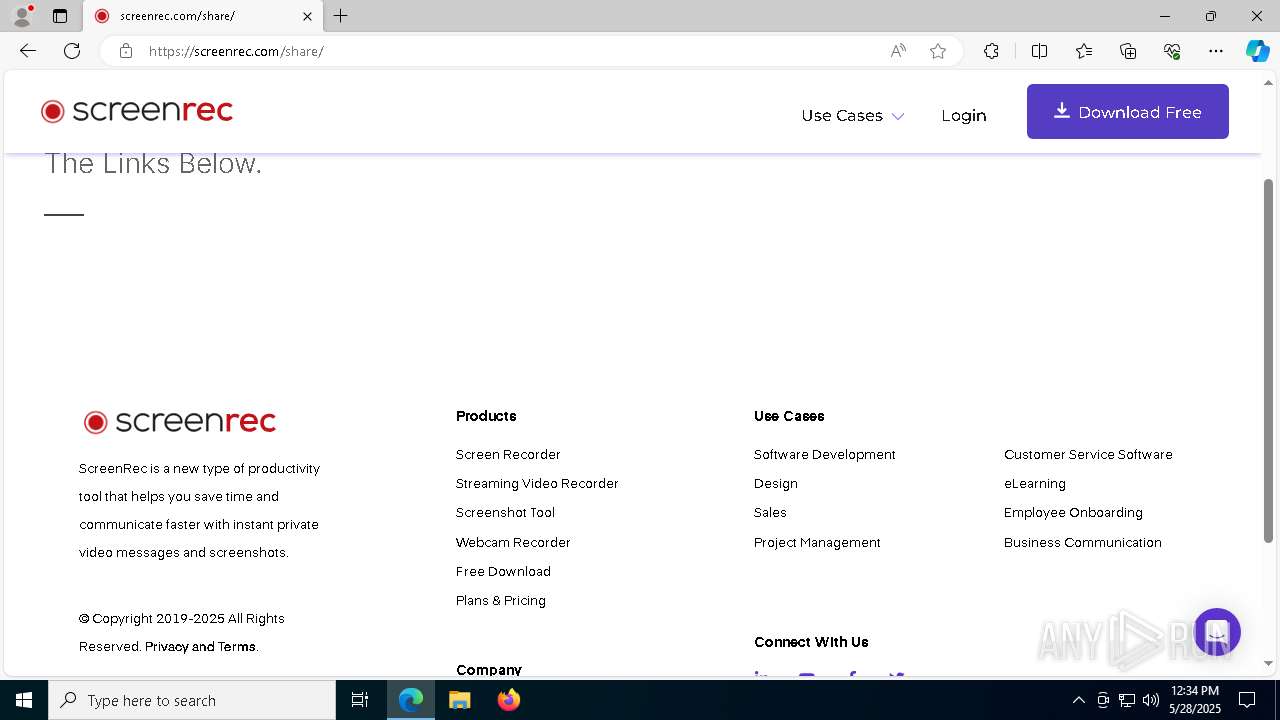
| URL: | https://screenrec.com/share/ainyb9o47r |
| Full analysis: | https://app.any.run/tasks/75c9aedb-70c2-482b-8945-55f634fa7a38 |
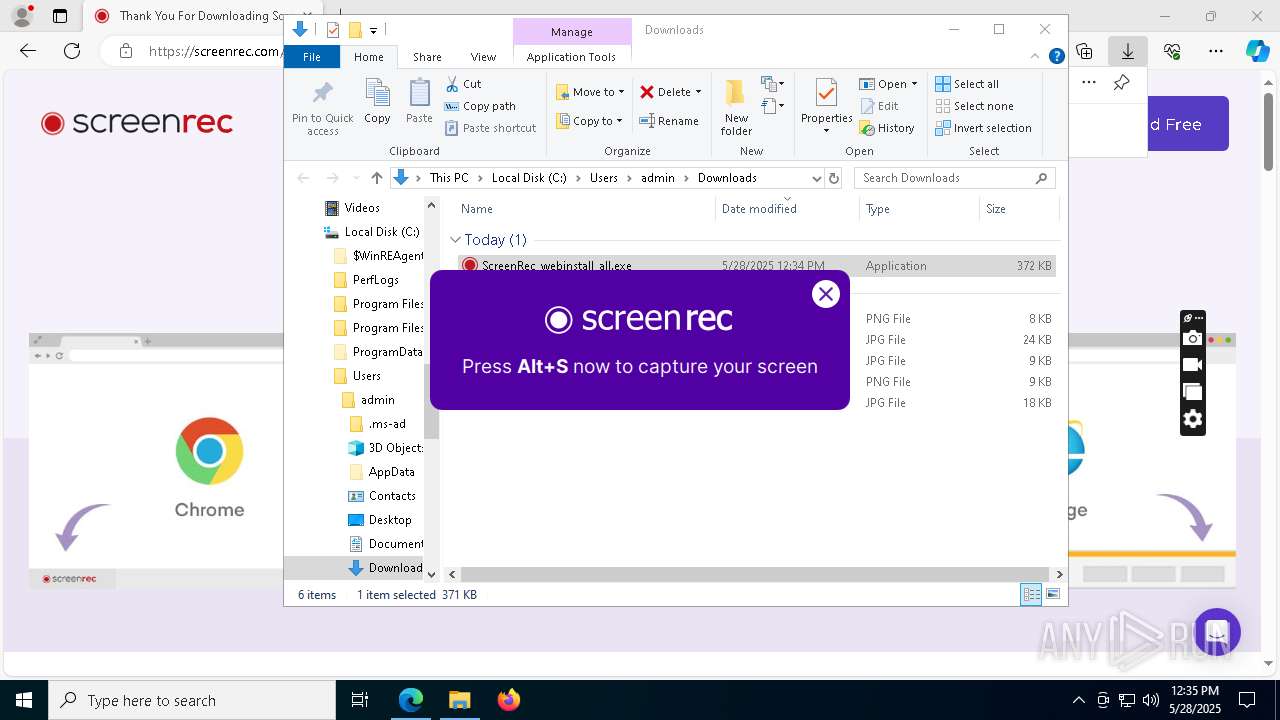
| Verdict: | Malicious activity |
| Analysis date: | May 28, 2025, 12:33:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 125F40C83925B376E5E69AE33E486806 |
| SHA1: | 3D6E92B85575CFE7010C12B8D8D846596120669E |
| SHA256: | 20E7464B00D96C5D7150DA6D0C7E42F382073E572E34B14050B14212884E9AD9 |
| SSDEEP: | 3:N8LzKC9Z:2a6 |
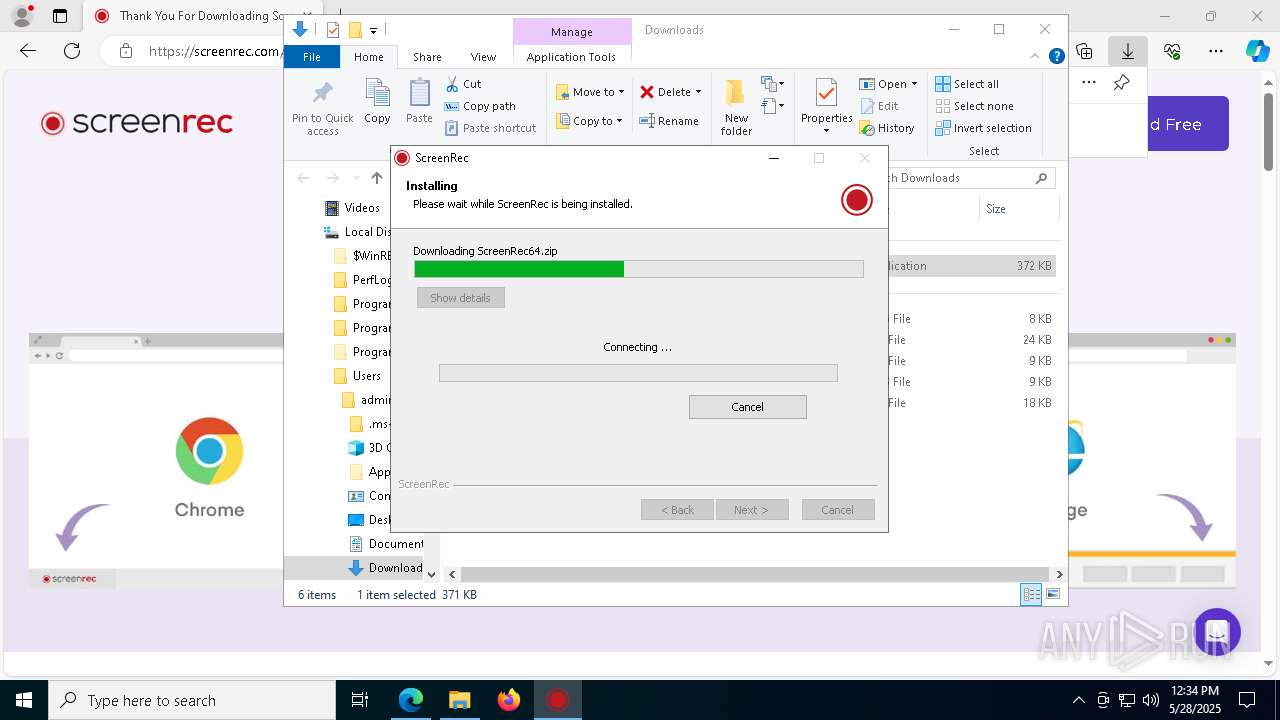
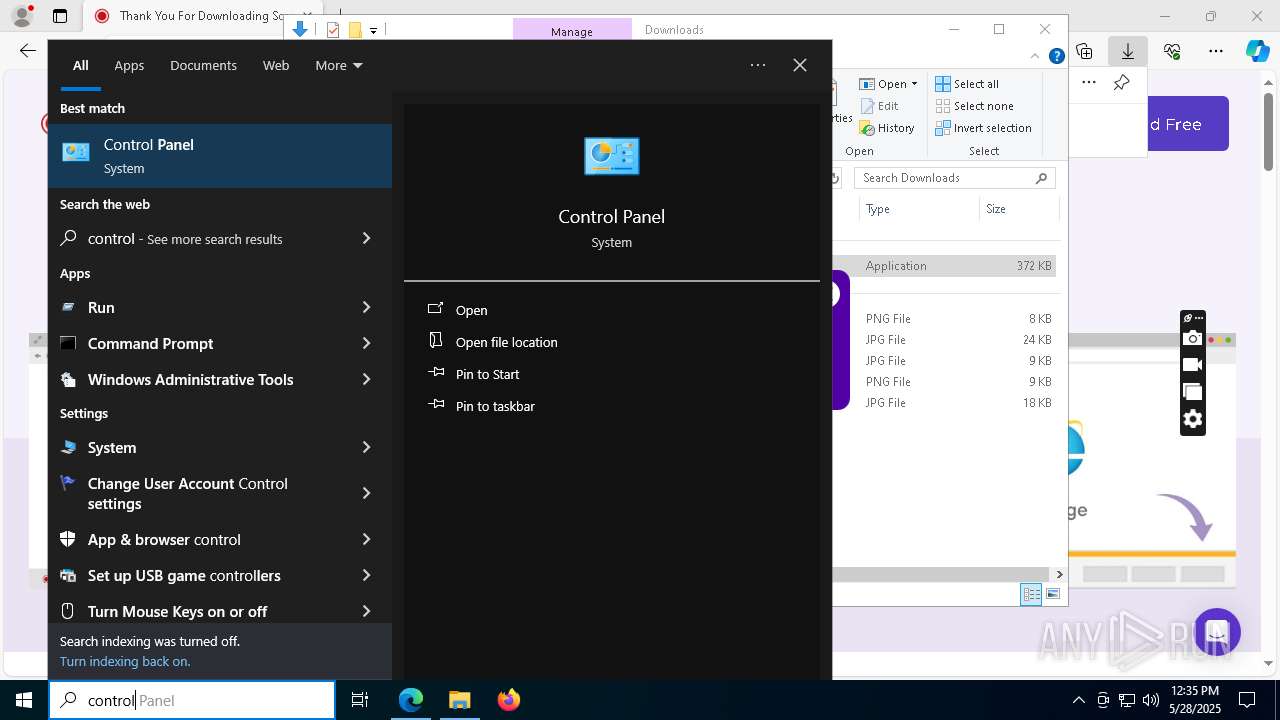
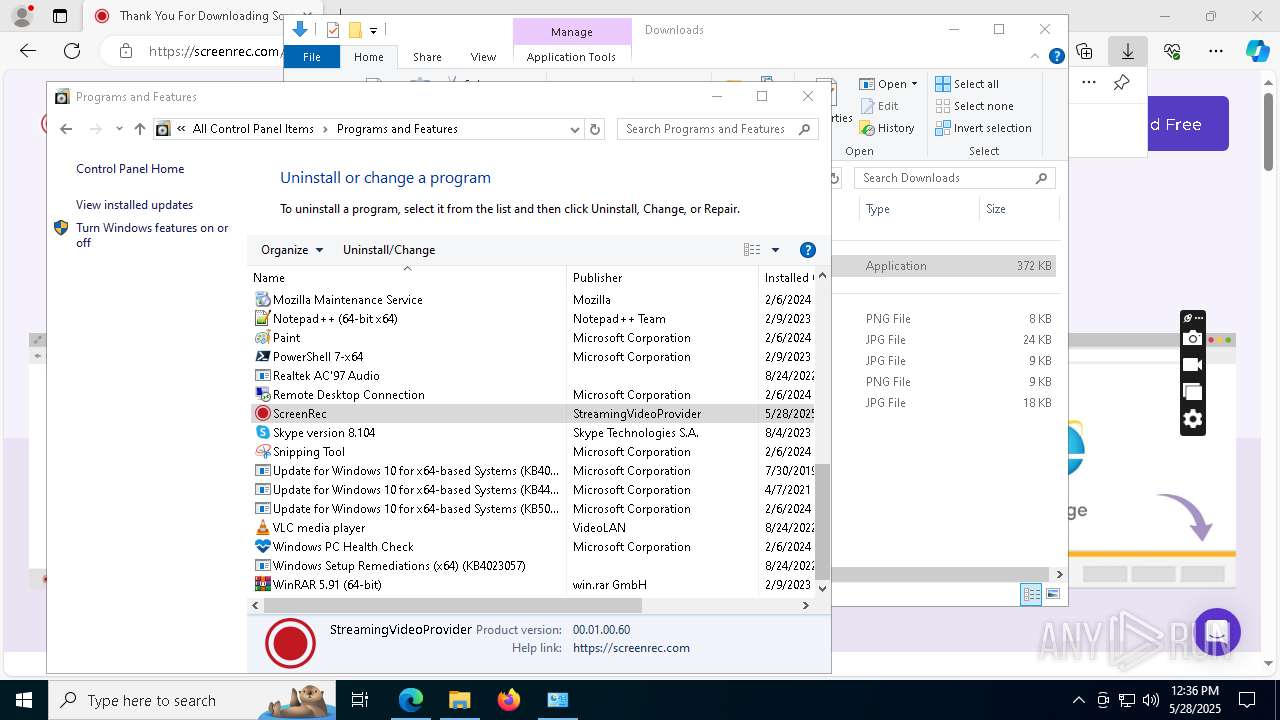
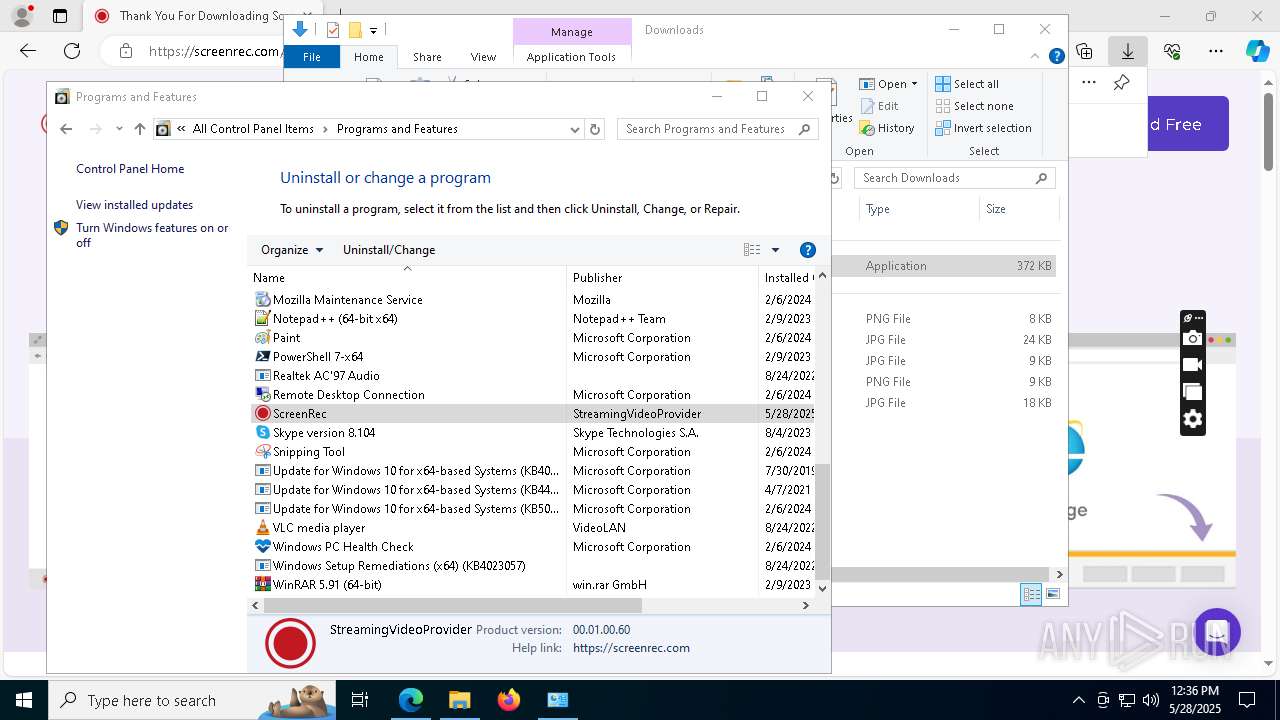
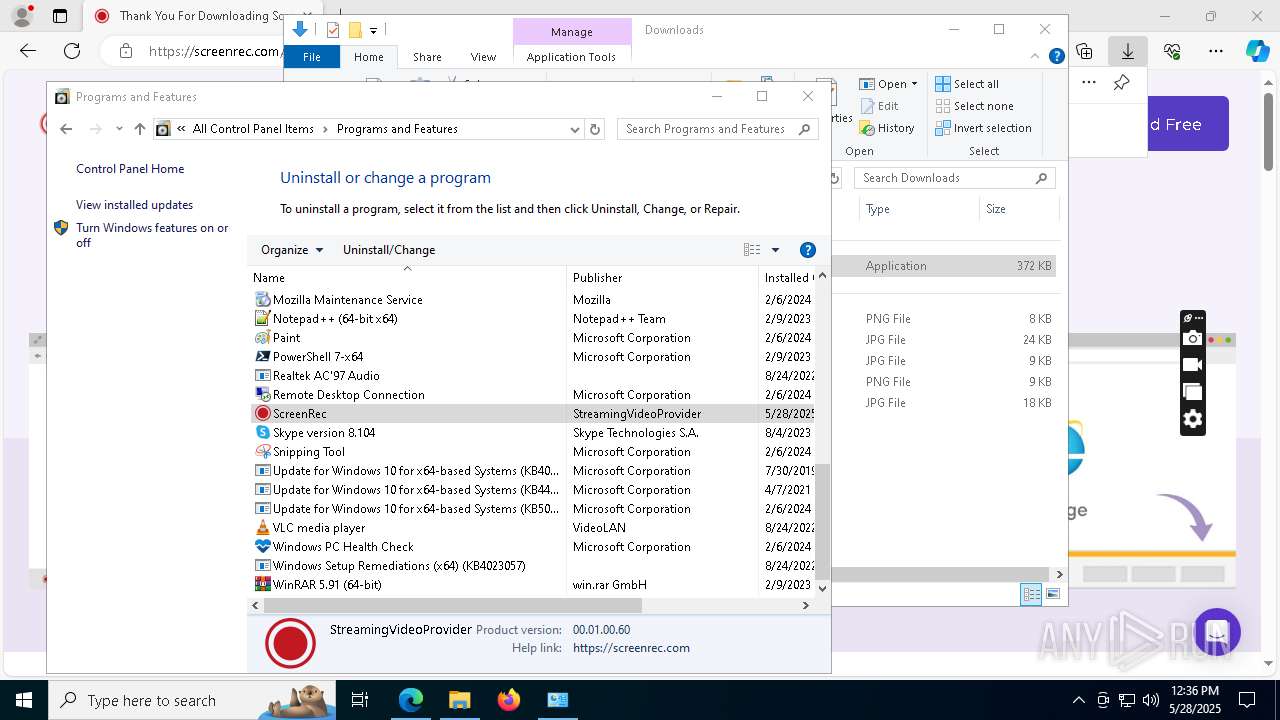
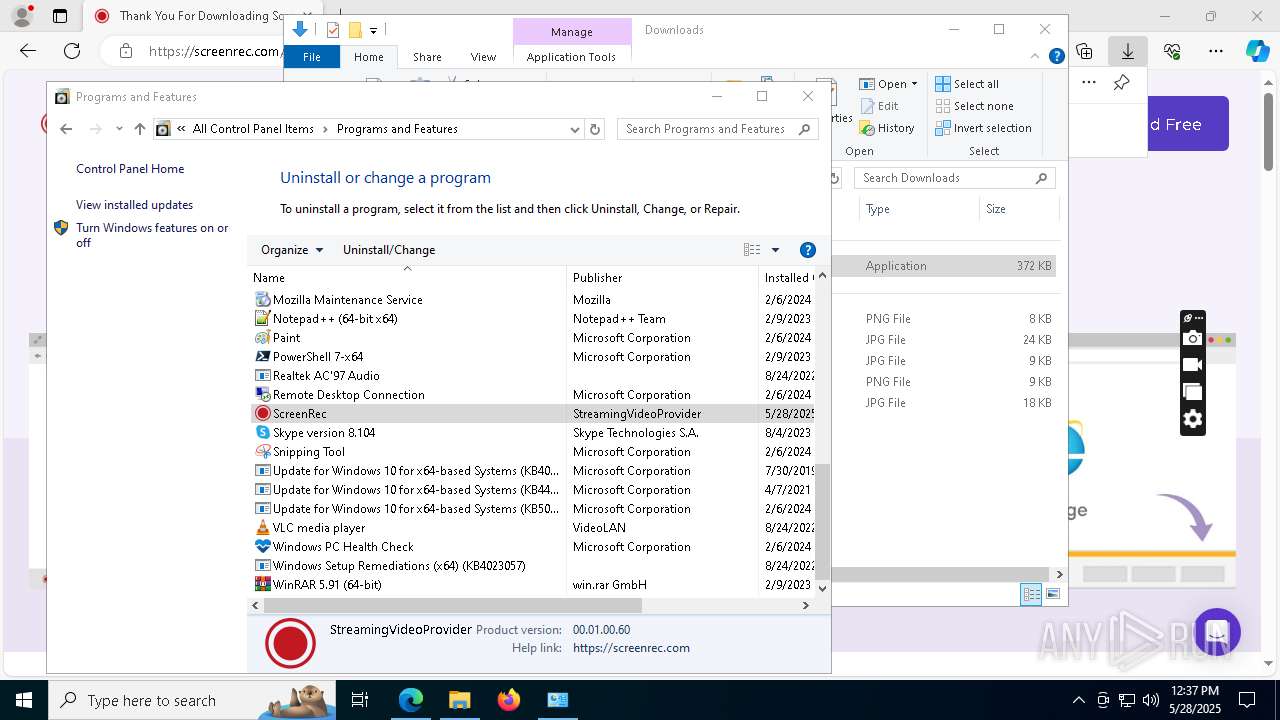
MALICIOUS
Changes the autorun value in the registry
- ScreenRec_webinstall_all.exe (PID: 7744)
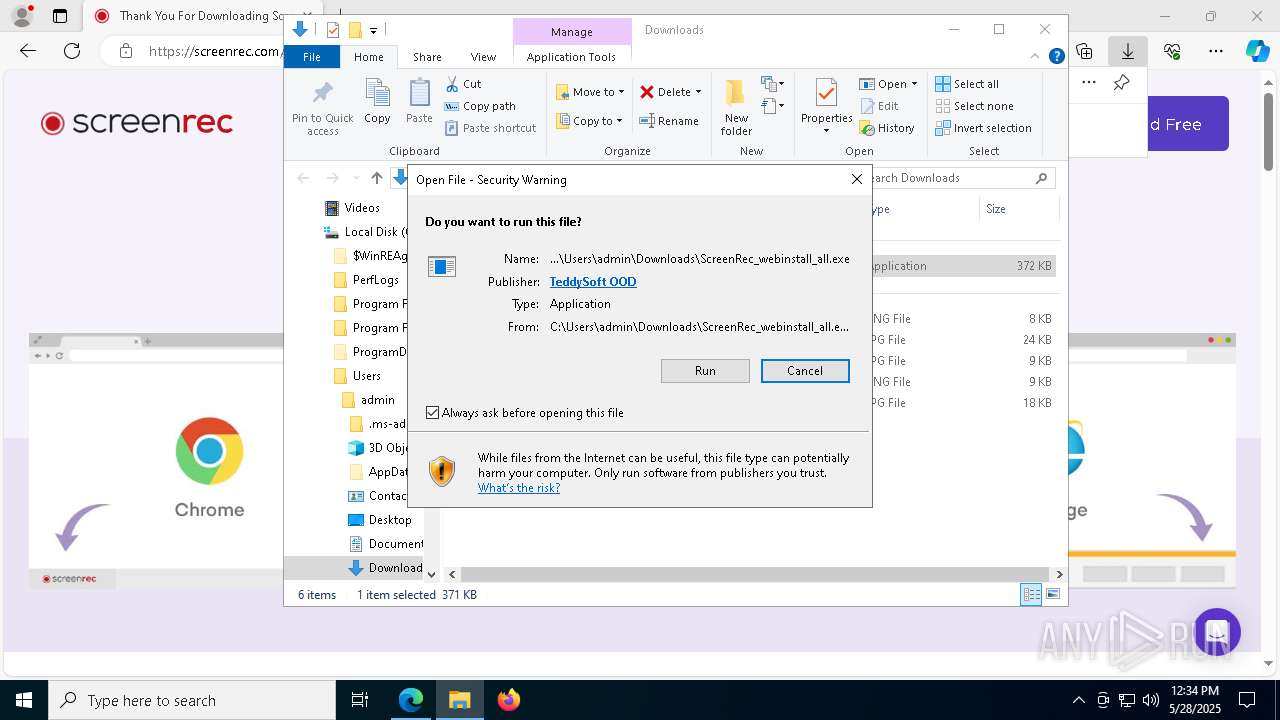
Executing a file with an untrusted certificate
- vcredist_x64.exe (PID: 5580)
SUSPICIOUS
Creates file in the systems drive root
- explorer.exe (PID: 5492)
The process creates files with name similar to system file names
- ScreenRec_webinstall_all.exe (PID: 7744)
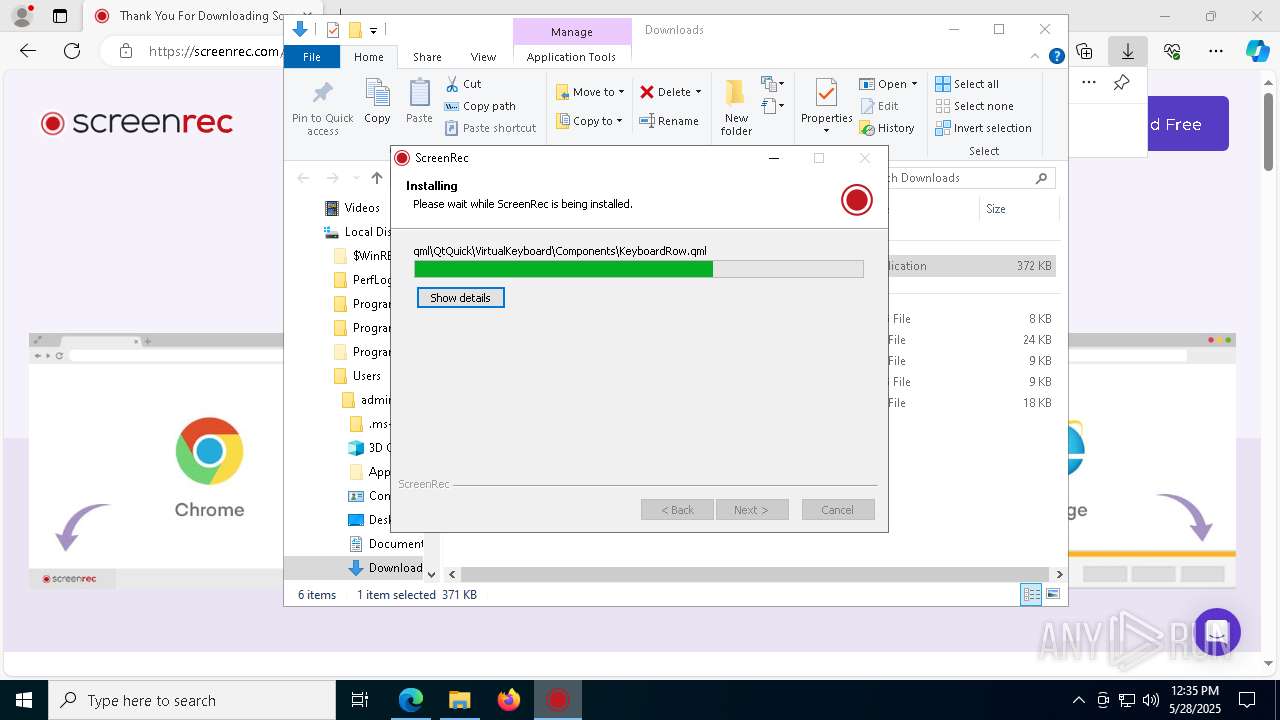
Executable content was dropped or overwritten
- ScreenRec_webinstall_all.exe (PID: 7744)
- vc_redist.x64.exe (PID: 496)
- vc_redist.x64.exe (PID: 5212)
- uninstall.exe (PID: 6476)
- Un.exe (PID: 896)
Malware-specific behavior (creating "System.dll" in Temp)
- ScreenRec_webinstall_all.exe (PID: 7744)
- Un.exe (PID: 896)
Reads security settings of Internet Explorer
- ScreenRec_webinstall_all.exe (PID: 7744)
Process drops legitimate windows executable
- vc_redist.x64.exe (PID: 496)
- ScreenRec_webinstall_all.exe (PID: 7744)
Starts a Microsoft application from unusual location
- vc_redist.x64.exe (PID: 5212)
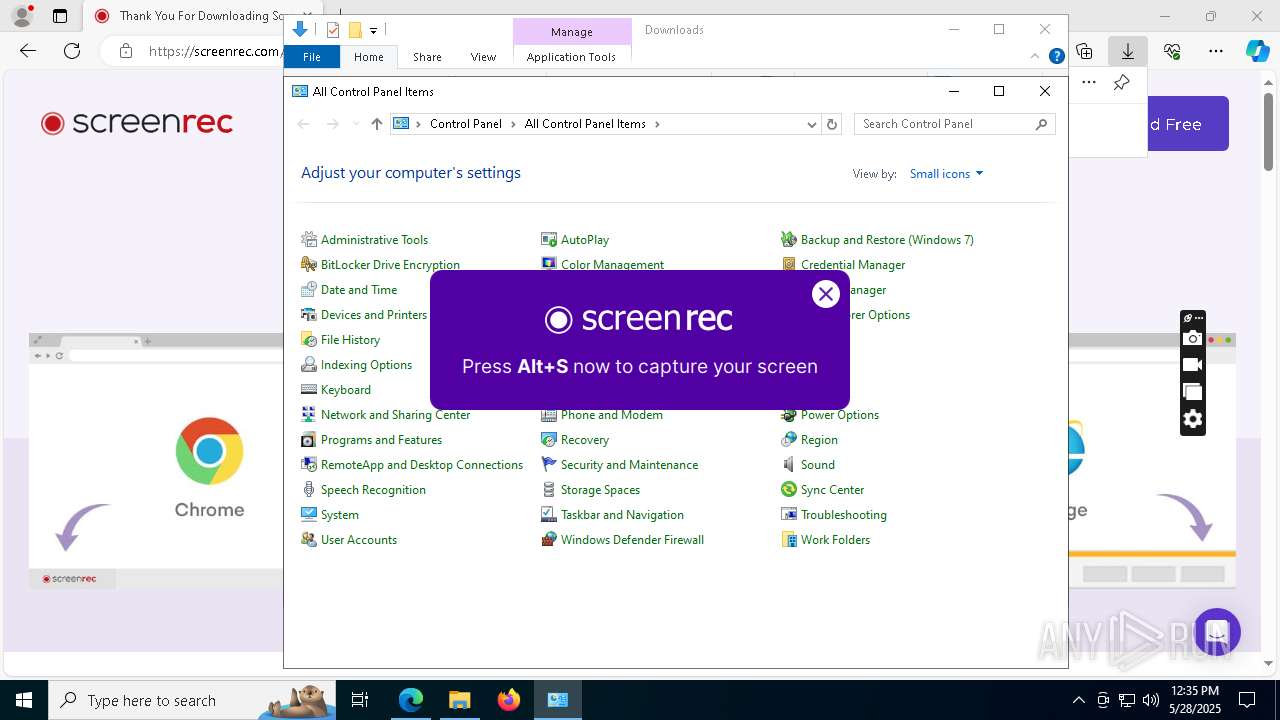
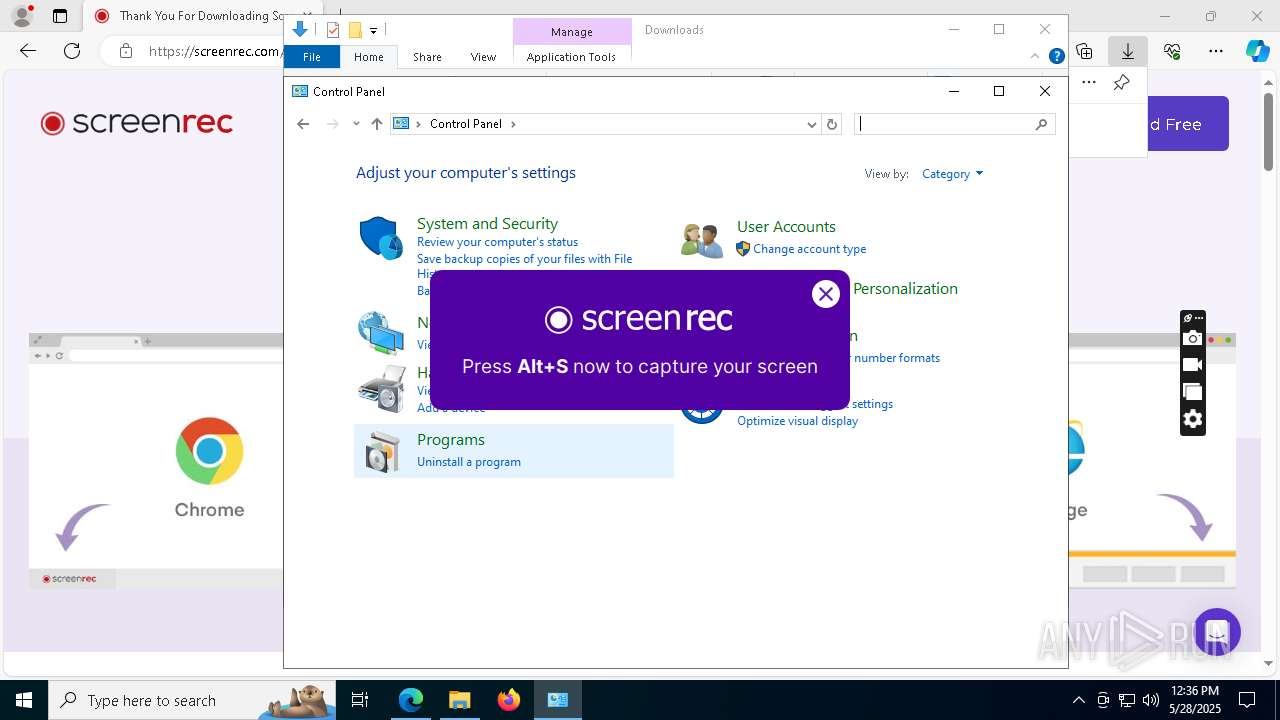
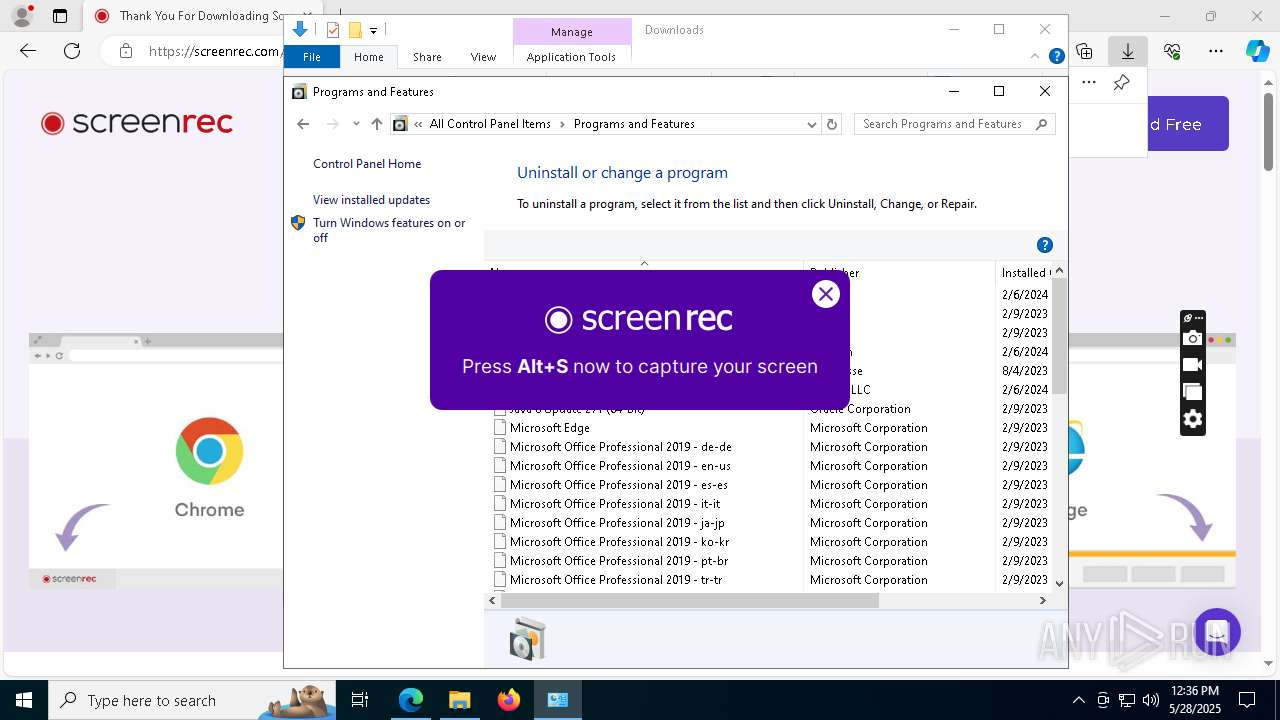
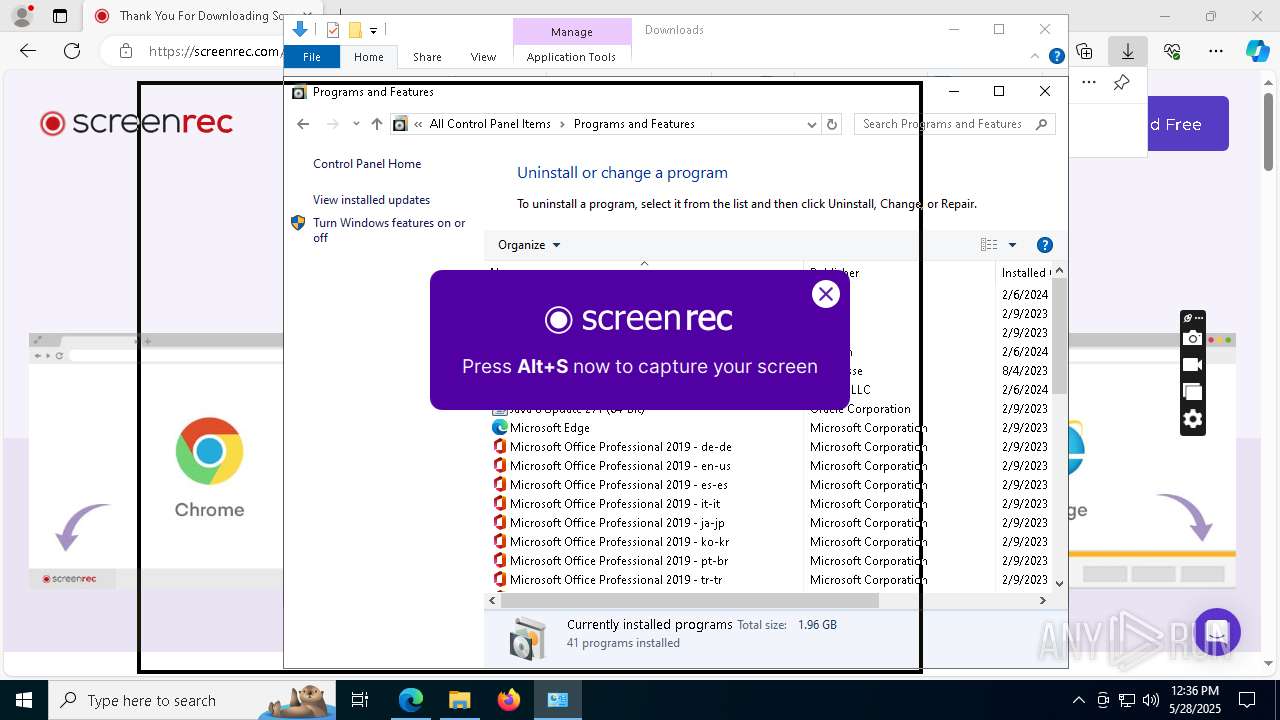
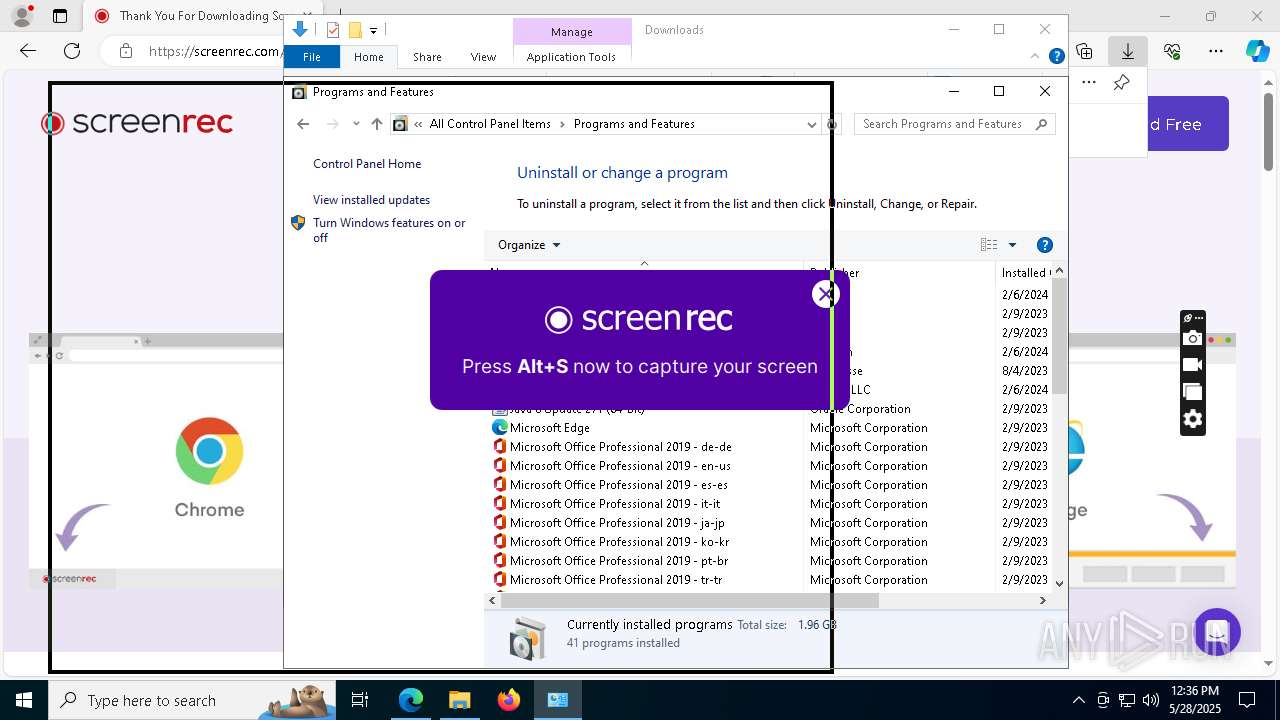
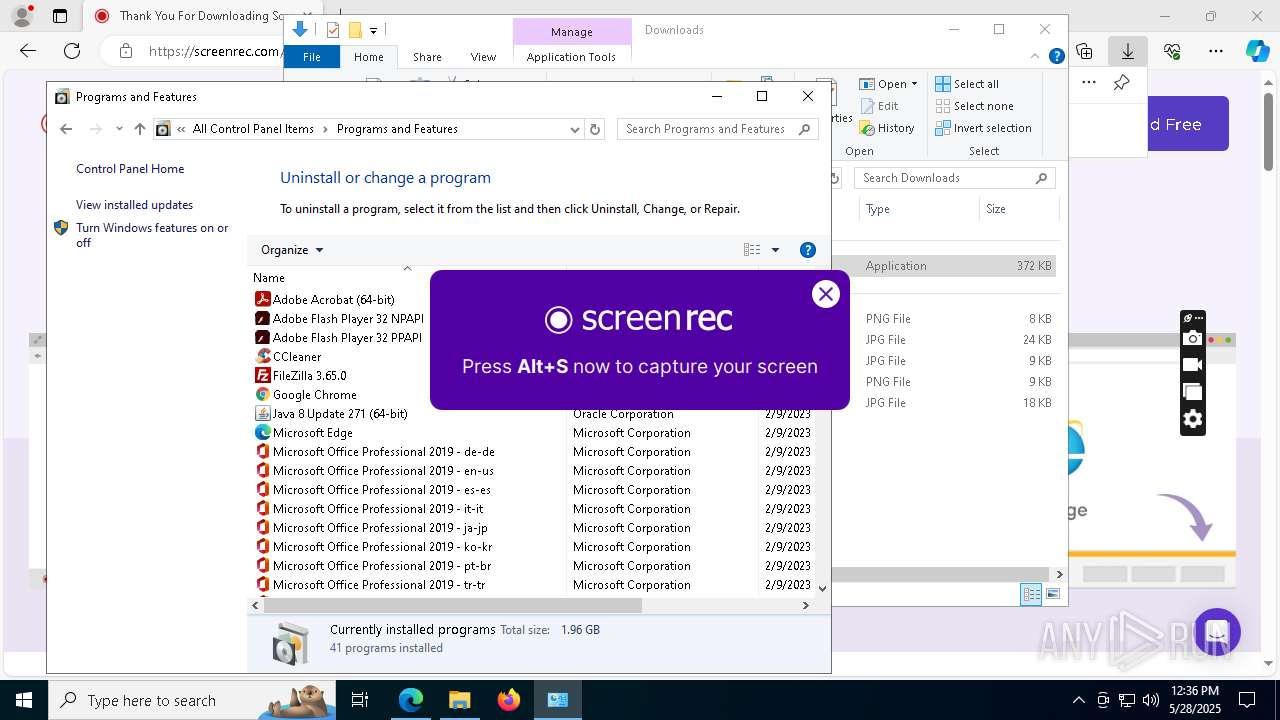
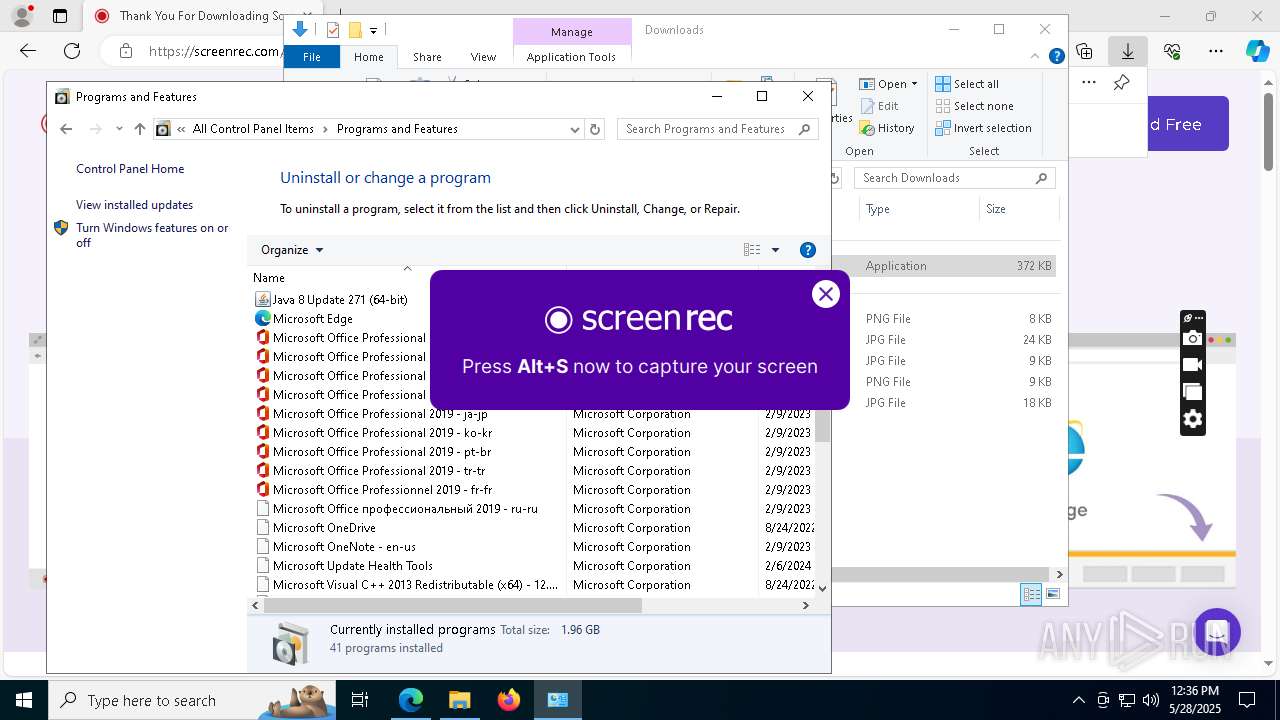
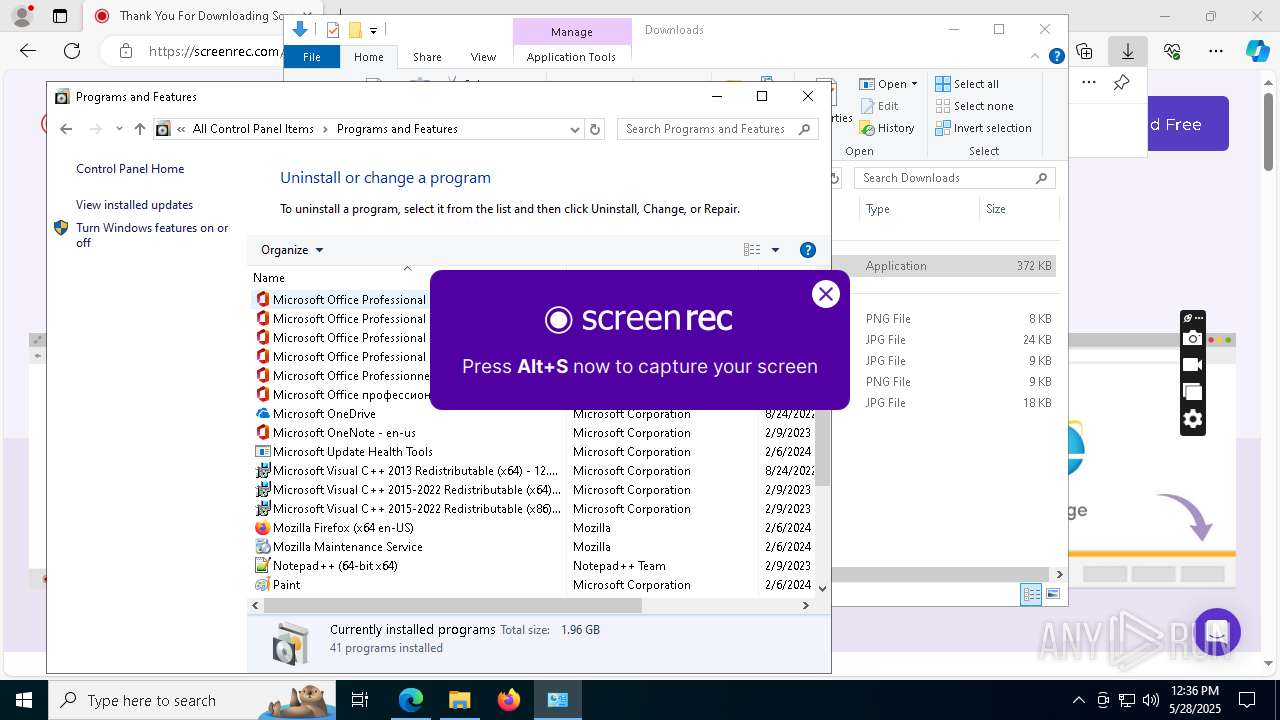
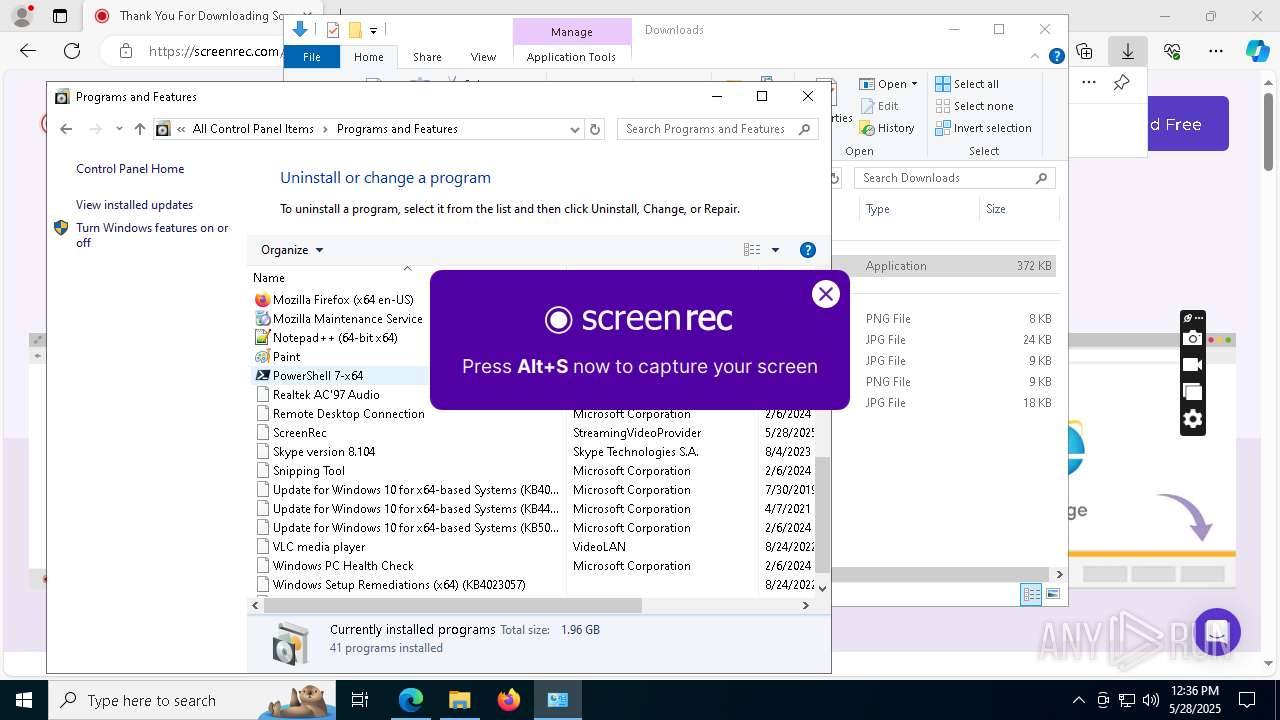
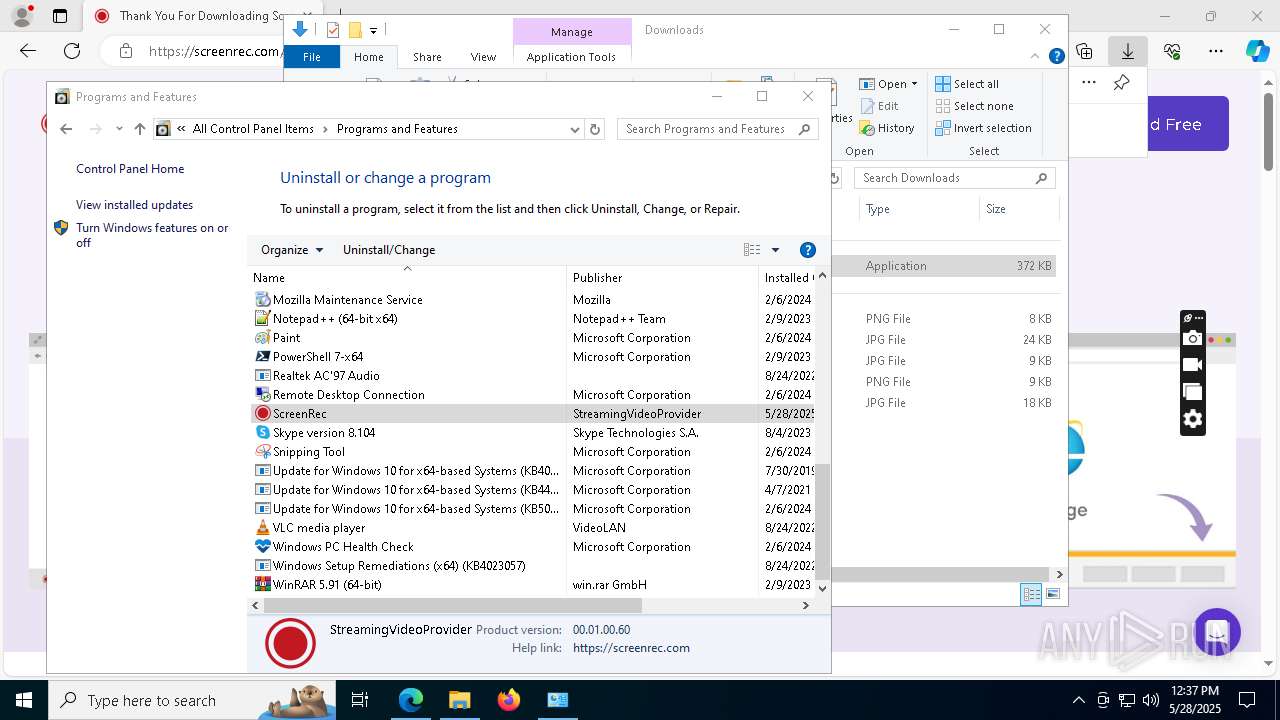
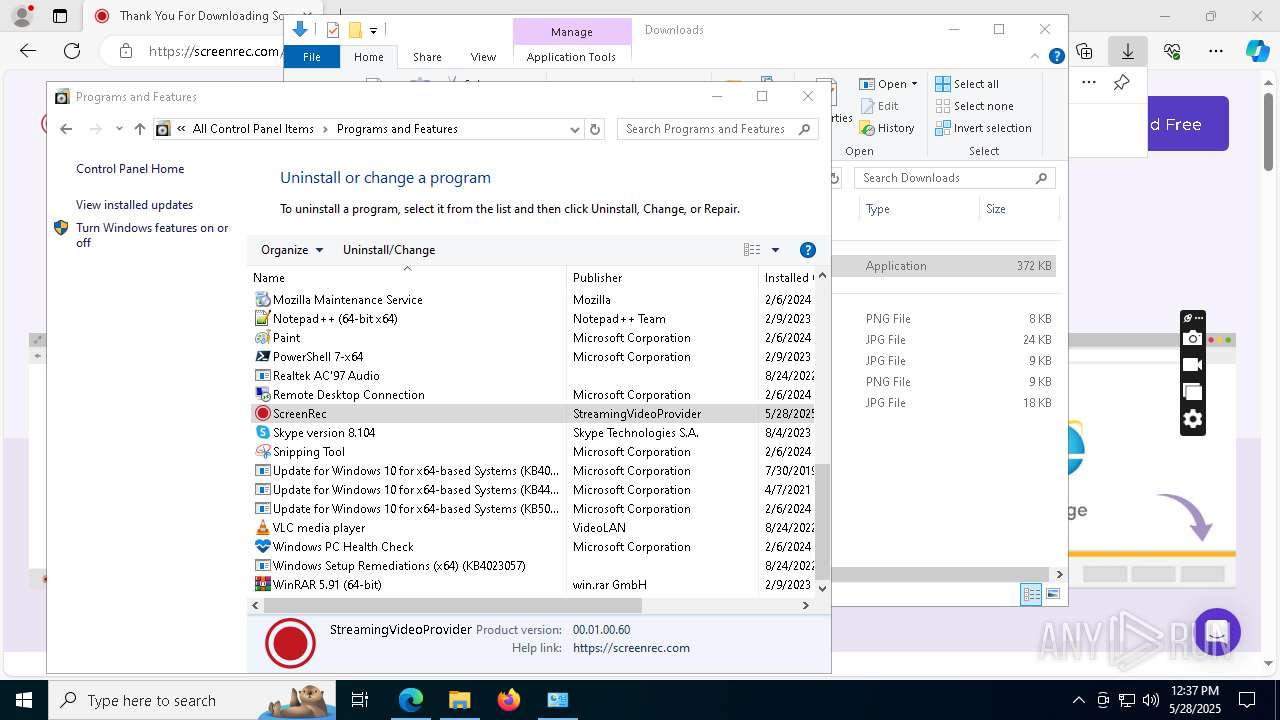
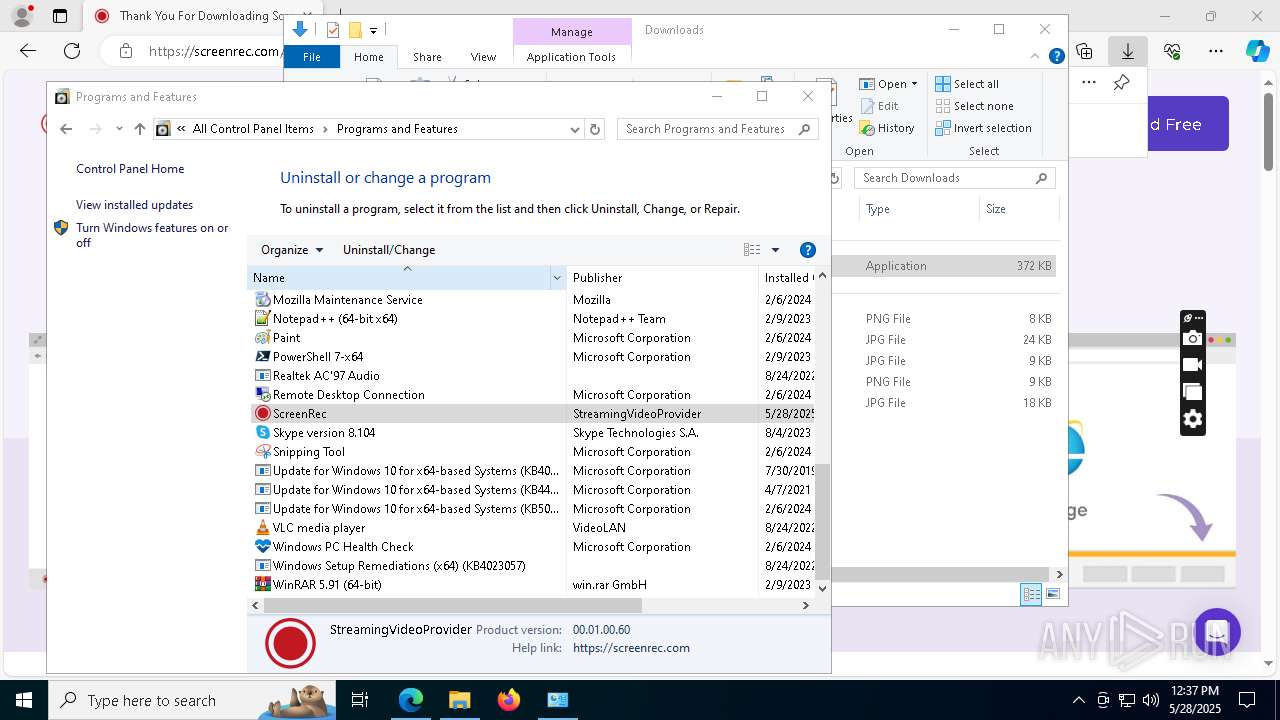
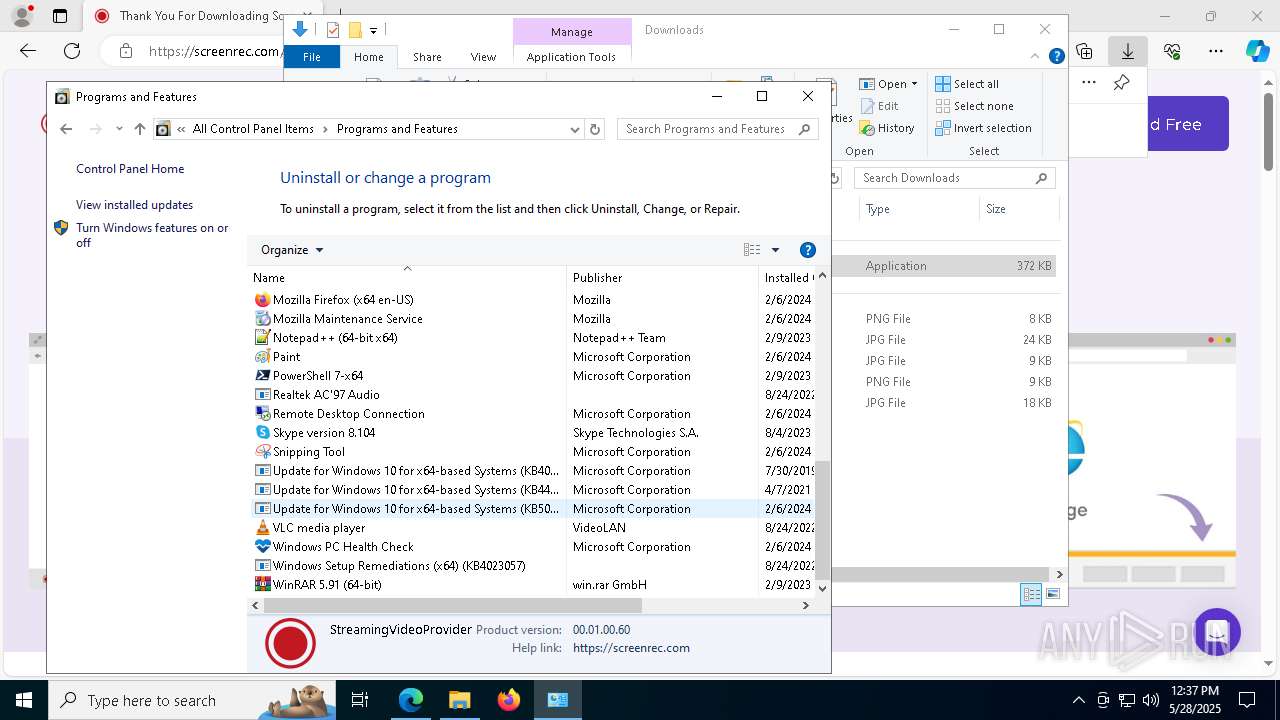
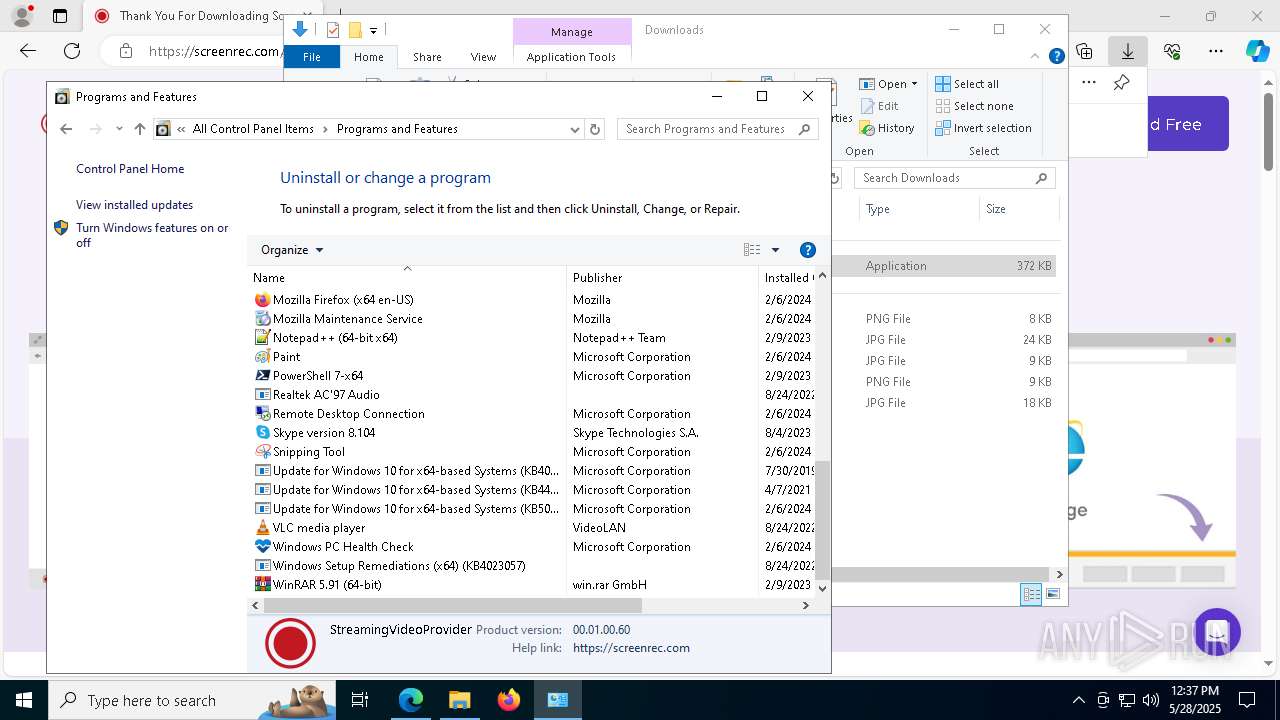
Searches for installed software
- vc_redist.x64.exe (PID: 5212)
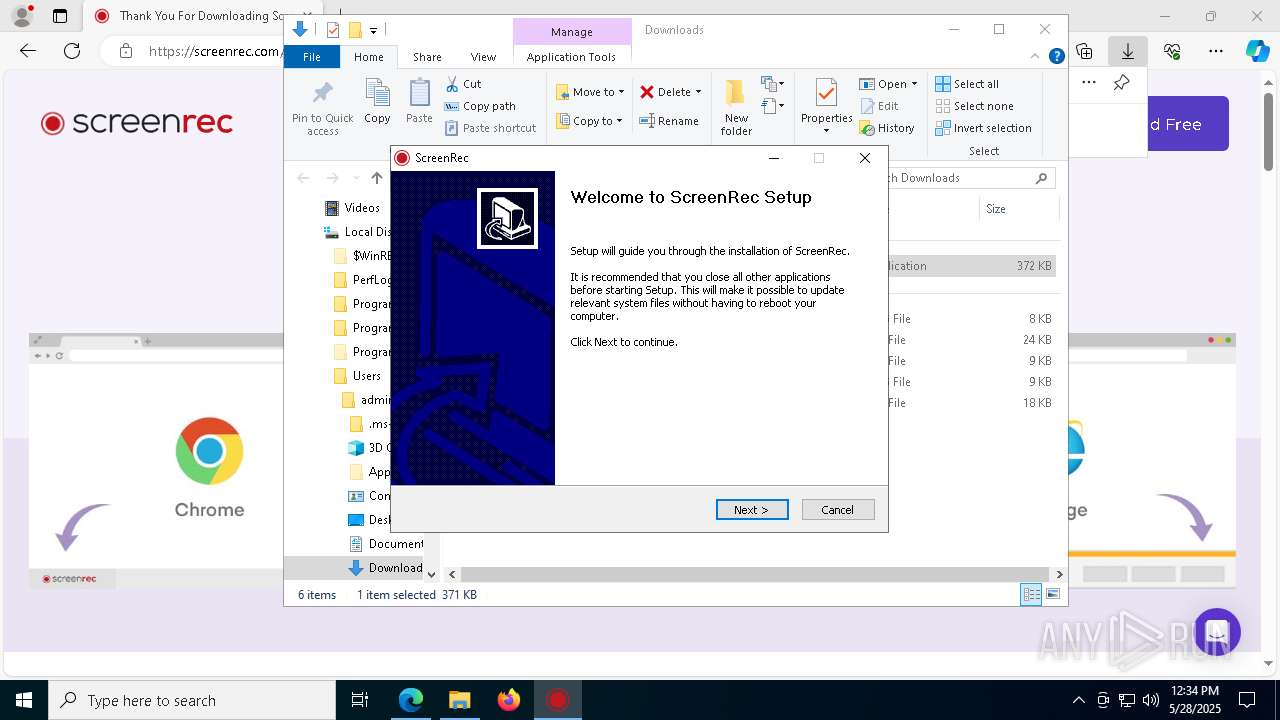
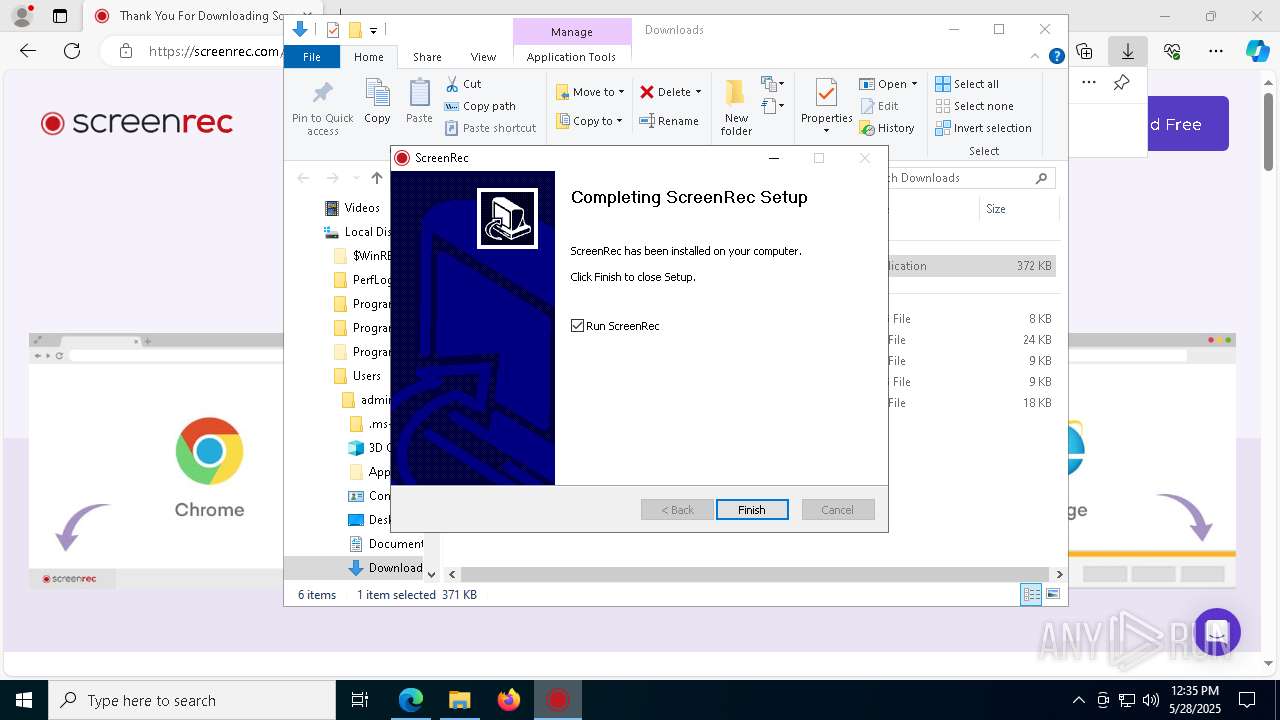
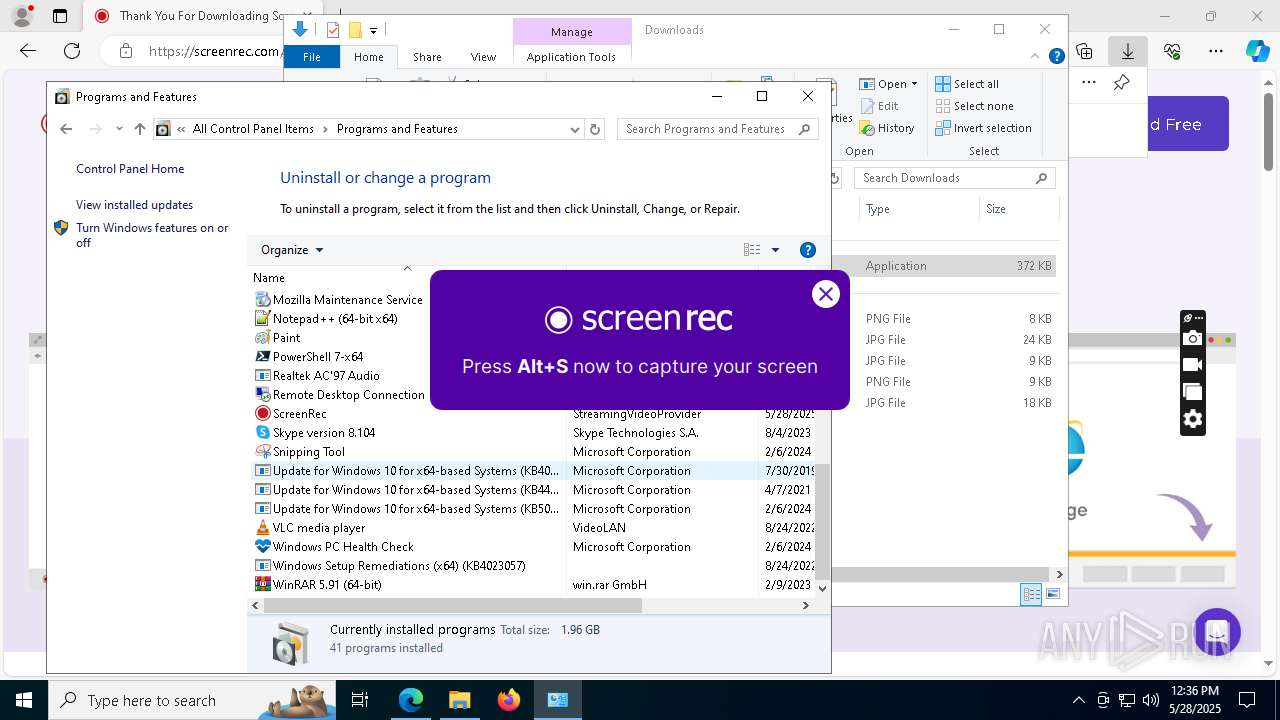
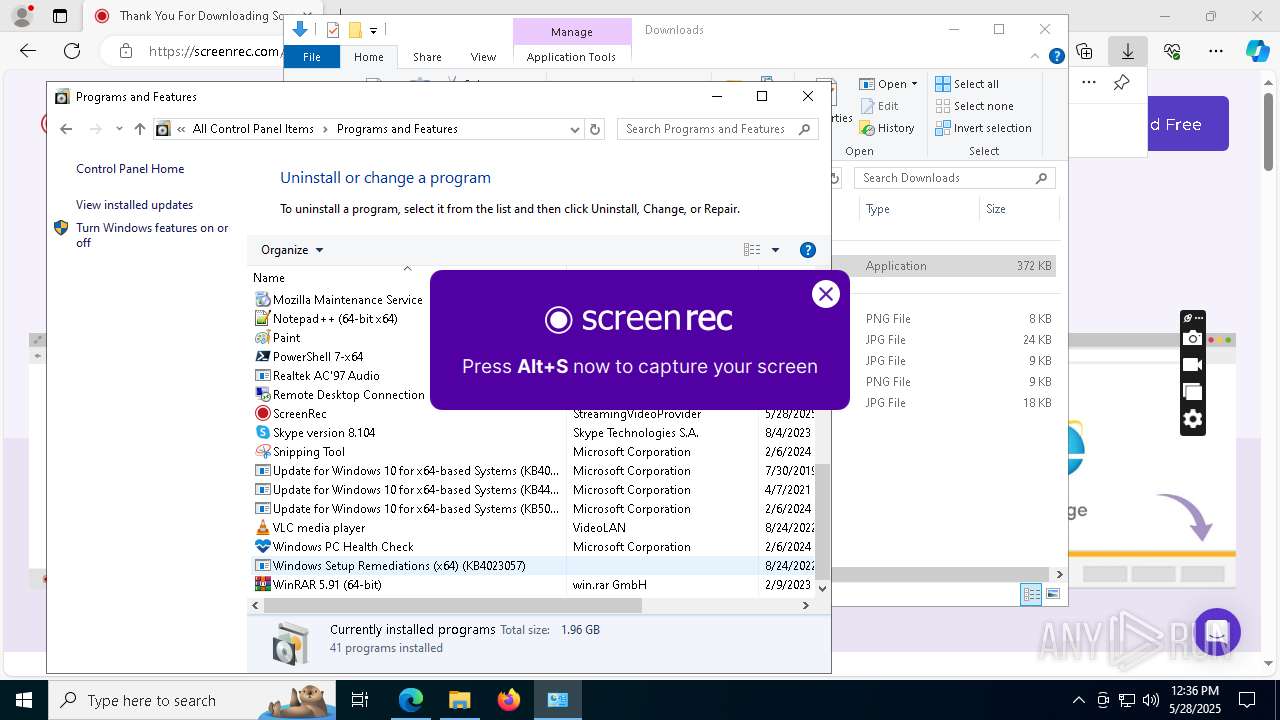
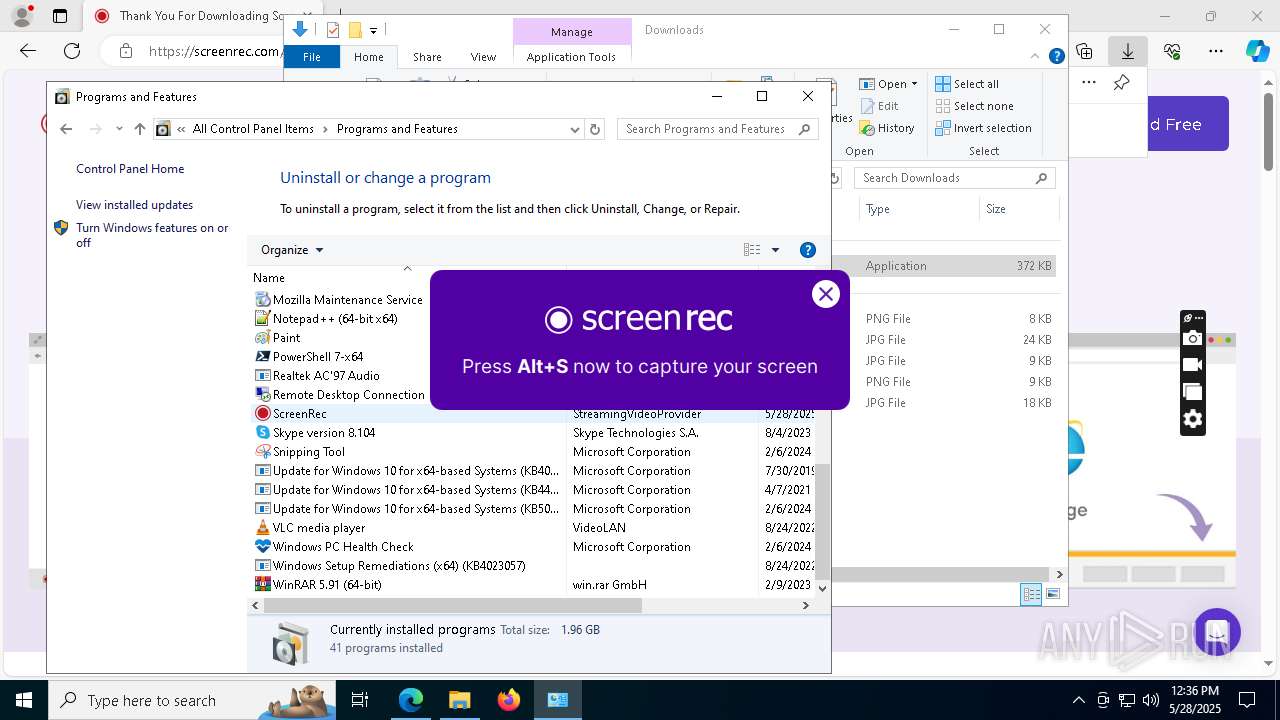
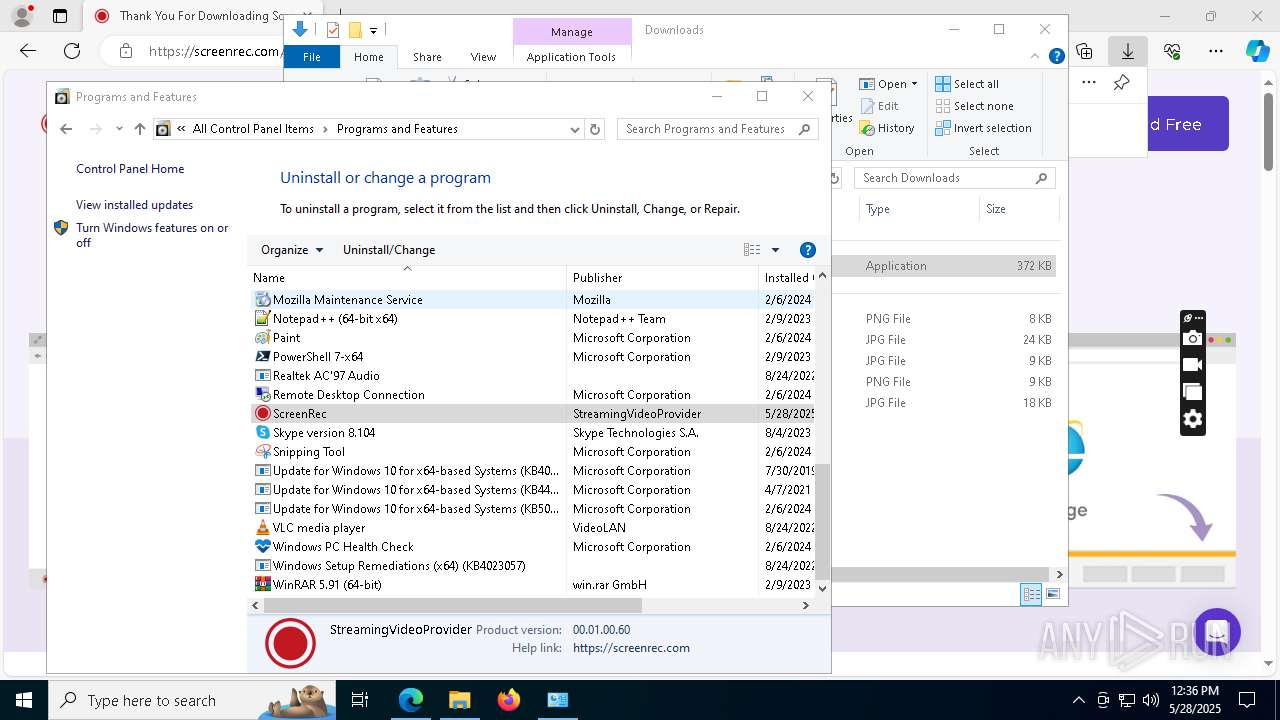
Creates a software uninstall entry
- ScreenRec_webinstall_all.exe (PID: 7744)
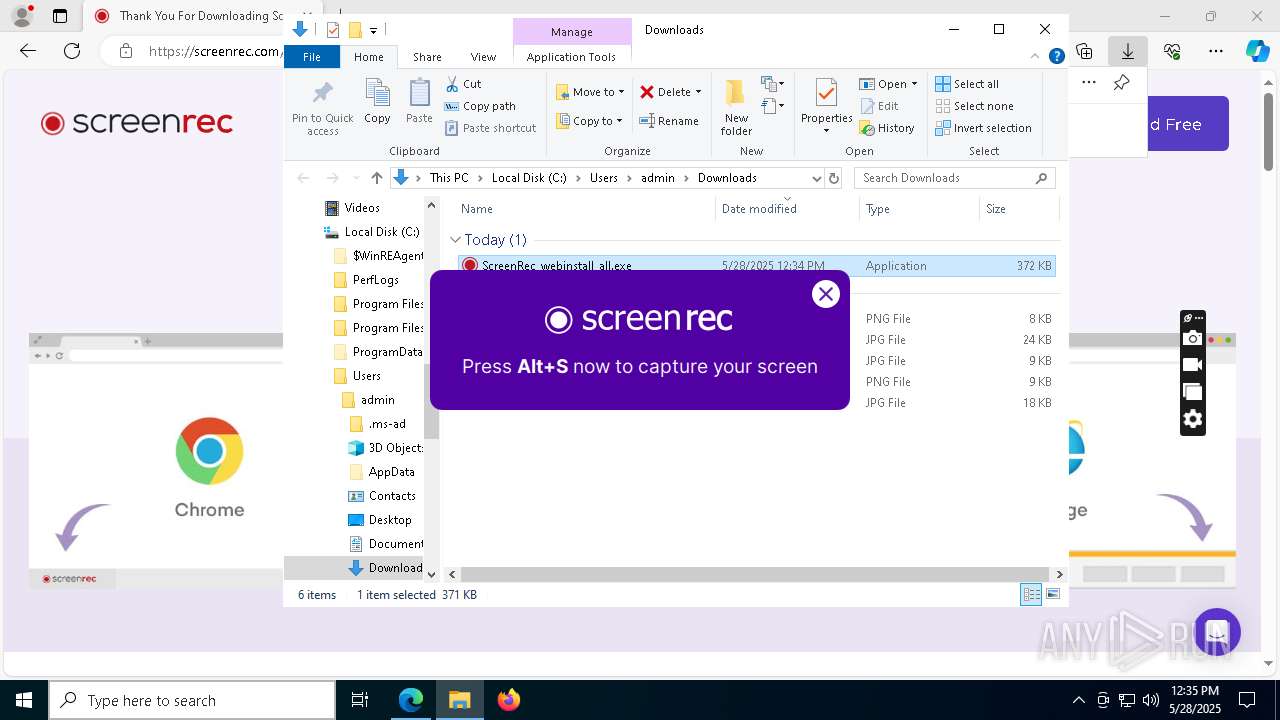
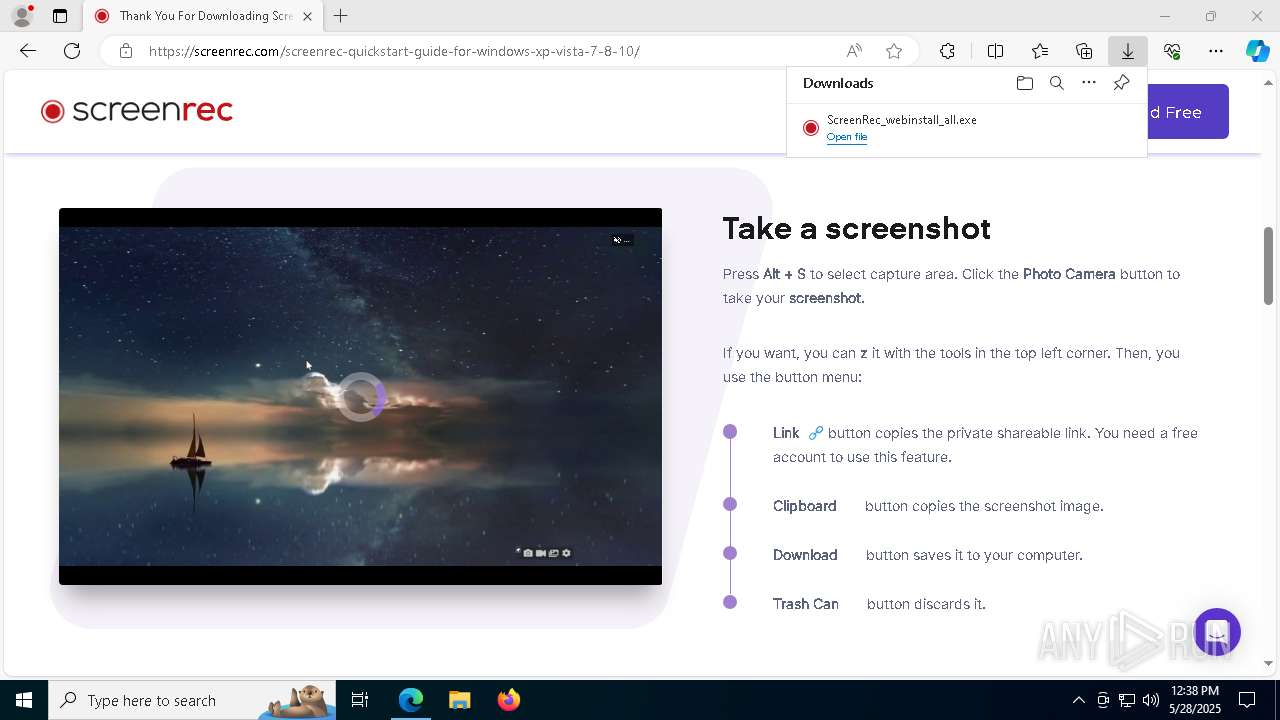
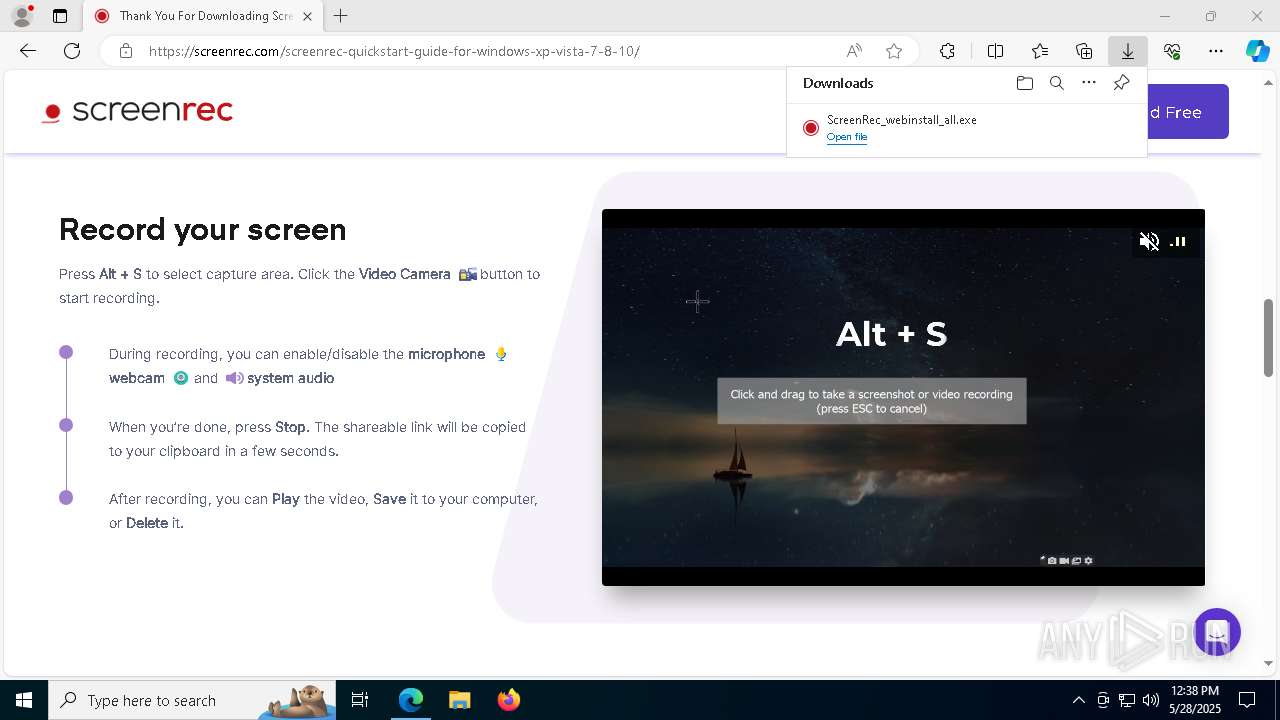
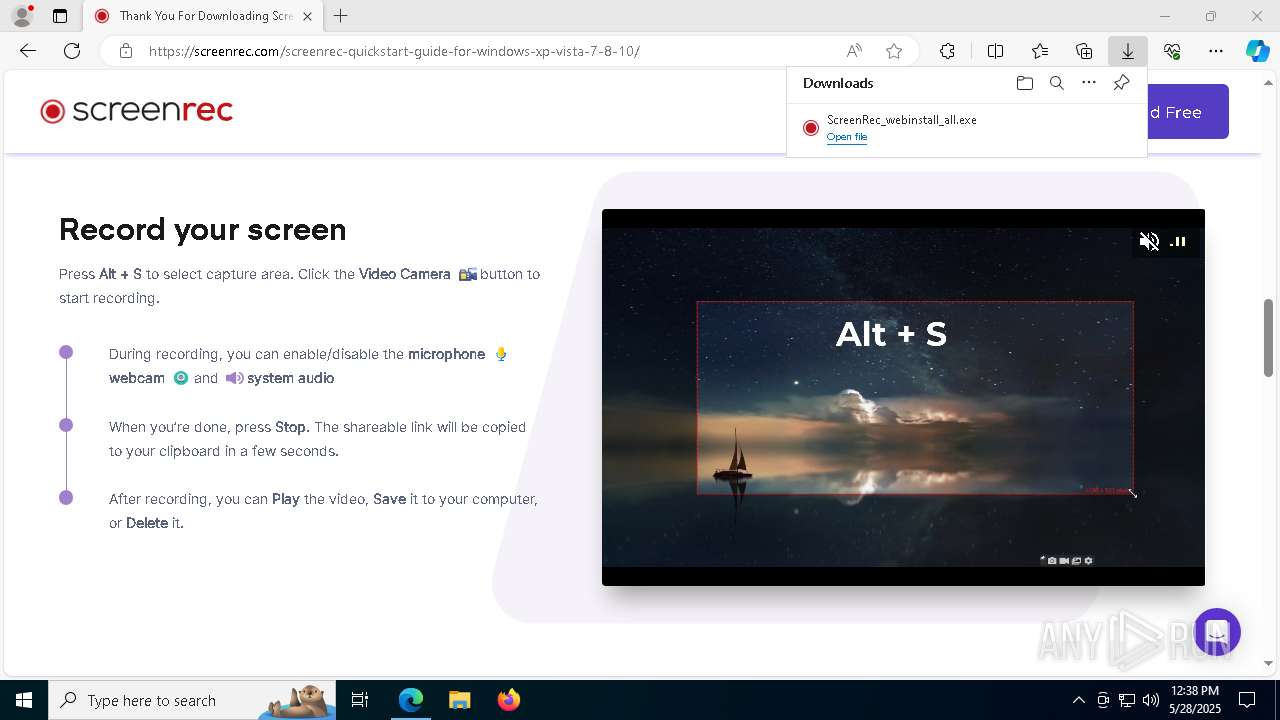
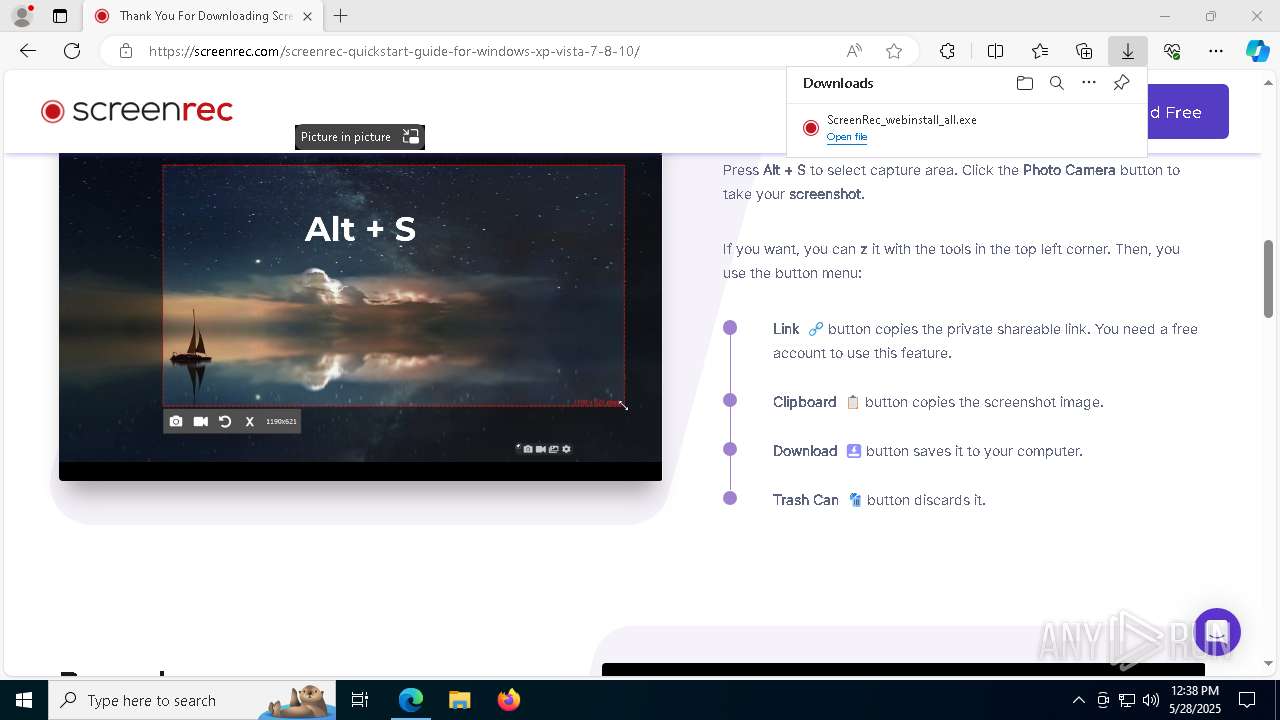
There is functionality for taking screenshot (YARA)
- ScreenRec_webinstall_all.exe (PID: 7744)
- screenrec.exe (PID: 5244)
The process drops C-runtime libraries
- ScreenRec_webinstall_all.exe (PID: 7744)
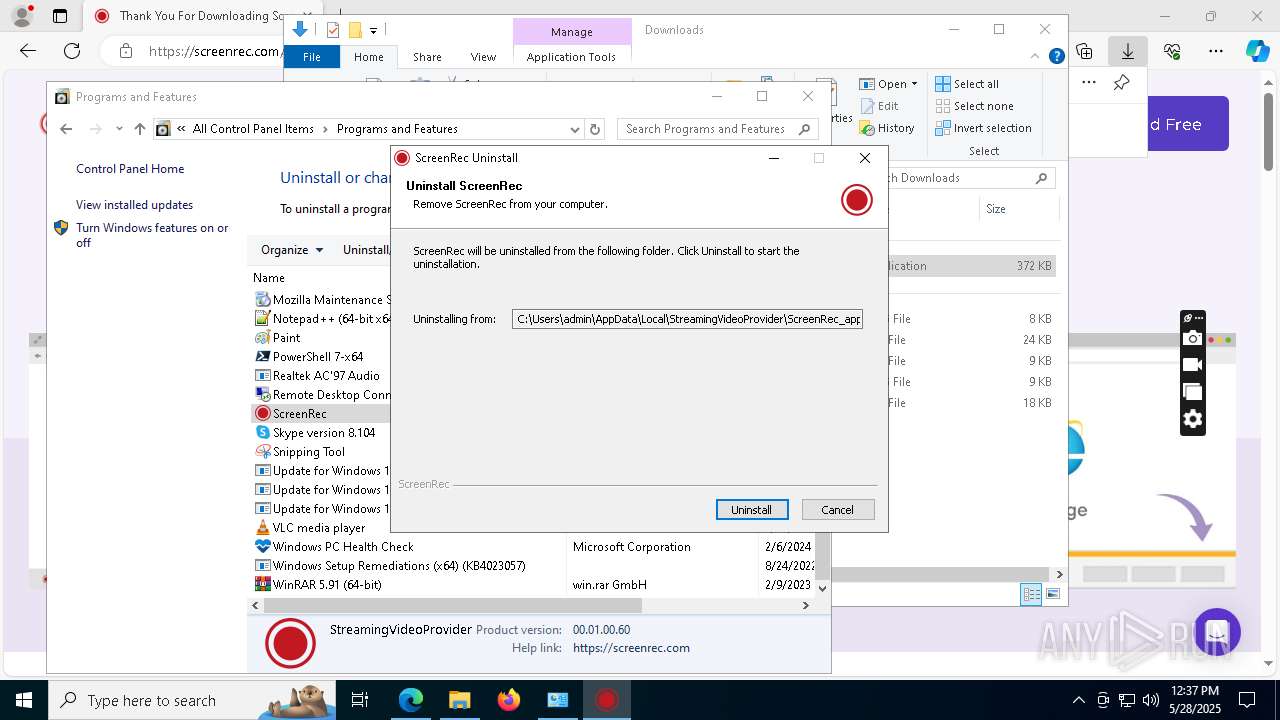
Starts itself from another location
- uninstall.exe (PID: 6476)
INFO
Reads the computer name
- identity_helper.exe (PID: 7820)
- identity_helper.exe (PID: 668)
- ScreenRec_webinstall_all.exe (PID: 7744)
- vc_redist.x64.exe (PID: 5212)
- screenrec.exe (PID: 5244)
Reads Environment values
- identity_helper.exe (PID: 7820)
- identity_helper.exe (PID: 668)
- screenrec.exe (PID: 5244)
Checks supported languages
- identity_helper.exe (PID: 7820)
- identity_helper.exe (PID: 668)
- ScreenRec_webinstall_all.exe (PID: 7744)
- vc_redist.x64.exe (PID: 5212)
- vc_redist.x64.exe (PID: 496)
- screenrec.exe (PID: 5244)
- crashpad_handler.exe (PID: 5056)
The sample compiled with english language support
- msedge.exe (PID: 4112)
- msedge.exe (PID: 7312)
- ScreenRec_webinstall_all.exe (PID: 7744)
- vc_redist.x64.exe (PID: 496)
- vc_redist.x64.exe (PID: 5212)
- uninstall.exe (PID: 6476)
Application launched itself
- msedge.exe (PID: 4112)
- msedge.exe (PID: 7908)
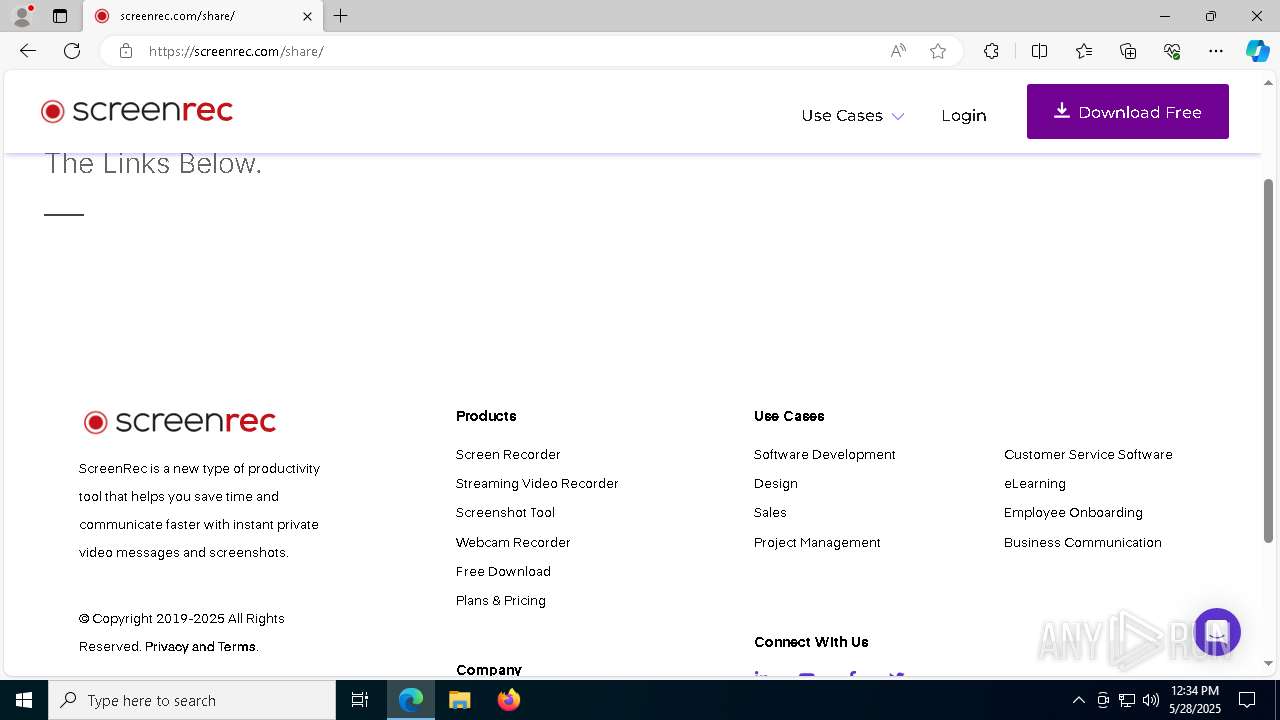
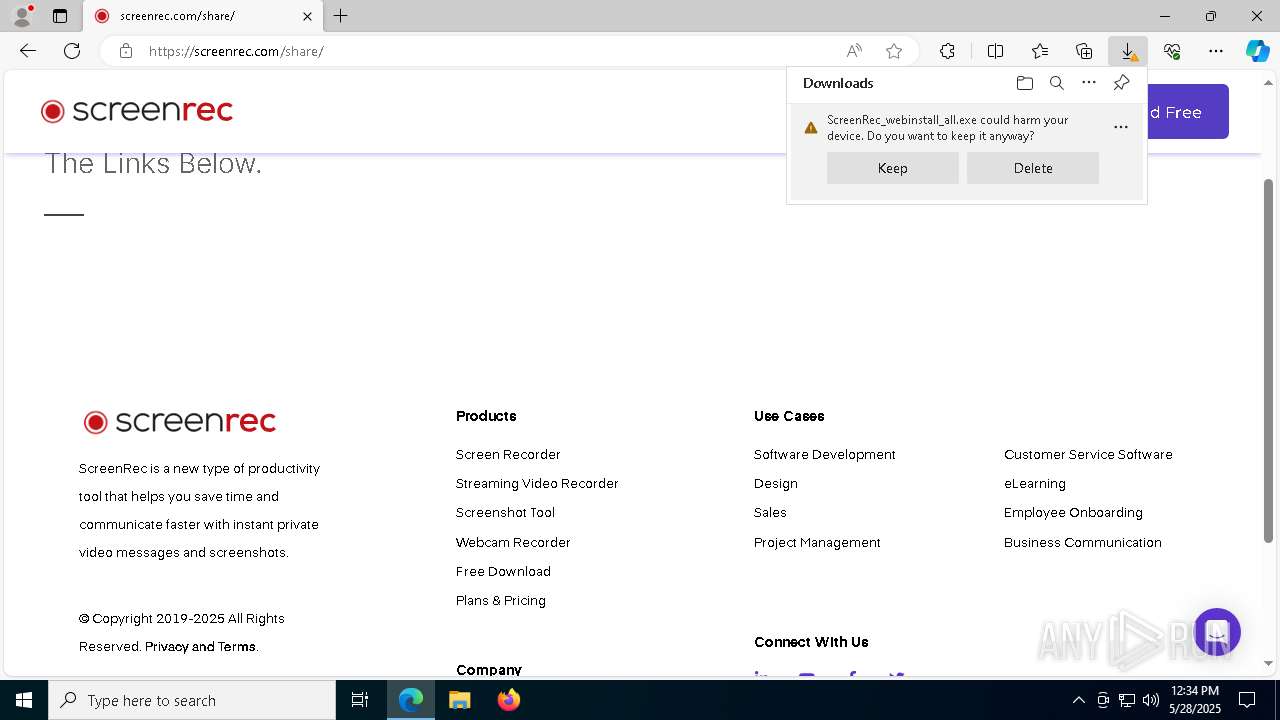
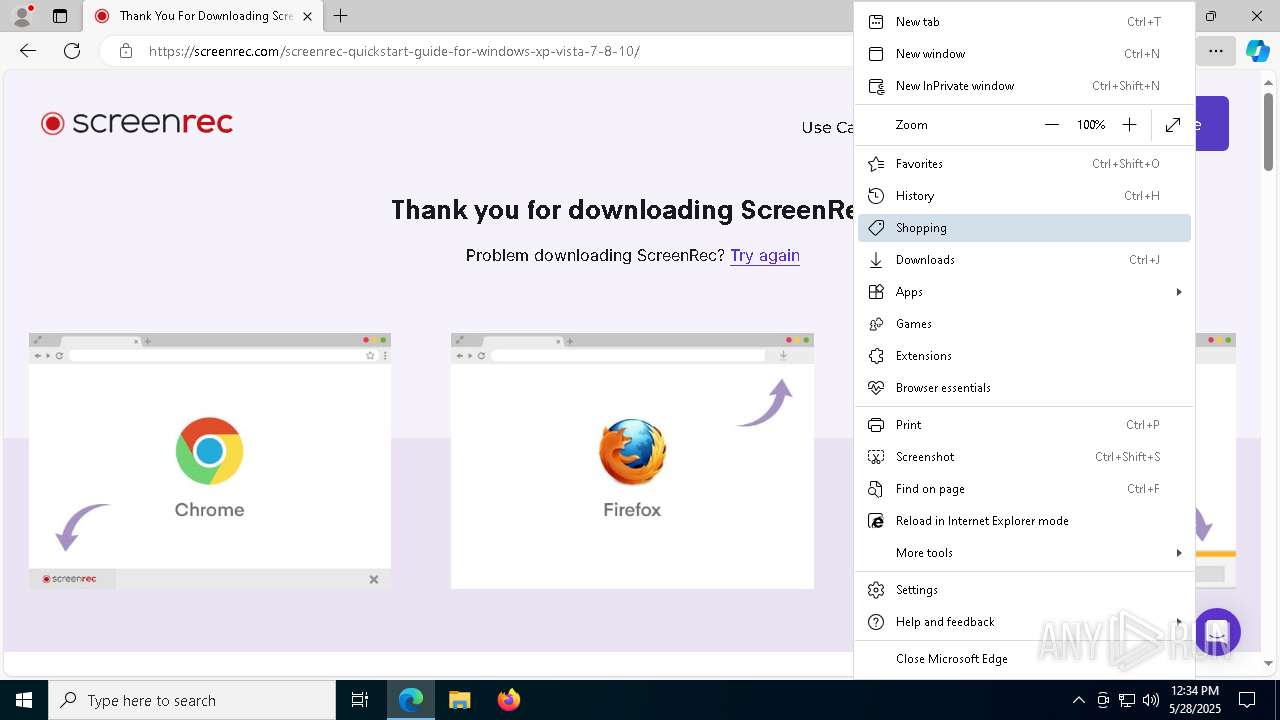
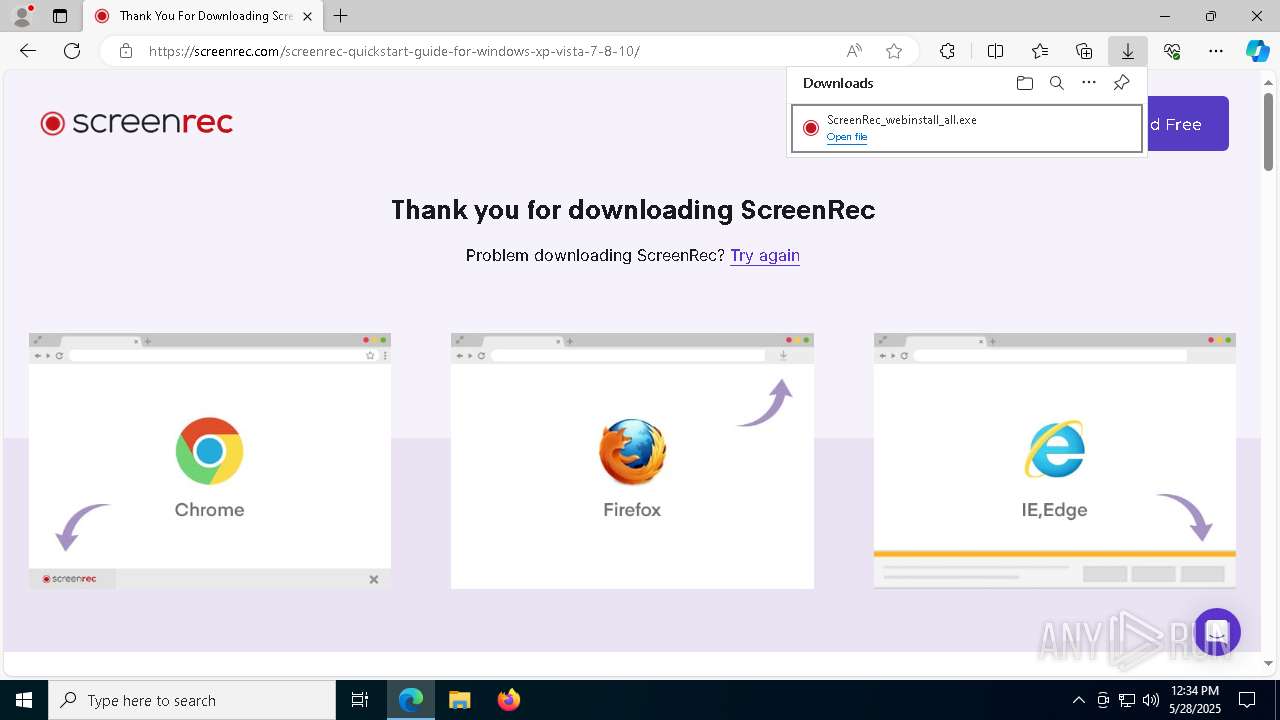
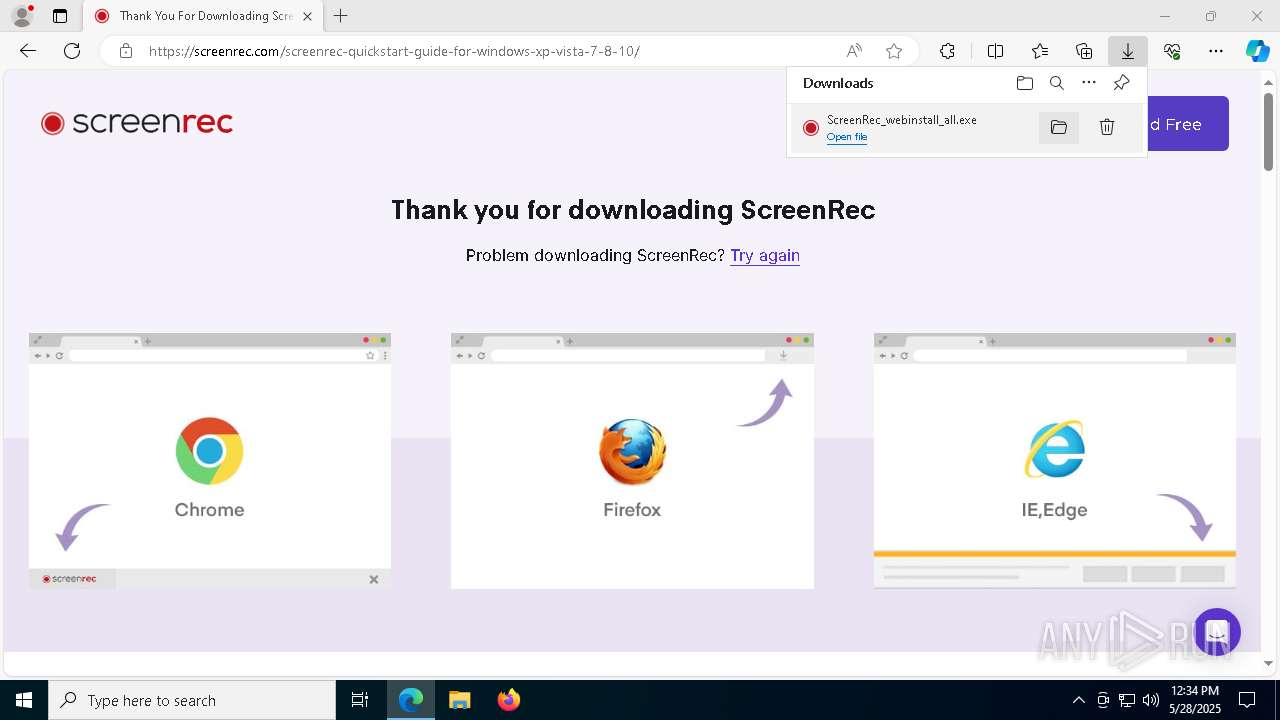
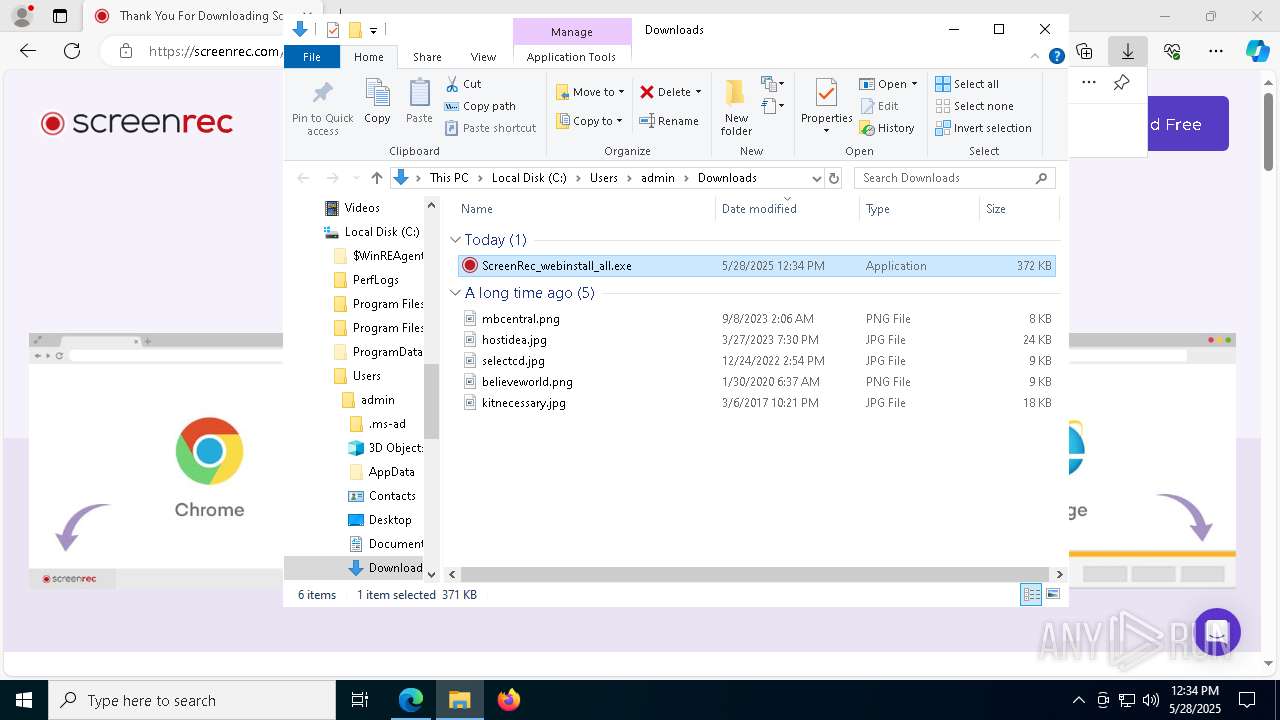
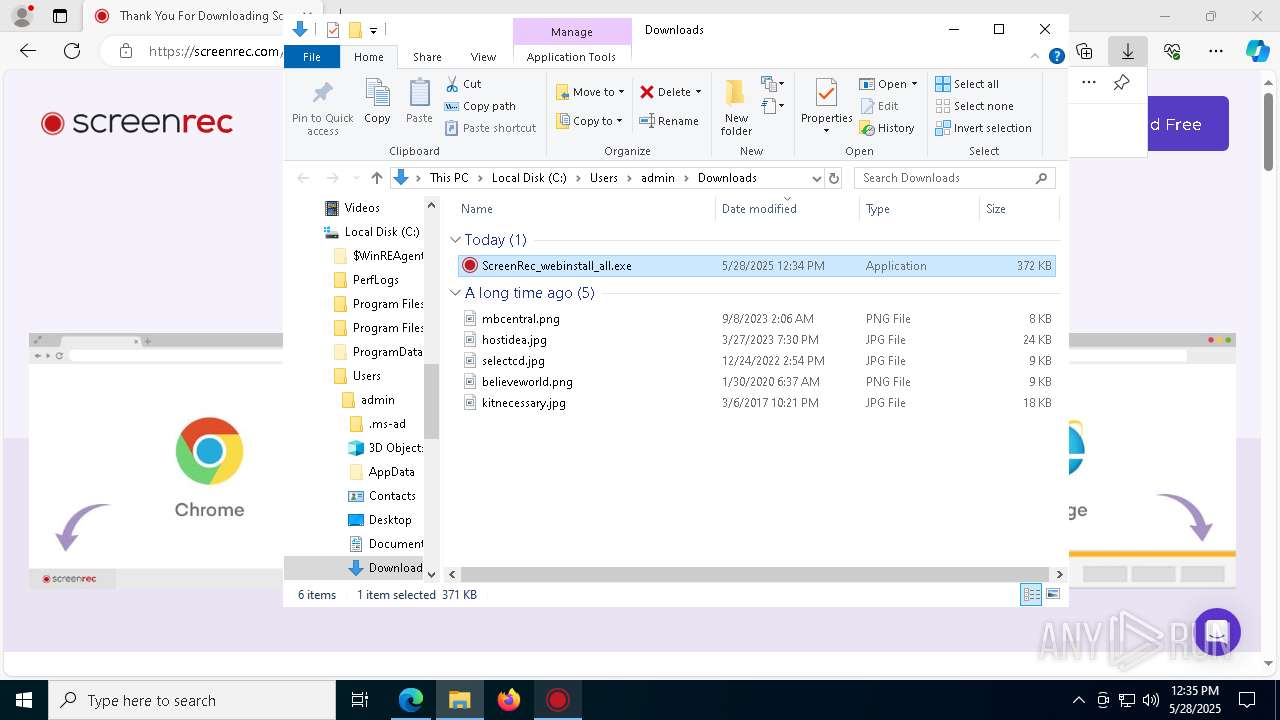
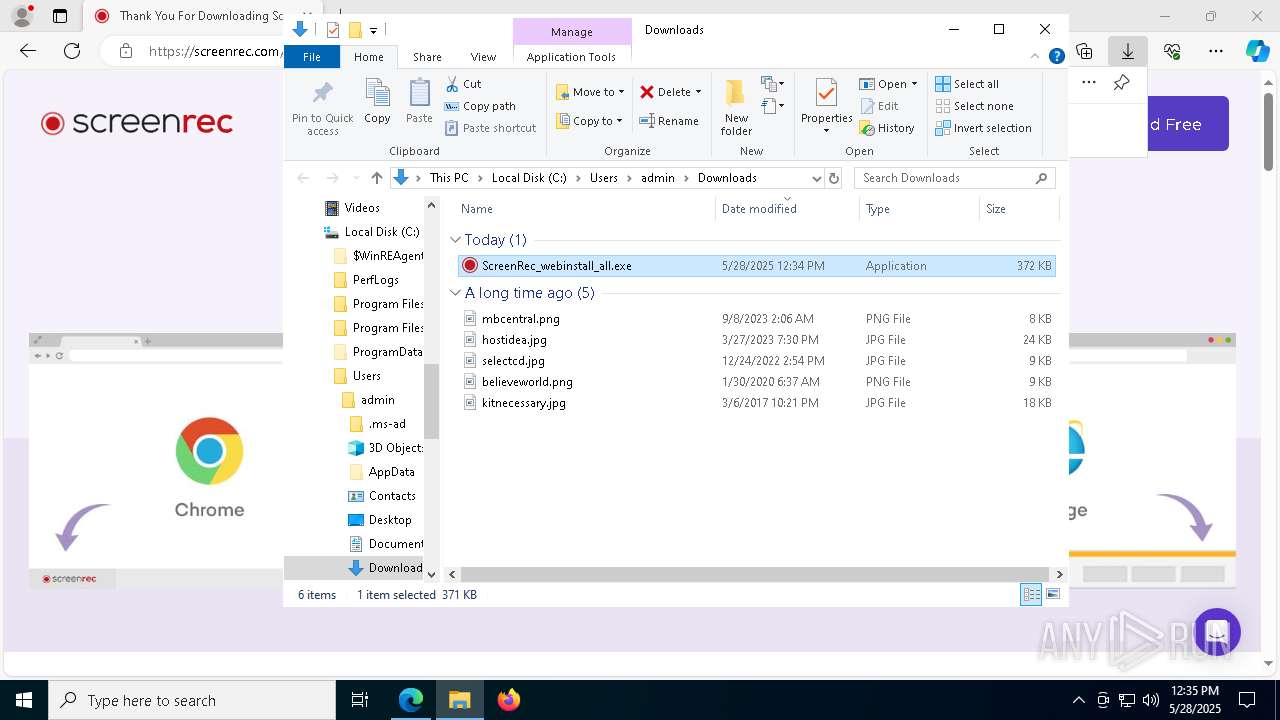
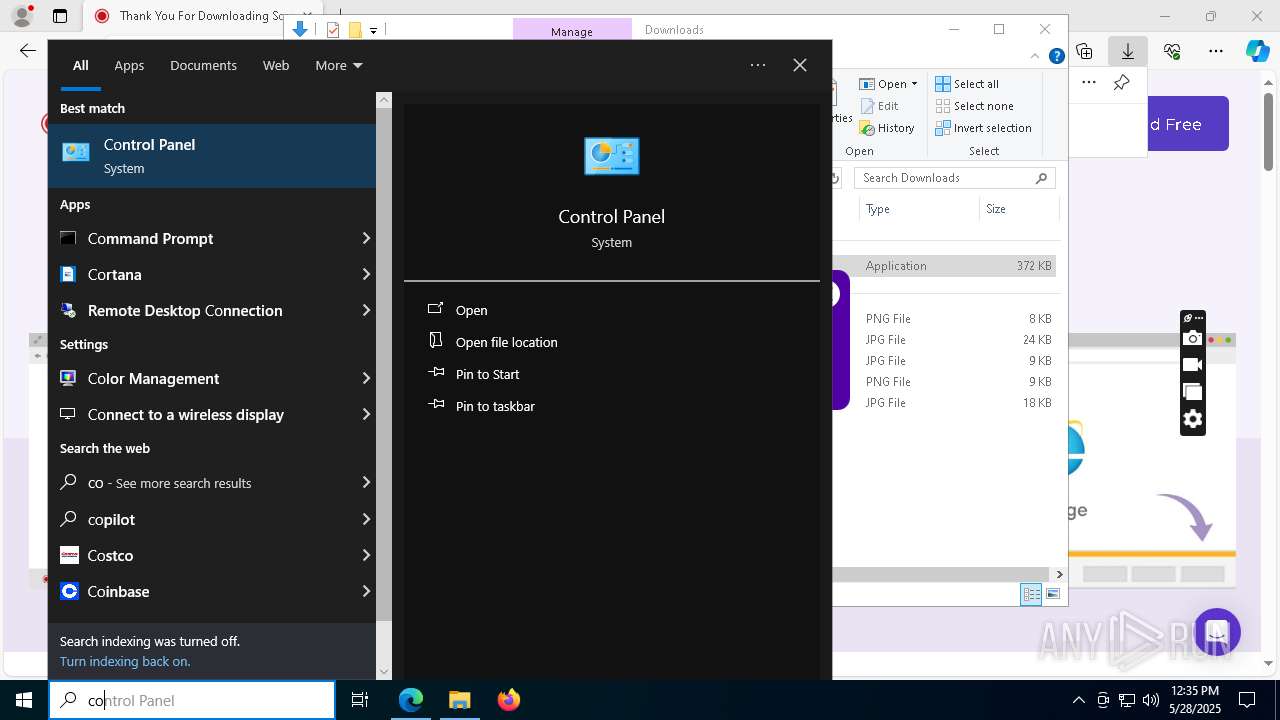
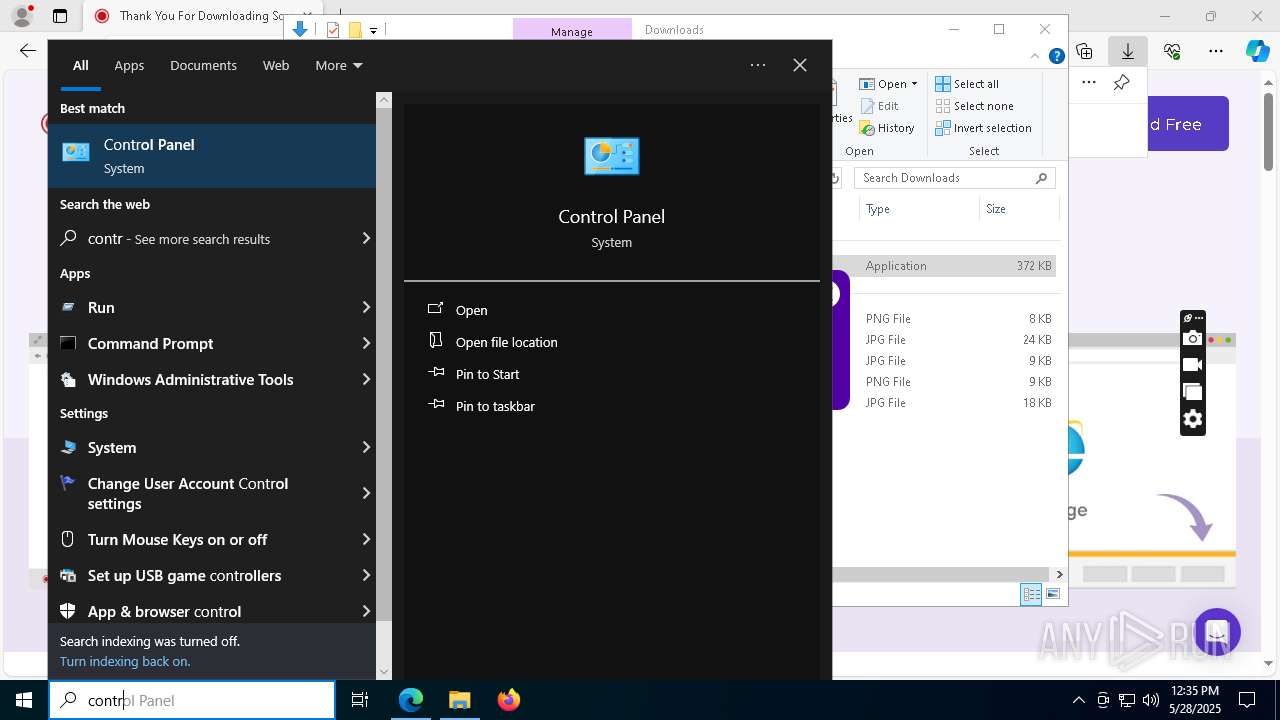
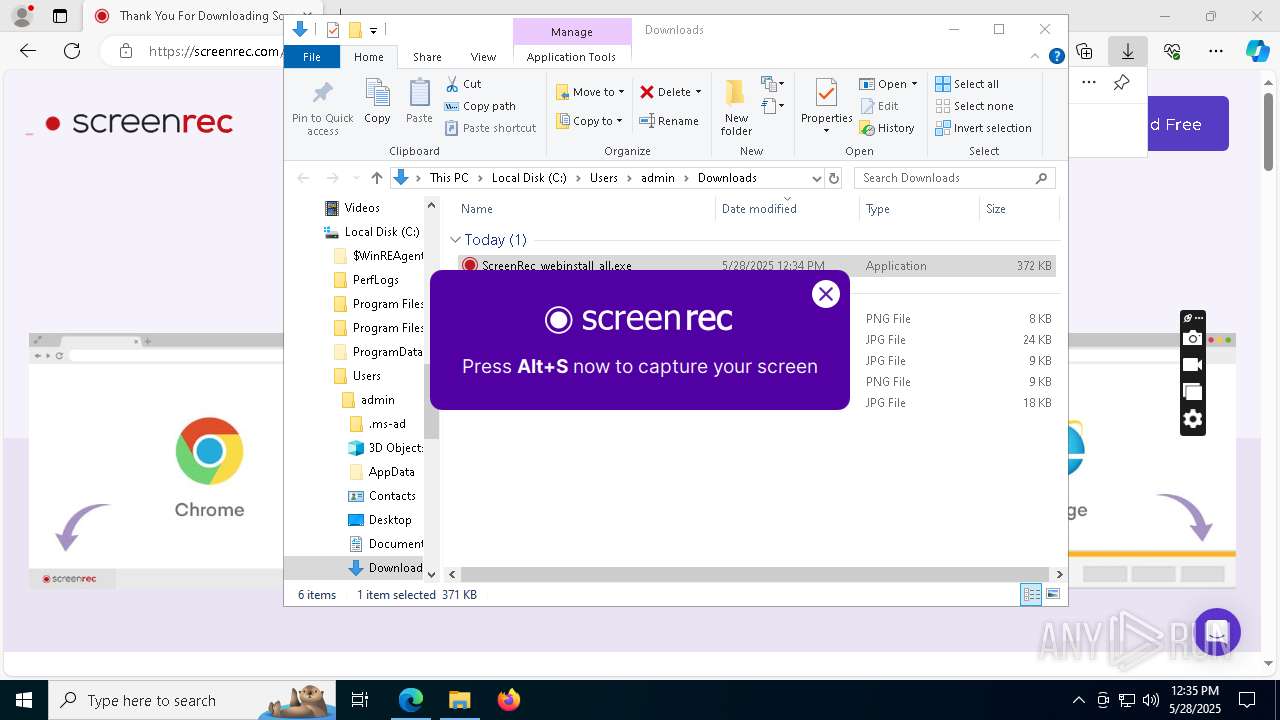
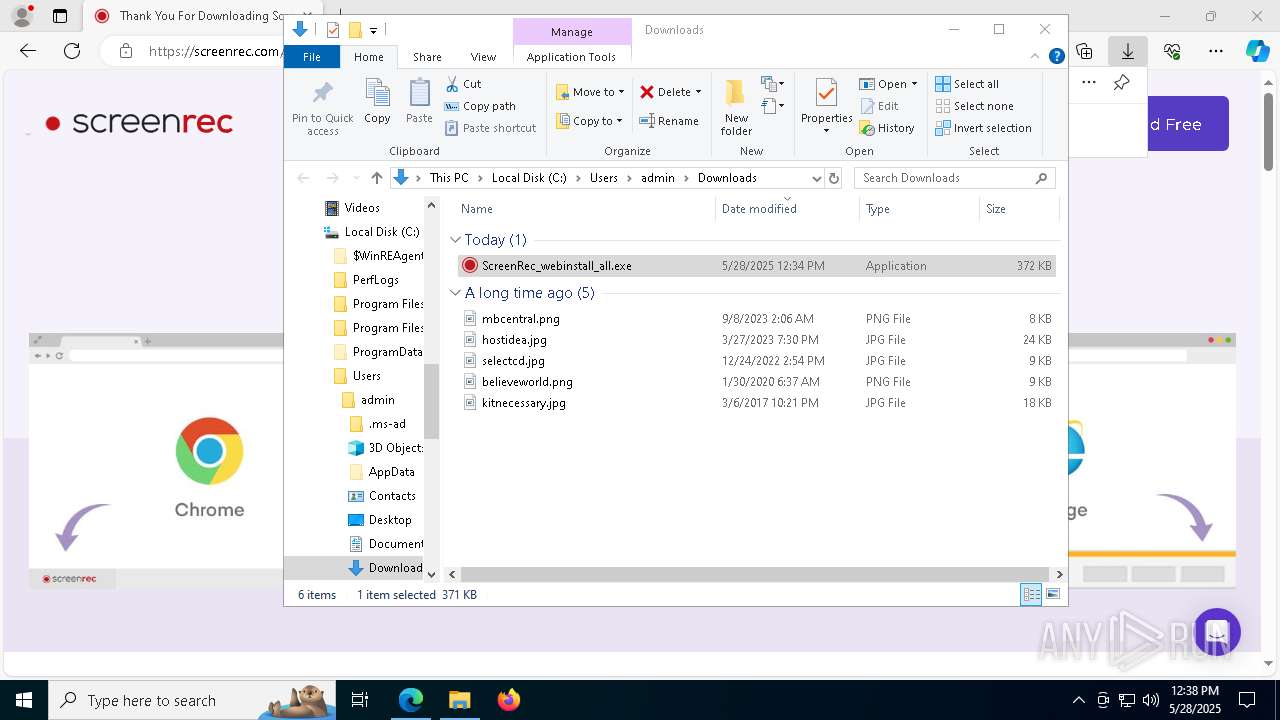
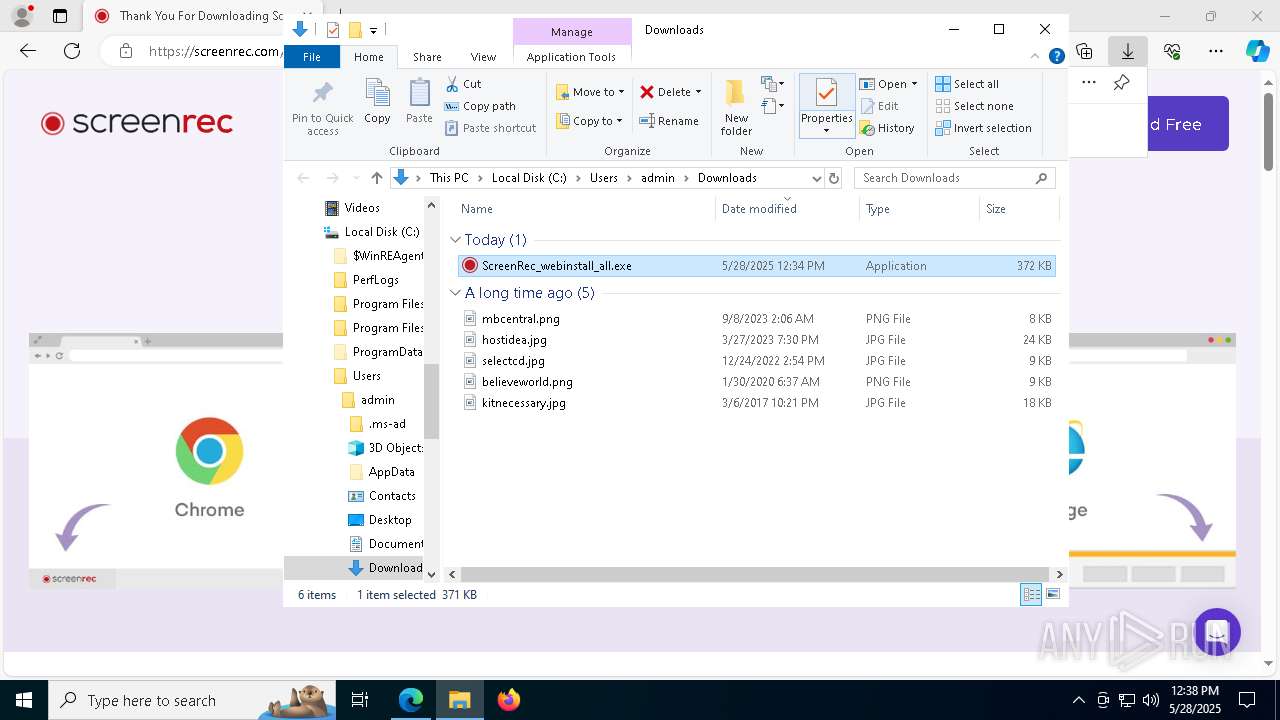
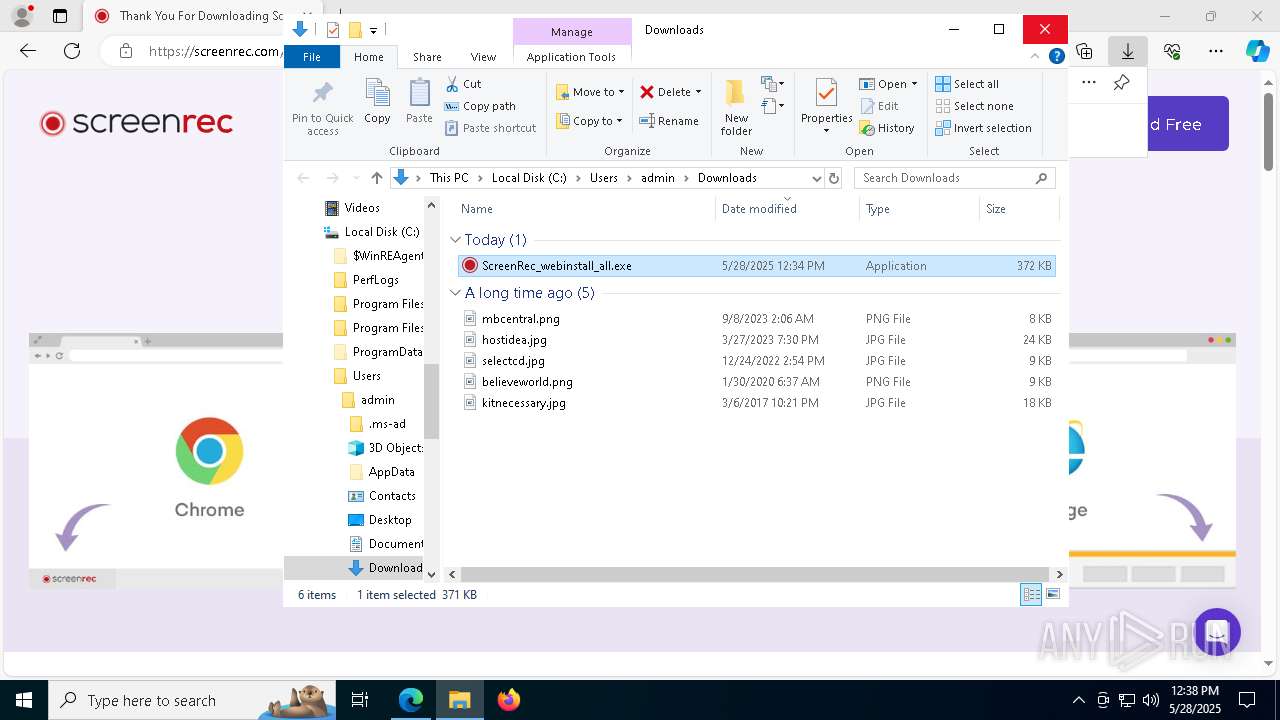
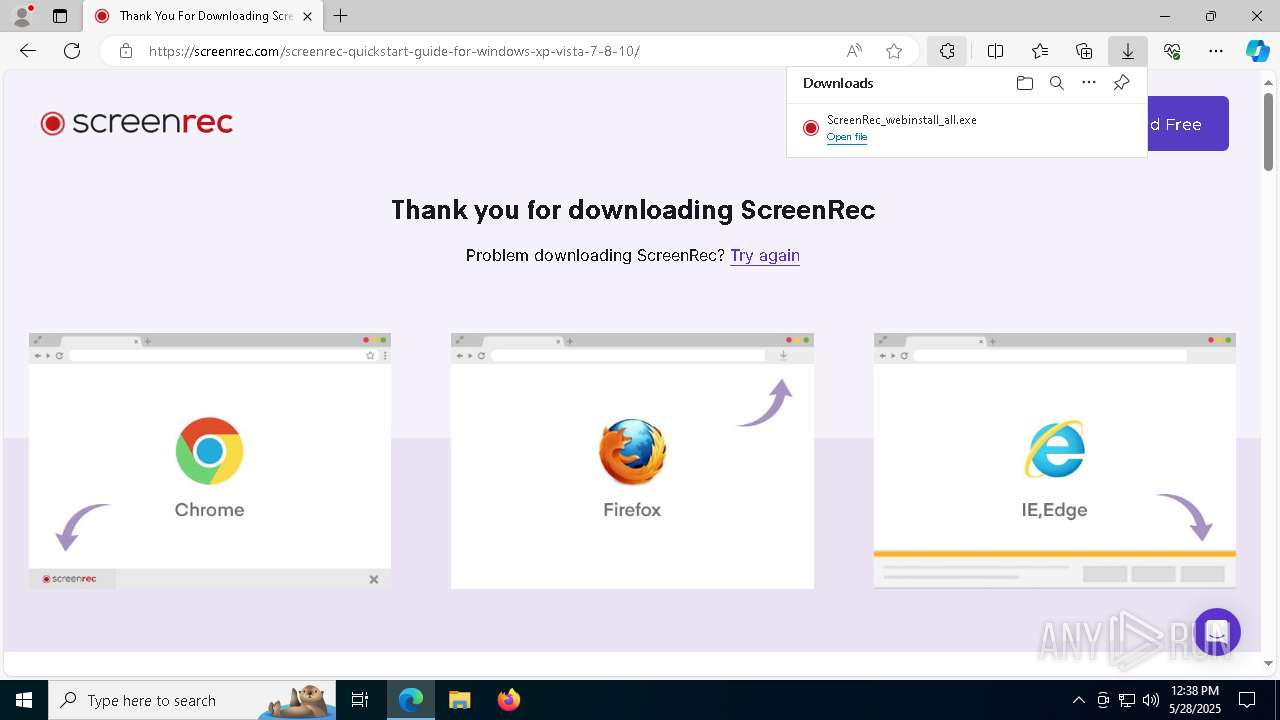
Launch of the file from Downloads directory
- msedge.exe (PID: 4112)
Reads security settings of Internet Explorer
- explorer.exe (PID: 5492)
Executable content was dropped or overwritten
- msedge.exe (PID: 7312)
- msedge.exe (PID: 4112)
Checks proxy server information
- explorer.exe (PID: 5492)
- ScreenRec_webinstall_all.exe (PID: 7744)
Creates files or folders in the user directory
- explorer.exe (PID: 5492)
- ScreenRec_webinstall_all.exe (PID: 7744)
- screenrec.exe (PID: 5244)
- crashpad_handler.exe (PID: 5056)
Reads the machine GUID from the registry
- ScreenRec_webinstall_all.exe (PID: 7744)
Reads the software policy settings
- ScreenRec_webinstall_all.exe (PID: 7744)
- explorer.exe (PID: 5492)
- slui.exe (PID: 2568)
Create files in a temporary directory
- ScreenRec_webinstall_all.exe (PID: 7744)
- vc_redist.x64.exe (PID: 496)
- vc_redist.x64.exe (PID: 5212)
- screenrec.exe (PID: 5244)
Launch of the file from Registry key
- ScreenRec_webinstall_all.exe (PID: 7744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
225
Monitored processes
80
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --mojo-platform-channel-handle=7236 --field-trial-handle=2312,i,16036444125555612849,9085793100895220079,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4896 --field-trial-handle=2420,i,2730440633673650740,6346421152928869551,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 496 | "C:\Users\admin\AppData\Local\StreamingVideoProvider\ScreenRec_app\vc_redist.x64.exe" /passive /norestart | C:\Users\admin\AppData\Local\StreamingVideoProvider\ScreenRec_app\vc_redist.x64.exe | ScreenRec_webinstall_all.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2015-2019 Redistributable (x64) - 14.29.30139 Exit code: 1638 Version: 14.29.30139.0 Modules
| |||||||||||||||
| 512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4864 --field-trial-handle=2420,i,2730440633673650740,6346421152928869551,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 524 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2588 --field-trial-handle=2420,i,2730440633673650740,6346421152928869551,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 668 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7212 --field-trial-handle=2312,i,16036444125555612849,9085793100895220079,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 896 | "C:\Users\admin\AppData\Local\Temp\~nsu1.tmp\Un.exe" _?=C:\Users\admin\AppData\Local\StreamingVideoProvider\ScreenRec_app\ | C:\Users\admin\AppData\Local\Temp\~nsu1.tmp\Un.exe | uninstall.exe | ||||||||||||
User: admin Company: StreamingVideoProvider Integrity Level: MEDIUM Description: Desktop Recording application Exit code: 0 Version: 00.01.00.59 Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1300 --field-trial-handle=2312,i,16036444125555612849,9085793100895220079,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6852 --field-trial-handle=2312,i,16036444125555612849,9085793100895220079,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4896 --field-trial-handle=2420,i,2730440633673650740,6346421152928869551,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
133 305
Read events
132 933
Write events
356
Delete events
16
Modification events
| (PID) Process: | (4112) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4112) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4112) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4112) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4112) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 87B9D7ADC7942F00 | |||
| (PID) Process: | (4112) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7513E0ADC7942F00 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:0000000000040282 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (4112) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B14D09AEC7942F00 | |||
| (PID) Process: | (4112) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262786 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FAED989E-CFC6-4BCA-A1E3-26E75433E88B} | |||
| (PID) Process: | (4112) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262786 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {AE9F728D-201C-4C7D-A677-F216081EB681} | |||
Executable files
177
Suspicious files
266
Text files
429
Unknown types
124
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4112 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10a961.TMP | — | |
MD5:— | SHA256:— | |||
| 4112 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4112 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10a961.TMP | — | |
MD5:— | SHA256:— | |||
| 4112 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4112 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10a990.TMP | — | |
MD5:— | SHA256:— | |||
| 4112 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4112 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF10a9ee.TMP | — | |
MD5:— | SHA256:— | |||
| 4112 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4112 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10a9ee.TMP | — | |
MD5:— | SHA256:— | |||
| 4112 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
141
DNS requests
141
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5796 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7312 | msedge.exe | GET | 200 | 104.18.38.233:80 | http://crt.sectigo.com/SectigoRSADomainValidationSecureServerCA.crt | unknown | — | — | whitelisted |
1072 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1072 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5492 | explorer.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
5492 | explorer.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | — | — | whitelisted |
5492 | explorer.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEE%2BWeYWDRE0e4Ng2URD5nLU%3D | unknown | — | — | whitelisted |
7744 | ScreenRec_webinstall_all.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5796 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2560 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4112 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7312 | msedge.exe | 95.179.209.76:443 | screenrec.com | AS-CHOOPA | FR | suspicious |
7312 | msedge.exe | 52.123.224.68:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
screenrec.com |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |