| File name: | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.7z |
| Full analysis: | https://app.any.run/tasks/19f322bb-09aa-427c-acfd-0ef07eb52f31 |
| Verdict: | Malicious activity |
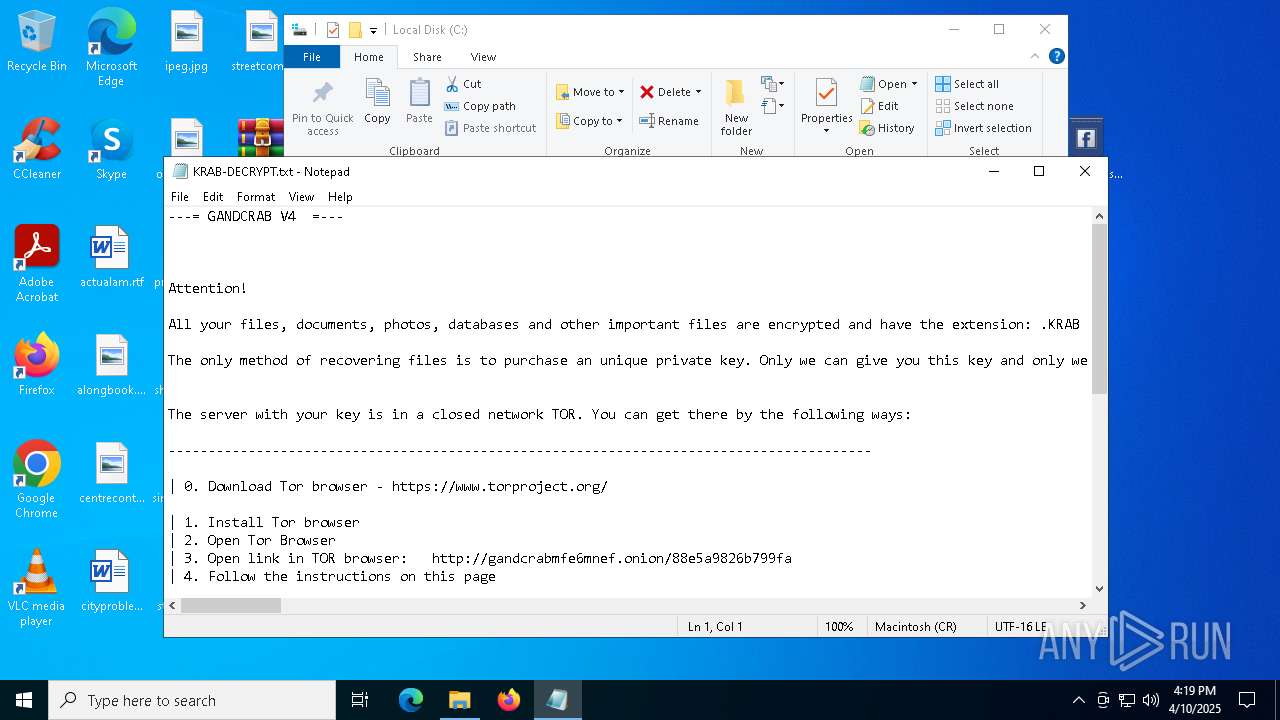
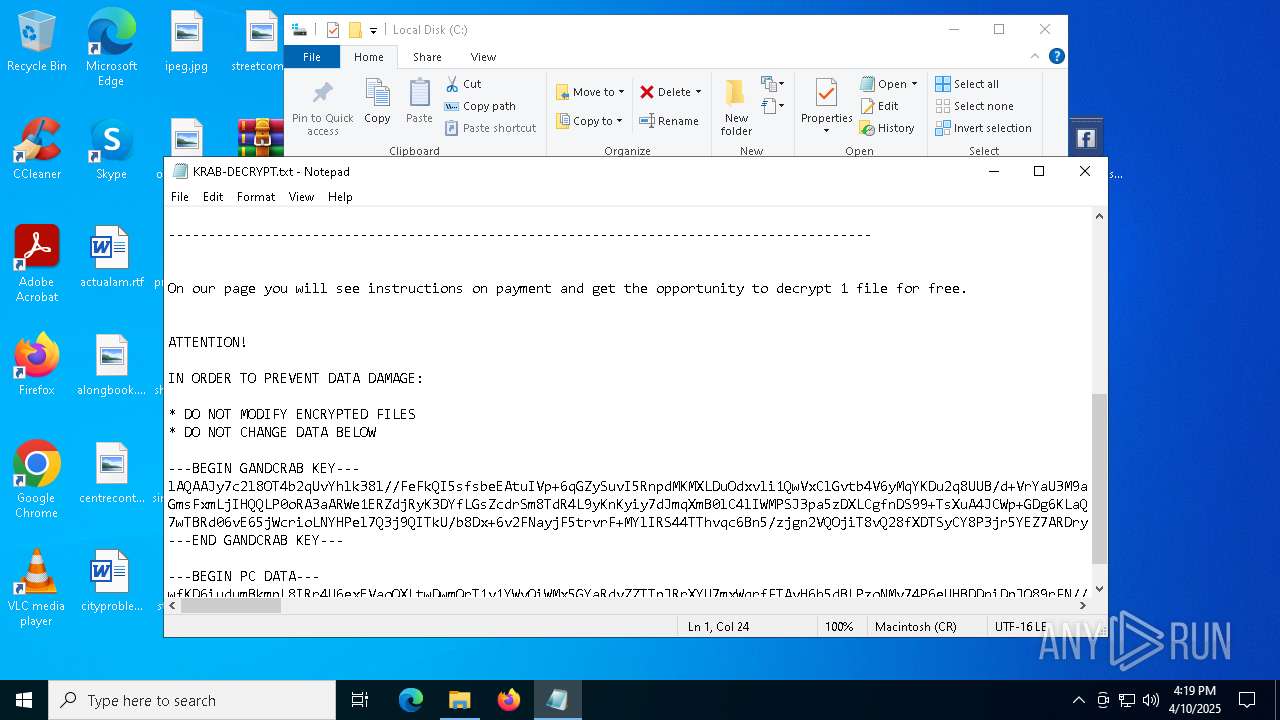
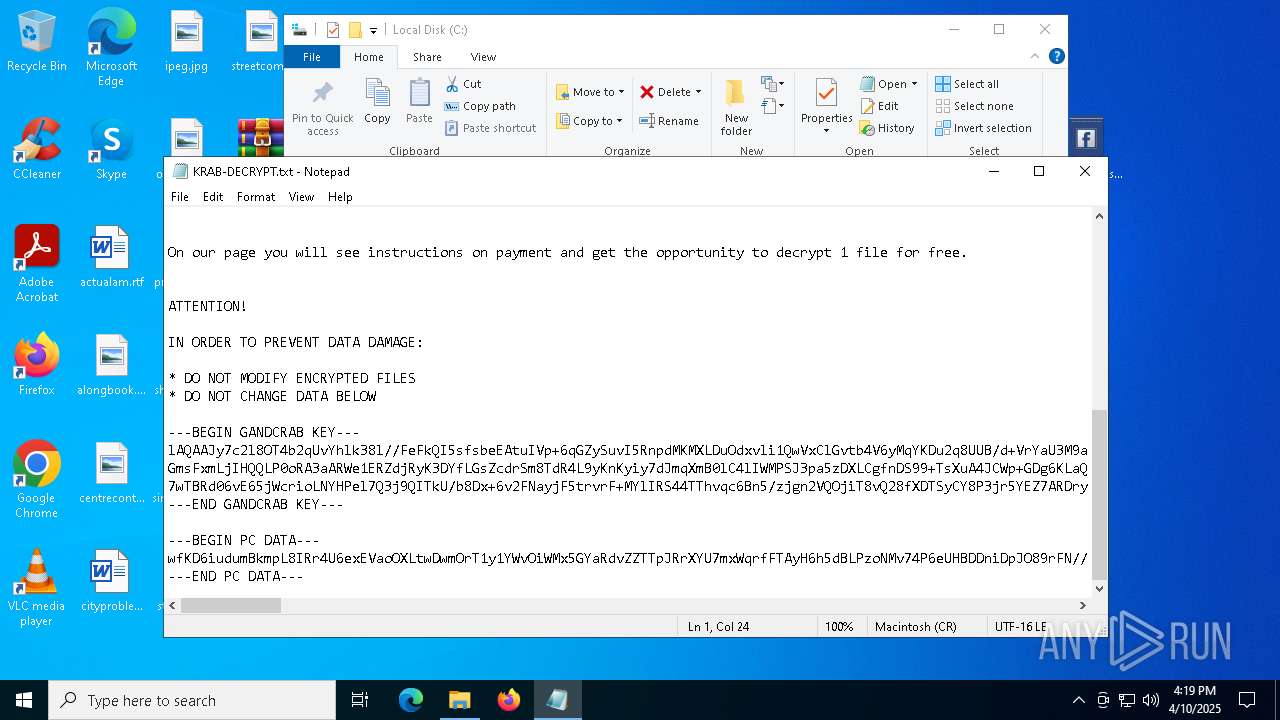
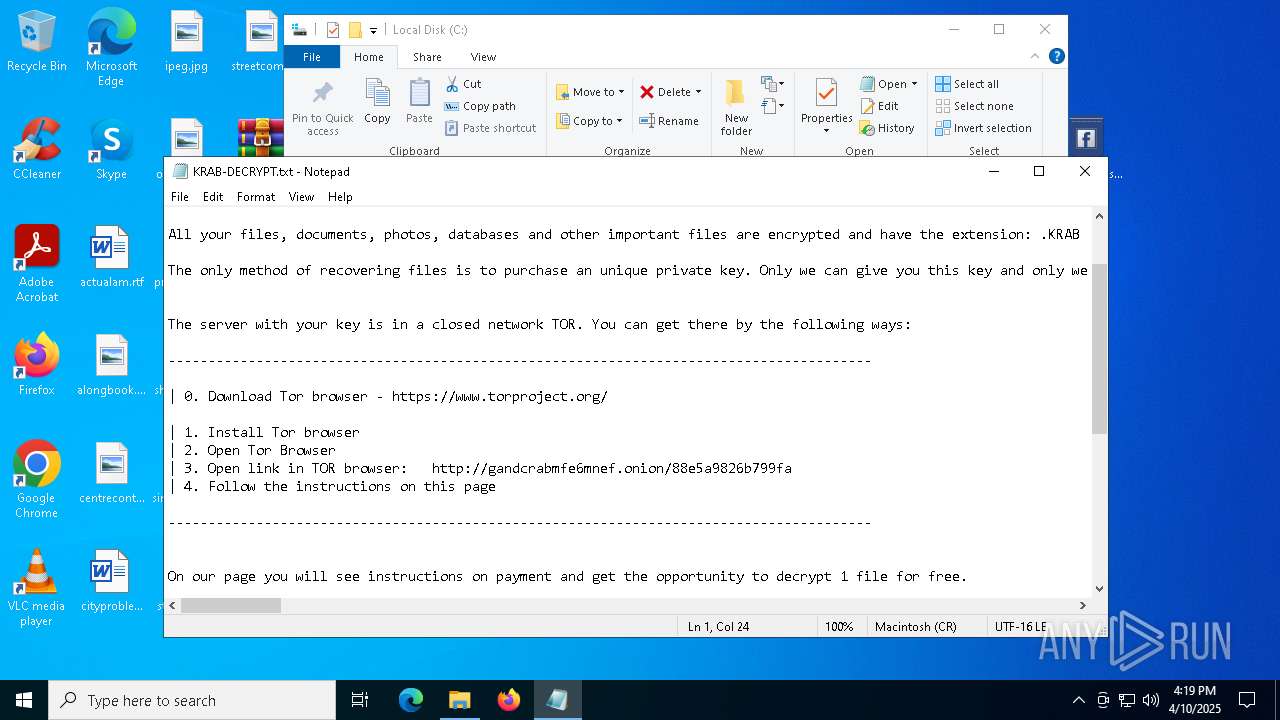
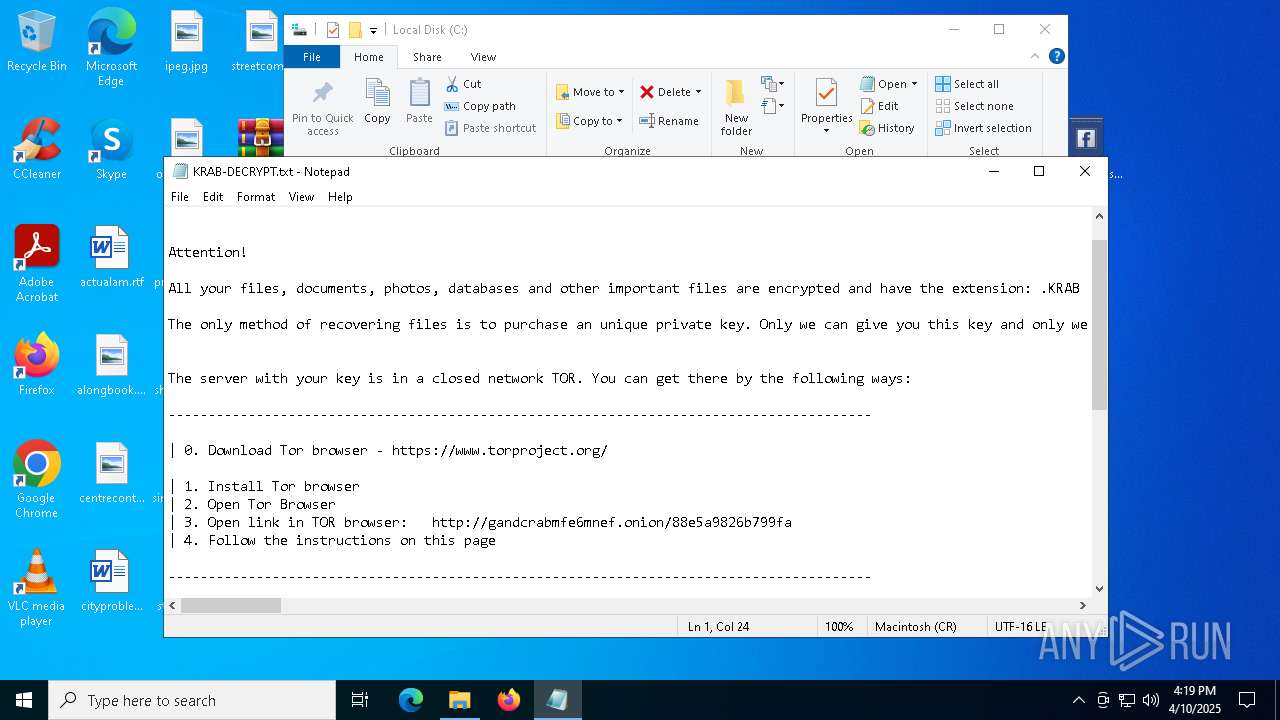
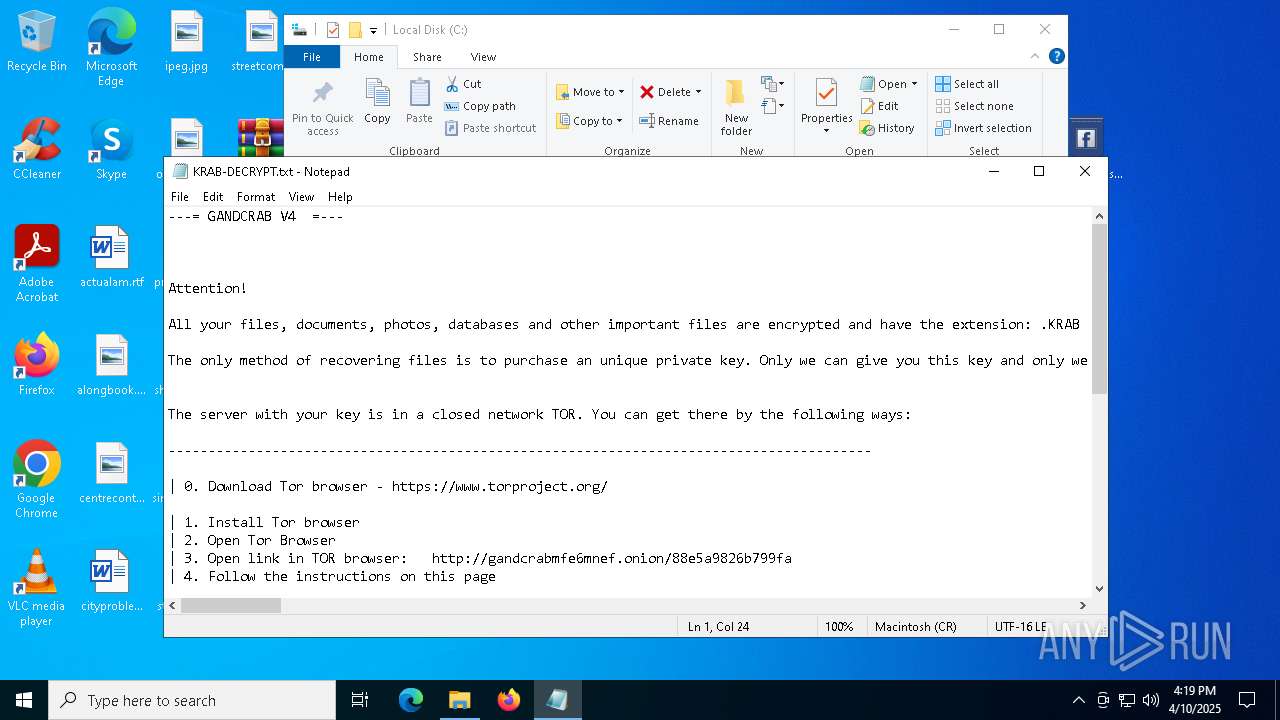
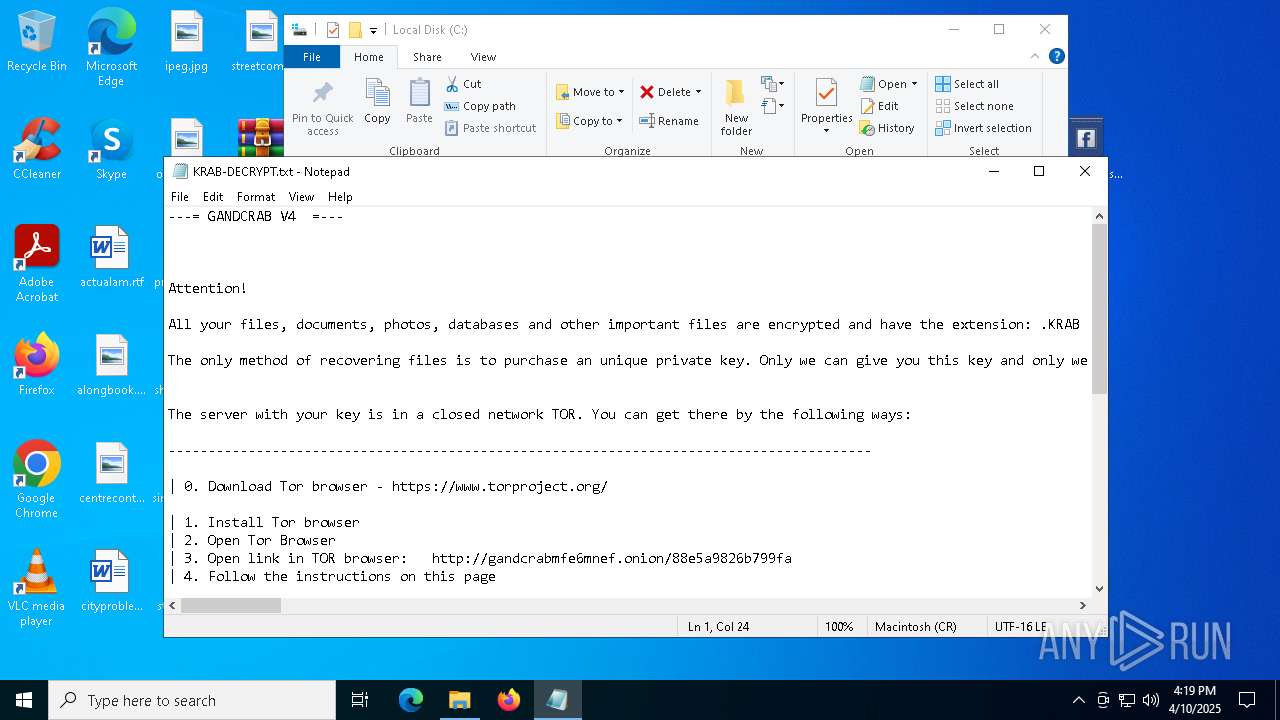
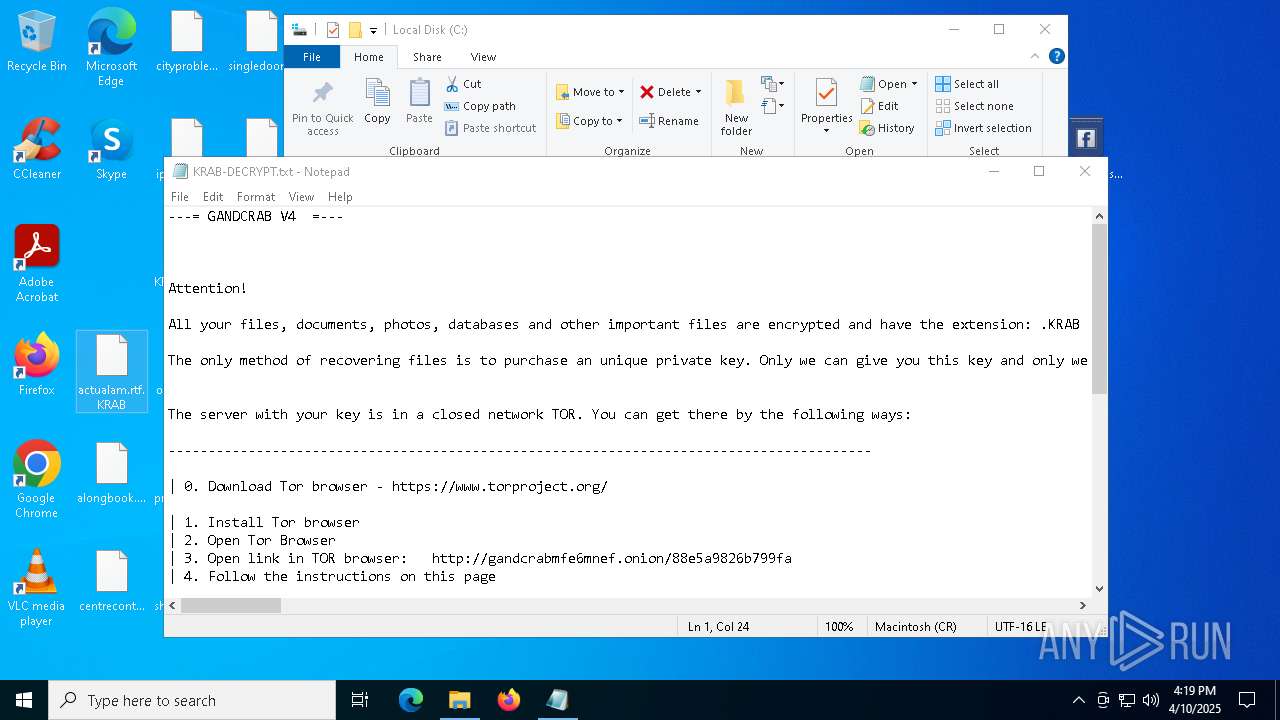
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | April 10, 2025, 16:17:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 592AB94B2A6AAC027A19E0A84DA7A363 |
| SHA1: | CAB25296704362320490BE44AB4F6FA2C3DF8762 |
| SHA256: | 20DEE2A951204608A6118F50AD77A49F3BC4AD34C6258D485C2AA7A9558AF1B1 |
| SSDEEP: | 12288:u7ACg4gA6mmNs+vH+DyZVn/q8YyEmNrV6BvzQWh+fX3qk7tbBJmJ:u7ACg4B6mmNs+veDyZVi3yEmNrV6BcW1 |
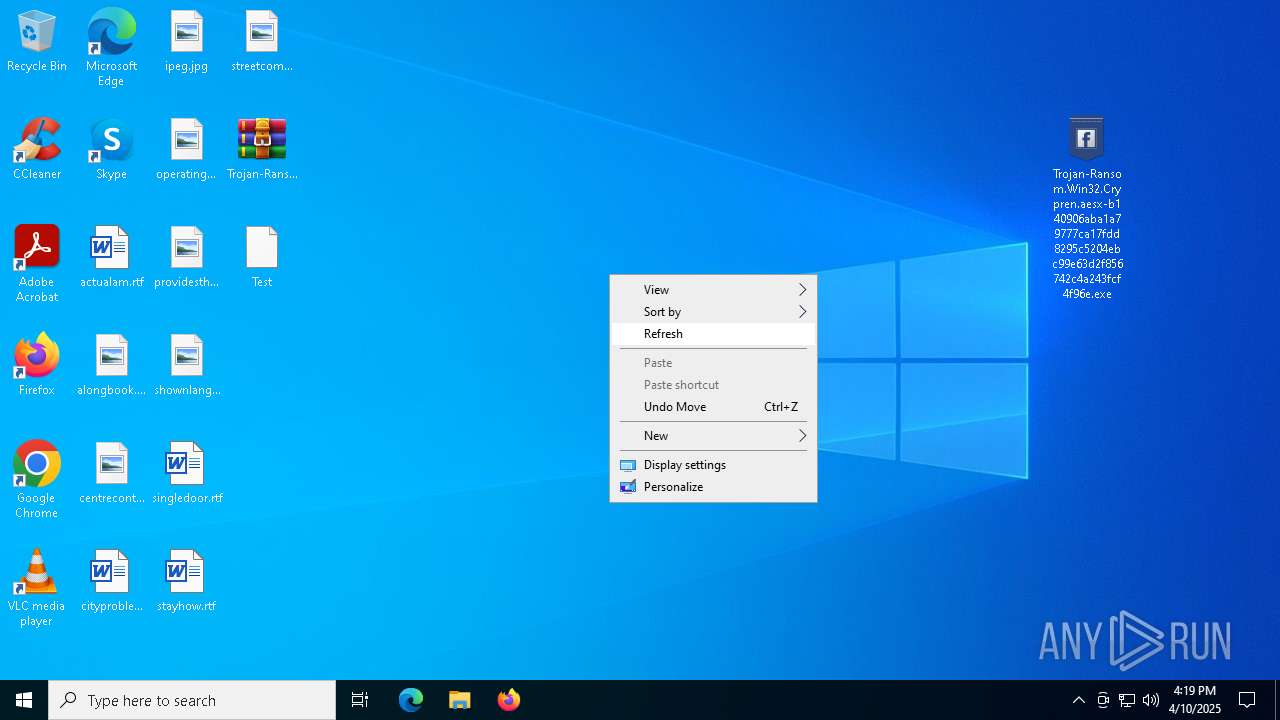
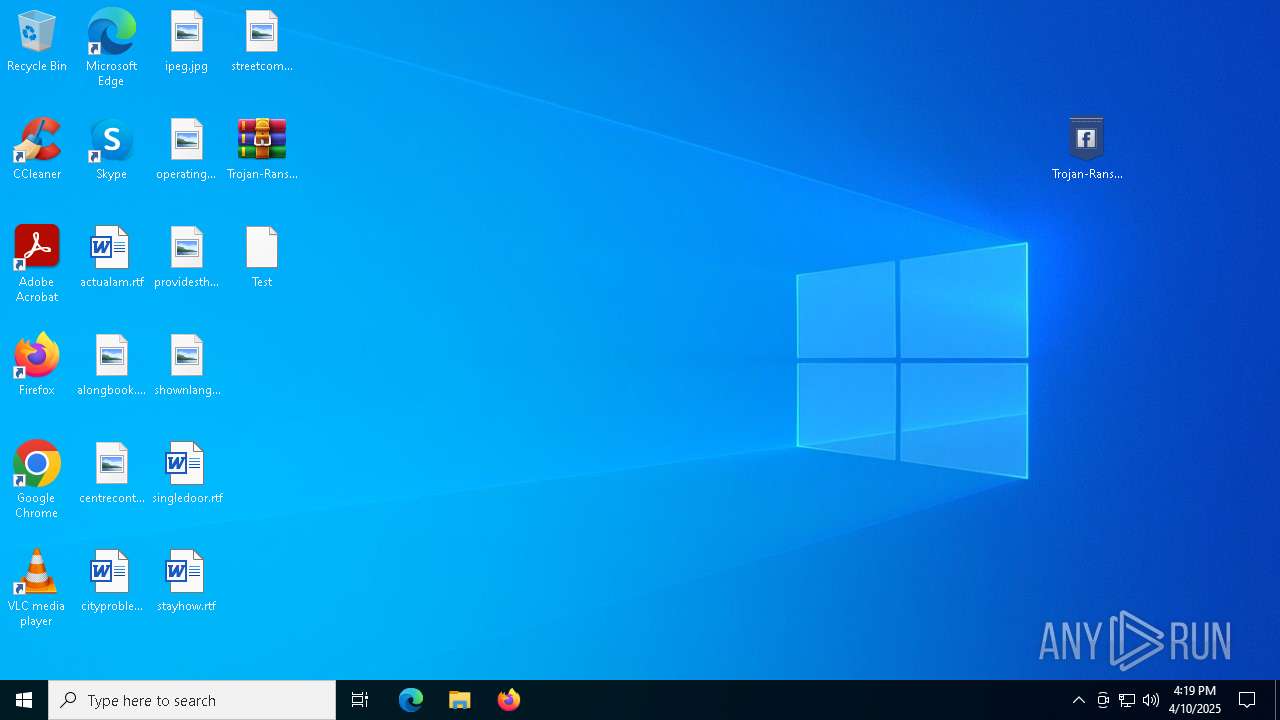
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 4300)
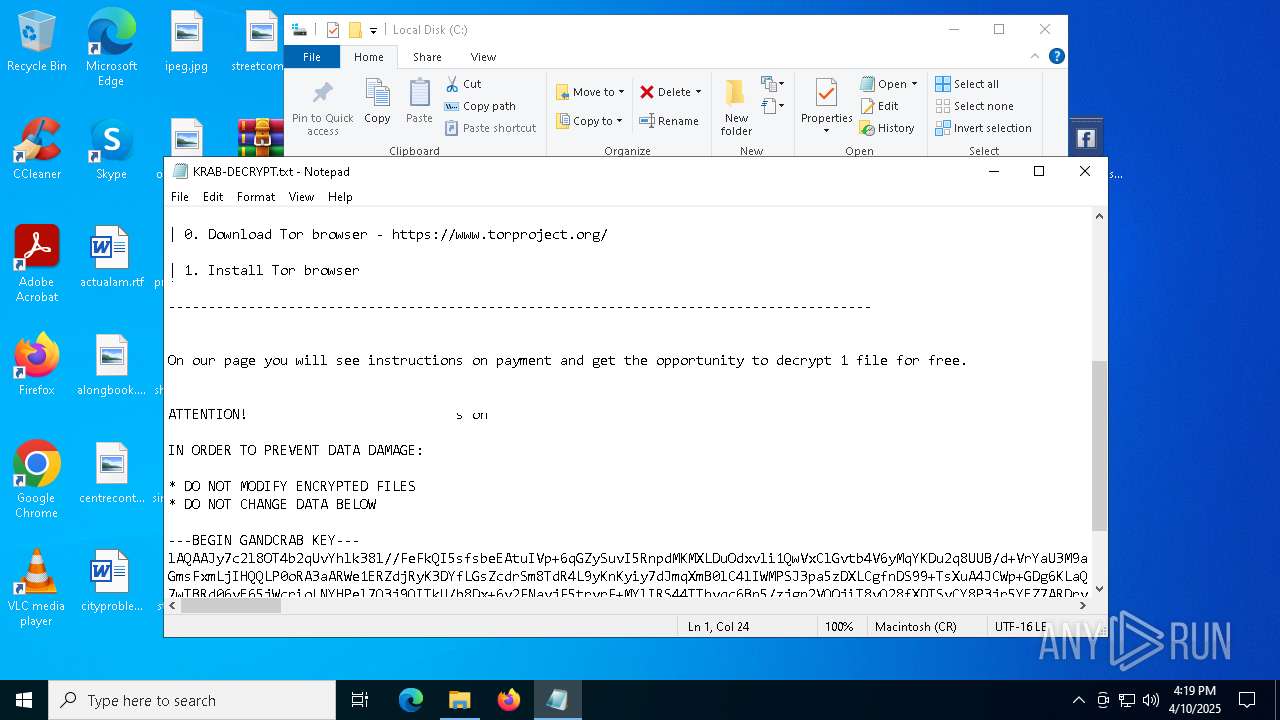
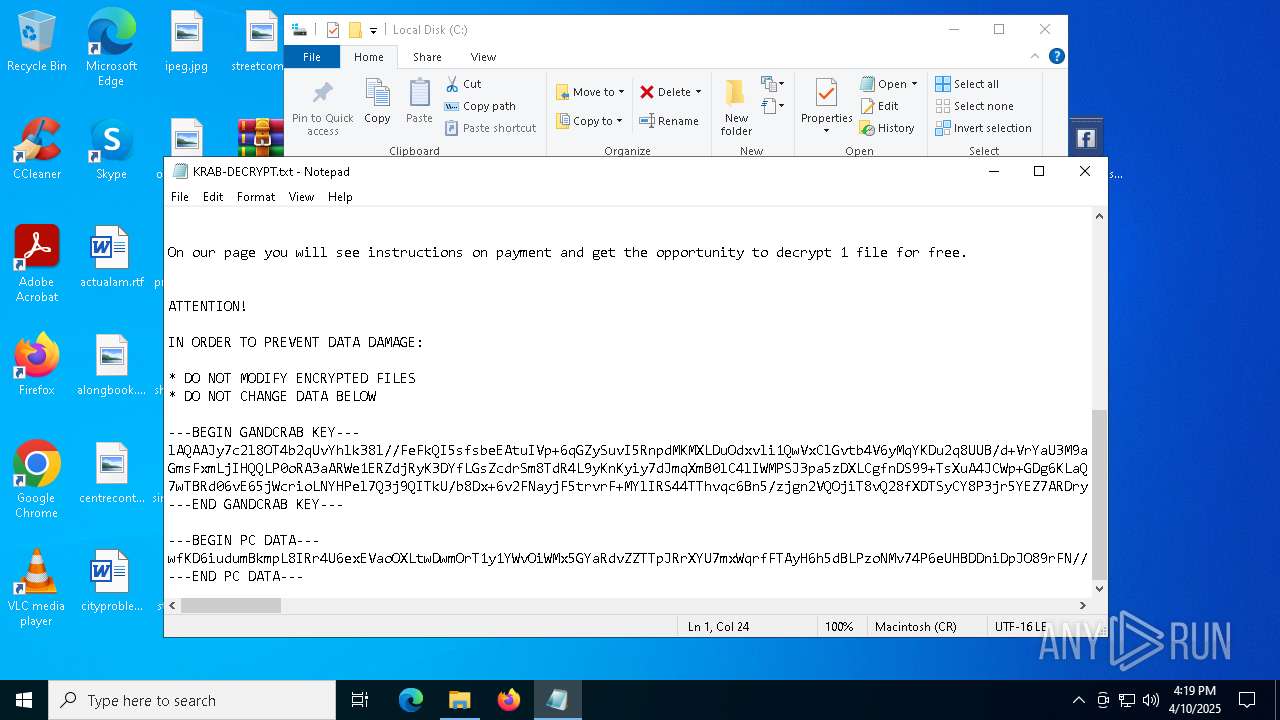
GandCrab keys are found
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
RANSOMWARE has been detected
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
GANDCRAB has been detected (SURICATA)
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
XORed URL has been found (YARA)
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
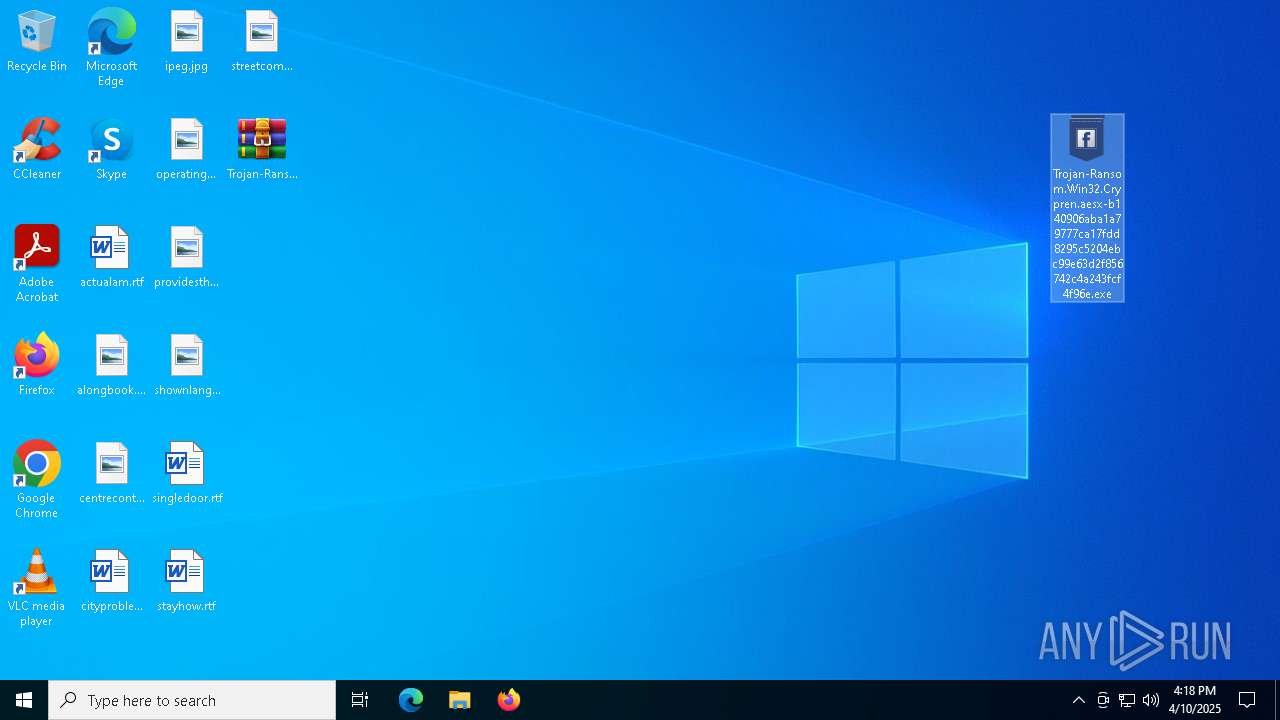
Writes a file to the Word startup folder
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
Actions looks like stealing of personal data
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
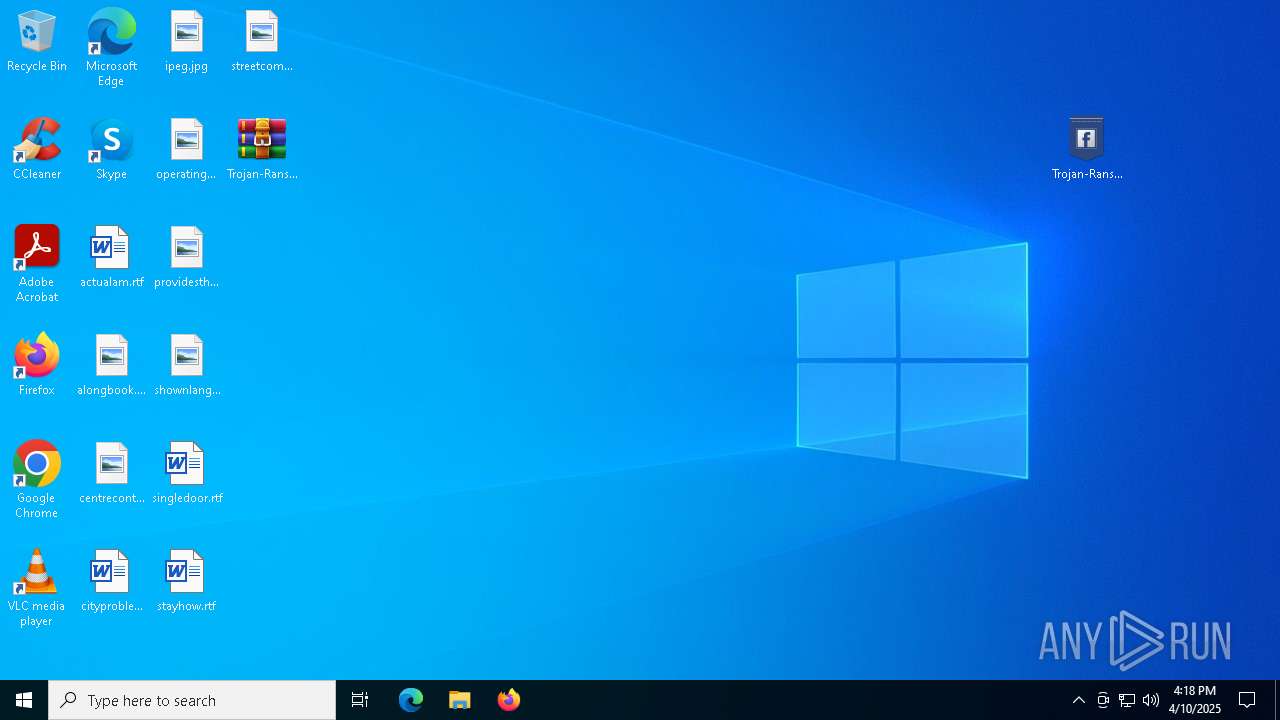
Renames files like ransomware
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
Connects to the CnC server
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
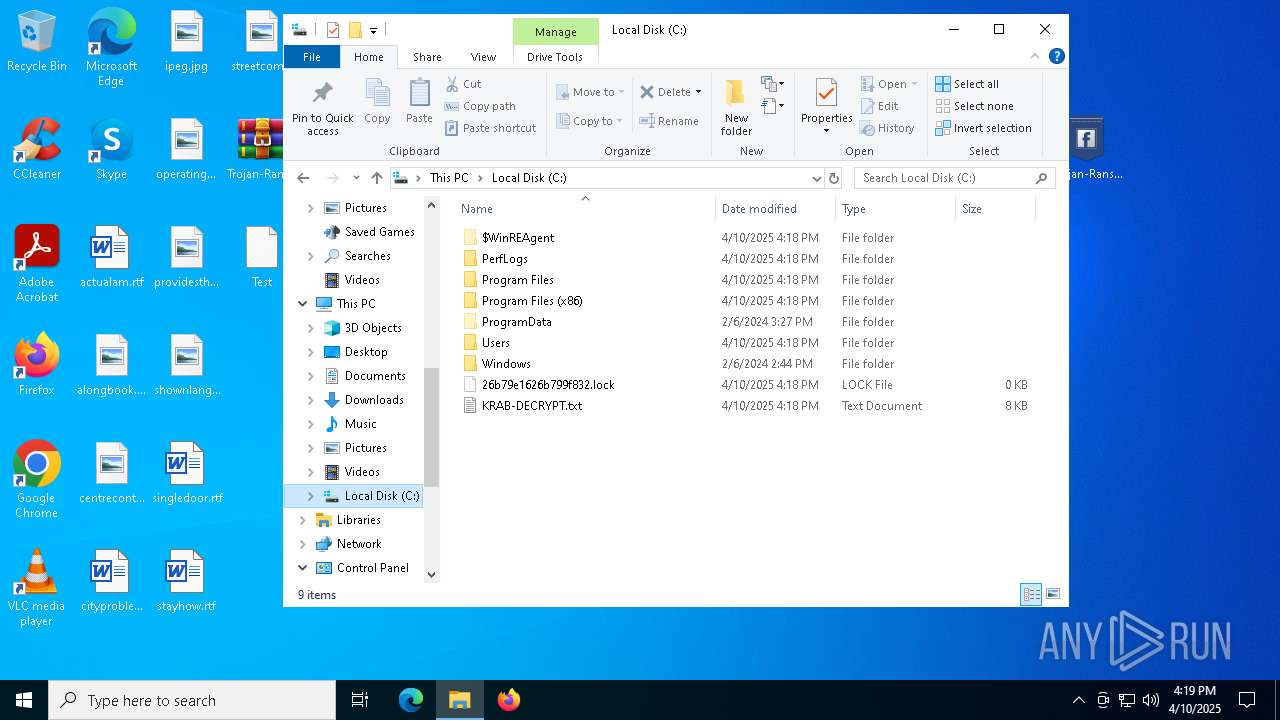
SUSPICIOUS
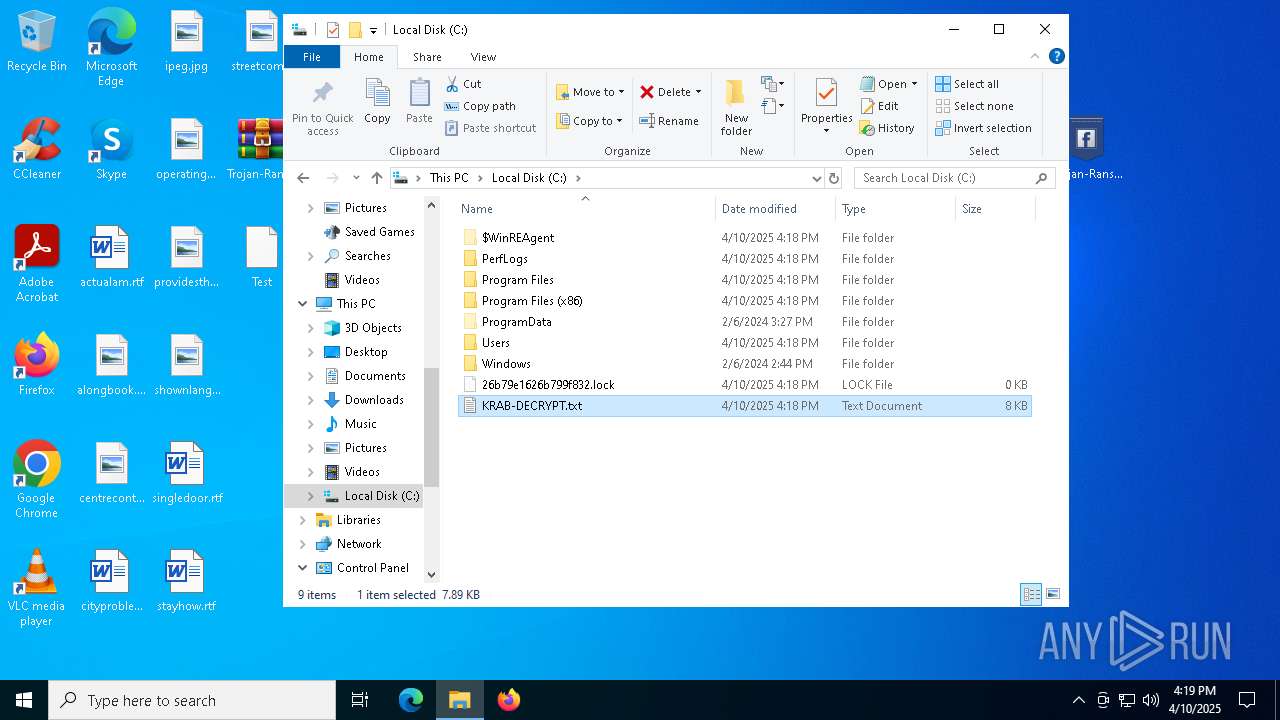
Creates file in the systems drive root
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
Contacting a server suspected of hosting an CnC
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
Reads security settings of Internet Explorer
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
INFO
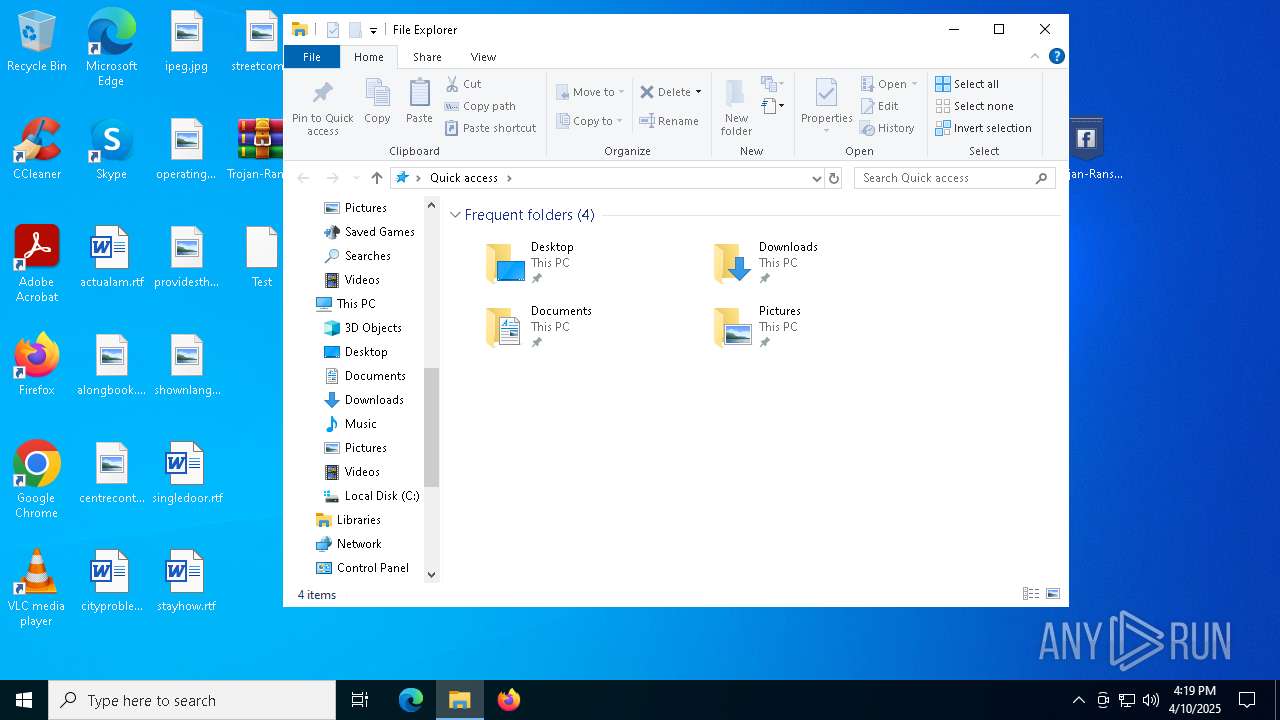
Creates files or folders in the user directory
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
Reads CPU info
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
Checks proxy server information
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
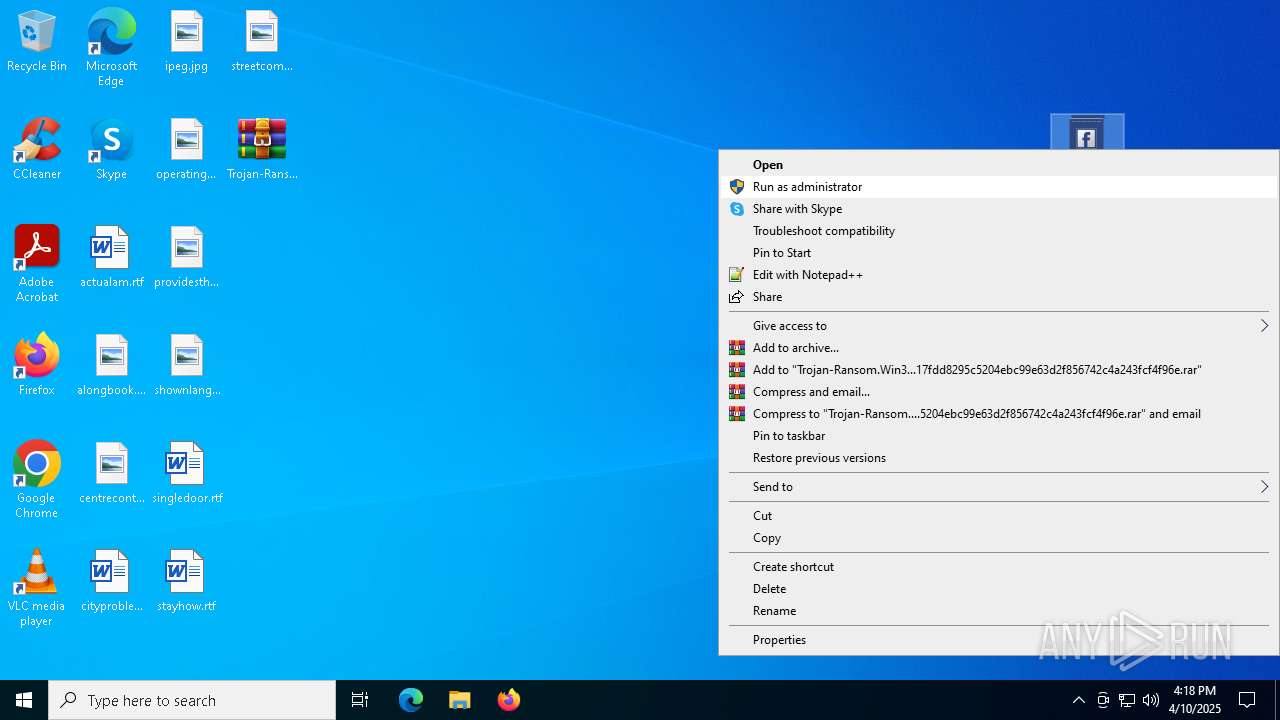
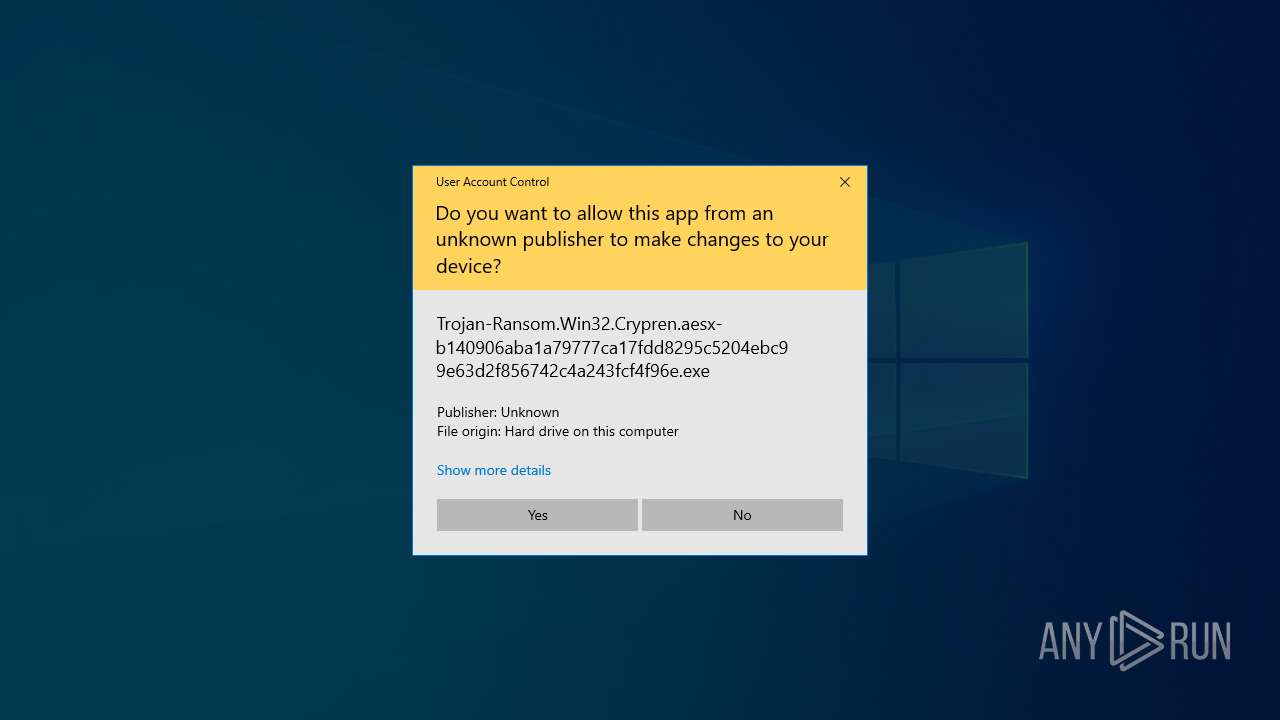
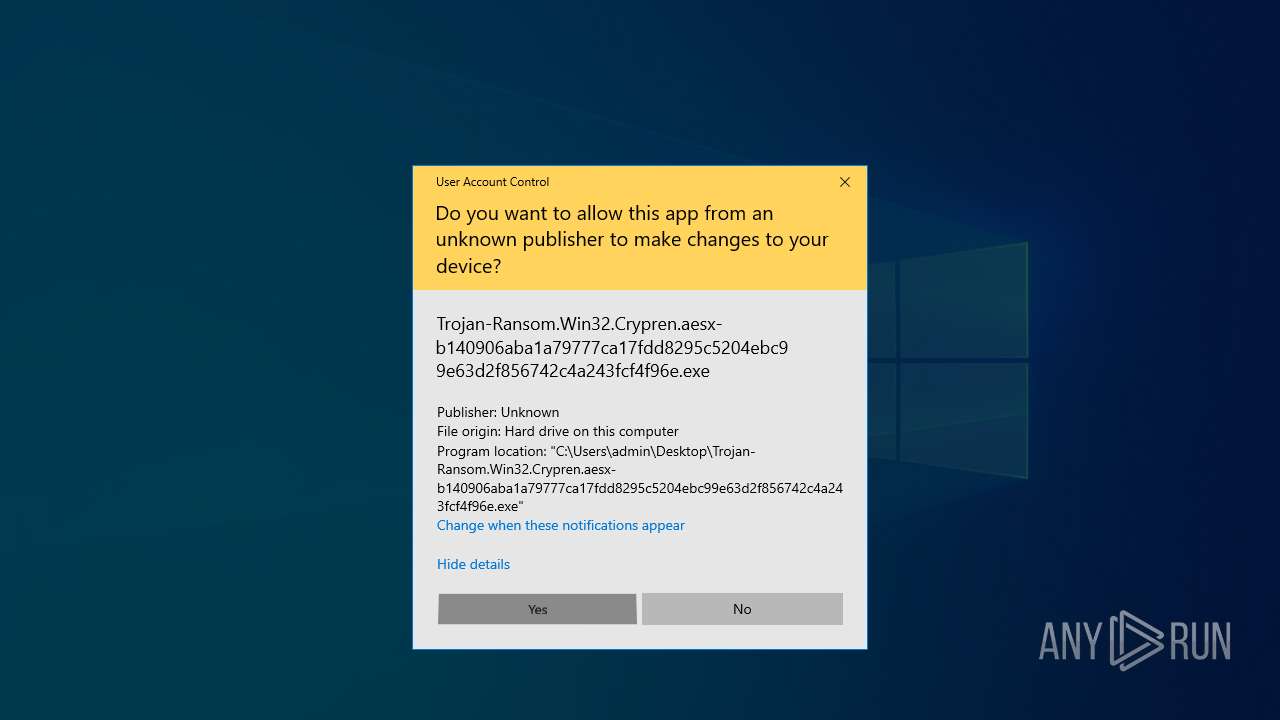
Manual execution by a user
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
- notepad.exe (PID: 3100)
The sample compiled with english language support
- WinRAR.exe (PID: 4300)
Reads the machine GUID from the registry
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
Checks supported languages
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
Reads the computer name
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
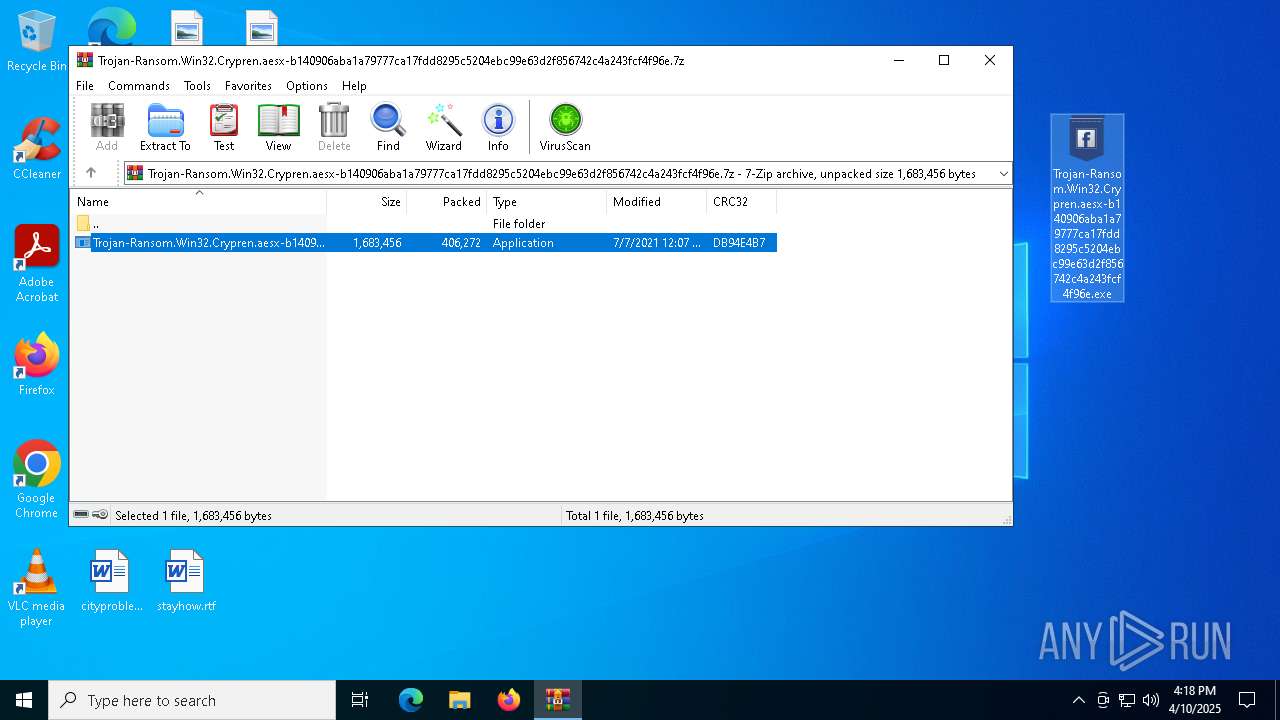
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4300)
Reads the software policy settings
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
- slui.exe (PID: 7224)
Creates files in the program directory
- Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe (PID: 7884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(7884) Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe
Decrypted-URLs (1)http://gandcrabmfe6mnef.onion/
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2021:07:07 12:07:30+00:00 |
| ArchivedFileName: | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe |
Total processes
133
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3100 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\KRAB-DECRYPT.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
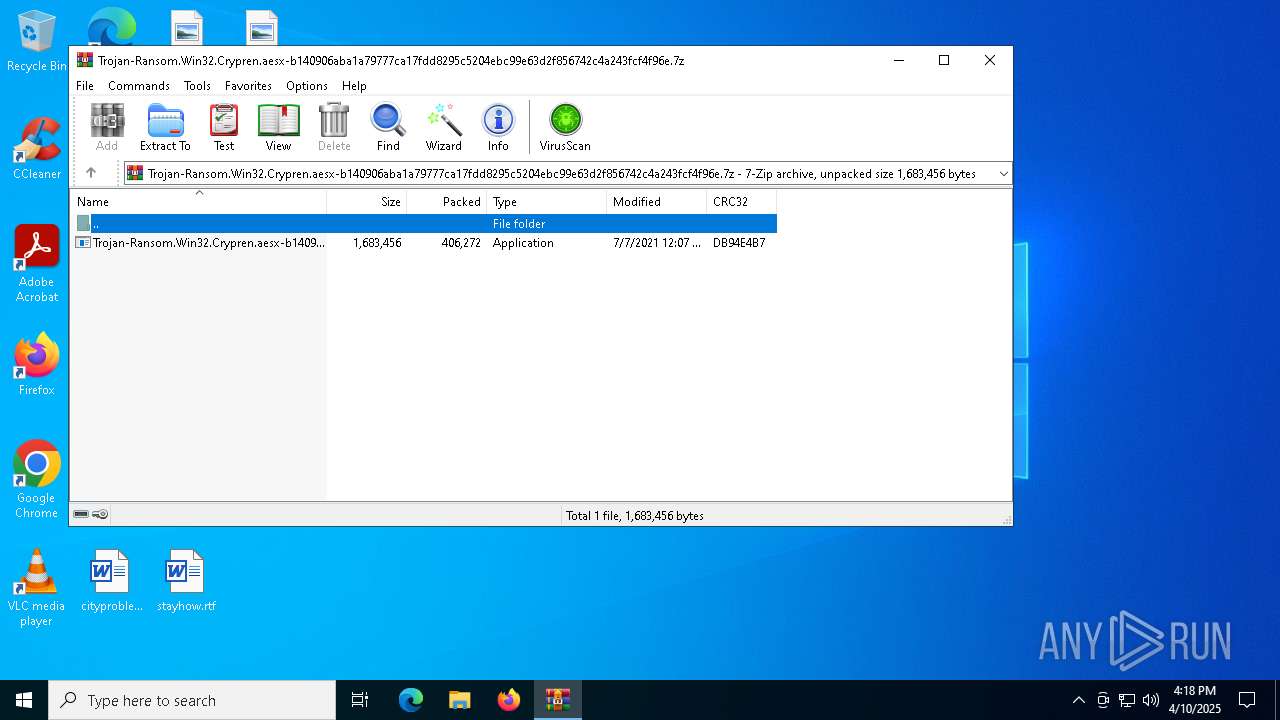
| 4300 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5256 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7192 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7224 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7884 | "C:\Users\admin\Desktop\Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe" | C:\Users\admin\Desktop\Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | explorer.exe | ||||||||||||
User: admin Company: Huimin Integrity Level: HIGH Description: Whos Collectors Brochures Modules
xor-url(PID) Process(7884) Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe Decrypted-URLs (1)http://gandcrabmfe6mnef.onion/ | |||||||||||||||
Total events
20 492
Read events
20 468
Write events
24
Delete events
0
Modification events
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.7z | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
7
Suspicious files
1 058
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | C:\Users\admin\Desktop\Test | binary | |
MD5:2FA02853E7FC5139DA9F400935B0FDB8 | SHA256:4E91C2E9964F473F6556AEADC0018BF7F3A2E31D2F59828834ACF754AADF59DA | |||
| 7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | C:\$WinREAgent\Backup\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | C:\$WinREAgent\Backup\Winre.wim.KRAB | — | |
MD5:— | SHA256:— | |||
| 7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | C:\$Recycle.Bin\KRAB-DECRYPT.txt | binary | |
MD5:6E1C692C310CD4CCA0662D18F077367C | SHA256:C3A6A4C37BB888A76A5314AC49E2D7A2825E4A4E4F84AE2401D1EBD75062F60C | |||
| 7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:BA4100D78EB9F48F3D00C998AC99BC64 | SHA256:245F13B2DBB3681E522EF7F5A3973CC12D073DCD9D80D987AC8A0171D8DD1E99 | |||
| 4300 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb4300.19662\Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | executable | |
MD5:52D42678D4F92D5B038CCFB69FC12294 | SHA256:B140906ABA1A79777CA17FDD8295C5204EBC99E63D2F856742C4A243FCF4F96E | |||
| 7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:4A90329071AE30B759D279CCA342B0A6 | SHA256:4F544379EDA8E2653F71472AB968AEFD6B5D1F4B3CE28A5EDB14196184ED3B60 | |||
| 7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | C:\$WinREAgent\KRAB-DECRYPT.txt | binary | |
MD5:6E1C692C310CD4CCA0662D18F077367C | SHA256:C3A6A4C37BB888A76A5314AC49E2D7A2825E4A4E4F84AE2401D1EBD75062F60C | |||
| 7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | C:\$WinREAgent\Backup\boot.sdi.KRAB | binary | |
MD5:E85A714E71E26AE73D4998F6979B4145 | SHA256:EC0F6B3C6FDB7FB4F2C7F06E5F32BAD0C7A095B0FA056CB9981958FAA436EB49 | |||
| 7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | C:\$WinREAgent\Scratch\update.wim | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
30
DNS requests
23
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 104.124.11.58:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | GET | 301 | 172.67.145.98:80 | http://www.macartegrise.eu/ | unknown | — | — | malicious |
7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | GET | 200 | 34.136.111.81:80 | http://www.poketeg.com/ | unknown | — | — | malicious |
7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | POST | — | 87.236.16.243:80 | http://asl-company.ru/uploads/tmp/thzufusezu.gif | unknown | — | — | malicious |
7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | GET | — | 104.21.40.198:80 | http://www.wash-wear.com/ | unknown | — | — | malicious |
7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | POST | 200 | 34.136.111.81:80 | http://www.poketeg.com/uploads/graphic/amdemo.bmp | unknown | — | — | malicious |
7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | GET | — | 87.236.16.243:80 | http://asl-company.ru/ | unknown | — | — | malicious |
7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | GET | 301 | 66.235.200.146:80 | http://www.fabbfoundation.gm/ | unknown | — | — | malicious |
7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | GET | 200 | 172.217.18.3:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | GET | 200 | 172.217.18.3:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 104.124.11.58:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | 172.67.145.98:80 | www.macartegrise.eu | CLOUDFLARENET | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.billerimpex.com |
| whitelisted |
www.macartegrise.eu |
| malicious |
c.pki.goog |
| whitelisted |
www.poketeg.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | Malware Command and Control Activity Detected | ET MALWARE [eSentire] Win32/GandCrab v4/5 Ransomware CnC Activity |
7884 | Trojan-Ransom.Win32.Crypren.aesx-b140906aba1a79777ca17fdd8295c5204ebc99e63d2f856742c4a243fcf4f96e.exe | Malware Command and Control Activity Detected | ET MALWARE [eSentire] Win32/GandCrab v4/5 Ransomware CnC Activity |