| File name: | Mal%20Emails.zip |
| Full analysis: | https://app.any.run/tasks/9fd0de68-951b-4f00-87c5-d3f4b6ff8d9b |
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2019, 17:19:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | A8EED002561A1CDB748FED15D8D89EC8 |
| SHA1: | ED8EB0A43D8DA4C05F1CF8C52115D7E8FB7C81AF |
| SHA256: | 20FB9059FFA16666C66EF448DE5162113EC1CE4D2848A4E726598E0A641089D4 |
| SSDEEP: | 12288:F4JOxn7ATwqgJlcr2uOmSrBLk9oVBPl3QeMIhic668MZjlKpIhCroceHurzv:F44NAMqgYrDS5N3QeMBc661jCDeob |
MALICIOUS
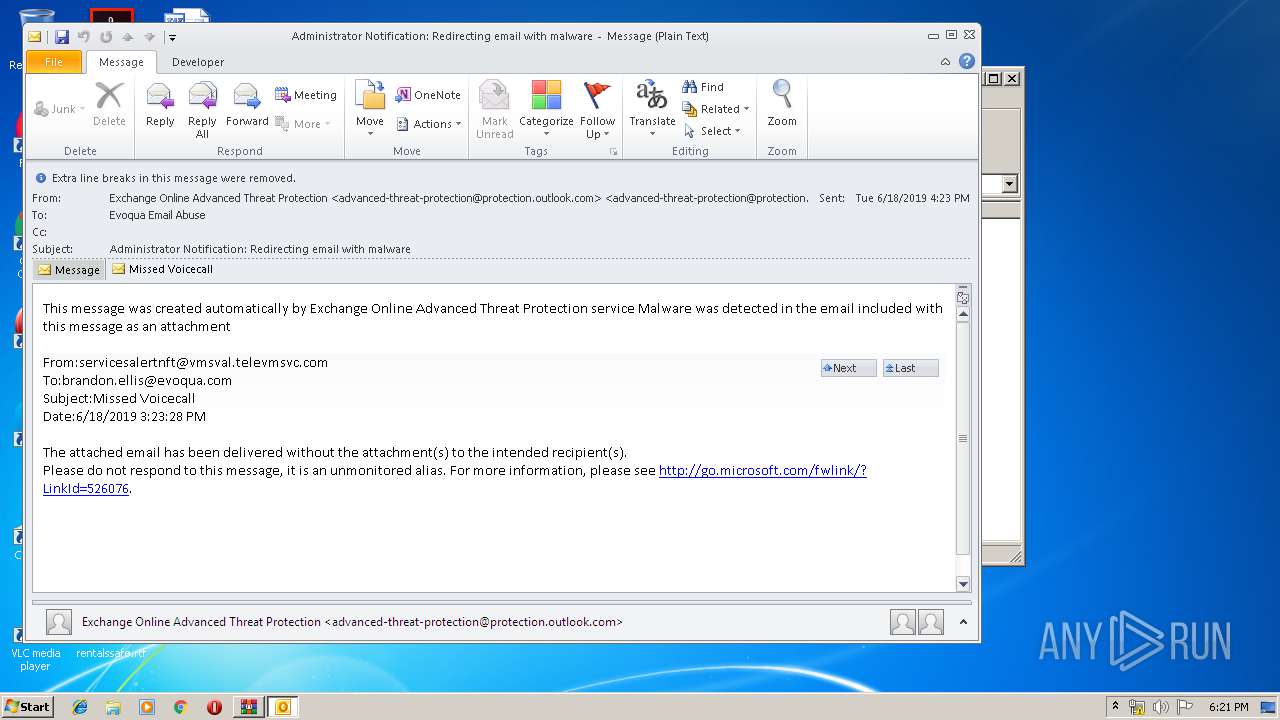
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3392)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3392)
Starts Microsoft Office Application
- WinRAR.exe (PID: 2948)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3392)
- OUTLOOK.EXE (PID: 2972)
- OUTLOOK.EXE (PID: 2432)
- OUTLOOK.EXE (PID: 2764)
Executed via COM
- OUTLOOK.EXE (PID: 3188)
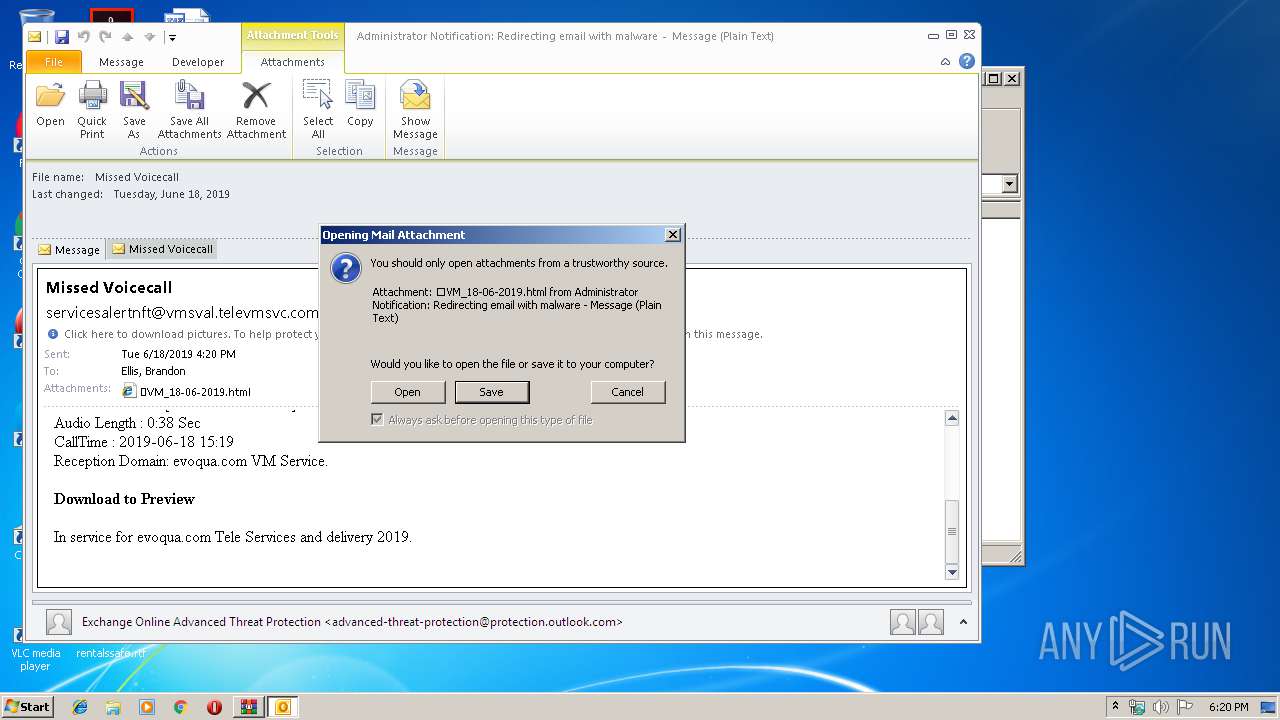
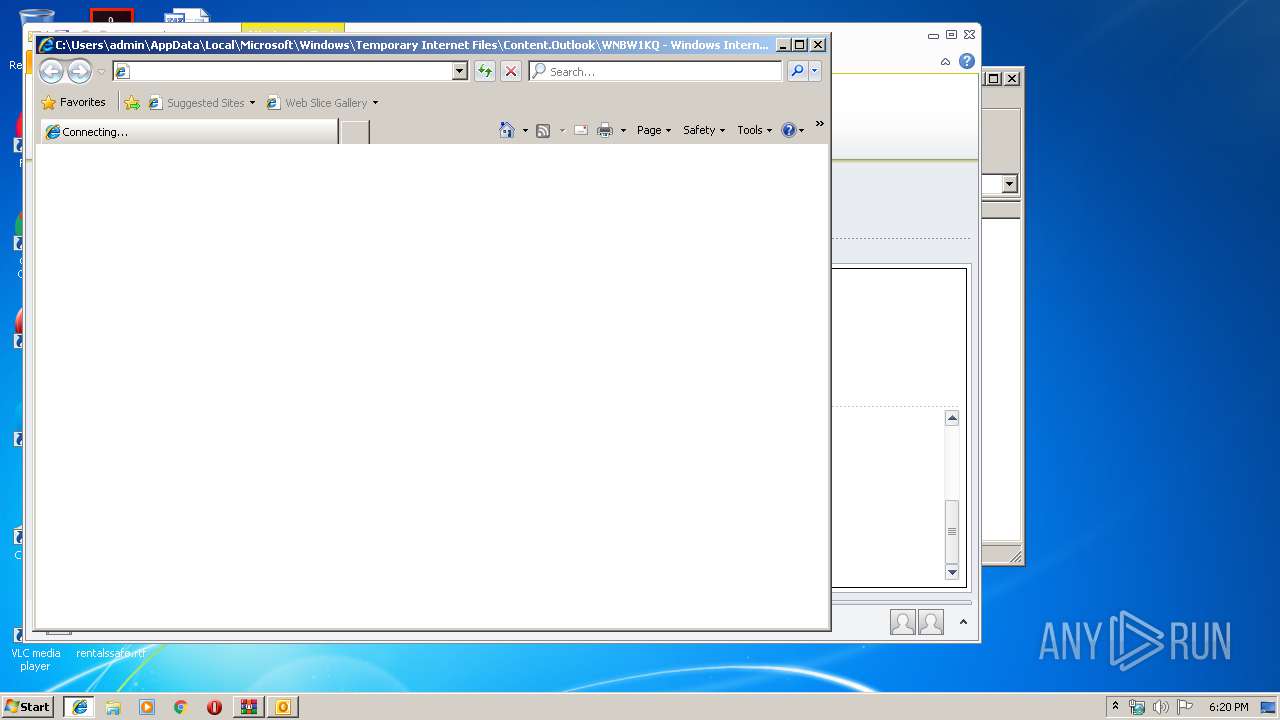
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3392)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2948)
- OUTLOOK.EXE (PID: 3392)
- OUTLOOK.EXE (PID: 2972)
- WinRAR.exe (PID: 676)
Changes internet zones settings
- iexplore.exe (PID: 3972)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3188)
- OUTLOOK.EXE (PID: 3392)
- OUTLOOK.EXE (PID: 2972)
- OUTLOOK.EXE (PID: 2432)
- OUTLOOK.EXE (PID: 2764)
Creates files in the user directory
- iexplore.exe (PID: 2800)
Application launched itself
- iexplore.exe (PID: 3972)
Reads Internet Cache Settings
- iexplore.exe (PID: 2800)
- iexplore.exe (PID: 3972)
Reads internet explorer settings
- iexplore.exe (PID: 2800)
Manual execution by user
- WinRAR.exe (PID: 676)
- OUTLOOK.EXE (PID: 2764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
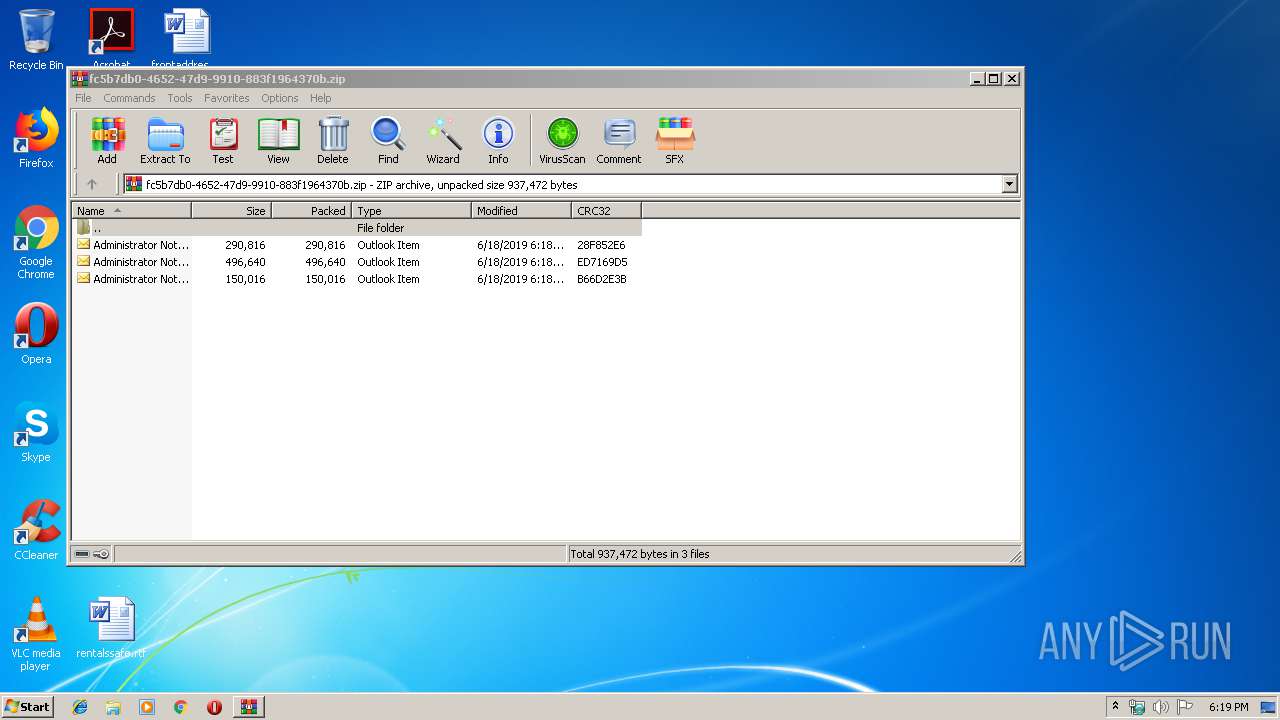
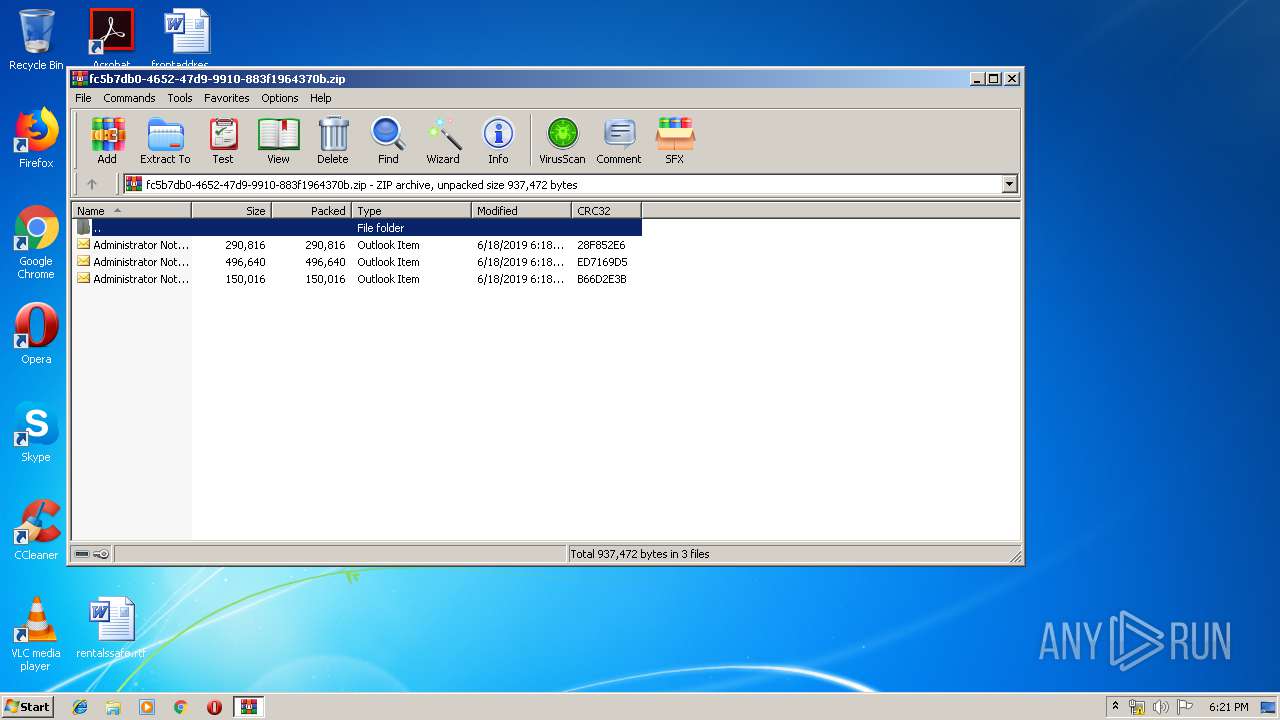
ZIP
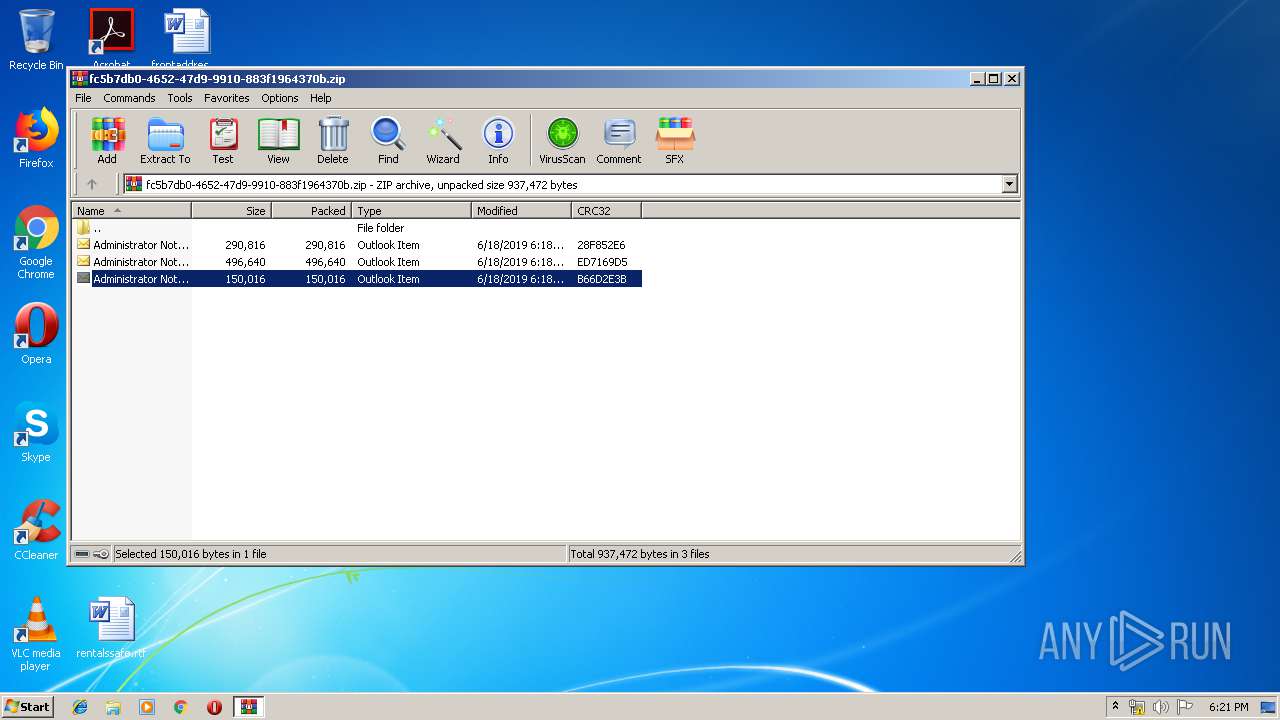
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | None |
| ZipModifyDate: | 2019:06:18 17:18:29 |
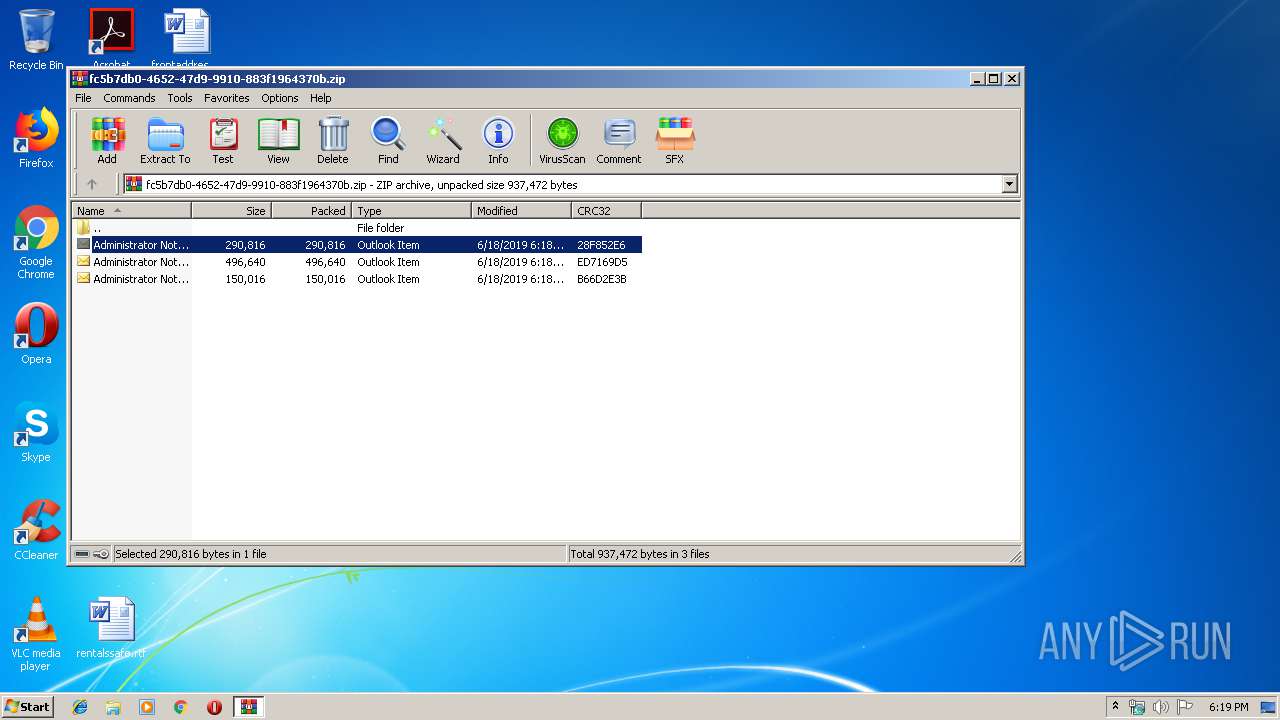
| ZipCRC: | 0x28f852e6 |
| ZipCompressedSize: | 290816 |
| ZipUncompressedSize: | 290816 |
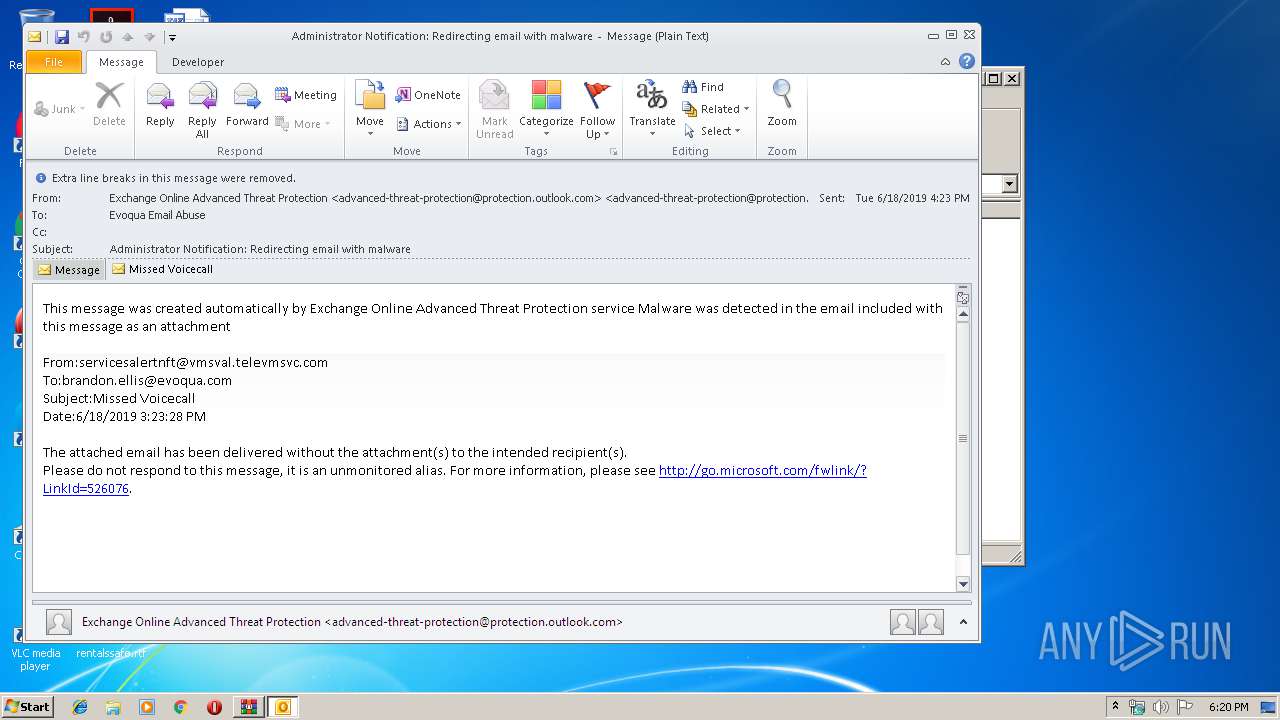
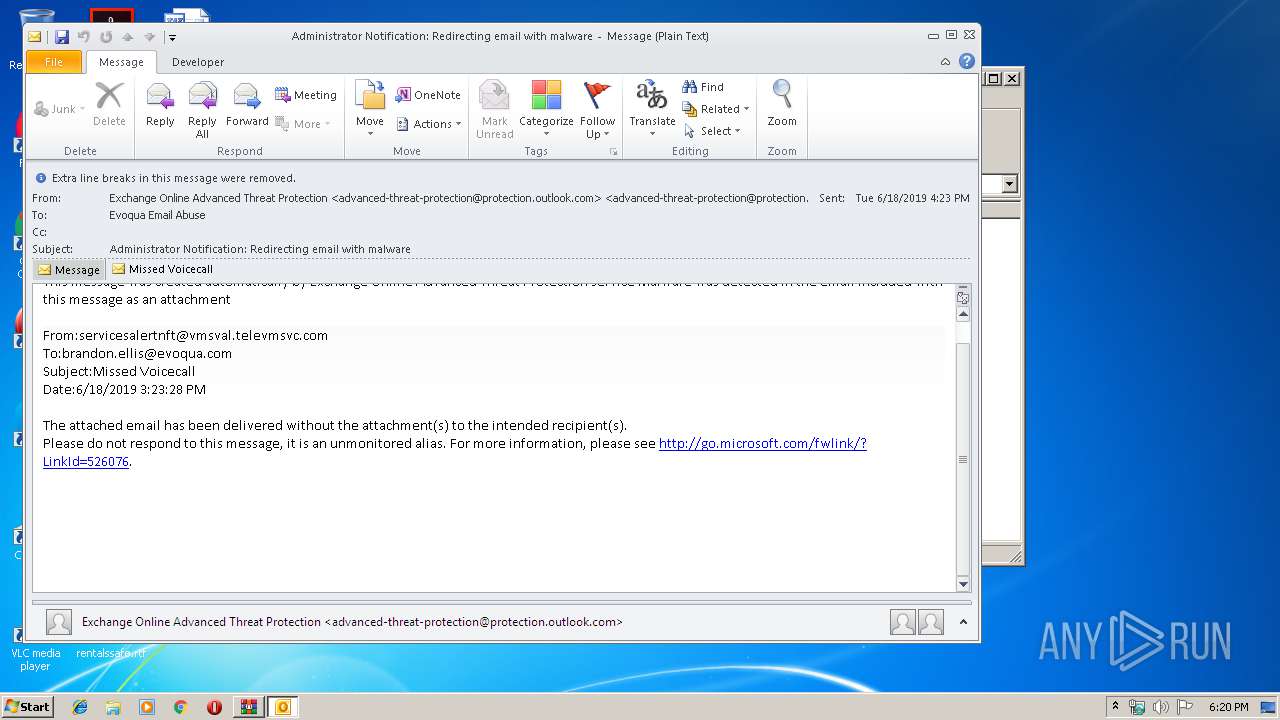
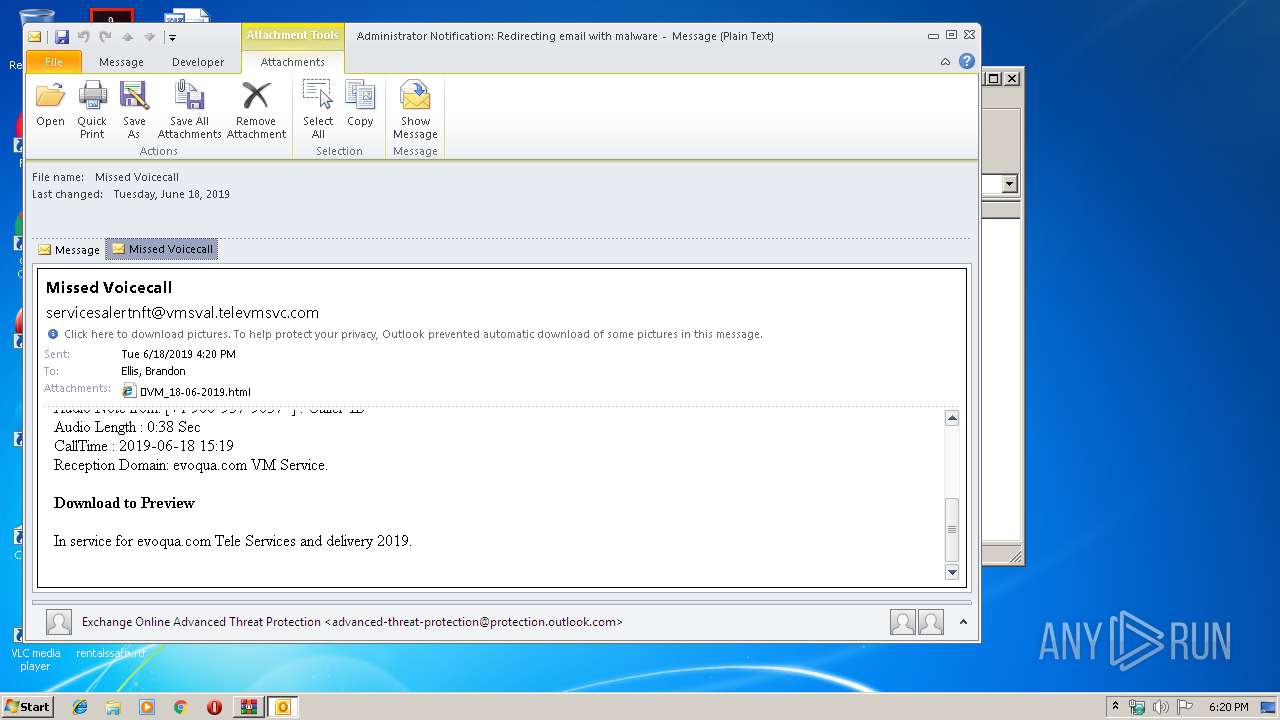
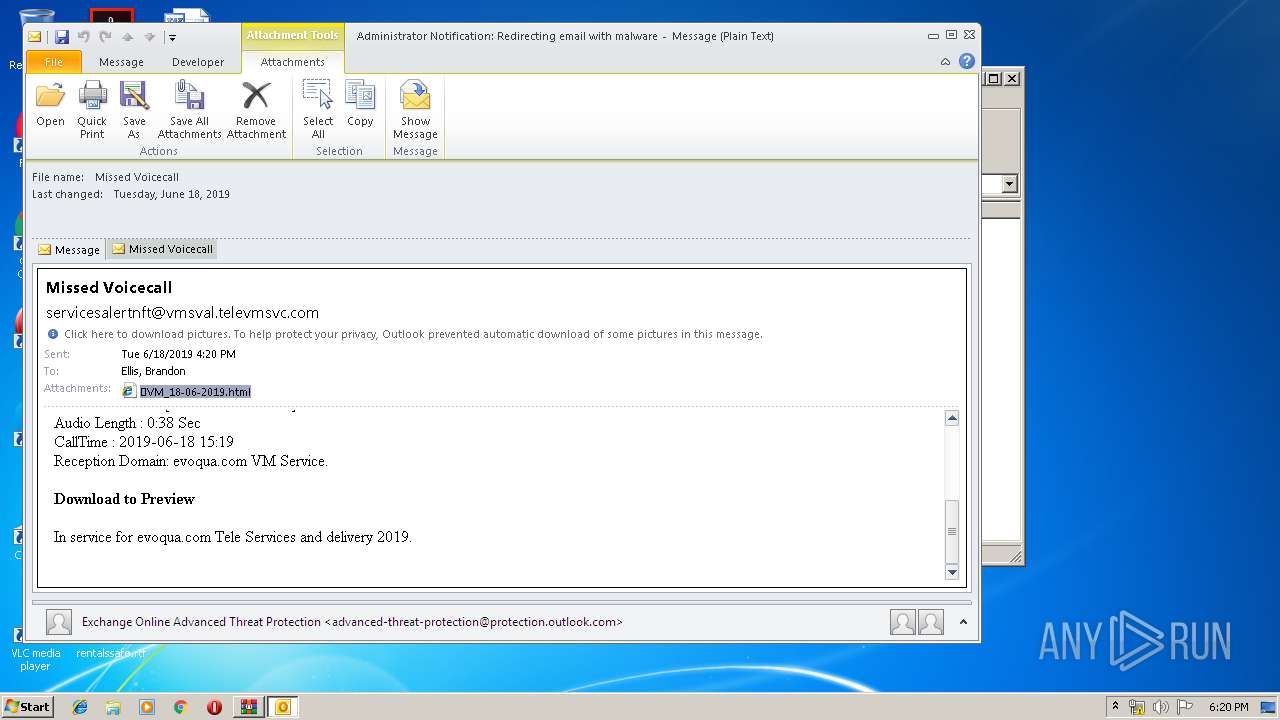
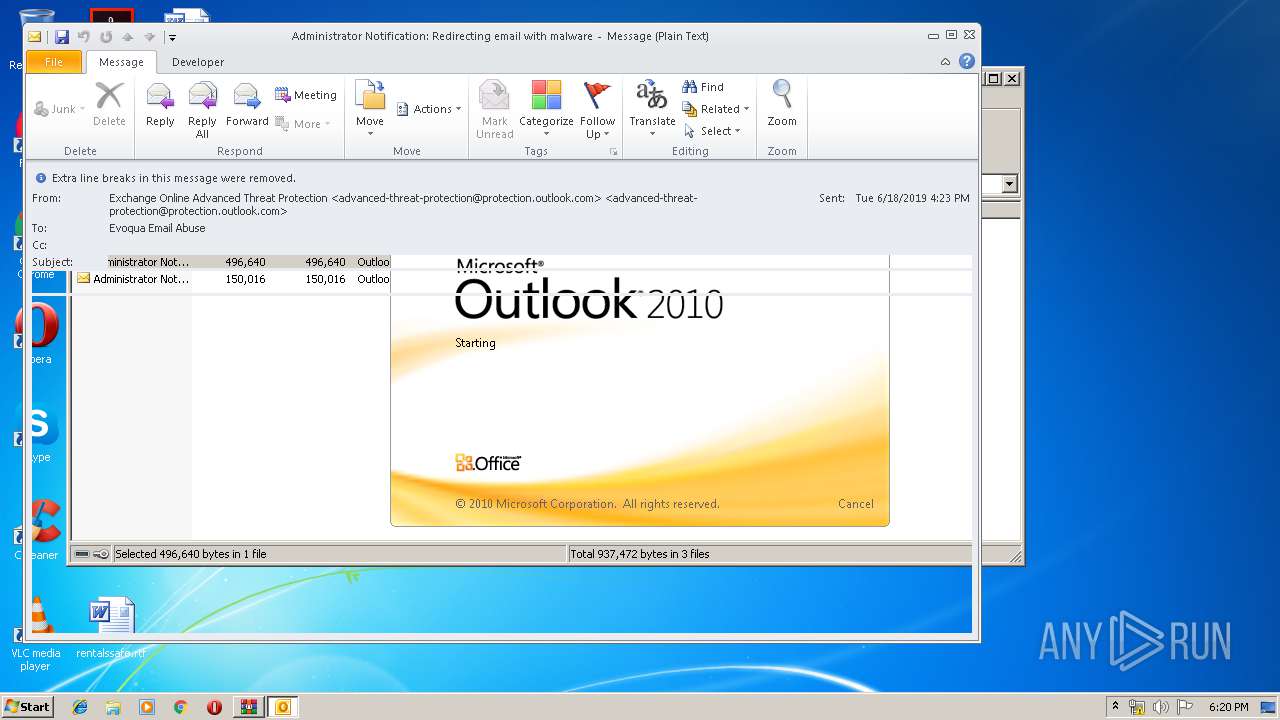
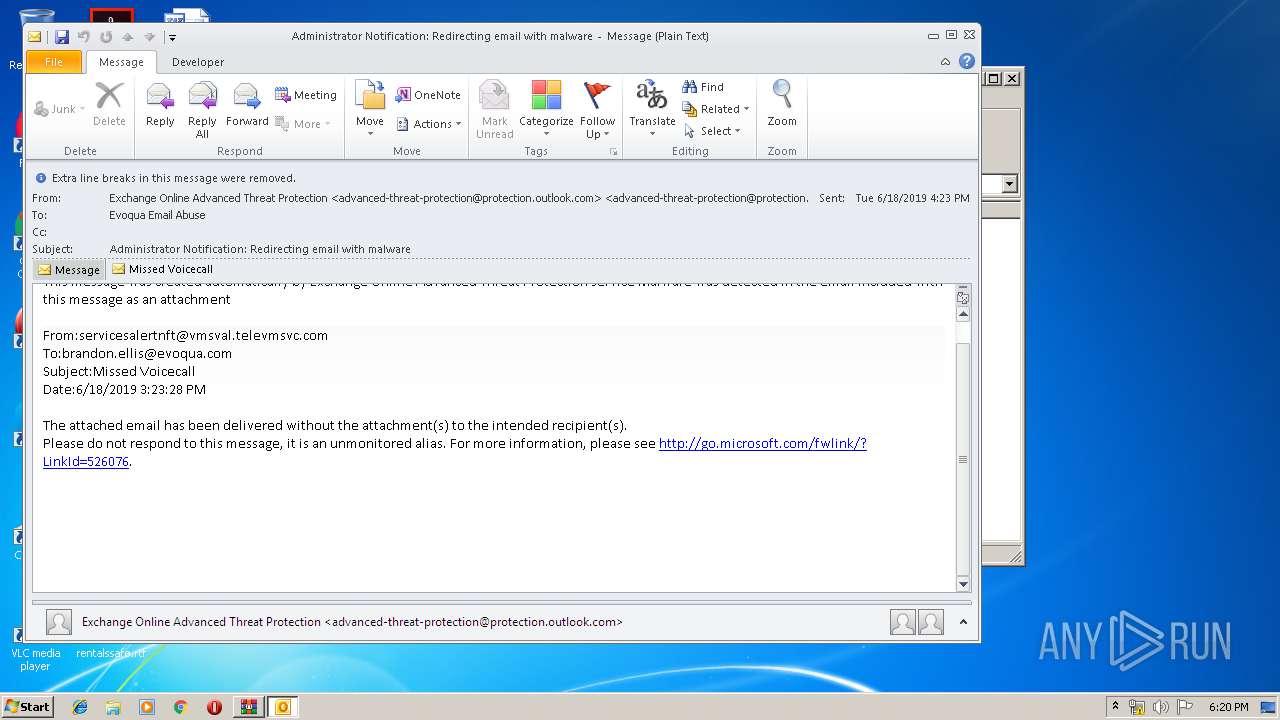
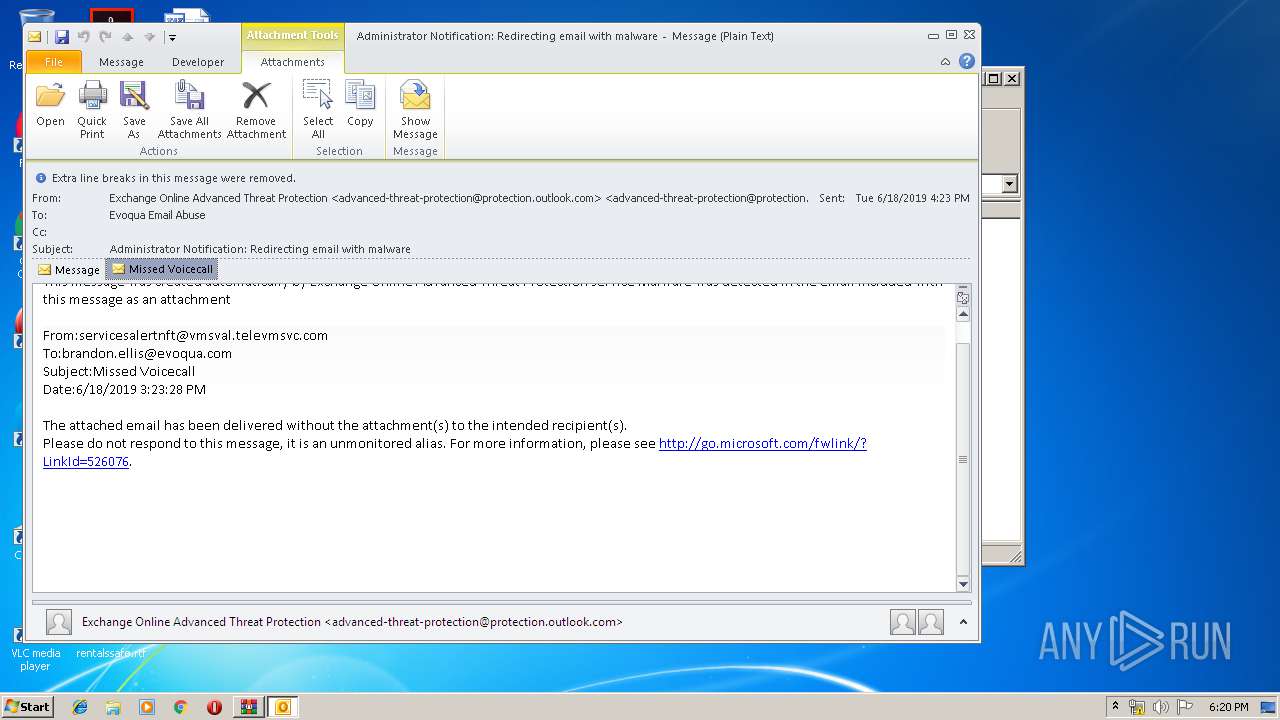
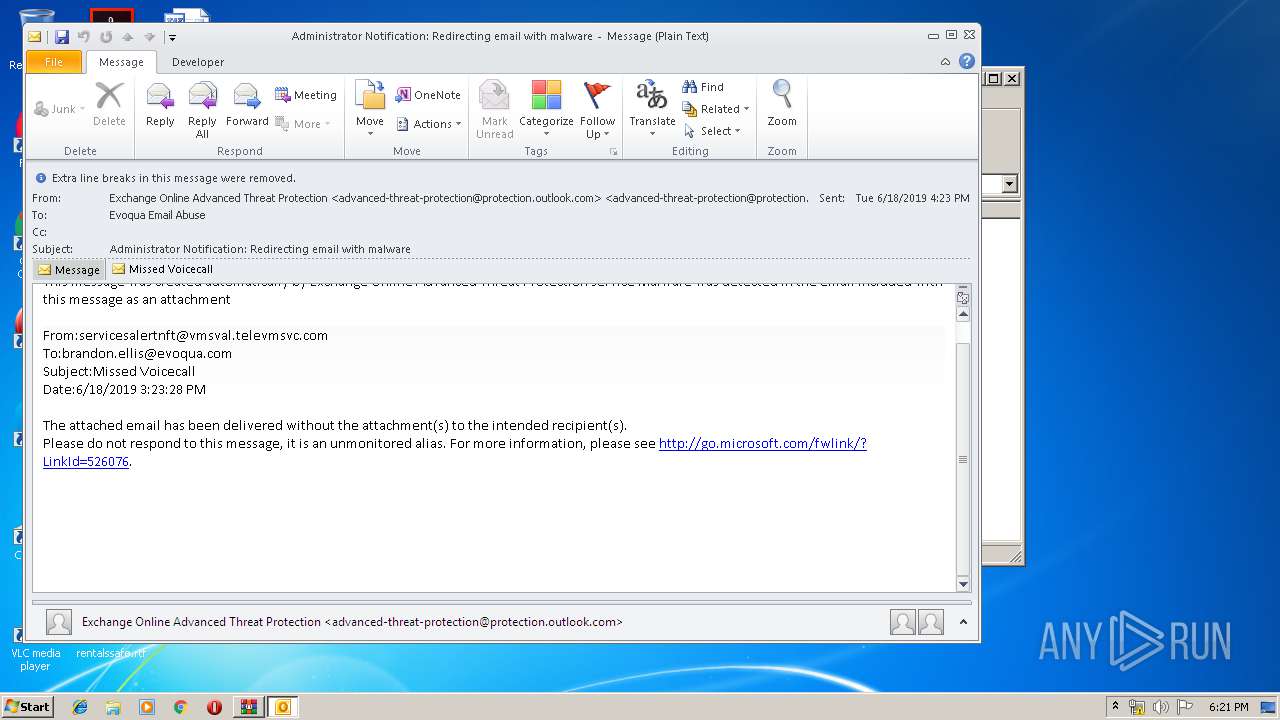
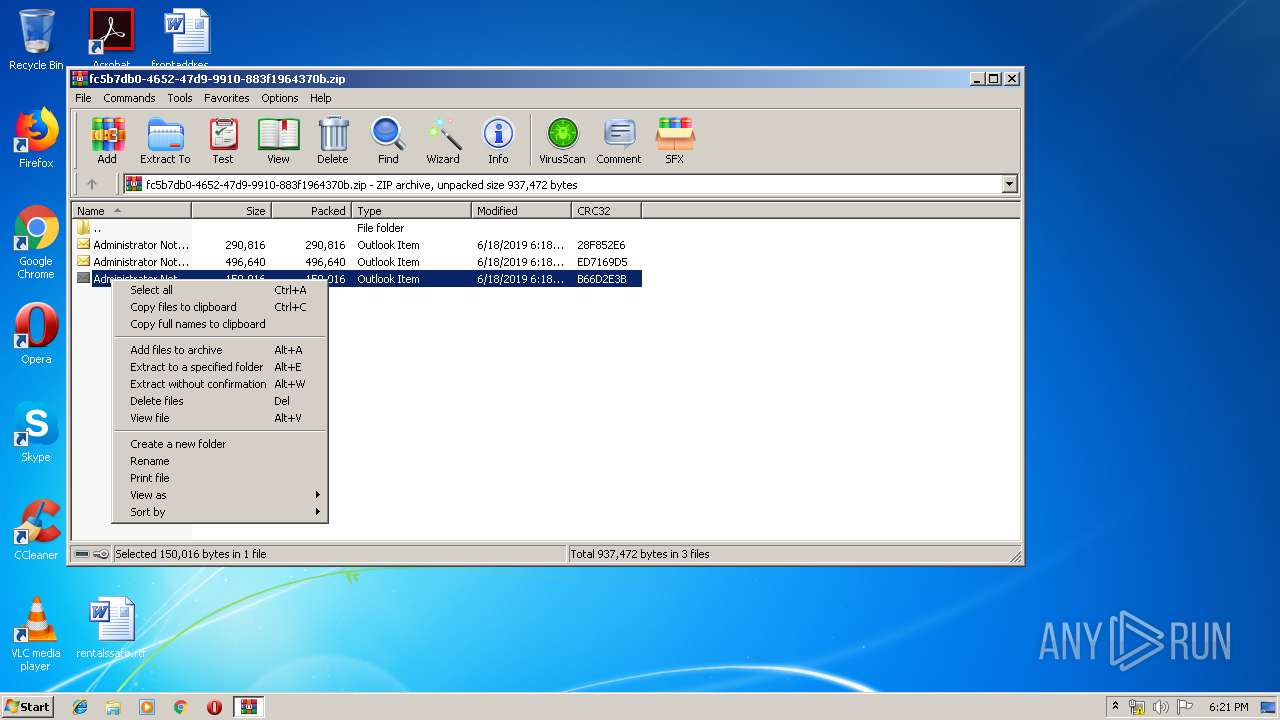
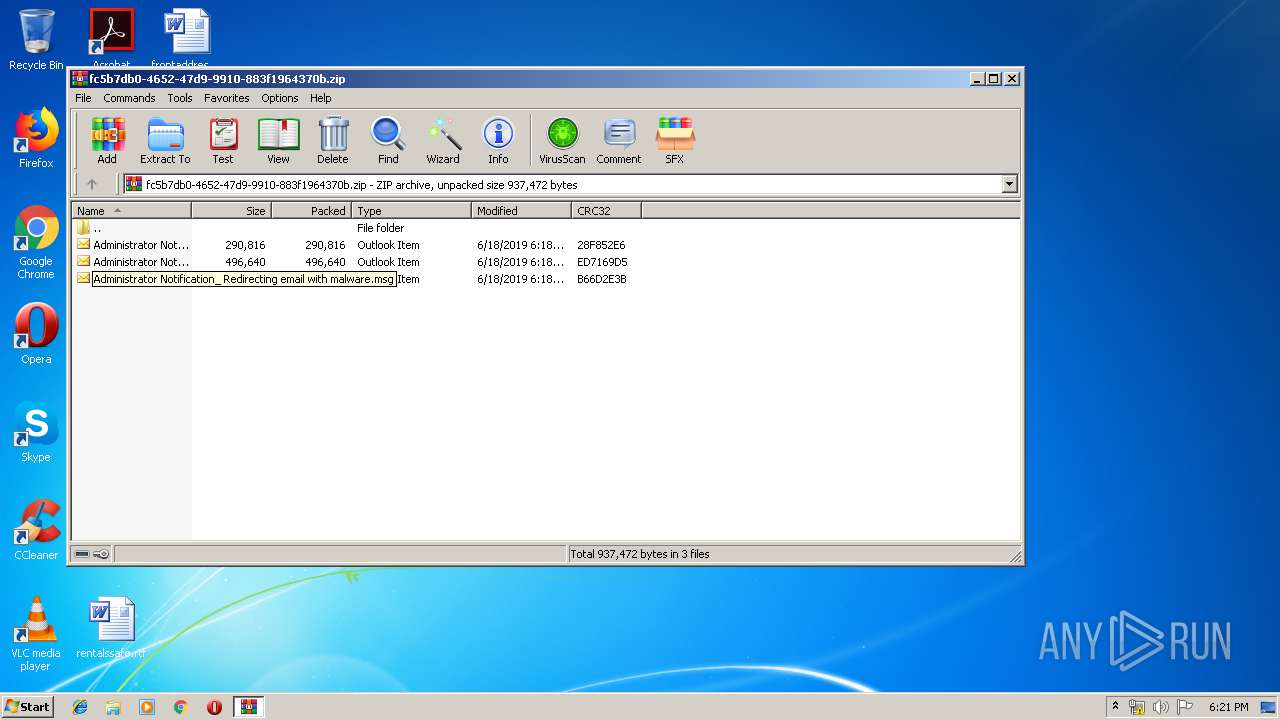
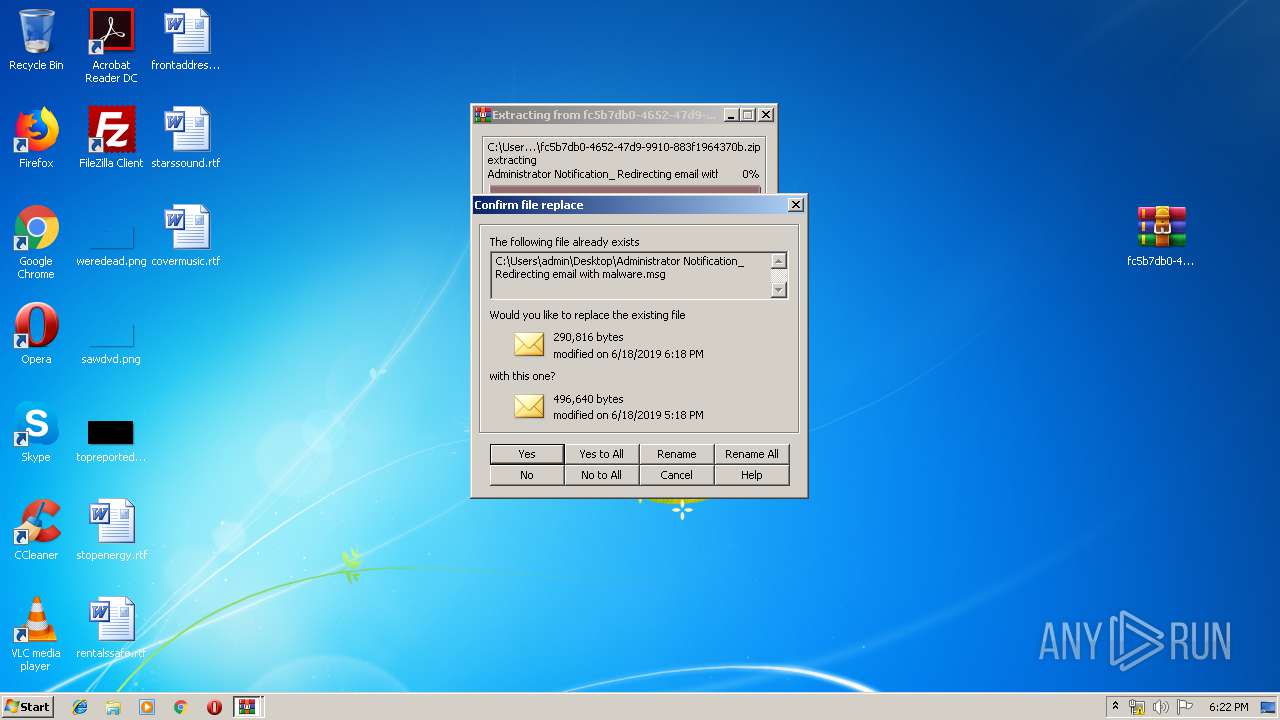
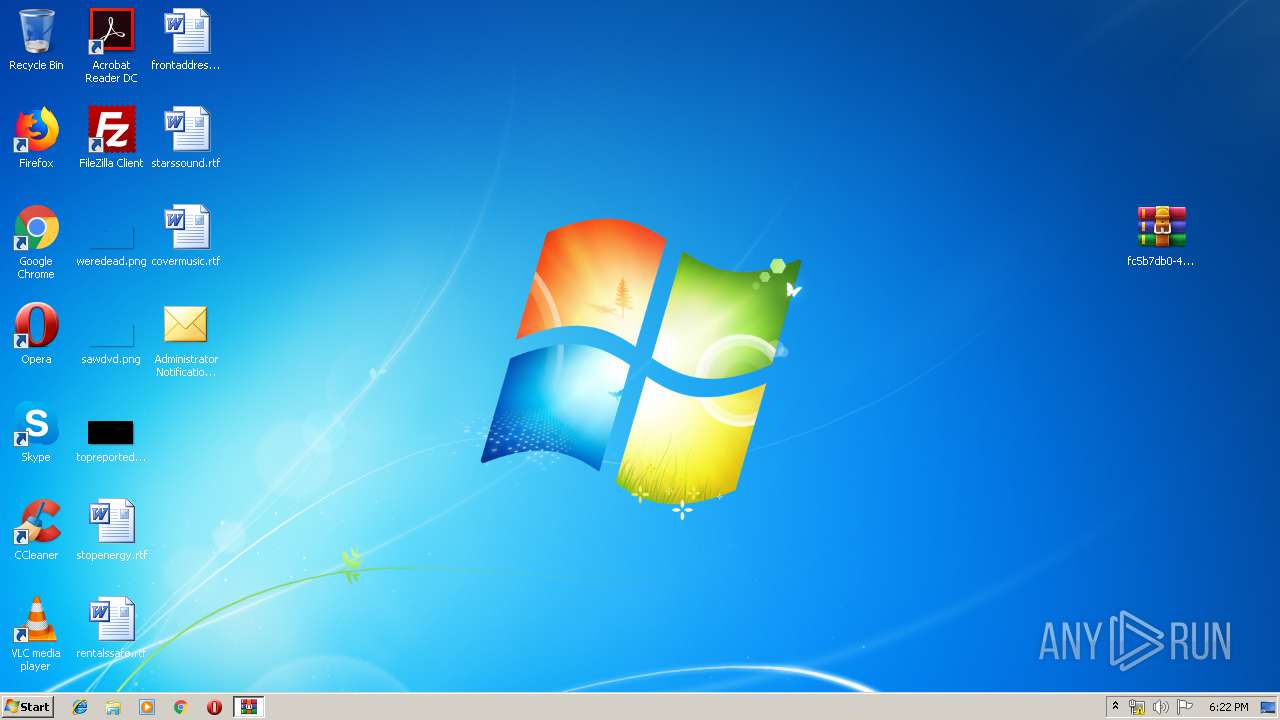
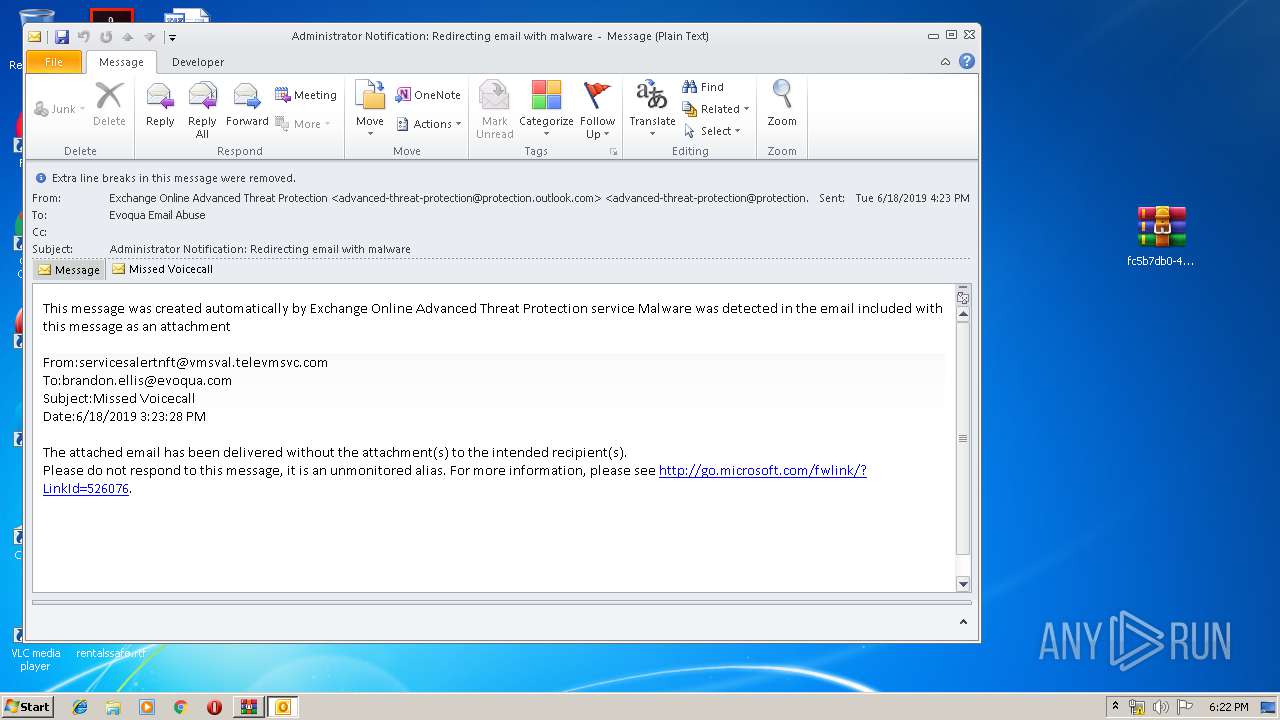
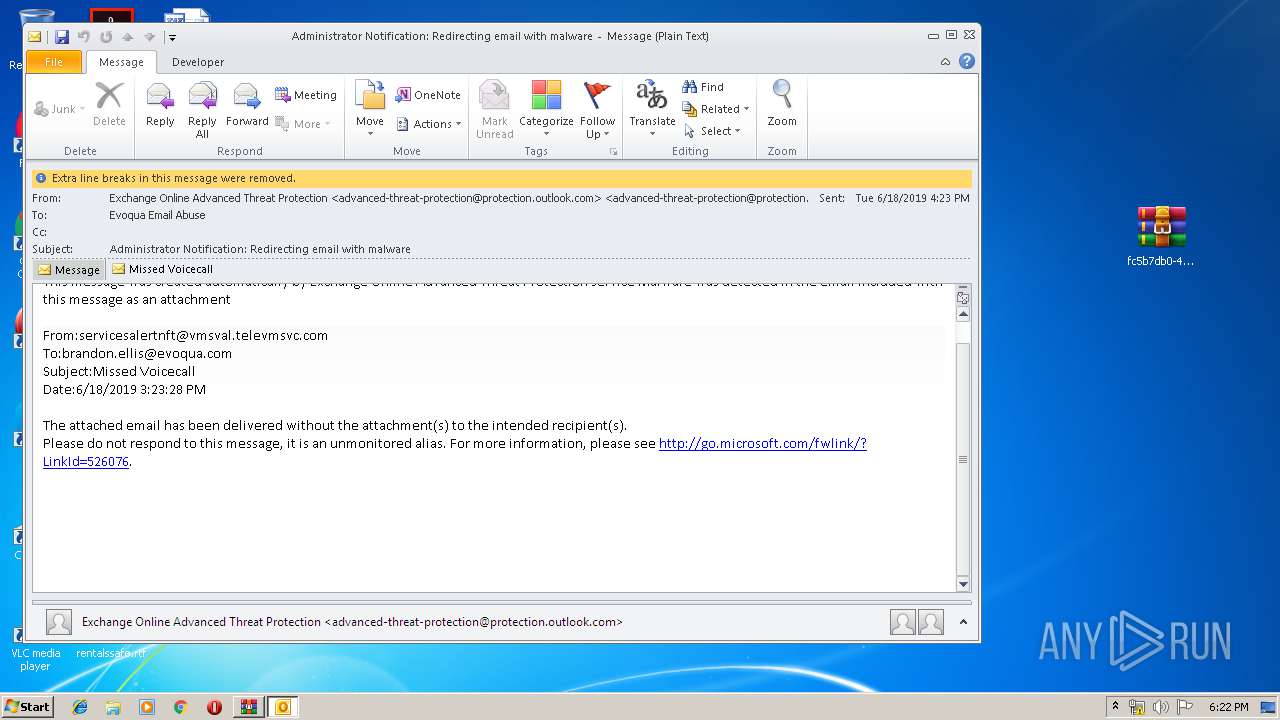
| ZipFileName: | Administrator Notification_ Redirecting email with malware.msg |
Total processes
50
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
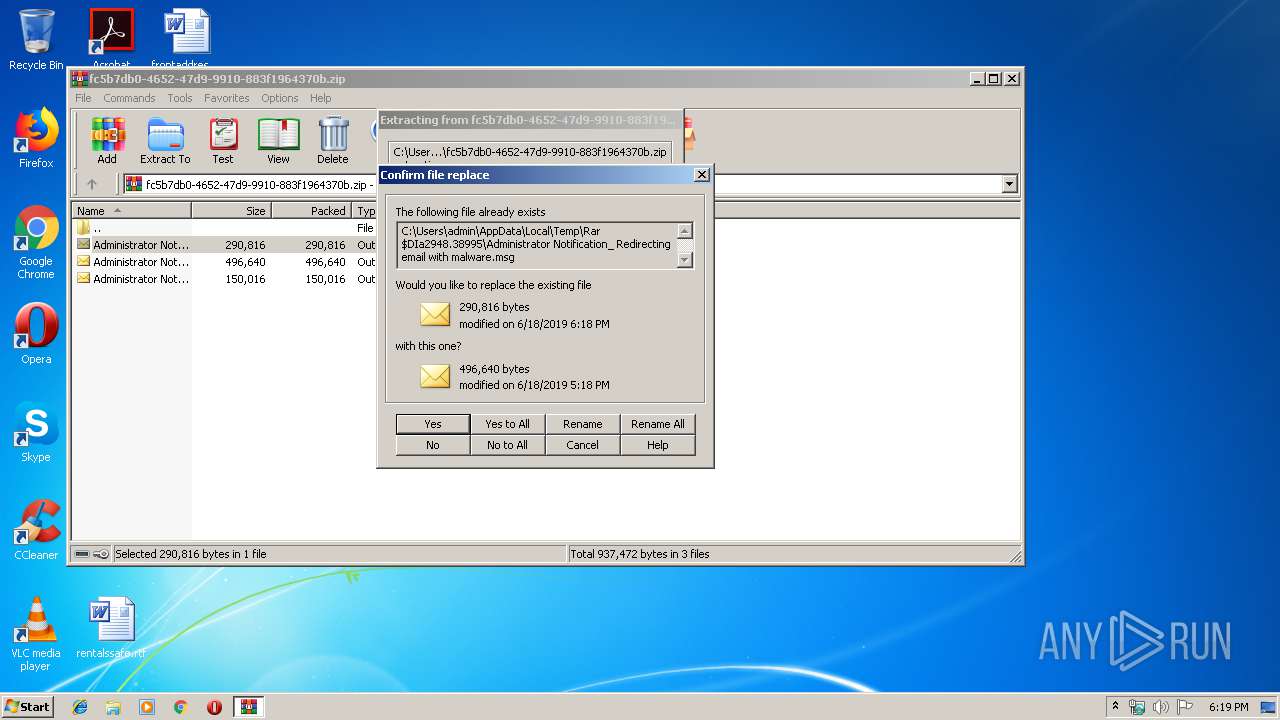
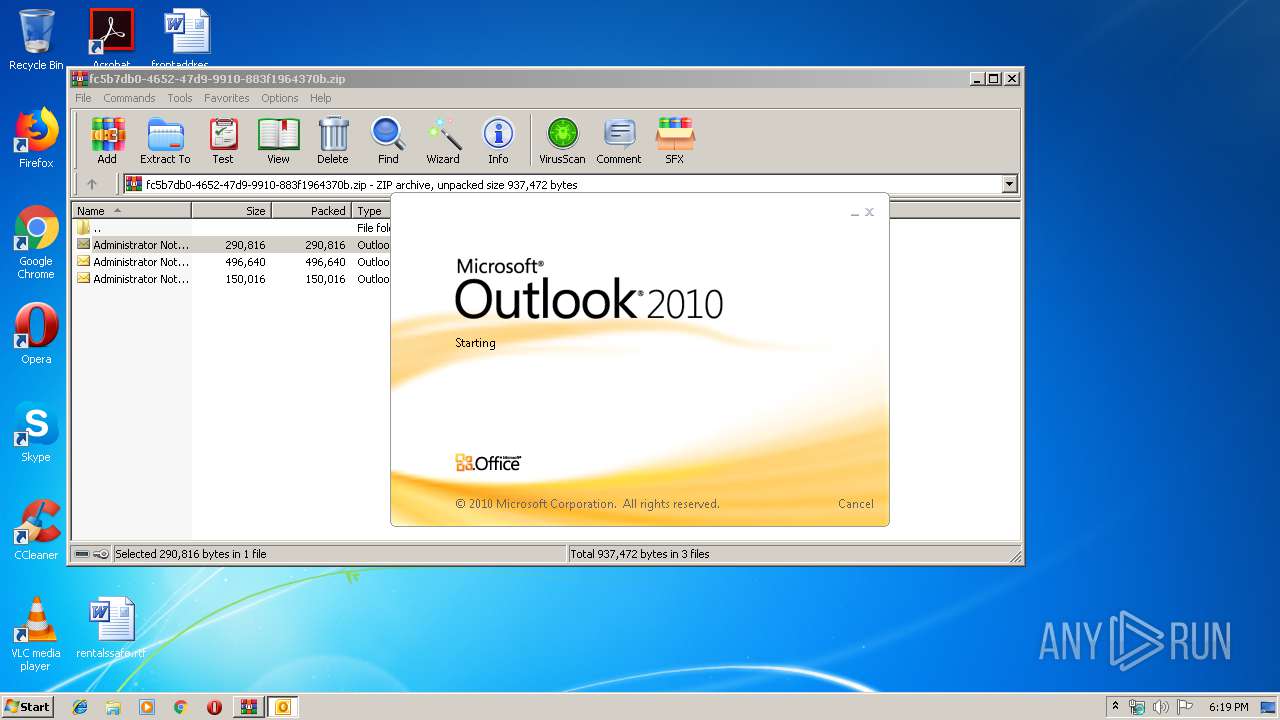
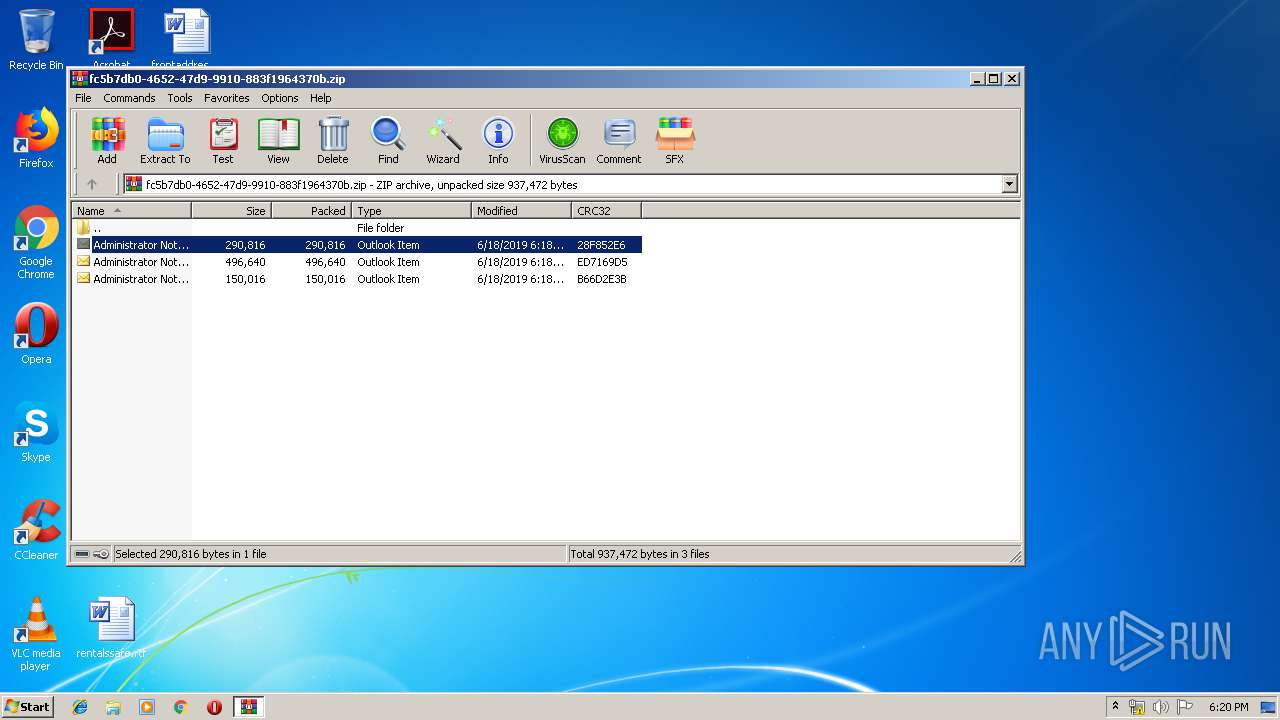
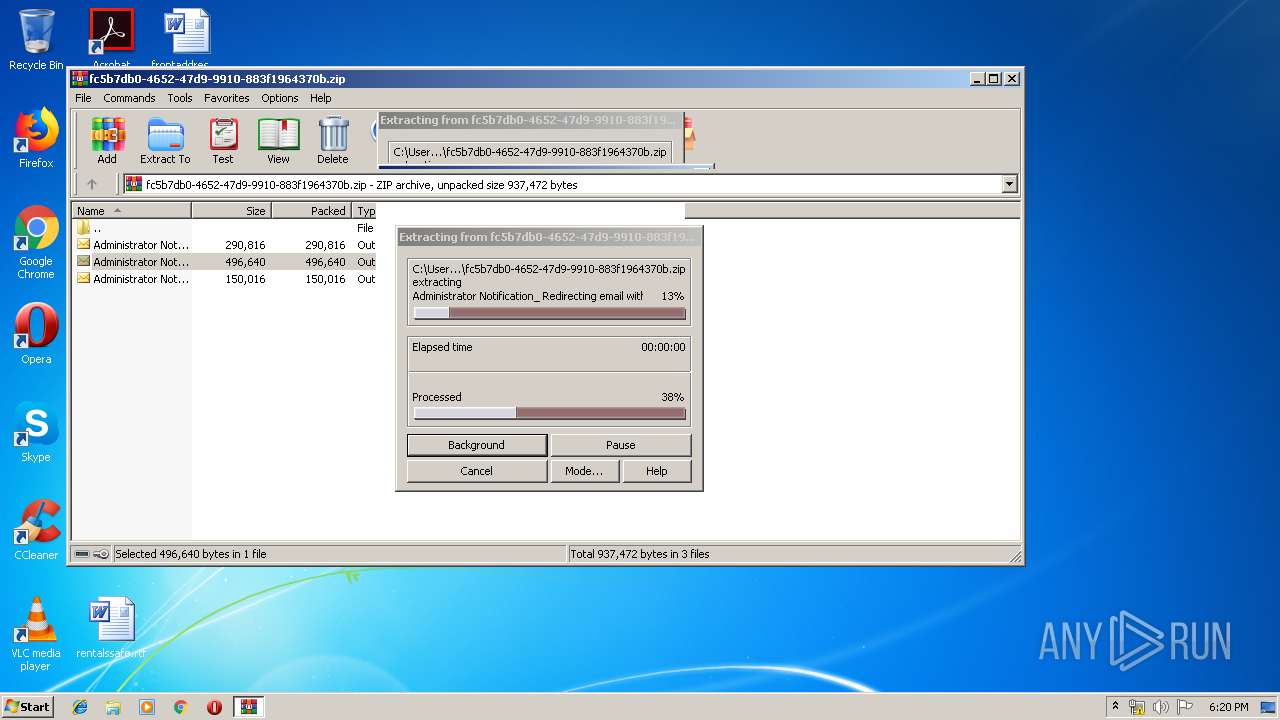
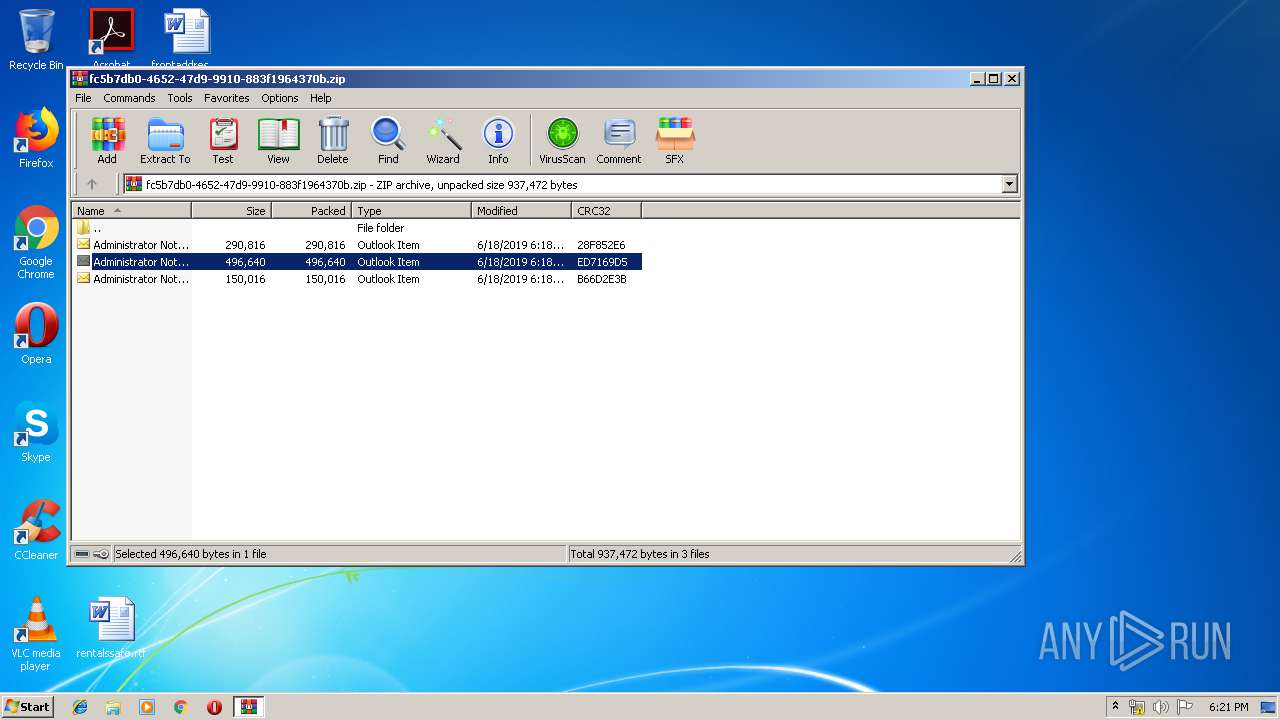
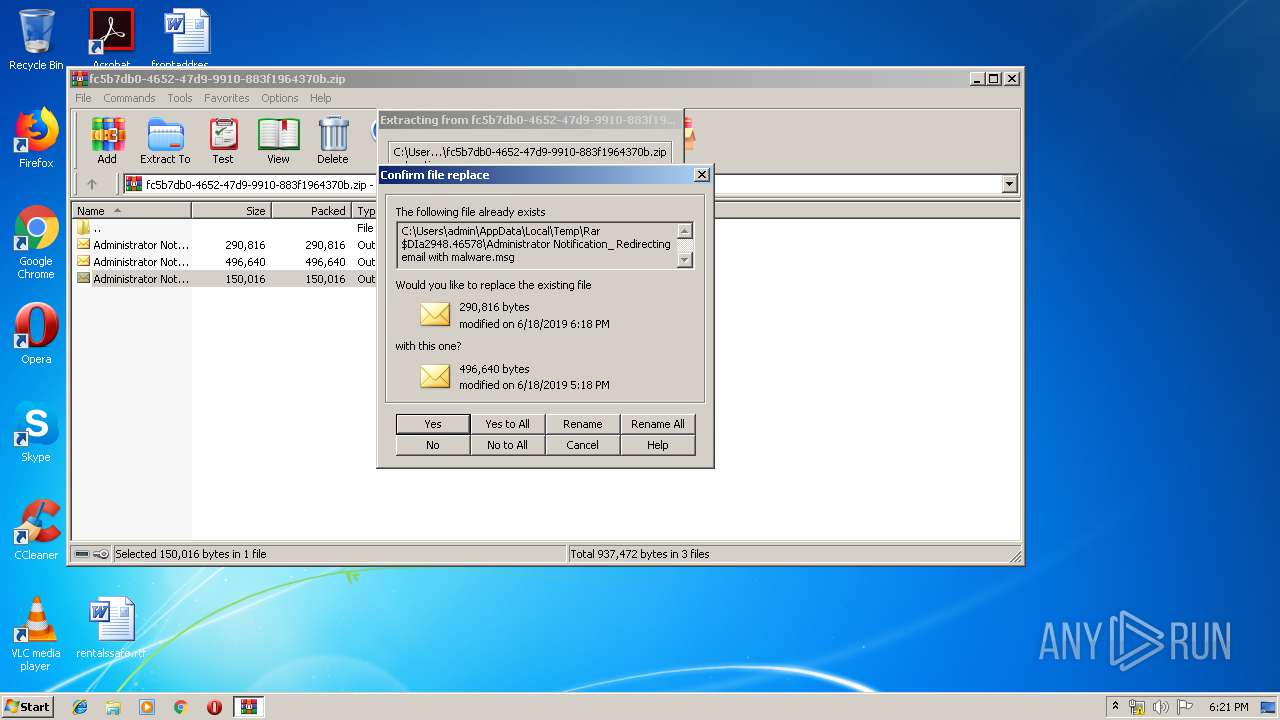
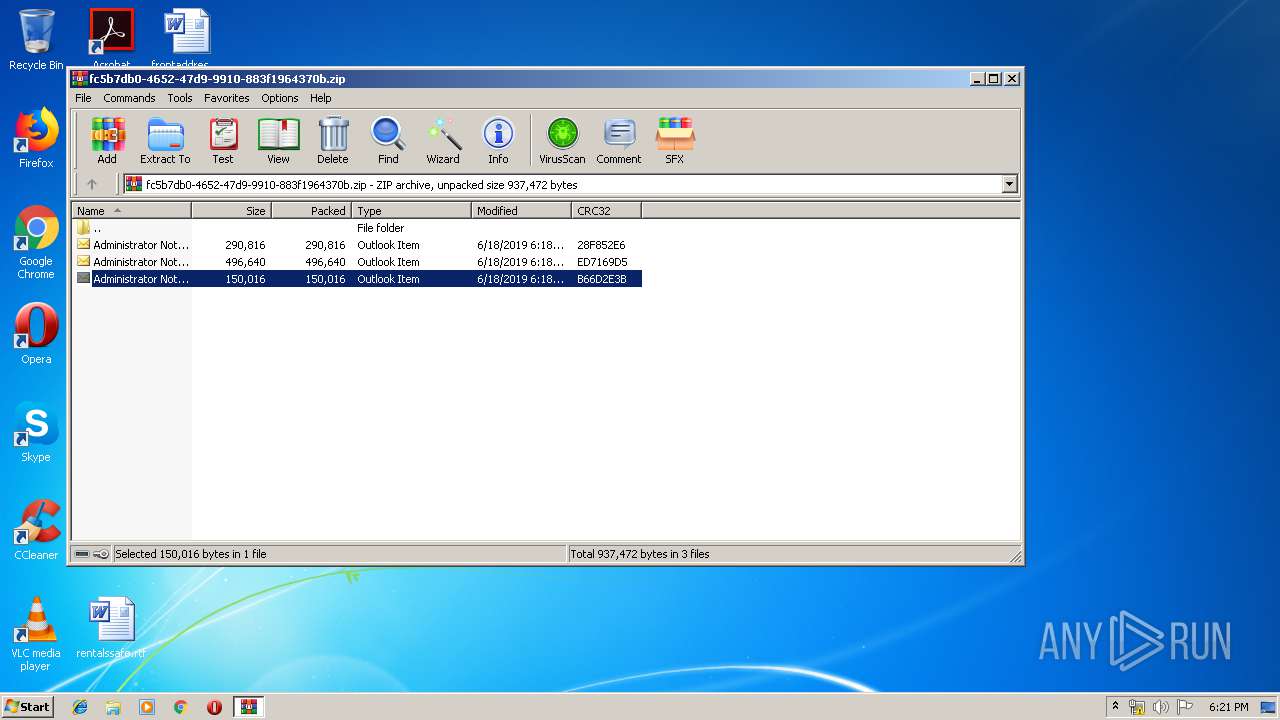
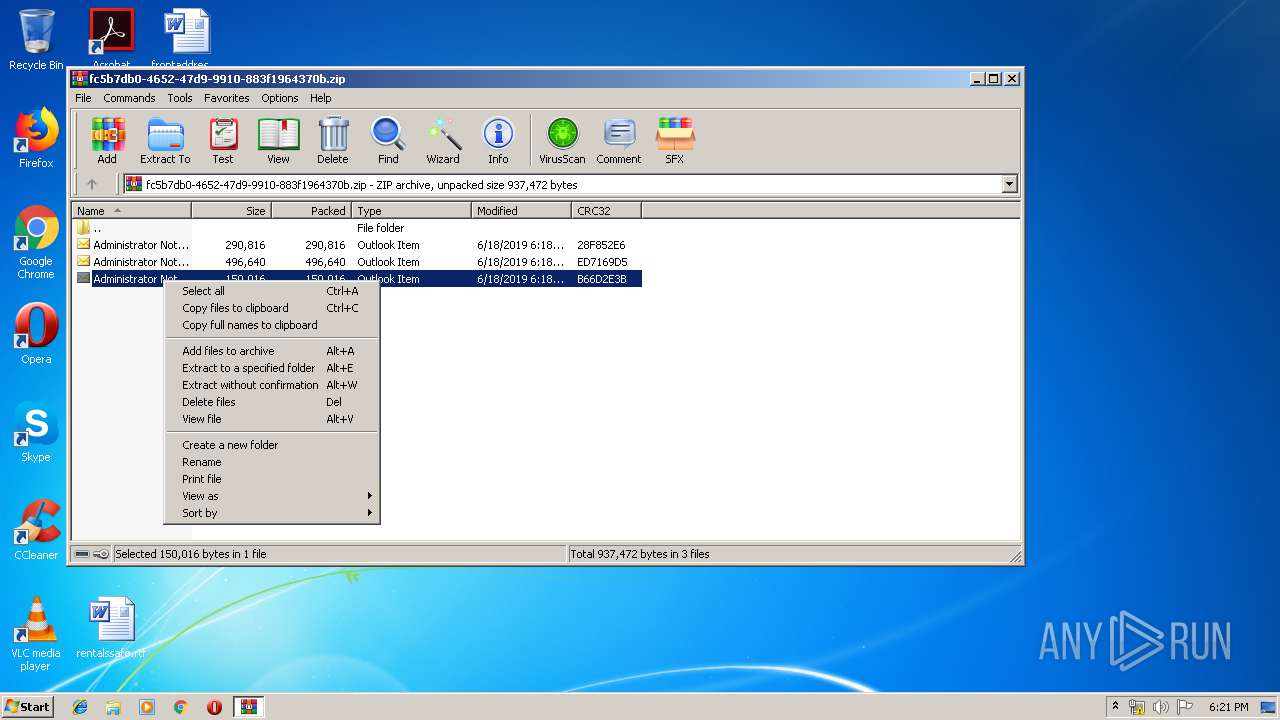
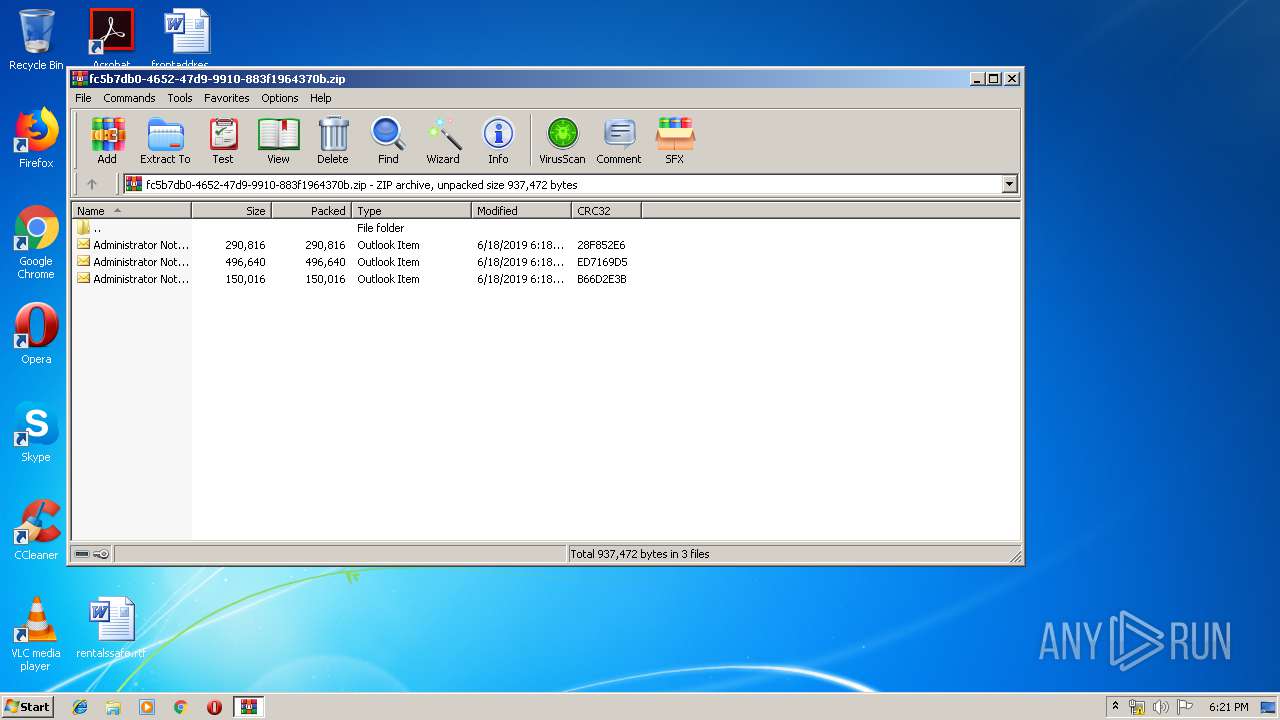
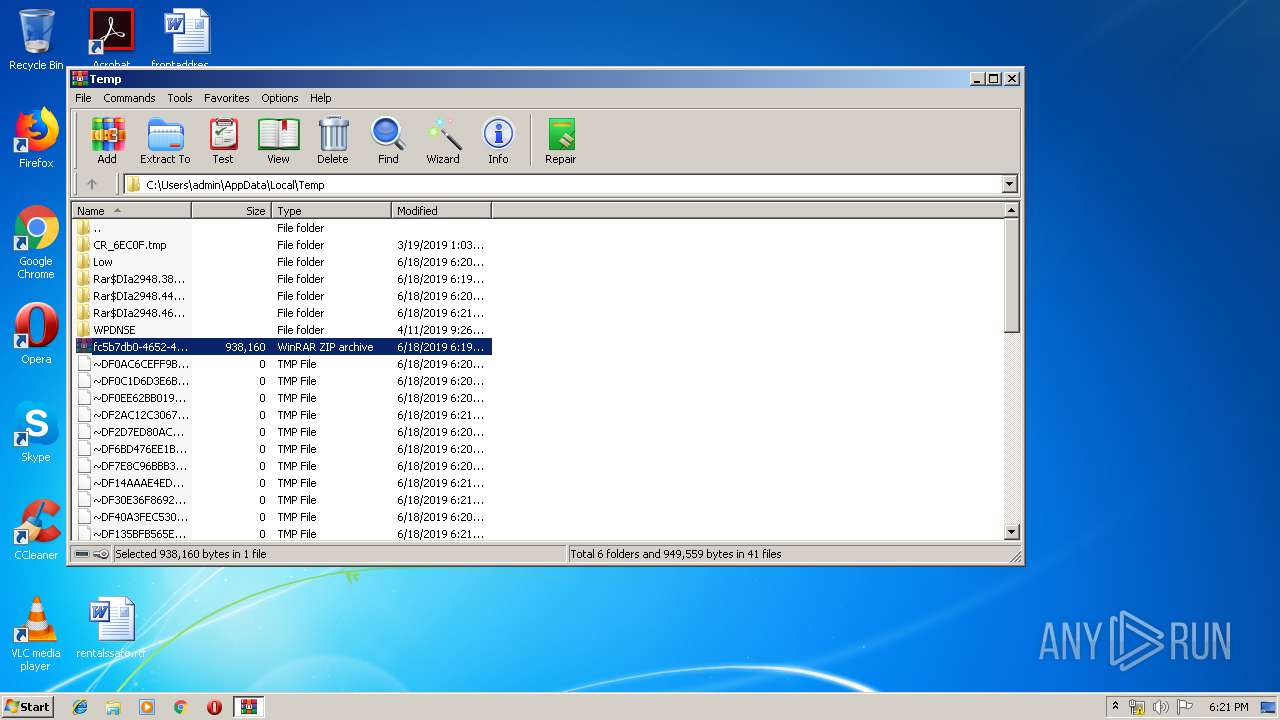
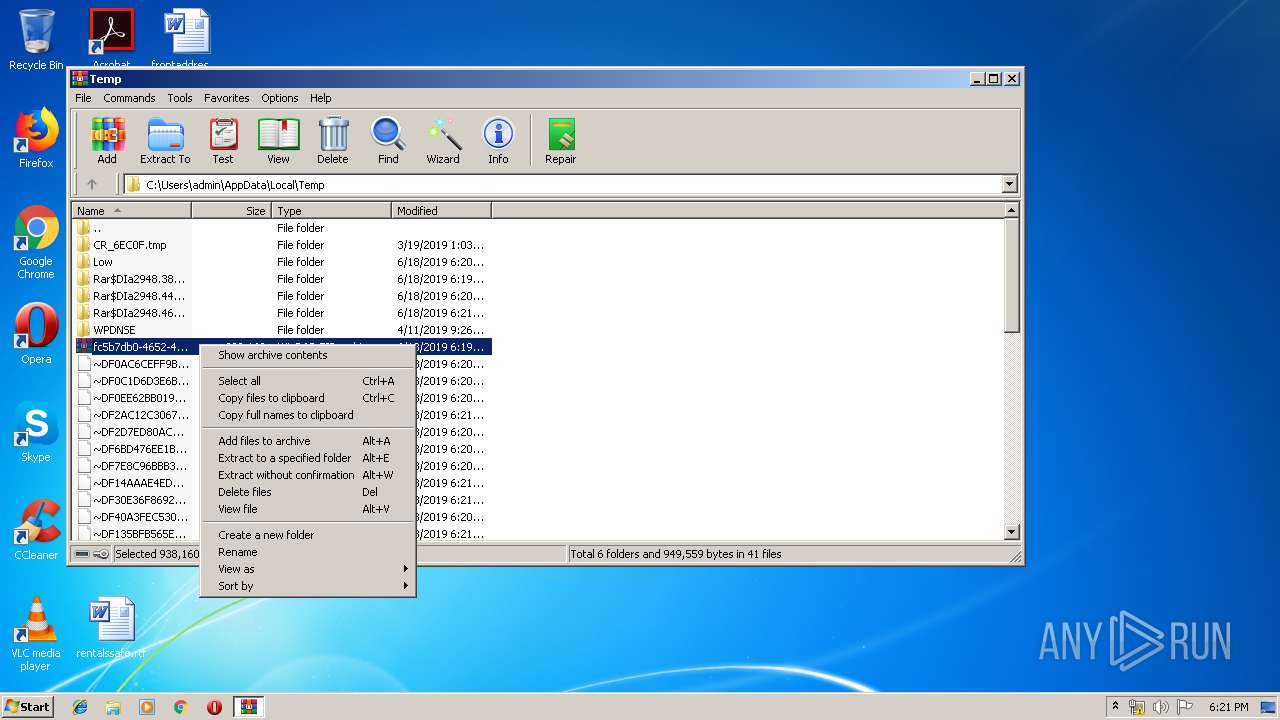
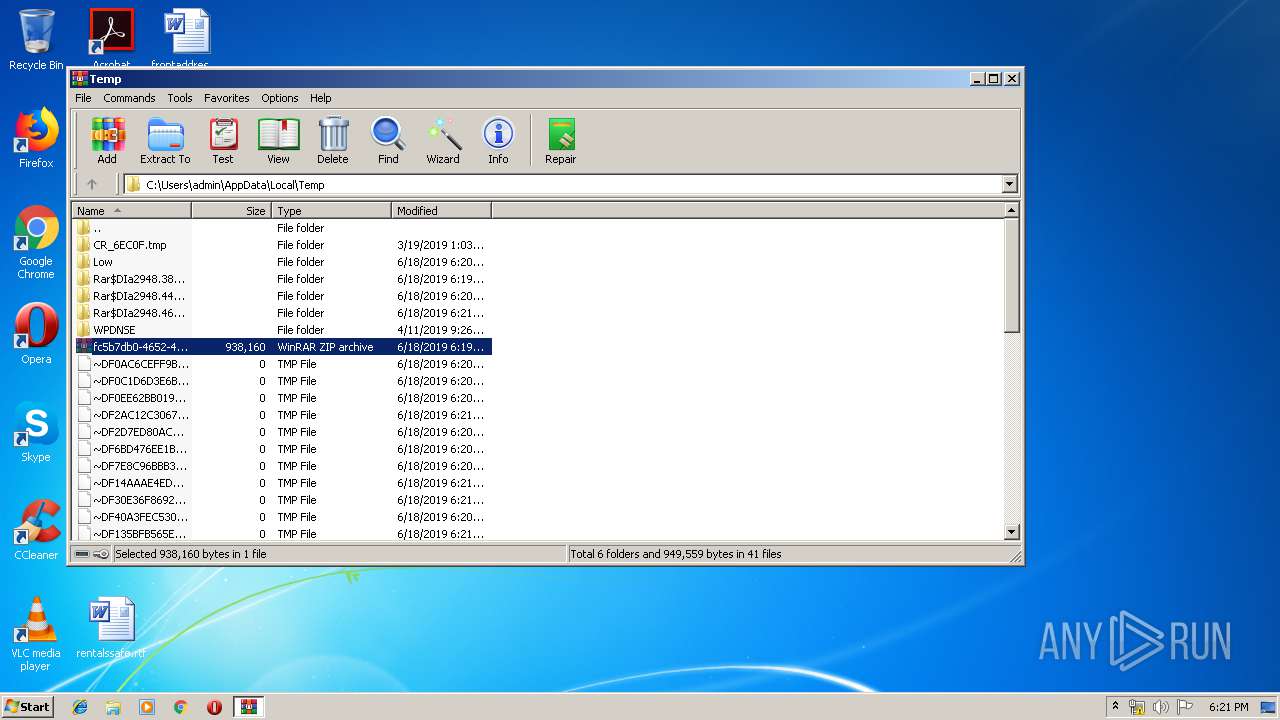
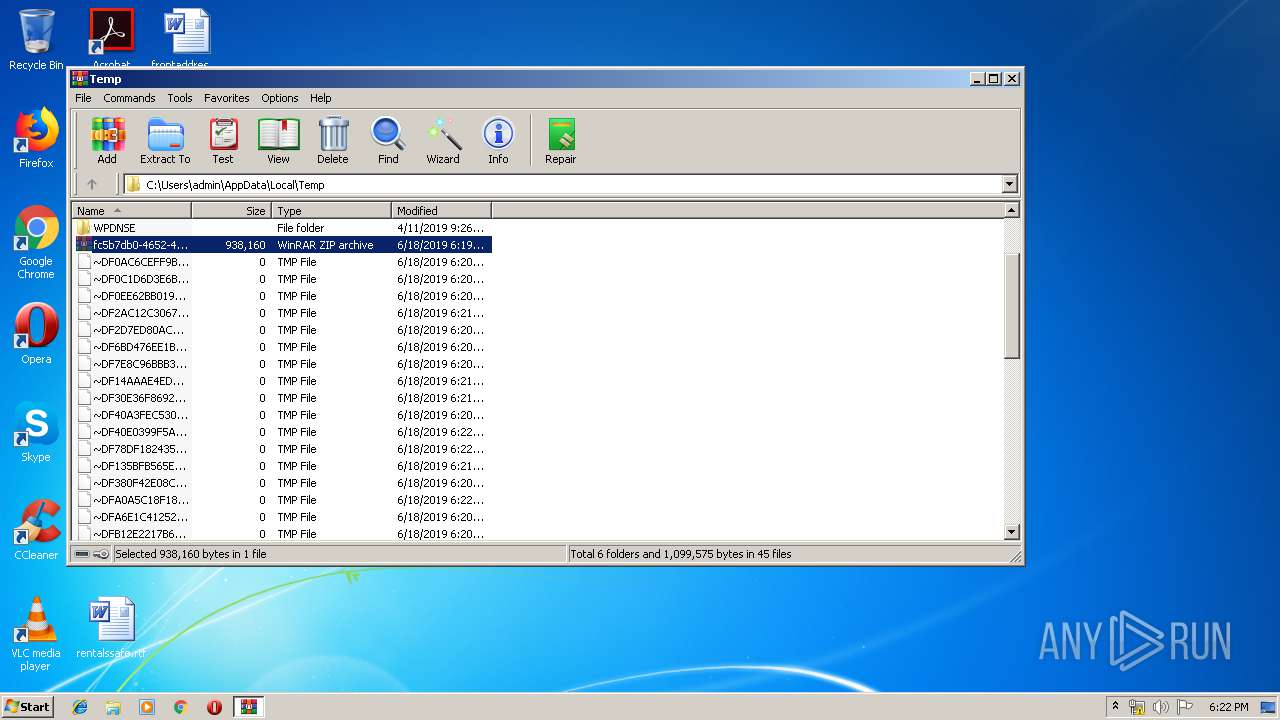
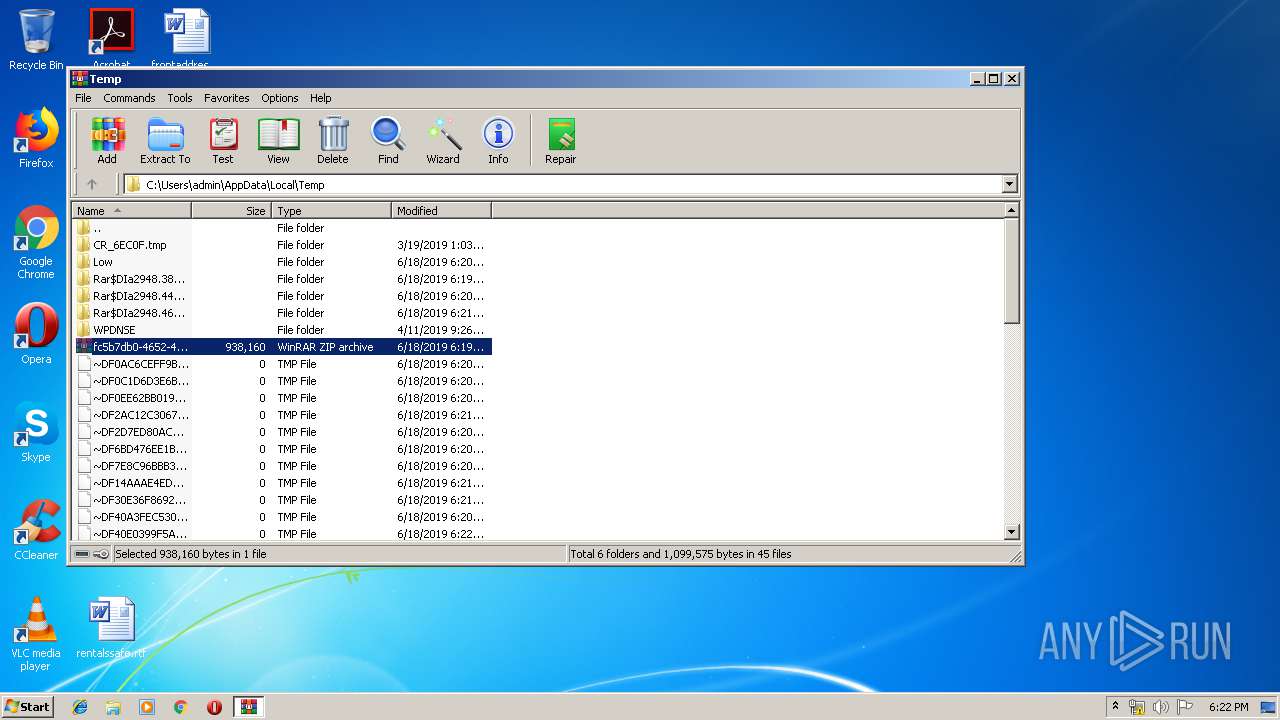
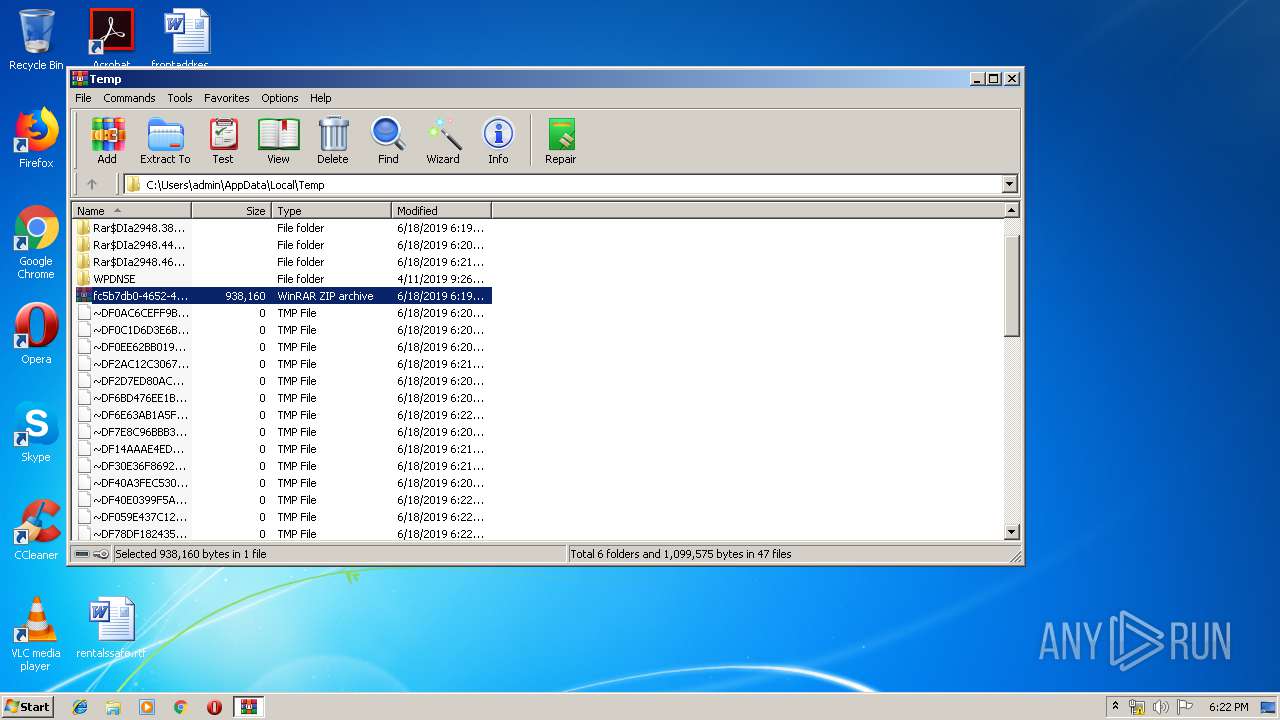
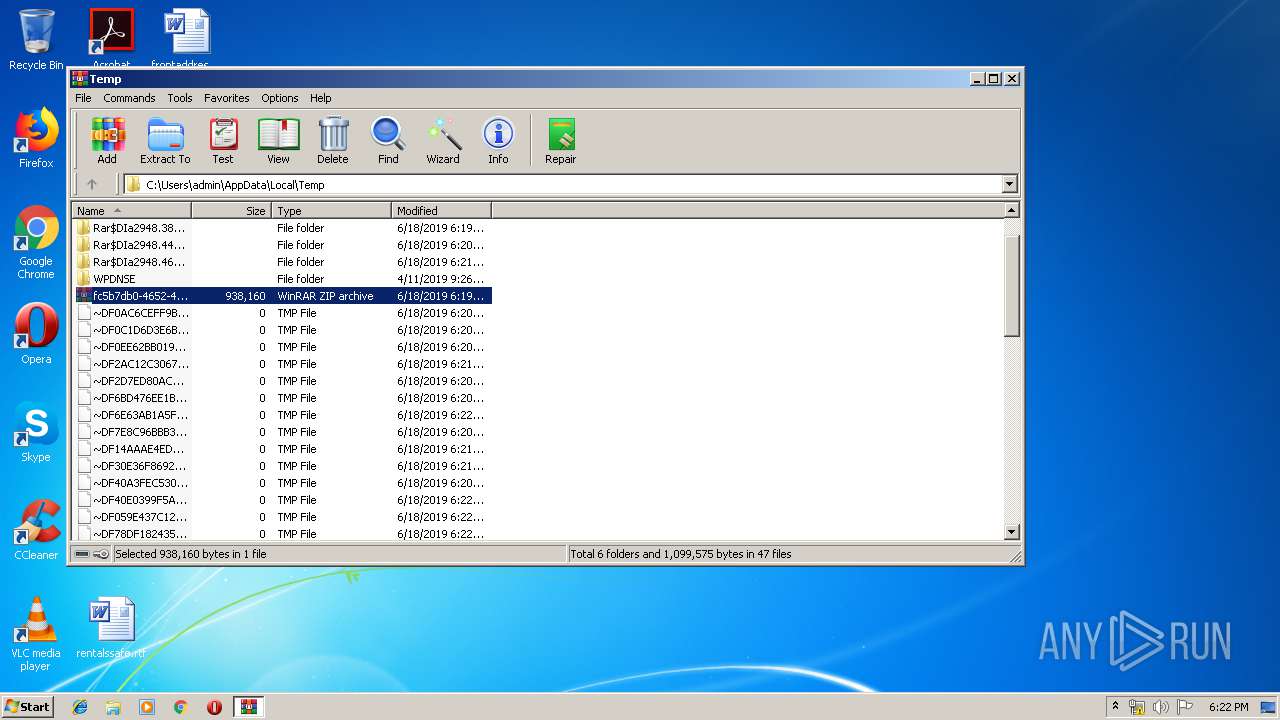
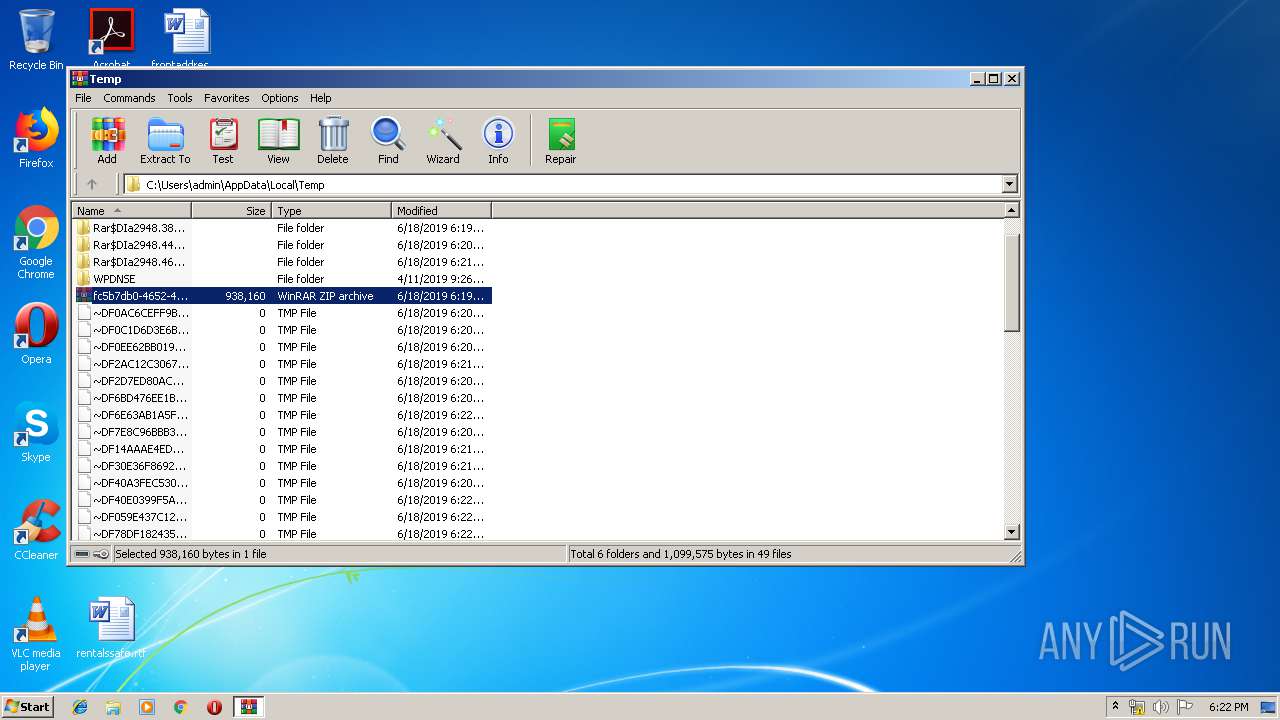
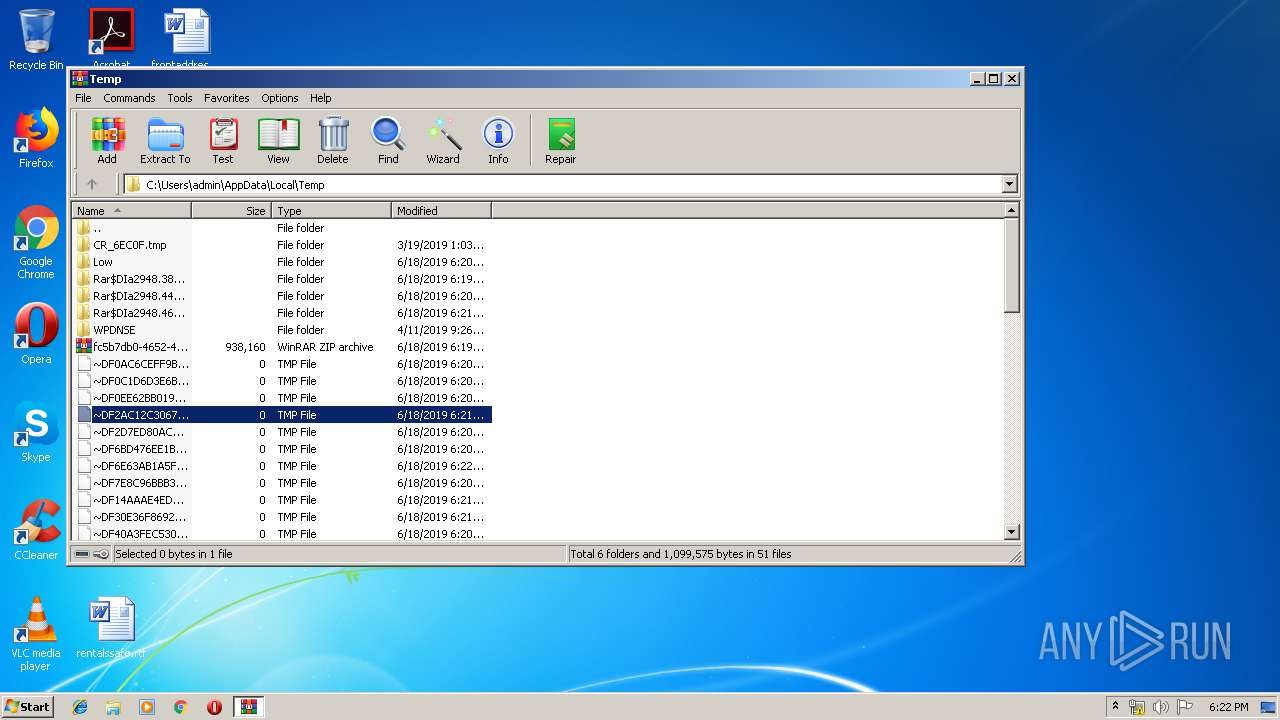
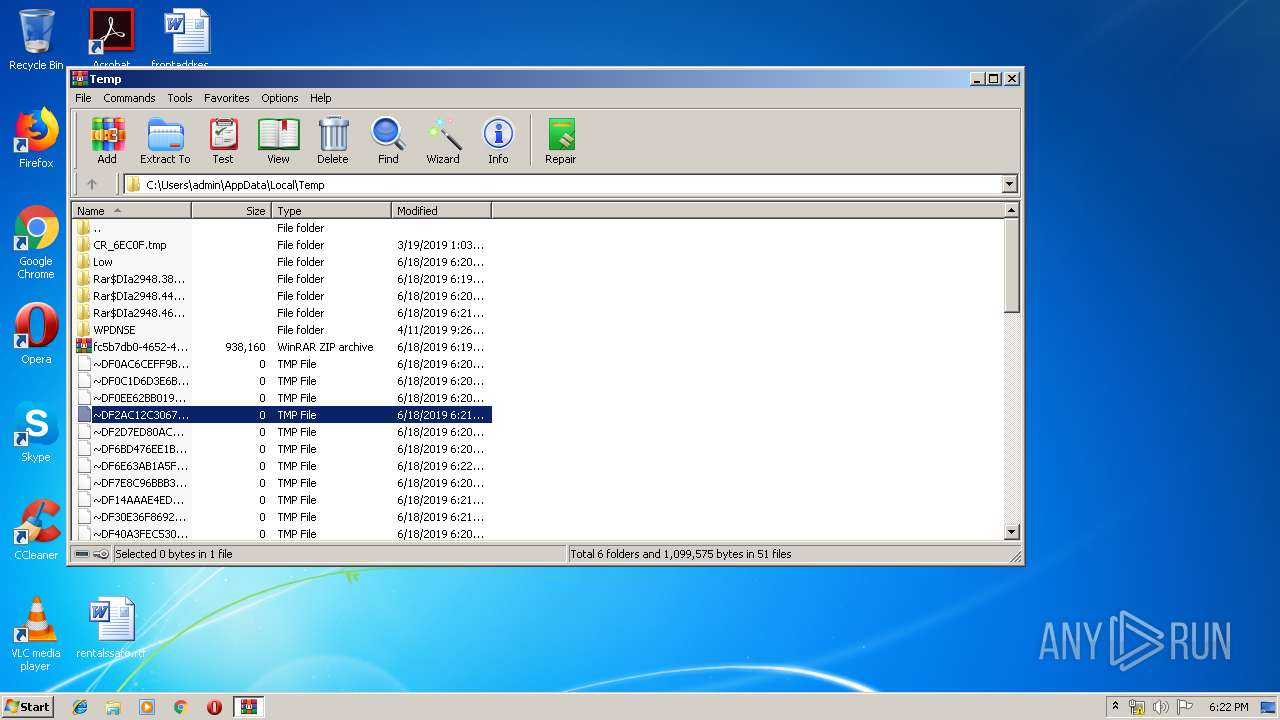
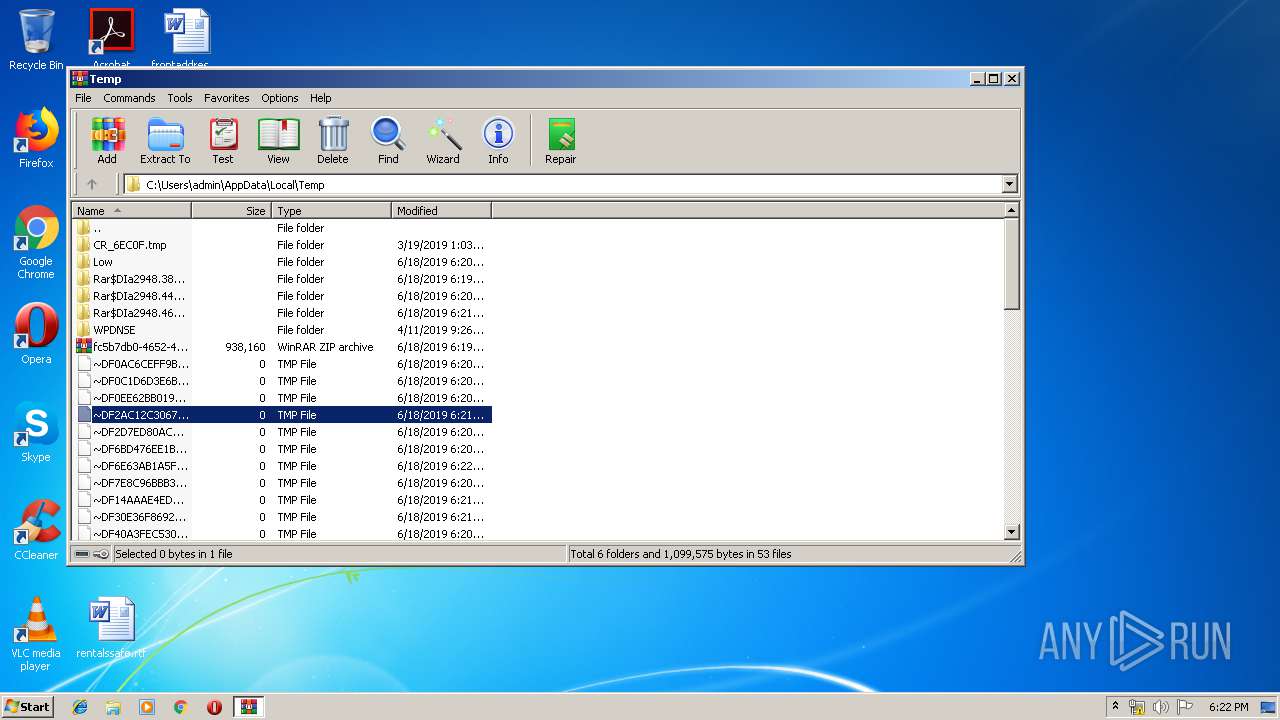
| 676 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\fc5b7db0-4652-47d9-9910-883f1964370b.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
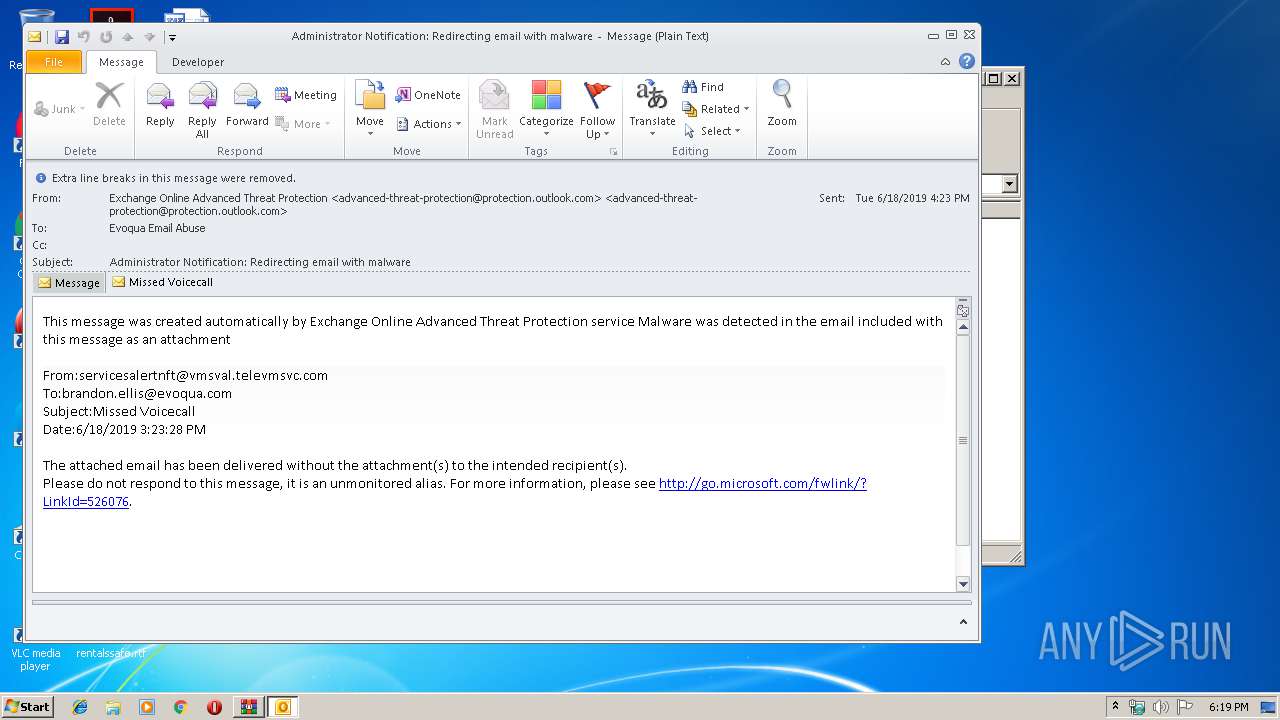
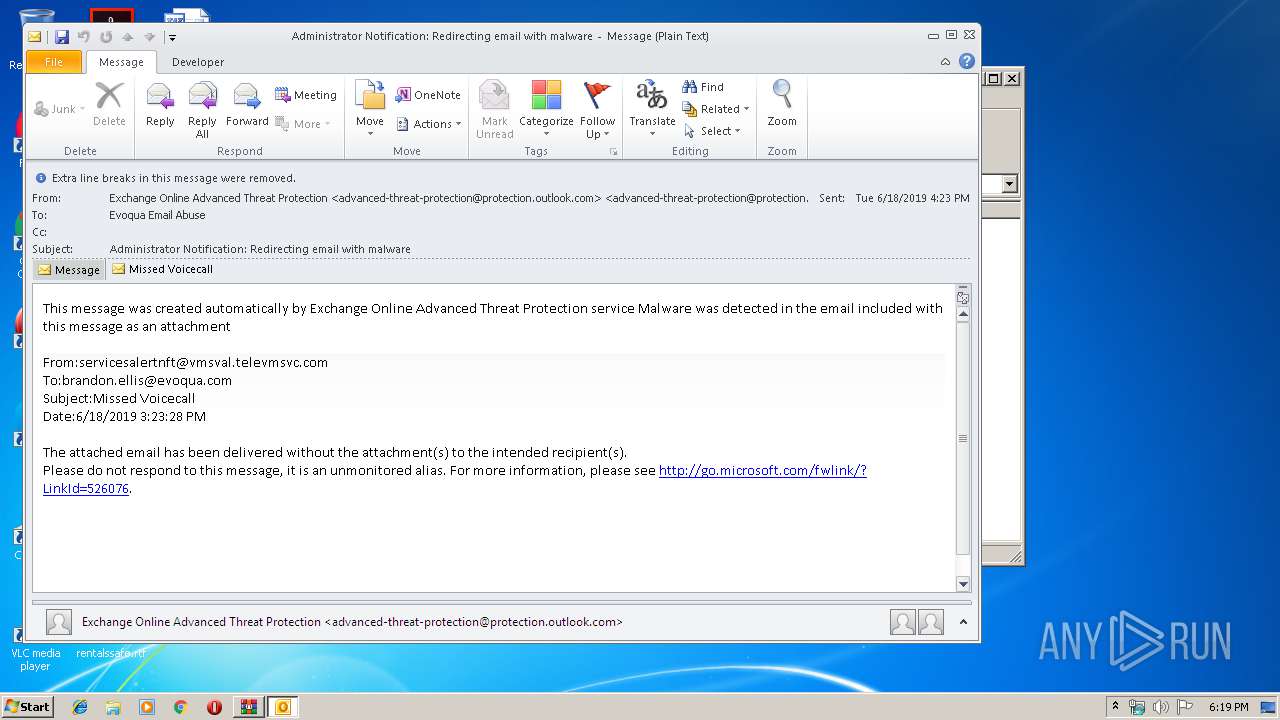
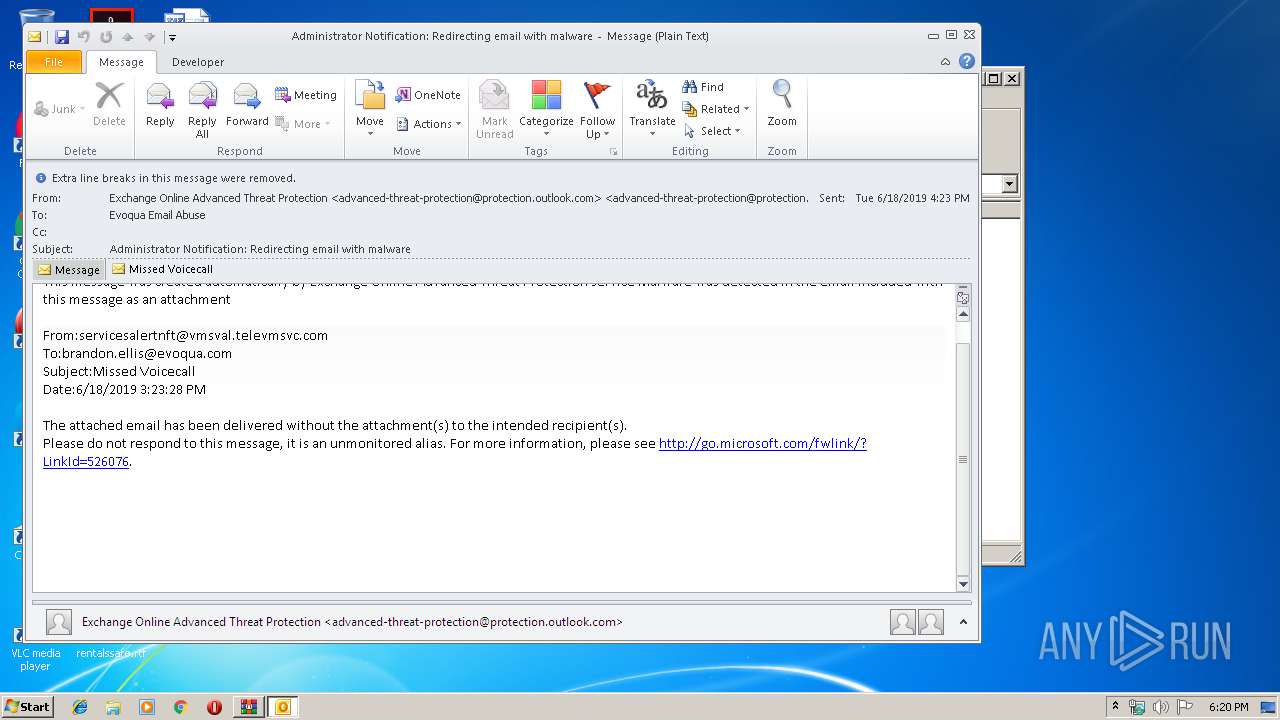
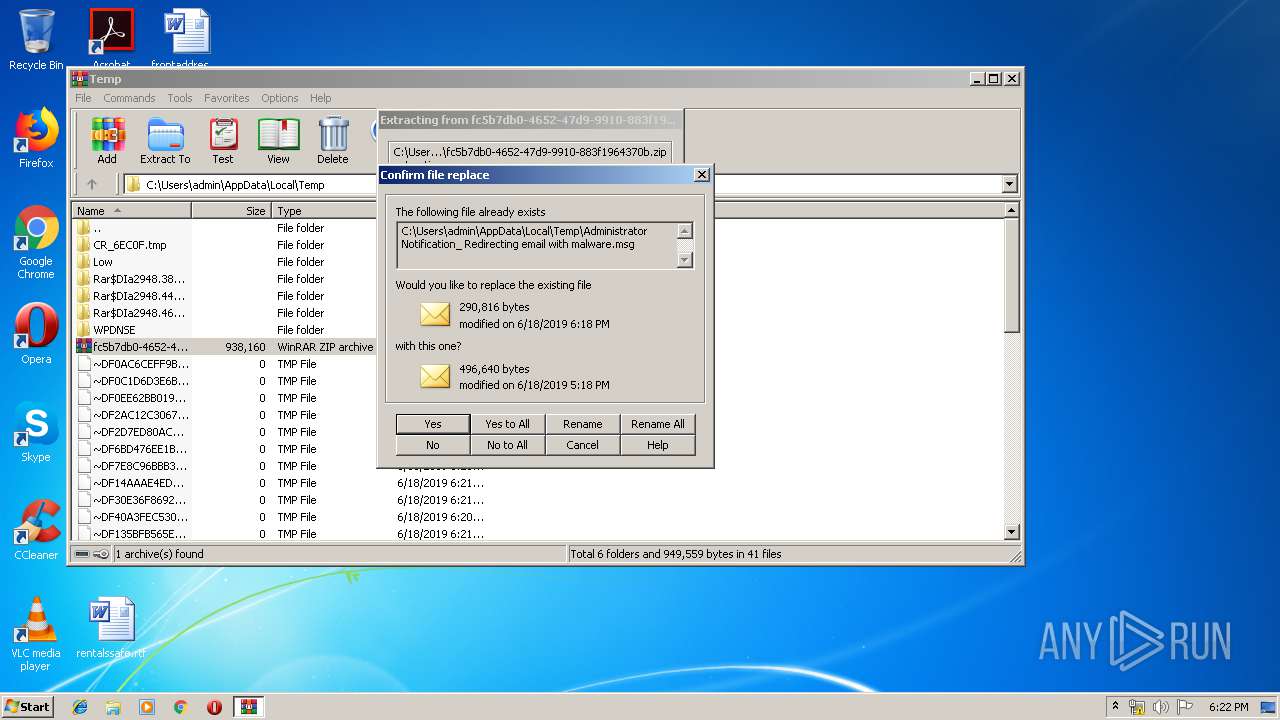
| 2432 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Rar$DIa2948.46578\Administrator Notification_ Redirecting email with malware.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2764 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\Desktop\Administrator Notification_ Redirecting email with malware.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2800 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3972 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
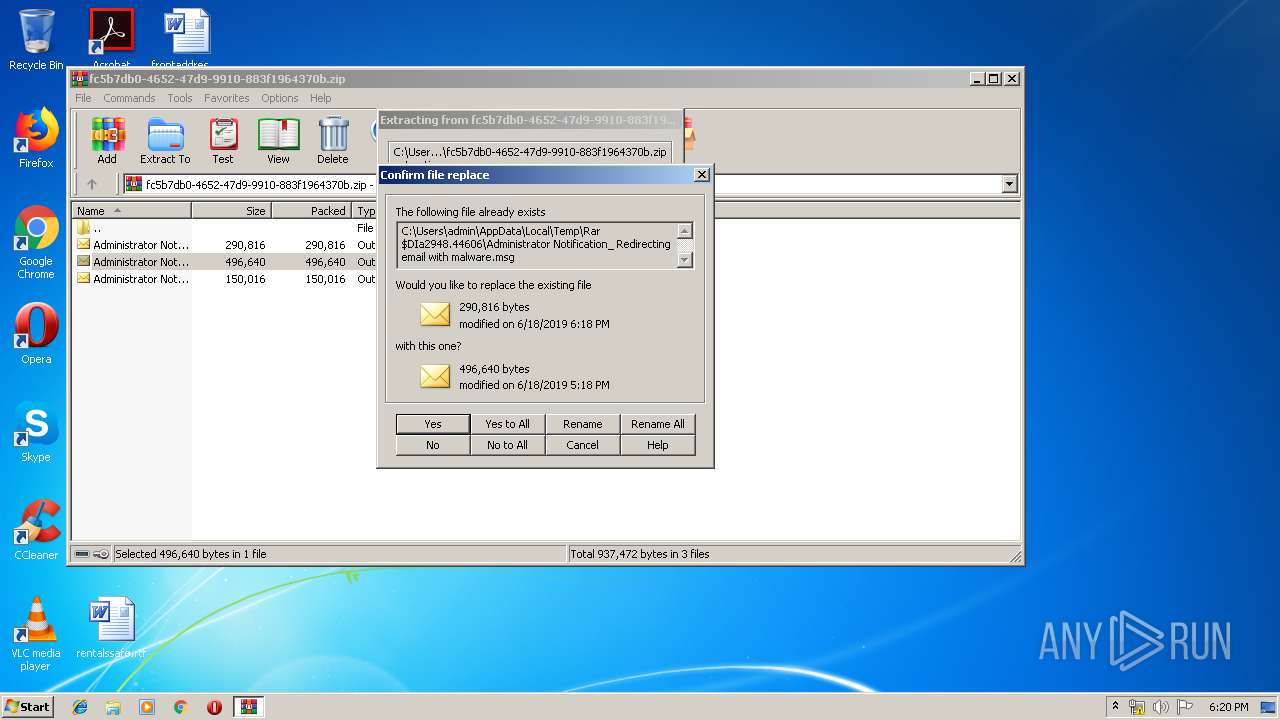
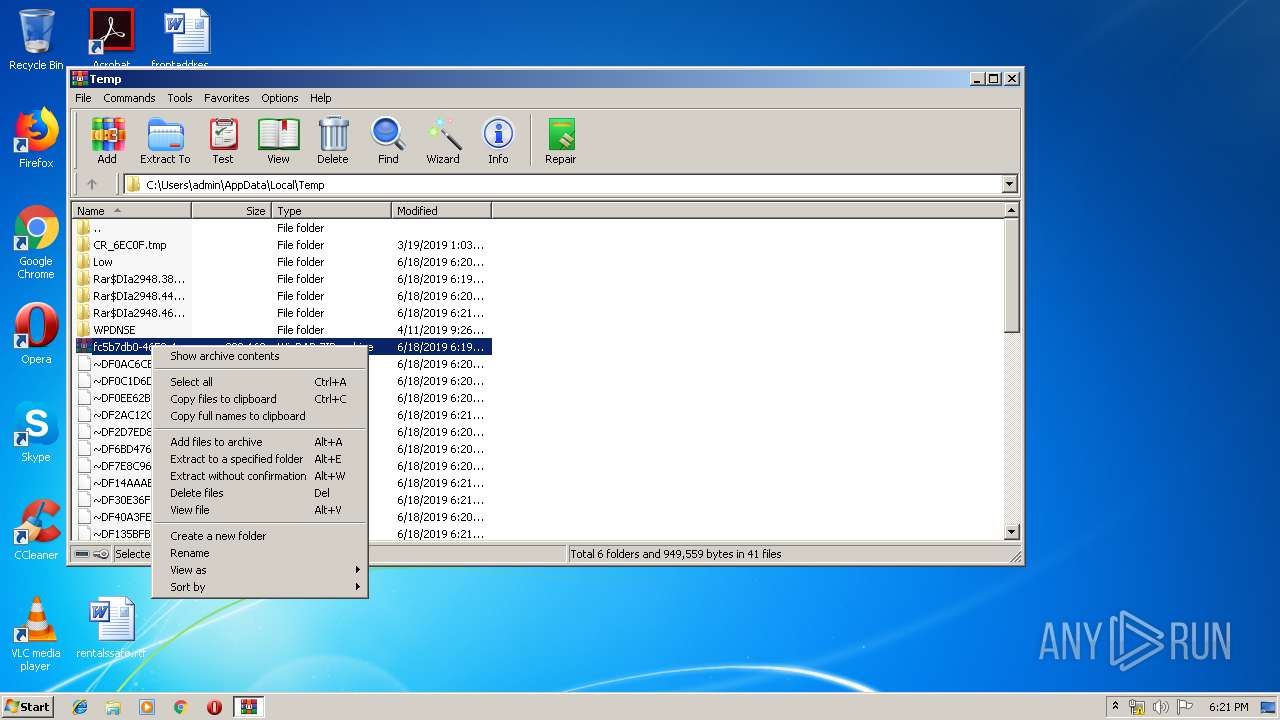
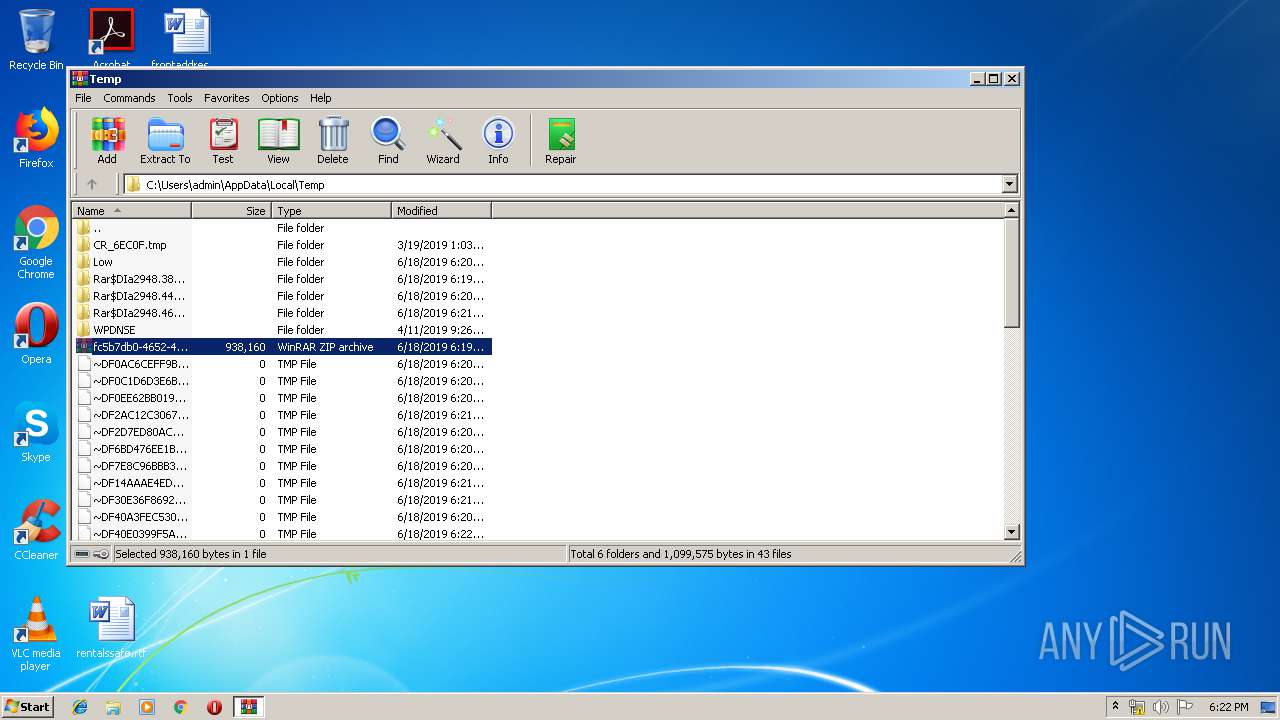
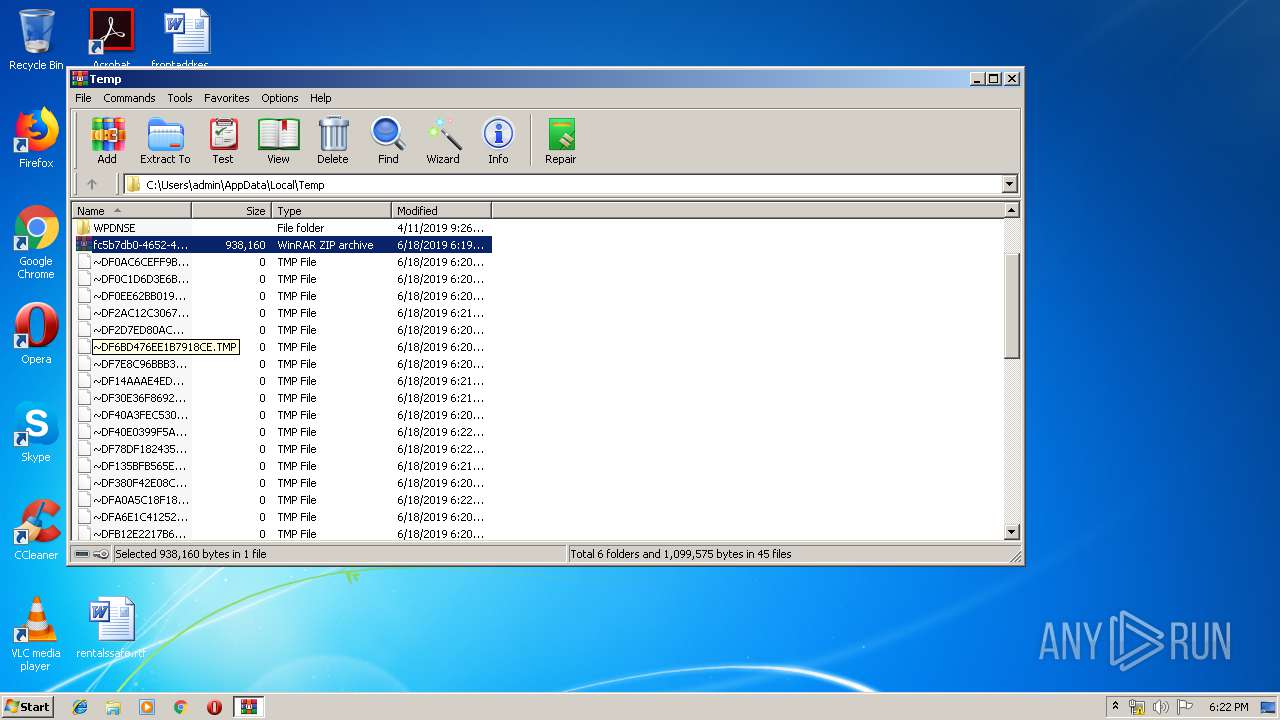
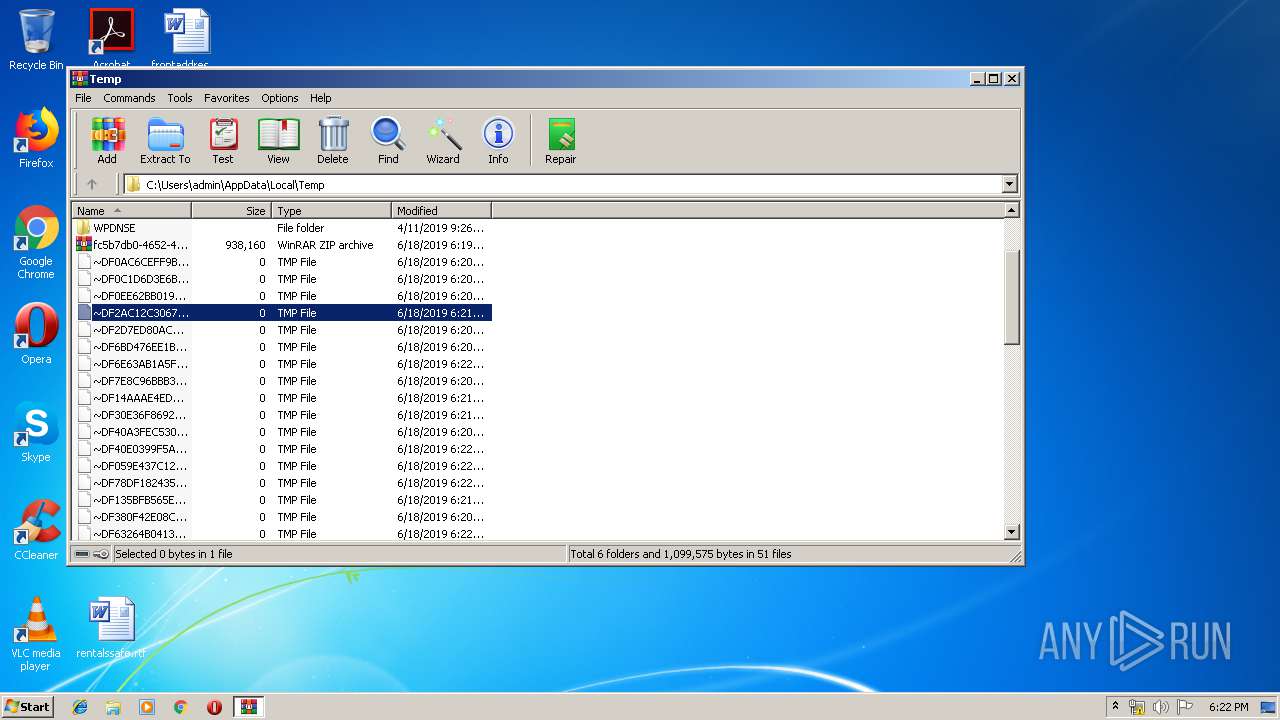
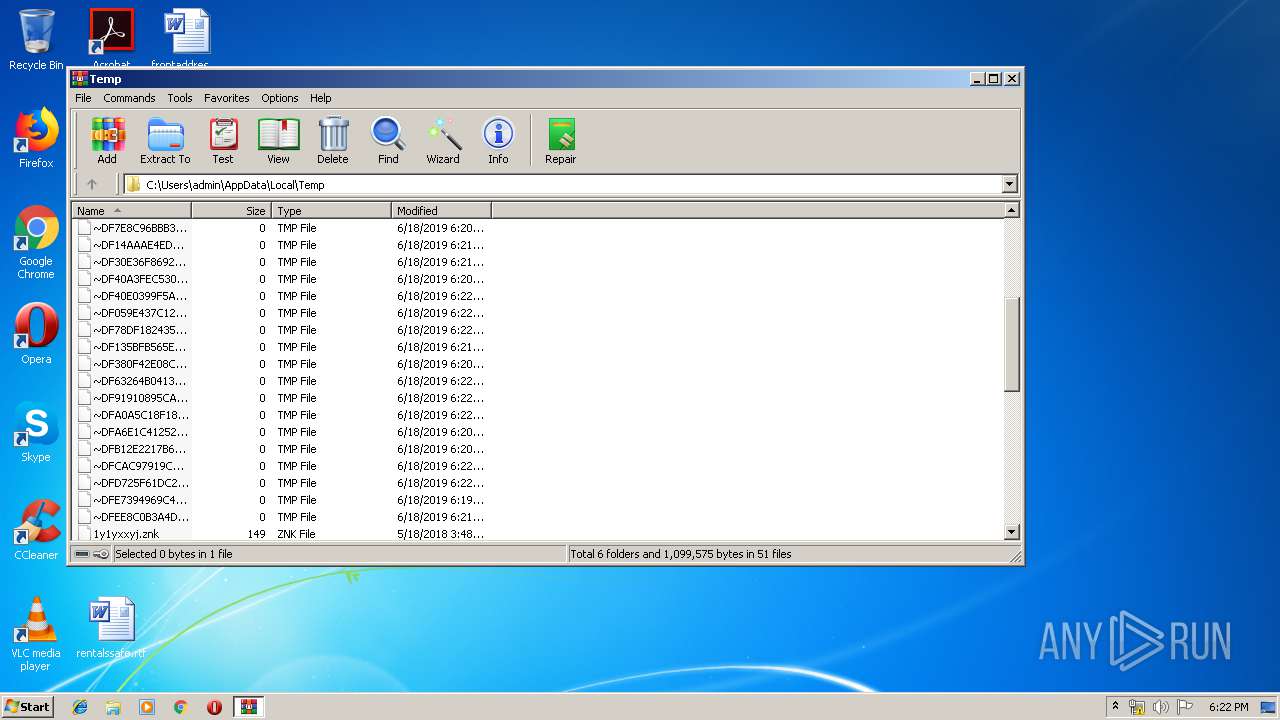
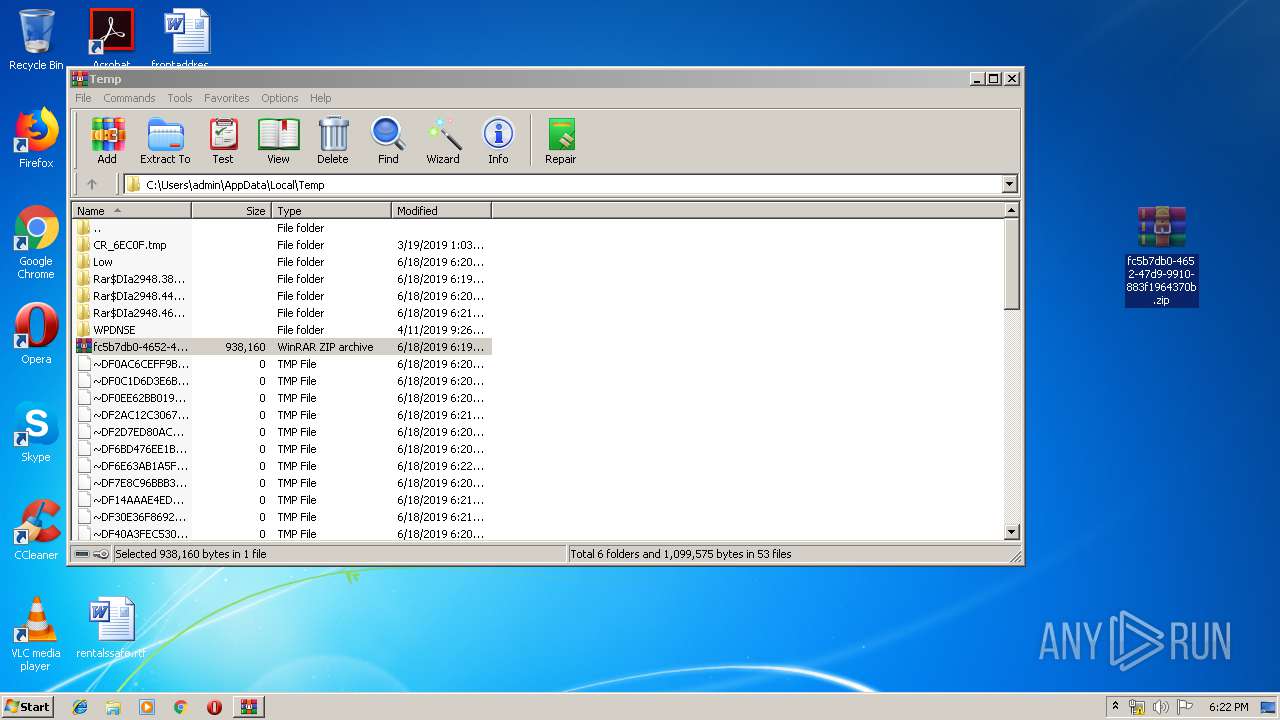
| 2948 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\fc5b7db0-4652-47d9-9910-883f1964370b.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Rar$DIa2948.44606\Administrator Notification_ Redirecting email with malware.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3188 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3392 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Rar$DIa2948.38995\Administrator Notification_ Redirecting email with malware.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
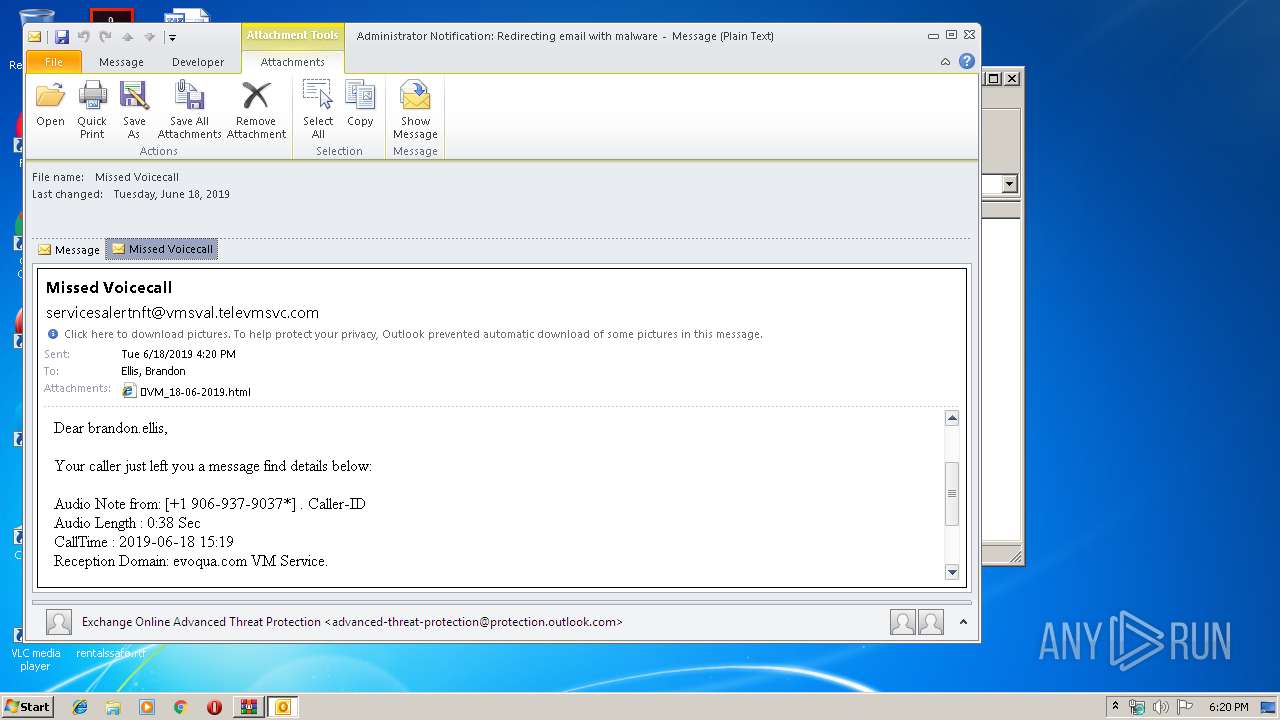
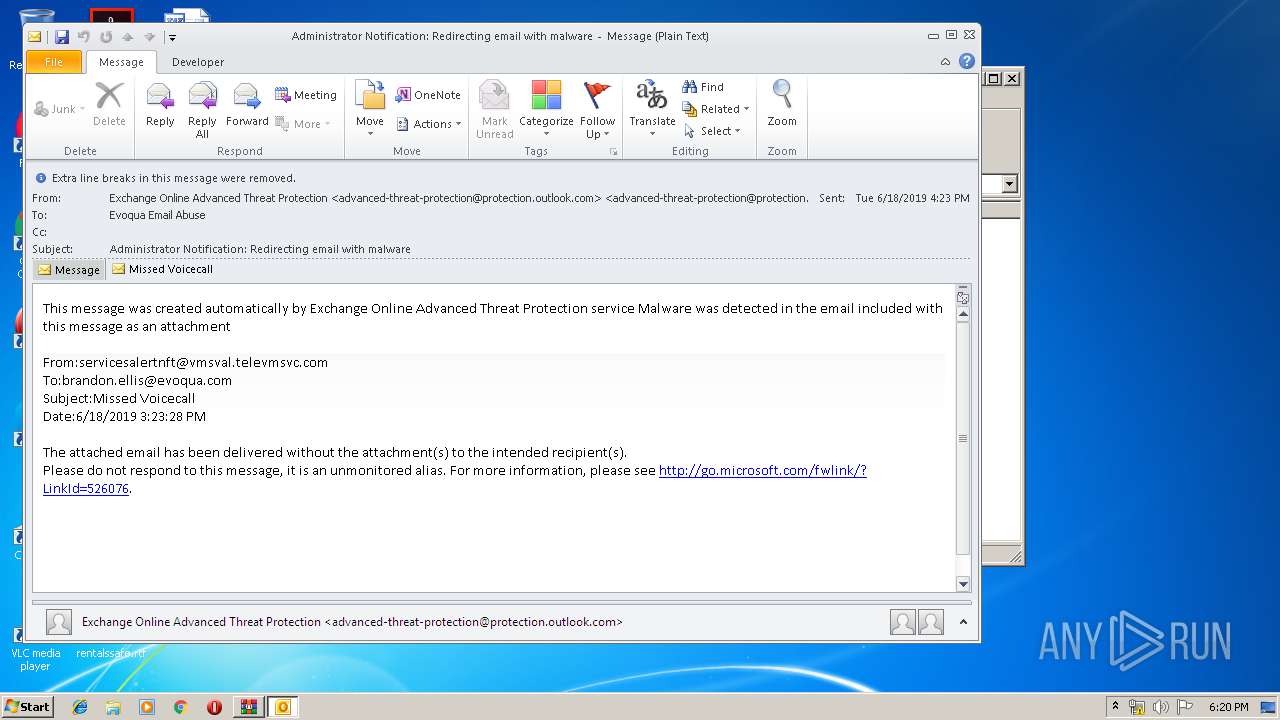
| 3972 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\WNBW1KQQ\🔊VM_18-06-2019.html | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 410
Read events
5 041
Write events
1 281
Delete events
88
Modification events
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\fc5b7db0-4652-47d9-9910-883f1964370b.zip | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214FA-0000-0000-C000-000000000046} 0xFFFF |
Value: 0100000000000000B023B205FA25D501 | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214EB-0000-0000-C000-000000000046} 0xFFFF |
Value: 0100000000000000BE4AB905FA25D501 | |||
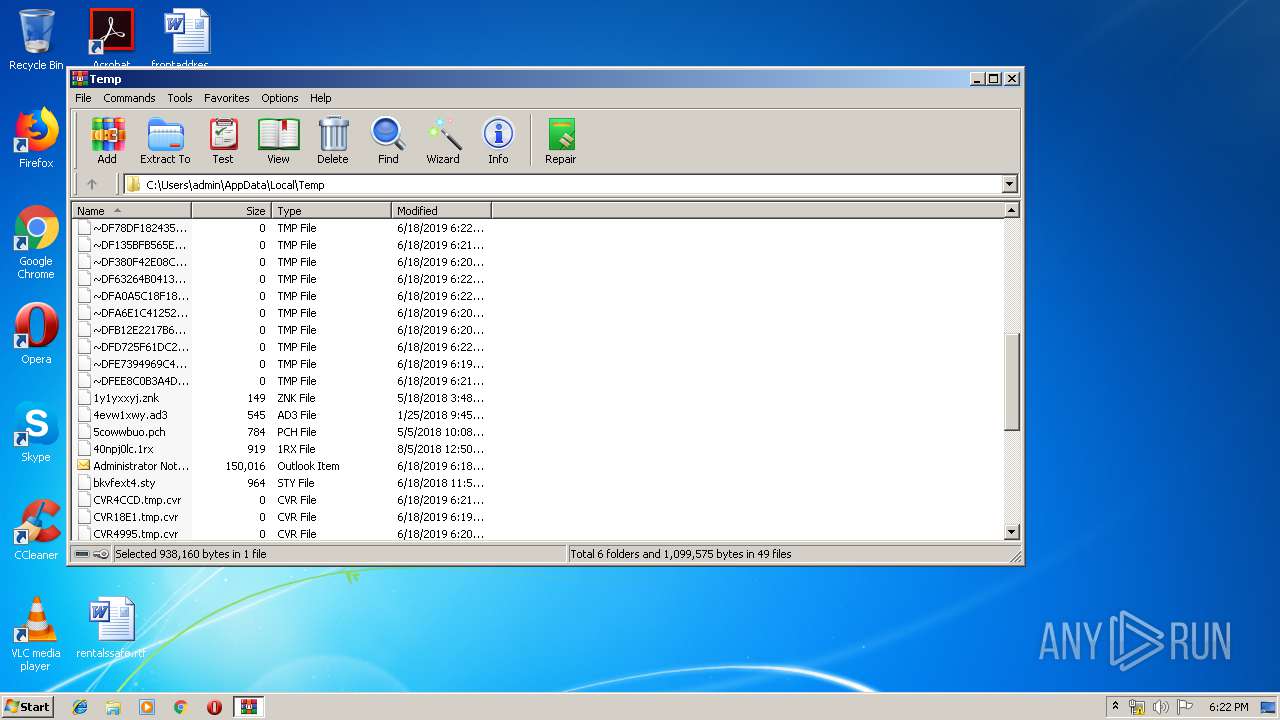
Executable files
0
Suspicious files
7
Text files
93
Unknown types
29
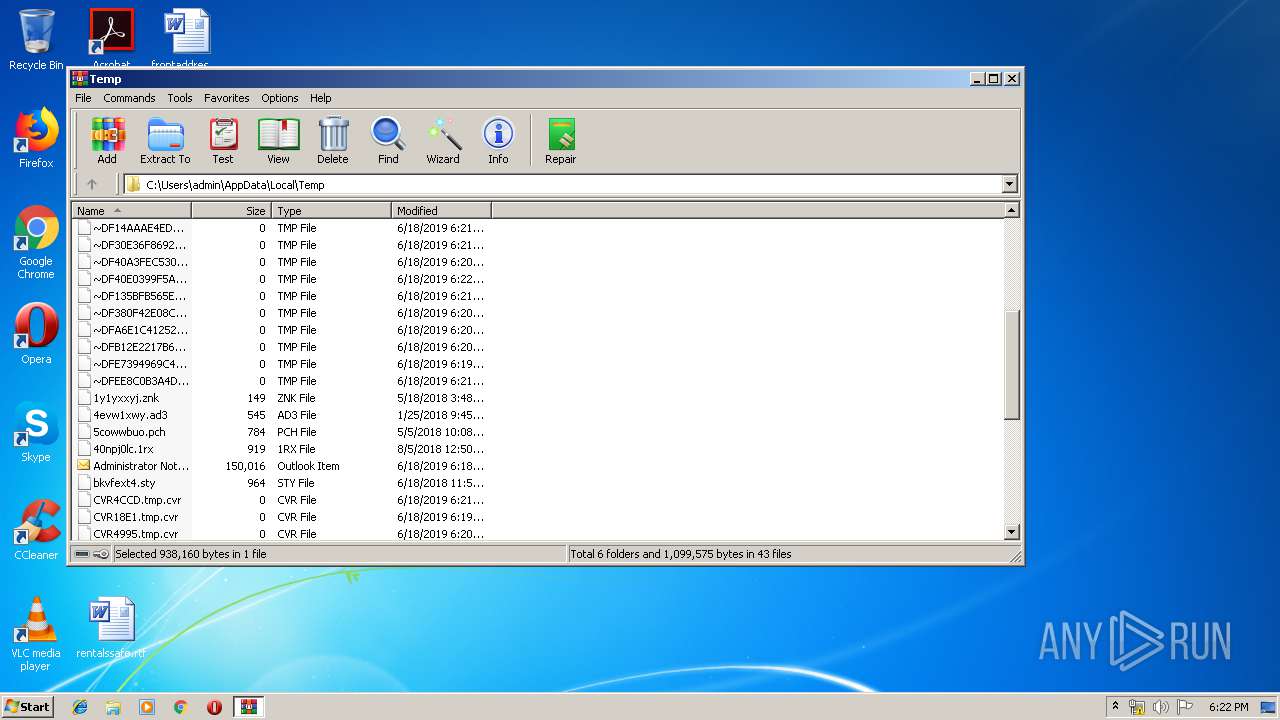
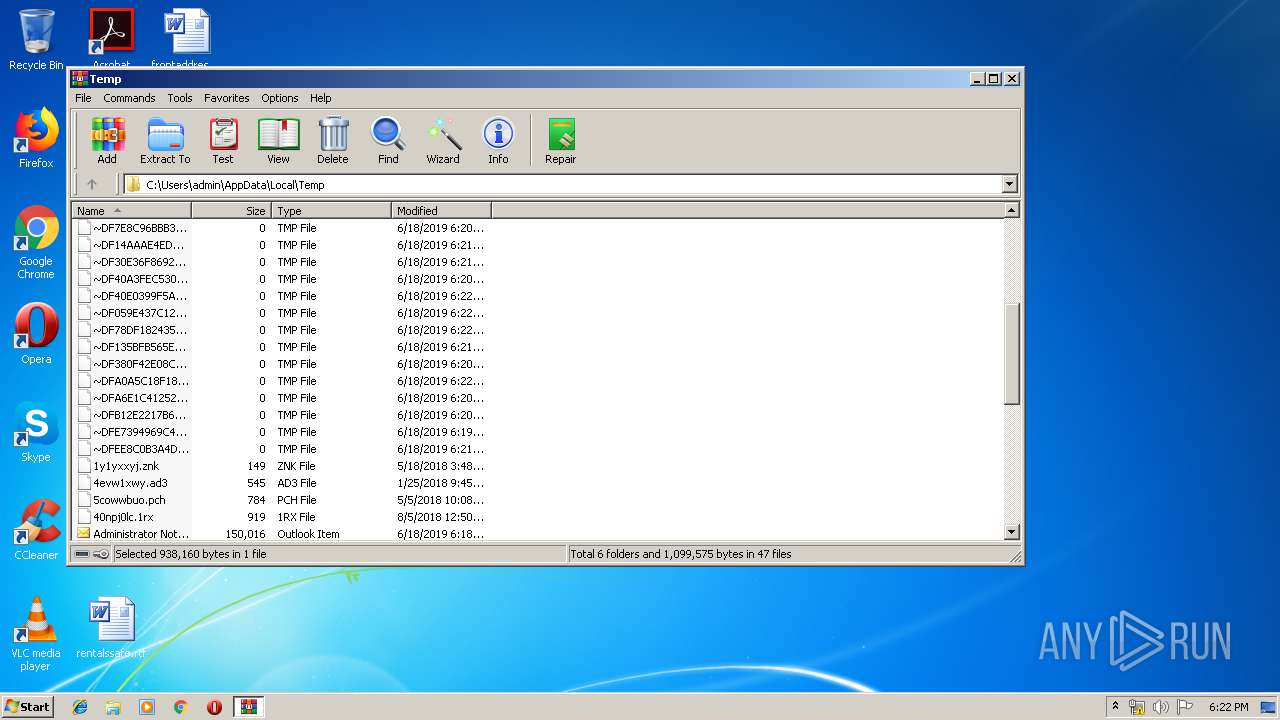
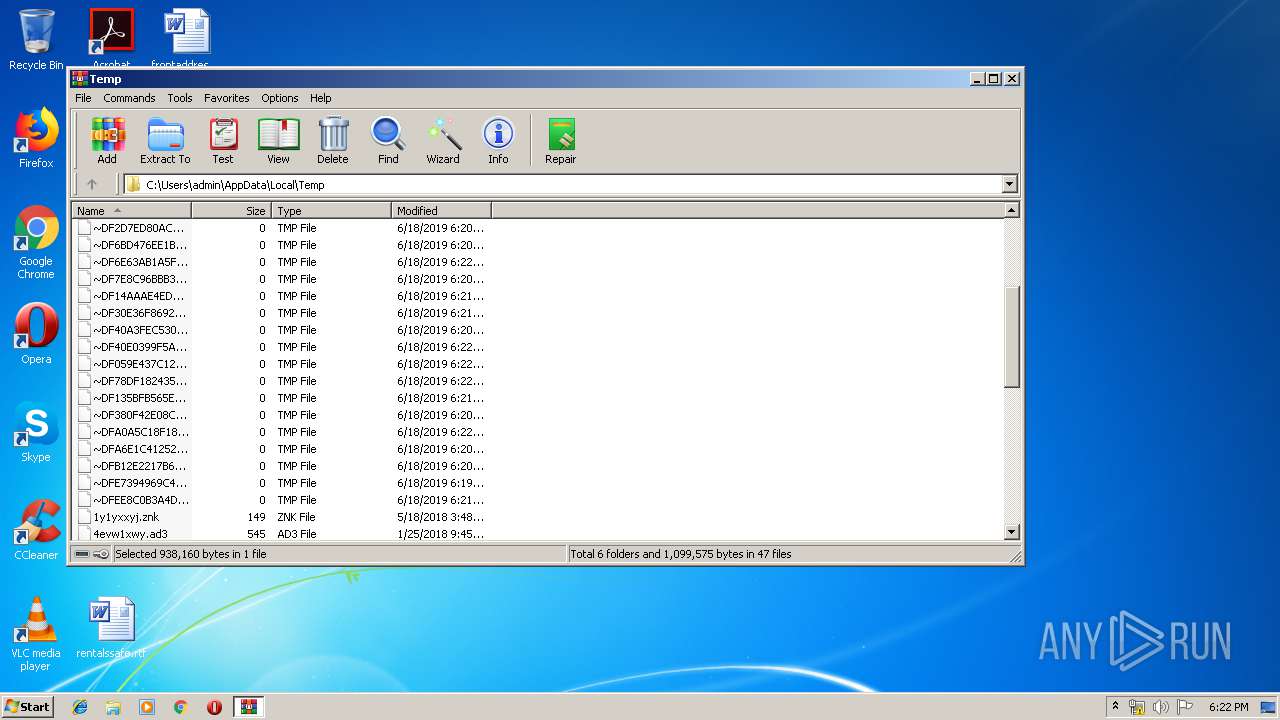
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2948 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\~DFE7394969C41CC5E7.TMP | — | |
MD5:— | SHA256:— | |||
| 3392 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR18E1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3188 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR4995.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3392 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFA6E1C412523A9B71.TMP | — | |
MD5:— | SHA256:— | |||
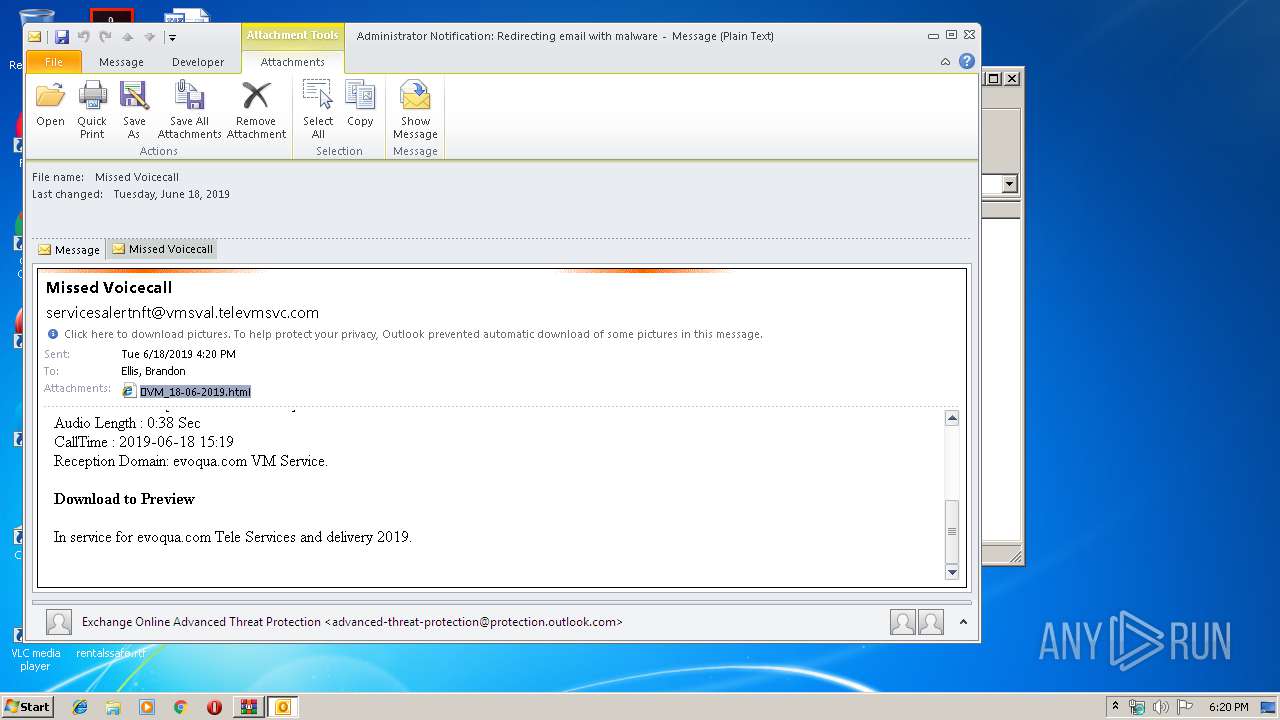
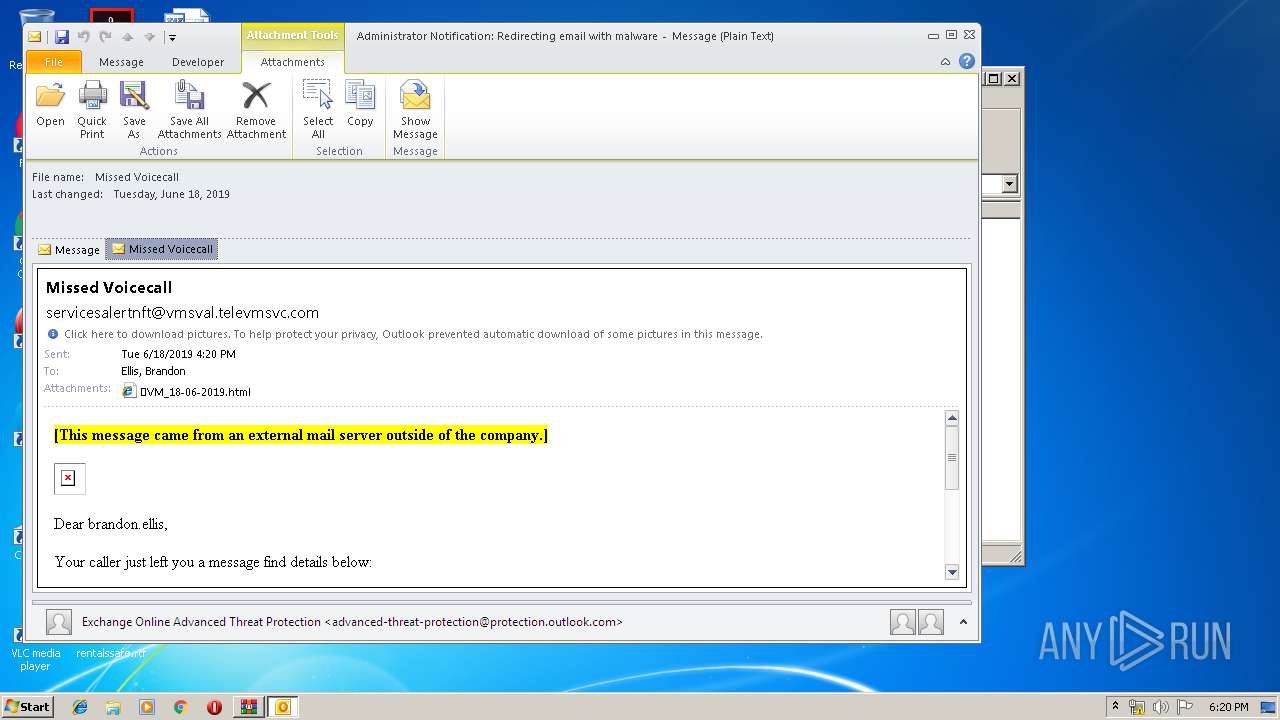
| 3392 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\WNBW1KQQ\🔊VM_18-06-2019 (2).html\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3392 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2948 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2948.38995\Administrator Notification_ Redirecting email with malware.msg | msg | |
MD5:— | SHA256:— | |||
| 3392 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 3392 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_20E4E55229A8B24FB2AE4AADB384602E.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
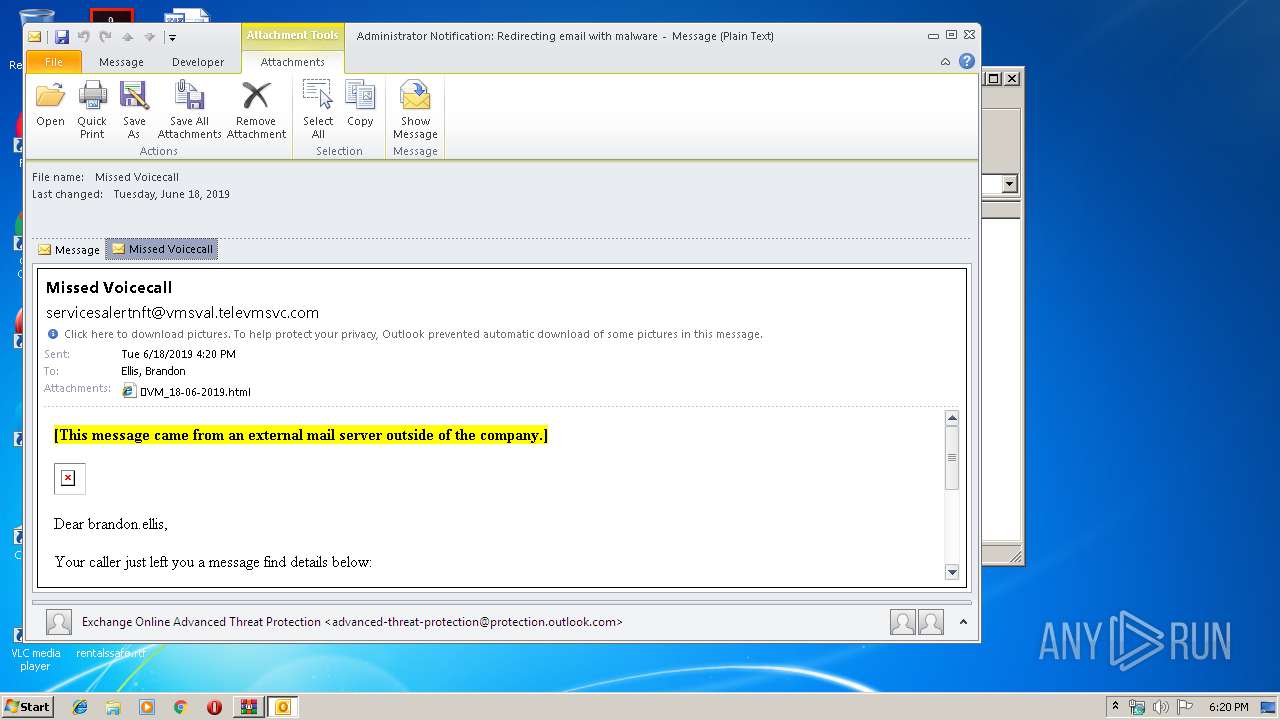
| 3392 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\WNBW1KQQ\Missed Voicecall.msg | msg | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
11
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2764 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2972 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3392 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2432 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3972 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2800 | iexplore.exe | GET | 200 | 93.185.104.64:80 | http://realmanbarber.cz/images/load.gif | CZ | image | 1.52 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2764 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3392 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
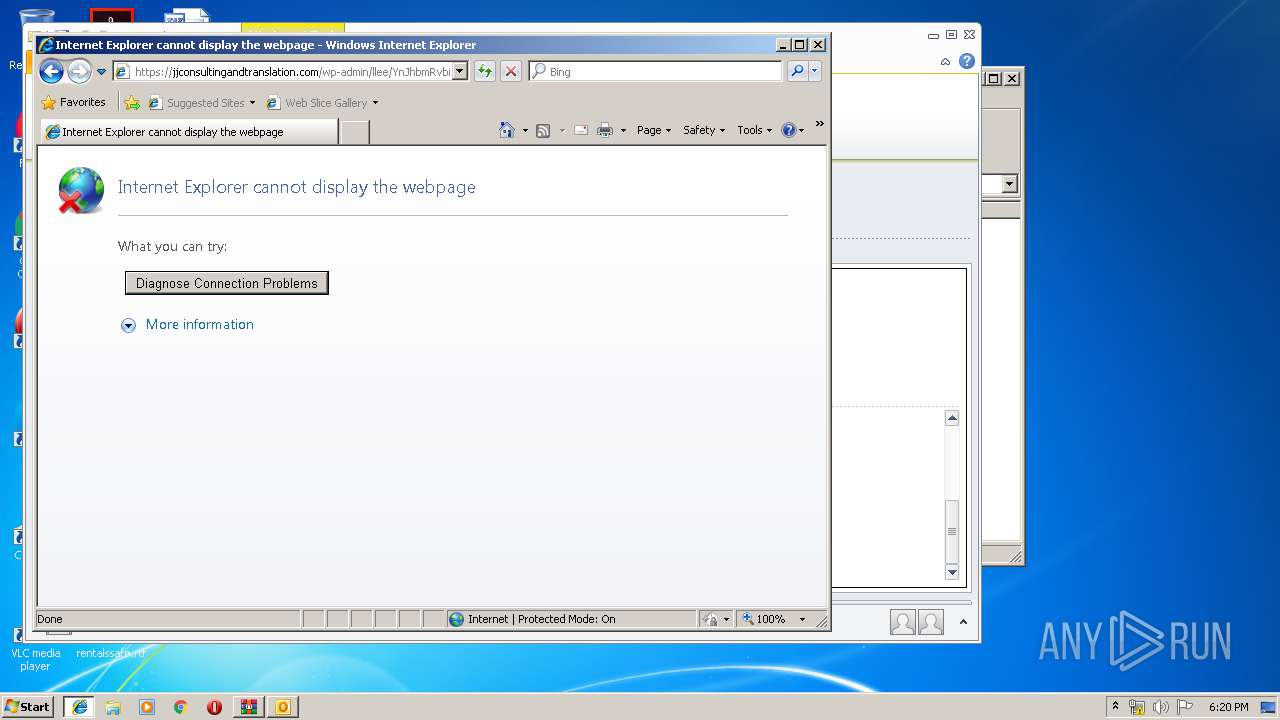
3972 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2800 | iexplore.exe | 93.185.104.64:80 | realmanbarber.cz | VSHosting s.r.o. | CZ | unknown |
2800 | iexplore.exe | 69.90.66.40:443 | jjconsultingandtranslation.com | Peer 1 Network (USA) Inc. | CA | suspicious |
2972 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2432 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2800 | iexplore.exe | 77.104.142.95:443 | www.erwantianshi.com | SoftLayer Technologies Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
realmanbarber.cz |
| malicious |
www.bing.com |
| whitelisted |
jjconsultingandtranslation.com |
| unknown |
www.erwantianshi.com |
| unknown |