| File name: | autoplay.exe |
| Full analysis: | https://app.any.run/tasks/db6416dd-9b21-40a2-9ec2-e9dad83070af |
| Verdict: | No threats detected |
| Analysis date: | February 19, 2019, 15:35:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7B1AE78C834BA79A12988704E94F0899 |
| SHA1: | 8D69167E9FE0990A6797310342FE595A3BEB08EA |
| SHA256: | 2108F4D657CDA5FABA06EFA6DBA77B31616E35DB1A8A244E559A2E137B68786A |
| SSDEEP: | 49152:vH5DoYTZ6oa+K+ijbUWBRrcAiQ6tabZFxBdv/Ujfcq7XQix3xAO0w6qUJSBo:vloYTZ6d+3i/UWj6BtiNdWfl53xAfqh |
MALICIOUS
Application was dropped or rewritten from another process
- AutoTrainJX.exe (PID: 2920)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 184)
SUSPICIOUS
Executable content was dropped or overwritten
- autoplay.exe (PID: 2564)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:18 18:46:01+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 832512 |
| InitializedDataSize: | 177152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x101a9 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Hồi Ức Võ Lâm |
| CompanyName: | Hồi Ức Võ Lâm |
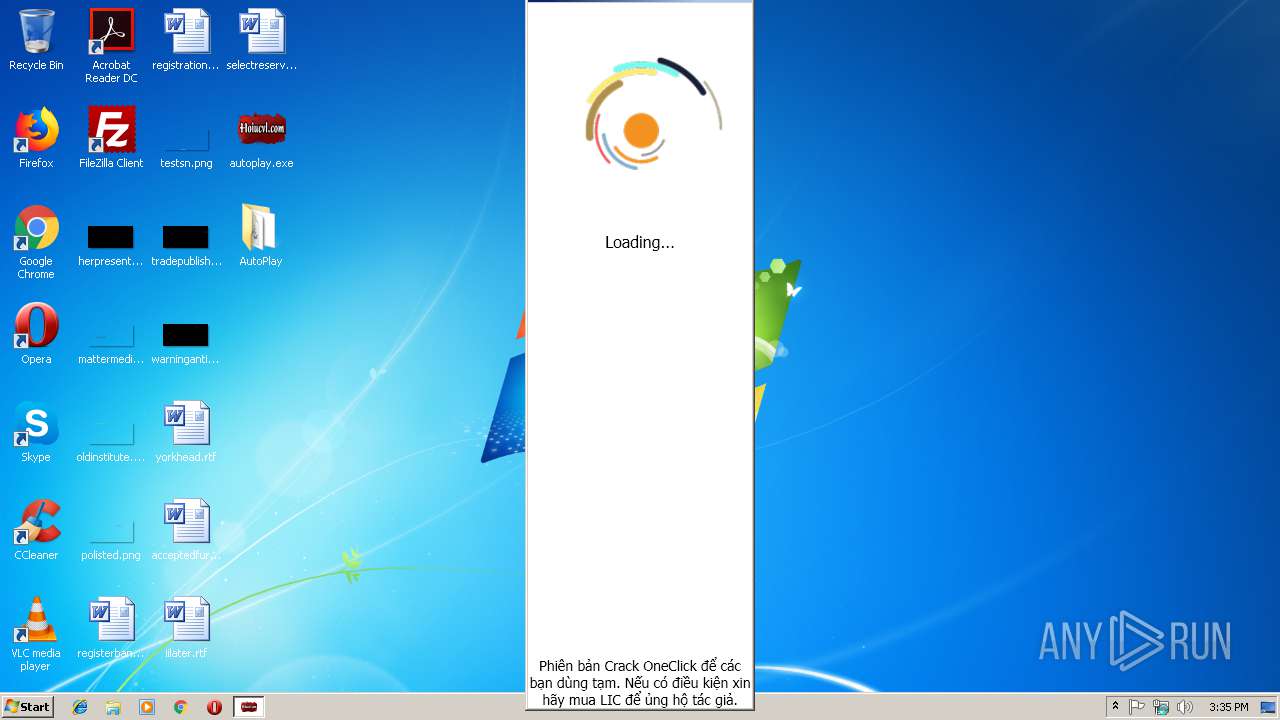
| FileDescription: | AutoPlay OneClick |
| FileVersion: | 1.0.0.0 |
| InternalName: | Crack_Auto.exe |
| LegalCopyright: | Copyright © Hồi Ức Võ Lâm 2019 |
| OriginalFileName: | Crack_Auto.exe |
| ProductName: | AutoPlayJX |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Feb-2019 17:46:01 |
| Comments: | Hồi Ức Võ Lâm |
| CompanyName: | Hồi Ức Võ Lâm |
| FileDescription: | AutoPlay OneClick |
| FileVersion: | 1.0.0.0 |
| InternalName: | Crack_Auto.exe |
| LegalCopyright: | Copyright © Hồi Ức Võ Lâm 2019 |
| OriginalFilename: | Crack_Auto.exe |
| ProductName: | AutoPlayJX |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 18-Feb-2019 17:46:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00128000 | 0x0027E000 | 0x000ACE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99919 | |
.rsrc | 0x000FC000 | 0x0002C000 | 0x0002B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.45642 |
.data | 0x003A6000 | 0x000D6000 | 0x000D5000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9863 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 7.98883 | 74641 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.4376 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.745 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.89852 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.02838 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.15296 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.87665 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
gdi32.dll |
kernel32.dll |
mscoree.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
33
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2564 | "C:\Users\admin\Desktop\autoplay.exe" | C:\Users\admin\Desktop\autoplay.exe | explorer.exe | ||||||||||||
User: admin Company: Hồi Ức Võ Lâm Integrity Level: MEDIUM Description: AutoPlay OneClick Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2920 | ".\AutoPlay\AutoTrainJX.exe" | C:\Users\admin\Desktop\AutoPlay\AutoTrainJX.exe | — | autoplay.exe | |||||||||||
User: admin Company: AutoTrainJX Integrity Level: MEDIUM Description: AutoTrainJX Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3248 | C:\Windows\Microsoft.Net\Framework\v3.0\WPF\PresentationFontCache.exe | C:\Windows\Microsoft.Net\Framework\v3.0\WPF\PresentationFontCache.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: PresentationFontCache.exe Exit code: 0 Version: 3.0.6920.4902 built by: NetFXw7 Modules
| |||||||||||||||
Total events
424
Read events
407
Write events
17
Delete events
0
Modification events
| (PID) Process: | (2564) autoplay.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: autoplay.exe | |||
| (PID) Process: | (2564) autoplay.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\autoplay_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2564) autoplay.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\autoplay_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2564) autoplay.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\autoplay_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2564) autoplay.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\autoplay_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2564) autoplay.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\autoplay_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2564) autoplay.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\autoplay_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2564) autoplay.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\autoplay_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2564) autoplay.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\autoplay_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2564) autoplay.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\autoplay_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
5
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2564 | autoplay.exe | C:\Users\admin\Desktop\AutoPlay\AutoTrainJX.exe | executable | |
MD5:9AA6BB3FF4FEA0E05A3EAF469EA9461B | SHA256:6D6D1913B8BB7CF8FEE8916127825E759AD59855DE84830B38CC9EE8C492B8DC | |||
| 2564 | autoplay.exe | C:\Users\admin\Desktop\err.log | text | |
MD5:50FA49AB14306BA89E546A982EDB0058 | SHA256:1AB558E4F6E6897B7D90343759374632982F7B63F1D3A35AC0F26809F86C211C | |||
| 2564 | autoplay.exe | C:\Users\admin\AppData\Local\Temp\evbEC65.tmp | executable | |
MD5:1039552FB7D52C4E9E8D0FE3A9EEBC43 | SHA256:5424B8A6414839EBF07EFC0C388081EAEB629EAB91FEB0B250B5EDACD572D104 | |||
| 2564 | autoplay.exe | C:\Users\admin\Desktop\AutoPlay\DotNetZip.dll | executable | |
MD5:EAA795B9D45DDB6B1FAB02C8EA372295 | SHA256:8EA95DE4024018888C833024F3E249C1BC4CB633908DB25CFD5DAF14BC66875F | |||
| 2564 | autoplay.exe | C:\Users\admin\AppData\Local\Temp\evbEC75.tmp | executable | |
MD5:1039552FB7D52C4E9E8D0FE3A9EEBC43 | SHA256:5424B8A6414839EBF07EFC0C388081EAEB629EAB91FEB0B250B5EDACD572D104 | |||
| 2564 | autoplay.exe | C:\Users\admin\AppData\Local\Temp\evbEC86.tmp | executable | |
MD5:1039552FB7D52C4E9E8D0FE3A9EEBC43 | SHA256:5424B8A6414839EBF07EFC0C388081EAEB629EAB91FEB0B250B5EDACD572D104 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2564 | autoplay.exe | 103.200.23.32:443 | hoiucvl.com | The Corporation for Financing & Promoting Technology | VN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hoiucvl.com |
| unknown |
Threats
Process | Message |
|---|---|
autoplay.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
autoplay.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
autoplay.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
autoplay.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
autoplay.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
autoplay.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
autoplay.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
autoplay.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
autoplay.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
autoplay.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|