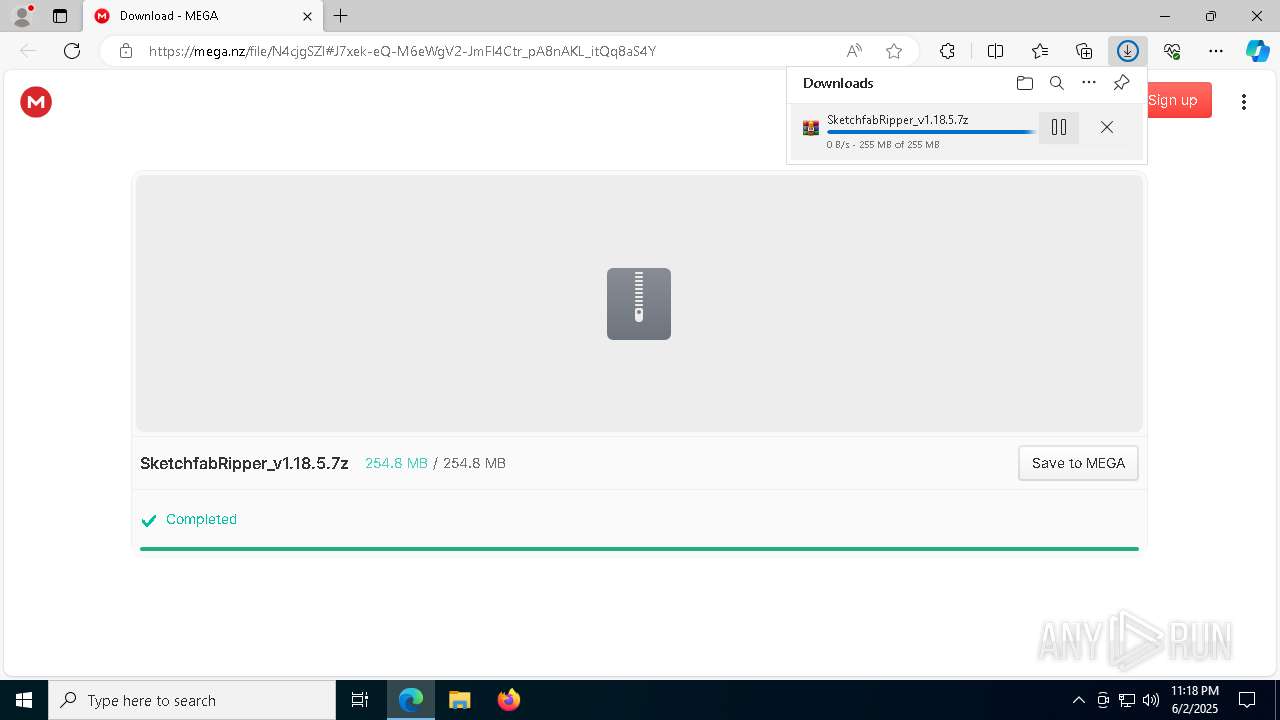
| URL: | https://mega.nz/file/N4cjgSZI#J7xek-eQ-M6eWgV2-JmFl4Ctr_pA8nAKL_itQq8aS4Y |
| Full analysis: | https://app.any.run/tasks/580794d0-765d-4f36-99e4-c053e8f8ec88 |
| Verdict: | Malicious activity |
| Analysis date: | June 02, 2025, 23:18:16 |
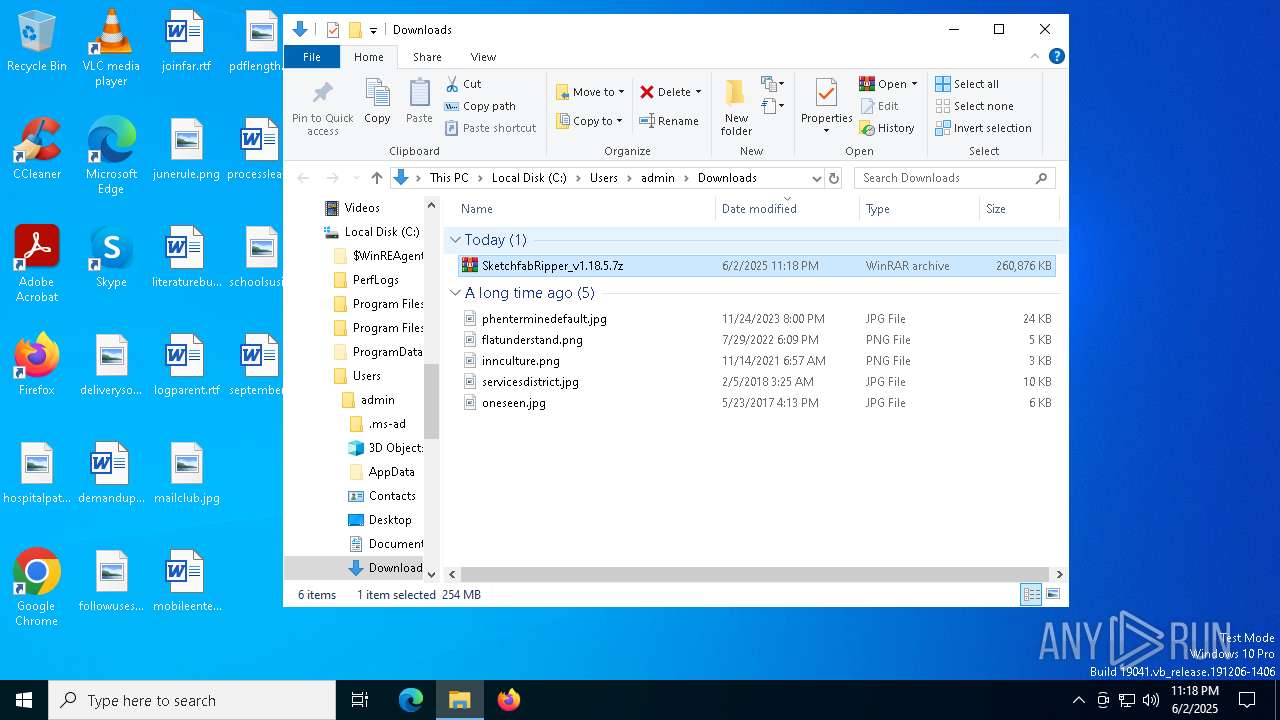
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FF24046FBC38A18DF39ED4947531F3CF |
| SHA1: | 75EF74BE93EF7EE6C95D3C29C562DC75802E81F5 |
| SHA256: | 20F3683ABA2F6C24FFC102DAD0AE06562EAFE8F1CE95742D90A82EB994C268C3 |
| SSDEEP: | 3:N8X/iq4XnAxv9o+kquUhUc:2S89VXbUc |
MALICIOUS
No malicious indicators.SUSPICIOUS
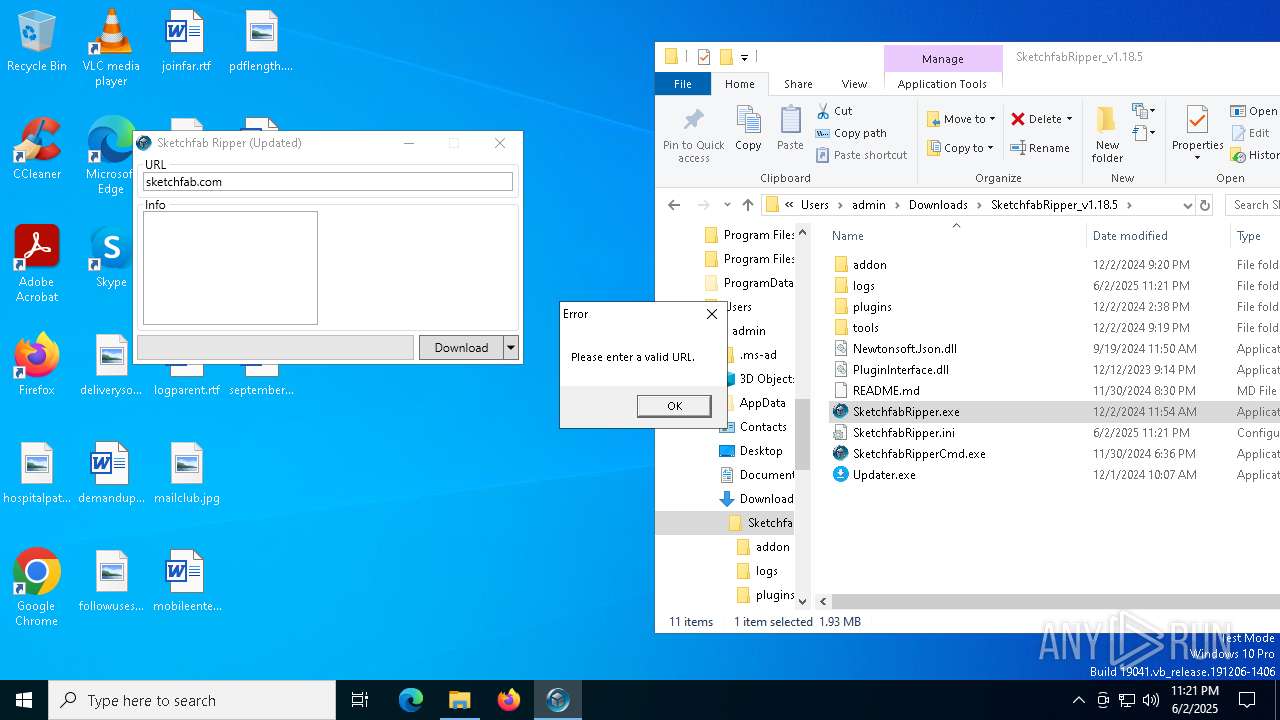
Possibly a phishing URL contains email has been detected
- msedge.exe (PID: 7128)
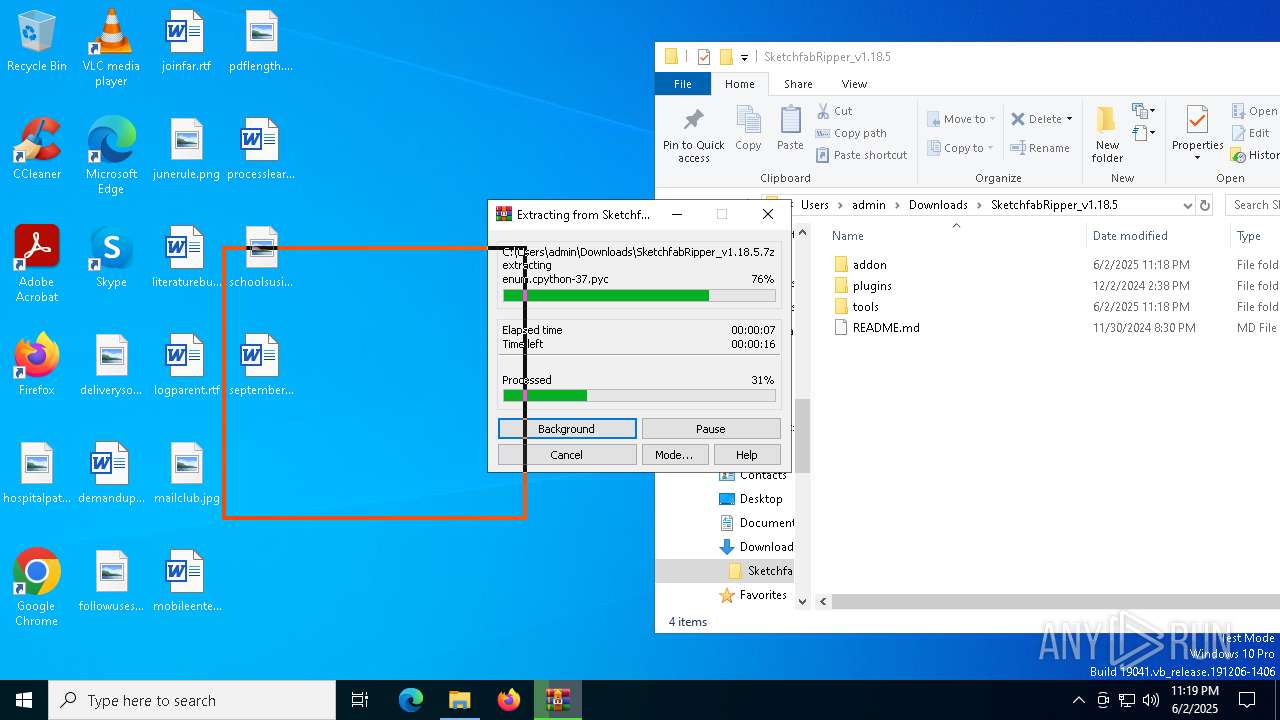
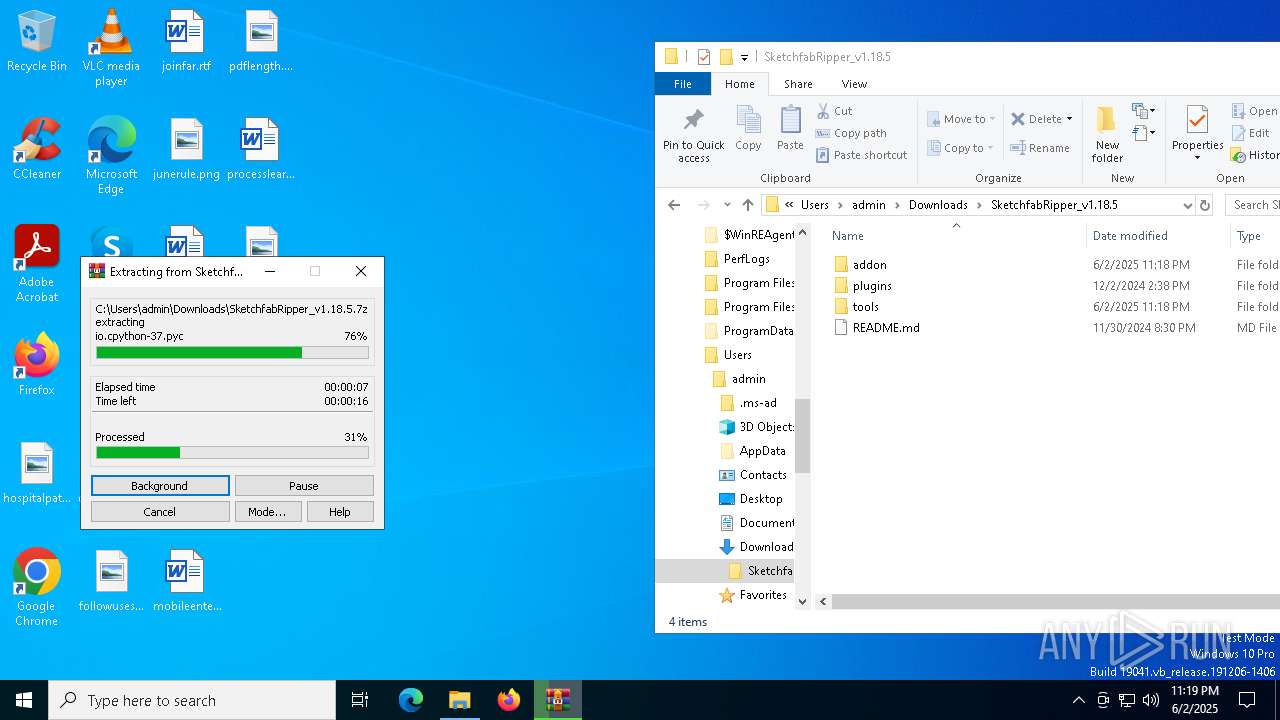
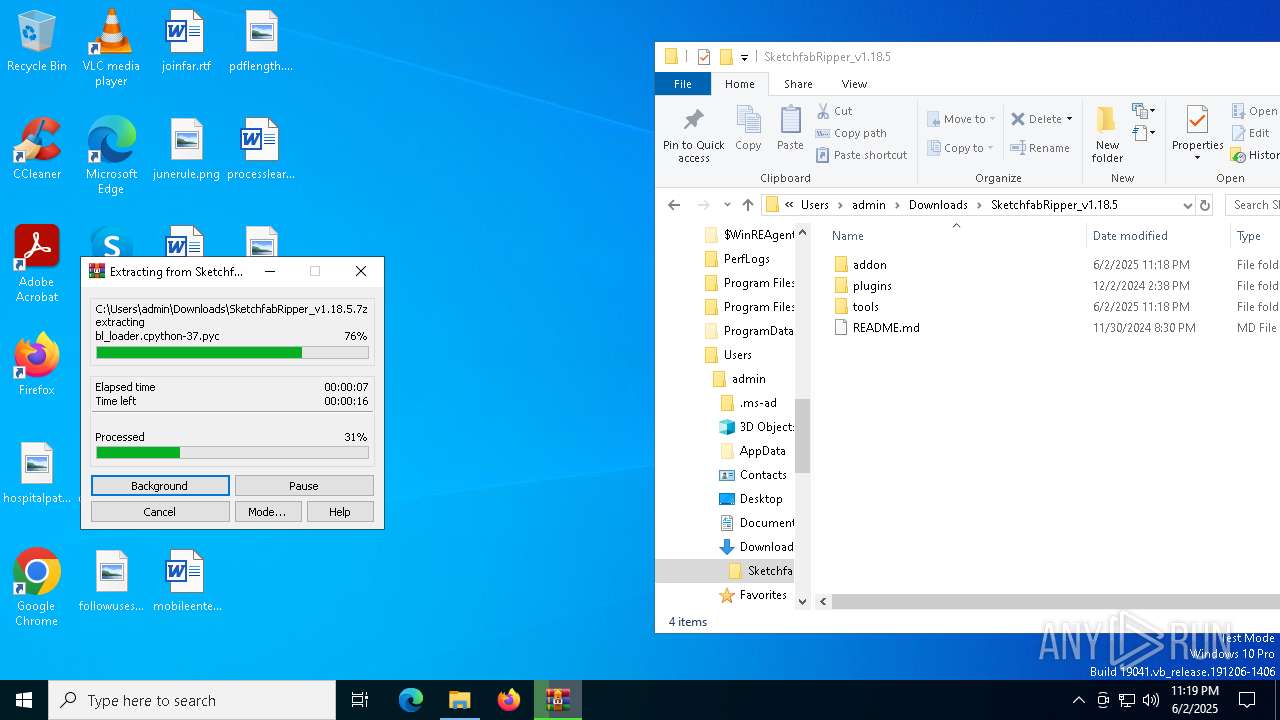
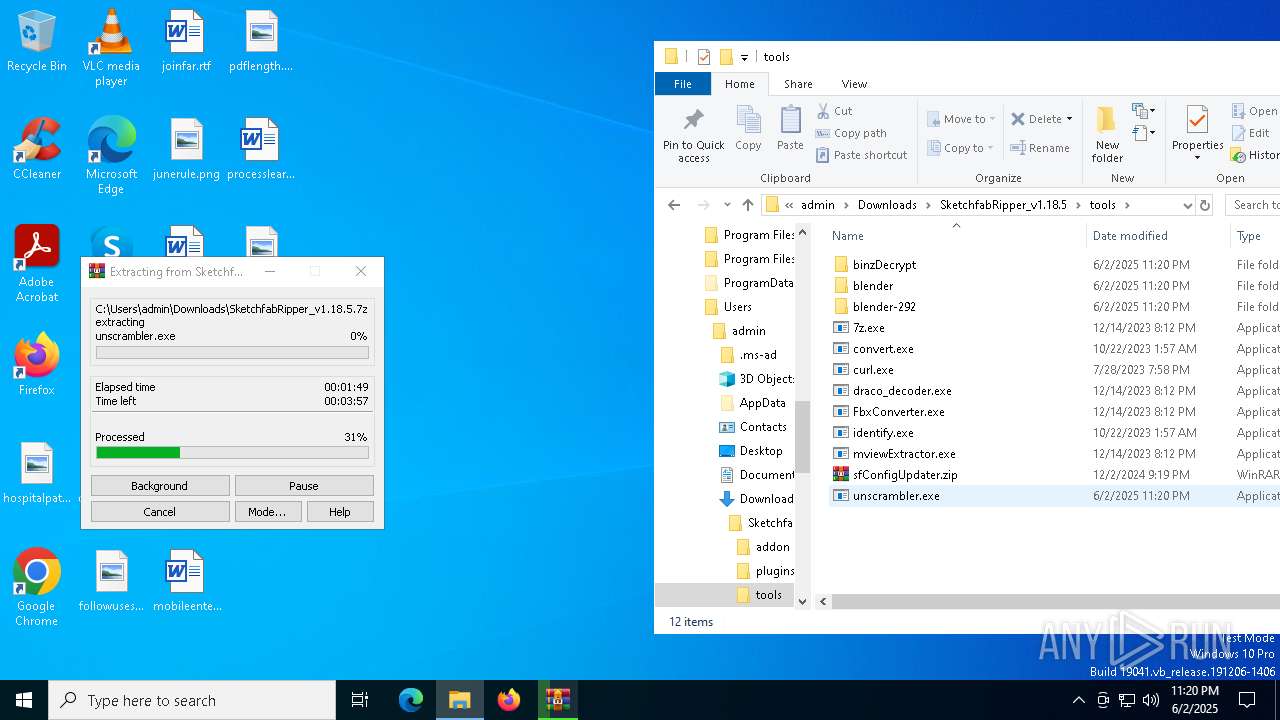
Process drops python dynamic module
- WinRAR.exe (PID: 472)
- unscrambler.exe (PID: 5384)
- unscrambler.exe (PID: 2552)
- unscrambler.exe (PID: 5348)
- unscrambler.exe (PID: 5504)
- unscrambler.exe (PID: 3768)
- unscrambler.exe (PID: 4244)
- unscrambler.exe (PID: 1600)
- unscrambler.exe (PID: 5720)
- unscrambler.exe (PID: 2108)
- unscrambler.exe (PID: 8020)
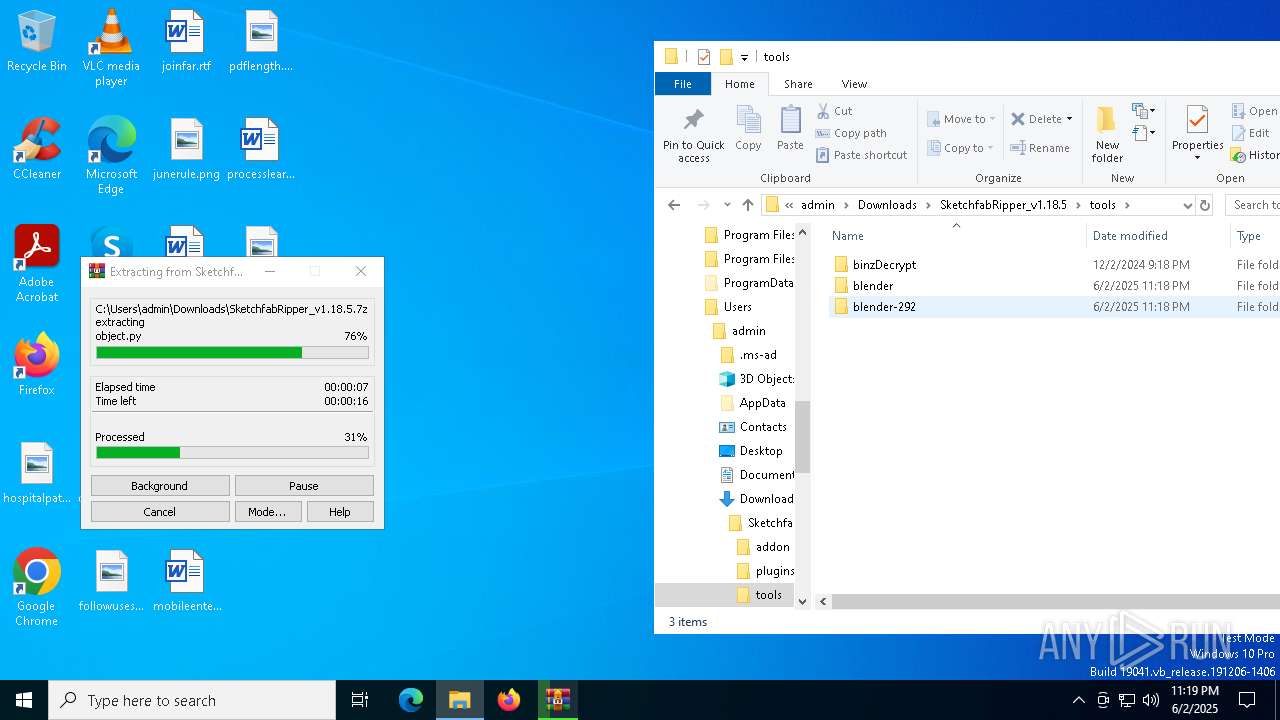
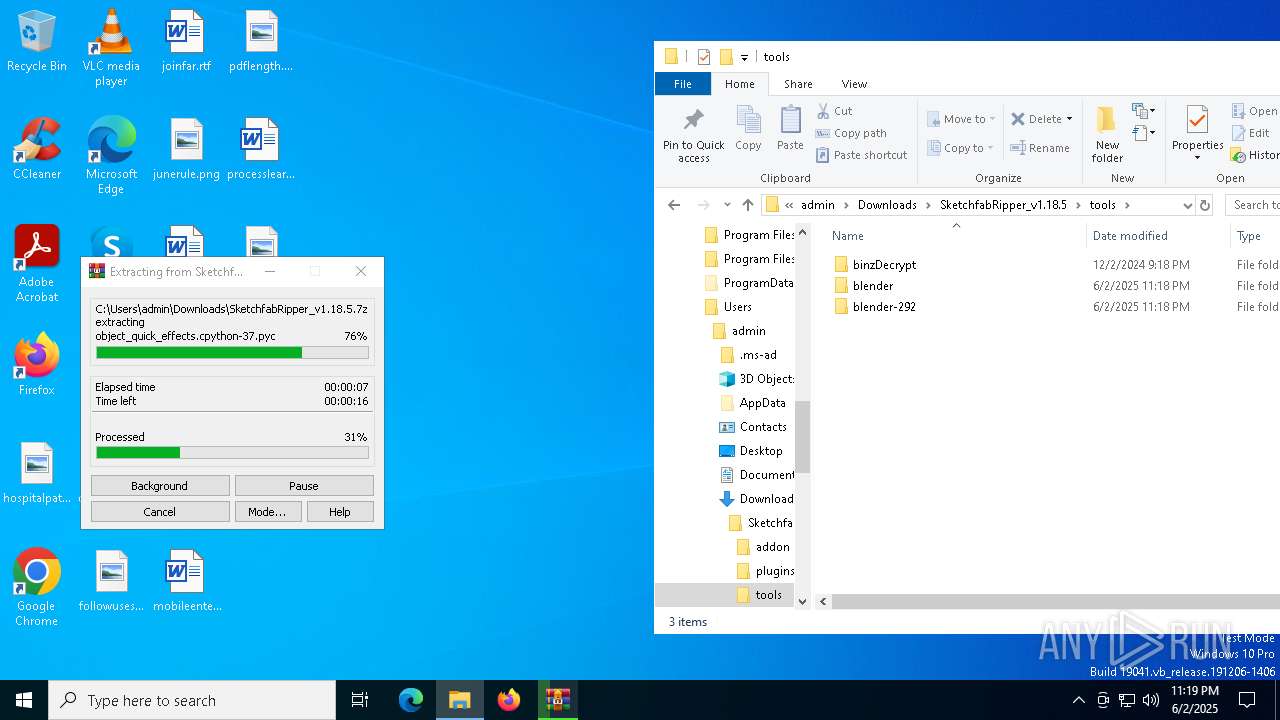
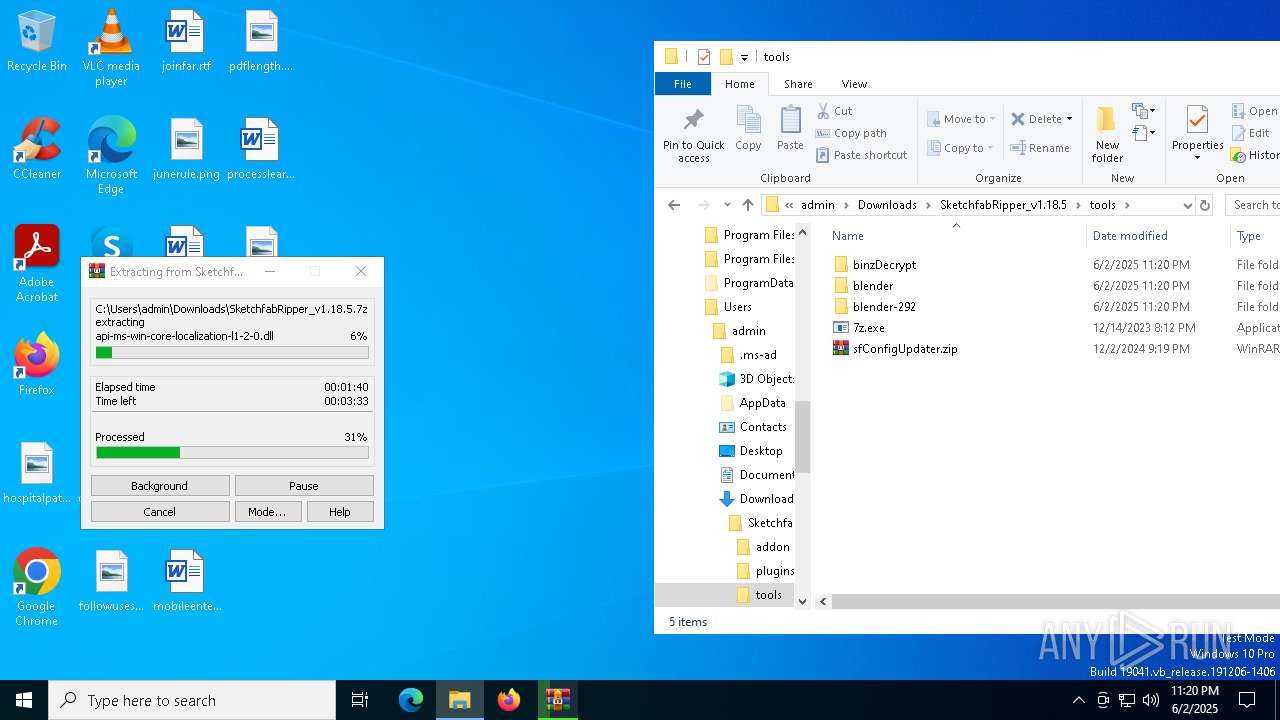
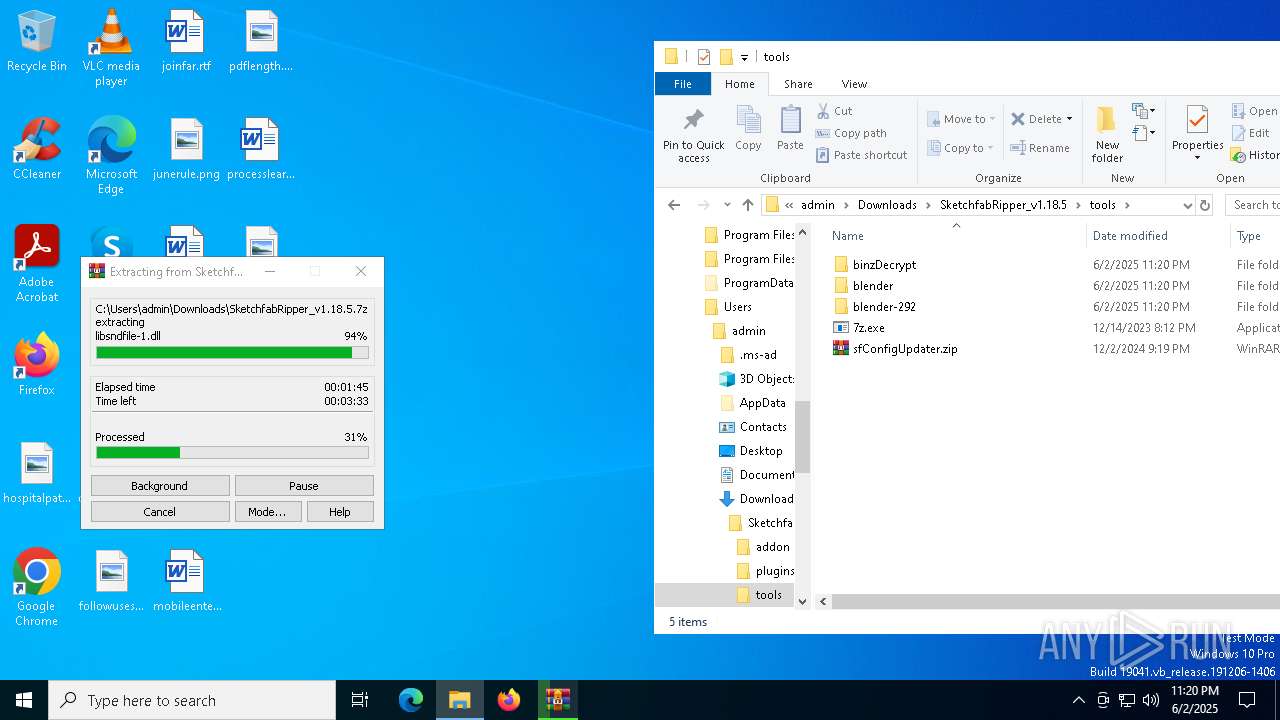
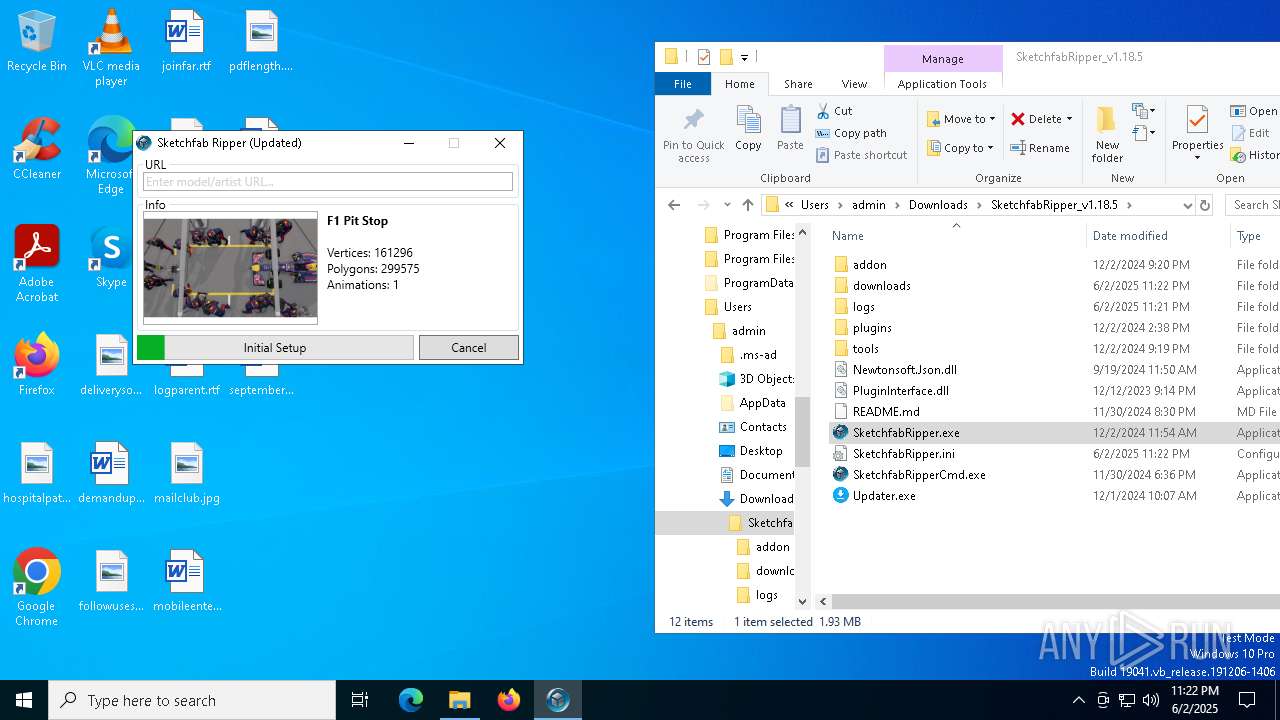
Drops 7-zip archiver for unpacking
- WinRAR.exe (PID: 472)
Node.exe was dropped
- WinRAR.exe (PID: 472)
The process drops C-runtime libraries
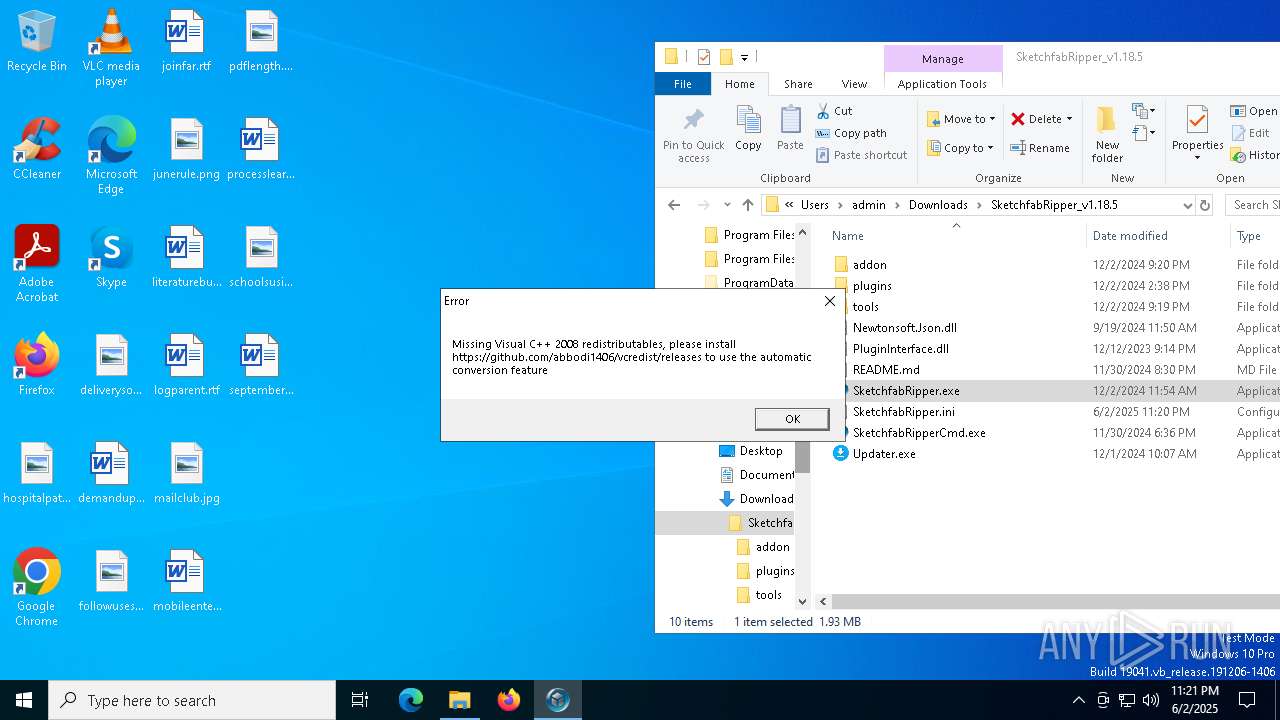
- SketchfabRipper.exe (PID: 1812)
- unscrambler.exe (PID: 5384)
- unscrambler.exe (PID: 2552)
- unscrambler.exe (PID: 5348)
- unscrambler.exe (PID: 5504)
- unscrambler.exe (PID: 3768)
- unscrambler.exe (PID: 4244)
- unscrambler.exe (PID: 1600)
- unscrambler.exe (PID: 5720)
- unscrambler.exe (PID: 2108)
- unscrambler.exe (PID: 8020)
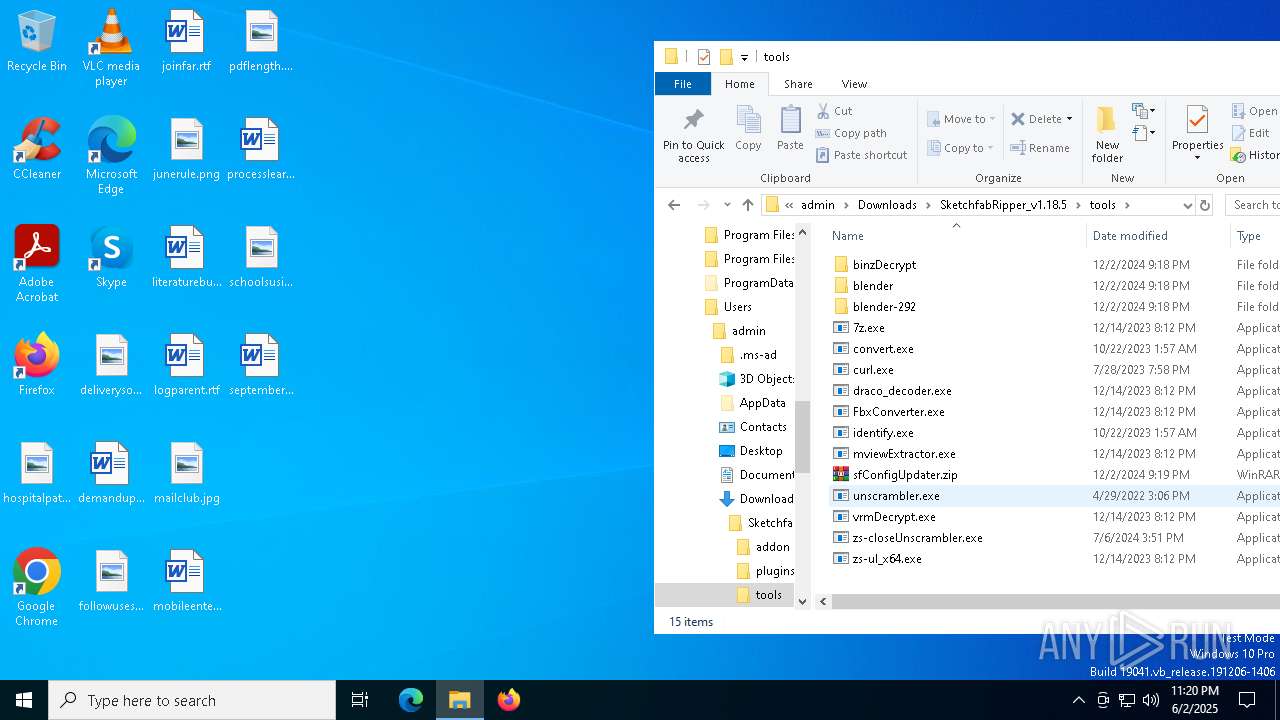
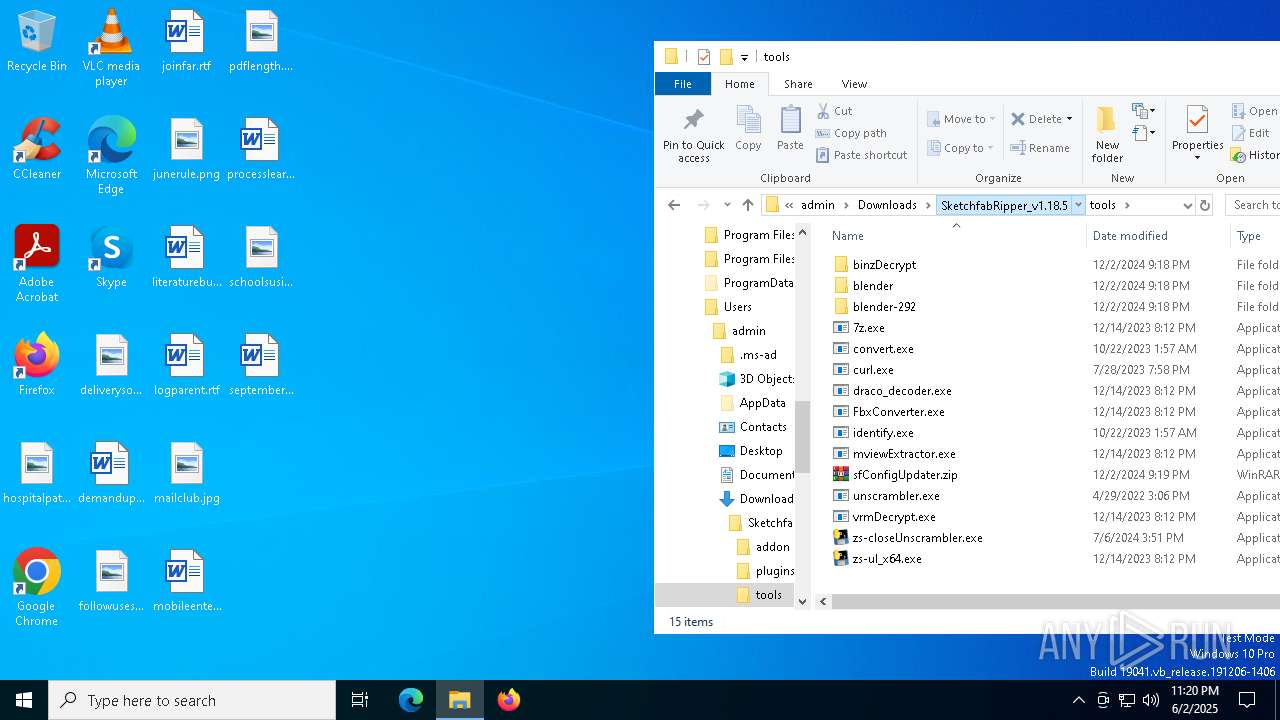
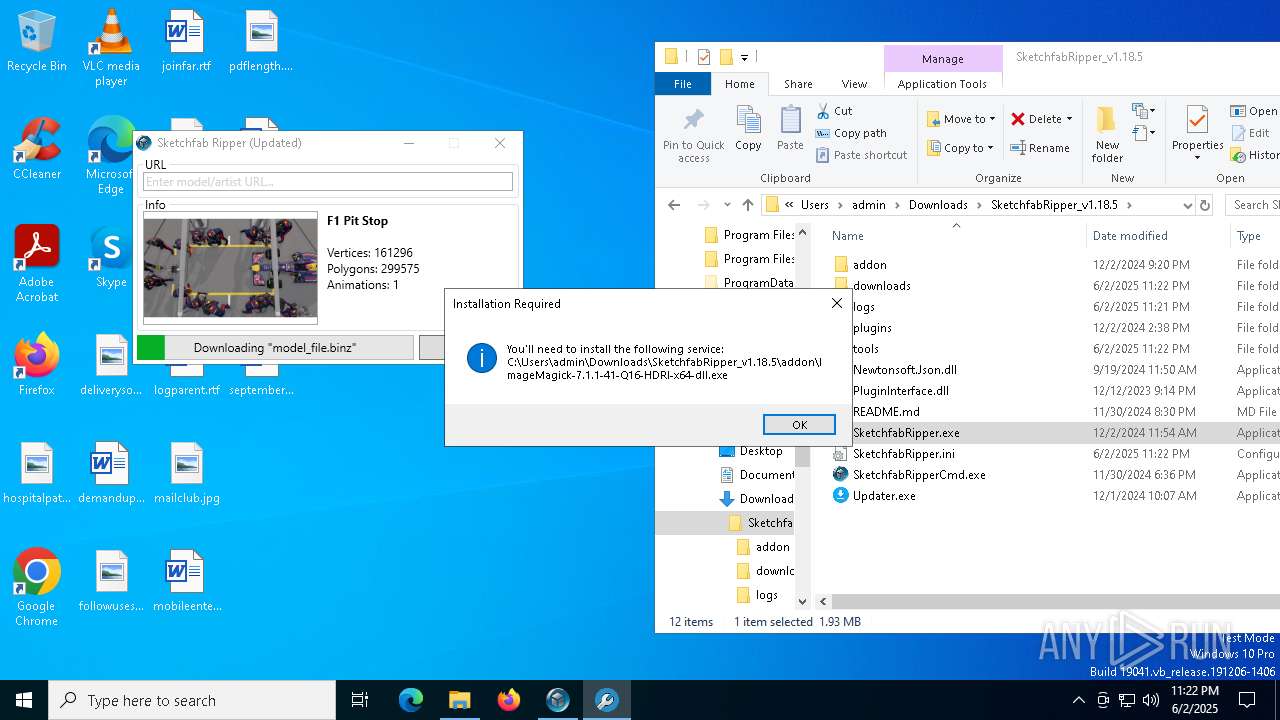
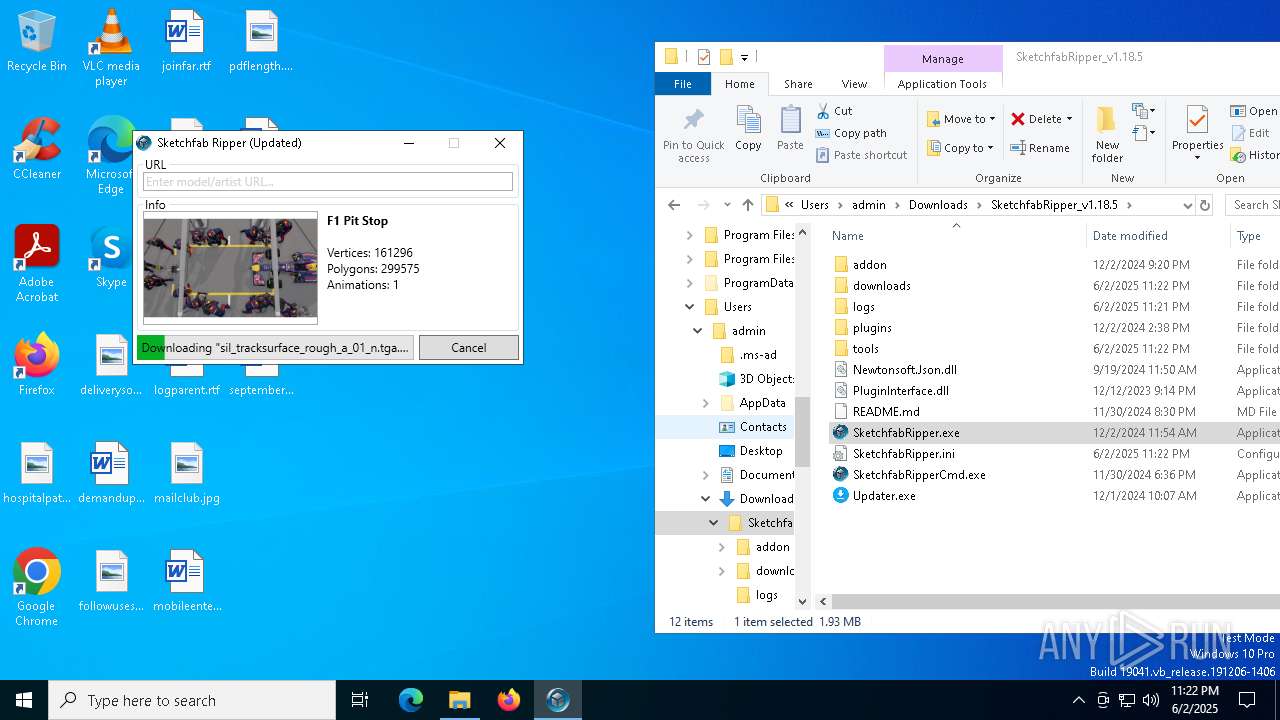
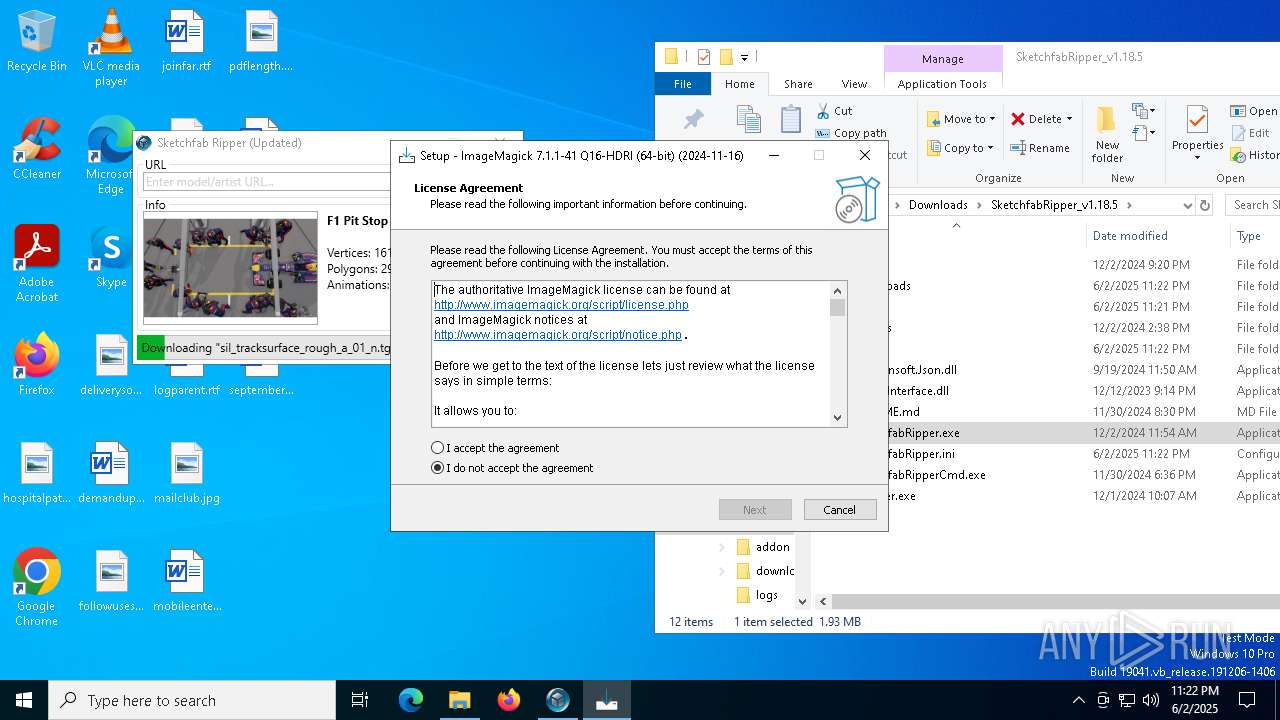
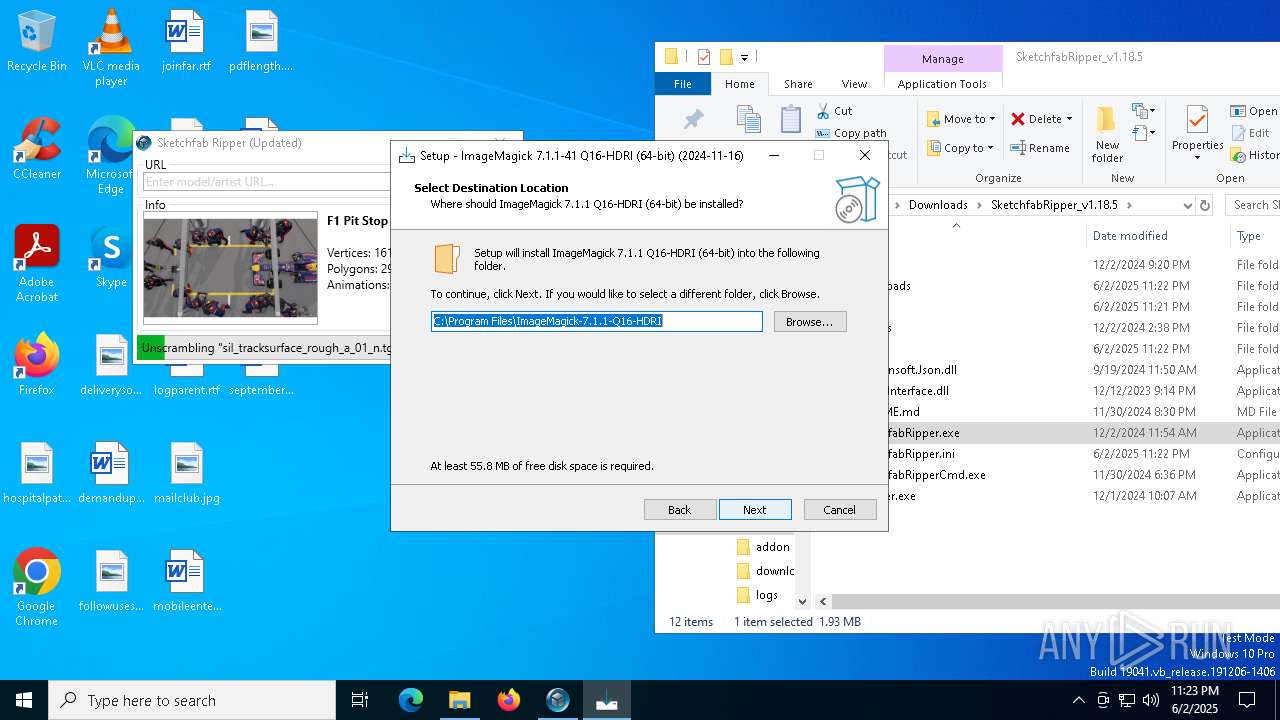
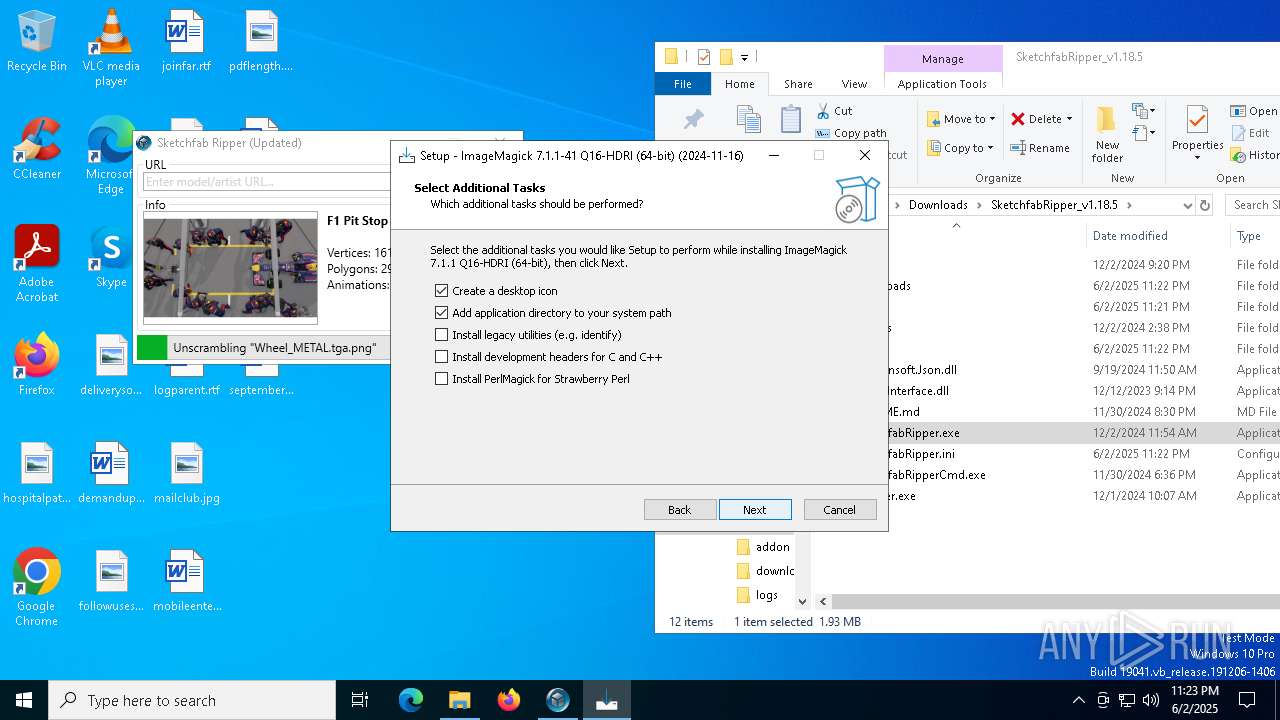
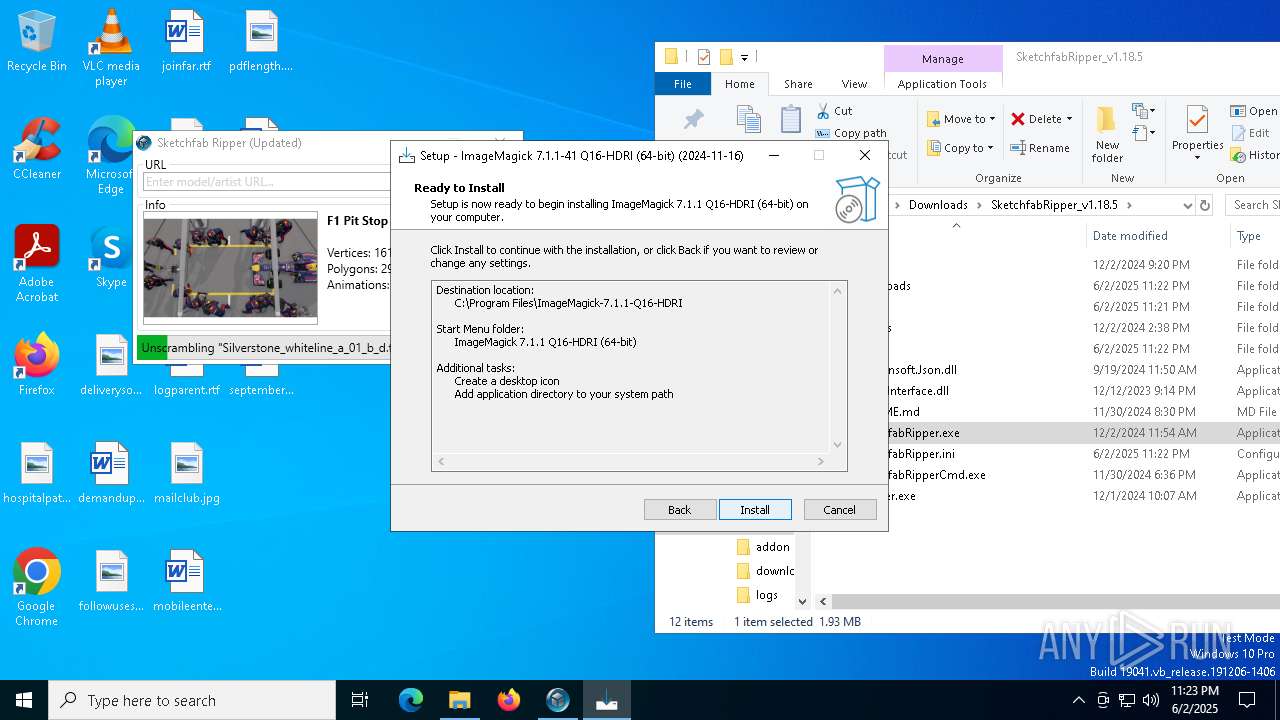
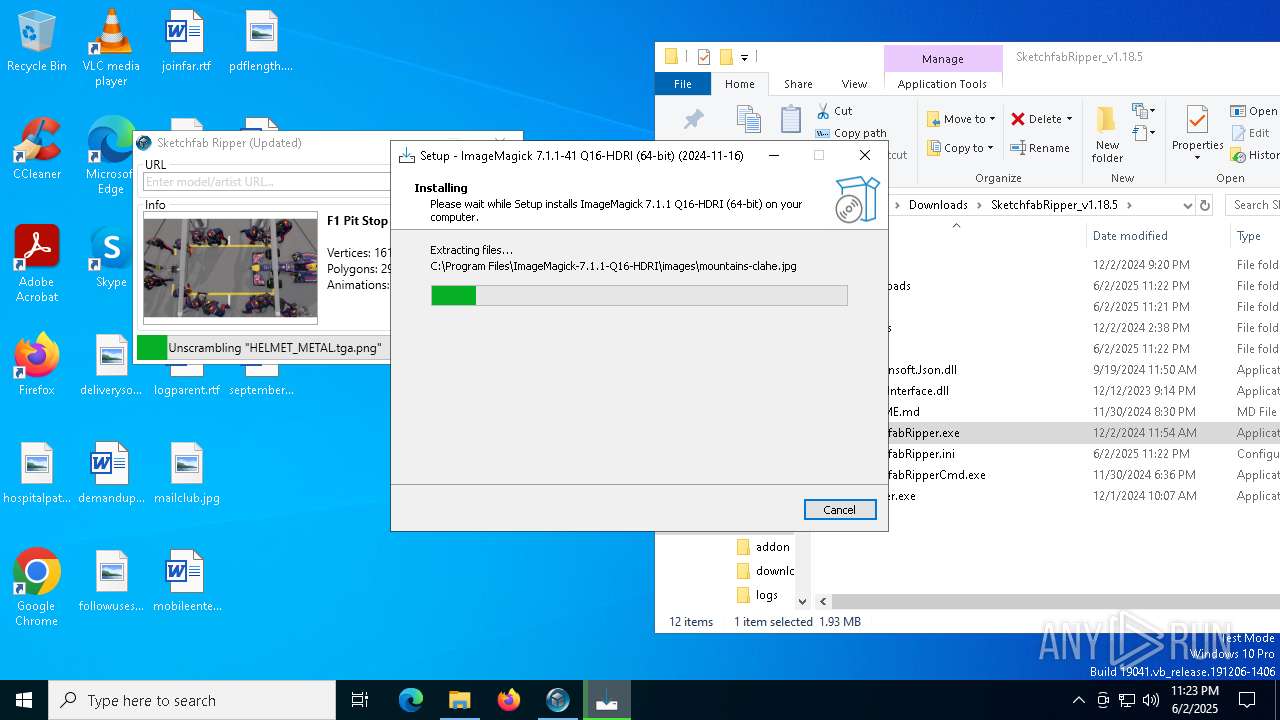
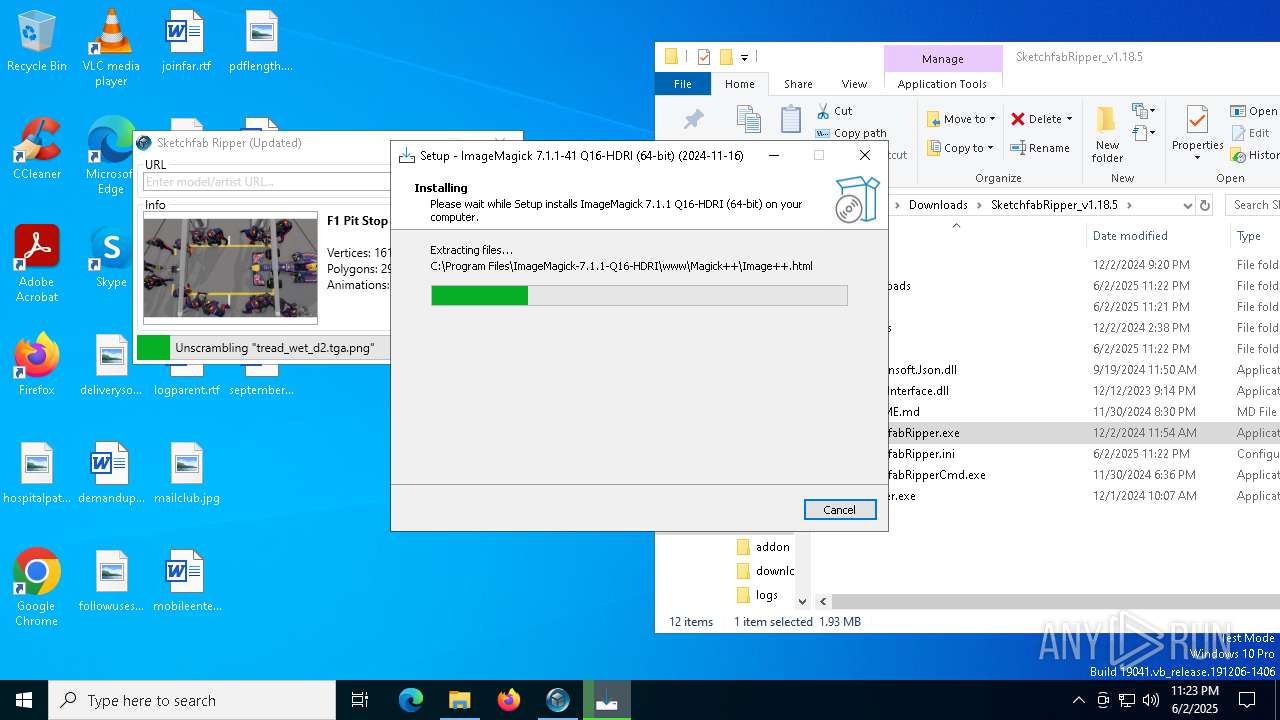
Executable content was dropped or overwritten
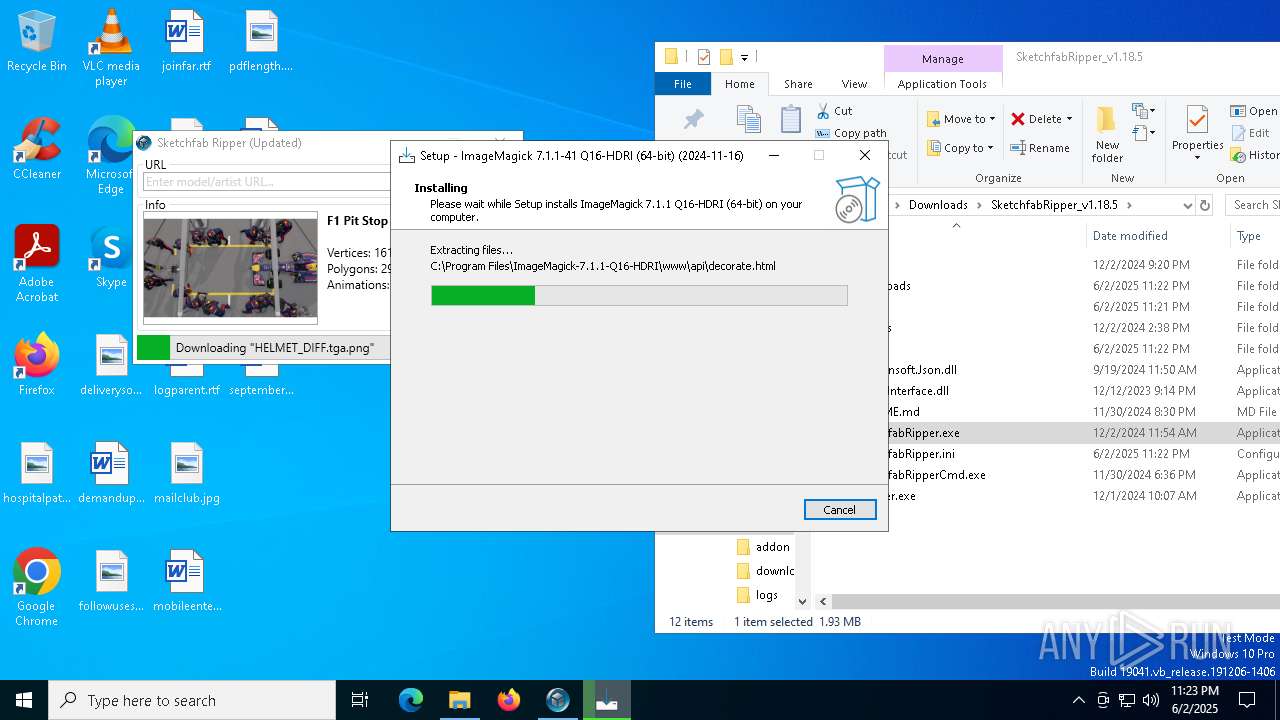
- ImageMagick-7.1.1-41-Q16-HDRI-x64-dll.exe (PID: 4844)
- unscrambler.exe (PID: 5384)
- ImageMagick-7.1.1-41-Q16-HDRI-x64-dll.tmp (PID: 3784)
- SketchfabRipper.exe (PID: 1812)
- unscrambler.exe (PID: 2552)
- unscrambler.exe (PID: 5348)
- unscrambler.exe (PID: 5504)
- unscrambler.exe (PID: 3768)
- unscrambler.exe (PID: 4244)
- unscrambler.exe (PID: 1600)
- unscrambler.exe (PID: 5720)
- unscrambler.exe (PID: 2108)
- unscrambler.exe (PID: 8020)
Process drops legitimate windows executable
- unscrambler.exe (PID: 5384)
- WinRAR.exe (PID: 472)
- SketchfabRipper.exe (PID: 1812)
- unscrambler.exe (PID: 5348)
- unscrambler.exe (PID: 5504)
- unscrambler.exe (PID: 2552)
- unscrambler.exe (PID: 3768)
- unscrambler.exe (PID: 4244)
- unscrambler.exe (PID: 5720)
- unscrambler.exe (PID: 1600)
- unscrambler.exe (PID: 2108)
- unscrambler.exe (PID: 8020)
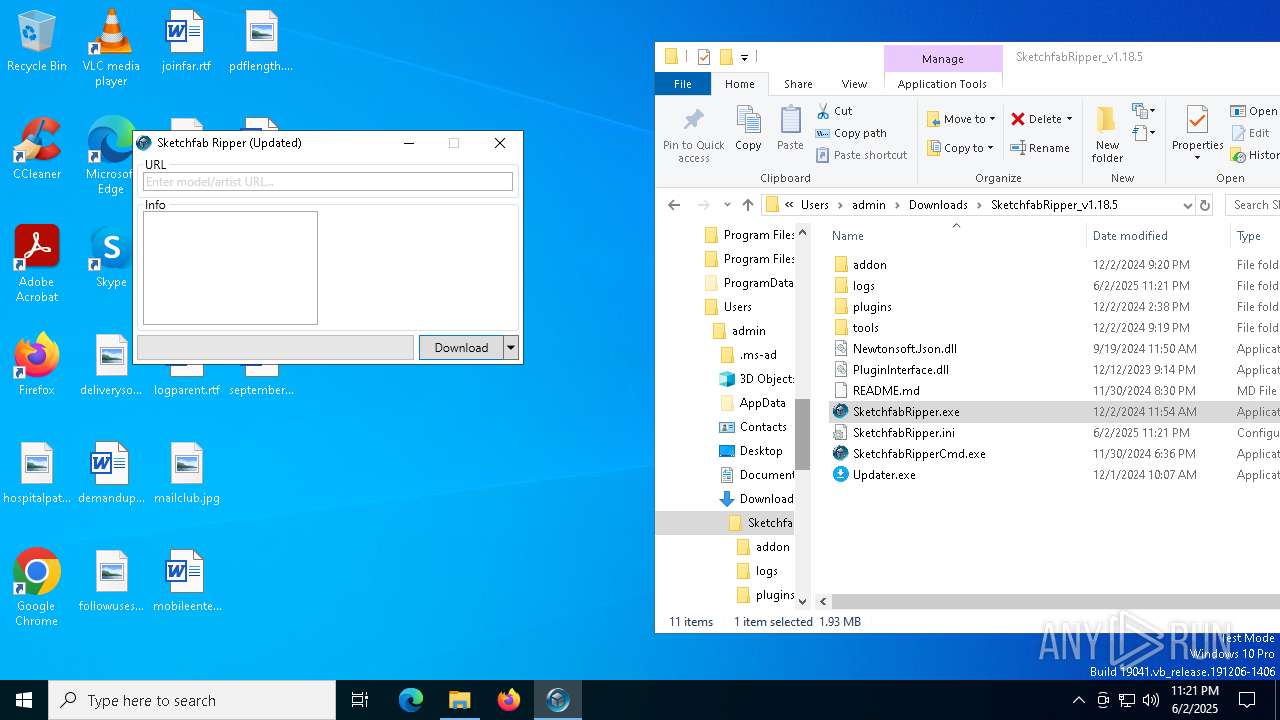
Application launched itself
- unscrambler.exe (PID: 5384)
- sfConfigUpdater.exe (PID: 7152)
- unscrambler.exe (PID: 5504)
- unscrambler.exe (PID: 2552)
- unscrambler.exe (PID: 5348)
- unscrambler.exe (PID: 3768)
- unscrambler.exe (PID: 4244)
- unscrambler.exe (PID: 1600)
- unscrambler.exe (PID: 2108)
- unscrambler.exe (PID: 5720)
INFO
Reads Environment values
- identity_helper.exe (PID: 2656)
Checks supported languages
- identity_helper.exe (PID: 2656)
Reads the computer name
- identity_helper.exe (PID: 2656)
Application launched itself
- msedge.exe (PID: 7128)
- msedge.exe (PID: 7652)
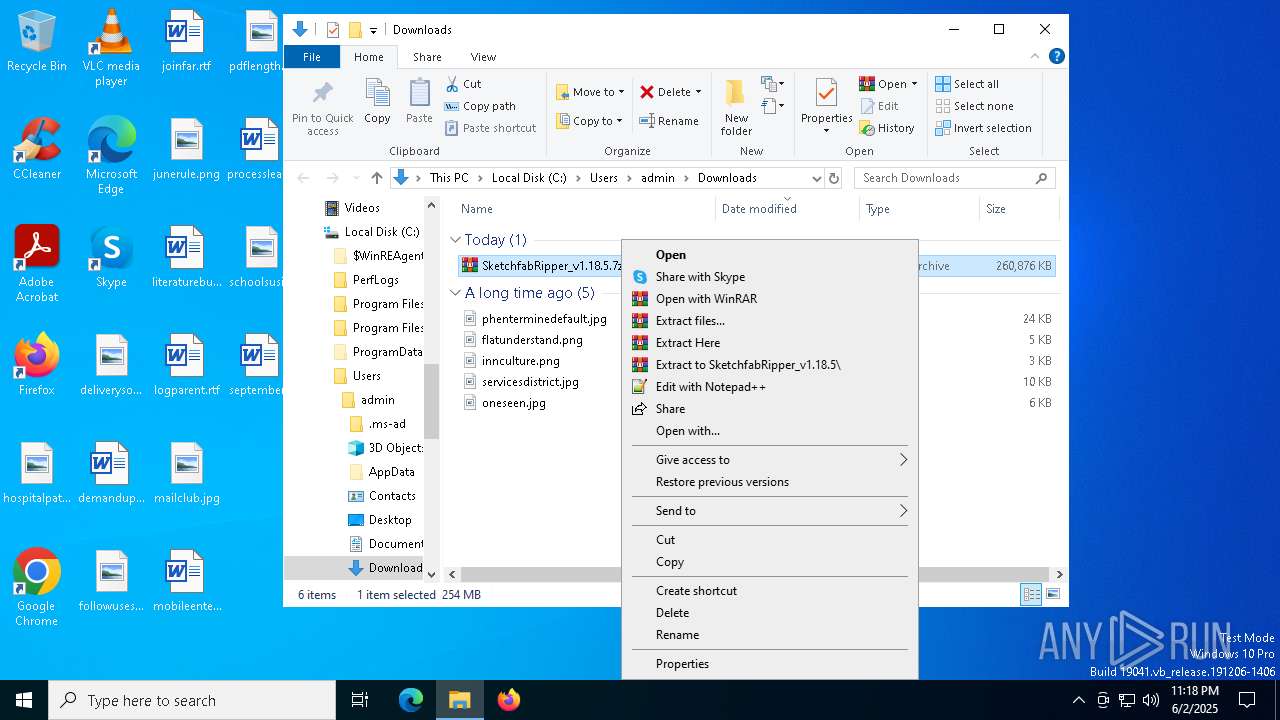
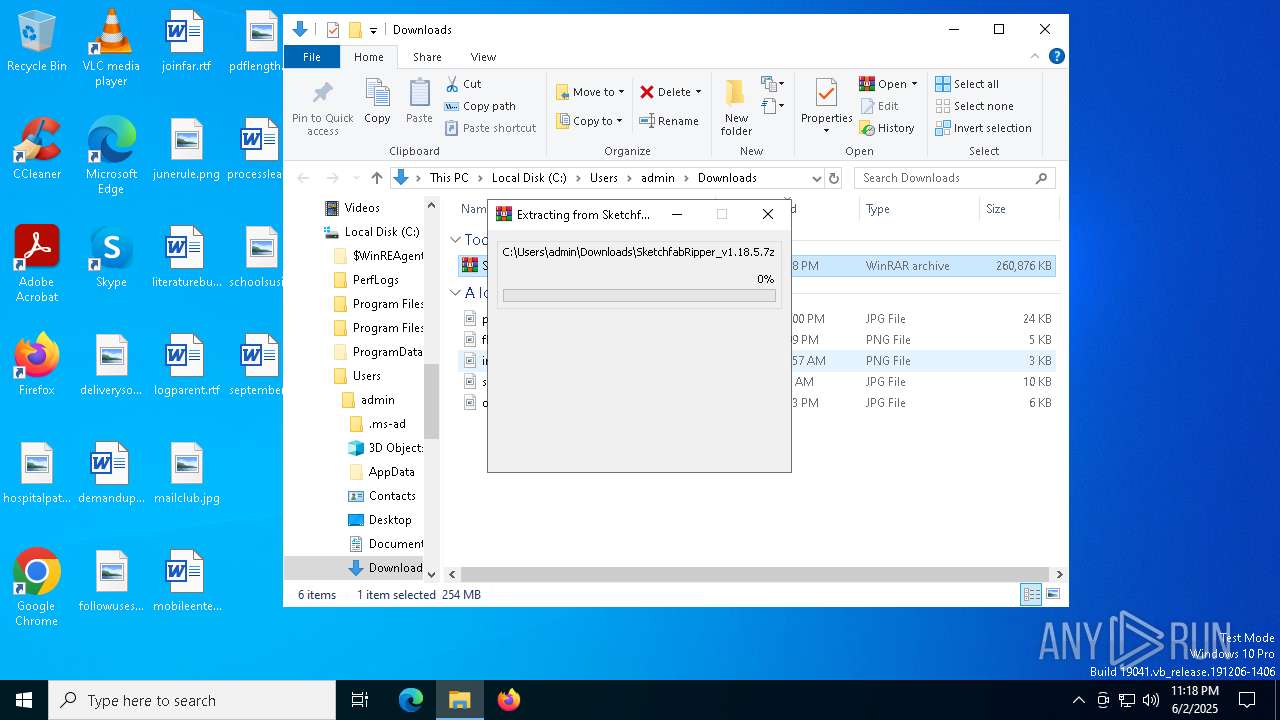
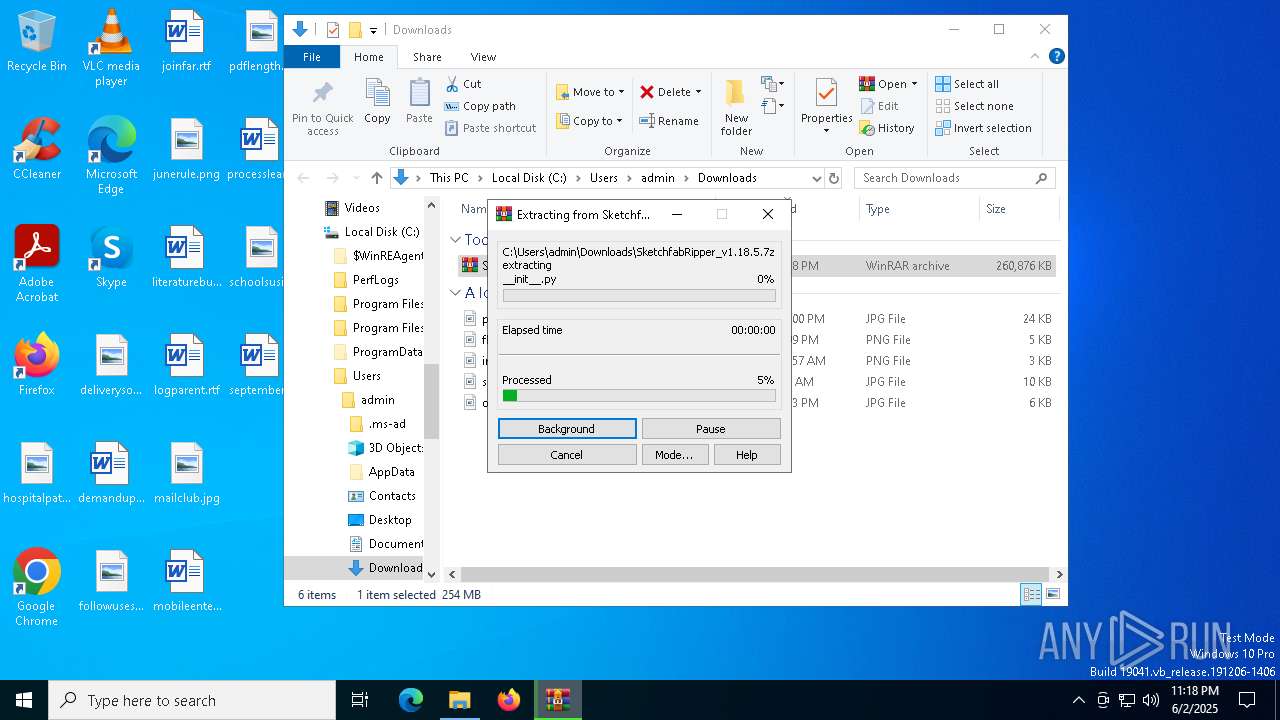
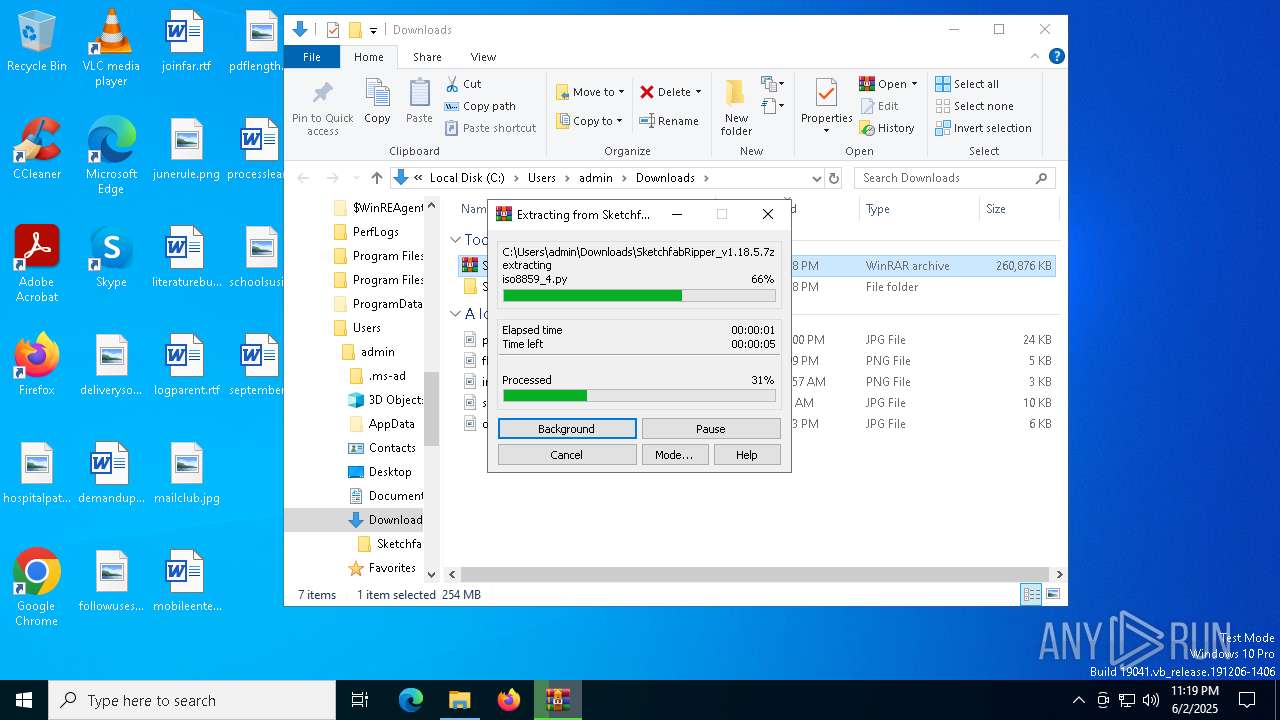
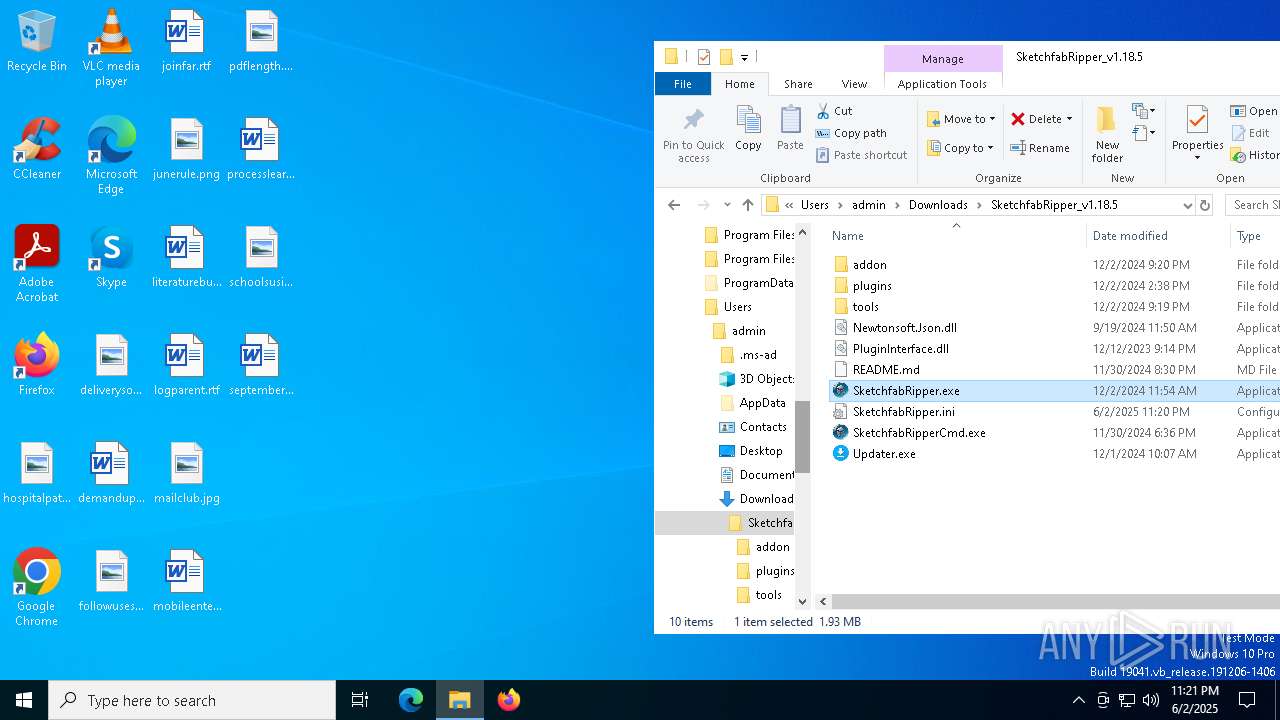
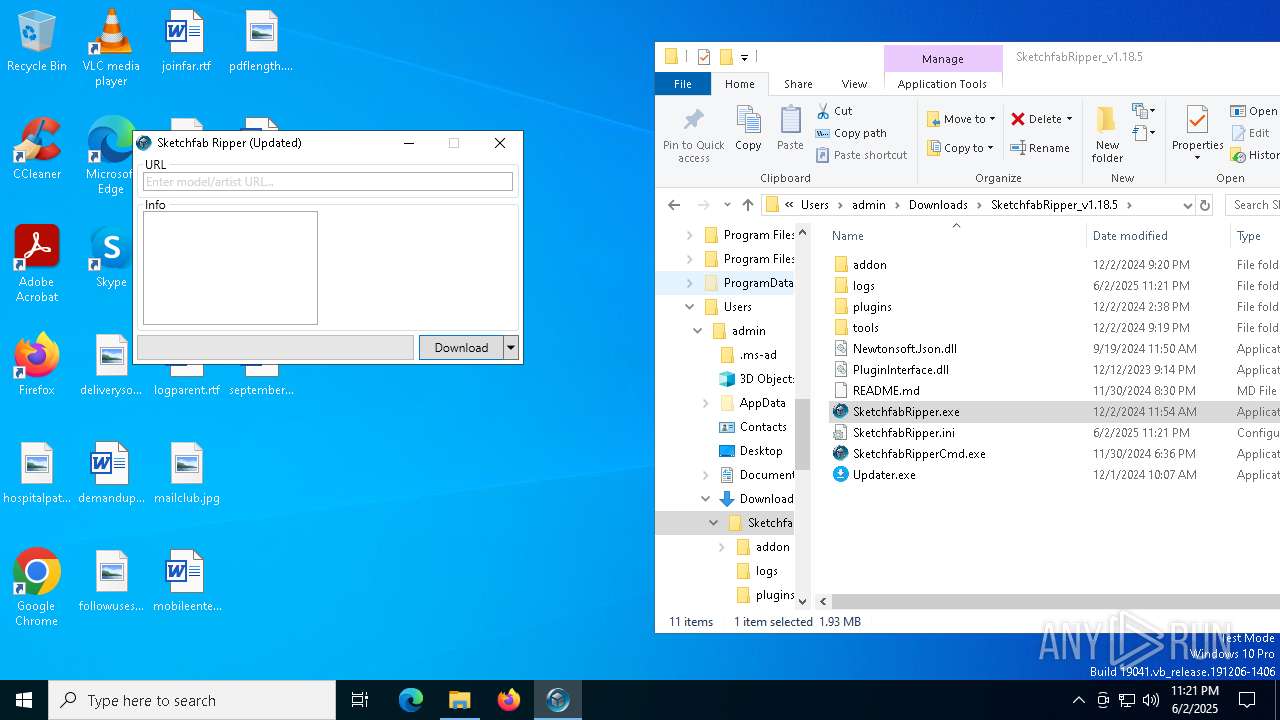
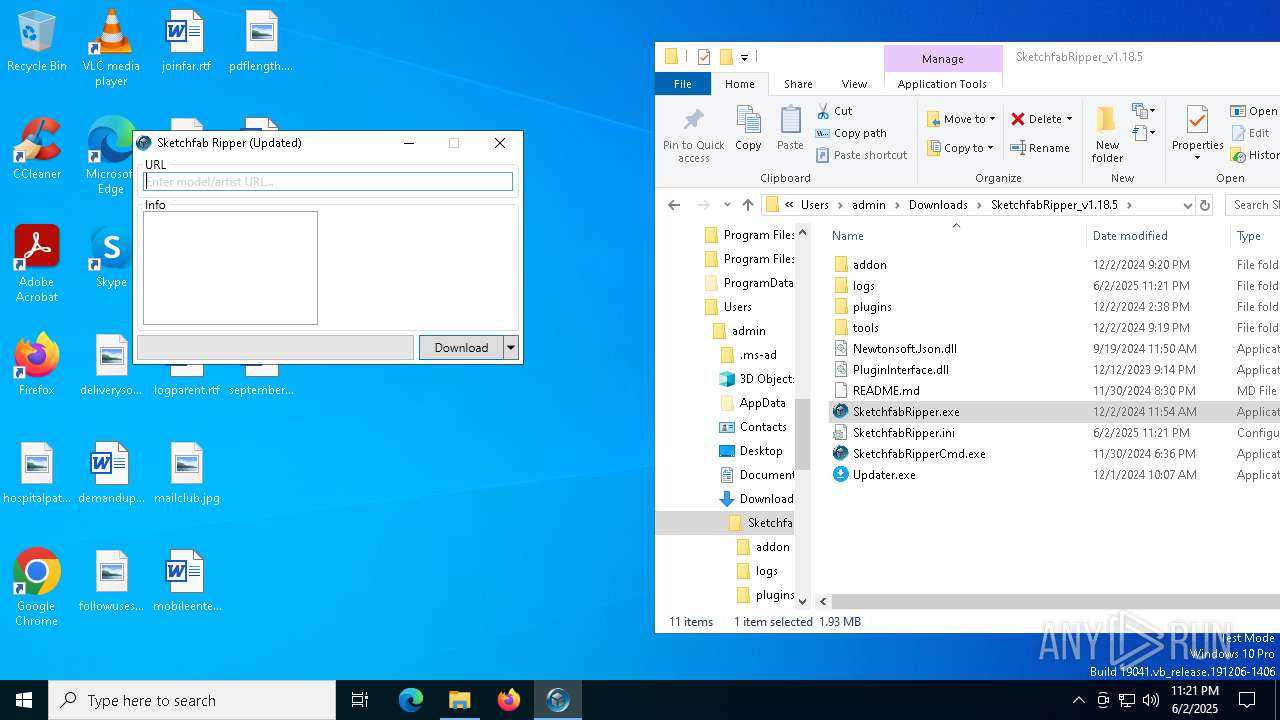
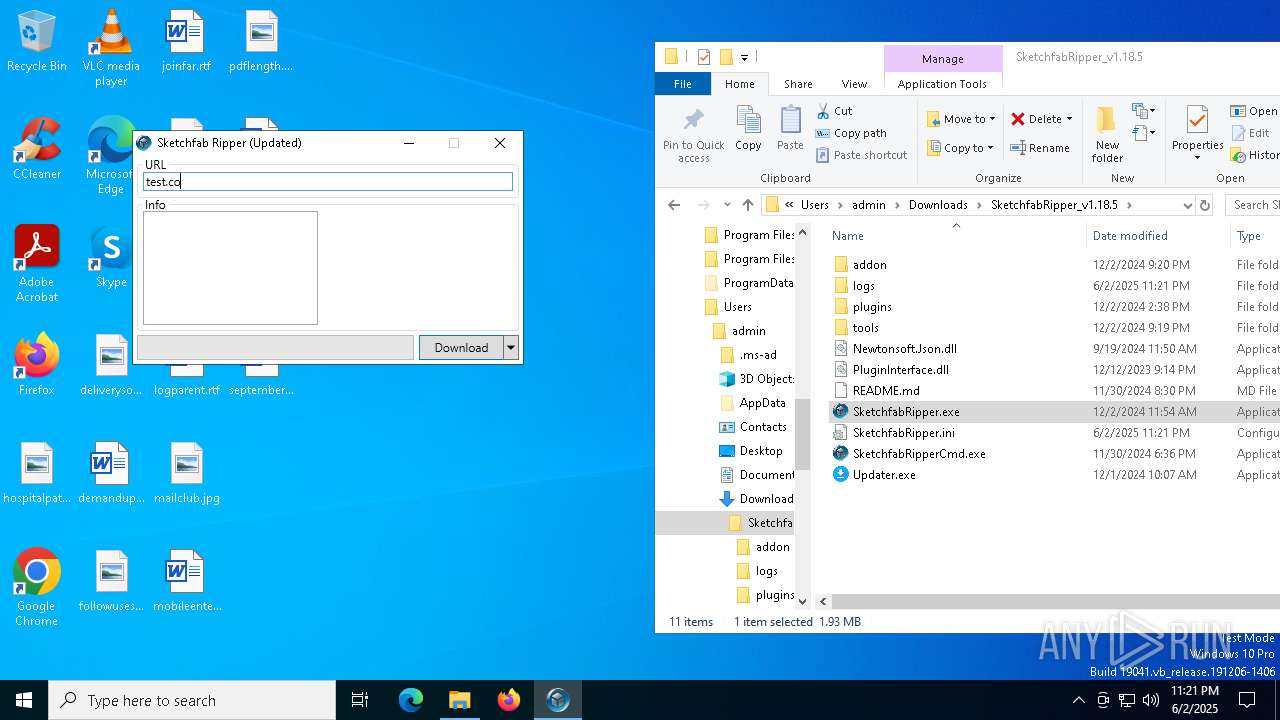
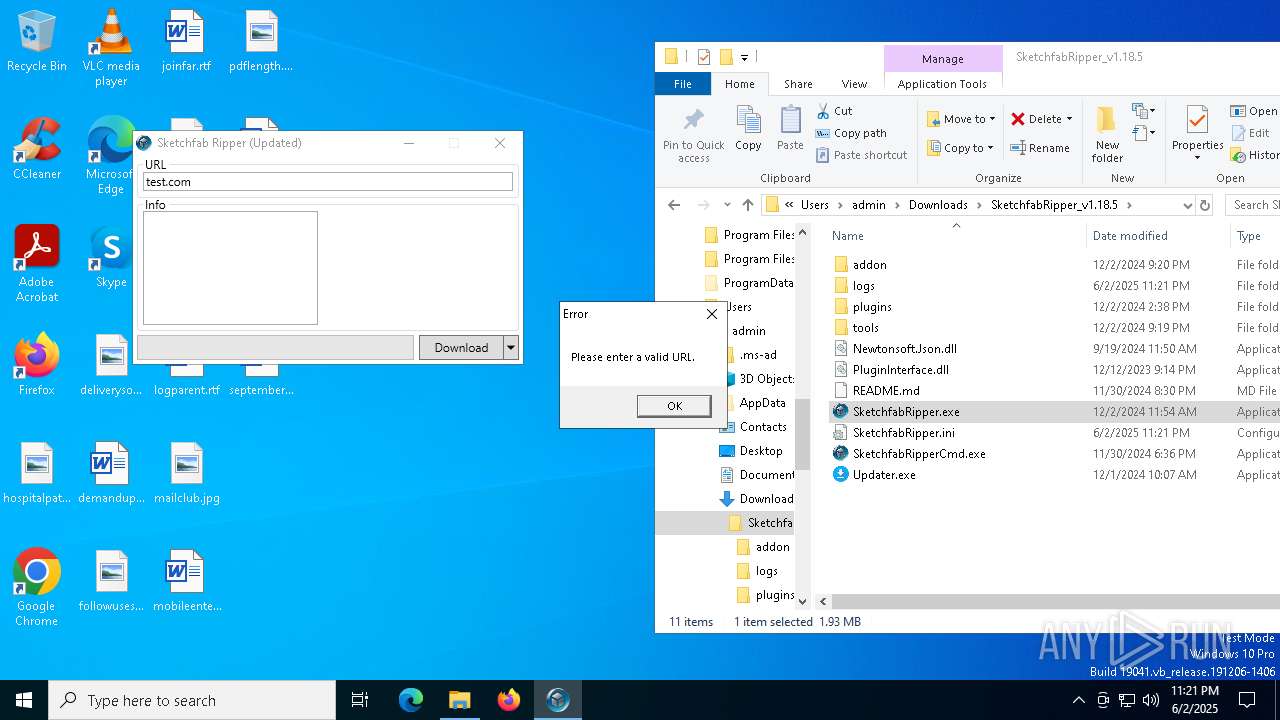
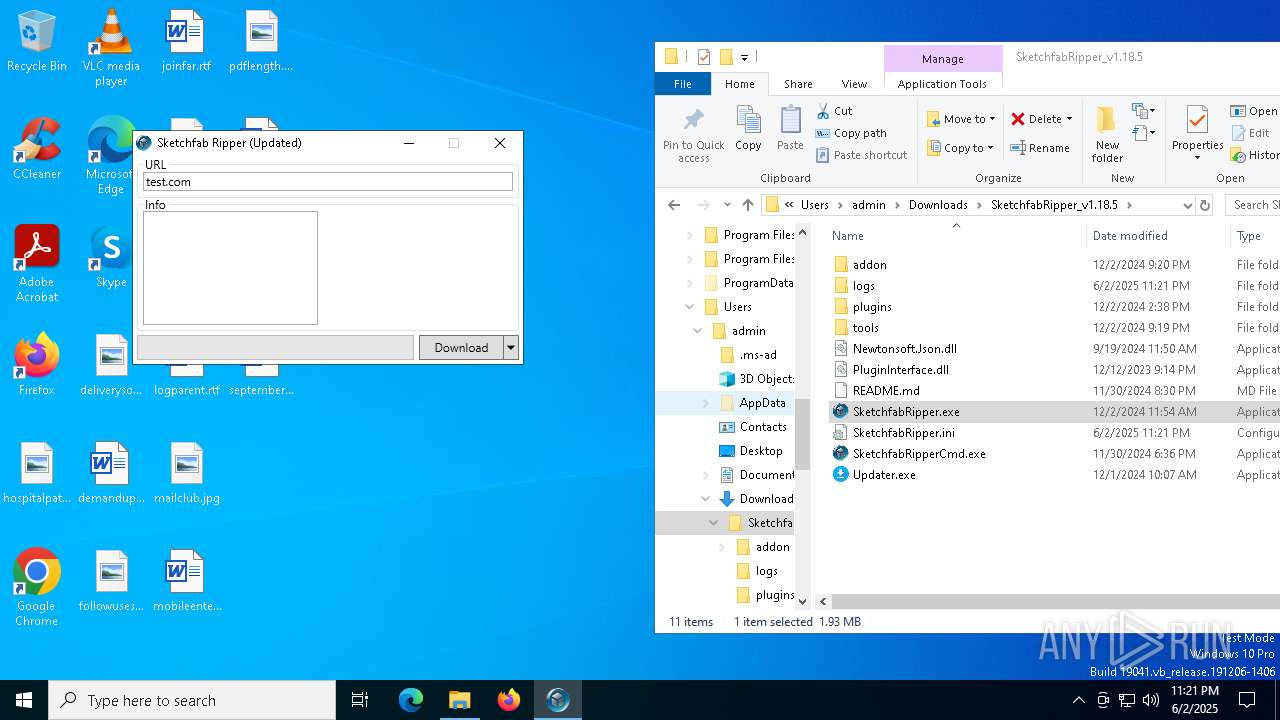
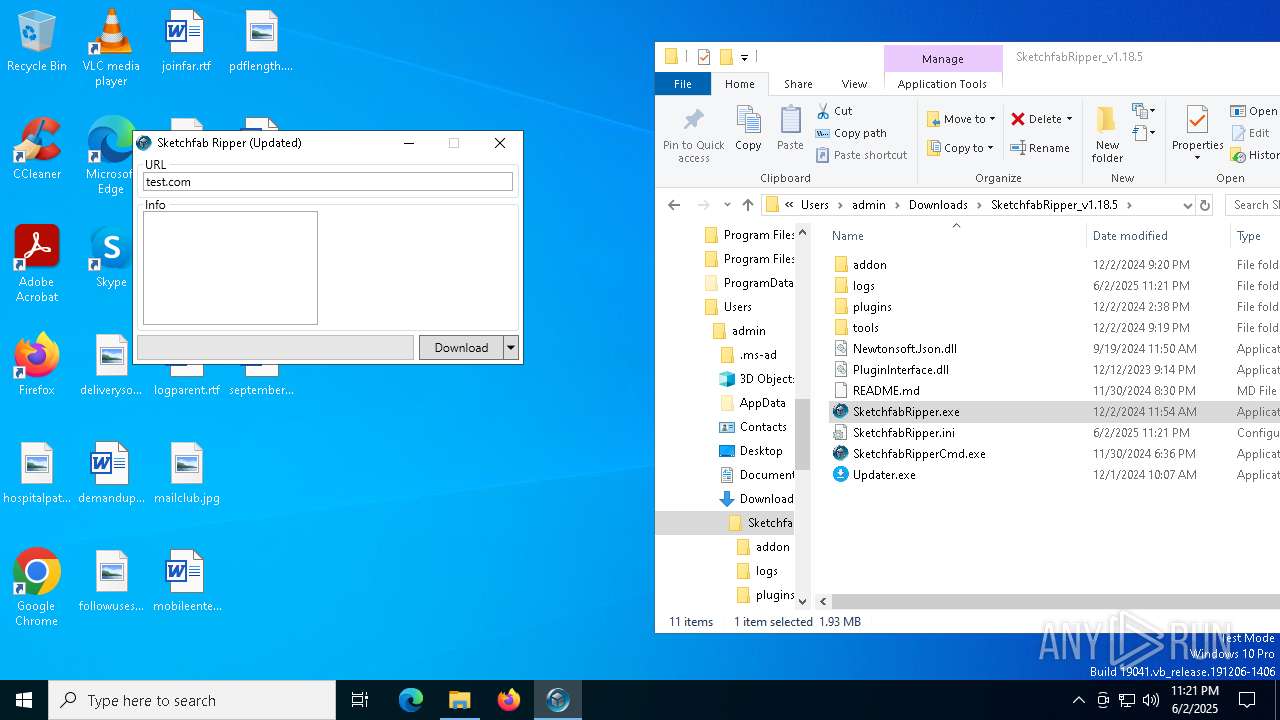
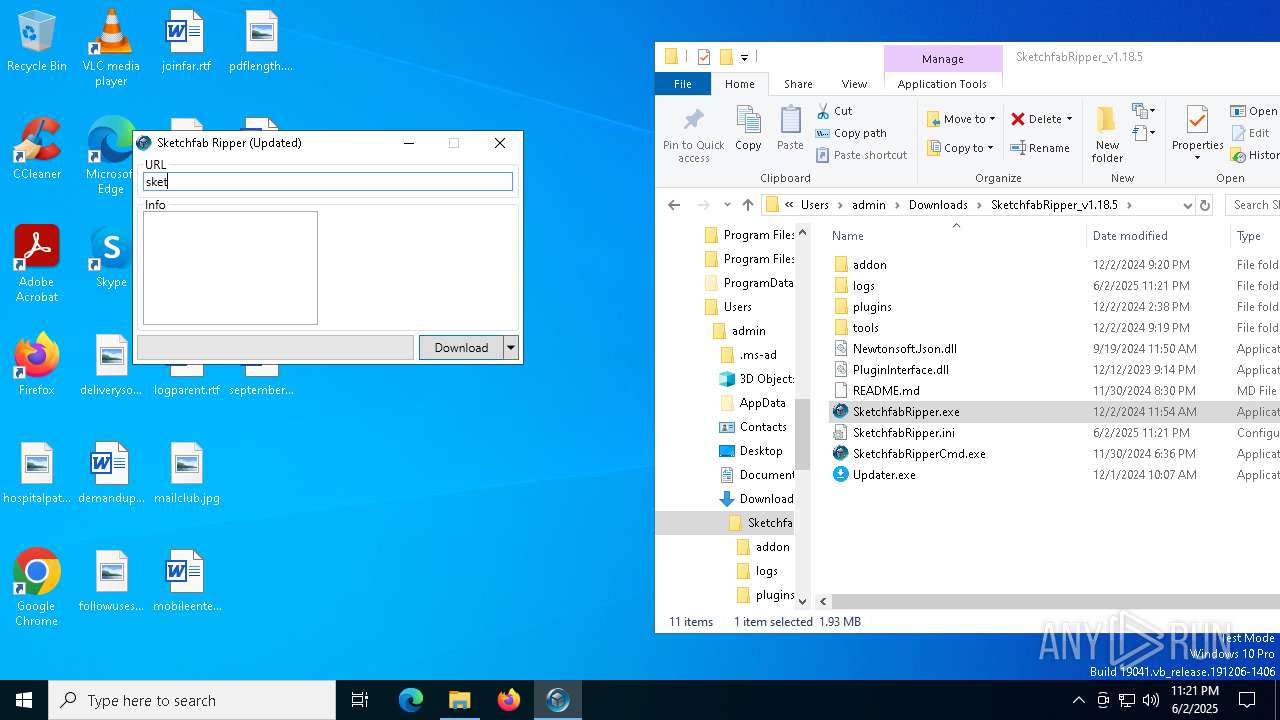
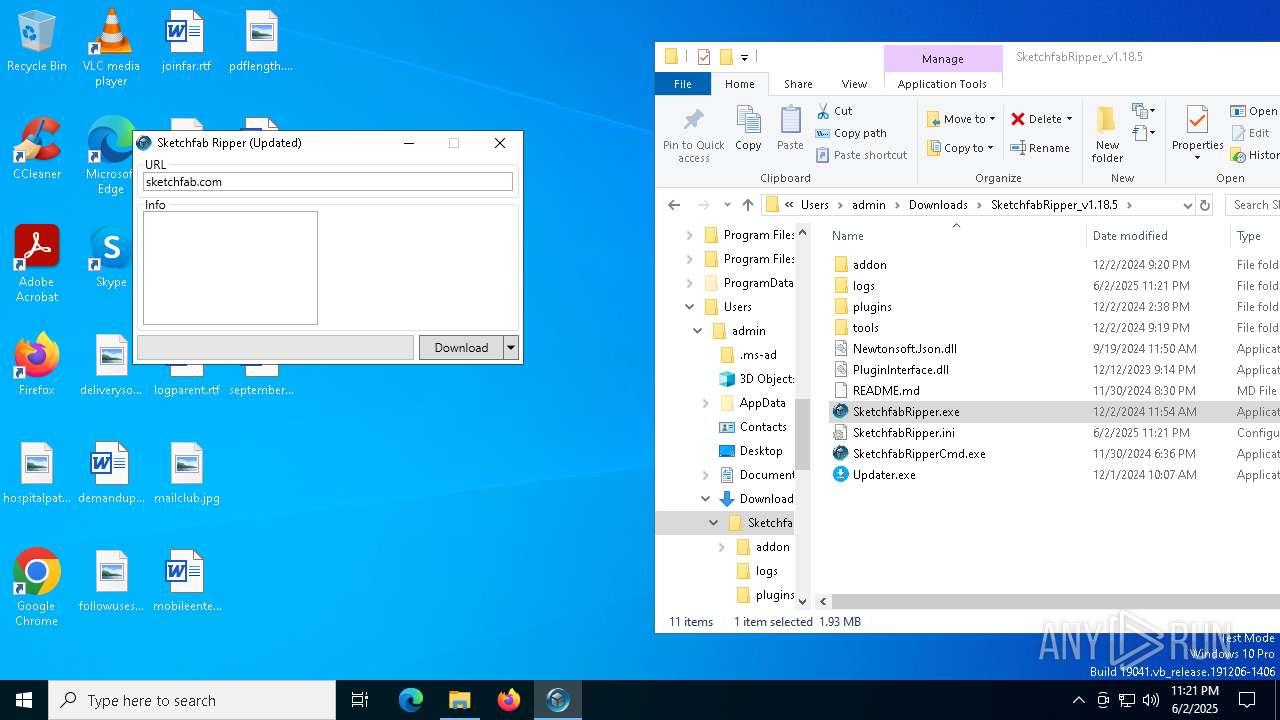
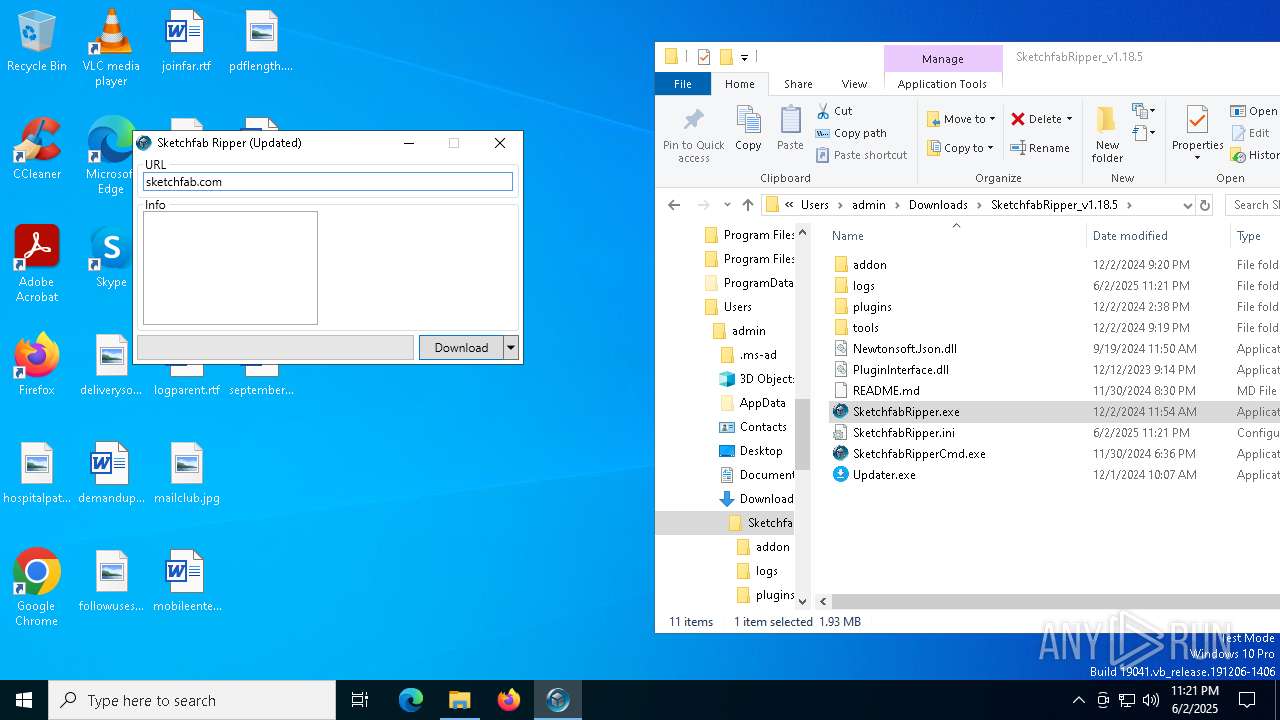
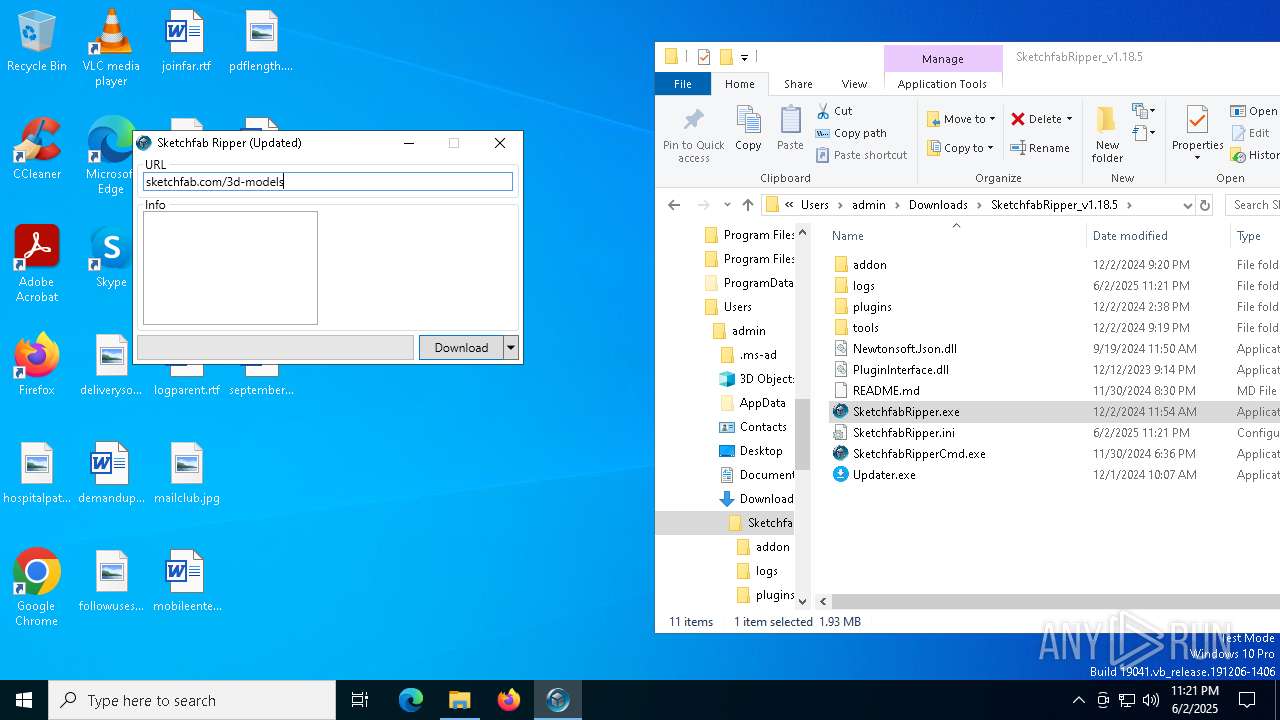
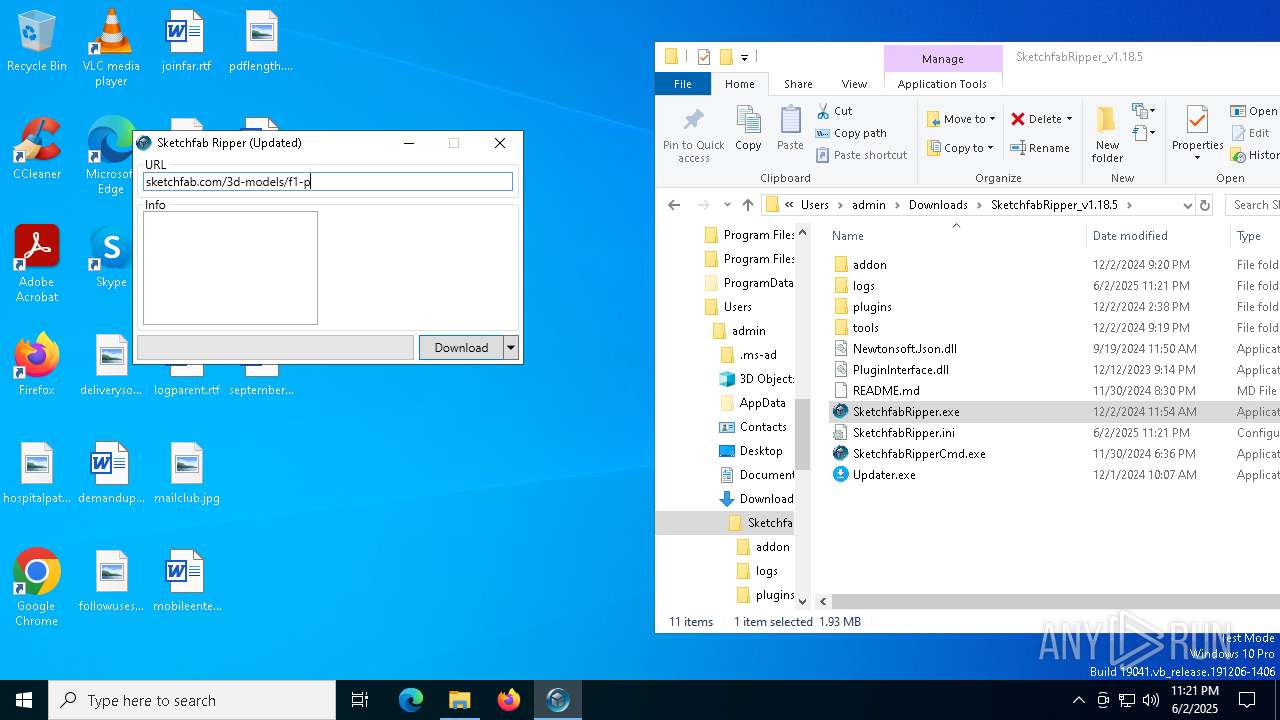
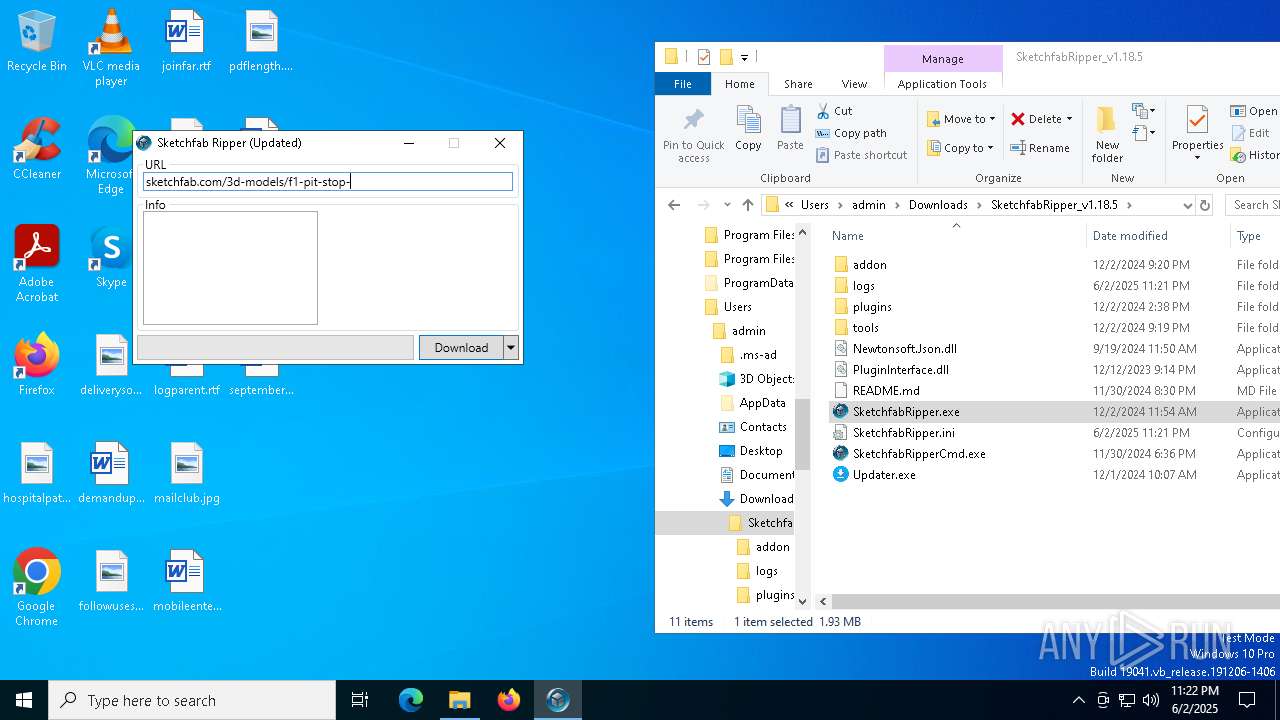
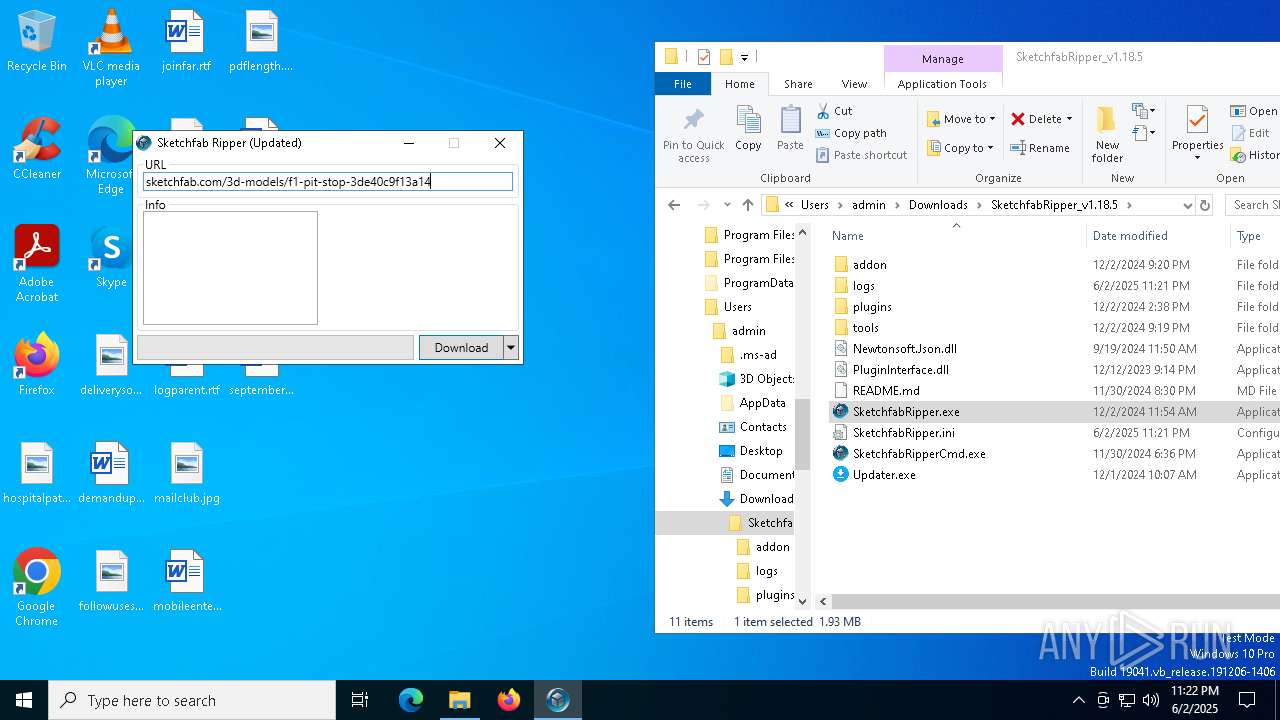
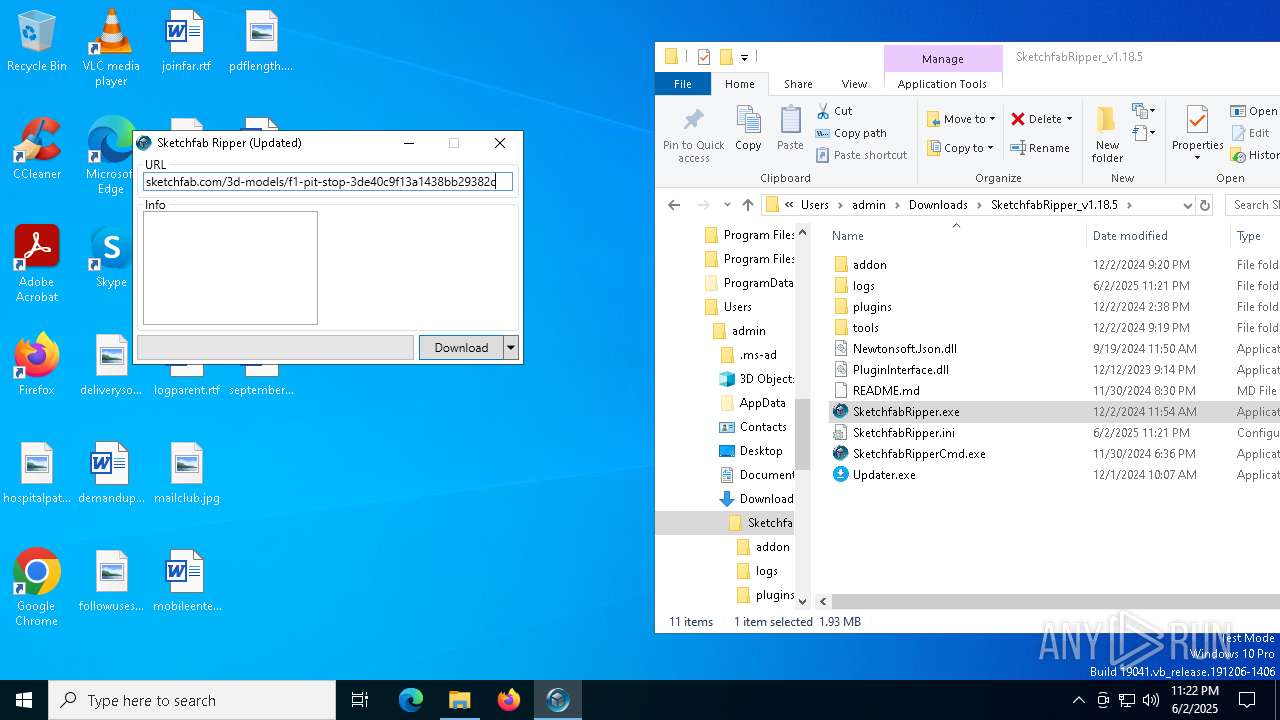
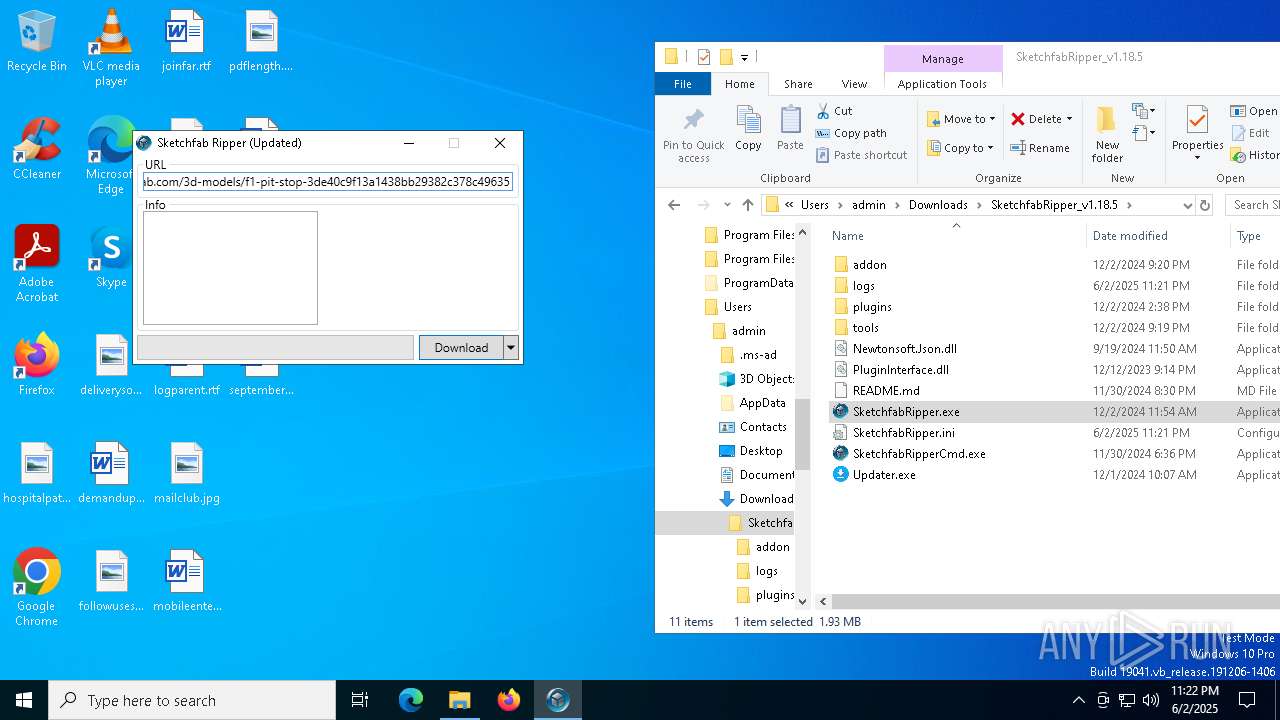
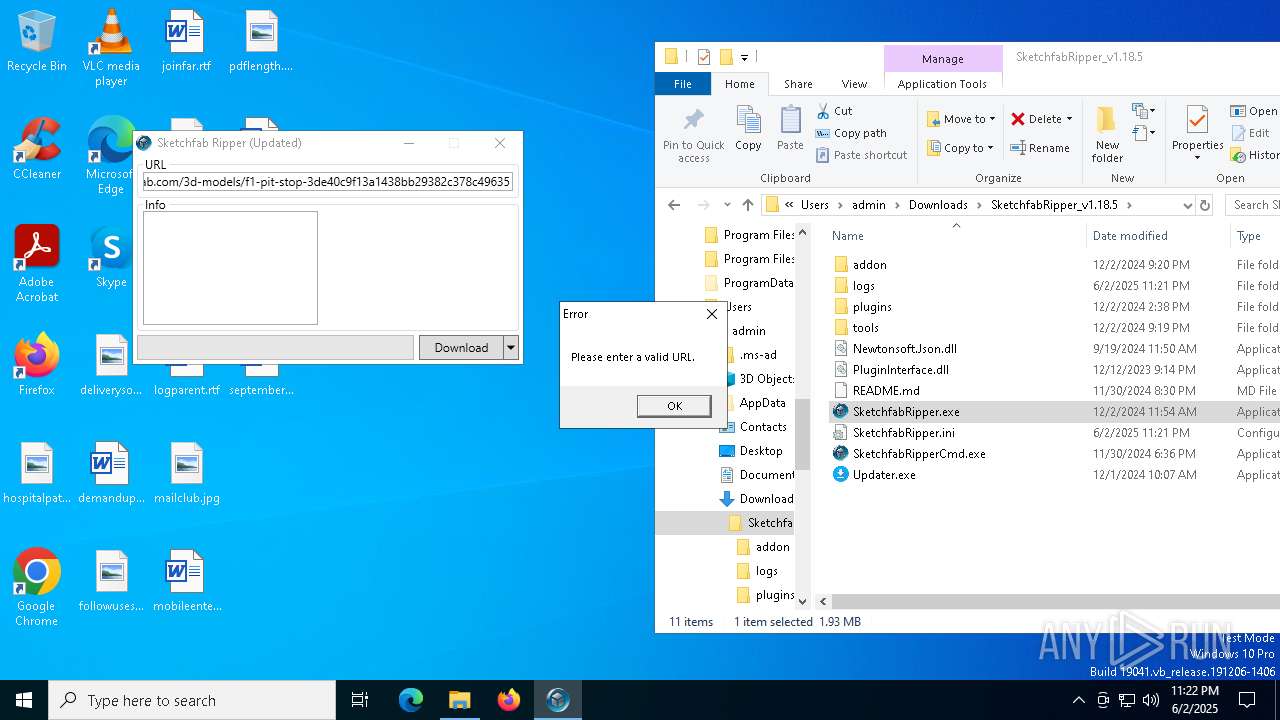
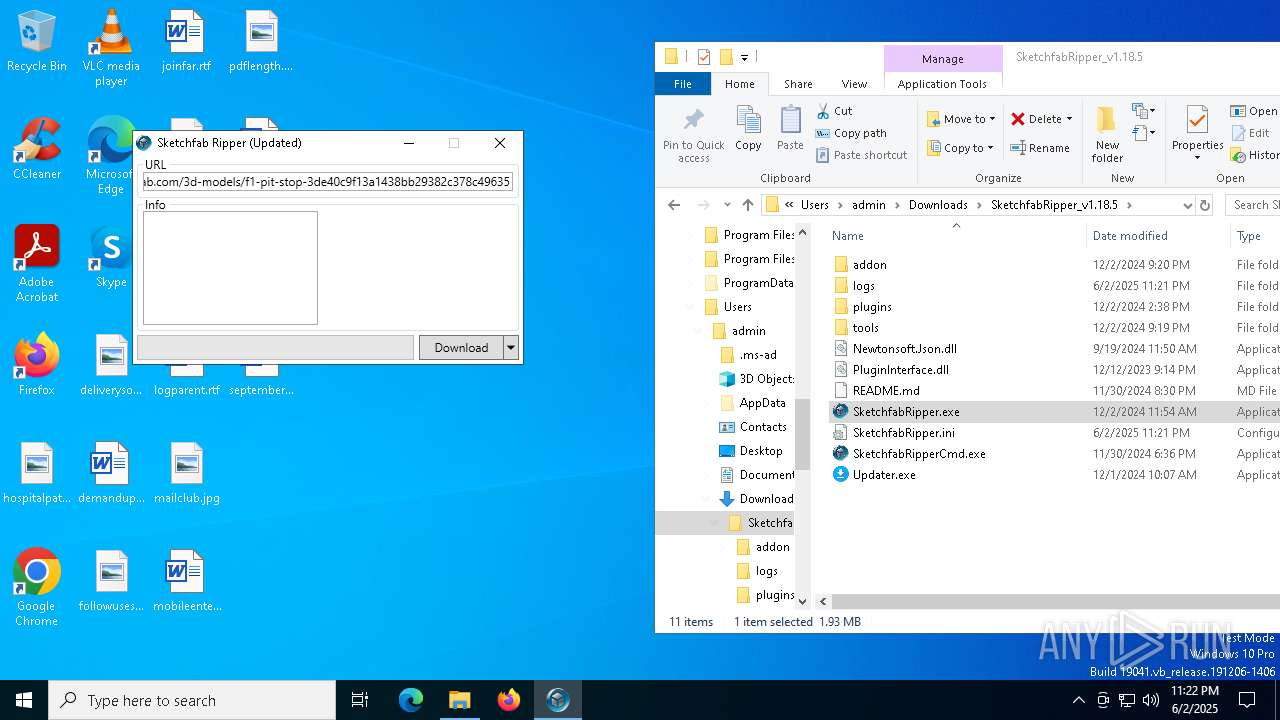
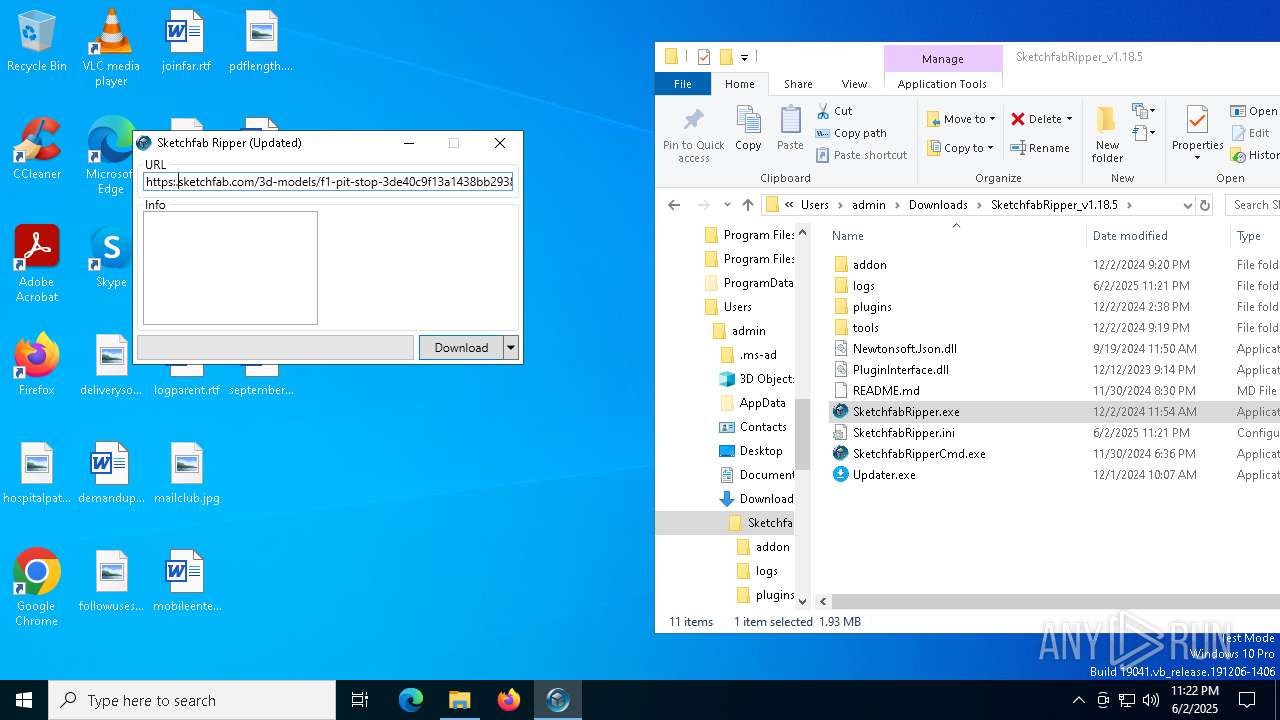
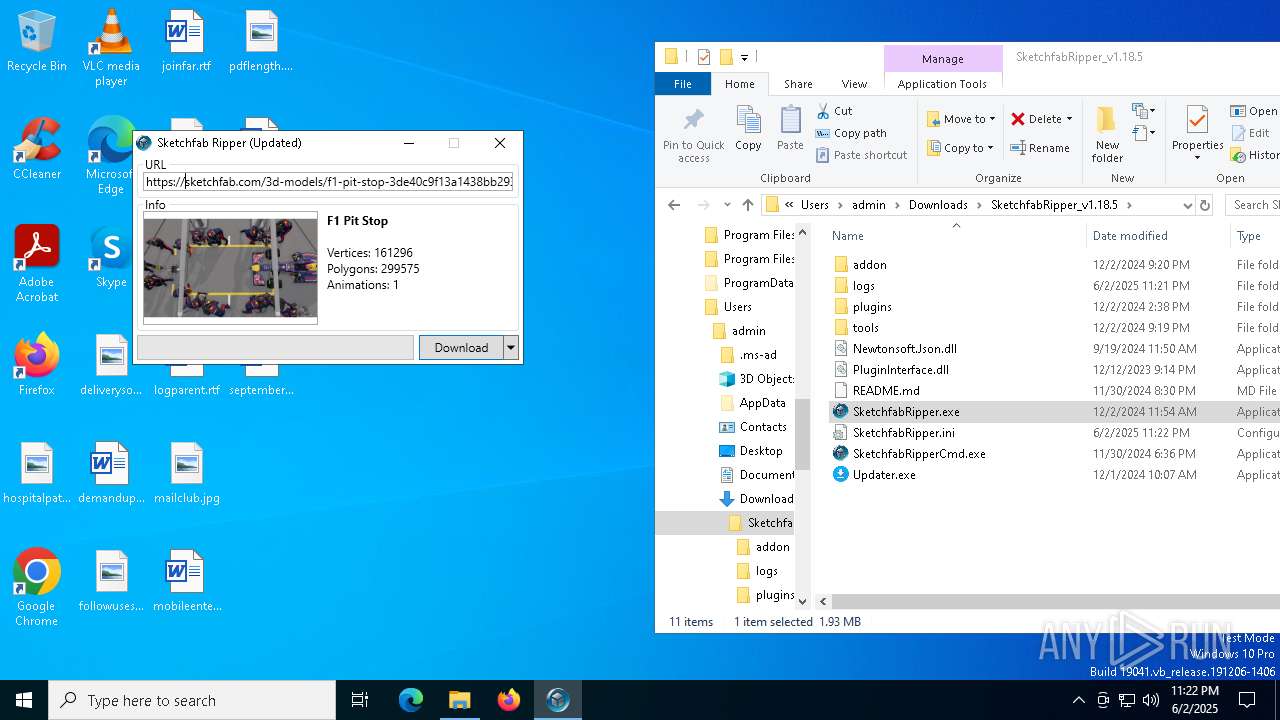
Manual execution by a user
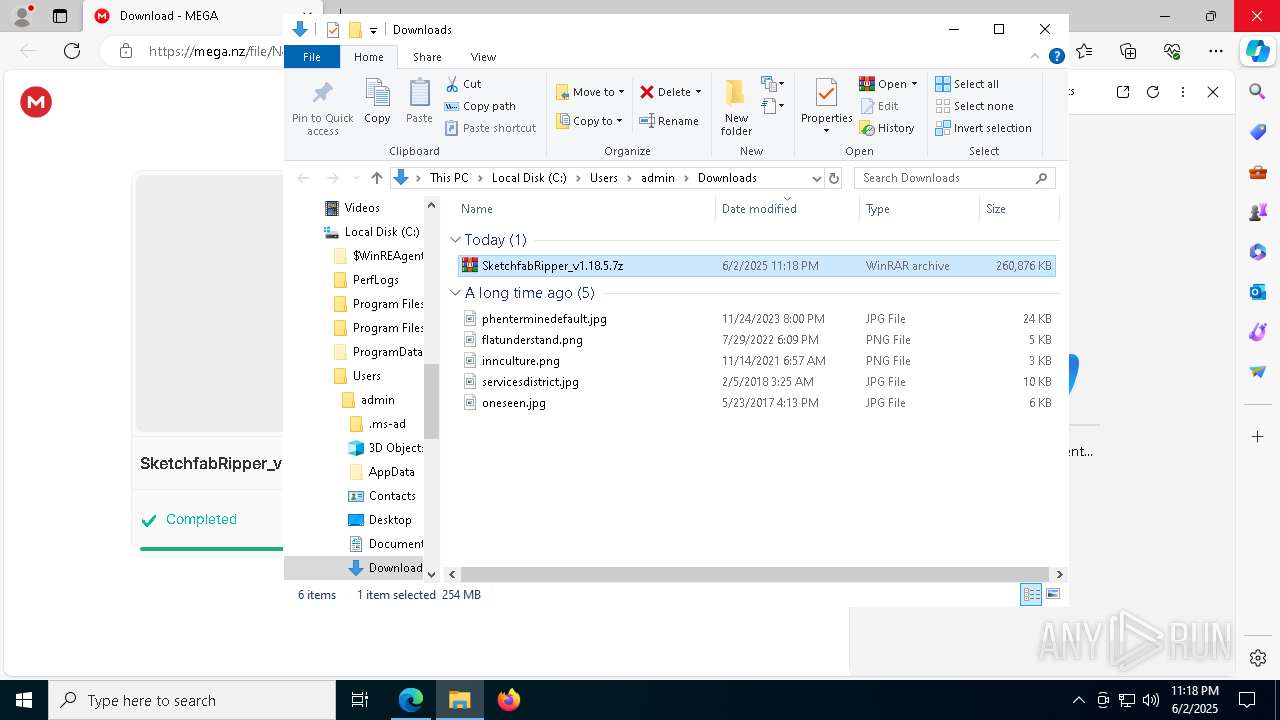
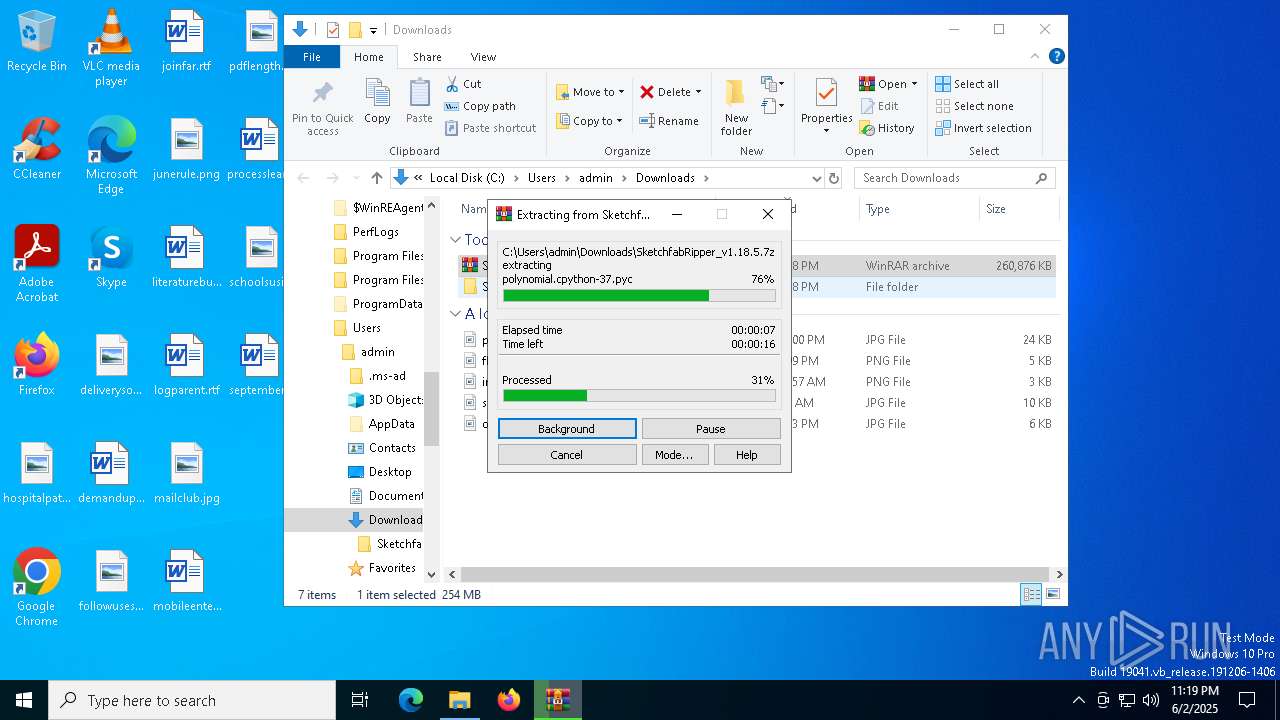
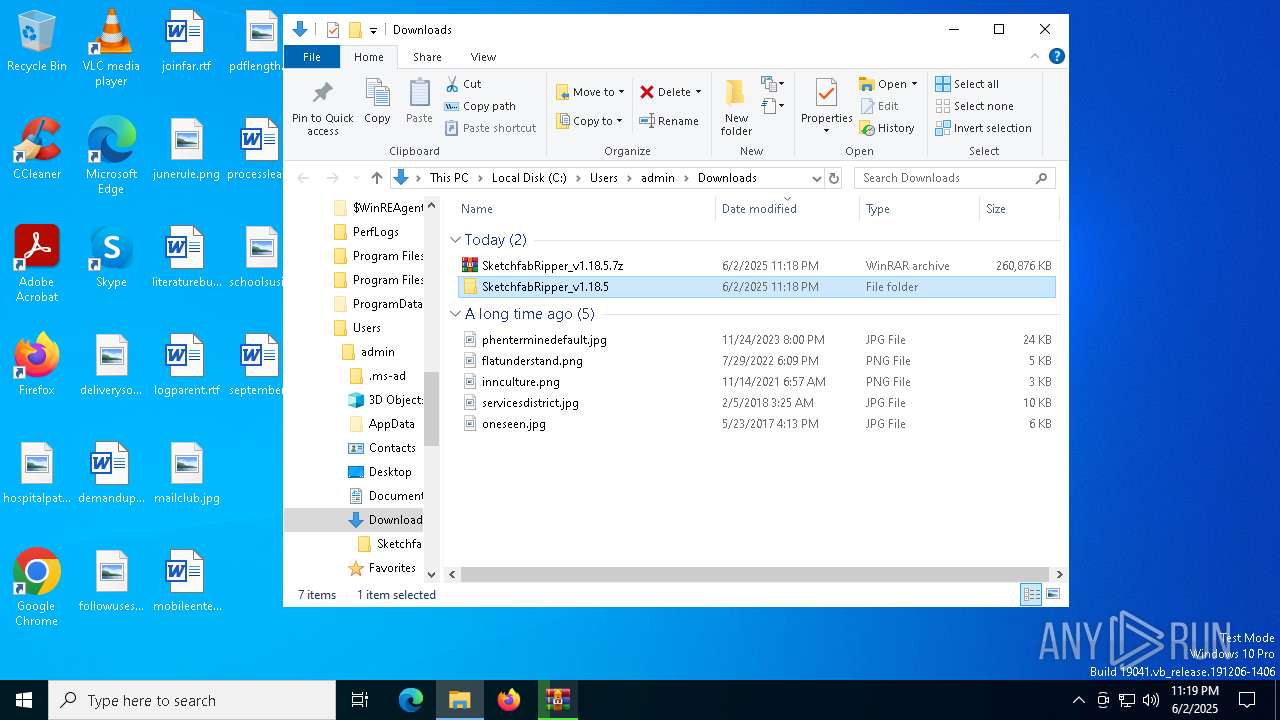
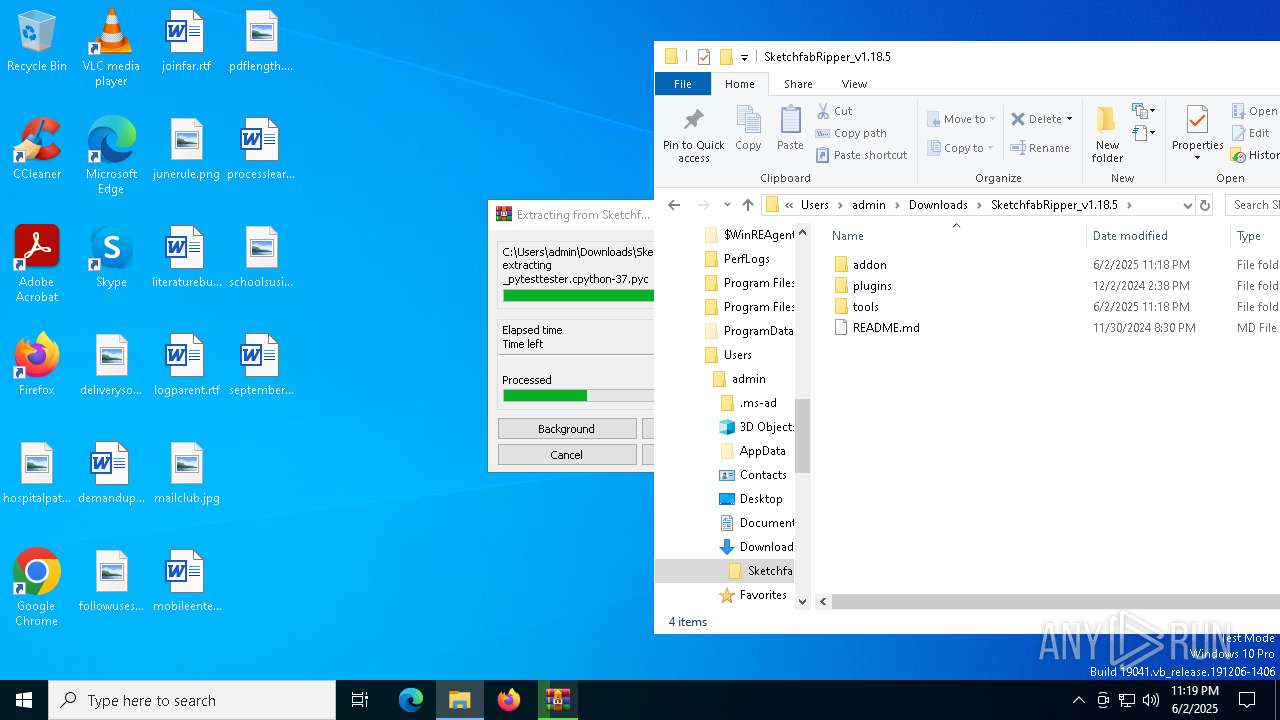
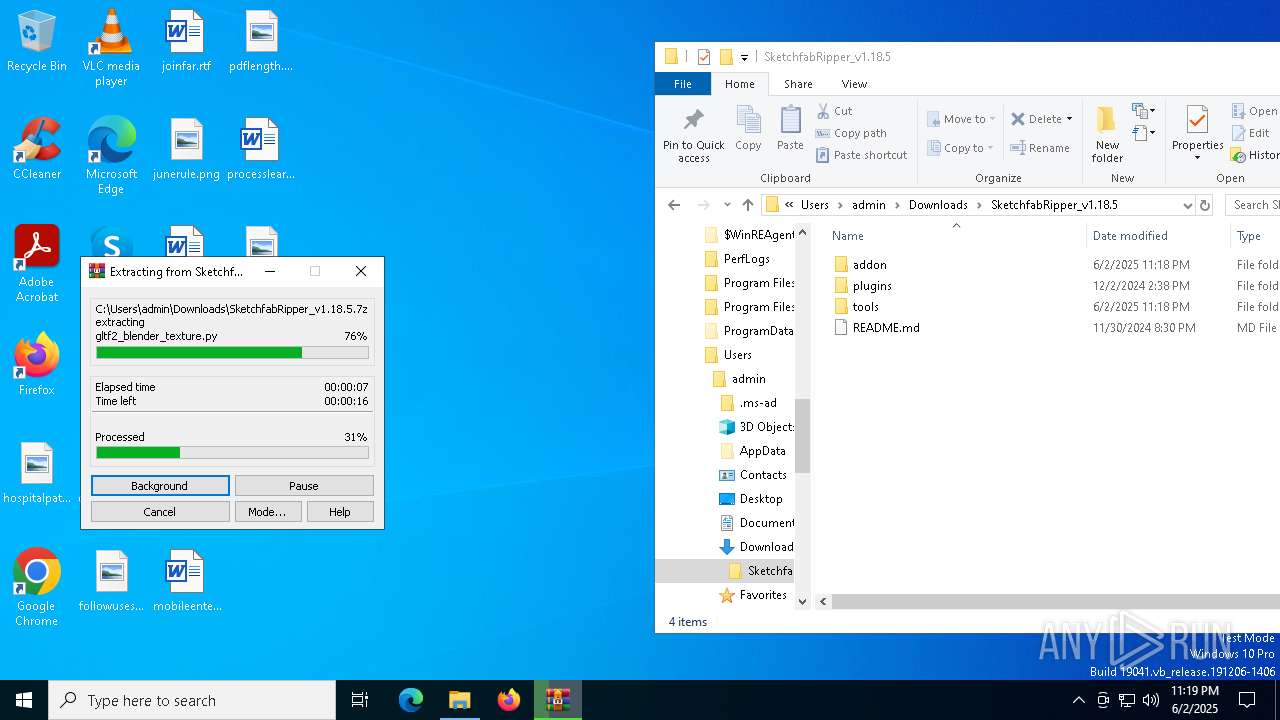
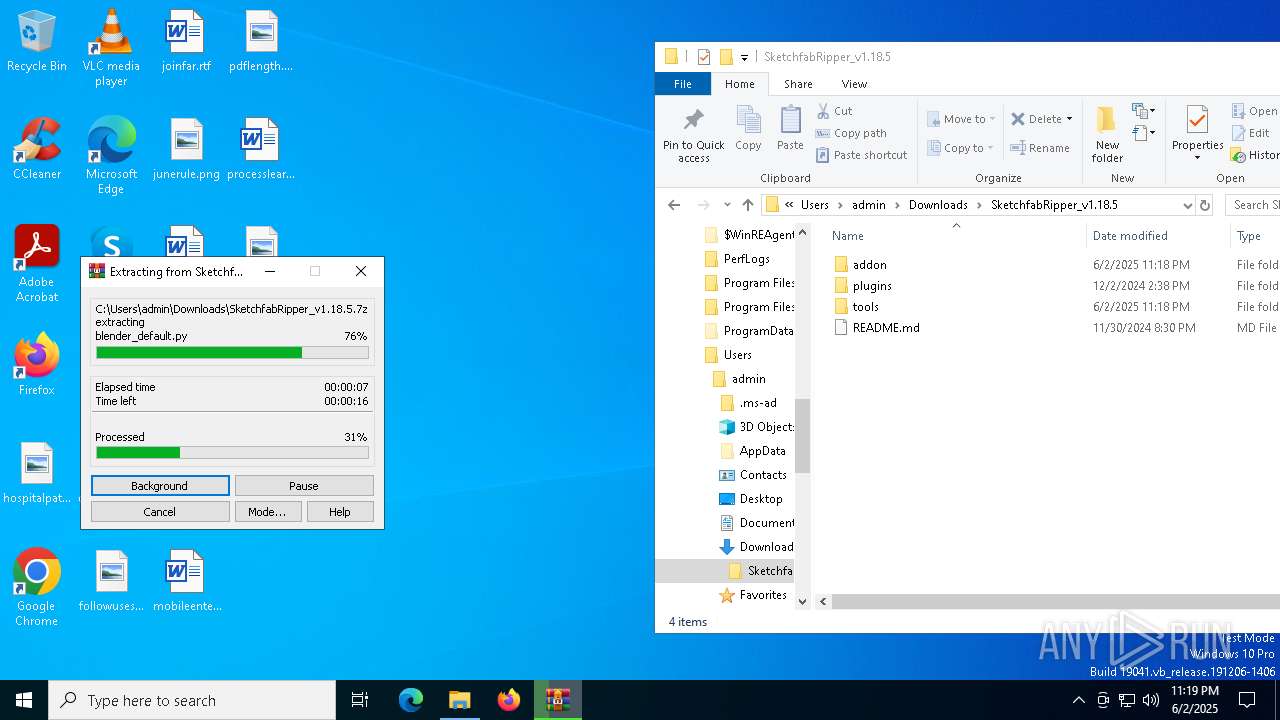
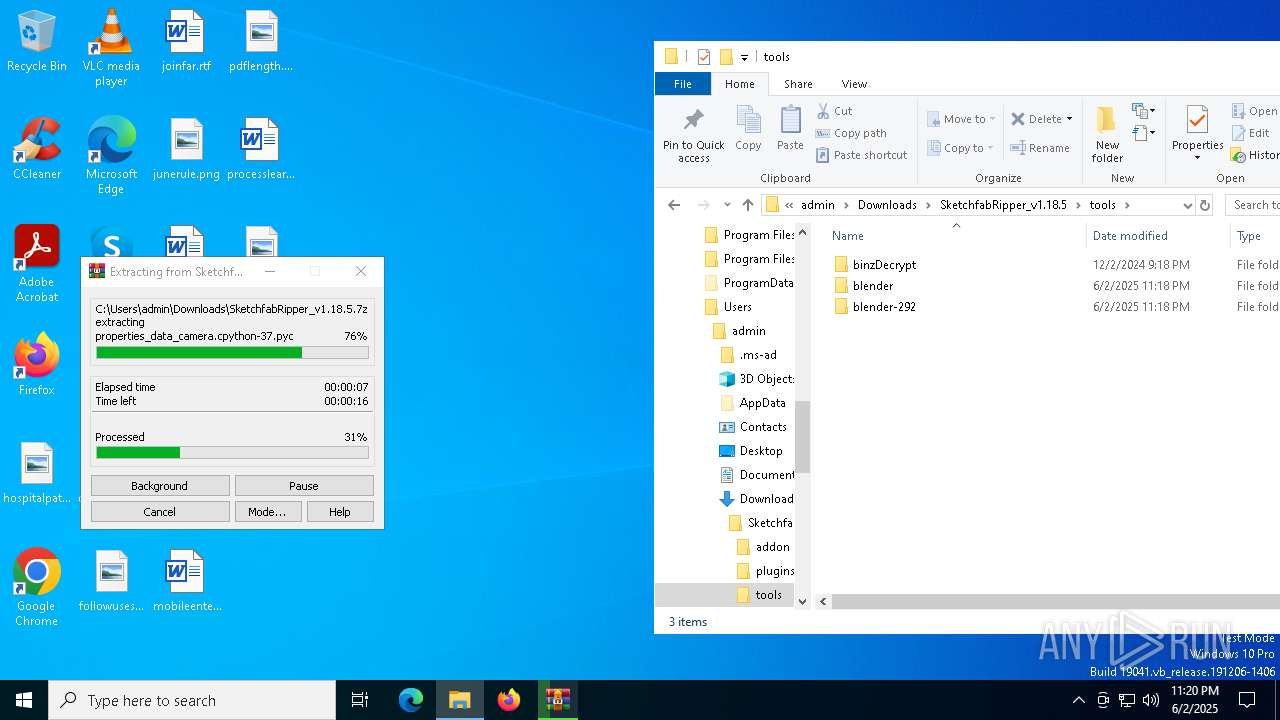
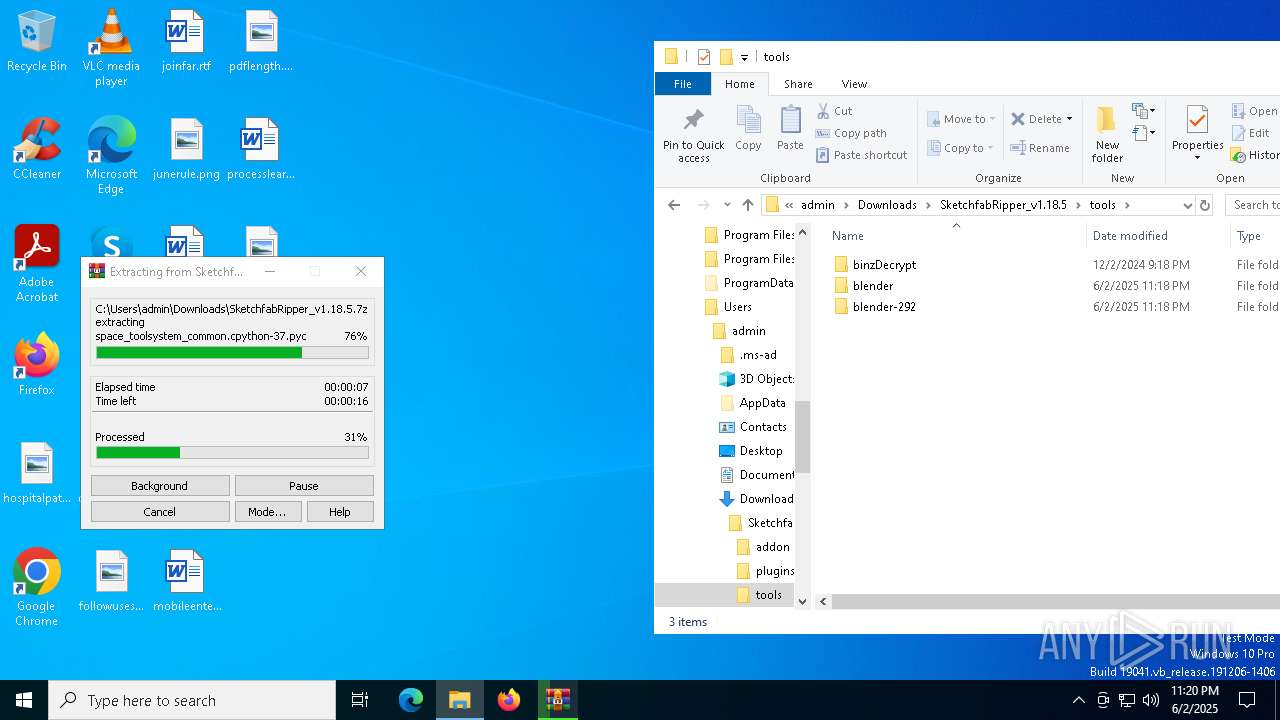
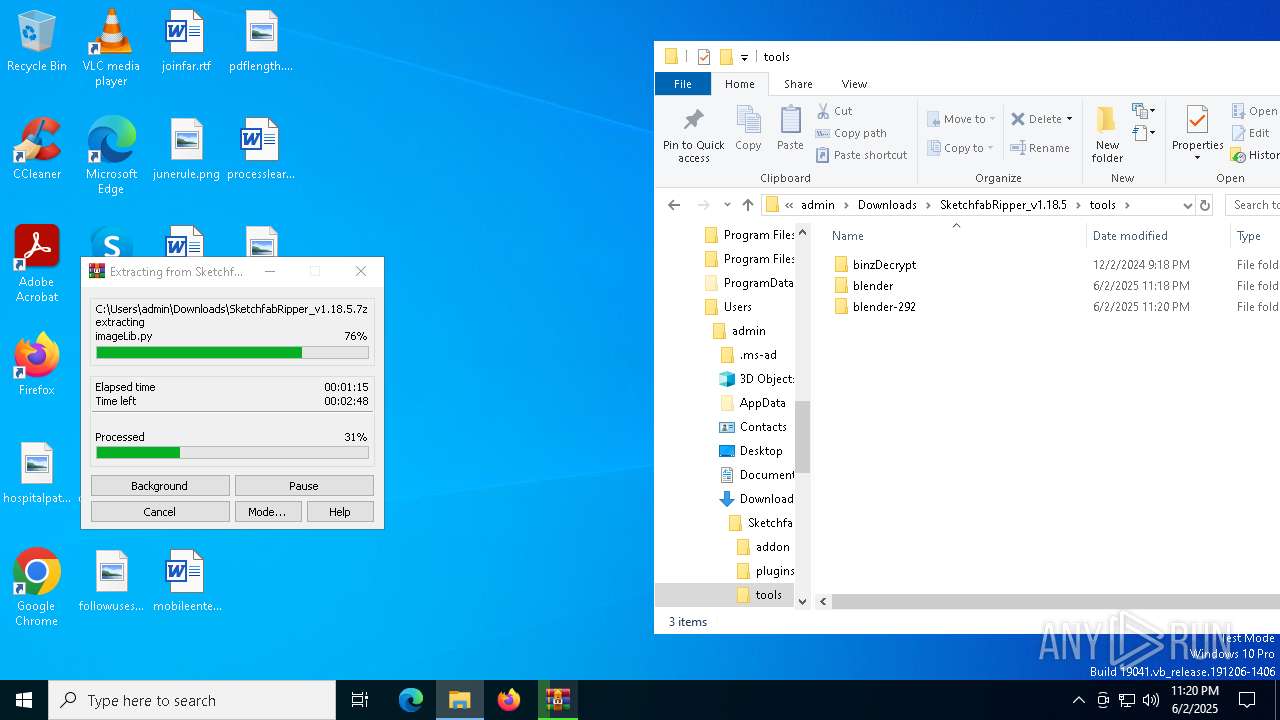
- WinRAR.exe (PID: 472)
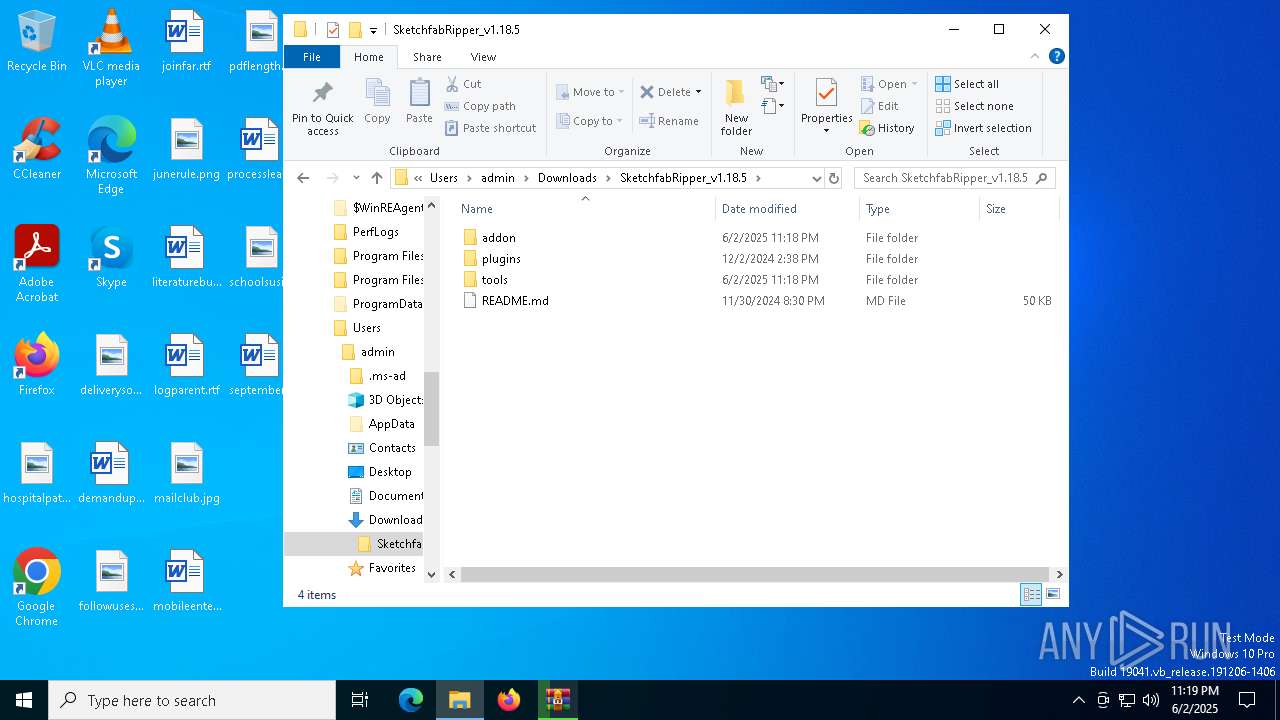
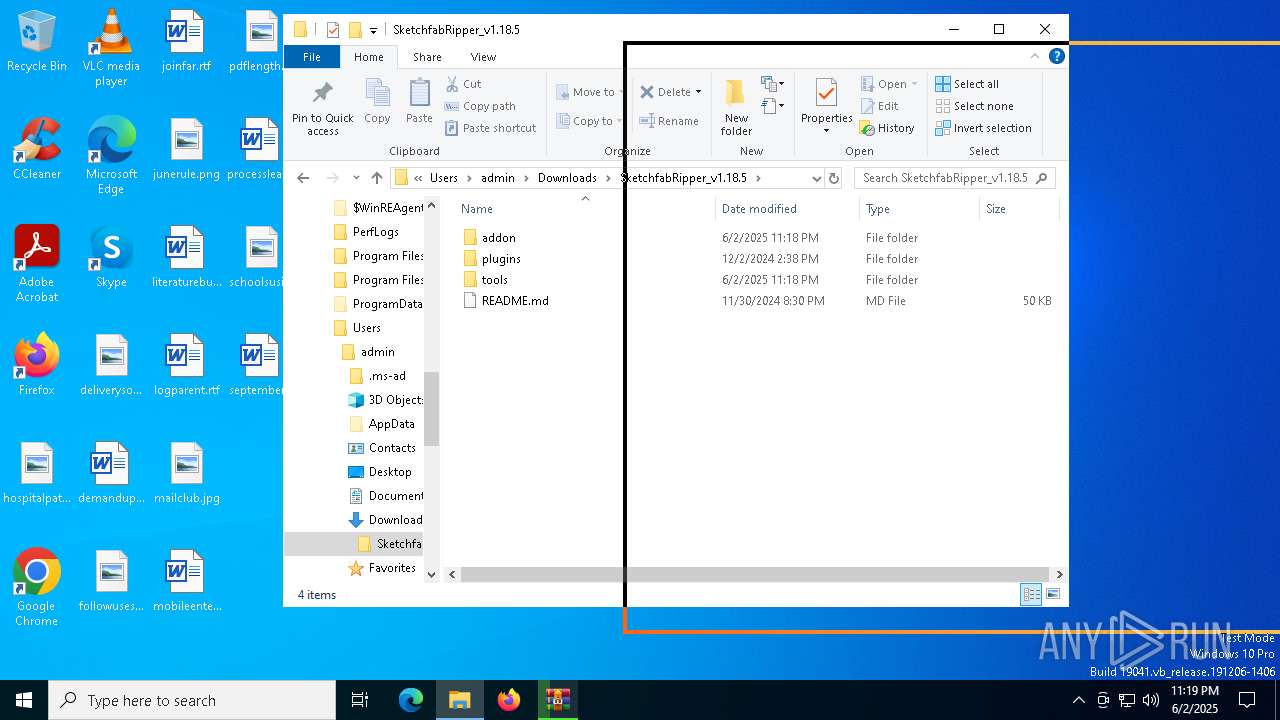
- SketchfabRipper.exe (PID: 1812)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 472)
- msedge.exe (PID: 6920)
The sample compiled with english language support
- WinRAR.exe (PID: 472)
- unscrambler.exe (PID: 5384)
- unscrambler.exe (PID: 2552)
- SketchfabRipper.exe (PID: 1812)
- msedge.exe (PID: 6920)
- unscrambler.exe (PID: 5348)
- unscrambler.exe (PID: 3768)
- unscrambler.exe (PID: 5504)
- ImageMagick-7.1.1-41-Q16-HDRI-x64-dll.tmp (PID: 3784)
- unscrambler.exe (PID: 4244)
- unscrambler.exe (PID: 1600)
- unscrambler.exe (PID: 5720)
- unscrambler.exe (PID: 2108)
- unscrambler.exe (PID: 8020)
UPX packer has been detected
- SketchfabRipper.exe (PID: 1812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
286
Monitored processes
153
Malicious processes
12
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Users\admin\Downloads\SketchfabRipper_v1.18.5\tools\identify.exe" -format "%[type]" "C:\Users\admin\Downloads\SketchfabRipper_v1.18.5\tools\binzDecrypt\_tmp\e6303c1b-81e6-4a46-a79a-d9a919bb0f65\sil_tracksurface_rough_a_01_n.tga.png" | C:\Users\admin\Downloads\SketchfabRipper_v1.18.5\tools\identify.exe | — | SketchfabRipper.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225781 Modules
| |||||||||||||||
| 300 | "C:\Users\admin\Downloads\SketchfabRipper_v1.18.5\tools\convert.exe" "_tmp\e6303c1b-81e6-4a46-a79a-d9a919bb0f65\_fixed\Silverstone_whiteline_a_01_b_d.tga.png.png" -flip "_tmp\e6303c1b-81e6-4a46-a79a-d9a919bb0f65\_fixed\Silverstone_whiteline_a_01_b_d.tga.png.png" | C:\Users\admin\Downloads\SketchfabRipper_v1.18.5\tools\convert.exe | — | SketchfabRipper.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225781 Modules
| |||||||||||||||
| 444 | "C:\Users\admin\Downloads\SketchfabRipper_v1.18.5\tools\identify.exe" -format "%[type]" "C:\Users\admin\Downloads\SketchfabRipper_v1.18.5\tools\binzDecrypt\_tmp\e6303c1b-81e6-4a46-a79a-d9a919bb0f65\HELMET_METAL.tga.png" | C:\Users\admin\Downloads\SketchfabRipper_v1.18.5\tools\identify.exe | — | SketchfabRipper.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225781 Modules
| |||||||||||||||
| 448 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | identify.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5828 --field-trial-handle=2348,i,16651875772863543595,15431968020972242372,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 472 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\SketchfabRipper_v1.18.5.7z" C:\Users\admin\Downloads\SketchfabRipper_v1.18.5\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | convert.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 512 | "C:\Users\admin\Downloads\SketchfabRipper_v1.18.5\tools\identify.exe" -format "%[type]" "C:\Users\admin\Downloads\SketchfabRipper_v1.18.5\tools\binzDecrypt\_tmp\e6303c1b-81e6-4a46-a79a-d9a919bb0f65\garage_pit_decal_a_01_n.tga.png" | C:\Users\admin\Downloads\SketchfabRipper_v1.18.5\tools\identify.exe | — | SketchfabRipper.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225781 Modules
| |||||||||||||||
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5856 --field-trial-handle=2348,i,16651875772863543595,15431968020972242372,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | unscrambler.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 877
Read events
13 812
Write events
65
Delete events
0
Modification events
| (PID) Process: | (7128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7128) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 374E4E4335952F00 | |||
| (PID) Process: | (7128) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7370574335952F00 | |||
| (PID) Process: | (7128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\525106 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {186FB2A9-0DEA-44EE-A504-9FDA1837FEF8} | |||
| (PID) Process: | (7128) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F7BA7D4335952F00 | |||
| (PID) Process: | (7128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\525106 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {031C66D3-7069-4E8E-B089-107A912862F0} | |||
| (PID) Process: | (7128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\525106 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D5DAEF1E-89E7-4325-BE88-4E44452CF937} | |||
Executable files
962
Suspicious files
1 003
Text files
1 718
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF11f559.TMP | — | |
MD5:— | SHA256:— | |||
| 7128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF11f579.TMP | — | |
MD5:— | SHA256:— | |||
| 7128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF11f598.TMP | — | |
MD5:— | SHA256:— | |||
| 7128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11f598.TMP | — | |
MD5:— | SHA256:— | |||
| 7128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11f598.TMP | — | |
MD5:— | SHA256:— | |||
| 7128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF11f5b7.TMP | — | |
MD5:— | SHA256:— | |||
| 7128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
123
DNS requests
100
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7984 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7984 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6368 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1749039337&P2=404&P3=2&P4=NQB3Cr5ma39oAt%2br%2bX%2bNWdJLVPTQfIh3kSSTuJQdSEJZEIlPjAZ8ji9J9Rw7kEDf%2fXA4V%2fzg5AZcPdm0FbIQIg%3d%3d | unknown | — | — | whitelisted |
6368 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1749039337&P2=404&P3=2&P4=NQB3Cr5ma39oAt%2br%2bX%2bNWdJLVPTQfIh3kSSTuJQdSEJZEIlPjAZ8ji9J9Rw7kEDf%2fXA4V%2fzg5AZcPdm0FbIQIg%3d%3d | unknown | — | — | whitelisted |
6368 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1749039337&P2=404&P3=2&P4=NQB3Cr5ma39oAt%2br%2bX%2bNWdJLVPTQfIh3kSSTuJQdSEJZEIlPjAZ8ji9J9Rw7kEDf%2fXA4V%2fzg5AZcPdm0FbIQIg%3d%3d | unknown | — | — | whitelisted |
6368 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1749039337&P2=404&P3=2&P4=NQB3Cr5ma39oAt%2br%2bX%2bNWdJLVPTQfIh3kSSTuJQdSEJZEIlPjAZ8ji9J9Rw7kEDf%2fXA4V%2fzg5AZcPdm0FbIQIg%3d%3d | unknown | — | — | whitelisted |
6368 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1749039337&P2=404&P3=2&P4=NQB3Cr5ma39oAt%2br%2bX%2bNWdJLVPTQfIh3kSSTuJQdSEJZEIlPjAZ8ji9J9Rw7kEDf%2fXA4V%2fzg5AZcPdm0FbIQIg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7636 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 20.190.160.65:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
6584 | msedge.exe | 31.216.145.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
7128 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6584 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6584 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
mega.nz |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
eu.static.mega.co.nz |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6584 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
6584 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
6584 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
6584 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
6584 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
6584 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
6584 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
6584 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
6584 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
6584 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |