| File name: | SA2526-01558_SI003572 12.03.2026 PDF.JS |
| Full analysis: | https://app.any.run/tasks/93963358-2fc9-4ec5-8615-e74cd0548f78 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | March 12, 2026, 19:56:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text, with very long lines (502), with CRLF line terminators |
| MD5: | 289B8E23ACE9BF4A5461FD1CD5305C20 |
| SHA1: | 1D36B2A20C797414FE5F10C54ACF6315A7B478ED |
| SHA256: | 20E96722673872DC789302D6C66AACC88E79E023118DFC8851528E5903CF3190 |
| SSDEEP: | 196608:DnRoZQFiS2Bwh0heagmLPsN92i0IjTVs/eh:FoeF2Bw2l0nXJs/eh |
MALICIOUS
Uses base64 encoding (SCRIPT)
- wscript.exe (PID: 7392)
Detects the decoding of a binary file from Base64 (SCRIPT)
- wscript.exe (PID: 7392)
Changes the autorun value in the registry
- colorcpl.exe (PID: 6992)
Actions looks like stealing of personal data
- colorcpl.exe (PID: 6992)
PHANTOM has been detected (YARA)
- colorcpl.exe (PID: 6992)
PHANTOM has been detected
- colorcpl.exe (PID: 6992)
Steals credentials from Web Browsers
- colorcpl.exe (PID: 6992)
SUSPICIOUS
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 7392)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 7392)
Script creates XML DOM node (SCRIPT)
- wscript.exe (PID: 7392)
Gets name of the script (SCRIPT)
- wscript.exe (PID: 7392)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7392)
The process executes JS scripts
- wscript.exe (PID: 7392)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 7392)
Creates XML DOM element (SCRIPT)
- wscript.exe (PID: 7392)
Executable content was dropped or overwritten
- wscript.exe (PID: 7392)
- colorcpl.exe (PID: 6992)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 7392)
Likely accesses (executes) a file from the Public directory
- BLHXDZLJYTBNGKMVLKAPRLCAXATITCNTZLMUWQBWRWASFSKUBWIRBYOBYQHDHEEEJ.exe (PID: 404)
Starts the AutoIt3 executable file
- wscript.exe (PID: 7392)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7392)
Browser launch with unusual user-data-dir
- colorcpl.exe (PID: 6992)
- chrome.exe (PID: 3388)
- msedge.exe (PID: 1036)
Browser sandbox disabling
- chrome.exe (PID: 3388)
- chrome.exe (PID: 8532)
- chrome.exe (PID: 8364)
- chrome.exe (PID: 7924)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 8284)
- chrome.exe (PID: 4952)
- chrome.exe (PID: 9136)
- chrome.exe (PID: 8328)
- msedge.exe (PID: 7496)
- msedge.exe (PID: 5512)
- msedge.exe (PID: 7212)
- msedge.exe (PID: 7776)
- firefox.exe (PID: 3544)
- msedge.exe (PID: 6440)
- firefox.exe (PID: 5636)
- chrome.exe (PID: 1232)
- firefox.exe (PID: 6416)
- firefox.exe (PID: 1700)
- msedge.exe (PID: 1036)
Possible stealing of email data
- colorcpl.exe (PID: 6992)
Checks for external IP
- colorcpl.exe (PID: 6992)
- svchost.exe (PID: 2292)
Possible usage of Discord/Telegram API has been detected (YARA)
- colorcpl.exe (PID: 6992)
Found regular expressions for crypto-addresses (YARA)
- colorcpl.exe (PID: 6992)
Multiple wallet extension IDs have been found
- colorcpl.exe (PID: 6992)
INFO
The sample compiled with english language support
- wscript.exe (PID: 7392)
- colorcpl.exe (PID: 6992)
Launching a file from a Registry key
- colorcpl.exe (PID: 6992)
Checks supported languages
- BLHXDZLJYTBNGKMVLKAPRLCAXATITCNTZLMUWQBWRWASFSKUBWIRBYOBYQHDHEEEJ.exe (PID: 404)
- colorcpl.exe (PID: 2220)
Reads mouse settings
- BLHXDZLJYTBNGKMVLKAPRLCAXATITCNTZLMUWQBWRWASFSKUBWIRBYOBYQHDHEEEJ.exe (PID: 404)
Creates files or folders in the user directory
- colorcpl.exe (PID: 6992)
Application launched itself
- chrome.exe (PID: 3388)
- firefox.exe (PID: 1700)
- msedge.exe (PID: 1036)
- firefox.exe (PID: 3544)
- firefox.exe (PID: 6416)
- firefox.exe (PID: 5636)
Manual execution by a user
- colorcpl.exe (PID: 2220)
Create files in a temporary directory
- colorcpl.exe (PID: 6992)
Disables trace logs
- colorcpl.exe (PID: 6992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
188
Monitored processes
48
Malicious processes
5
Suspicious processes
0
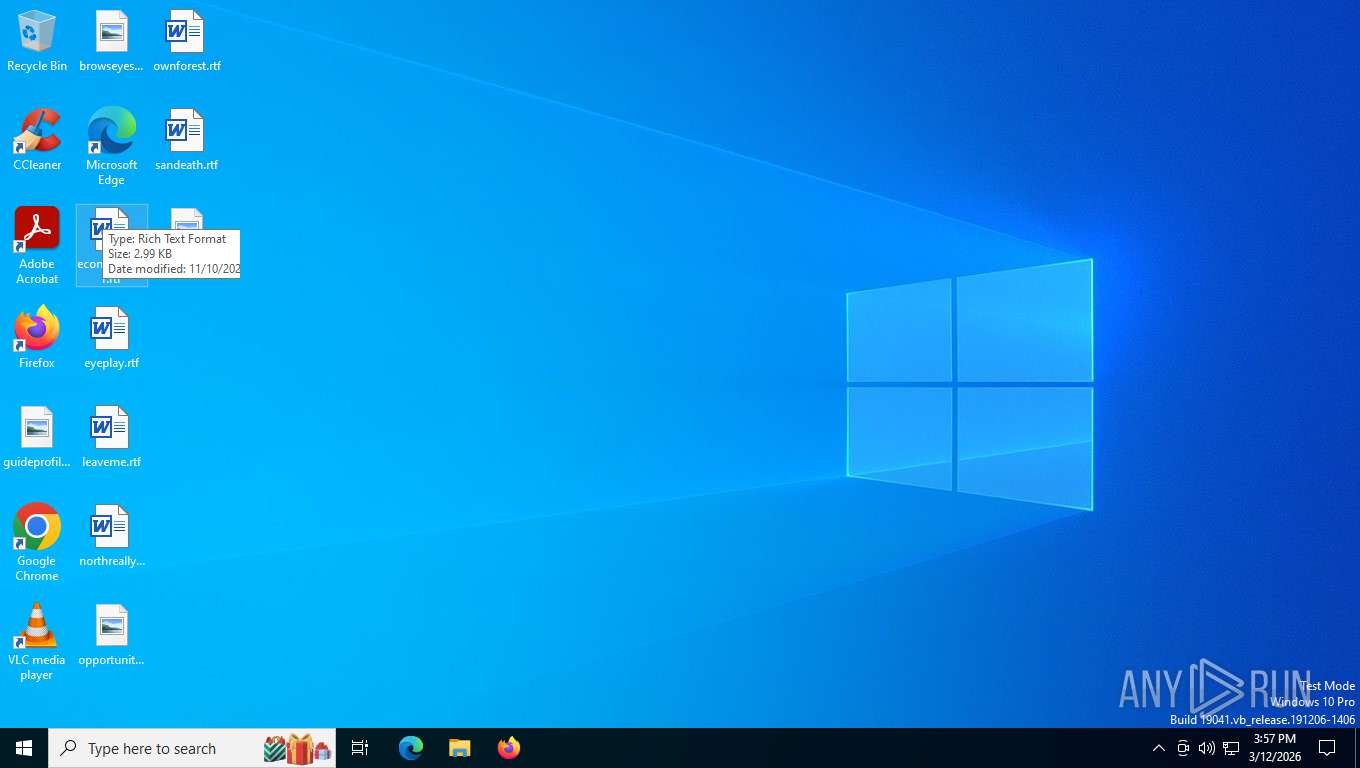
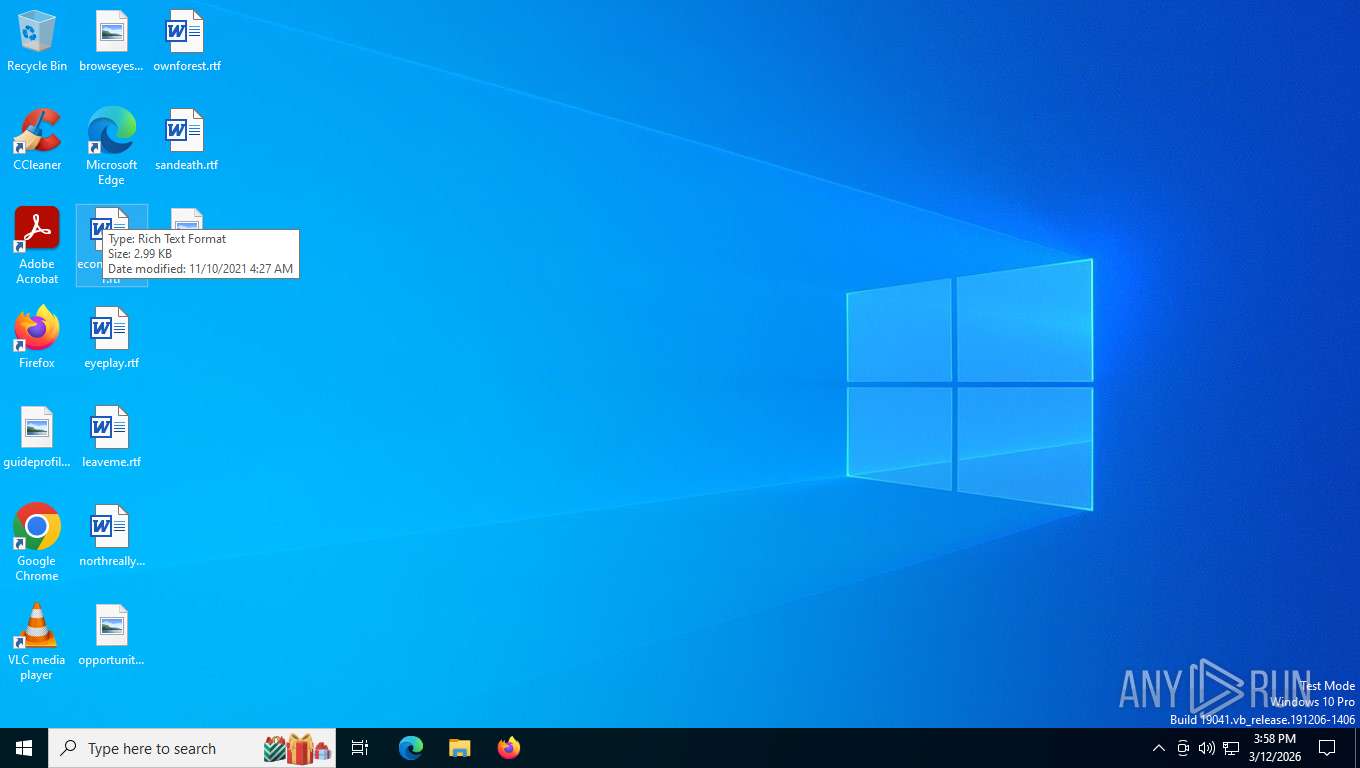
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | "C:\Users\Public\Libraries\BLHXDZLJYTBNGKMVLKAPRLCAXATITCNTZLMUWQBWRWASFSKUBWIRBYOBYQHDHEEEJ.exe" C:\Users\Public\Libraries\BLHXDZLJYTBNGKMVLKAPRLCAXATITCNTZLMUWQBWRWASFSKUBWIRBYOBYQHDHEEEJ.png | C:\Users\Public\Libraries\BLHXDZLJYTBNGKMVLKAPRLCAXATITCNTZLMUWQBWRWASFSKUBWIRBYOBYQHDHEEEJ.exe | — | wscript.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 16, 1 Modules
| |||||||||||||||
| 1036 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-sandbox --allow-no-sandbox-job --disable-gpu --mute-audio --disable-audio --user-data-dir="C:\Users\admin\AppData\Local\Temp\vagfhyhc.swx" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | colorcpl.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\pd5t2xu2.xdh" --extension-process --enable-dinosaur-easter-egg-alt-images --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=10 --field-trial-handle=3632,i,11103230966164308585,12423340353518533728,262144 --variations-seed-version --mojo-platform-channel-handle=3712 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4664 -prefsLen 39264 -prefMapHandle 2632 -prefMapSize 272981 -jsInitHandle 4712 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4816 -initialChannelId {f177757d-eb6a-442e-b660-e125b0ed5087} -parentPid 5636 -crashReporter "\\.\pipe\gecko-crash-server-pipe.5636" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 9 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -prefsHandle 1916 -prefsLen 36578 -prefMapHandle 1920 -prefMapSize 272981 -ipcHandle 1984 -initialChannelId {95bd7413-5120-40ca-8bb3-22bdcb06b452} -parentPid 5636 -crashReporter "\\.\pipe\gecko-crash-server-pipe.5636" -appDir "C:\Program Files\Mozilla Firefox\browser" - 1 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4648 -prefsLen 45212 -prefMapHandle 4652 -prefMapSize 272981 -jsInitHandle 4656 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4572 -initialChannelId {accdef0e-d256-45f9-88f5-65bd660fbff2} -parentPid 1700 -crashReporter "\\.\pipe\gecko-crash-server-pipe.1700" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 7 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1656 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -sandboxingKind 0 -prefsHandle 4148 -prefsLen 45160 -prefMapHandle 4332 -prefMapSize 272981 -ipcHandle 4260 -initialChannelId {9f63060b-9f93-467e-95f0-b706e5e0a108} -parentPid 1700 -crashReporter "\\.\pipe\gecko-crash-server-pipe.1700" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 6 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Mozilla Firefox\firefox.exe" --no-sandbox --allow-no-sandbox-job --disable-gpu --mute-audio --disable-audio --user-data-dir=C:\Users\admin\AppData\Local\Temp\j4hotrwh.p04 | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 3392 -prefsLen 37305 -prefMapHandle 3396 -prefMapSize 272981 -jsInitHandle 3400 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 3408 -initialChannelId {415d5b06-080a-4c4e-988d-e57037b86f93} -parentPid 5636 -crashReporter "\\.\pipe\gecko-crash-server-pipe.5636" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 3 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 2220 | C:\Users\admin\AppData\Roaming\colorcpl.exe | C:\Users\admin\AppData\Roaming\colorcpl.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Color Control Panel Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 911
Read events
3 894
Write events
17
Delete events
0
Modification events
| (PID) Process: | (7392) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: A6611E0000000000 | |||
| (PID) Process: | (6992) colorcpl.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ICM\ProfileAssociations\Display\{4d36e96e-e325-11ce-bfc1-08002be10318}\0008 |
| Operation: | write | Name: | UsePerUserProfiles |
Value: 0 | |||
| (PID) Process: | (6992) colorcpl.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | colorcpl |
Value: C:\Users\admin\AppData\Roaming\colorcpl.exe | |||
| (PID) Process: | (6992) colorcpl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\colorcpl_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6992) colorcpl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\colorcpl_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6992) colorcpl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\colorcpl_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6992) colorcpl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\colorcpl_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6992) colorcpl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\colorcpl_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6992) colorcpl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\colorcpl_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6992) colorcpl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\colorcpl_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
3
Suspicious files
270
Text files
57
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Temp\pd5t2xu2.xdh\First Run | — | |
MD5:— | SHA256:— | |||
| 7392 | wscript.exe | C:\Users\Public\Libraries\BLHXDZLJYTBNGKMVLKAPRLCAXATITCNTZLMUWQBWRWASFSKUBWIRBYOBYQHDHEEEJ.png | text | |
MD5:89932C797021AB45CB64739FE4CA07F4 | SHA256:1B7C43109A9DB7B8B9045528BA706C96997EAD29CEE4A7F224E1FD9302C23C8A | |||
| 7392 | wscript.exe | C:\Users\Public\Libraries\BLHXDZLJYTBNGKMVLKAPRLCAXATITCNTZLMUWQBWRWASFSKUBWIRBYOBYQHDHEEEJ | binary | |
MD5:D2F9973E639C5F941A9F7534C856EA57 | SHA256:46F045B134716AD06092F5E8F9ED22F8138BA8FB63801A97C539734BE939EB5D | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Temp\pd5t2xu2.xdh\Local State | text | |
MD5:73115DC6866E46E63775373595F6F530 | SHA256:171ADB3005D775CDEEE7EDFDD19FC32FC97812CD52E584D9EF8464227552D969 | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Temp\pd5t2xu2.xdh\Default\History-journal | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Temp\pd5t2xu2.xdh\Last Version | text | |
MD5:D18CE7F480944AE4E61A969D8C1E5003 | SHA256:E0CB362A73D69BAD940A018881701B5F2A8527C13C3F5ACBBEA43B8820DFC199 | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Temp\pd5t2xu2.xdh\Crashpad\settings.dat | binary | |
MD5:E70D96224D4BC92564318A30F7060806 | SHA256:C9594E0B3481E15A4BE2D5F20A65256AFF085BD8B883D9FAB09D5057AEAE28BB | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Temp\pd5t2xu2.xdh\Variations | text | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Temp\pd5t2xu2.xdh\Default\Sync Data\LevelDB\MANIFEST-000001 | binary | |
MD5:5AF87DFD673BA2115E2FCF5CFDB727AB | SHA256:F9D31B278E215EB0D0E9CD709EDFA037E828F36214AB7906F612160FEAD4B2B4 | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Temp\pd5t2xu2.xdh\Default\Sync Data\LevelDB\CURRENT | text | |
MD5:46295CAC801E5D4857D09837238A6394 | SHA256:0F1BAD70C7BD1E0A69562853EC529355462FCD0423263A3D39D6D0D70B780443 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
430
DNS requests
42
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1700 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
1700 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
1700 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
5636 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
5636 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
5636 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6992 | colorcpl.exe | GET | 200 | 104.16.184.241:80 | http://icanhazip.com/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.241.205:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 2.16.241.218:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7228 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6712 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8364 | chrome.exe | 142.250.201.174:80 | clients2.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
mozilla.map.fastly.net |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2292 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
6992 | colorcpl.exe | Attempted Information Leak | ET INFO IP Check Domain (icanhazip. com in HTTP Host) |
2292 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (icanhazip .com) |
6992 | colorcpl.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\pd5t2xu2.xdh directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\vagfhyhc.swx directory exists )
|