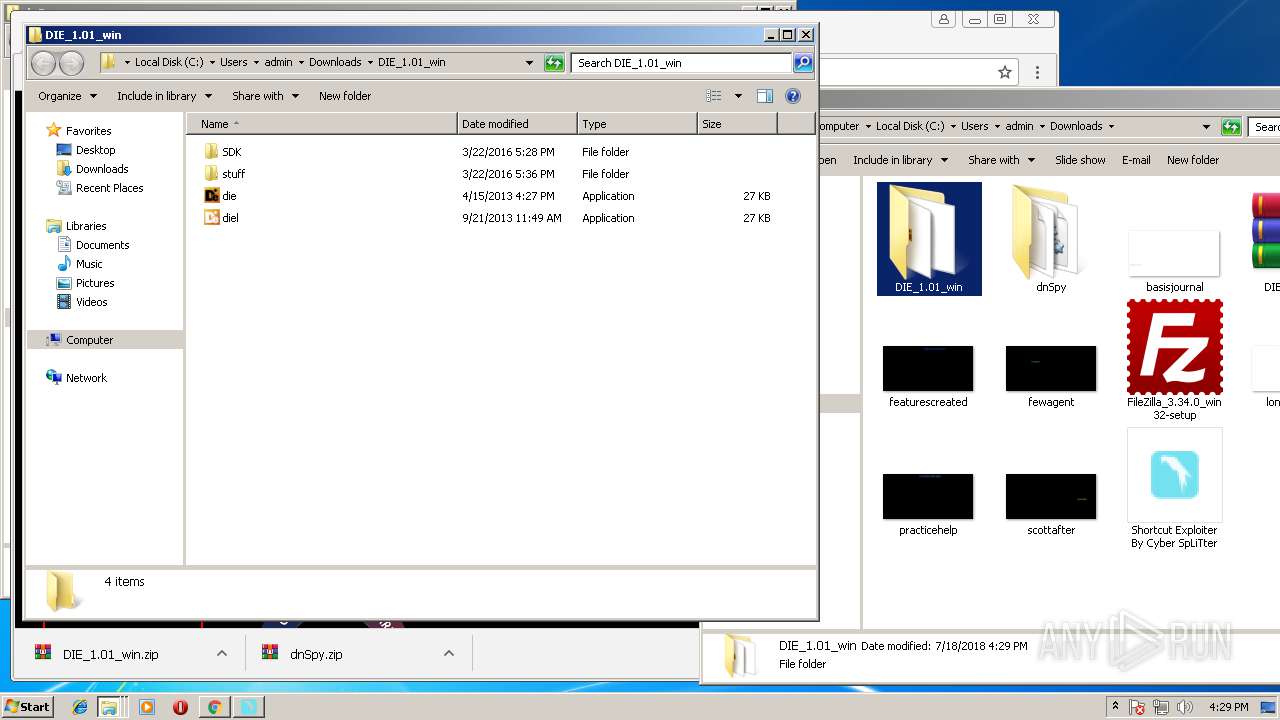
Loads dropped or rewritten executable
- die.exe (PID: 2728)
- SearchProtocolHost.exe (PID: 2992)
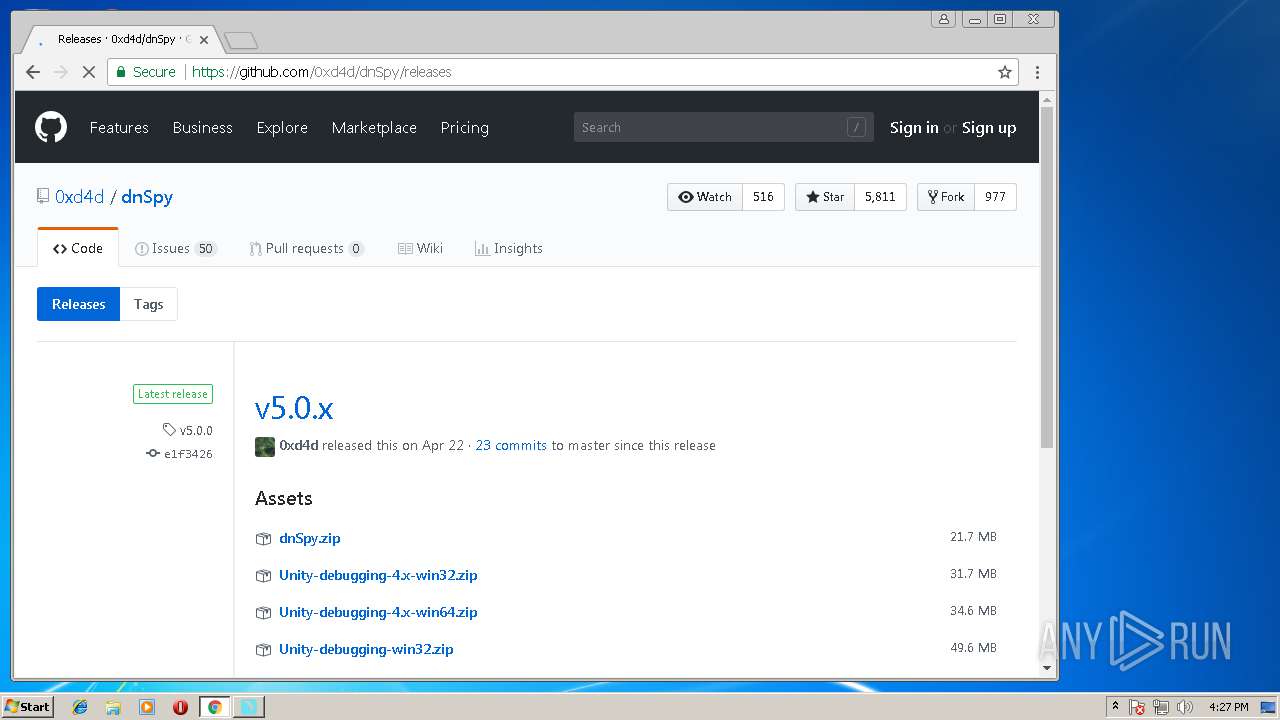
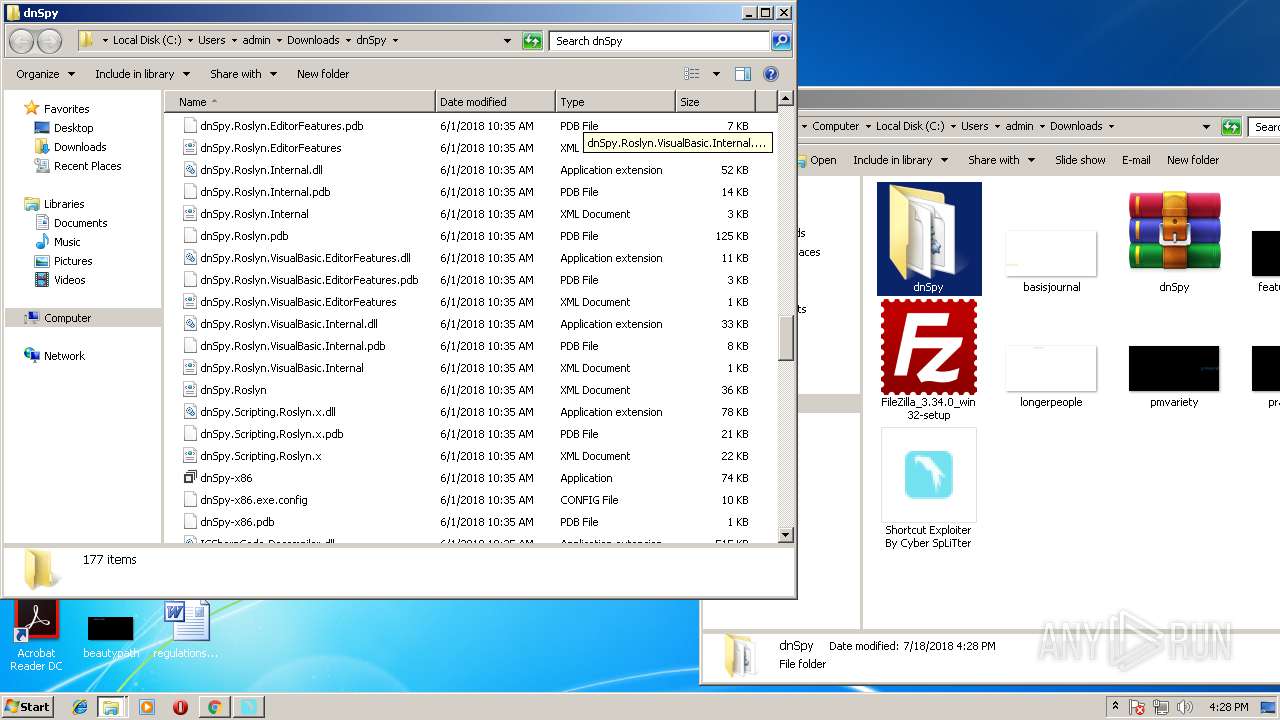
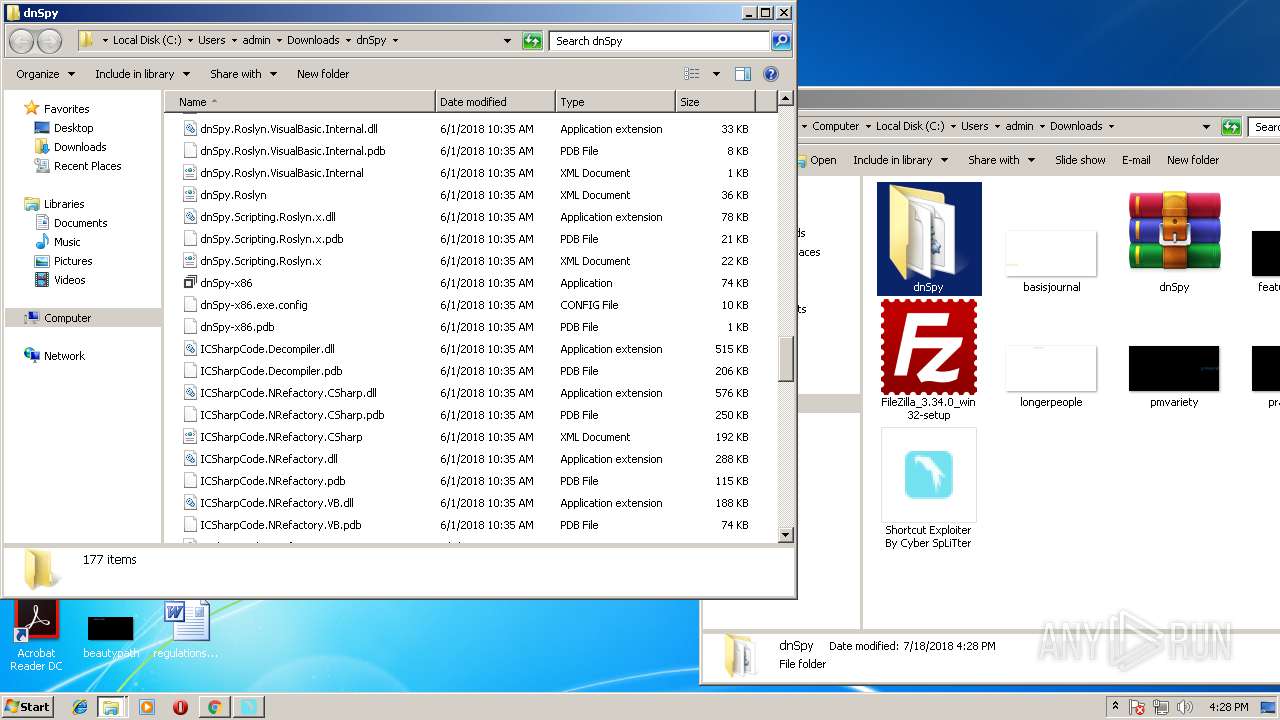
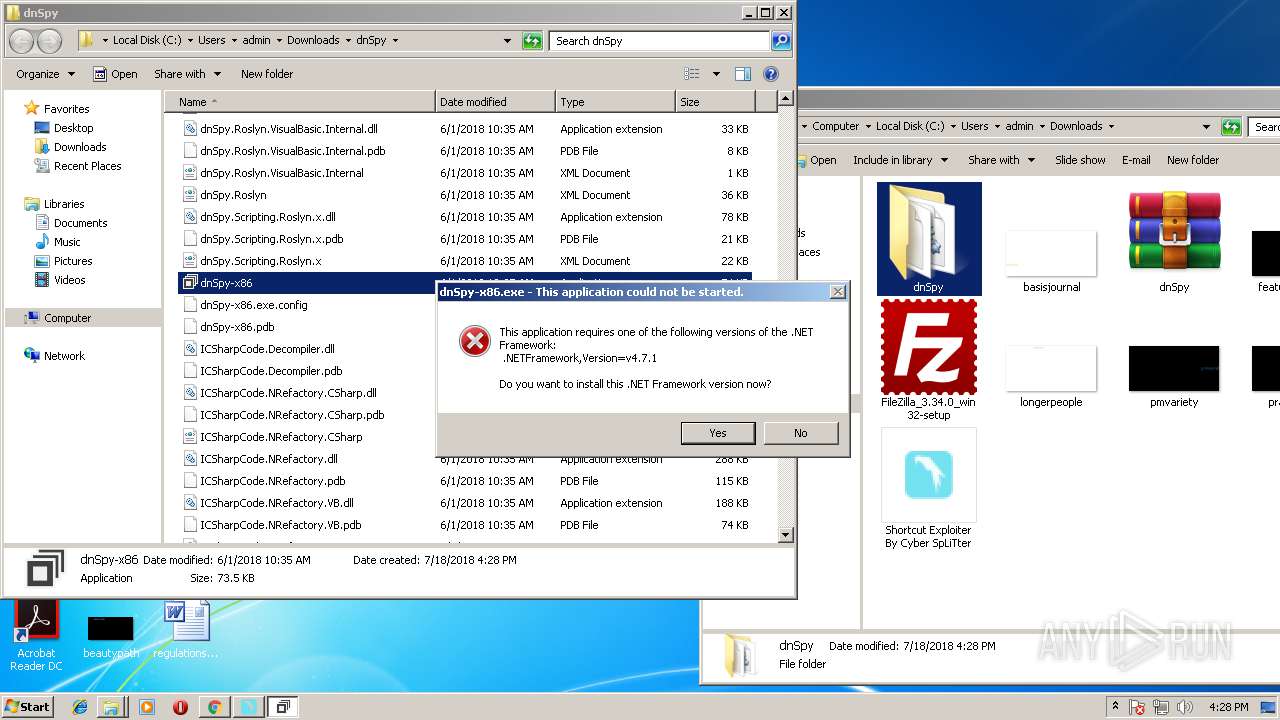
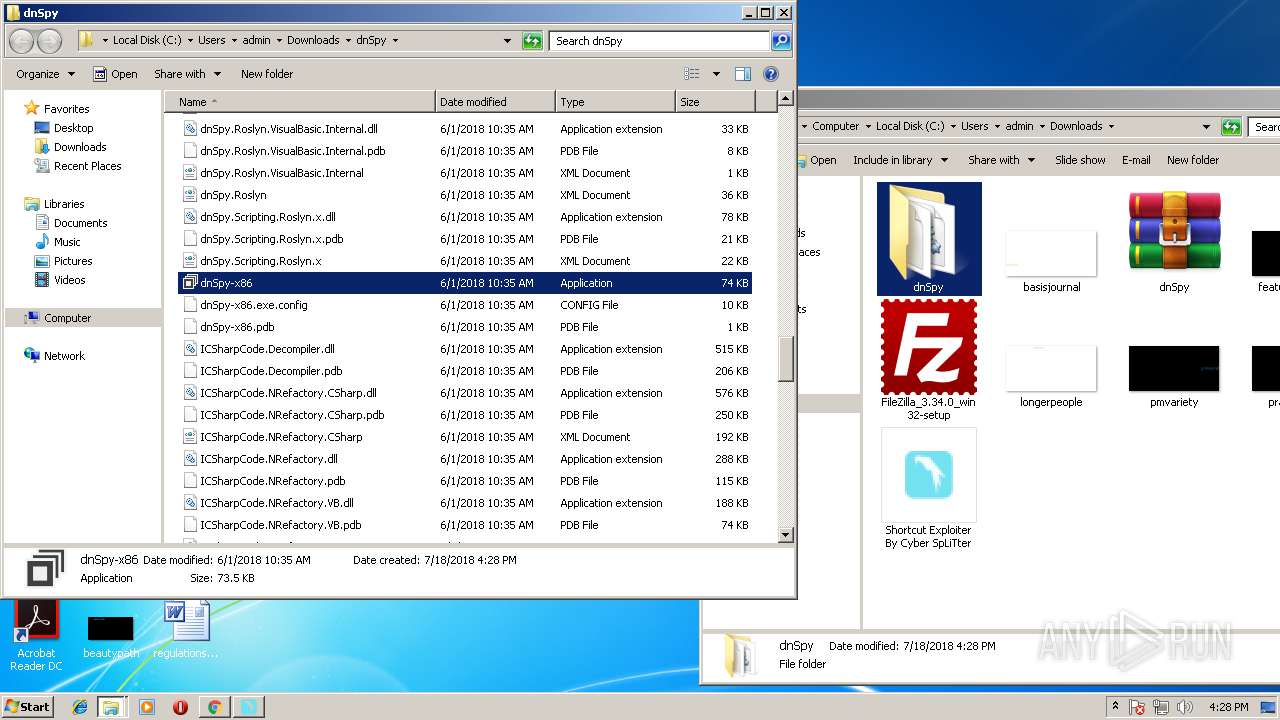
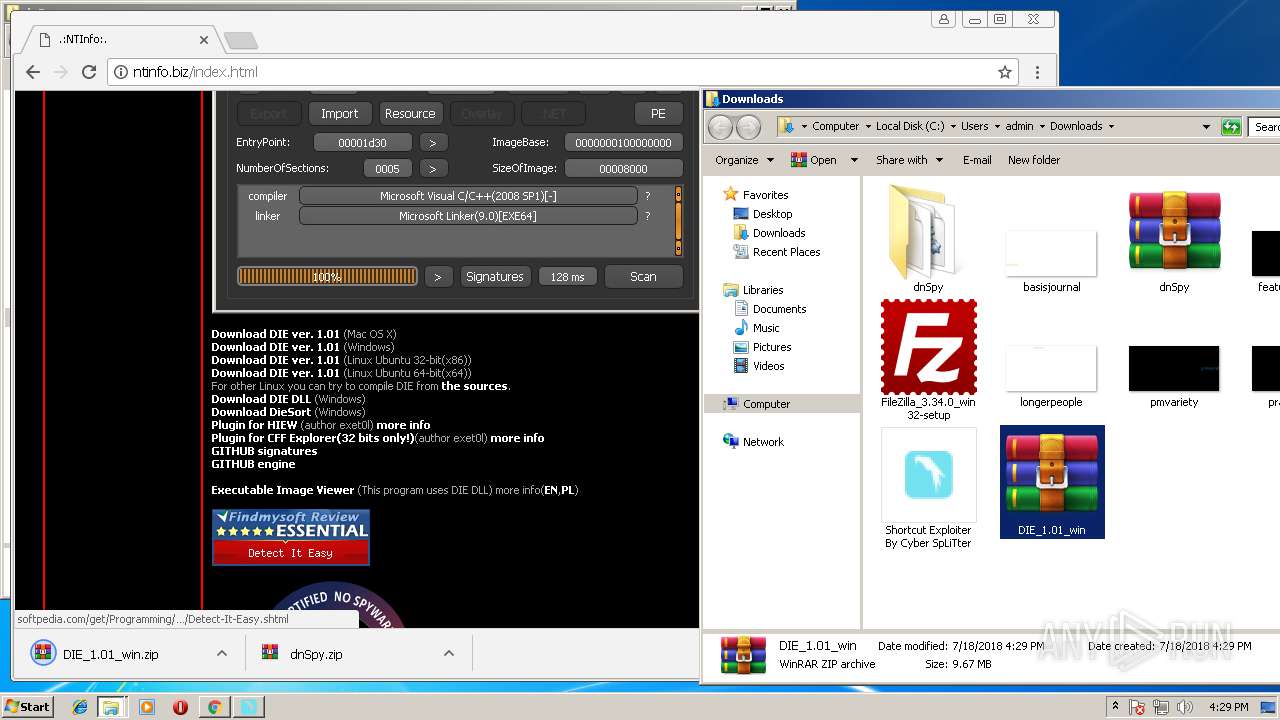
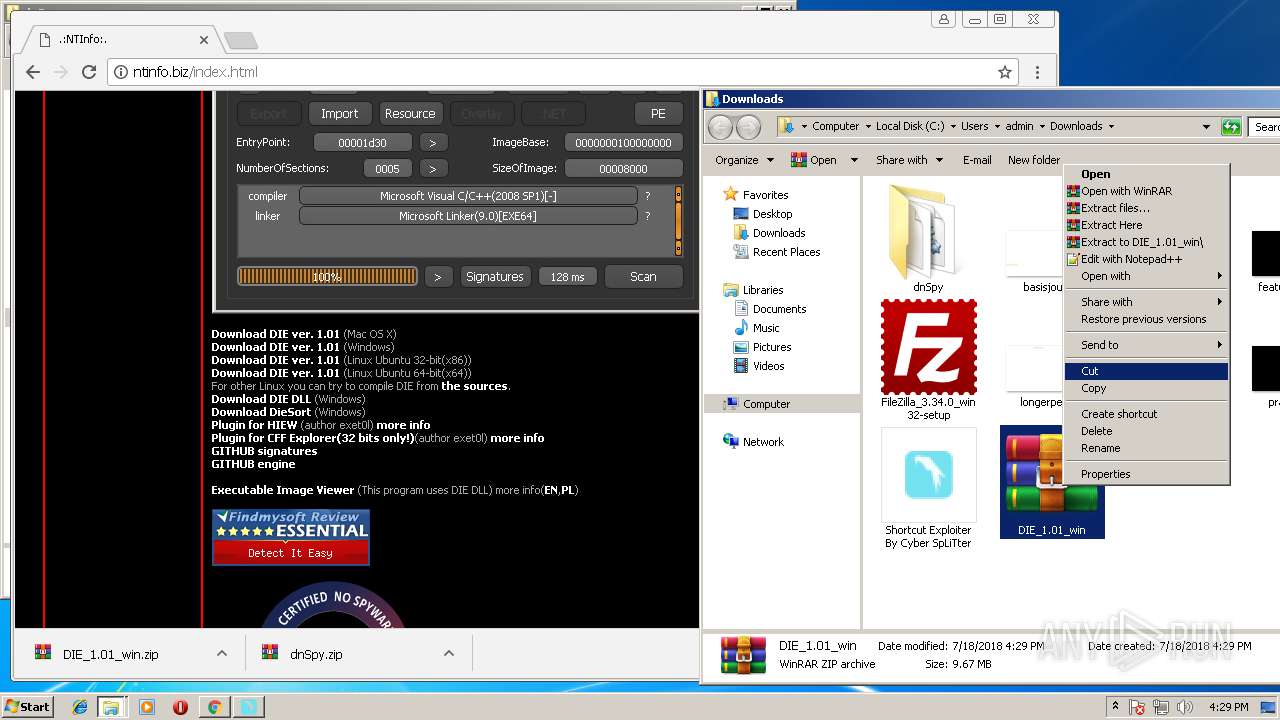
Application was dropped or rewritten from another process
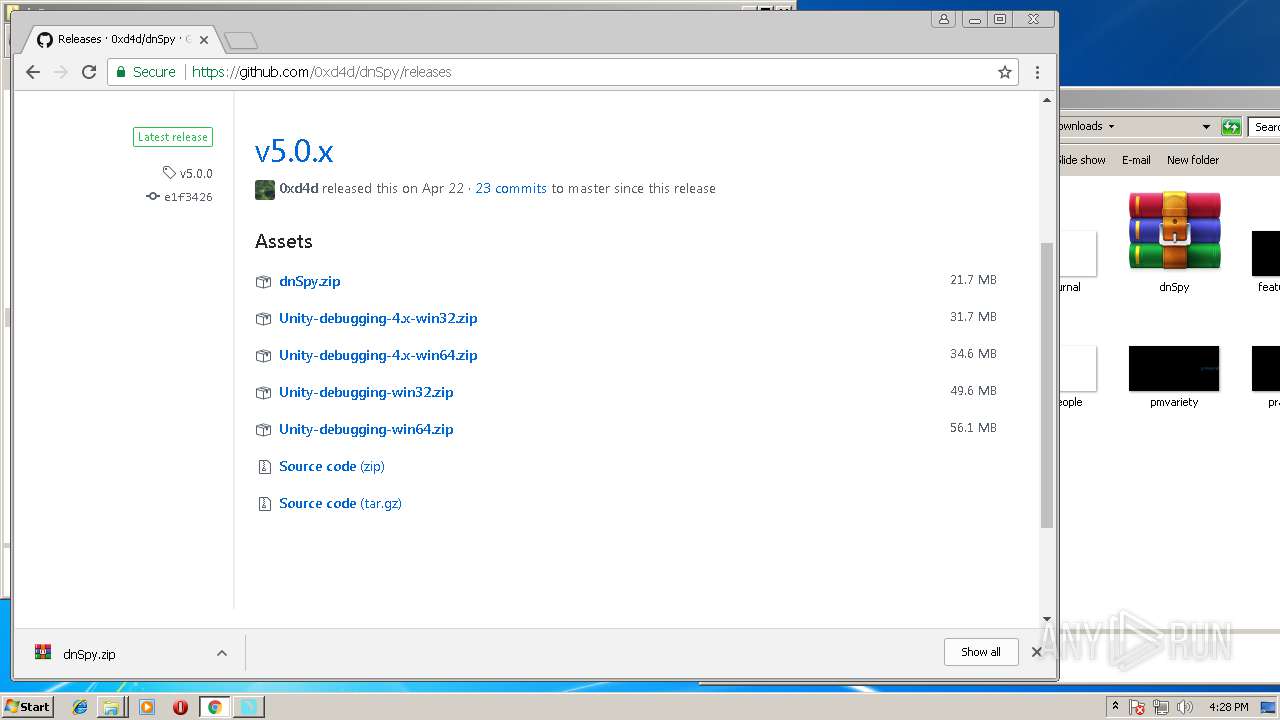
- dnSpy-x86.exe (PID: 404)
- die.exe (PID: 2728)
- die.exe (PID: 2780)
SUSPICIOUS
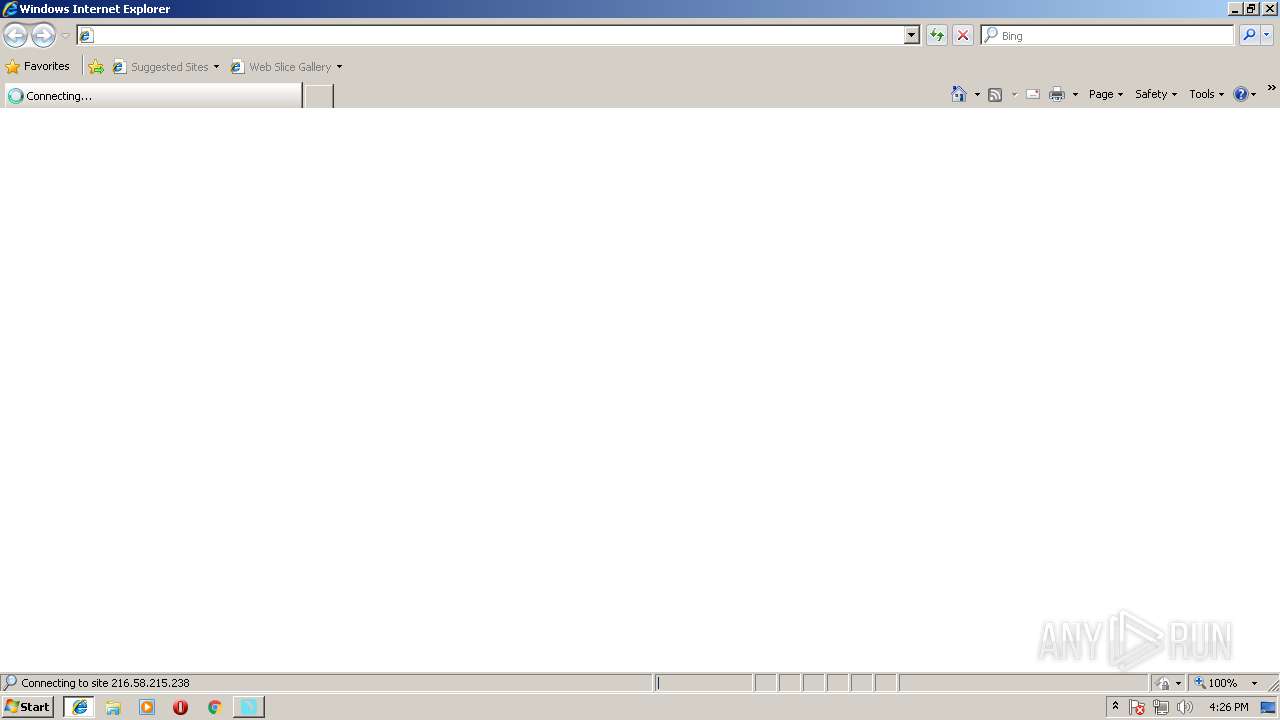
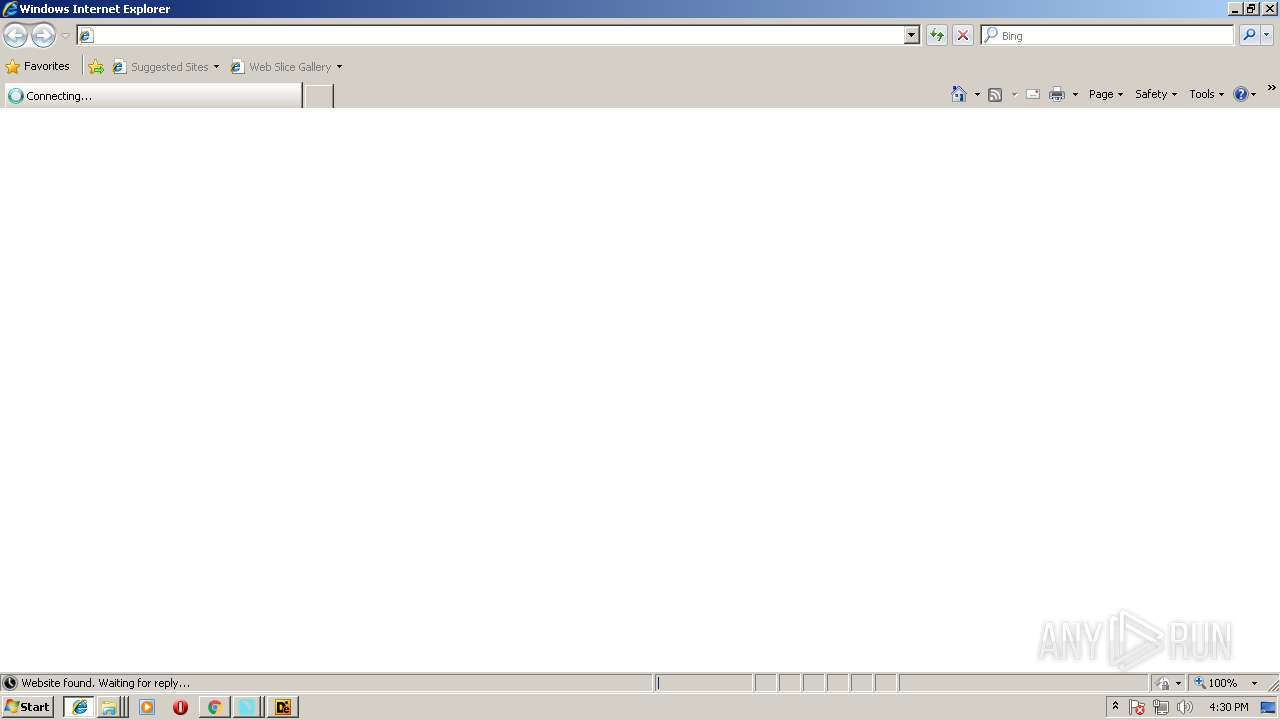
Starts Internet Explorer
- Shortcut Exploiter By Cyber SpLiTter.exe (PID: 2688)
- Shortcut Exploiter By Cyber SpLiTter.exe (PID: 3196)
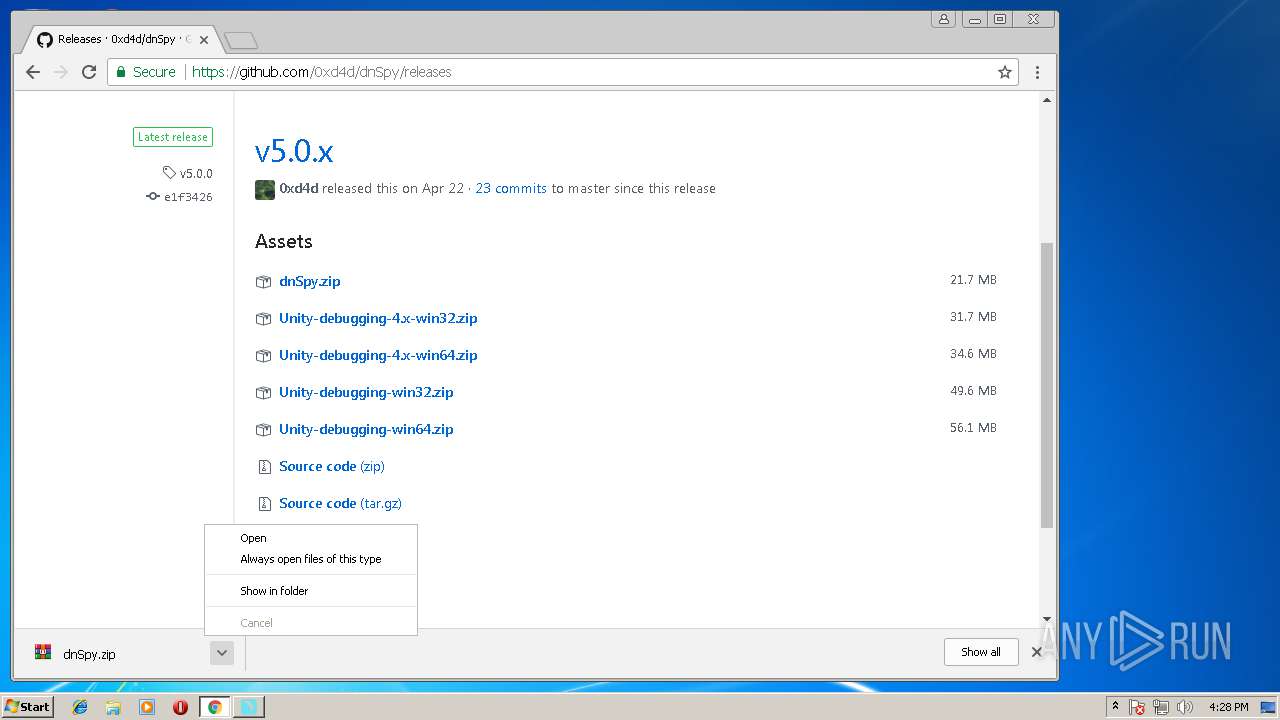
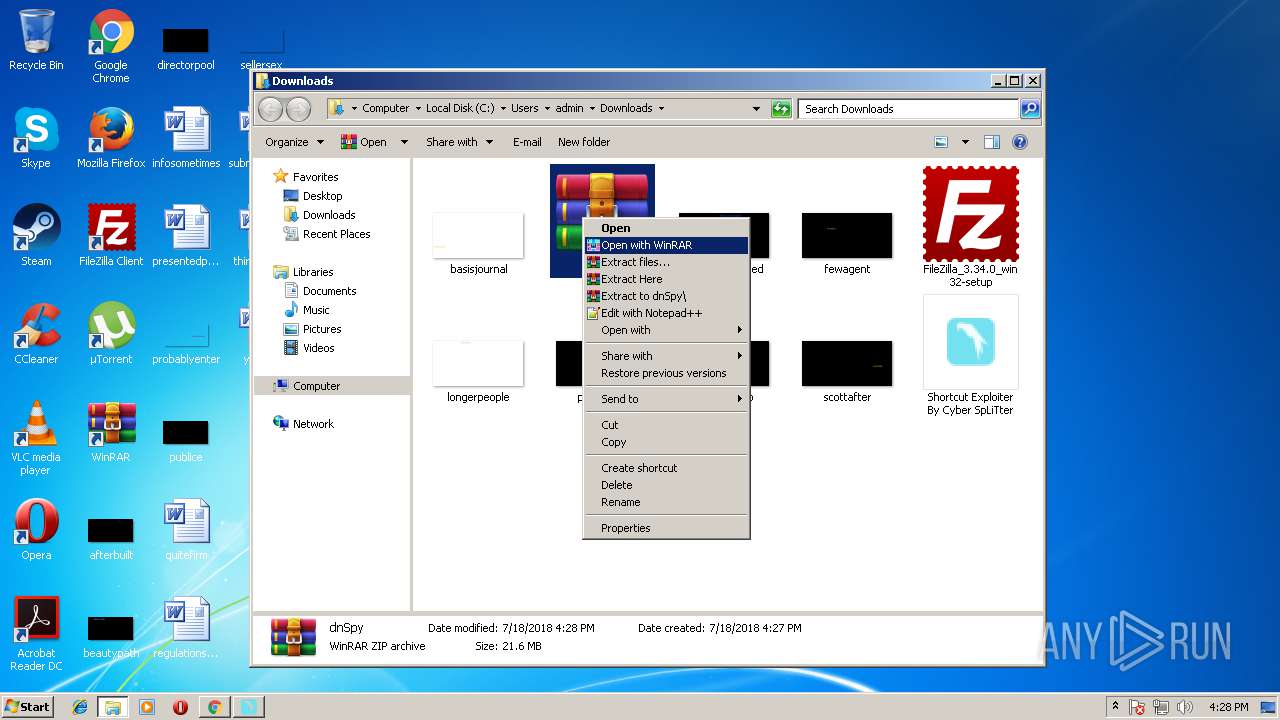
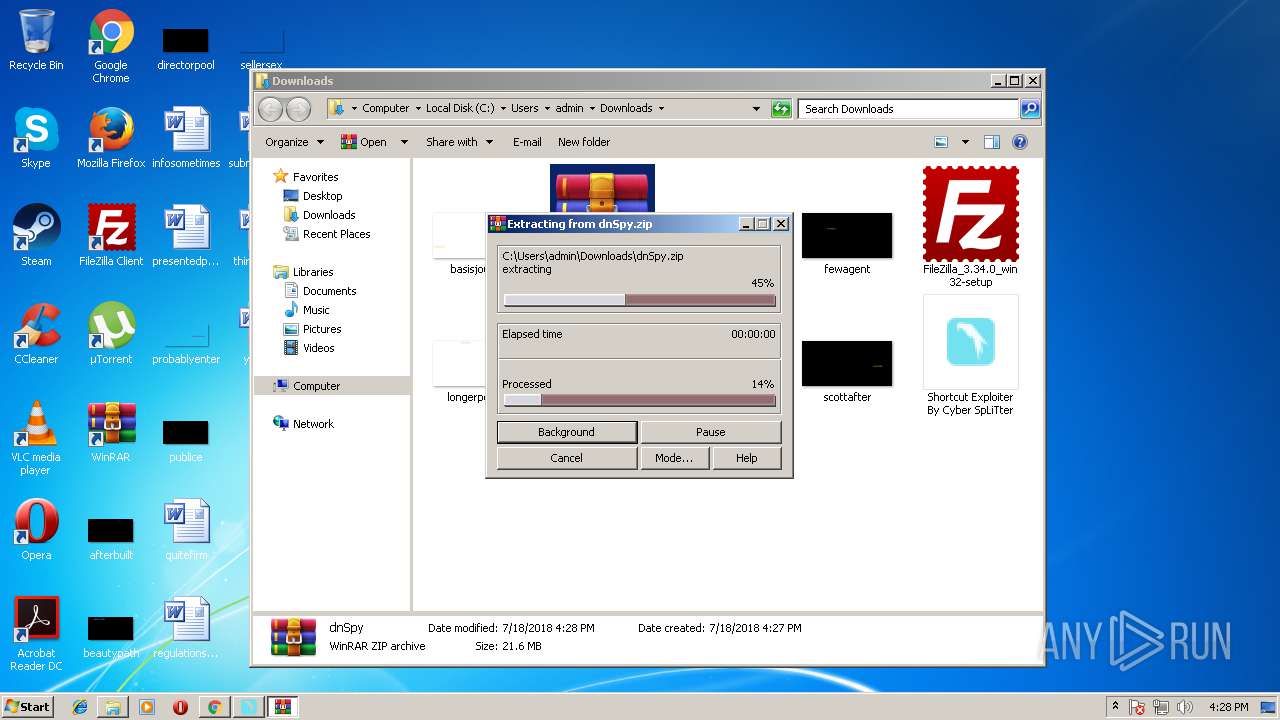
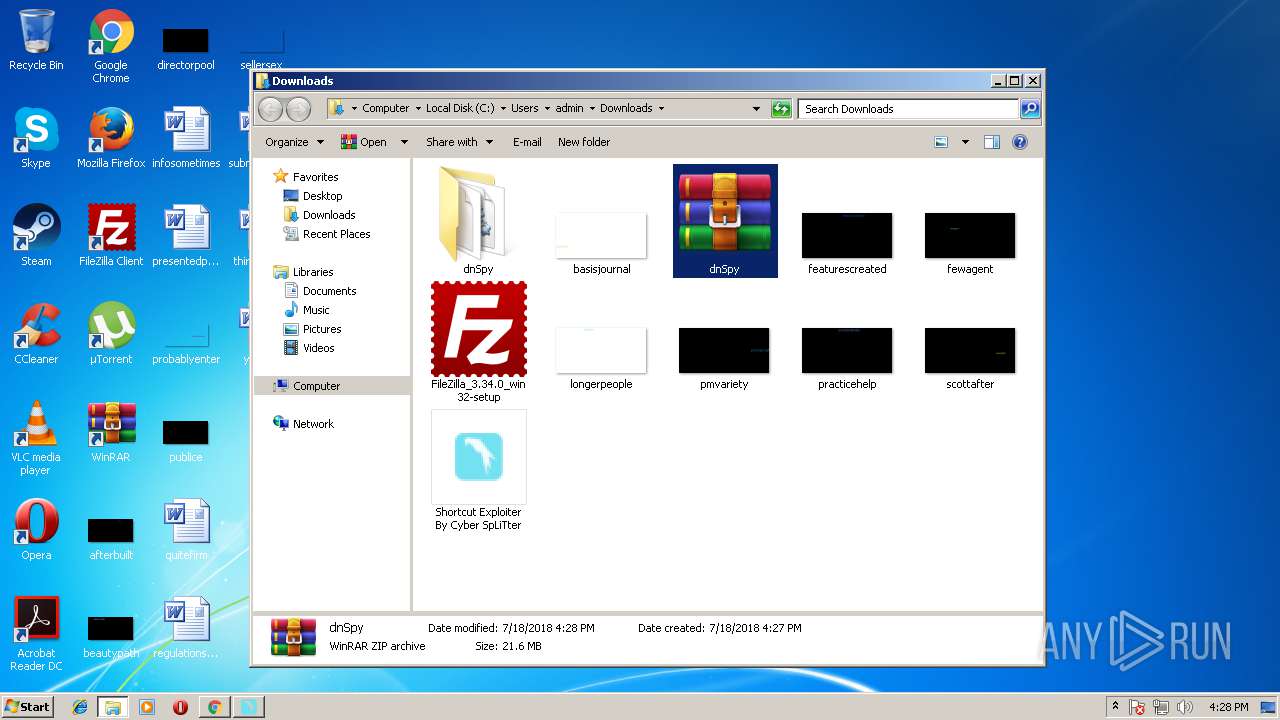
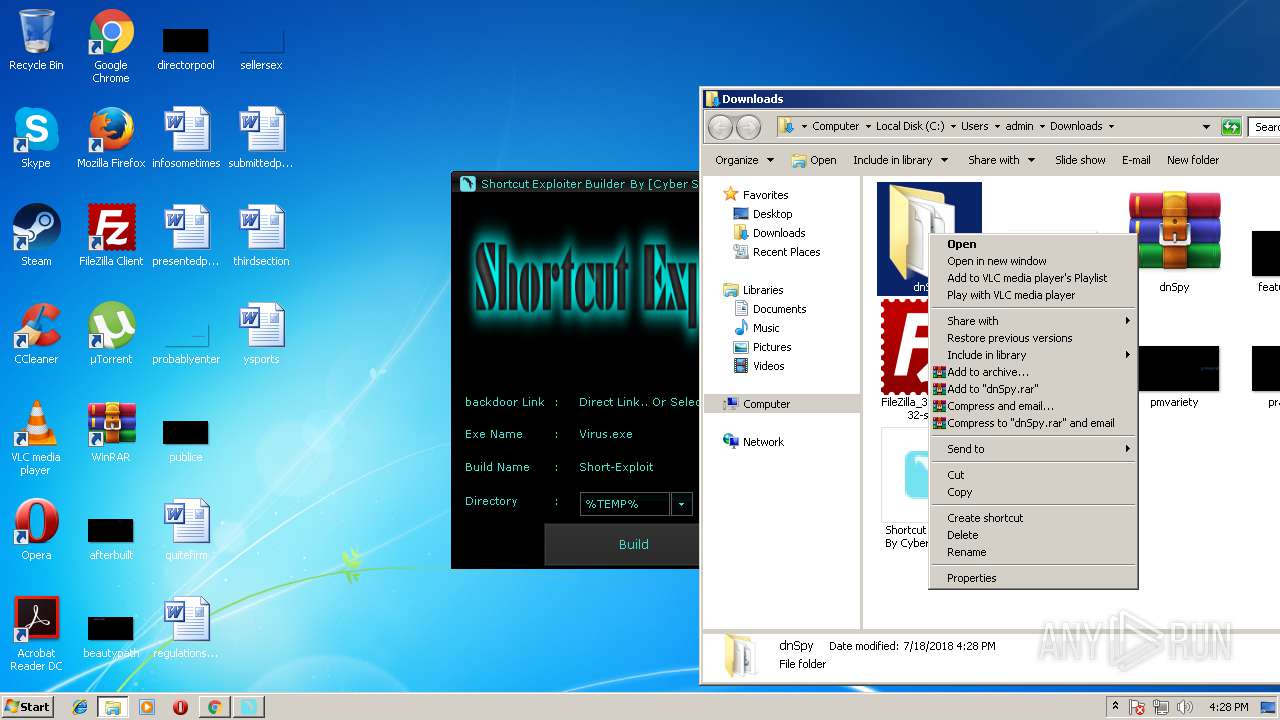
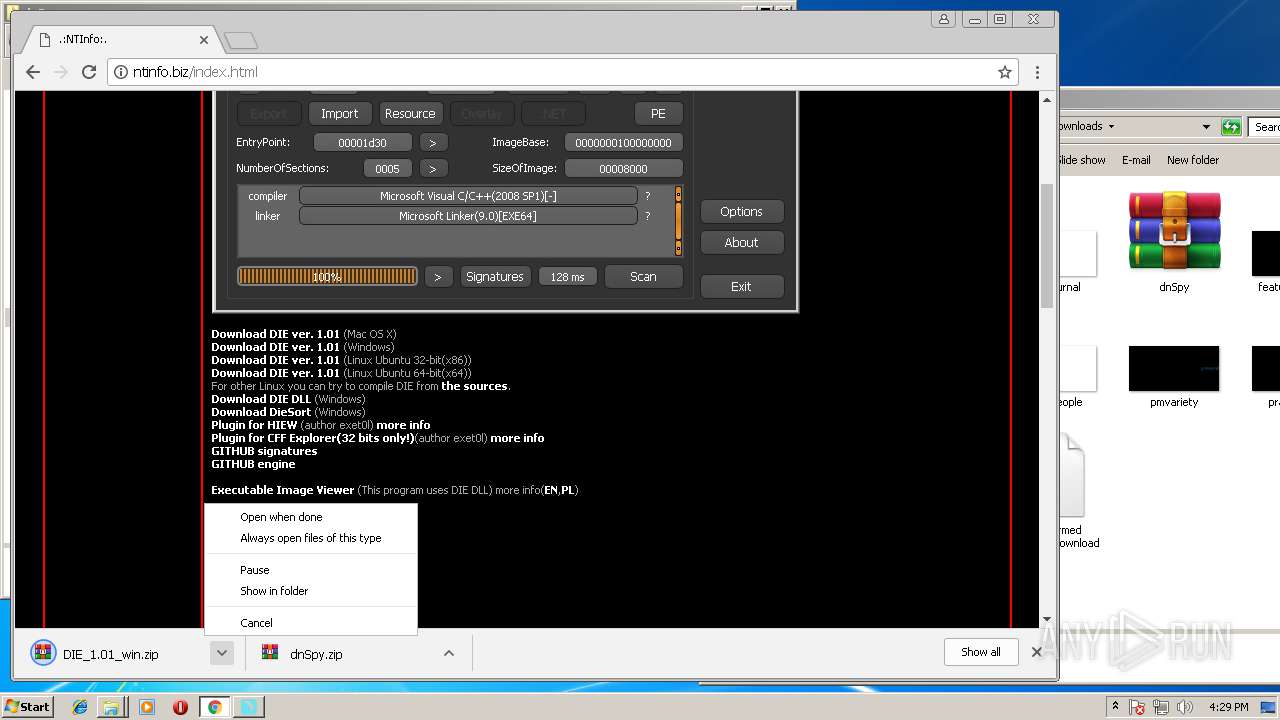
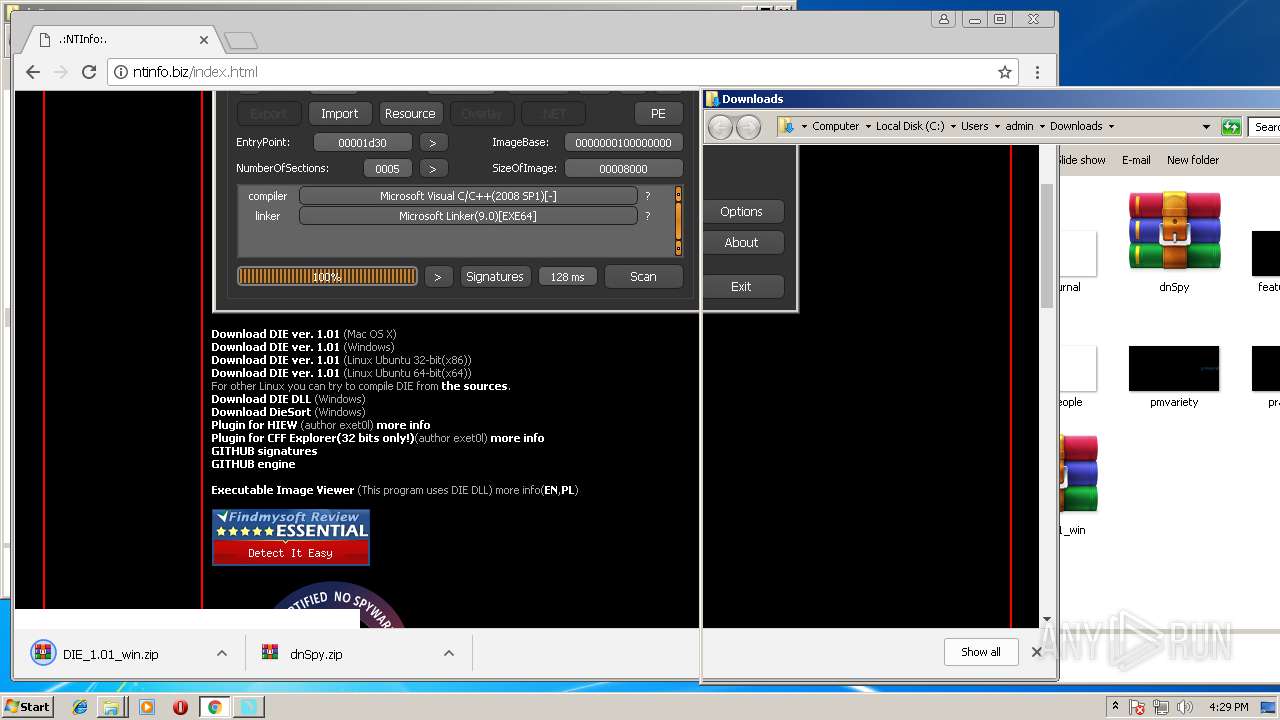
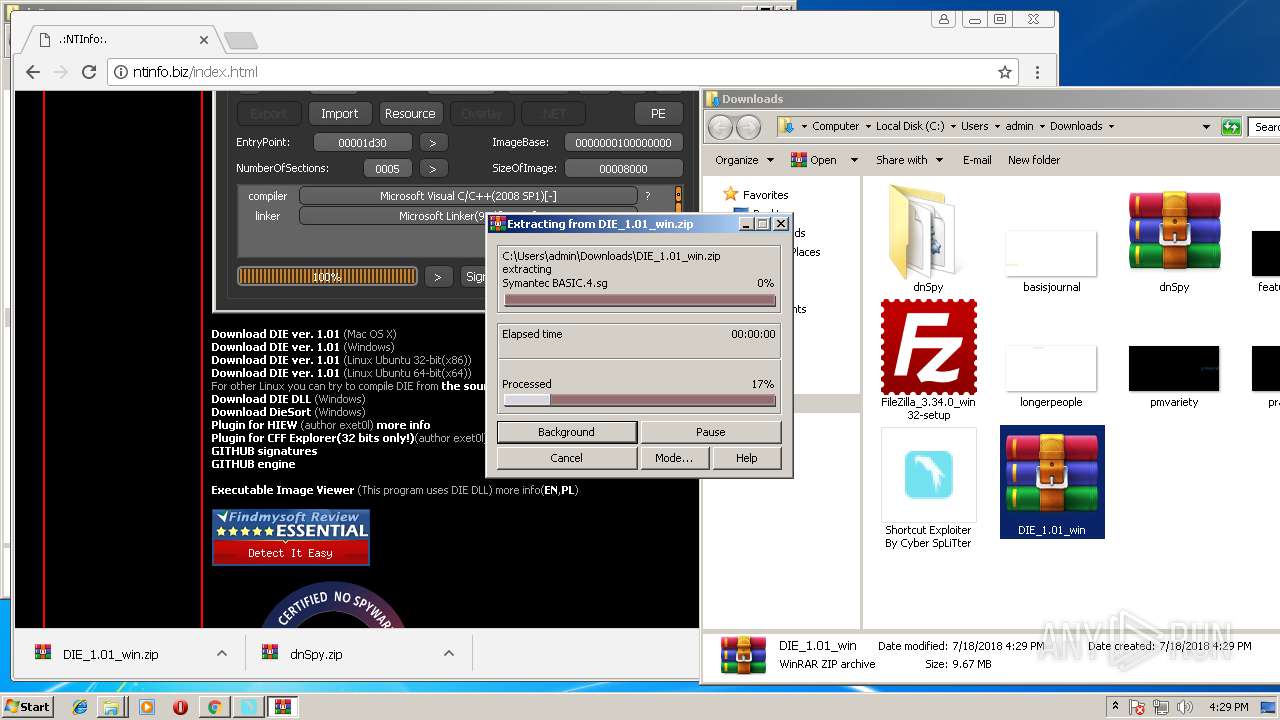
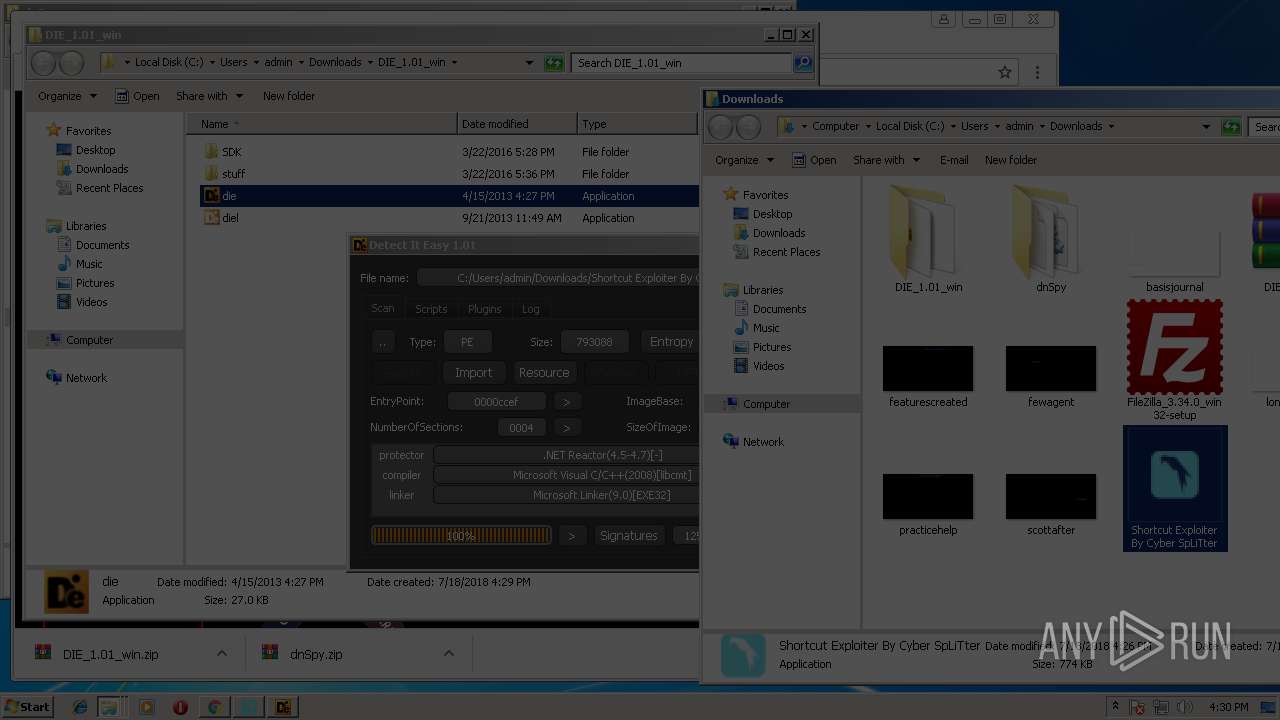
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3140)
- WinRAR.exe (PID: 1100)
Creates files in the program directory
- iexplore.exe (PID: 712)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2532)
- iexplore.exe (PID: 3360)
Reads Internet Cache Settings
- chrome.exe (PID: 1792)
- iexplore.exe (PID: 3792)
- iexplore.exe (PID: 712)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 1100)
- WinRAR.exe (PID: 3140)
- chrome.exe (PID: 1792)
Application launched itself
- chrome.exe (PID: 1792)
- iexplore.exe (PID: 3360)
Creates files in the user directory
- iexplore.exe (PID: 712)
Dropped object may contain URL's
- iexplore.exe (PID: 712)
- chrome.exe (PID: 1792)
- WinRAR.exe (PID: 1100)
- WinRAR.exe (PID: 3140)
- iexplore.exe (PID: 3360)
Changes settings of System certificates
- iexplore.exe (PID: 712)
Adds / modifies Windows certificates
- iexplore.exe (PID: 712)
Reads internet explorer settings
- iexplore.exe (PID: 712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:12:14 22:07:33+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 104448 |
| InitializedDataSize: | 687616 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xccef |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
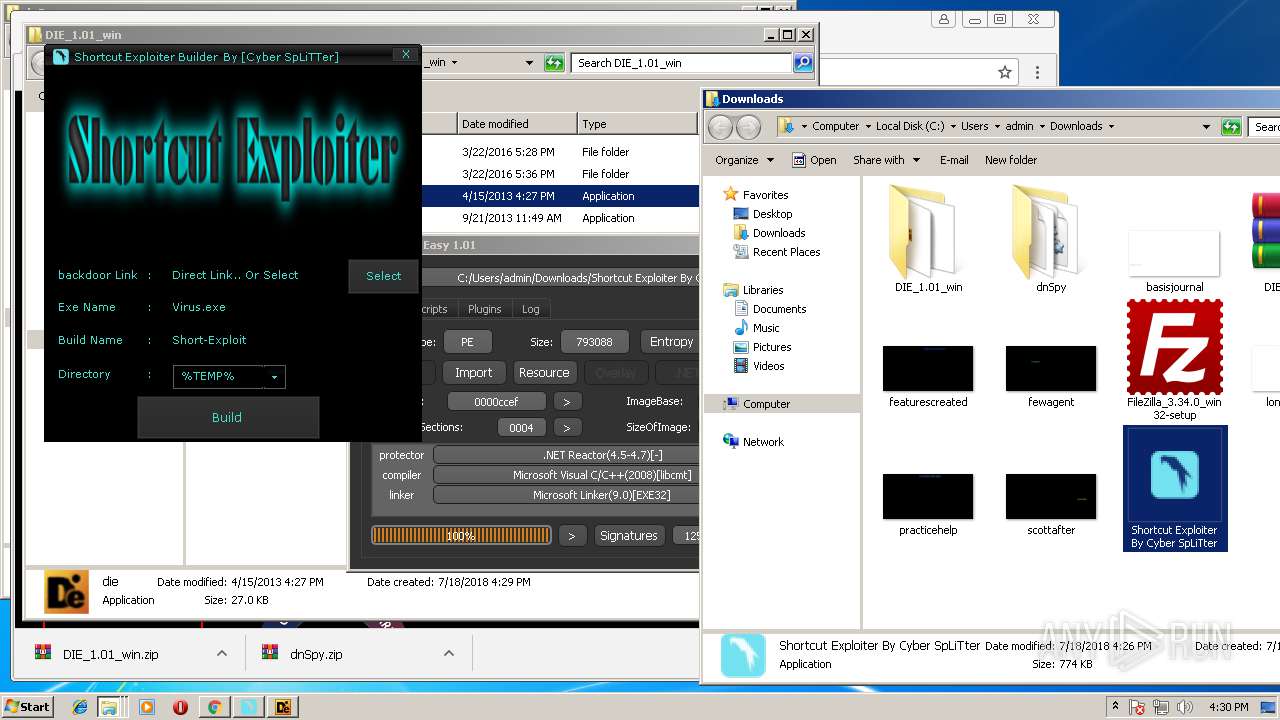
| Comments: | Cyber SpLiTTer |
| CompanyName: | Microsoft |
| FileDescription: | Shortcut Exploiter Builder |
| FileVersion: | 1.0.0.0 |
| InternalName: | Shortcut Exploiter loo.exe |
| LegalCopyright: | Copyright © 2018 |
| OriginalFileName: | Shortcut Exploiter loo.exe |
| ProductName: | Shortcut Exploiter Builder |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Dec-2017 21:07:33 |
| Debug artifacts: | |
| Comments: | Cyber SpLiTTer |
| CompanyName: | Microsoft |
| FileDescription: | Shortcut Exploiter Builder |
| FileVersion: | 1.0.0.0 |
| InternalName: | Shortcut Exploiter loo.exe |
| LegalCopyright: | Copyright © 2018 |
| OriginalFilename: | Shortcut Exploiter loo.exe |
| ProductName: | Shortcut Exploiter Builder |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 14-Dec-2017 21:07:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000196D8 | 0x00019800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.74599 |
.rdata | 0x0001B000 | 0x00006DF2 | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.44313 |
.data | 0x00022000 | 0x000030C0 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.26244 |
.rsrc | 0x00026000 | 0x0009F9FC | 0x0009FA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99894 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
__ | 7.99971 | 649475 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
~ | 4.9375 | 32 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
KERNEL32.dll |
OLEAUT32.dll |
mscoree.dll |
ole32.dll |
Total processes
68
Monitored processes
23
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
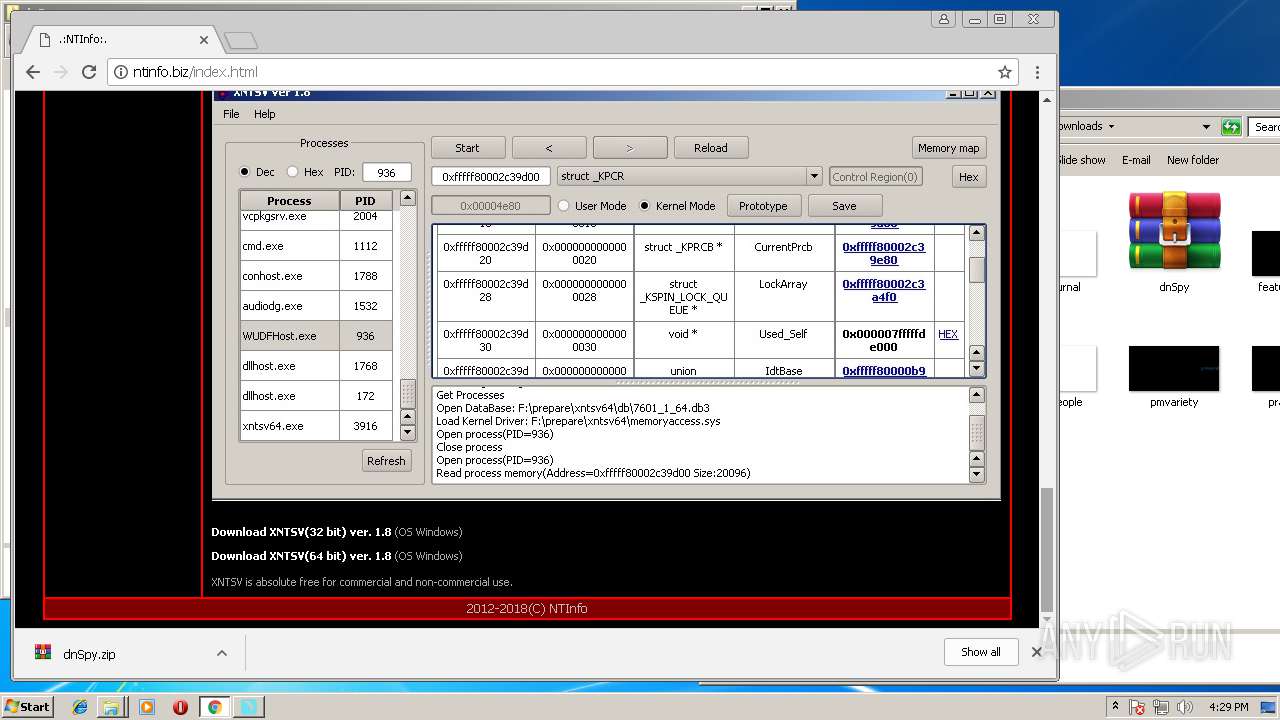
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
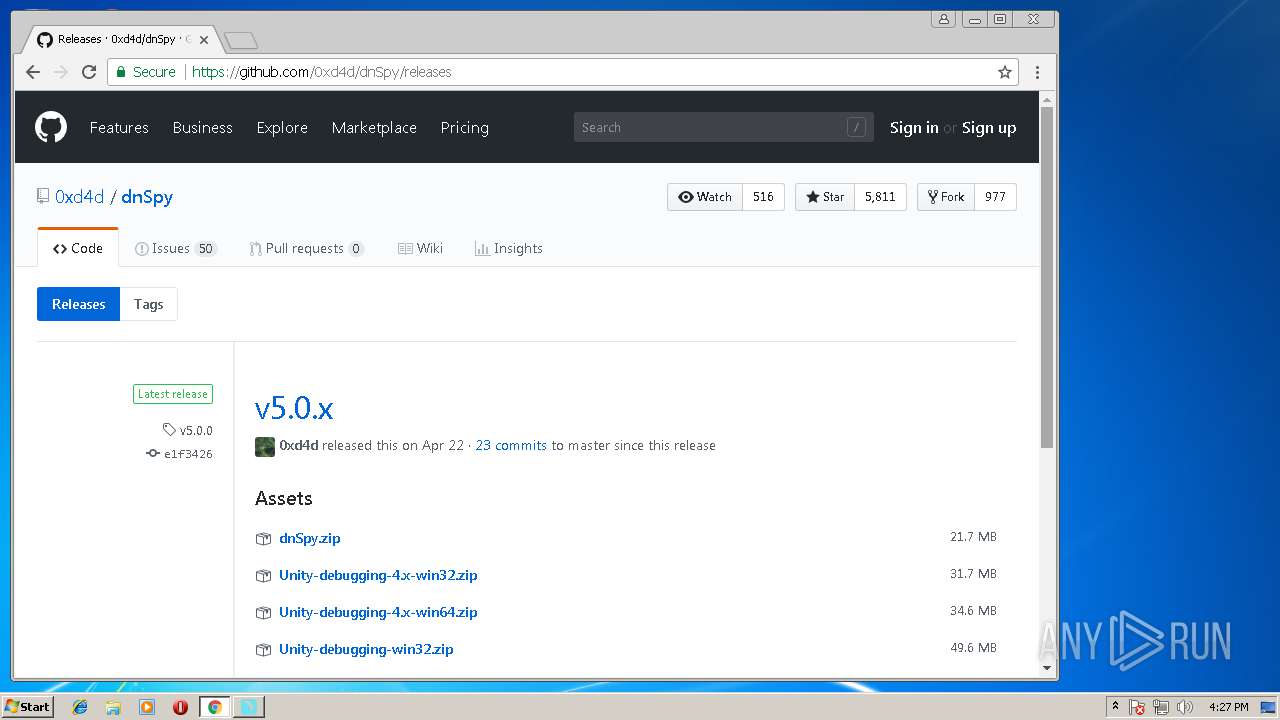
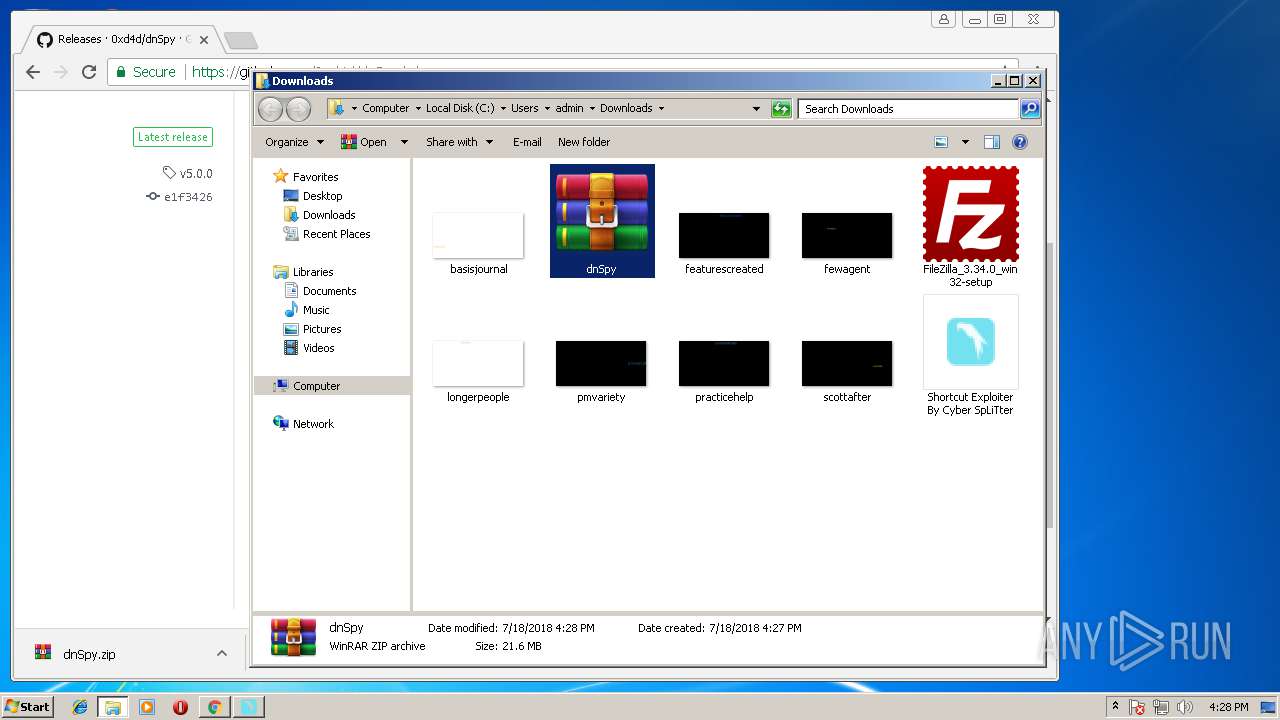
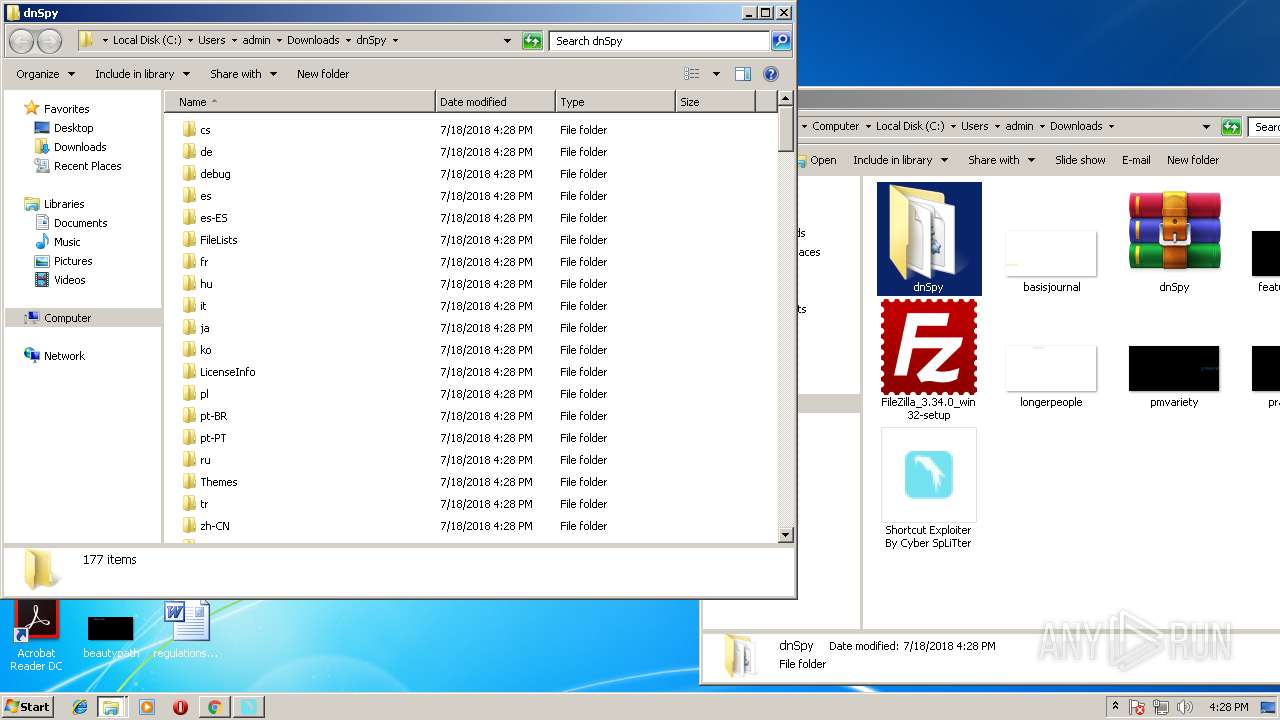
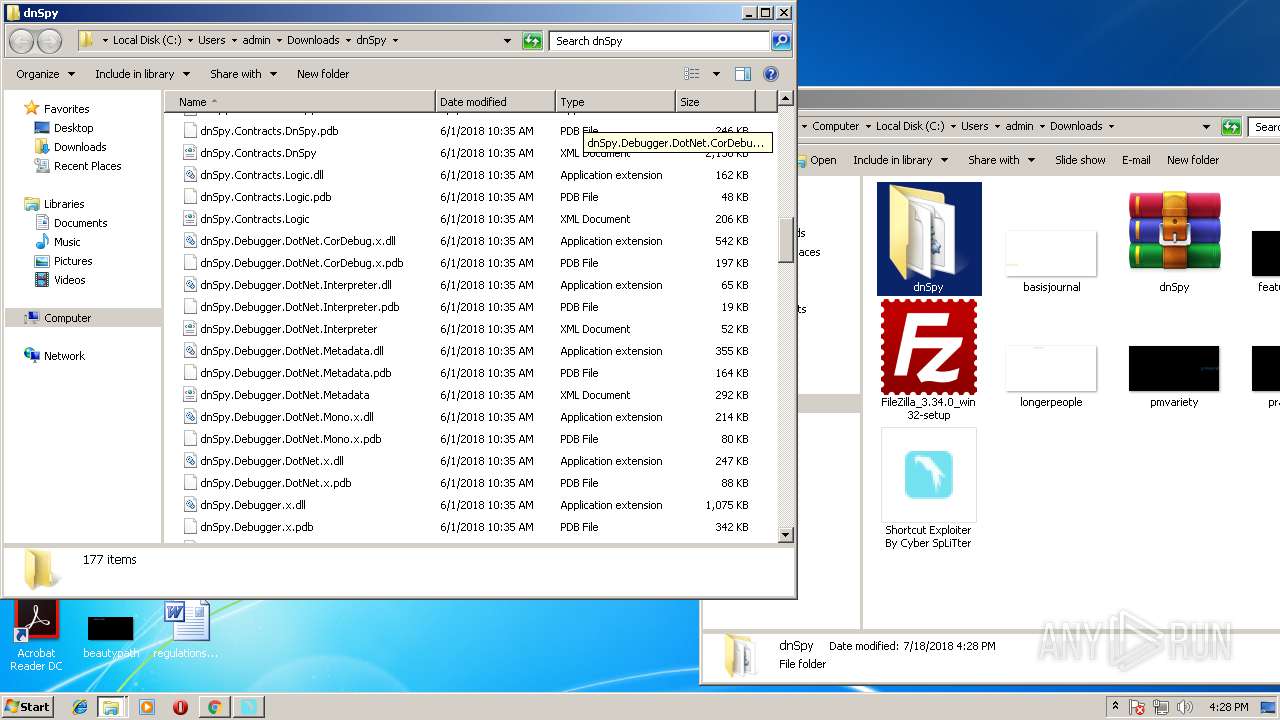
| 404 | "C:\Users\admin\Downloads\dnSpy\dnSpy-x86.exe" | C:\Users\admin\Downloads\dnSpy\dnSpy-x86.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: dnSpy-x86 Exit code: 2148734720 Version: 5.0.5.0 Modules
| |||||||||||||||
| 436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1740,4250128447171975602,4676652093211823654,131072 --lang=en-US --service-request-channel-token=FA2FA2DC9894D488C2A0F7551E5A3A24 --mojo-platform-channel-handle=4416 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1892 --on-initialized-event-handle=296 --parent-handle=300 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 712 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3360 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1100 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\dnSpy.zip" C:\Users\admin\Downloads\dnSpy\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1740,4250128447171975602,4676652093211823654,131072 --service-pipe-token=198E933806FD4053E3FFECB8C036D36A --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --blink-settings=disallowFetchForDocWrittenScriptsInMainFrame=false,disallowFetchForDocWrittenScriptsInMainFrameOnSlowConnections=true --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=198E933806FD4053E3FFECB8C036D36A --renderer-client-id=2 --mojo-platform-channel-handle=1888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1740,4250128447171975602,4676652093211823654,131072 --service-pipe-token=D6C2868A1C60F3D10B5DDEB626802258 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --blink-settings=disallowFetchForDocWrittenScriptsInMainFrame=false,disallowFetchForDocWrittenScriptsInMainFrameOnSlowConnections=true --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=D6C2868A1C60F3D10B5DDEB626802258 --renderer-client-id=5 --mojo-platform-channel-handle=3444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1740,4250128447171975602,4676652093211823654,131072 --lang=en-US --service-request-channel-token=B0635731FCED9A4C7A0F4DB0C0EF0A6A --mojo-platform-channel-handle=828 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1740,4250128447171975602,4676652093211823654,131072 --lang=en-US --service-request-channel-token=A62A34843B0AFEFE7A461FDF8E0AD09F --mojo-platform-channel-handle=2064 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
Total events
2 190
Read events
1 914
Write events
265
Delete events
11
Modification events
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003E000000010000000000000000000000000000000000000000000000B096B68868EBD301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000D8BFD602040000000000000000000000000000000000000000000000F4BFD602040000000000000000000000000000000000000000000000D8372A0000000000FFFFFFFF000000000000000000000000010000002E00000000000000000000000000000002000000C0A801640000000000000000D84ED505AC02000005000000010000000000000000000000010000000000000000000000BF060000000000000000000000000000000000001000000088C0D60204000000000000000000000000000000000000000000000000000000C8E40C00000000000C0000000000000000000000 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {01A7C34B-8A9F-11E8-ACE5-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070700030012000F001A003900D503 | |||
Executable files
247
Suspicious files
130
Text files
1 398
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\XB3OCR2W\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2532 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF44976C40C0AEA04B.TMP | — | |
MD5:— | SHA256:— | |||
| 2532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{0897FB32-8A9F-11E8-ACE5-5254004AAD11}.dat | — | |
MD5:— | SHA256:— | |||
| 2532 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1387B75972D65B26.TMP | — | |
MD5:— | SHA256:— | |||
| 2532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{01A7C34C-8A9F-11E8-ACE5-5254004AAD11}.dat | — | |
MD5:— | SHA256:— | |||
| 2532 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFFA3CF1667F1181B7.TMP | — | |
MD5:— | SHA256:— | |||
| 2532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{01A7C34B-8A9F-11E8-ACE5-5254004AAD11}.dat | — | |
MD5:— | SHA256:— | |||
| 1792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000006.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e5103555-f6f9-4495-bbbe-c73a436a6822.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
72
TCP/UDP connections
170
DNS requests
115
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1792 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAoGMEJ%2FW7ztaVc5ZZO2RR8%3D | US | der | 471 b | whitelisted |
2532 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
1792 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
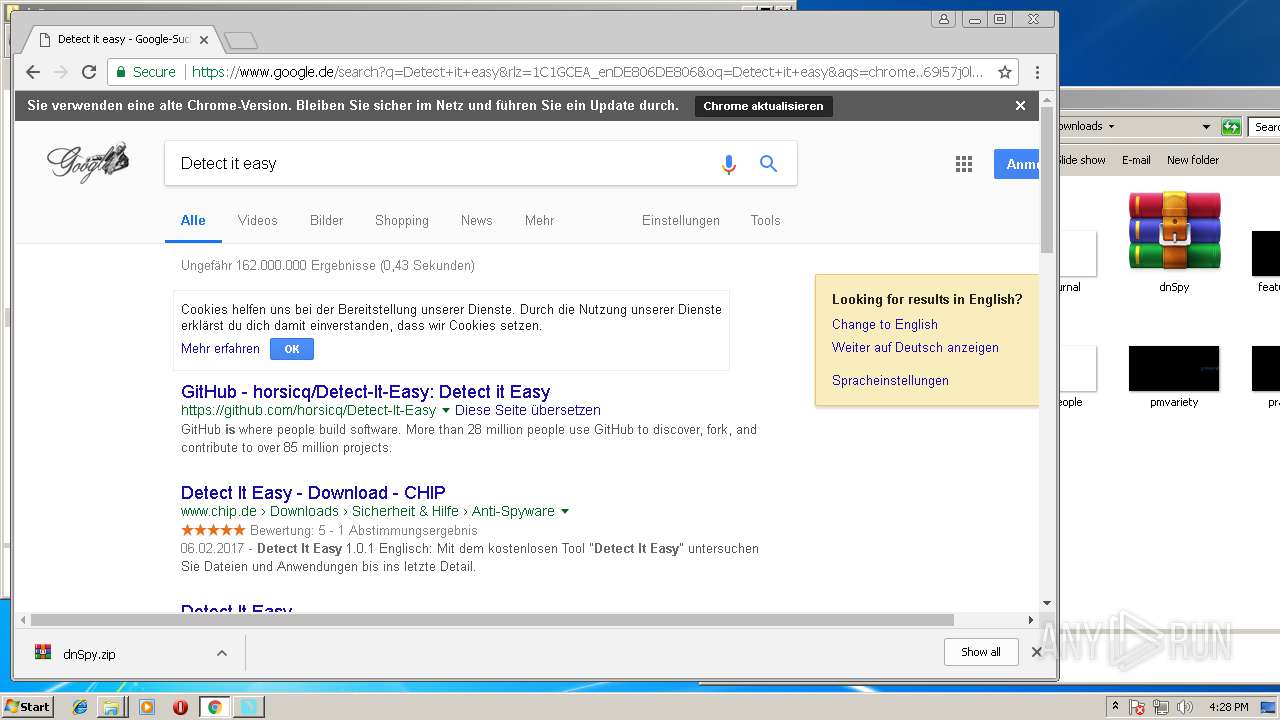
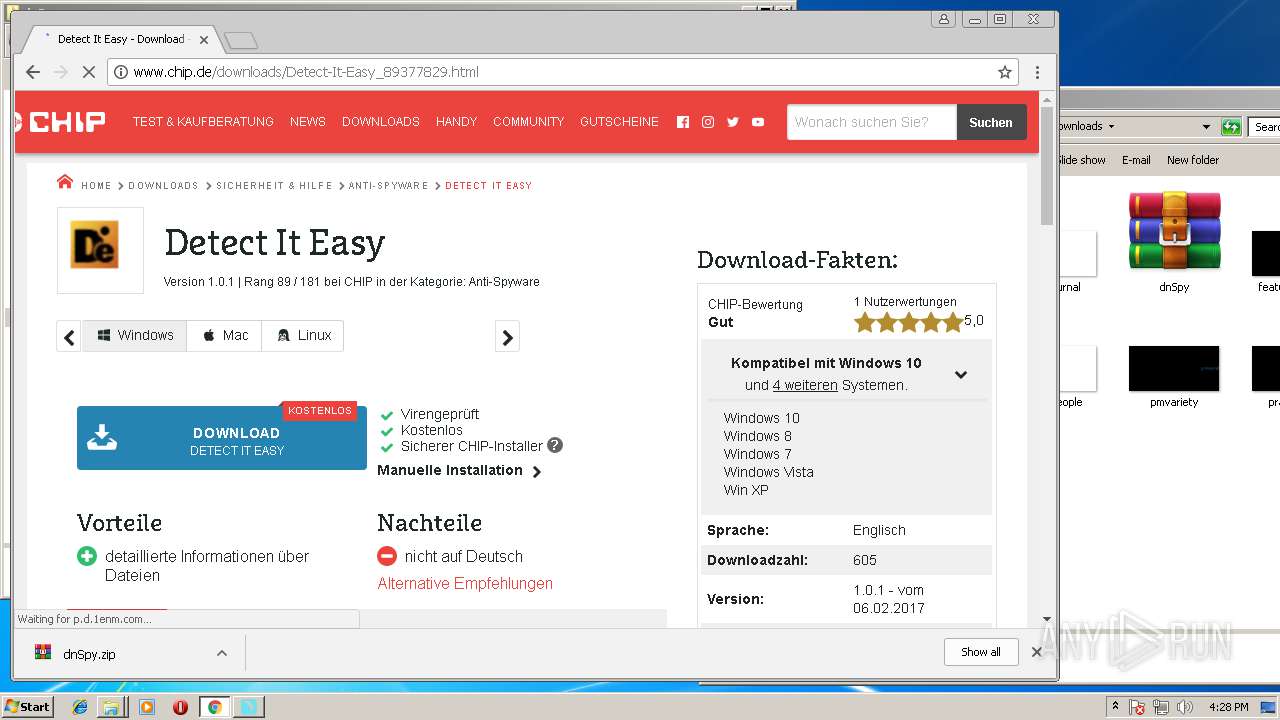
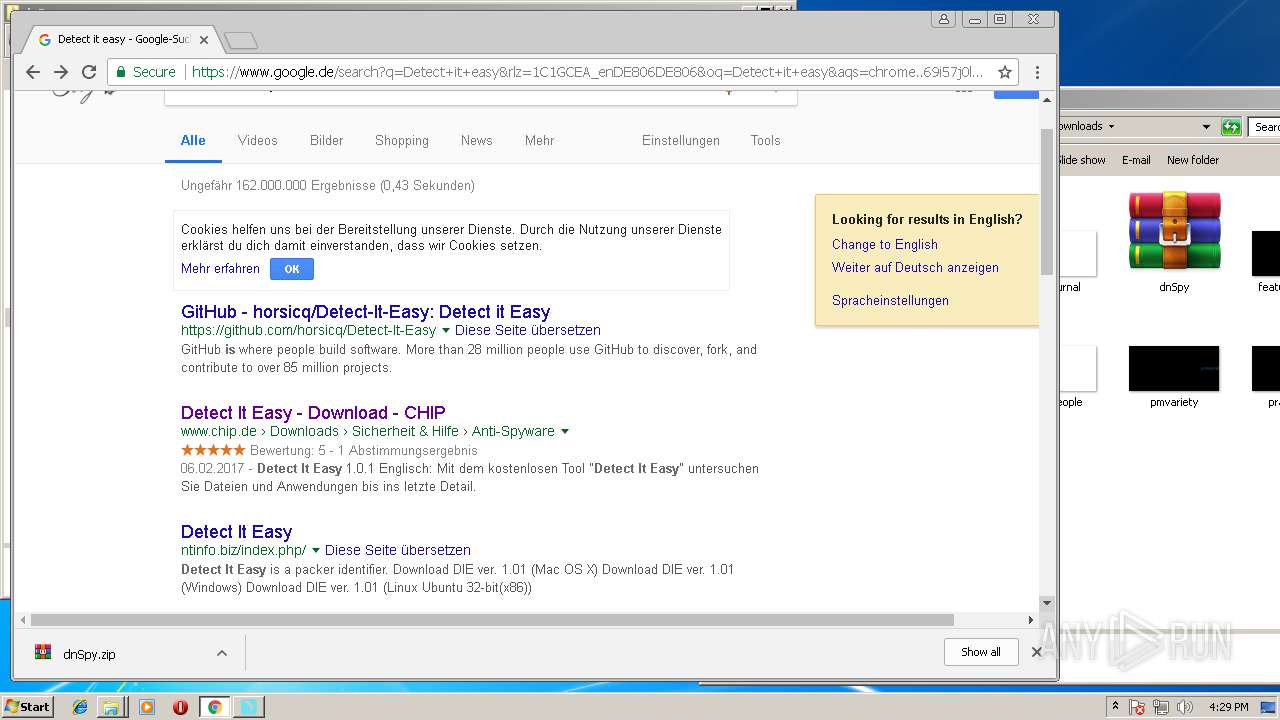
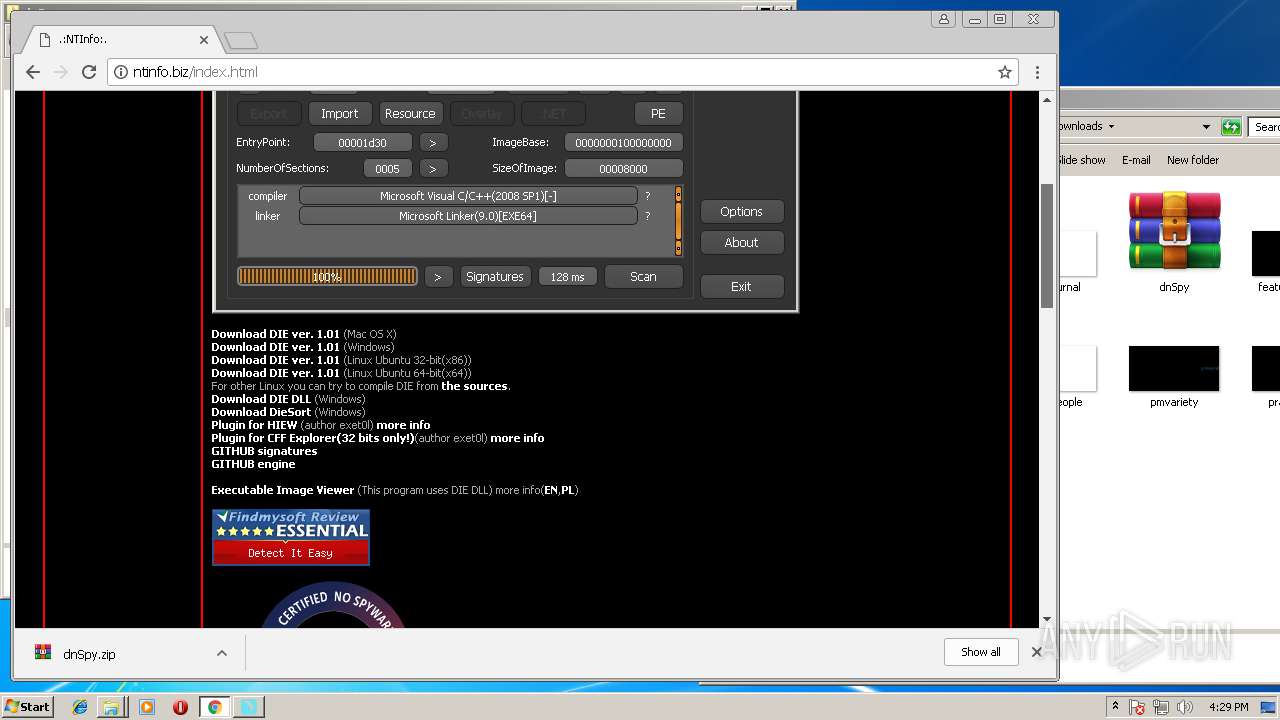
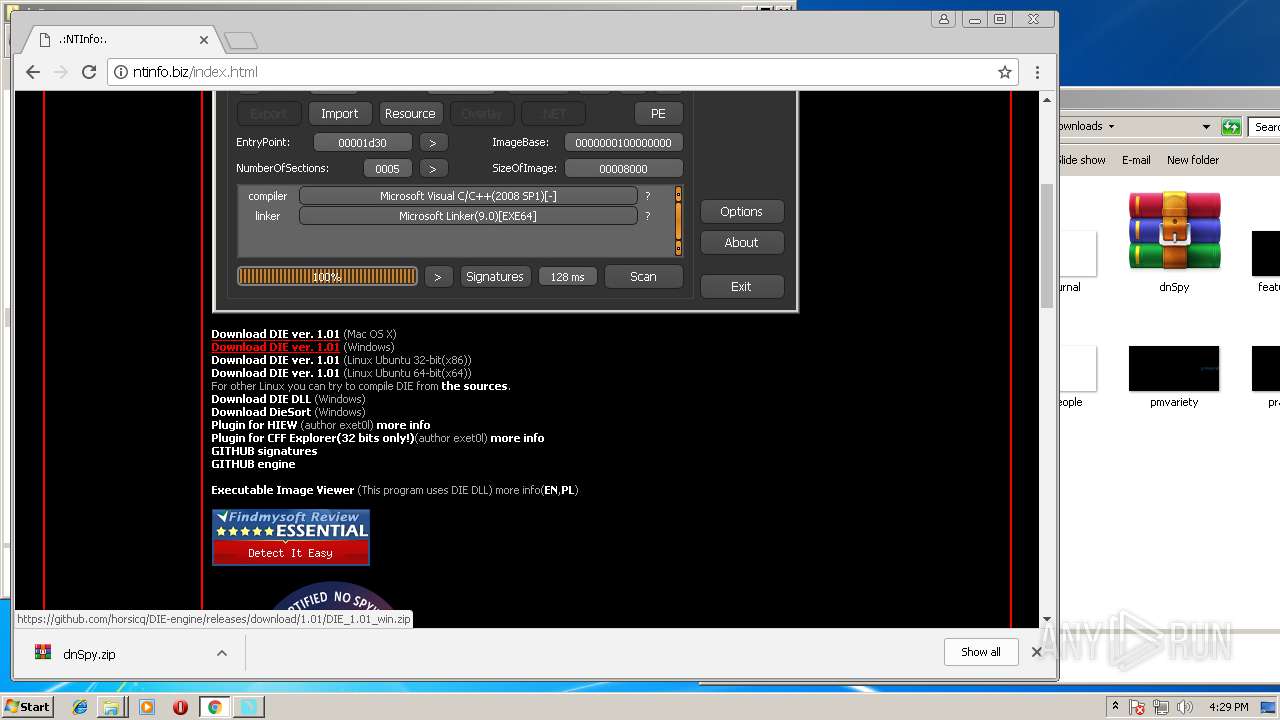
1792 | chrome.exe | GET | 200 | 2.18.235.97:80 | http://www.chip.de/downloads/Detect-It-Easy_89377829.html | unknown | html | 82.7 Kb | whitelisted |
1792 | chrome.exe | GET | 200 | 172.217.168.78:80 | http://clients1.google.com/tools/pso/ping?as=chrome&brand=GCEA&pid=&hl=en&events=C1F,C1I,C2I,C7I,C1S,C7S&rep=2&rlz=C1:,C2:,C7:&id=4E3014F88A1776A95D57E2AE3211A742FF35E455C4BA364784 | US | text | 140 b | whitelisted |
1792 | chrome.exe | GET | 200 | 104.104.187.133:80 | http://adtm.chip.de/3469f5db1bb7fc021f6829a881d1c8a6df48a471/satelliteLib-1f360a6db91f2db811a8431bff692897ac6cf408.js | NL | text | 30.4 Kb | whitelisted |
1792 | chrome.exe | GET | 200 | 2.18.235.97:80 | http://www.chip.de/download/assets/download-v1.4.22.css | unknown | text | 78.1 Kb | whitelisted |
1792 | chrome.exe | GET | 200 | 104.111.244.135:80 | http://a.bf-ad.net/makabo/ads_fol_init.js | NL | text | 33 b | whitelisted |
1792 | chrome.exe | GET | 200 | 2.18.235.97:80 | http://www.chip.de/download/assets/hook-v1.4.22.js | unknown | text | 97.7 Kb | whitelisted |
1792 | chrome.exe | GET | 200 | 2.18.235.97:80 | http://www.chip.de/download/assets/speedtestwidget-v1.4.22.css | unknown | text | 10.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3792 | iexplore.exe | 216.58.215.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
2532 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1792 | chrome.exe | 172.217.21.202:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 216.58.215.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 216.58.215.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 172.217.168.34:443 | adservice.google.de | Google Inc. | US | whitelisted |
1792 | chrome.exe | 64.233.184.94:443 | id.google.de | Google Inc. | US | whitelisted |
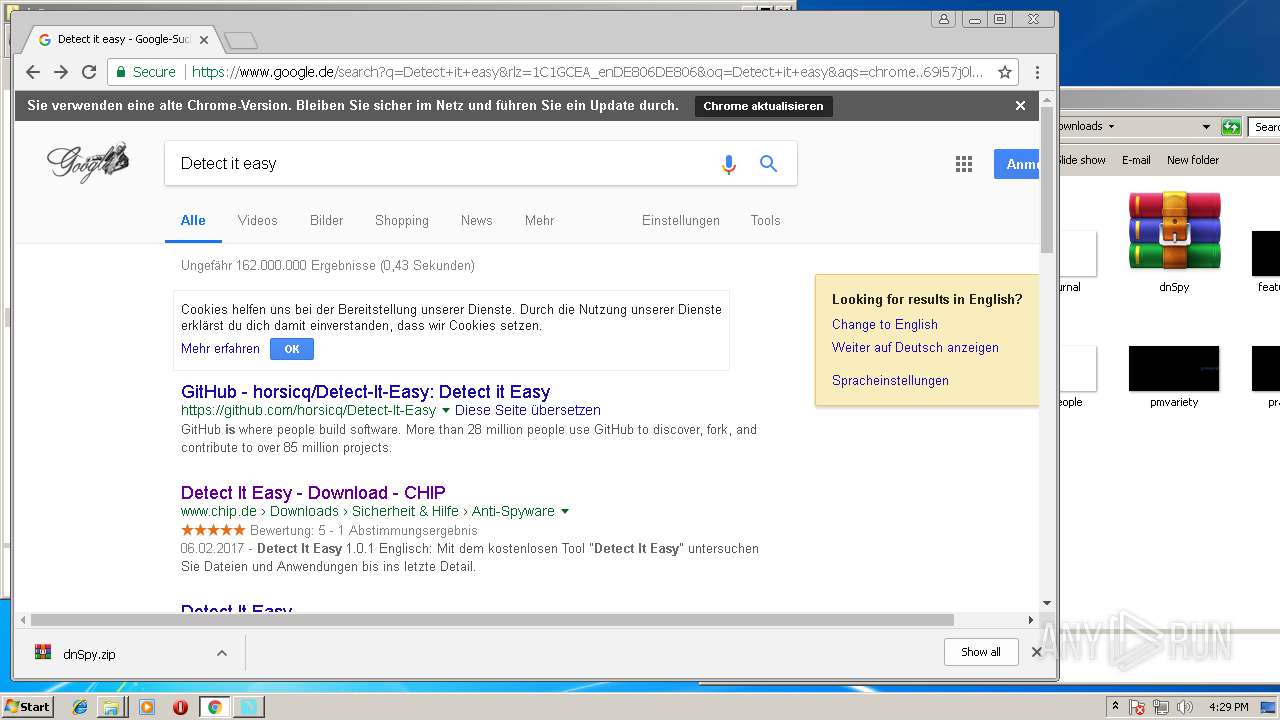
1792 | chrome.exe | 192.30.253.112:443 | github.com | GitHub, Inc. | US | shared |
1792 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
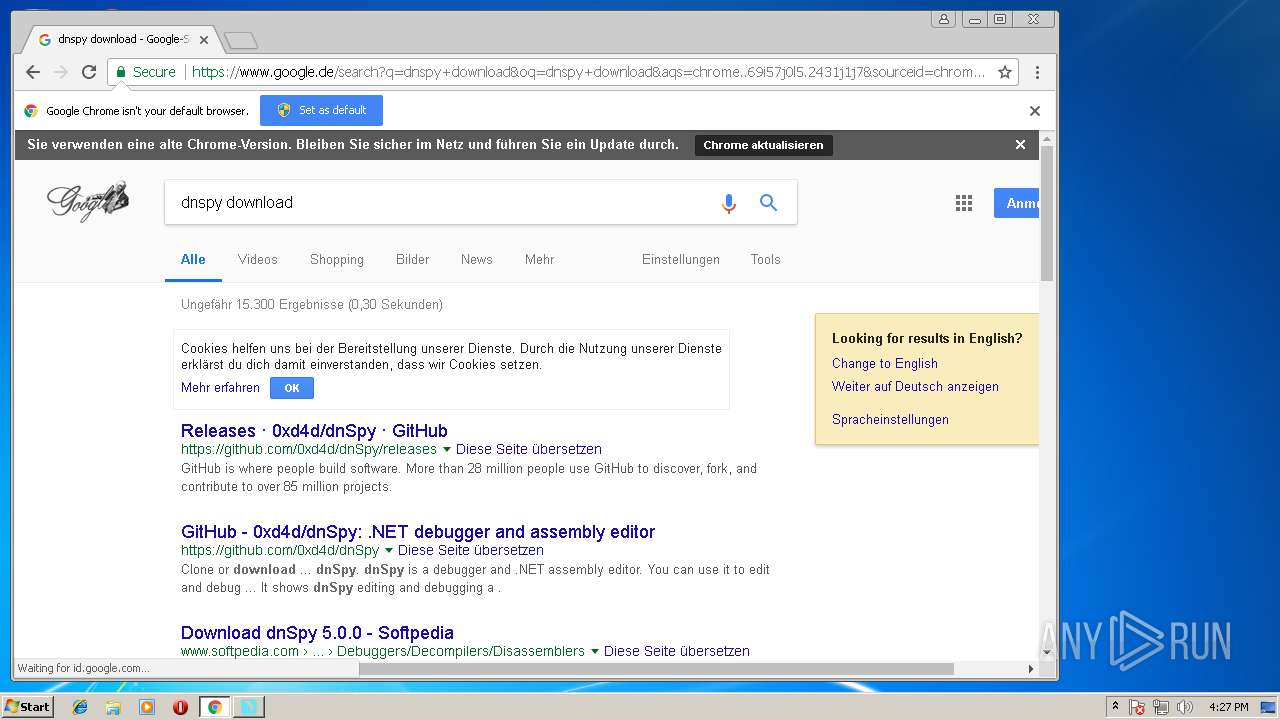
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtube.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google.com |
| malicious |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
id.google.de |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1792 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Phishing Redirect Dec 13 2016 |
1792 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Phishing Redirect Dec 13 2016 |