| File name: | ous7q.exe |
| Full analysis: | https://app.any.run/tasks/23e622d8-f009-4457-b862-195c9693901f |
| Verdict: | Malicious activity |
| Analysis date: | November 17, 2020, 11:47:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
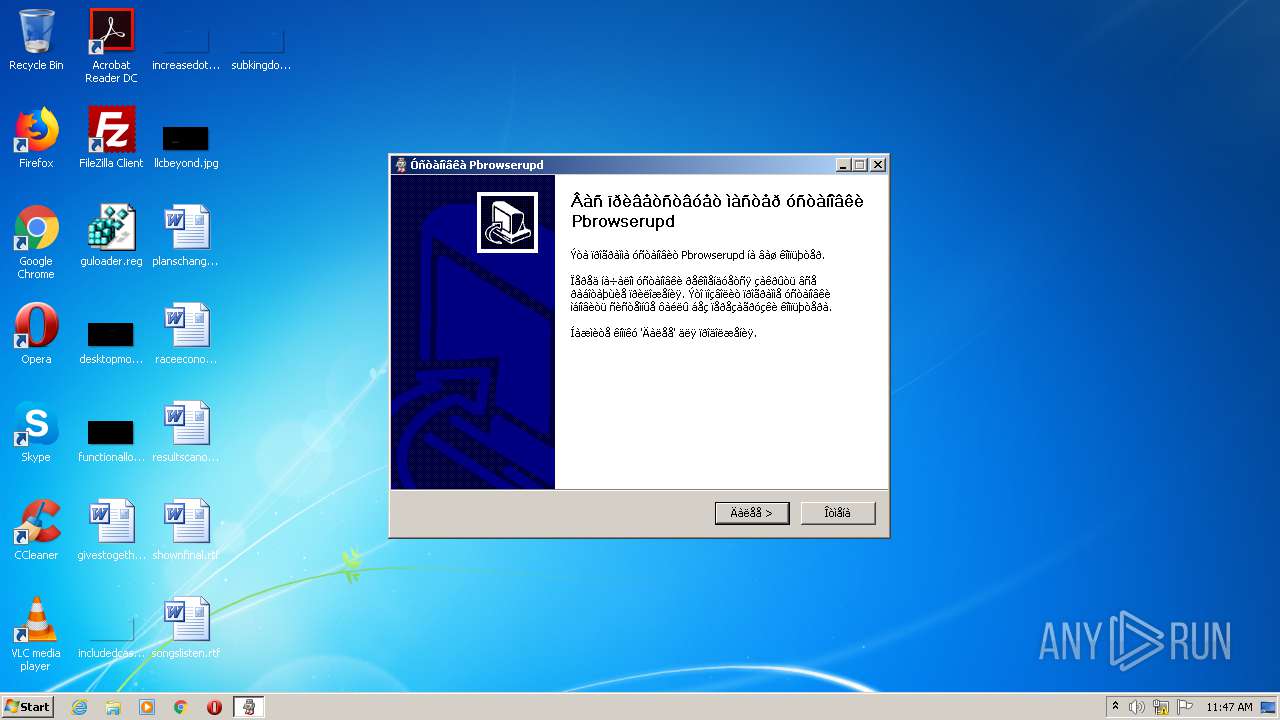
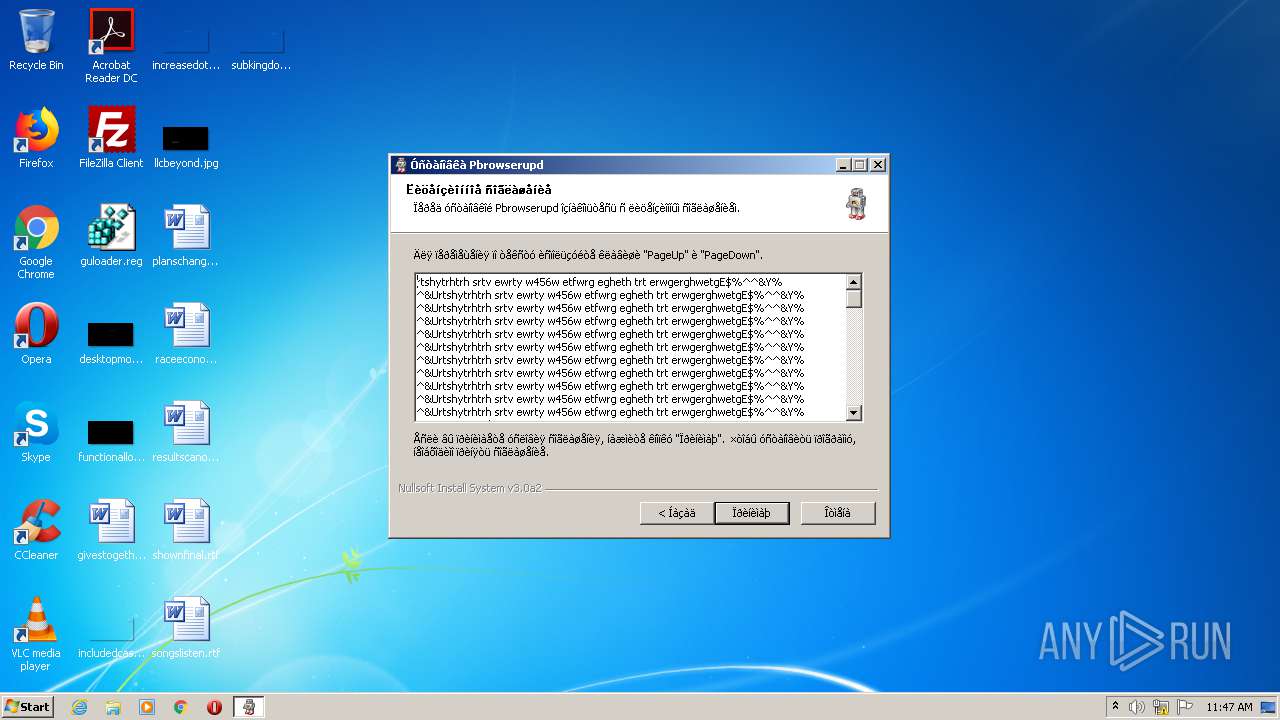
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 3C096A417A8B506945185245CB923CAC |
| SHA1: | 8136FD58A59B8ACD32A8518F7CC98F1A65F5D6F2 |
| SHA256: | 2100E30B6324A98229C6BA5989688EB25C2E7D4182420FF777E8B1DA6F1FB54E |
| SSDEEP: | 24576:RCLC79fVspdAnQ+mRDp45agmro7j6HjhILhbAfhZhn0+:RCsfVspyndaD8HShIl0JZhL |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2612)
SUSPICIOUS
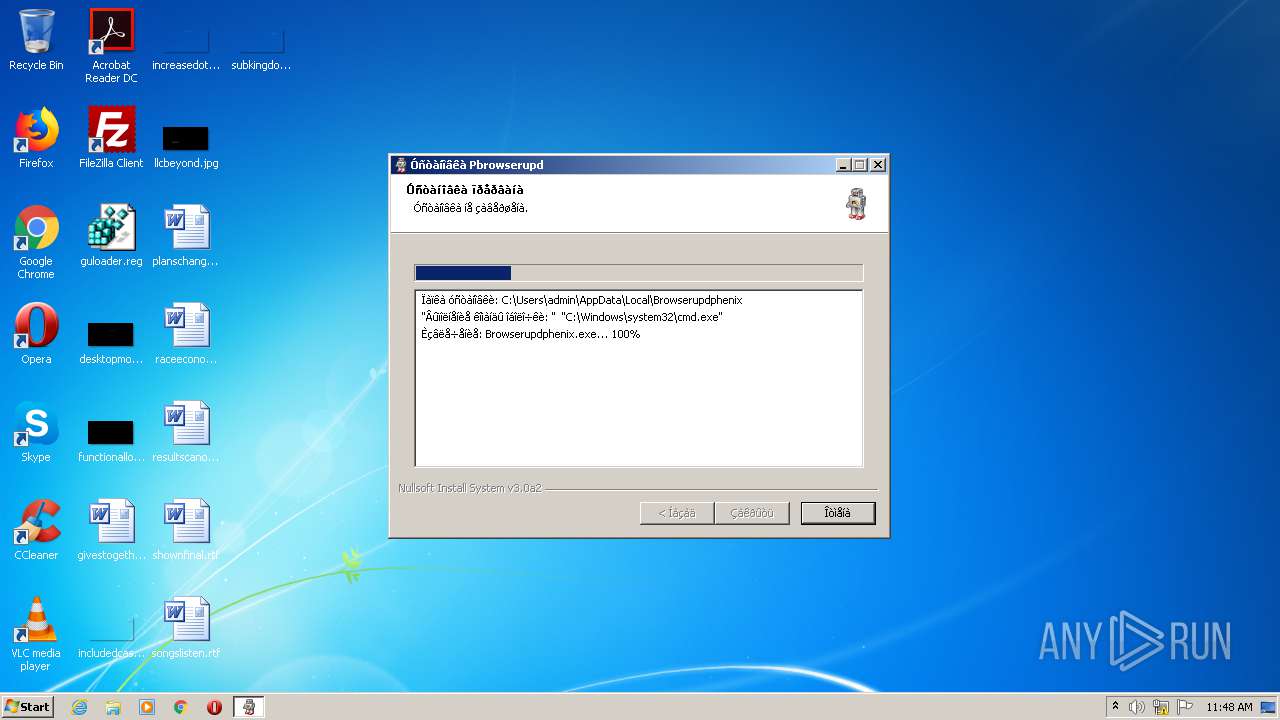
Starts CMD.EXE for commands execution
- ous7q.exe (PID: 2972)
Executable content was dropped or overwritten
- ous7q.exe (PID: 2972)
Creates files in the user directory
- powershell.exe (PID: 4064)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:12:25 06:01:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30e4 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Dec-2013 05:01:41 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Dec-2013 05:01:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005DE2 | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50844 |
.rdata | 0x00007000 | 0x000012DA | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.10051 |
.data | 0x00009000 | 0x00025498 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.04207 |
.ndata | 0x0002F000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003F000 | 0x00022850 | 0x00022A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.45345 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25973 | 1013 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.86261 | 21887 | UNKNOWN | English - United States | RT_ICON |
3 | 7.89086 | 11016 | UNKNOWN | English - United States | RT_ICON |
4 | 4.15518 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 4.39607 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 4.69987 | 3752 | UNKNOWN | English - United States | RT_ICON |
7 | 4.49678 | 2440 | UNKNOWN | English - United States | RT_ICON |
8 | 5.54548 | 2216 | UNKNOWN | English - United States | RT_ICON |
9 | 5.85917 | 1736 | UNKNOWN | English - United States | RT_ICON |
10 | 3.19231 | 1640 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
40
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2220 | "C:\Users\admin\AppData\Local\Temp\ous7q.exe" | C:\Users\admin\AppData\Local\Temp\ous7q.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
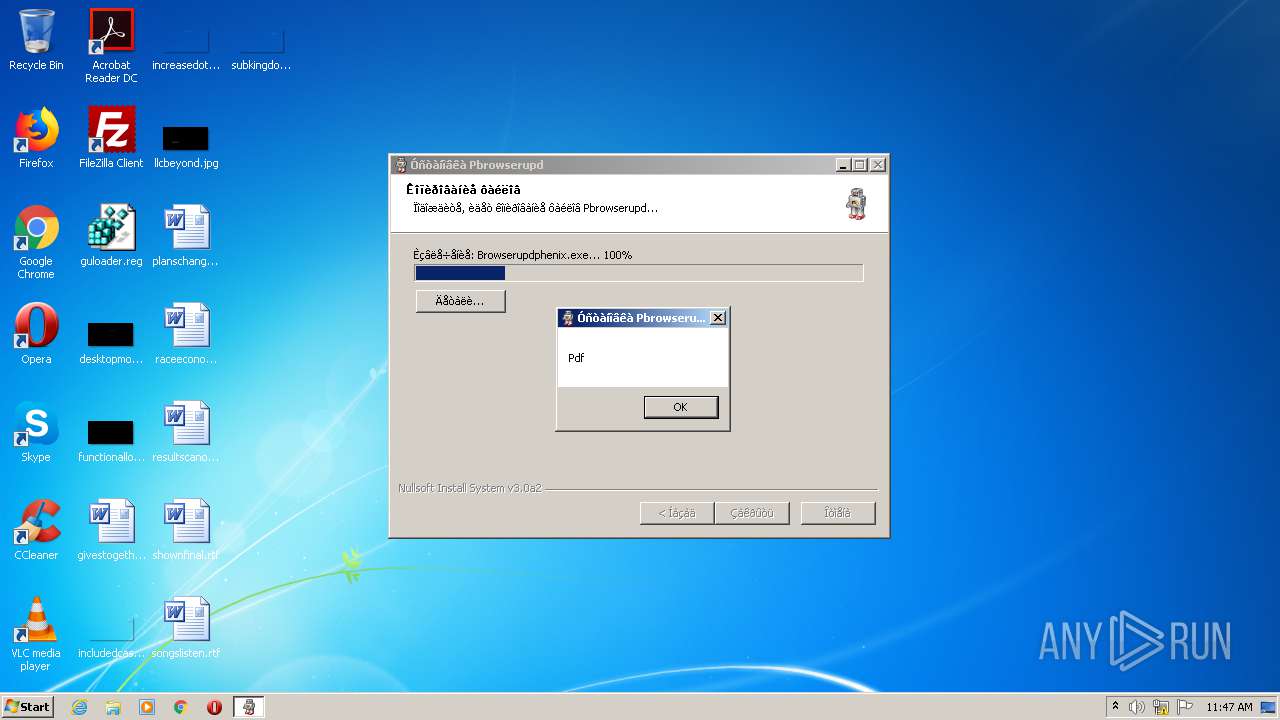
| 2612 | "C:\Windows\system32\cmd.exe" /C powershell -inputformat none -outputformat none -NonInteractive -Command "Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\Browserupdphenix'" | C:\Windows\system32\cmd.exe | — | ous7q.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2972 | "C:\Users\admin\AppData\Local\Temp\ous7q.exe" | C:\Users\admin\AppData\Local\Temp\ous7q.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4064 | powershell -inputformat none -outputformat none -NonInteractive -Command "Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\Browserupdphenix'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
599
Read events
540
Write events
59
Delete events
0
Modification events
| (PID) Process: | (2972) ous7q.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2972) ous7q.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4064) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
3
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4064 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\COSH5CG9S27Q2VW9VXJN.temp | — | |
MD5:— | SHA256:— | |||
| 4064 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF14173f.TMP | binary | |
MD5:— | SHA256:— | |||
| 4064 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2972 | ous7q.exe | C:\Users\admin\AppData\Local\Browserupdphenix\Browserupdphenix.exe | executable | |
MD5:7FD1076D1F4866834F83656800AAB72F | SHA256:D85562CB7F2D3469595E18375A9C5CD3A2A593E1770B94C53244DC1550F34C50 | |||
| 2972 | ous7q.exe | C:\Users\admin\AppData\Local\Temp\nsc203.tmp\nsDialogs.dll | executable | |
MD5:8CED0B79F7B9033D0795AAB3BE6D627C | SHA256:495BDDC0BE6E18E981DB82FAB9D1DE55C7E269AB4EC3FF43035193BC017A307B | |||
| 2972 | ous7q.exe | C:\Users\admin\AppData\Local\Temp\nsc203.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 2972 | ous7q.exe | C:\Users\admin\AppData\Local\Temp\nsc203.tmp\System.dll | executable | |
MD5:960A5C48E25CF2BCA332E74E11D825C9 | SHA256:484F8E9F194ED9016274EF3672B2C52ED5F574FB71D3884EDF3C222B758A75A2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report