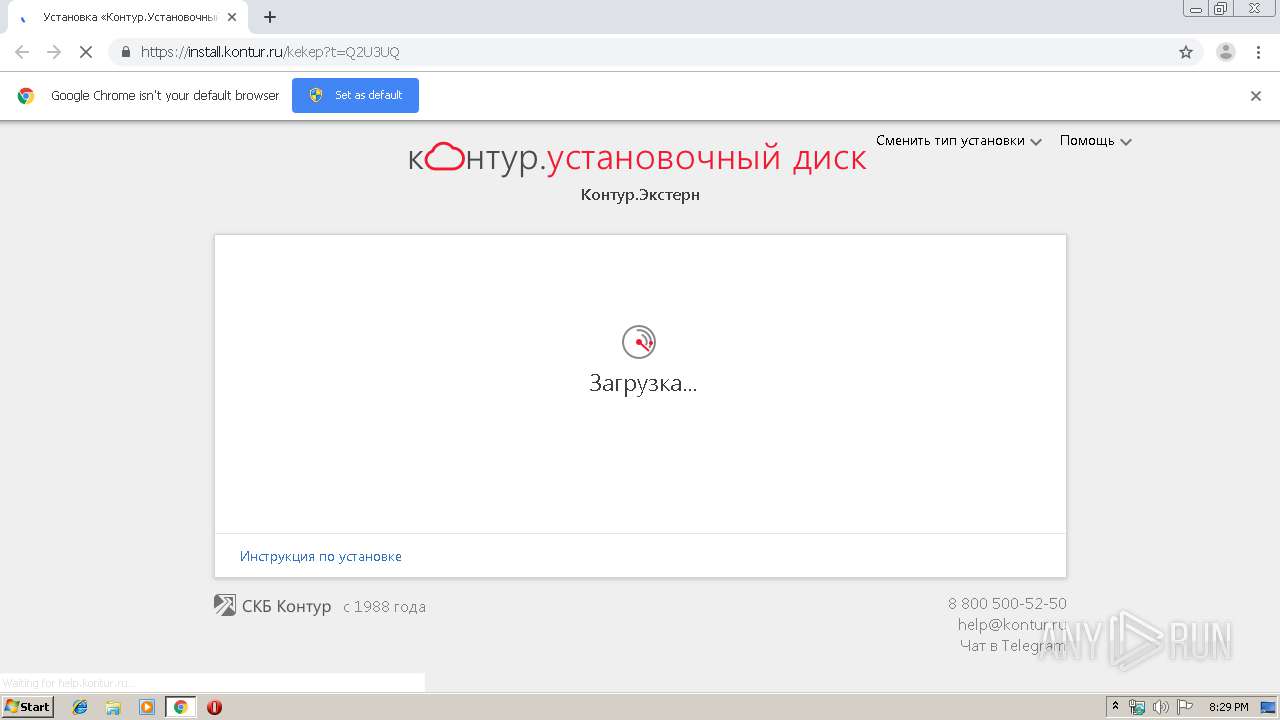
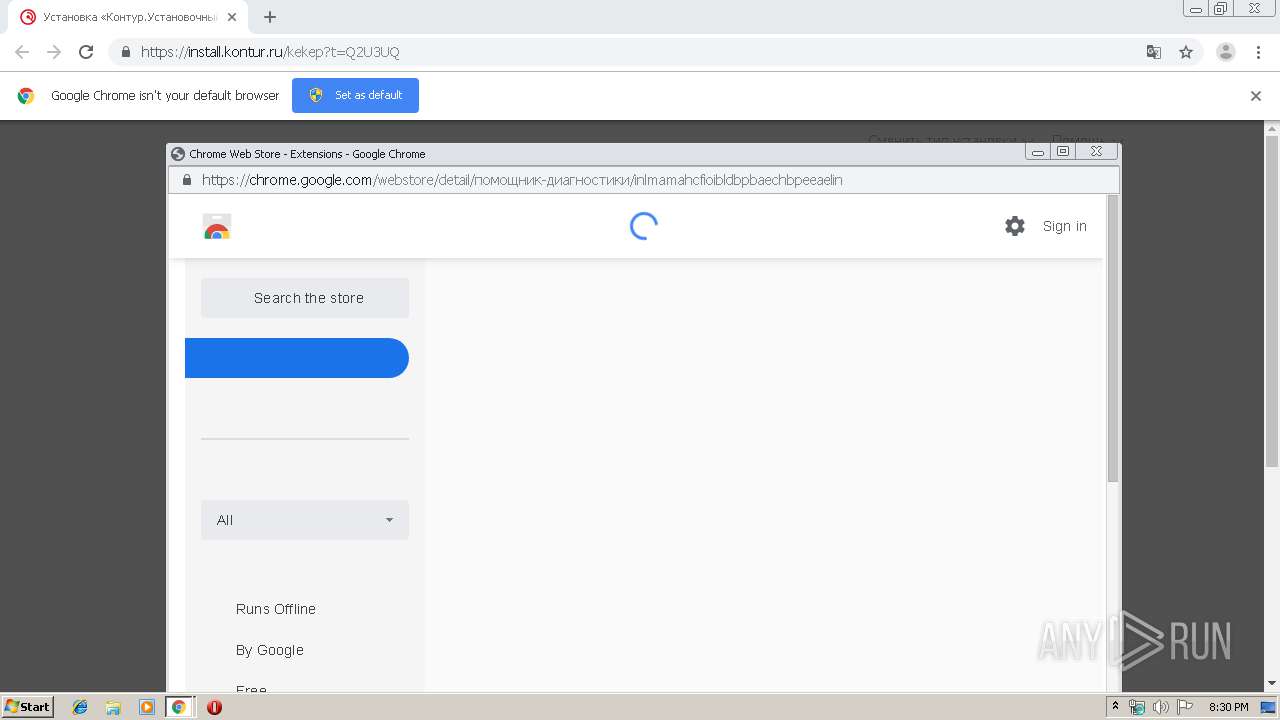
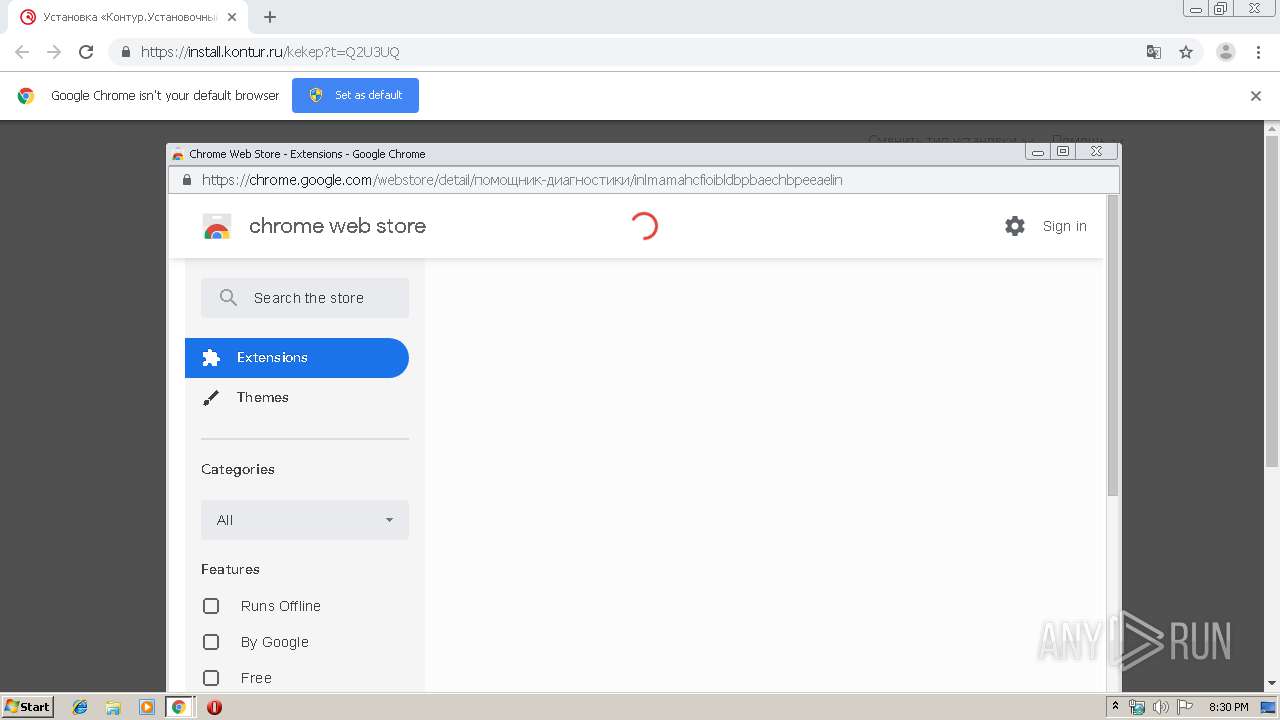
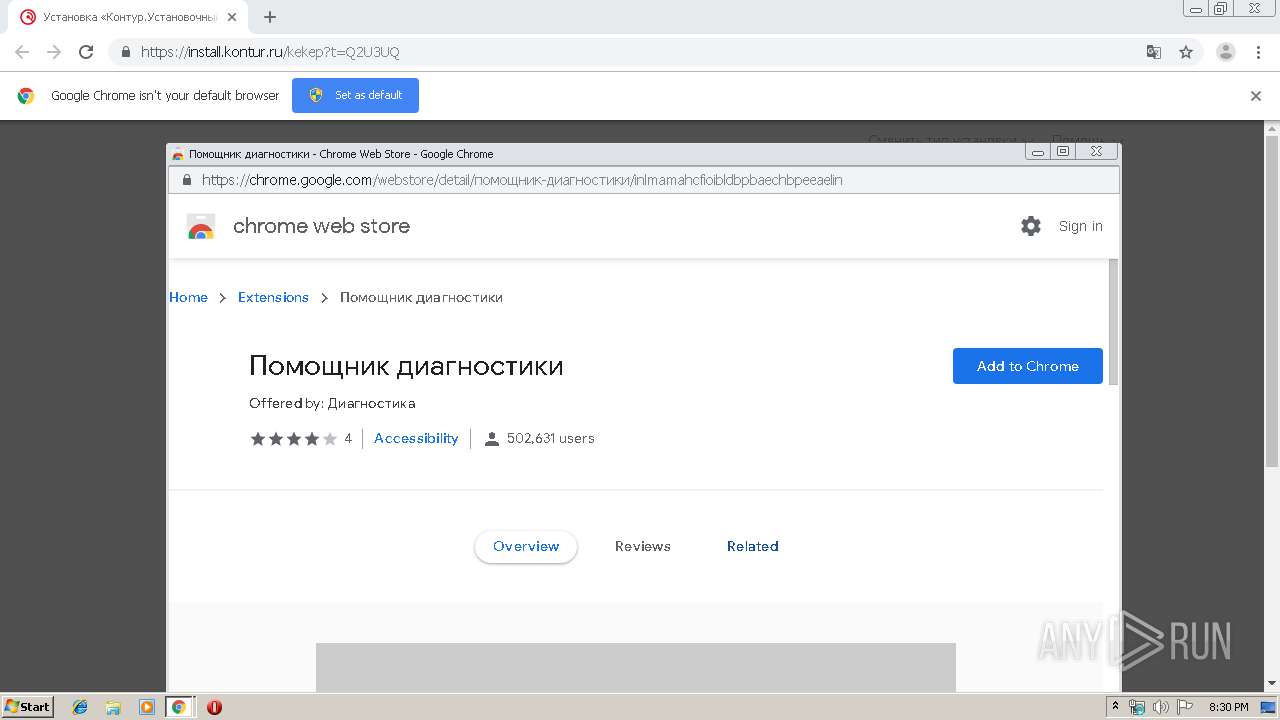
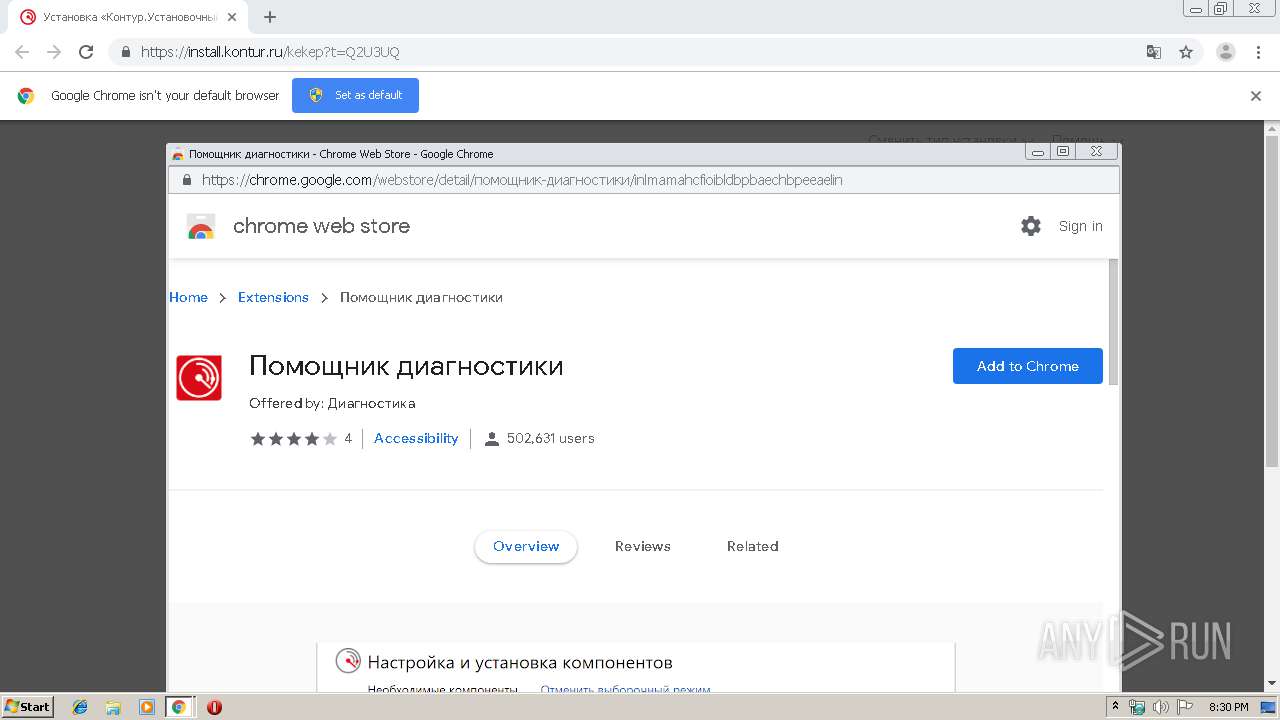
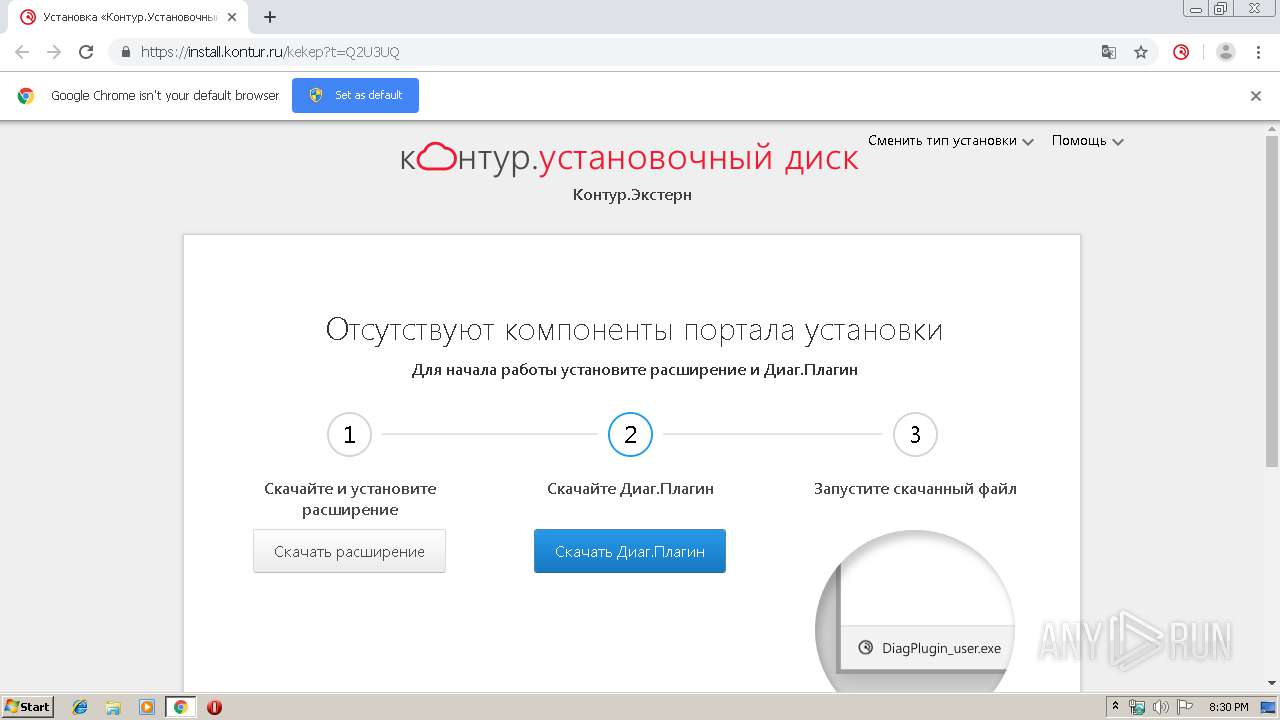
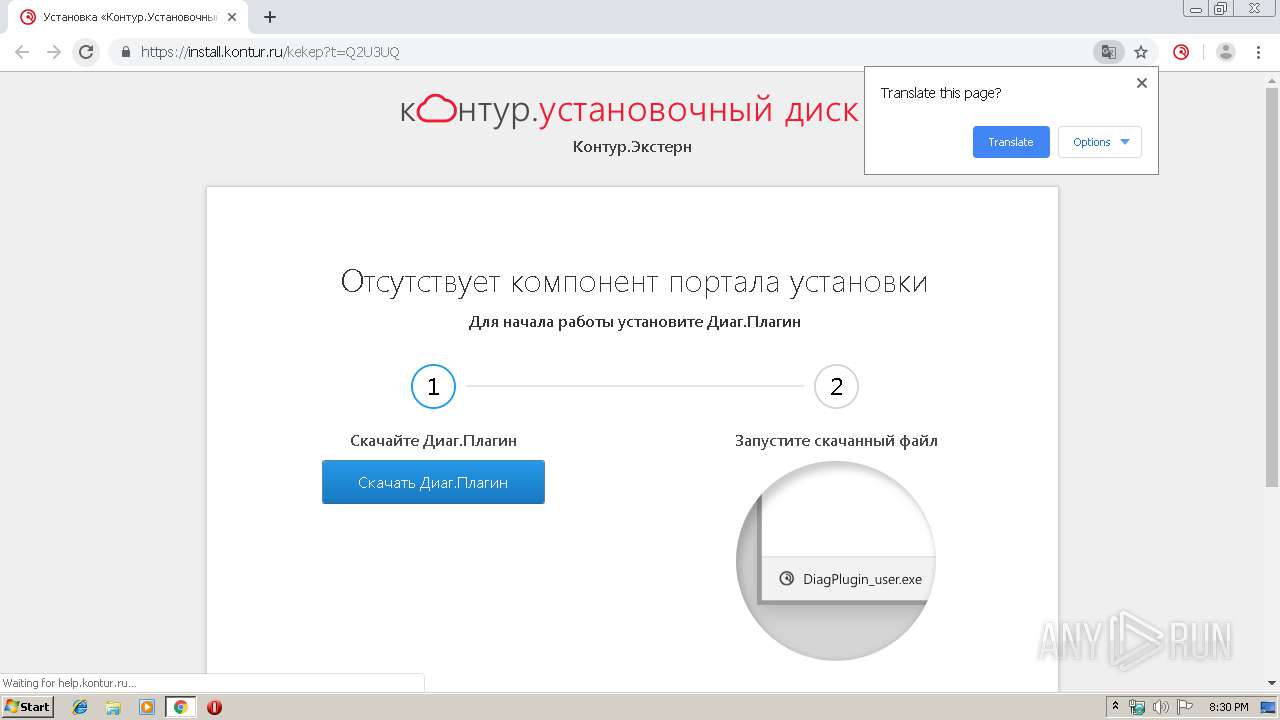
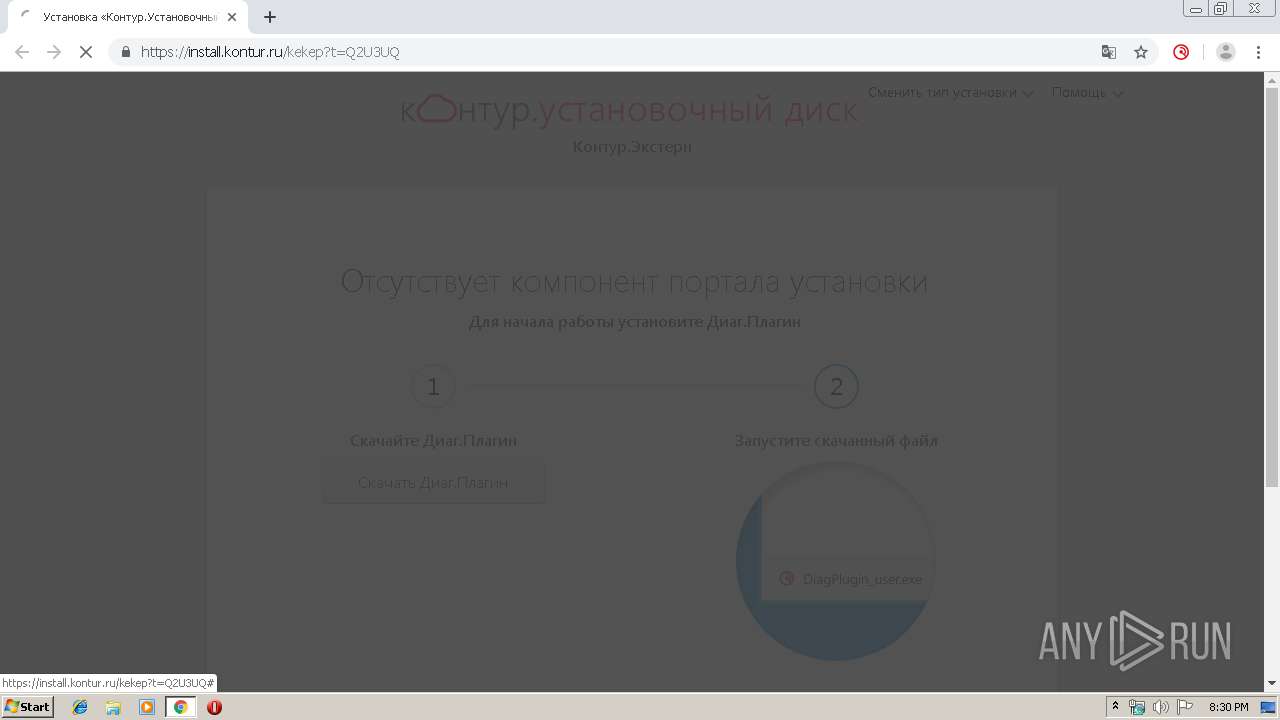
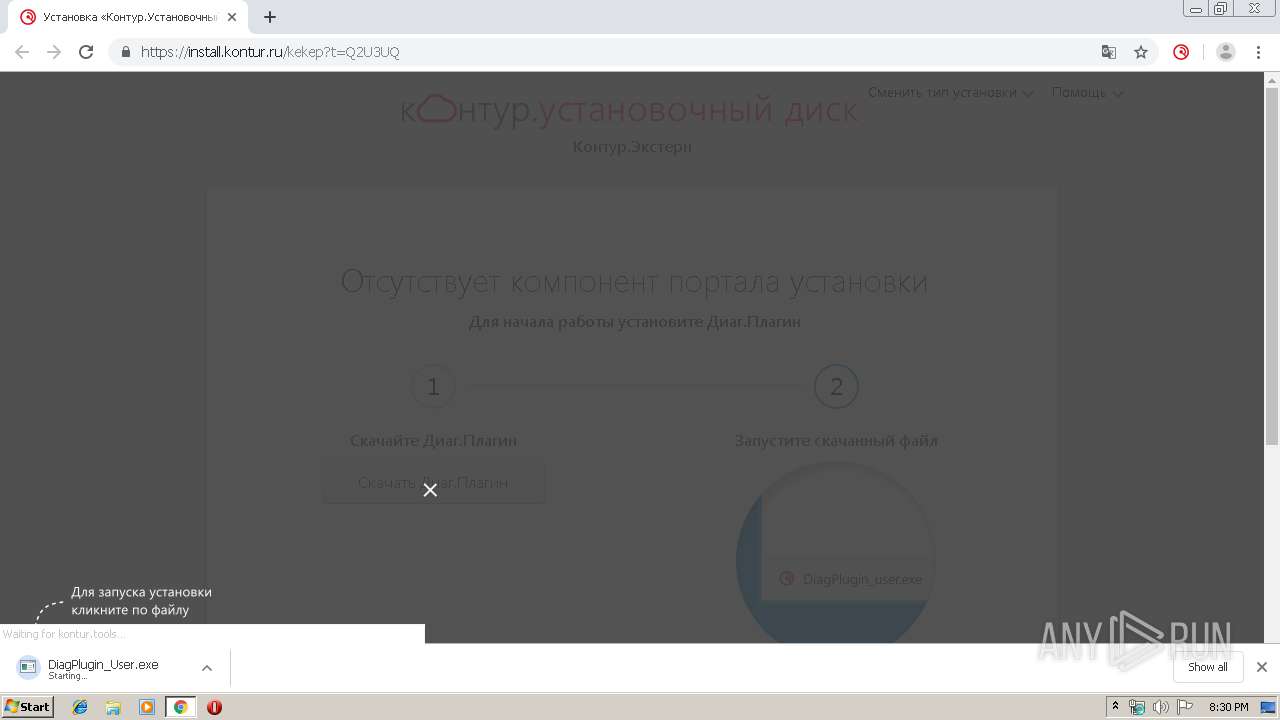
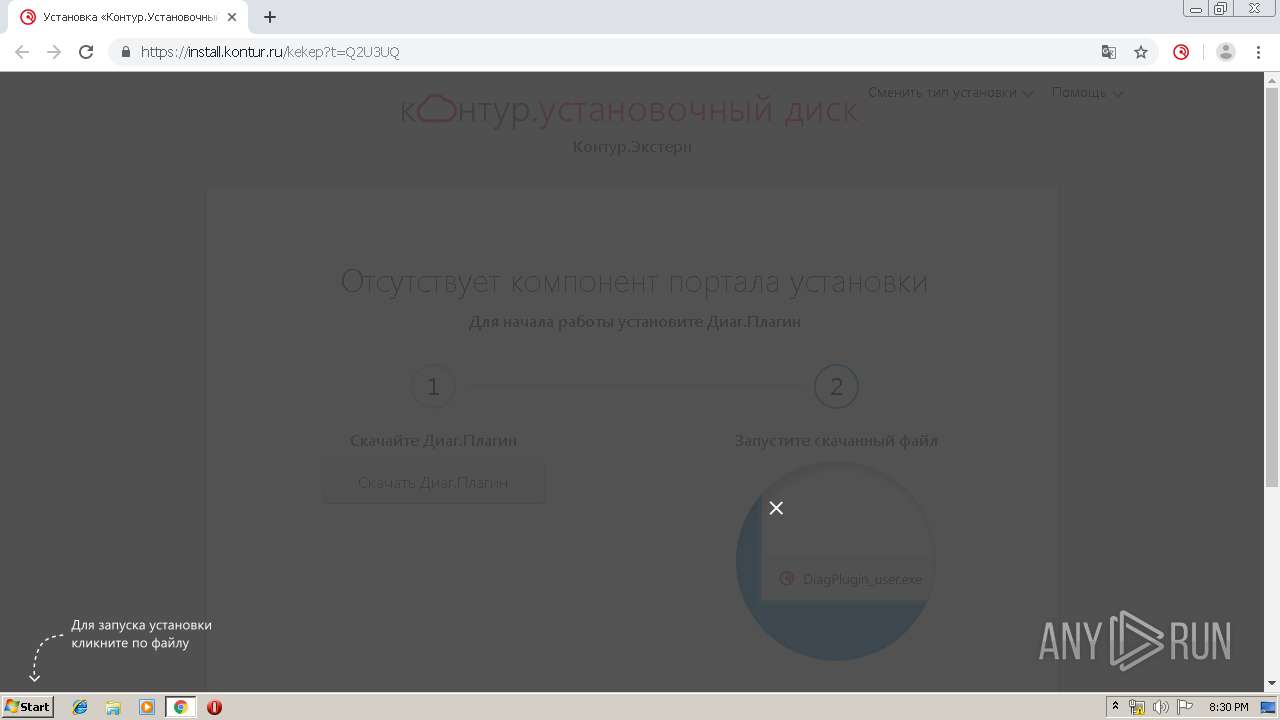
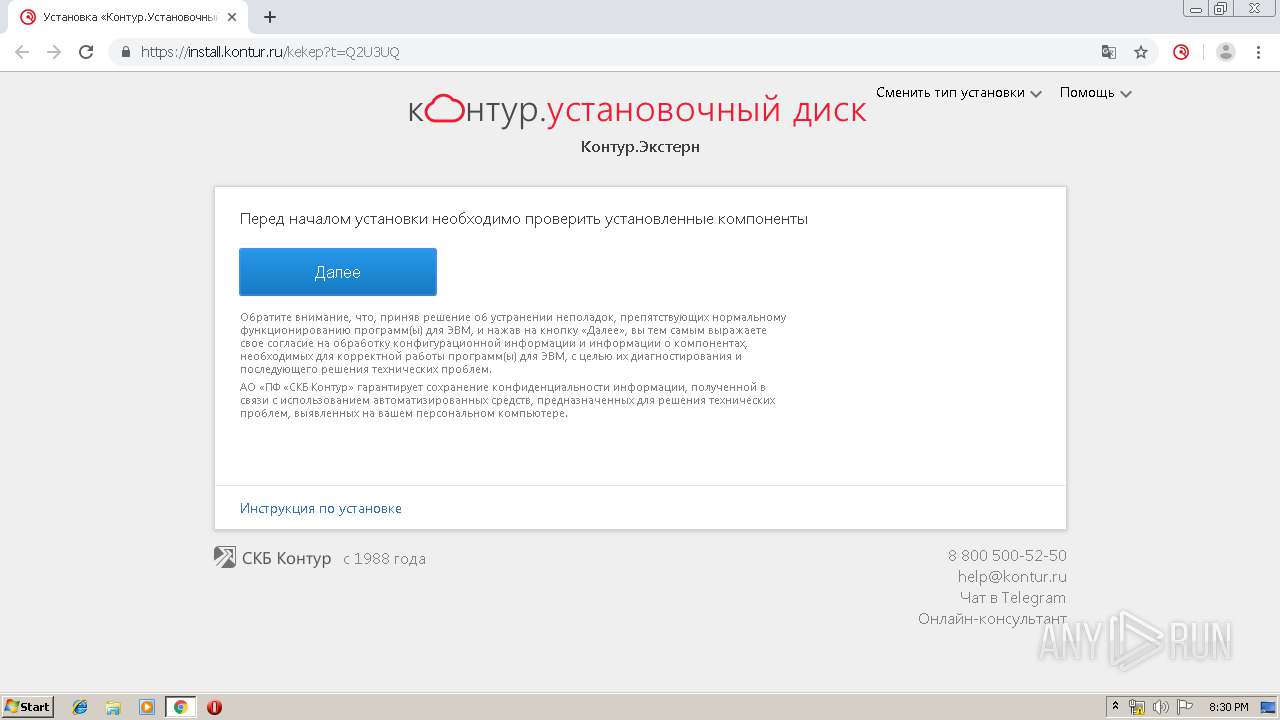
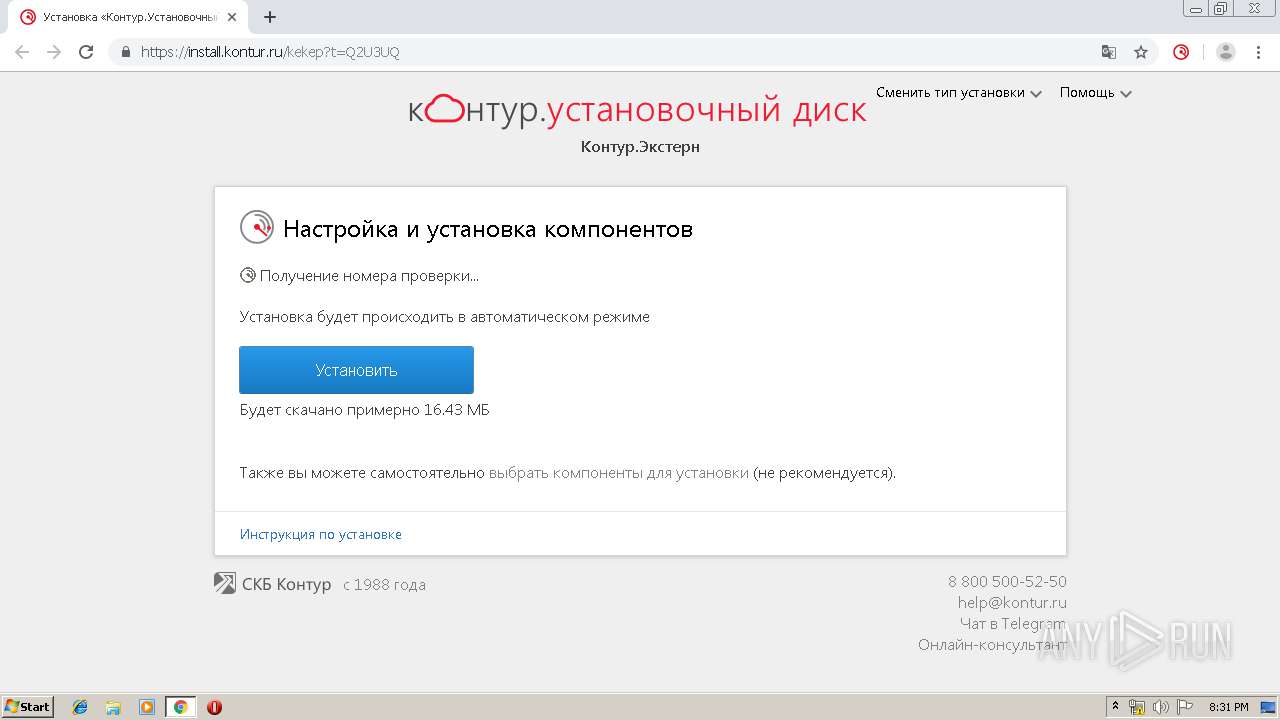
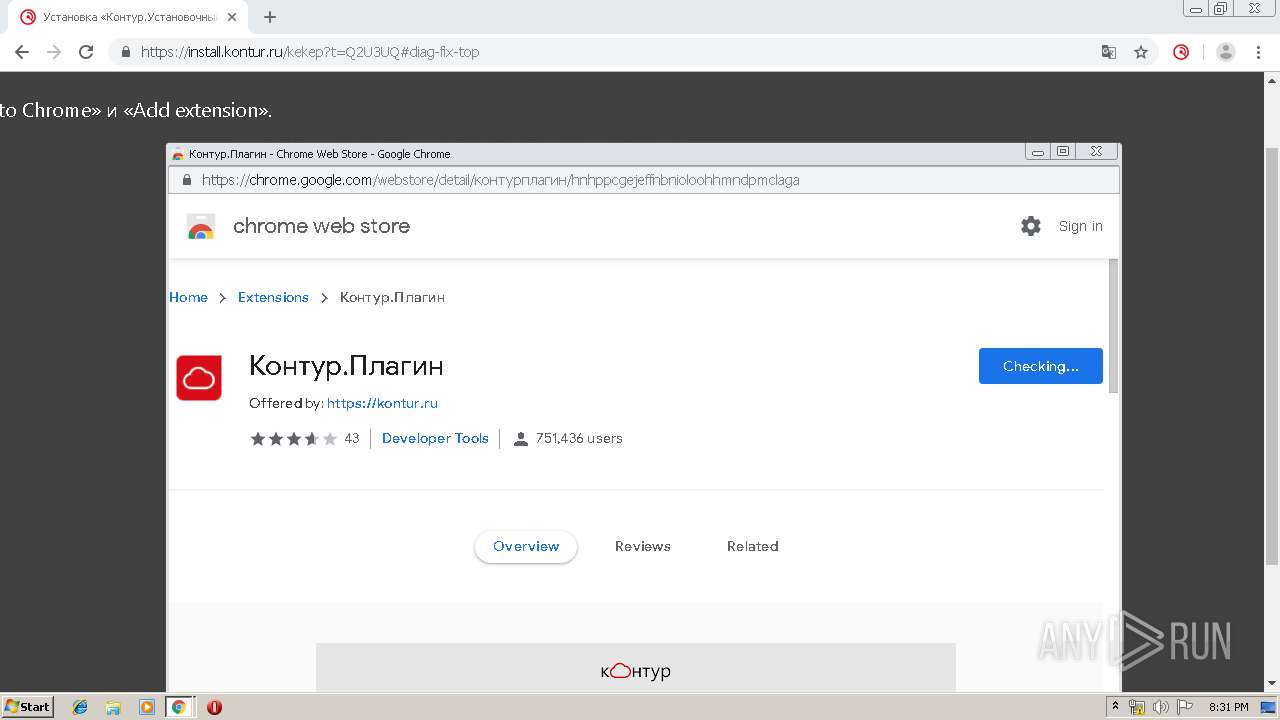
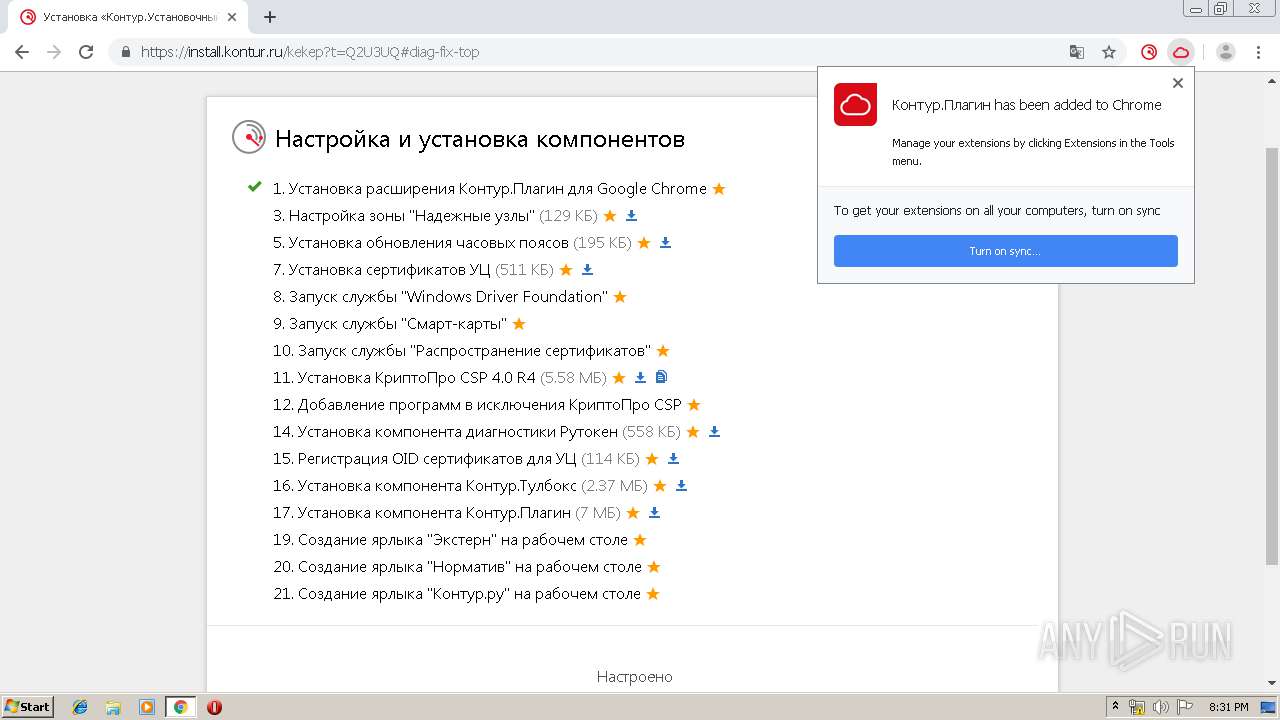
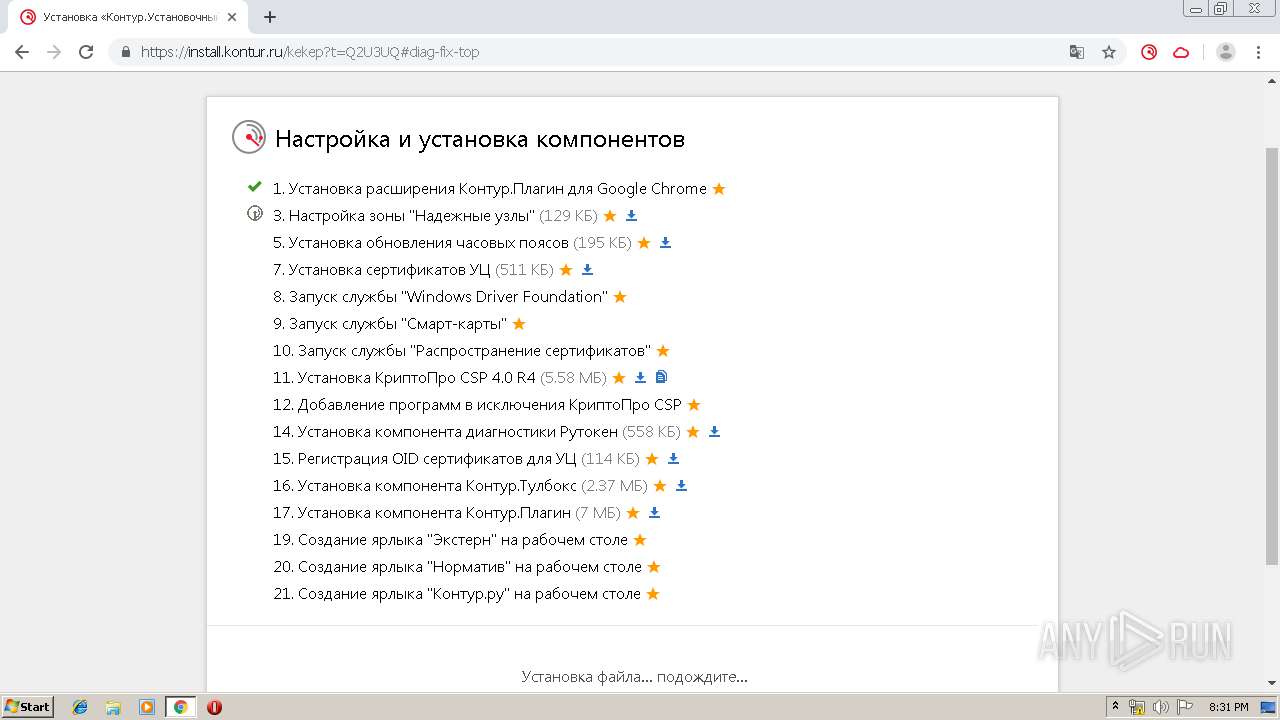
| URL: | https://install.kontur.ru/kekep?t=Q2U3UQ |
| Full analysis: | https://app.any.run/tasks/5f188a1b-b2aa-42ae-ac99-8efec2d12273 |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2019, 20:29:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A6D3CA829622AD1BD7C80F34ACA75572 |
| SHA1: | FEC542D1AFF577F2D279D951A0647253C35B10B1 |
| SHA256: | 2104024EF8B7E78889C740512BF89DFEA6C8F484CB14ED5EF5BF9CFBC11072E7 |
| SSDEEP: | 3:N8LREJFlL2XsVAOzTB:2lgzLNqOvB |
MALICIOUS
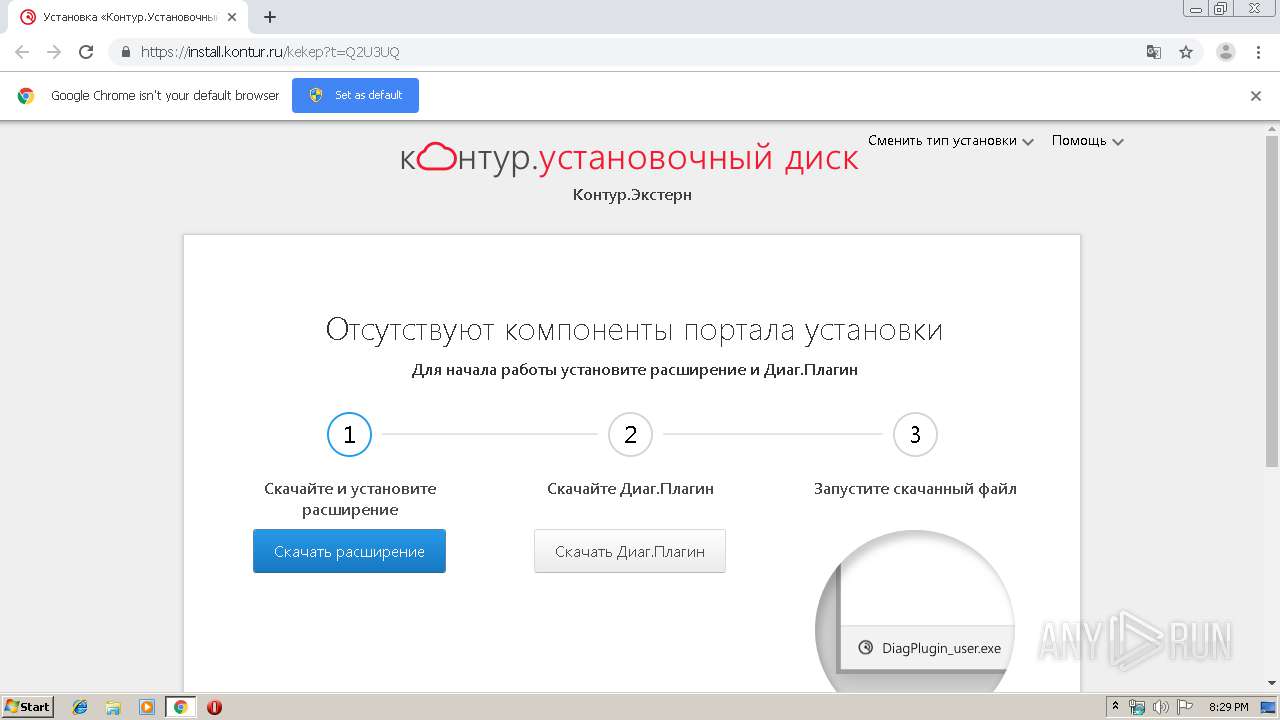
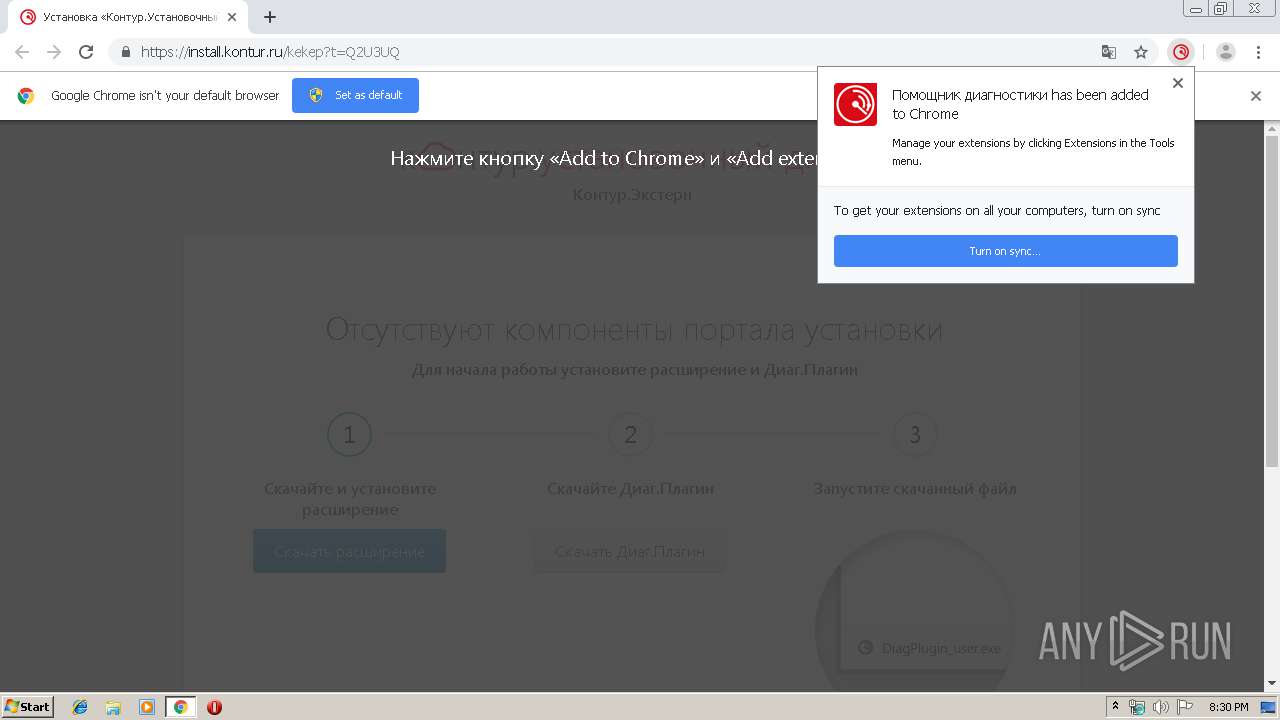
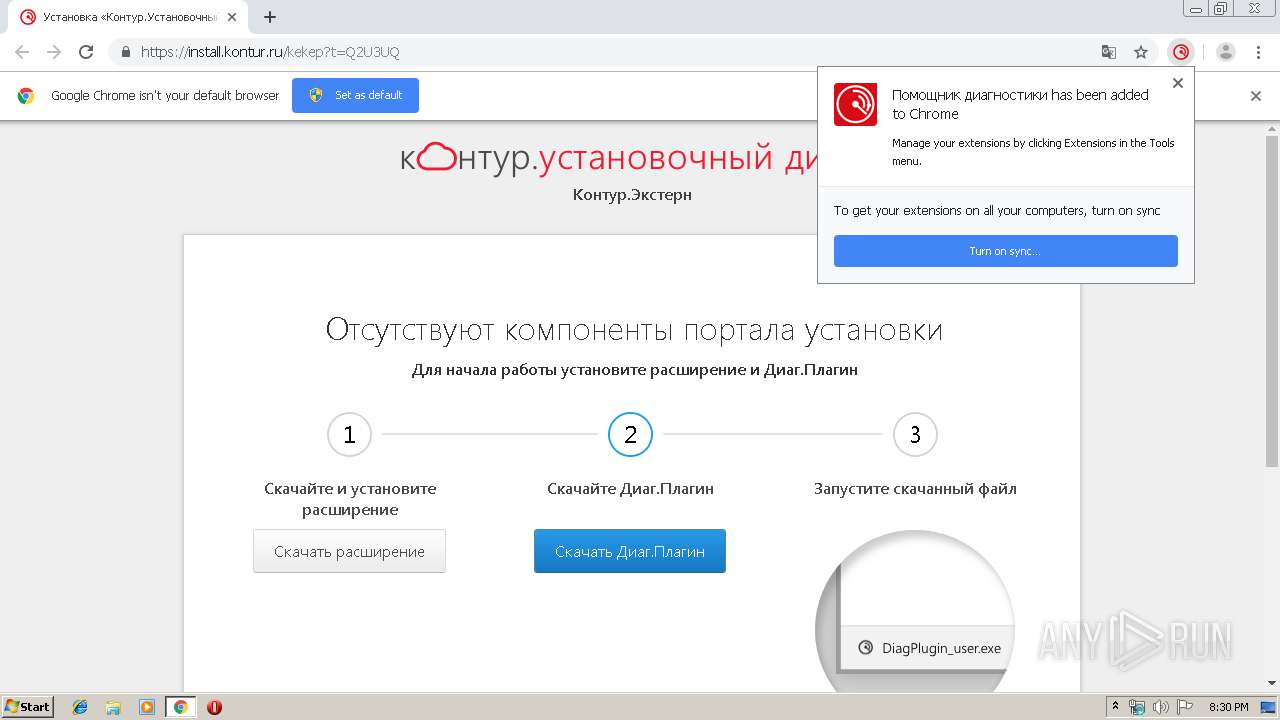
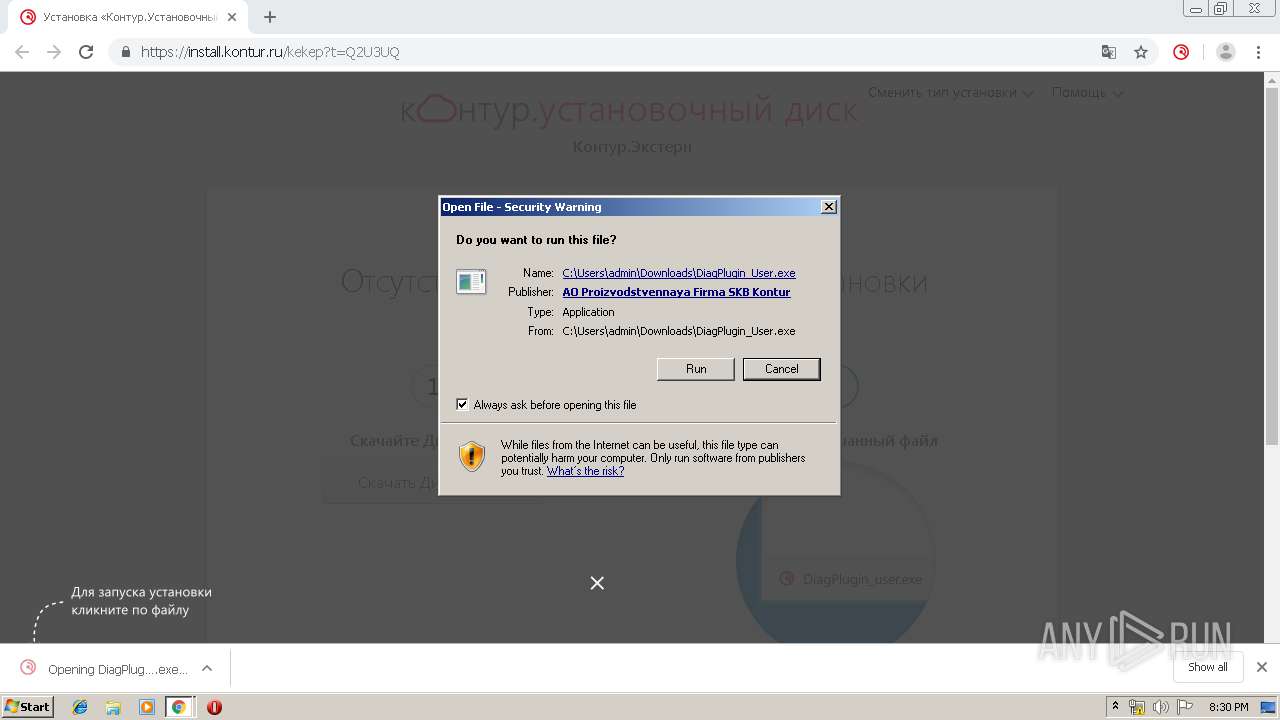
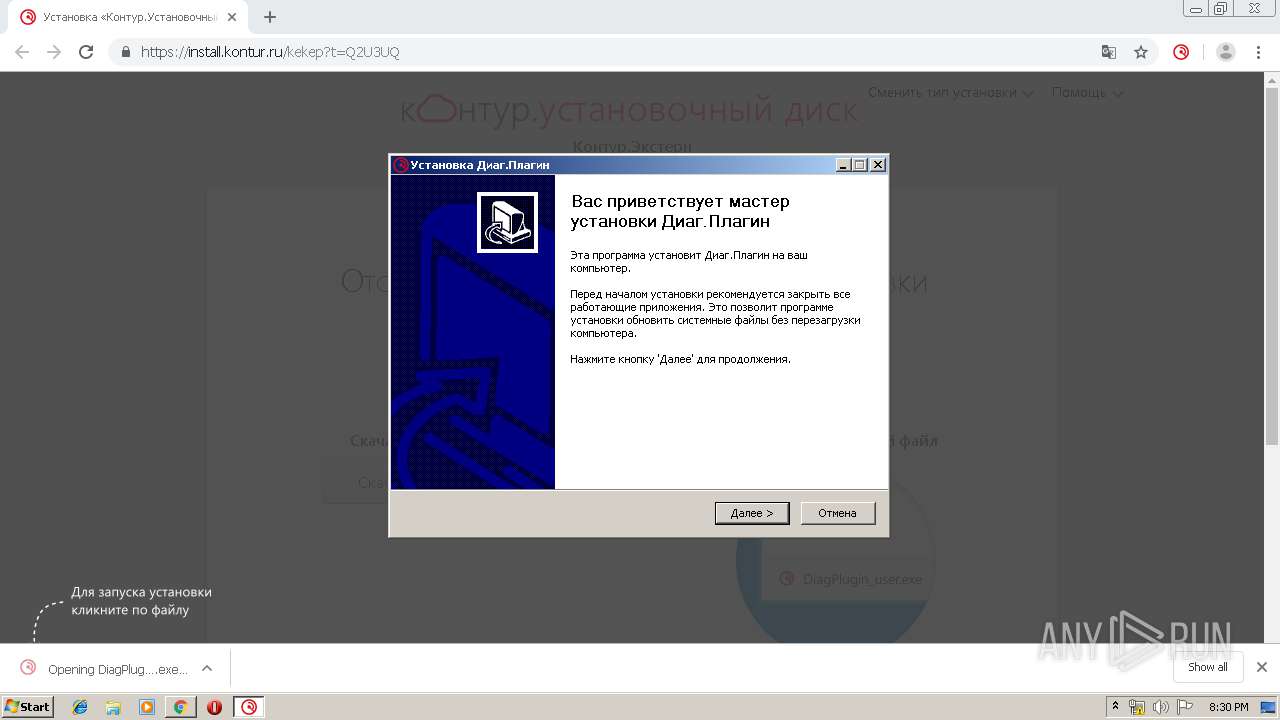
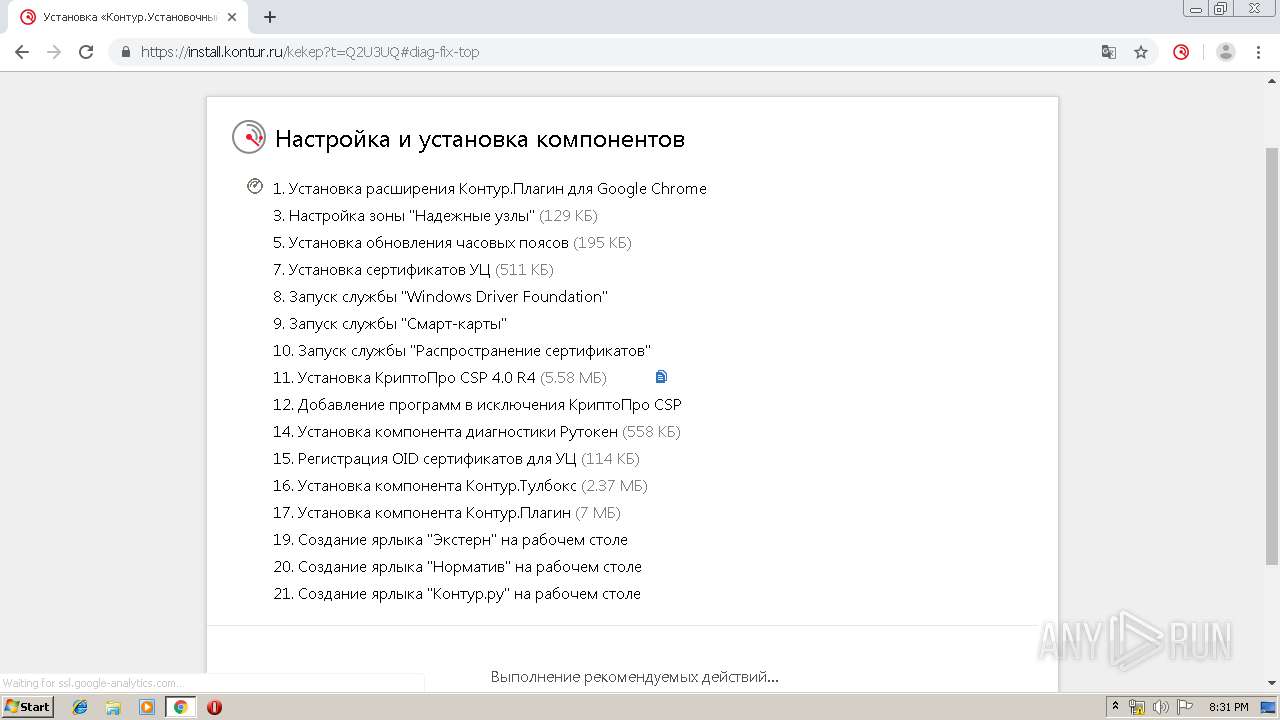
Application was dropped or rewritten from another process
- DiagPlugin_User.exe (PID: 2700)
- CertFix_Host.exe (PID: 2188)
- kdnchost.exe (PID: 2812)
- addtotrusted.exe (PID: 1932)
- kddisphost.exe (PID: 912)
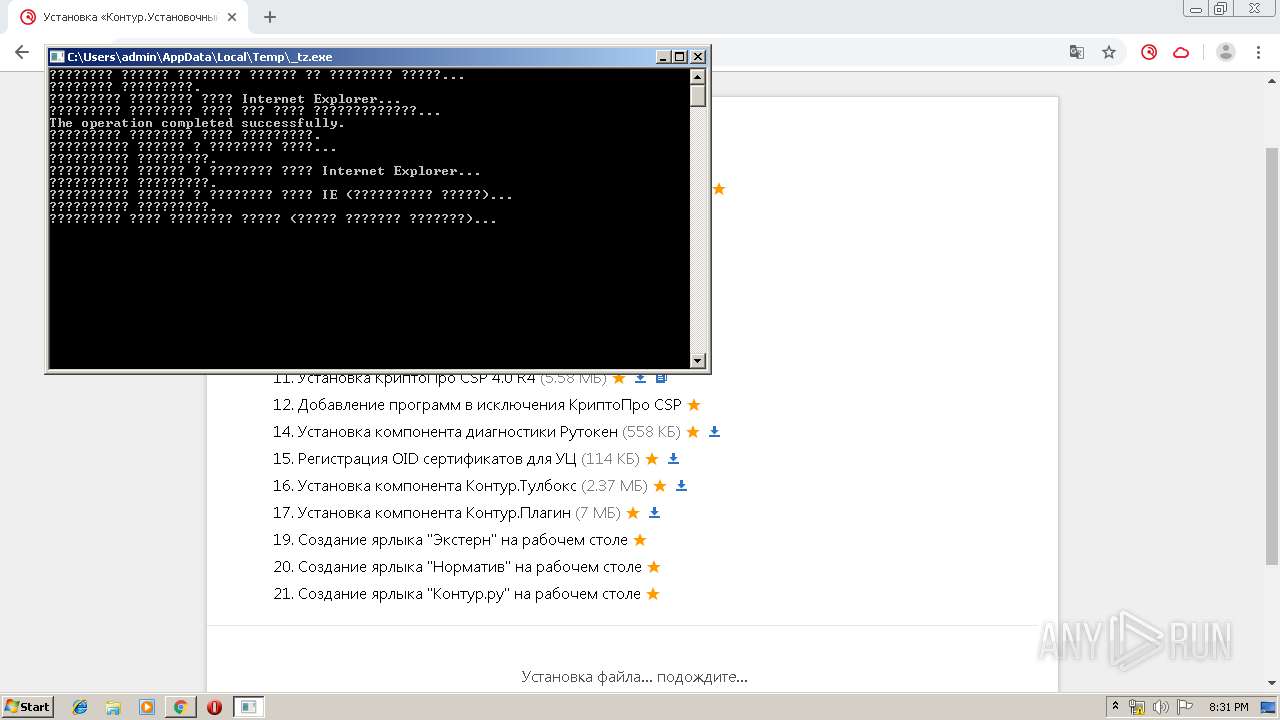
- _tz.exe (PID: 2840)
- updatetimezones_enu.exe (PID: 1732)
- ns6A95.tmp (PID: 1800)
- Certificates_Kontur_Admin.exe (PID: 2404)
- tzutil.exe (PID: 3208)
- tzutil.exe (PID: 1324)
- ns6B71.tmp (PID: 2328)
- CSP40R4Setup.exe (PID: 1104)
- cpverify.exe (PID: 920)
- cpverify.exe (PID: 3280)
- cpverify.exe (PID: 3748)
- cpverify.exe (PID: 3876)
- cpverify.exe (PID: 1936)
- cpverify.exe (PID: 2748)
- cpverify.exe (PID: 3852)
- cpverify.exe (PID: 1976)
- cpverify.exe (PID: 3168)
- cpverify.exe (PID: 1768)
- cpverify.exe (PID: 1324)
- cpverify.exe (PID: 3088)
- cpverify.exe (PID: 3020)
- cpverify.exe (PID: 2868)
- cpverify.exe (PID: 3624)
- cpverify.exe (PID: 2056)
- cpverify.exe (PID: 1552)
- RegOids.exe (PID: 2116)
- rtcomlite.exe (PID: 3952)
- Setup.exe (PID: 3664)
Loads dropped or rewritten executable
- DiagPlugin_User.exe (PID: 2700)
- regsvr32.exe (PID: 2444)
- kdnchost.exe (PID: 2812)
- kddisphost.exe (PID: 912)
- updatetimezones_enu.exe (PID: 1732)
- lsass.exe (PID: 456)
- msiexec.exe (PID: 3976)
- regsvr32.exe (PID: 4072)
- rtcomlite.exe (PID: 3952)
- svchost.exe (PID: 1028)
Changes internet zones settings
- DiagPlugin_User.exe (PID: 2700)
- kdnchost.exe (PID: 2812)
- addtotrusted.exe (PID: 1932)
- _tz.exe (PID: 2840)
- reg.exe (PID: 3944)
Registers / Runs the DLL via REGSVR32.EXE
- DiagPlugin_User.exe (PID: 2700)
- rtcomlite.exe (PID: 3952)
Changes settings of System certificates
- DiagPlugin_User.exe (PID: 2700)
- kdnchost.exe (PID: 2812)
- CertFix_Host.exe (PID: 2188)
- kddisphost.exe (PID: 912)
- Certificates_Kontur_Admin.exe (PID: 2404)
- msiexec.exe (PID: 2508)
- Setup.exe (PID: 3664)
- MsiExec.exe (PID: 3036)
SUSPICIOUS
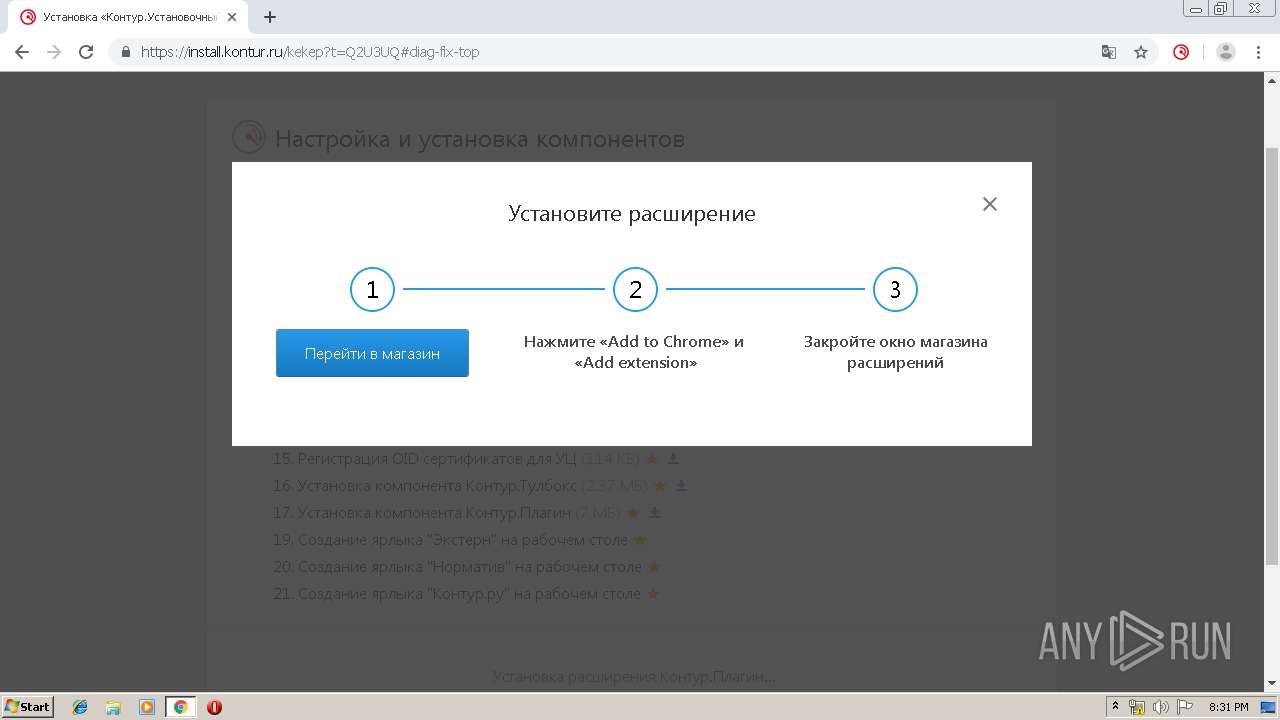
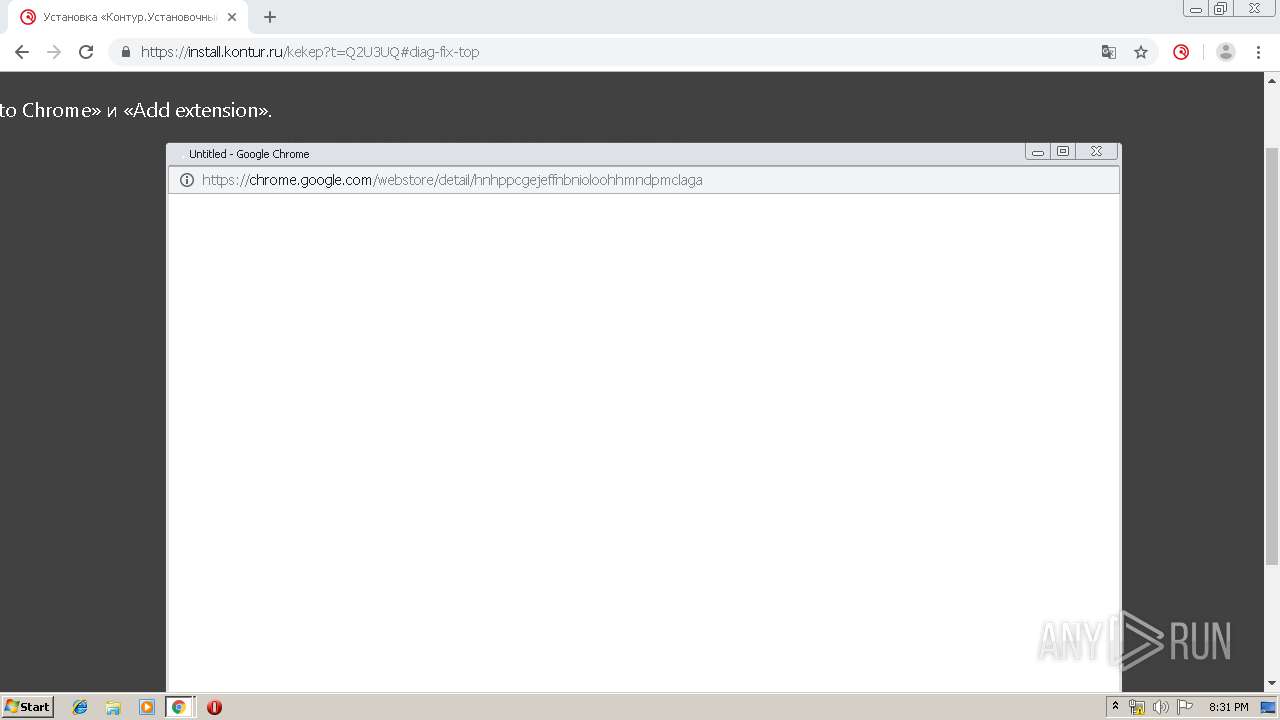
Executable content was dropped or overwritten
- chrome.exe (PID: 3936)
- chrome.exe (PID: 2896)
- DiagPlugin_User.exe (PID: 2700)
- kdnchost.exe (PID: 2812)
- addtotrusted.exe (PID: 1932)
- updatetimezones_enu.exe (PID: 1732)
- msiexec.exe (PID: 2508)
- MsiExec.exe (PID: 1544)
- CSP40R4Setup.exe (PID: 1104)
- DrvInst.exe (PID: 3080)
- rtcomlite.exe (PID: 3952)
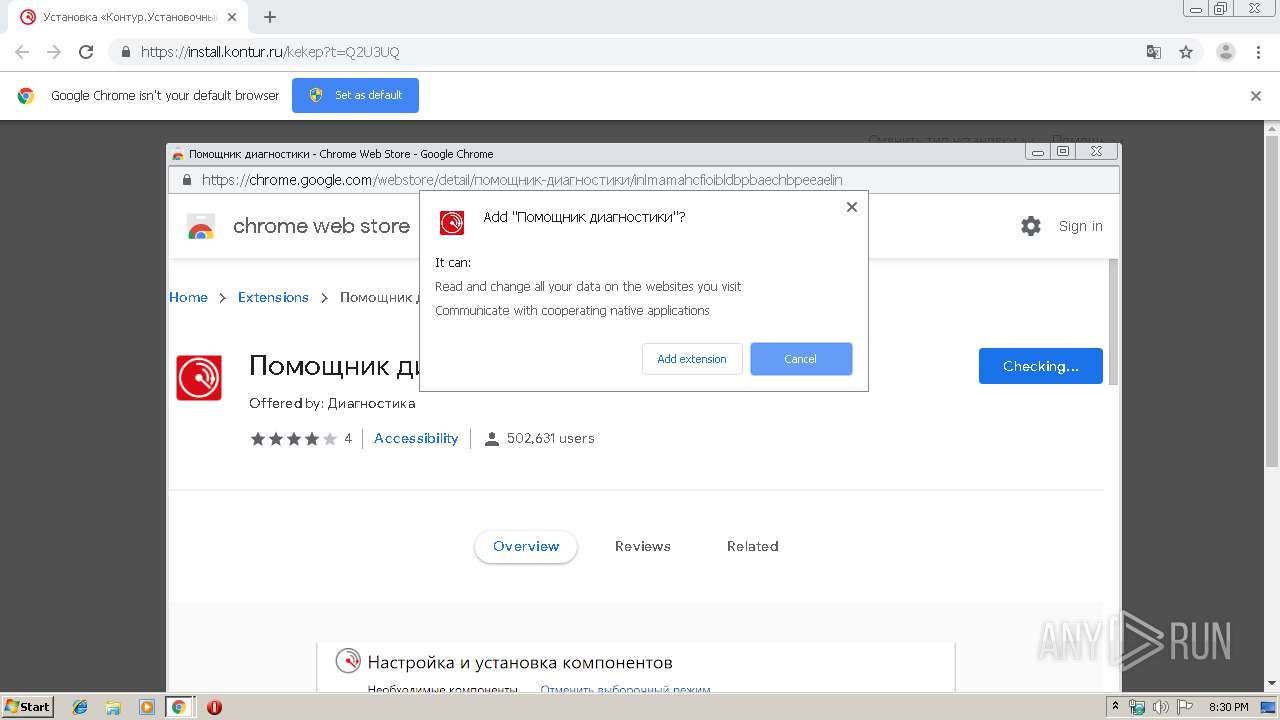
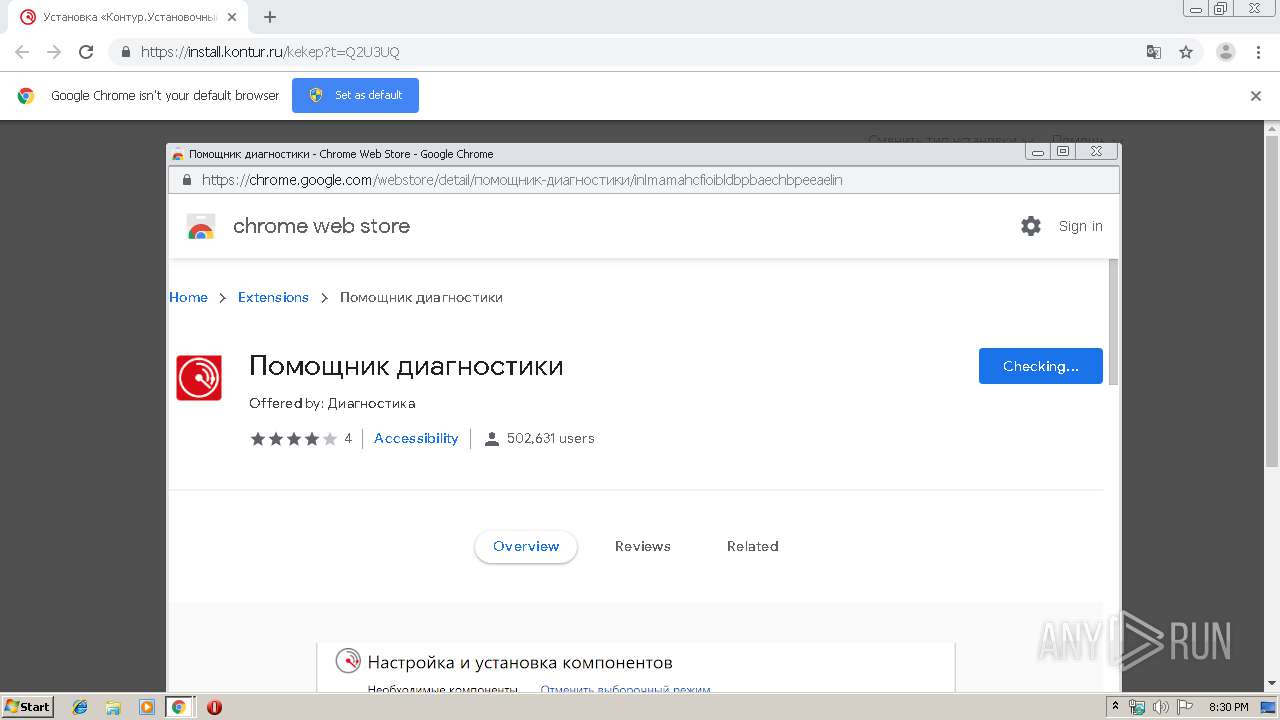
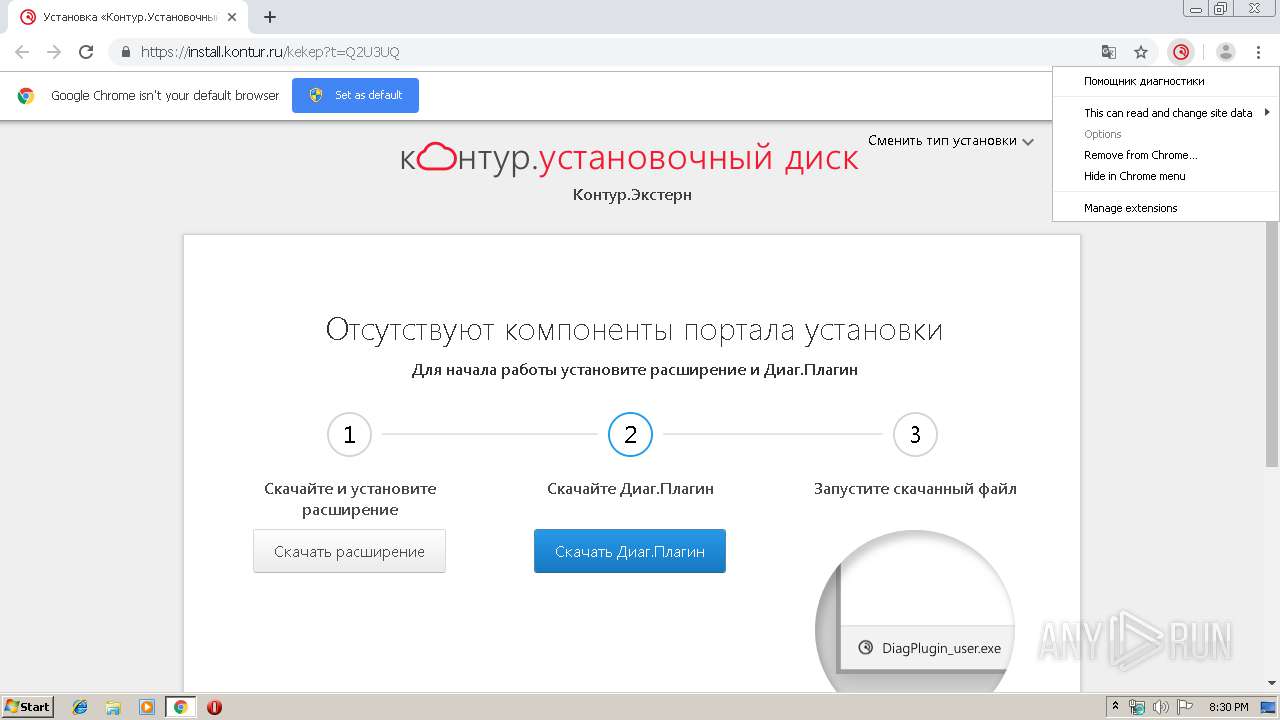
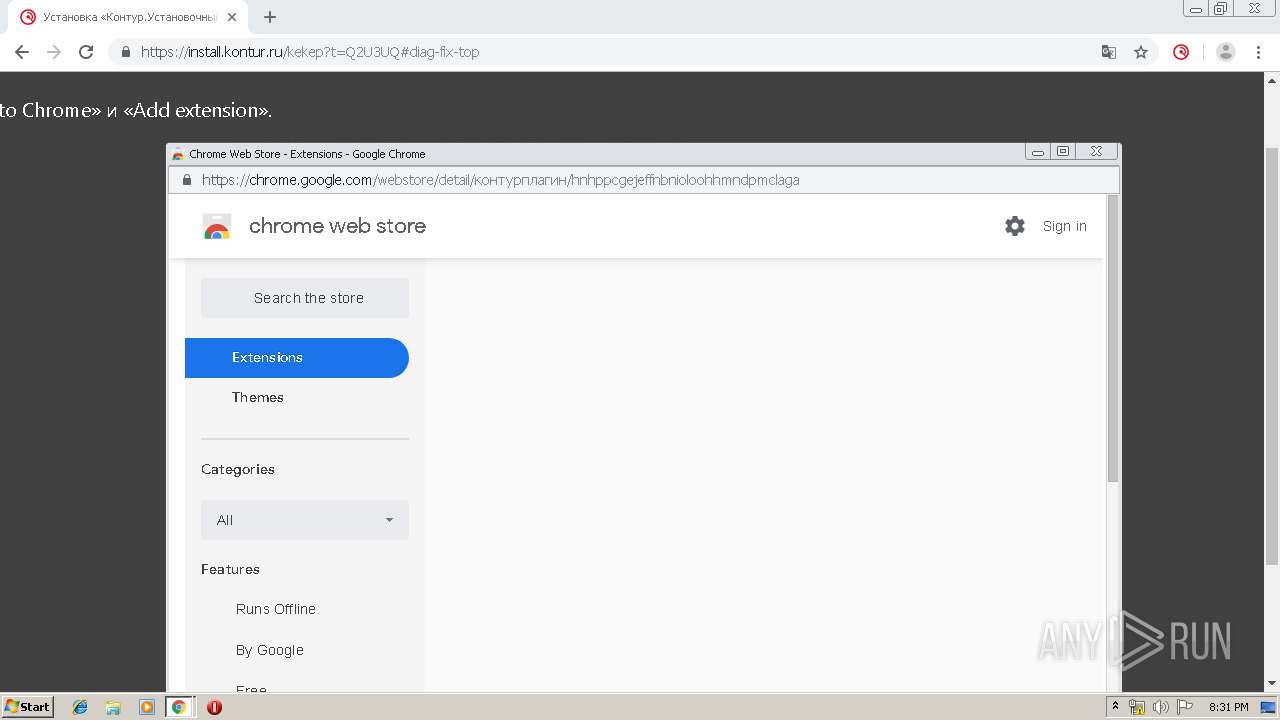
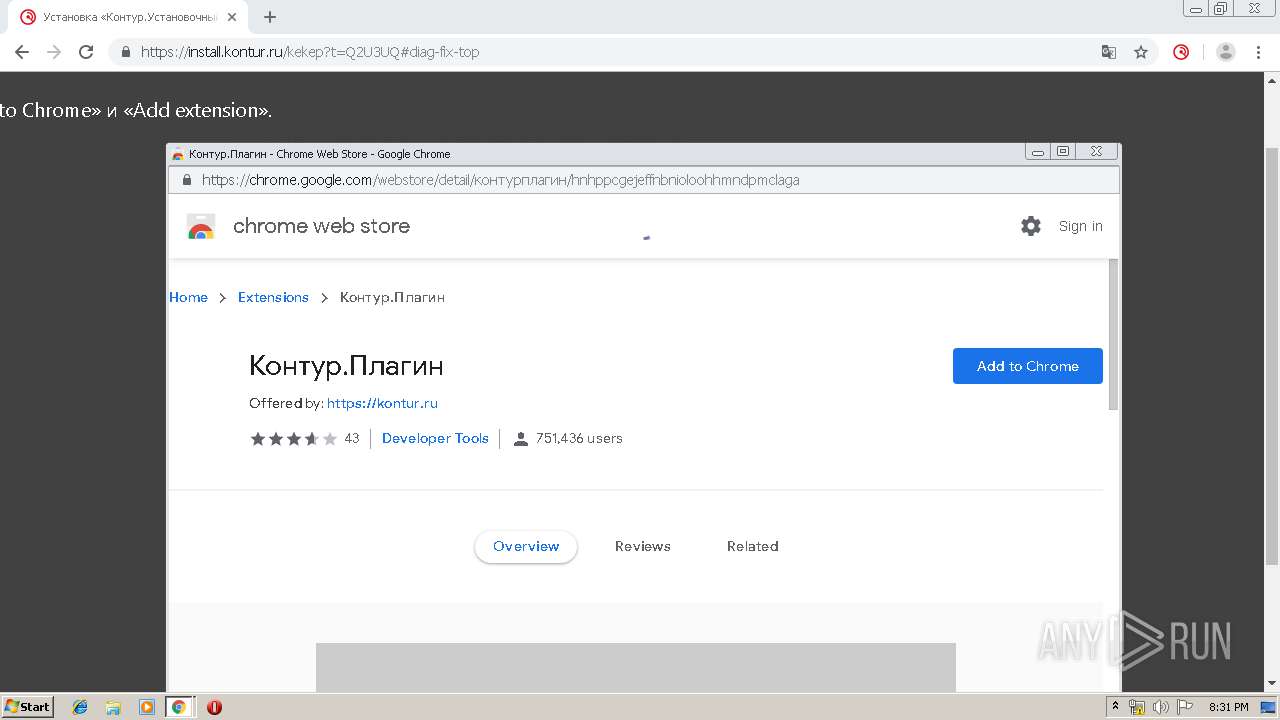
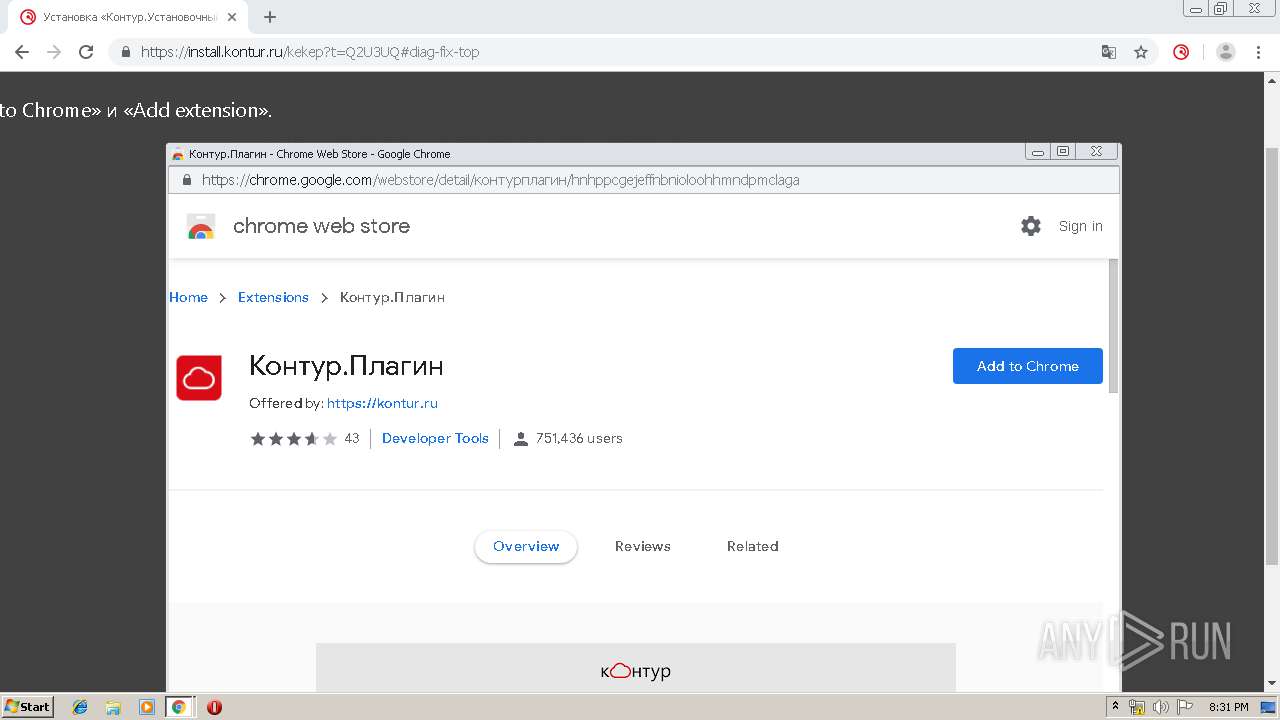
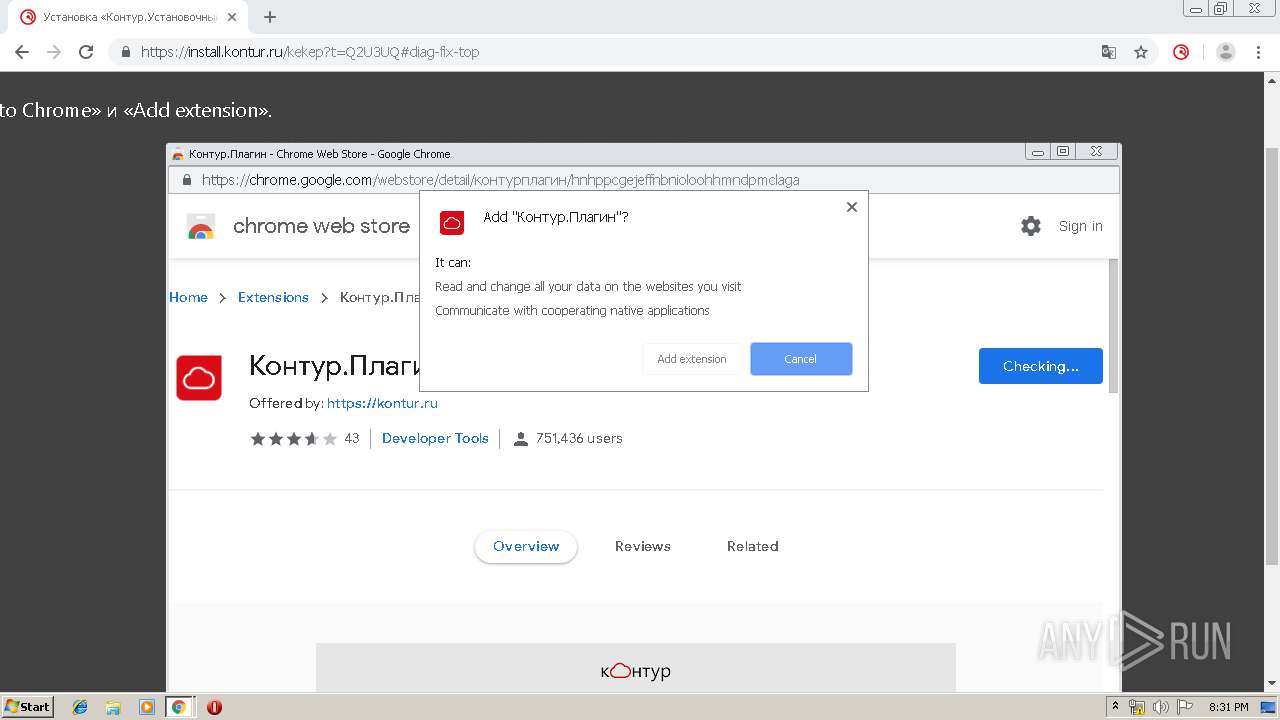
Modifies files in Chrome extension folder
- chrome.exe (PID: 2896)
Creates COM task schedule object
- regsvr32.exe (PID: 2444)
- msiexec.exe (PID: 2508)
- regsvr32.exe (PID: 4072)
Creates a software uninstall entry
- DiagPlugin_User.exe (PID: 2700)
- rtcomlite.exe (PID: 3952)
Creates files in the user directory
- DiagPlugin_User.exe (PID: 2700)
Starts CMD.EXE for commands execution
- chrome.exe (PID: 2896)
Adds / modifies Windows certificates
- kdnchost.exe (PID: 2812)
- CertFix_Host.exe (PID: 2188)
- kddisphost.exe (PID: 912)
Searches for installed software
- kdnchost.exe (PID: 2812)
Starts itself from another location
- addtotrusted.exe (PID: 1932)
Uses REG.EXE to modify Windows registry
- _tz.exe (PID: 2840)
Starts application with an unusual extension
- updatetimezones_enu.exe (PID: 1732)
Creates files in the Windows directory
- updatetimezones_enu.exe (PID: 1732)
- DrvInst.exe (PID: 3080)
- msiexec.exe (PID: 2508)
- MsiExec.exe (PID: 1544)
Starts Microsoft Installer
- Setup.exe (PID: 3664)
Executed via COM
- DrvInst.exe (PID: 3080)
Creates files in the program directory
- CSP40R4Setup.exe (PID: 1104)
- rtcomlite.exe (PID: 3952)
Removes files from Windows directory
- DrvInst.exe (PID: 3080)
- MsiExec.exe (PID: 1544)
Creates files in the driver directory
- DrvInst.exe (PID: 3080)
- MsiExec.exe (PID: 1544)
Executed as Windows Service
- vssvc.exe (PID: 1584)
INFO
Application launched itself
- chrome.exe (PID: 2896)
- msiexec.exe (PID: 2508)
Reads the hosts file
- chrome.exe (PID: 3936)
- chrome.exe (PID: 2896)
Reads Internet Cache Settings
- chrome.exe (PID: 2896)
Reads settings of System Certificates
- chrome.exe (PID: 2896)
- kdnchost.exe (PID: 2812)
- msiexec.exe (PID: 2508)
- Setup.exe (PID: 3664)
Creates files in the user directory
- chrome.exe (PID: 2896)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3036)
- MsiExec.exe (PID: 1544)
Creates a software uninstall entry
- MsiExec.exe (PID: 1544)
- msiexec.exe (PID: 2508)
Creates files in the program directory
- msiexec.exe (PID: 2508)
- MsiExec.exe (PID: 1544)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1584)
Changes settings of System certificates
- DrvInst.exe (PID: 3080)
Searches for installed software
- DrvInst.exe (PID: 3080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
152
Monitored processes
89
Malicious processes
18
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3313156030022675860 --mojo-platform-channel-handle=3796 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1474649840279584548 --mojo-platform-channel-handle=4068 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 456 | C:\Windows\system32\lsass.exe | C:\Windows\System32\lsass.exe | — | wininit.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Security Authority Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18164830790604595665 --mojo-platform-channel-handle=3380 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8790642685316126527 --mojo-platform-channel-handle=4884 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Users\admin\AppData\Local\SkbKontur\DiagPlugin\3.0.22.131\kddisphost.exe" 00000C039FA7E7BF pipe | C:\Users\admin\AppData\Local\SkbKontur\DiagPlugin\3.0.22.131\kddisphost.exe | kdnchost.exe | ||||||||||||
User: admin Company: АО "ПФ "СКБ Контур" Integrity Level: HIGH Description: Диаг.Плагин - хост-приложение диспетчера сообщений Exit code: 0 Version: 1.131.27.5040 Modules
| |||||||||||||||
| 920 | "C:\Users\admin\AppData\Local\Temp\HelpKontur\k4em0ukj\cpverify.exe" "C:\Users\admin\AppData\Local\Temp\HelpKontur\k4em0eok\CSP40R4Setup.exe" CDF7B587A56A488916DB961630B419285918DABD60EE67CBD18D41B04FC18A49 | C:\Users\admin\AppData\Local\Temp\HelpKontur\k4em0ukj\cpverify.exe | — | kdnchost.exe | |||||||||||
User: admin Company: Crypto-Pro LLC Integrity Level: MEDIUM Description: CSP/HSM integrity supervisor Exit code: 0 Version: 4.0.4643.0 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12668251100212323135 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8731098464082884726 --mojo-platform-channel-handle=3512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
9 390
Read events
4 354
Write events
4 986
Delete events
50
Modification events
| (PID) Process: | (1756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2896-13221347375750375 |
Value: 259 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
286
Suspicious files
88
Text files
479
Unknown types
78
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3998ef.TMP | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\deb104af-9a3a-41a1-9e4a-2c26f8e76789.tmp | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39990e.TMP | text | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39993d.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
140
DNS requests
91
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2188 | CertFix_Host.exe | GET | — | 93.184.220.29:80 | http://crl.verisign.com/pca3.crl | US | — | — | whitelisted |
3936 | chrome.exe | GET | 302 | 172.217.17.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
2812 | kdnchost.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gsextendcodesignsha2g3/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQ3DAV9N6WelMGCzSTdNIqjdmfHiAQU3CxYLCpvNS2feZWoSF3EbT5Tv7kCDEDpfxhRWoewamhEKQ%3D%3D | US | der | 1.55 Kb | whitelisted |
2812 | kdnchost.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDkgbagepQkweqv7zzfEP | US | der | 1.48 Kb | whitelisted |
2812 | kdnchost.exe | GET | 200 | 23.43.75.27:80 | http://ts-ocsp.ws.symantec.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRi82PVYYKWGJWdgVNyePy5kYTdqQQUX5r1blzMzHSa1N197z%2Fb7EyALt0CEA7P9DjI%2Fr81bgTYapgbGlA%3D | NL | der | 1.43 Kb | whitelisted |
1080 | svchost.exe | GET | 200 | 92.122.253.175:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | der | 813 b | whitelisted |
— | — | GET | 200 | 151.139.128.14:80 | http://ocsp.trust-provider.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEHbYt4bR81JP7pU%2BcUA9mdU%3D | US | der | 471 b | whitelisted |
— | — | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQCA9WBtOhYrFDrcEvvowgZv | US | der | 314 b | whitelisted |
— | — | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ2xvBYPgmu%2FP%2FmXiVKe%2BjES00TfwQU78EqlQwy2vtzMNyKE9gVS%2FcT6PgCEG8uQSIolB1kqNt7vj9%2B2M4%3D | US | der | 279 b | whitelisted |
1080 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3936 | chrome.exe | 172.217.20.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
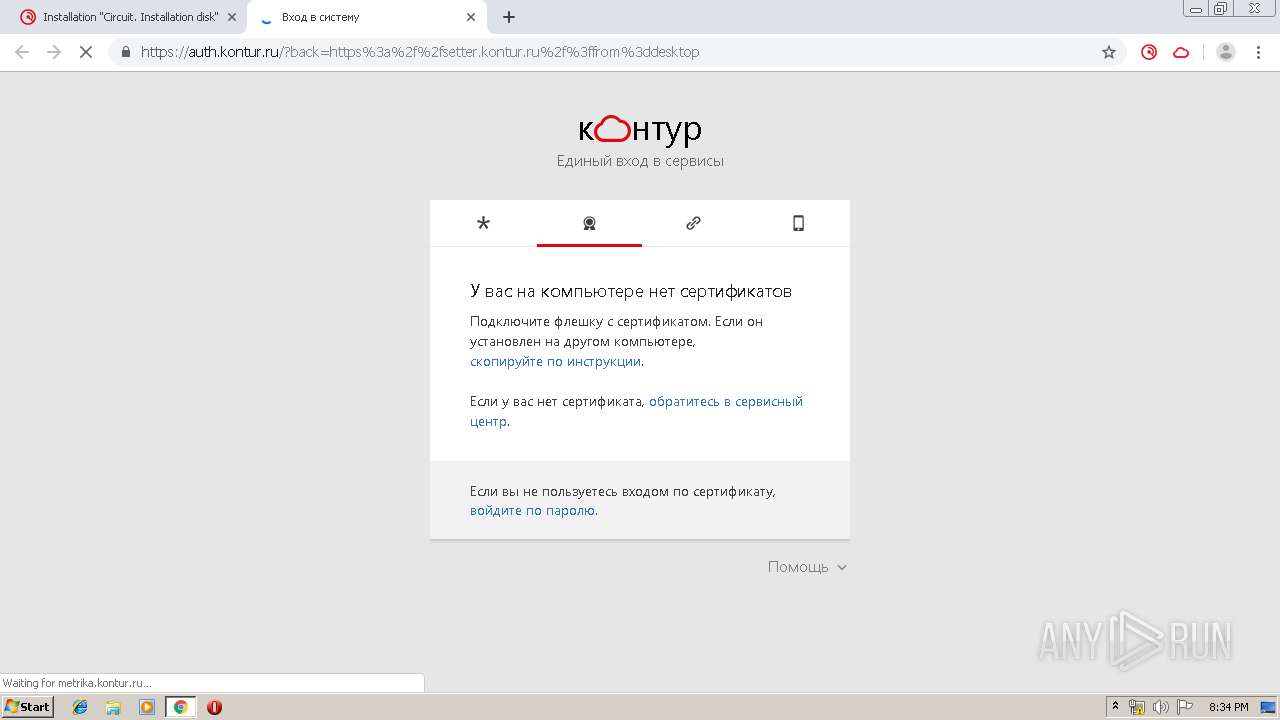
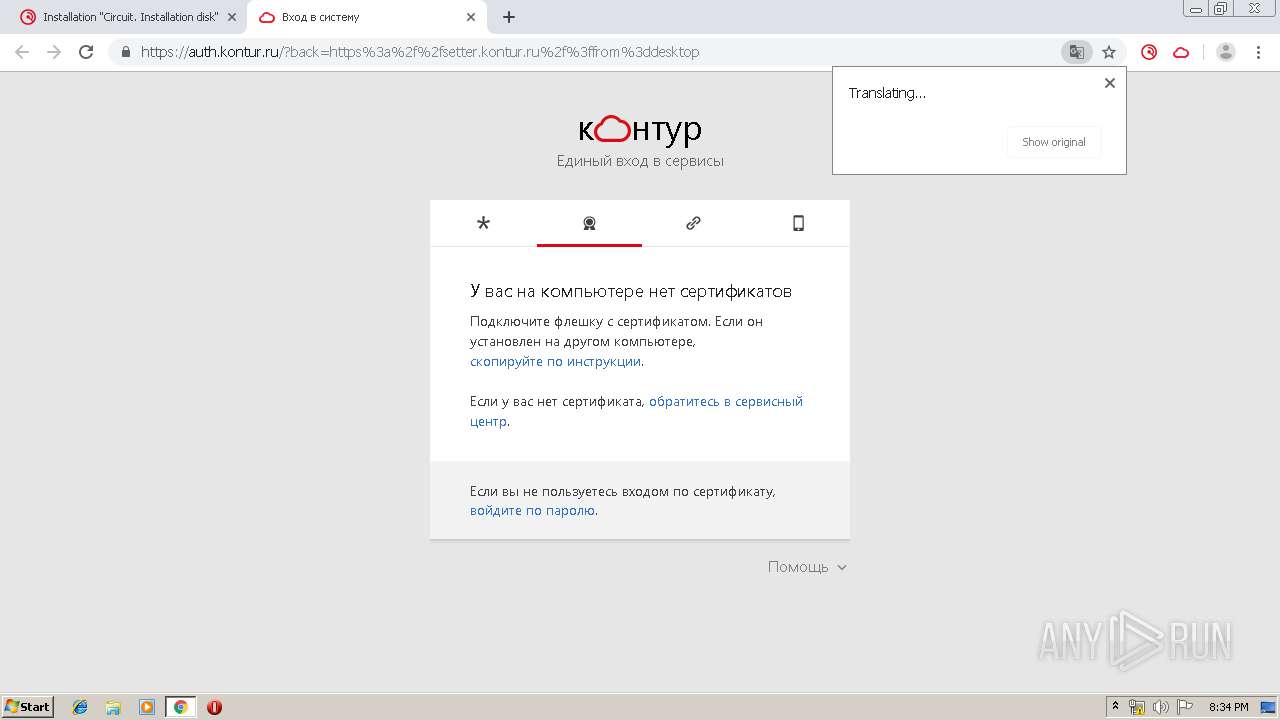
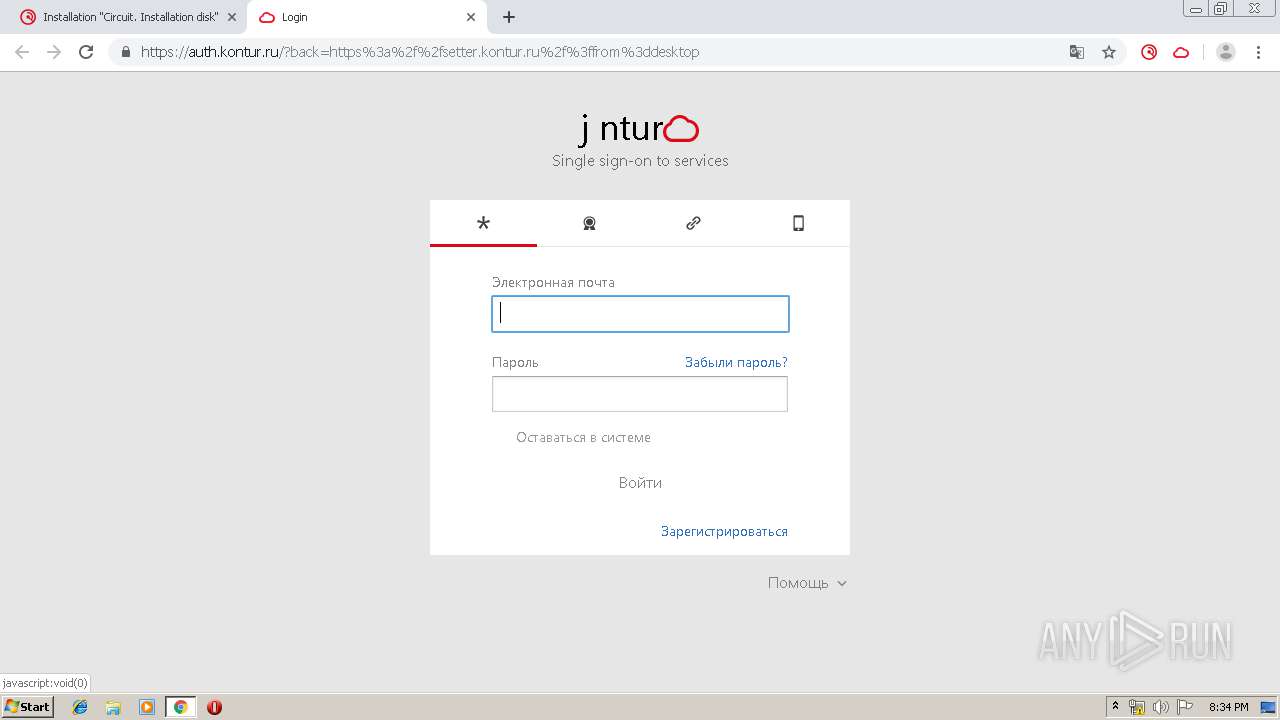
3936 | chrome.exe | 46.17.203.51:443 | install.kontur.ru | CJSC Production Company SKB Kontur | RU | suspicious |
3936 | chrome.exe | 172.217.17.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3936 | chrome.exe | 46.17.203.45:443 | api.kontur.ru | CJSC Production Company SKB Kontur | RU | unknown |
3936 | chrome.exe | 172.217.20.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
3936 | chrome.exe | 172.217.17.106:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3936 | chrome.exe | 172.217.19.200:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
3936 | chrome.exe | 46.17.203.250:443 | metrika.kontur.ru | CJSC Production Company SKB Kontur | RU | unknown |
3936 | chrome.exe | 216.58.208.100:443 | www.google.com | Google Inc. | US | whitelisted |
3936 | chrome.exe | 172.217.17.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
install.kontur.ru |
| suspicious |
accounts.google.com |
| shared |
help.kontur.ru |
| suspicious |
api.kontur.ru |
| unknown |
clients1.google.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
metrika.kontur.ru |
| unknown |
www.google.com |
| malicious |
Threats
13 ETPRO signatures available at the full report