| File name: | forkbomb.bat |
| Full analysis: | https://app.any.run/tasks/89ab36e0-9424-4821-9f9e-8b87e5e5e1b6 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 15:48:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | AE96E769138DD92870B7A3332F3ABD51 |
| SHA1: | 4D2DFF80A8F283552094D50C5ABB5F6F412AE6FF |
| SHA256: | 20FA2C6FD88E29B3E7B57D123BDA3B59EFA4F6B56A98A5B7C9EE1C818B25E456 |
| SSDEEP: | 3:+ys6V:+Q |
MALICIOUS
No malicious indicators.SUSPICIOUS
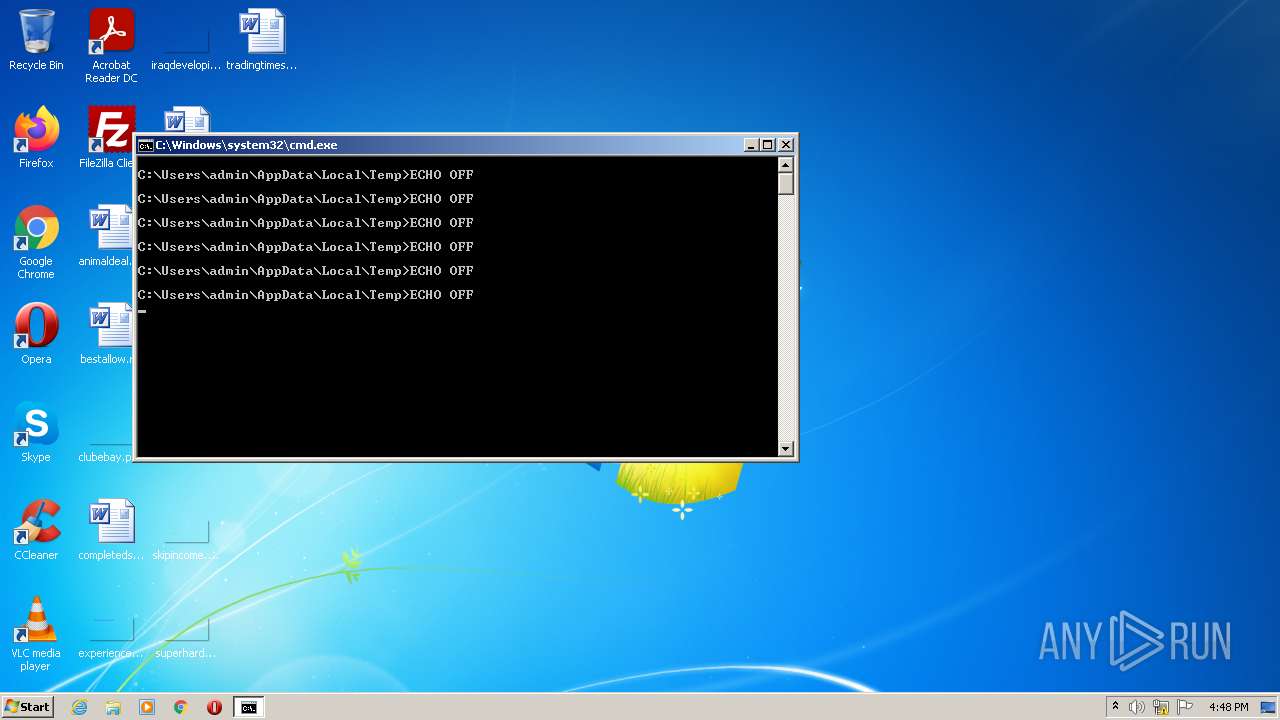
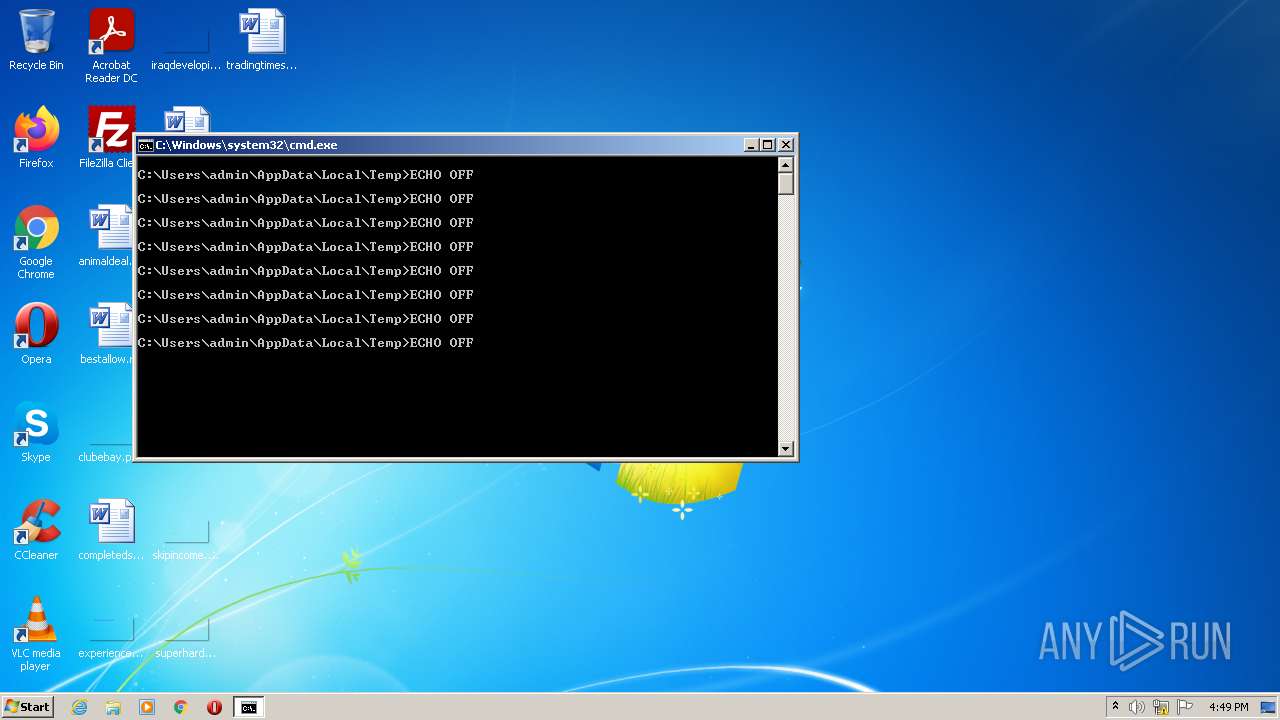
Application launched itself
- cmd.exe (PID: 3492)
- cmd.exe (PID: 2504)
- cmd.exe (PID: 1252)
- cmd.exe (PID: 3996)
- cmd.exe (PID: 3848)
- cmd.exe (PID: 4012)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 952)
- cmd.exe (PID: 1464)
- cmd.exe (PID: 3796)
- cmd.exe (PID: 2000)
- cmd.exe (PID: 2228)
- cmd.exe (PID: 2400)
- cmd.exe (PID: 2368)
- cmd.exe (PID: 3256)
- cmd.exe (PID: 964)
- cmd.exe (PID: 1020)
- cmd.exe (PID: 2720)
- cmd.exe (PID: 2716)
- cmd.exe (PID: 3604)
- cmd.exe (PID: 1716)
- cmd.exe (PID: 556)
- cmd.exe (PID: 1368)
- cmd.exe (PID: 1864)
- cmd.exe (PID: 2488)
- cmd.exe (PID: 1332)
- cmd.exe (PID: 2676)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 3596)
- cmd.exe (PID: 372)
- cmd.exe (PID: 2244)
- cmd.exe (PID: 3320)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 2304)
- cmd.exe (PID: 2336)
- cmd.exe (PID: 2476)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 1840)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 1504)
- cmd.exe (PID: 2580)
- cmd.exe (PID: 2012)
- cmd.exe (PID: 1944)
- cmd.exe (PID: 980)
- cmd.exe (PID: 3792)
- cmd.exe (PID: 3336)
- cmd.exe (PID: 2340)
- cmd.exe (PID: 1984)
- cmd.exe (PID: 1848)
- cmd.exe (PID: 2808)
- cmd.exe (PID: 528)
- cmd.exe (PID: 700)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 3116)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 3820)
- cmd.exe (PID: 996)
- cmd.exe (PID: 1872)
- cmd.exe (PID: 1824)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 2556)
- cmd.exe (PID: 1496)
- cmd.exe (PID: 3428)
Checks supported languages
- cmd.exe (PID: 2504)
- cmd.exe (PID: 3492)
- cmd.exe (PID: 1252)
- cmd.exe (PID: 3848)
- cmd.exe (PID: 3996)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 4012)
- cmd.exe (PID: 2228)
- cmd.exe (PID: 2368)
- cmd.exe (PID: 2720)
- cmd.exe (PID: 2716)
- cmd.exe (PID: 2000)
- cmd.exe (PID: 3604)
- cmd.exe (PID: 3796)
- cmd.exe (PID: 1464)
- cmd.exe (PID: 2400)
- cmd.exe (PID: 952)
- cmd.exe (PID: 1864)
- cmd.exe (PID: 1716)
- cmd.exe (PID: 2676)
- cmd.exe (PID: 2244)
- cmd.exe (PID: 1368)
- cmd.exe (PID: 3320)
- cmd.exe (PID: 2304)
- cmd.exe (PID: 964)
- cmd.exe (PID: 3256)
- cmd.exe (PID: 1020)
- cmd.exe (PID: 372)
- cmd.exe (PID: 556)
- cmd.exe (PID: 1848)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 980)
- cmd.exe (PID: 528)
- cmd.exe (PID: 2488)
- cmd.exe (PID: 1332)
- cmd.exe (PID: 2340)
- cmd.exe (PID: 2580)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 1984)
- cmd.exe (PID: 2336)
- cmd.exe (PID: 1504)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 2476)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 1944)
- cmd.exe (PID: 3596)
- cmd.exe (PID: 1840)
- cmd.exe (PID: 700)
- cmd.exe (PID: 3792)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 2808)
- cmd.exe (PID: 2012)
- cmd.exe (PID: 2192)
- cmd.exe (PID: 3116)
- cmd.exe (PID: 3336)
- cmd.exe (PID: 2556)
- cmd.exe (PID: 3776)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 4092)
- cmd.exe (PID: 1268)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 4088)
- cmd.exe (PID: 3864)
- cmd.exe (PID: 3428)
- cmd.exe (PID: 2772)
- cmd.exe (PID: 2152)
- cmd.exe (PID: 2688)
- cmd.exe (PID: 2500)
- cmd.exe (PID: 3840)
- cmd.exe (PID: 2312)
- cmd.exe (PID: 1120)
- cmd.exe (PID: 1732)
- cmd.exe (PID: 2184)
- cmd.exe (PID: 1496)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 3820)
- cmd.exe (PID: 996)
- cmd.exe (PID: 1872)
- cmd.exe (PID: 3032)
- cmd.exe (PID: 3748)
- cmd.exe (PID: 2640)
- cmd.exe (PID: 2540)
- cmd.exe (PID: 1824)
- cmd.exe (PID: 3656)
- cmd.exe (PID: 3508)
- cmd.exe (PID: 3000)
- cmd.exe (PID: 3512)
- cmd.exe (PID: 3124)
- cmd.exe (PID: 1536)
- cmd.exe (PID: 3416)
- cmd.exe (PID: 3396)
- cmd.exe (PID: 3784)
- cmd.exe (PID: 3364)
- cmd.exe (PID: 3564)
- cmd.exe (PID: 2896)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 2784)
- cmd.exe (PID: 3188)
- cmd.exe (PID: 3900)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
139
Monitored processes
105
Malicious processes
16
Suspicious processes
20
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\forkbomb.bat" " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 528 | C:\Windows\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\forkbomb.bat"" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 556 | C:\Windows\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\forkbomb.bat"" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 700 | C:\Windows\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\forkbomb.bat" " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 952 | C:\Windows\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\forkbomb.bat" " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 964 | C:\Windows\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\forkbomb.bat"" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 980 | C:\Windows\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\forkbomb.bat"" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 996 | C:\Windows\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\forkbomb.bat" " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1020 | C:\Windows\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\forkbomb.bat"" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1120 | C:\Windows\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\forkbomb.bat" " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 560
Read events
1 560
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report