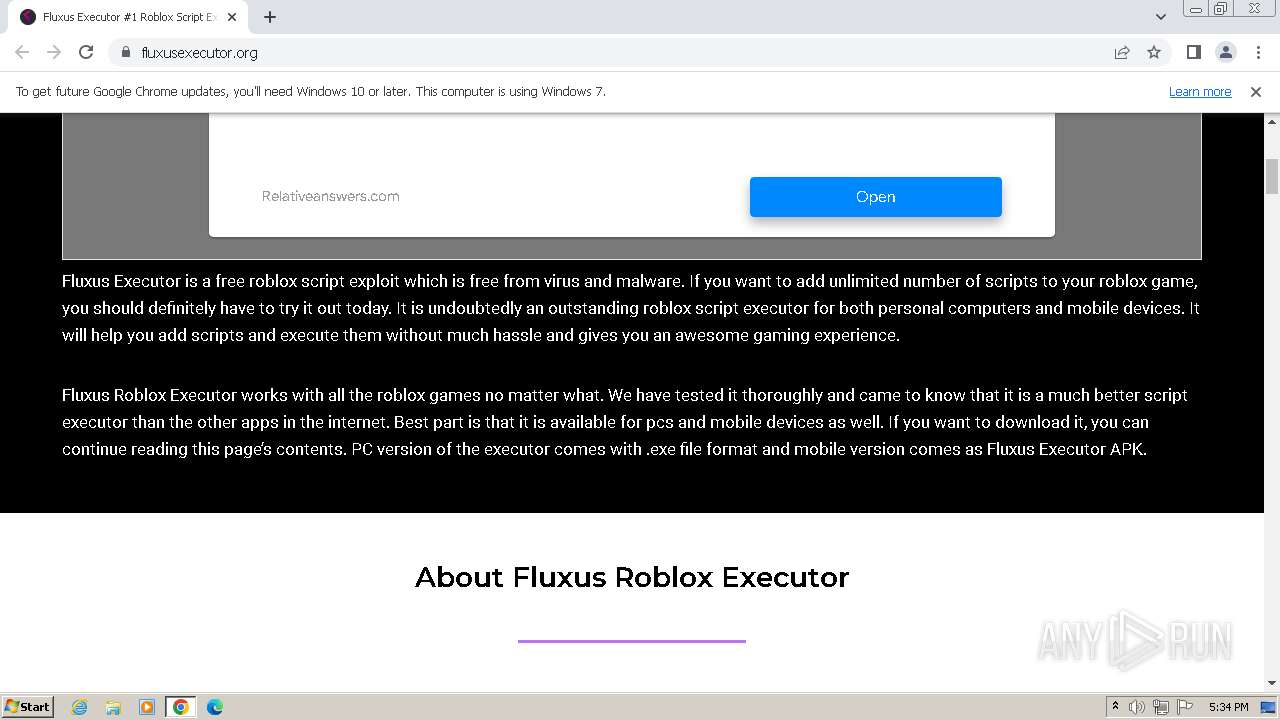
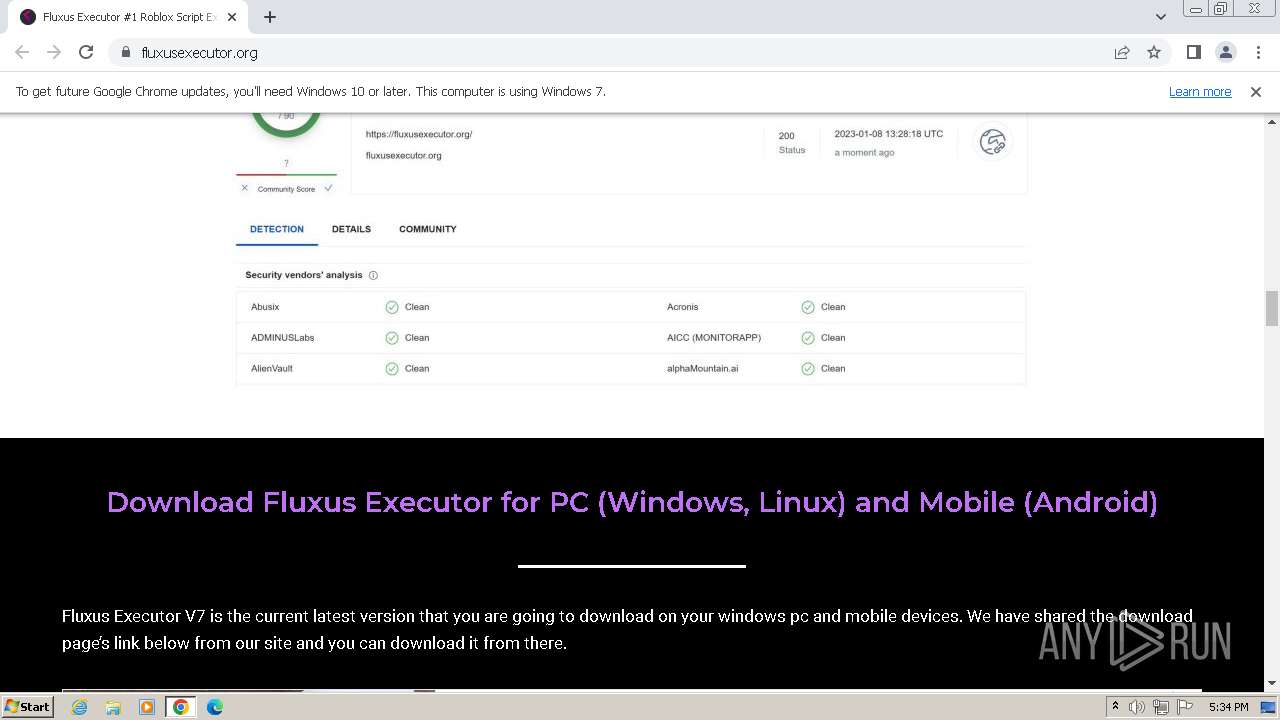
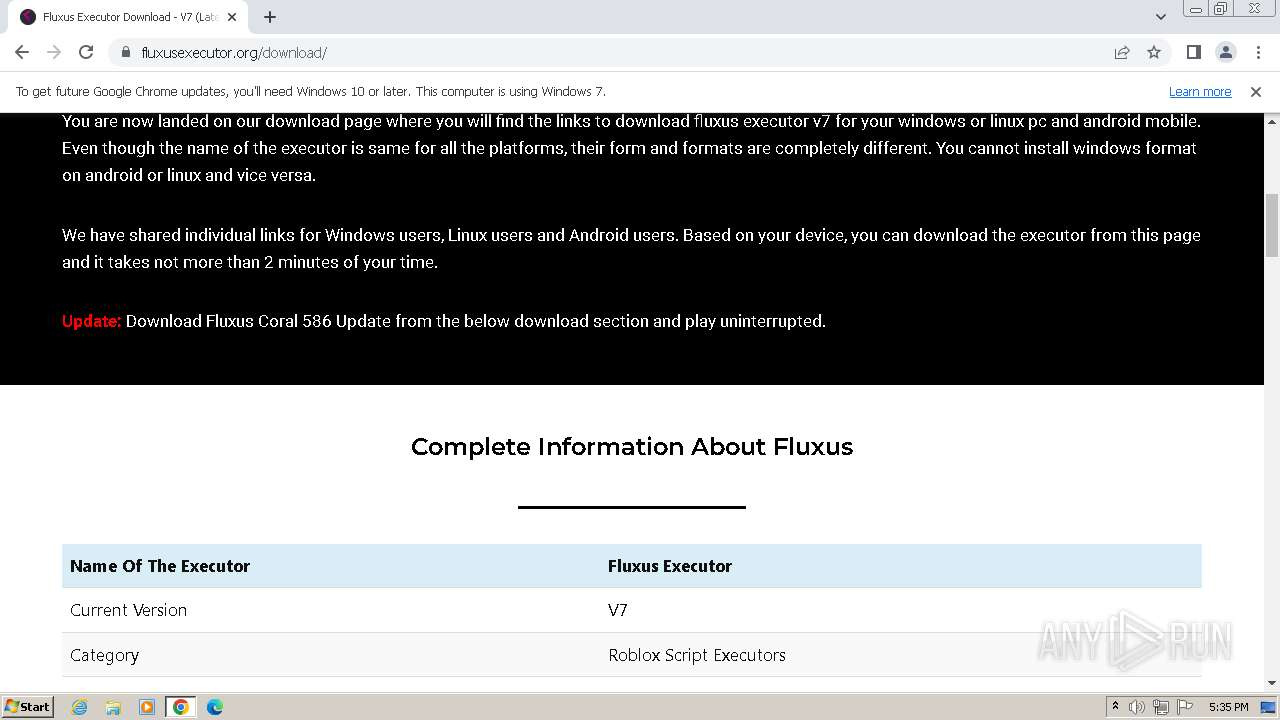
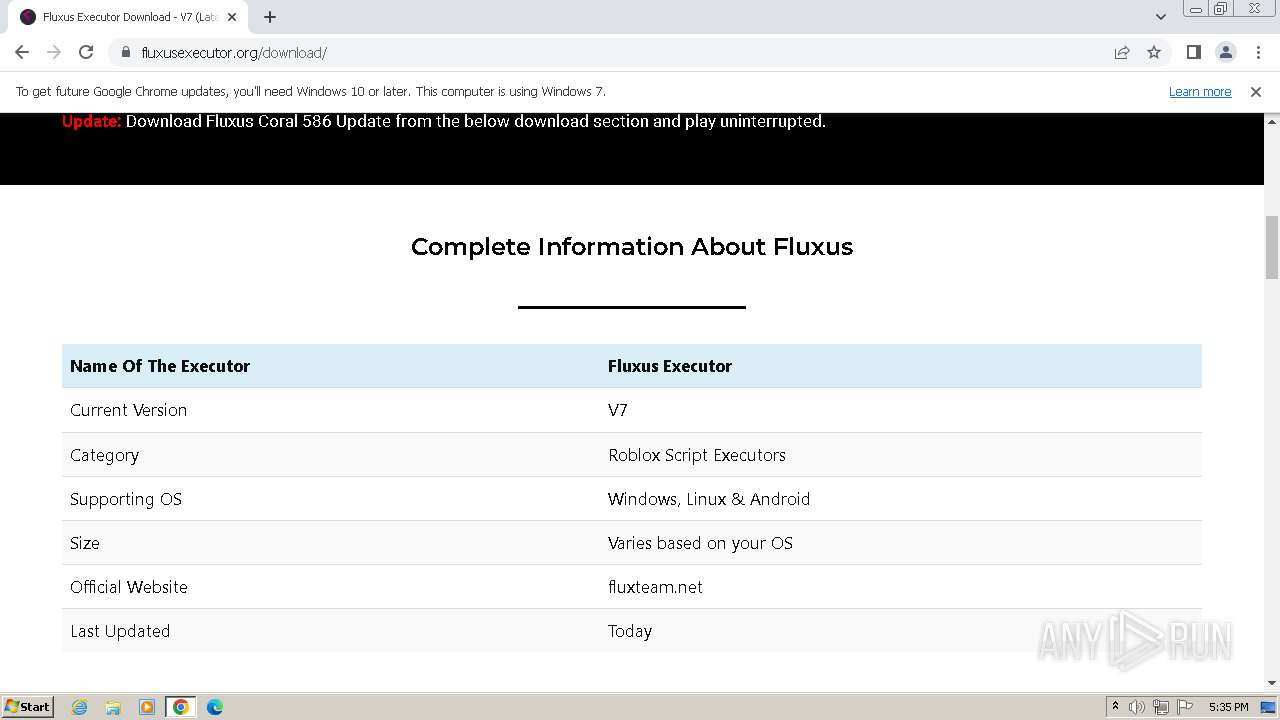
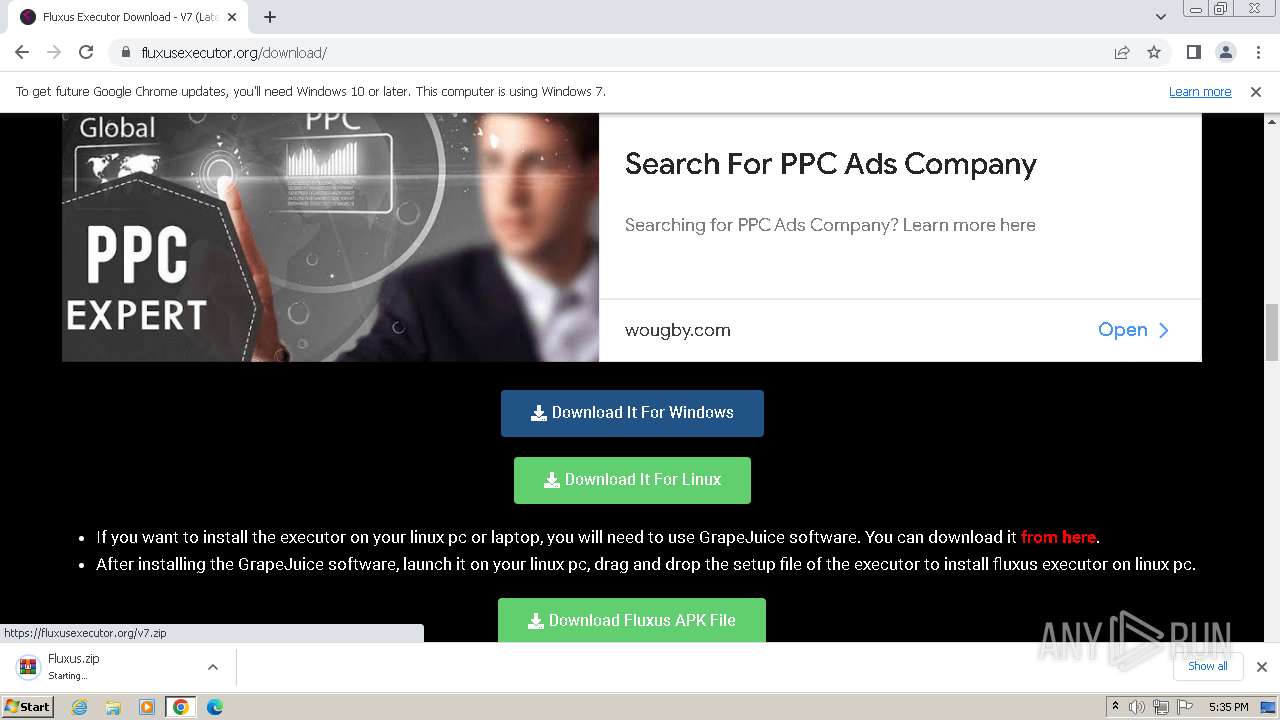
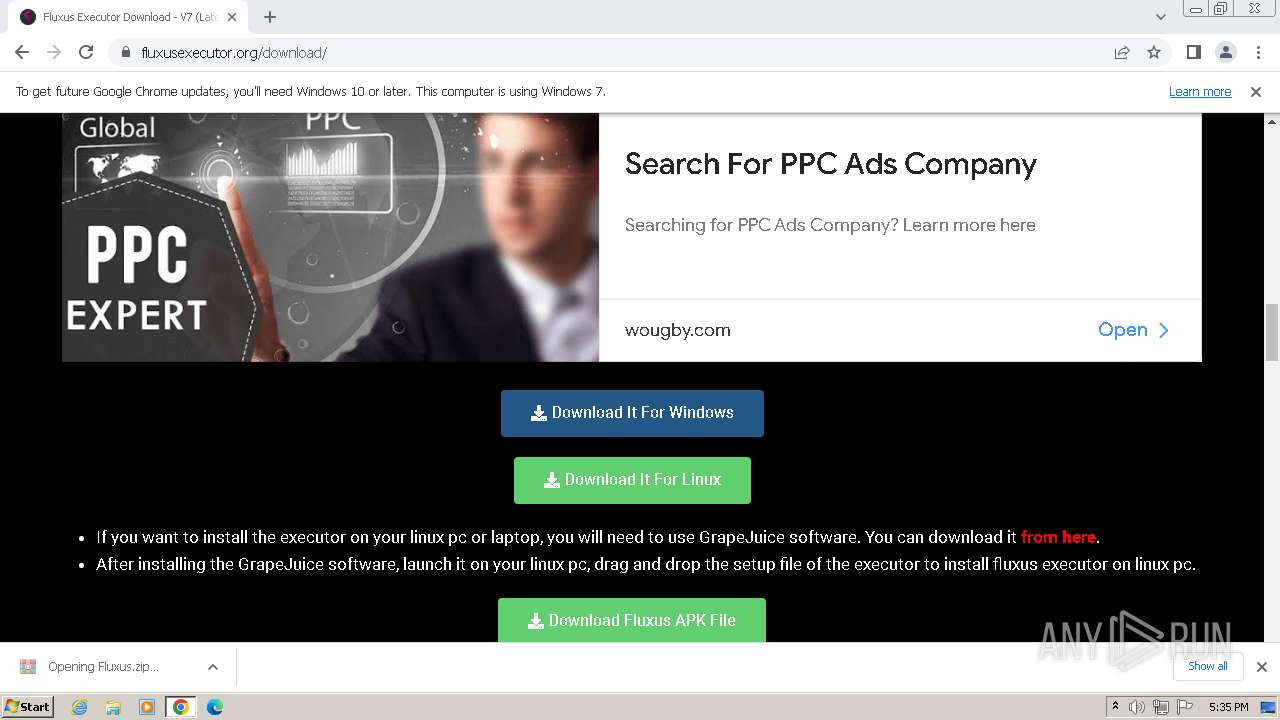
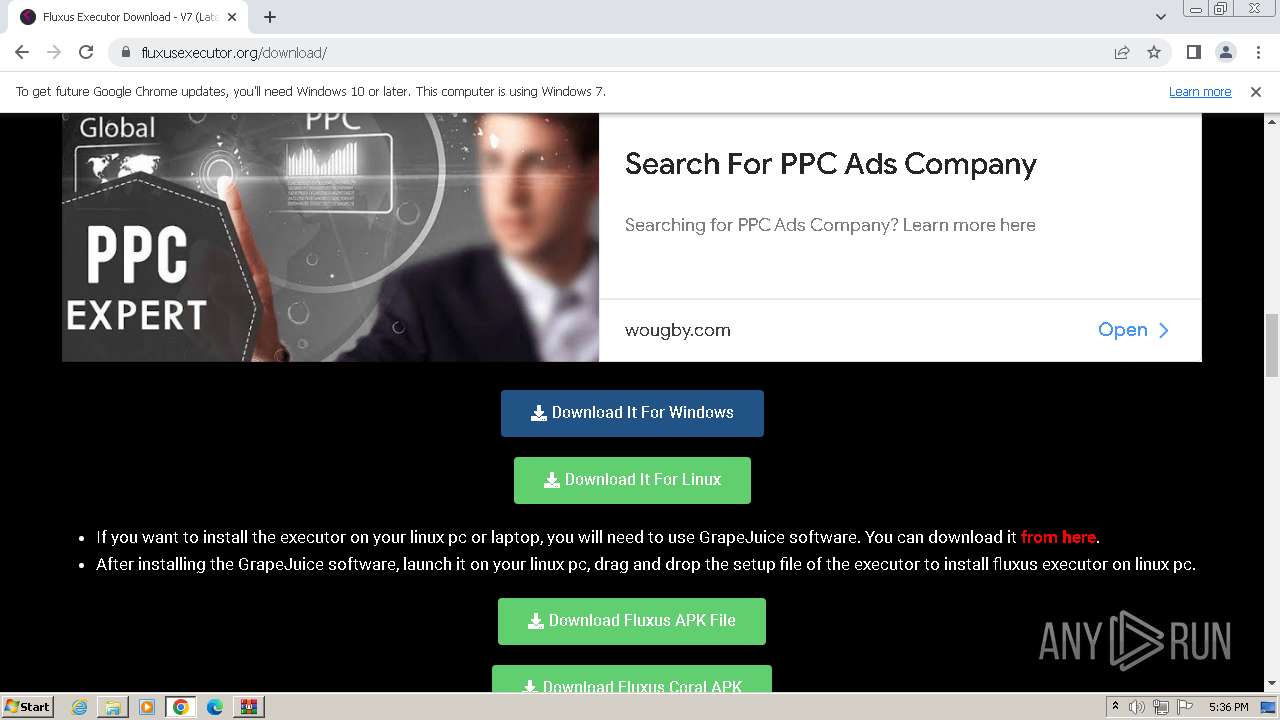
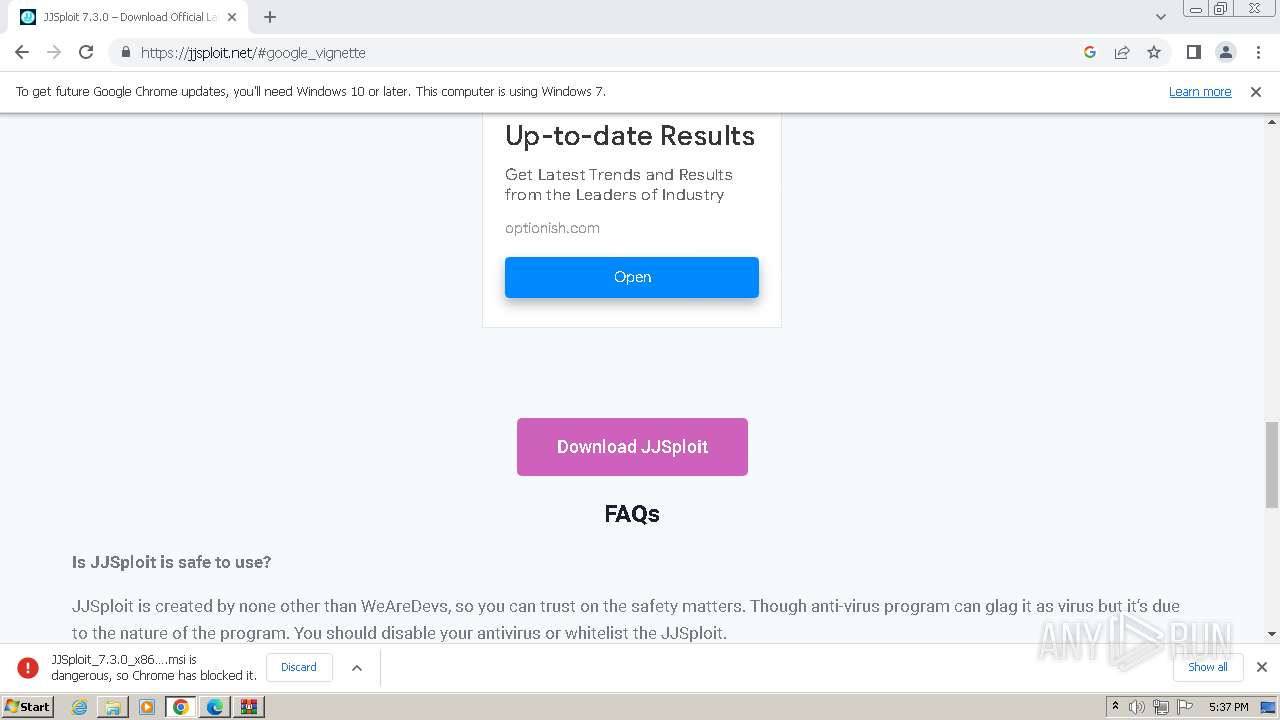
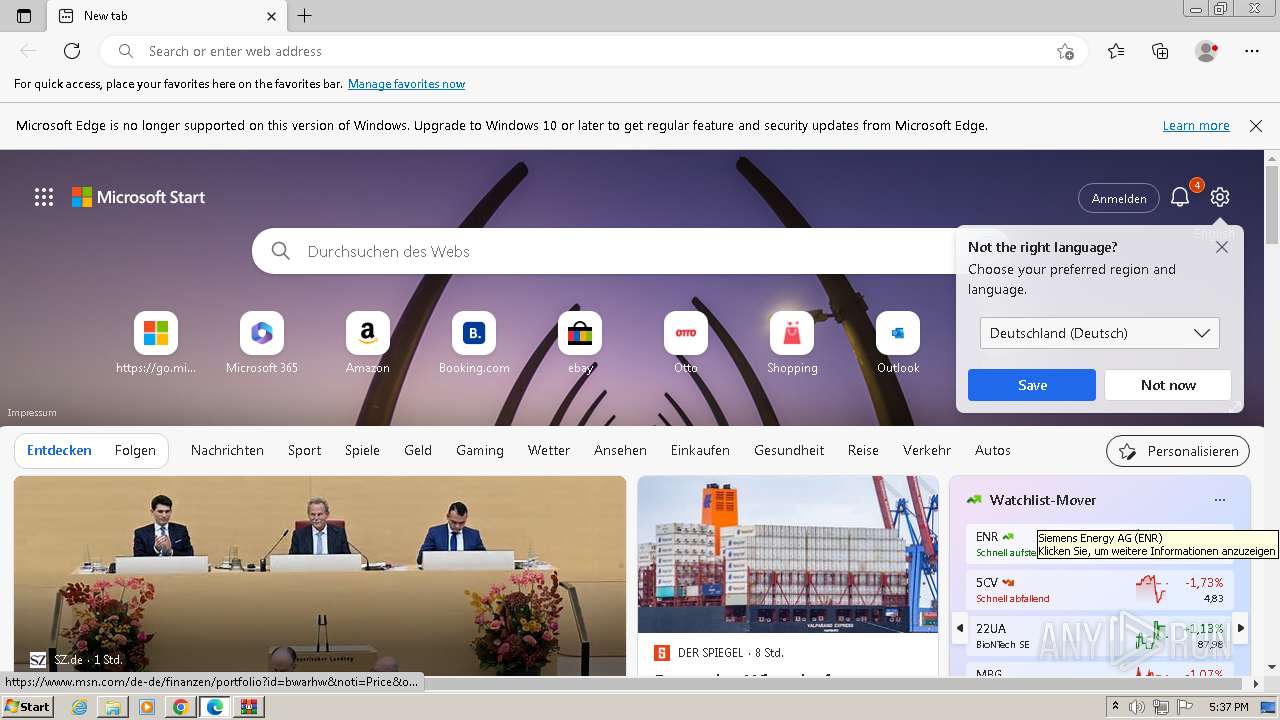
| URL: | https://fluxusexecutor.org/ |
| Full analysis: | https://app.any.run/tasks/258db5d6-a3a2-41f9-b8aa-e4f1bc7da9f0 |
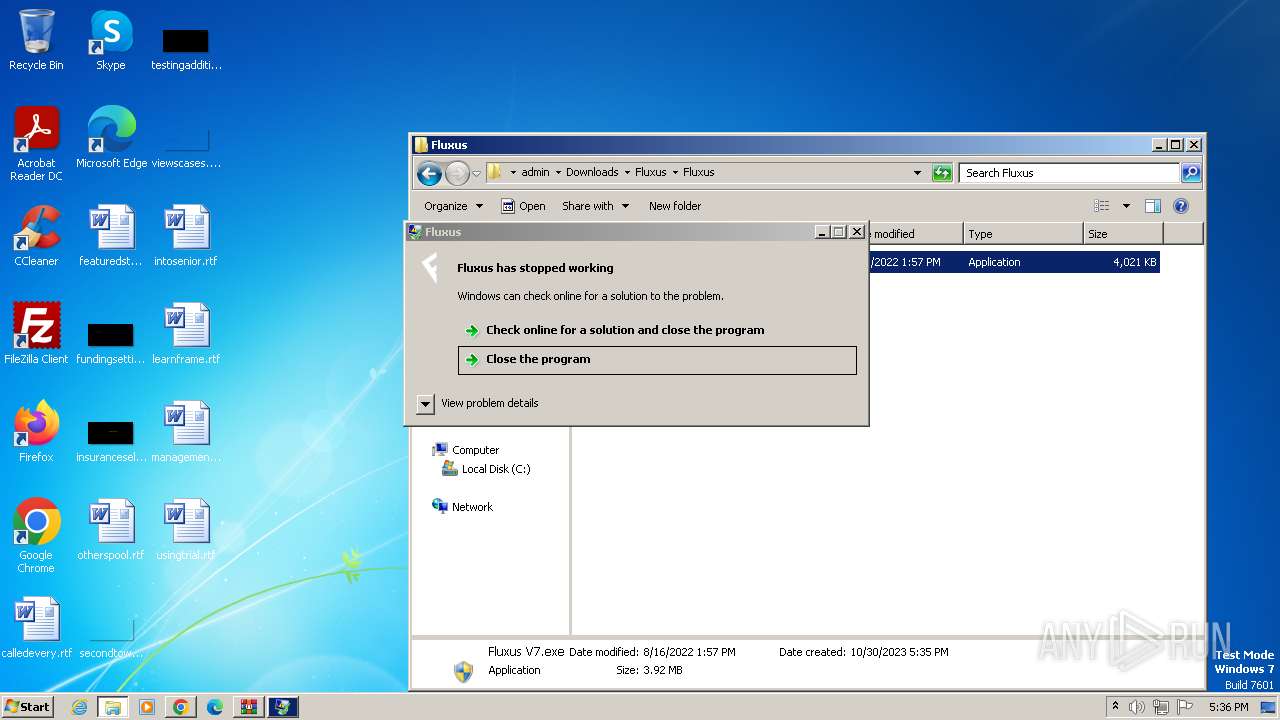
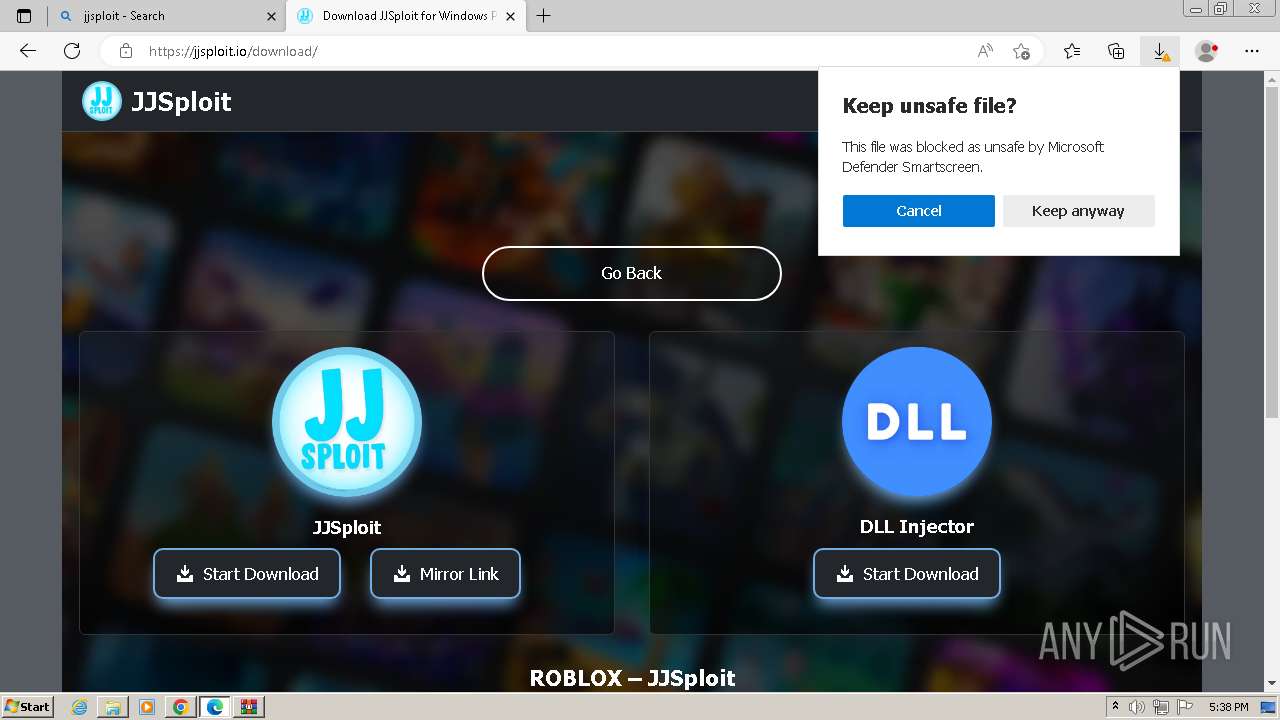
| Verdict: | Malicious activity |
| Analysis date: | October 30, 2023, 17:34:38 |
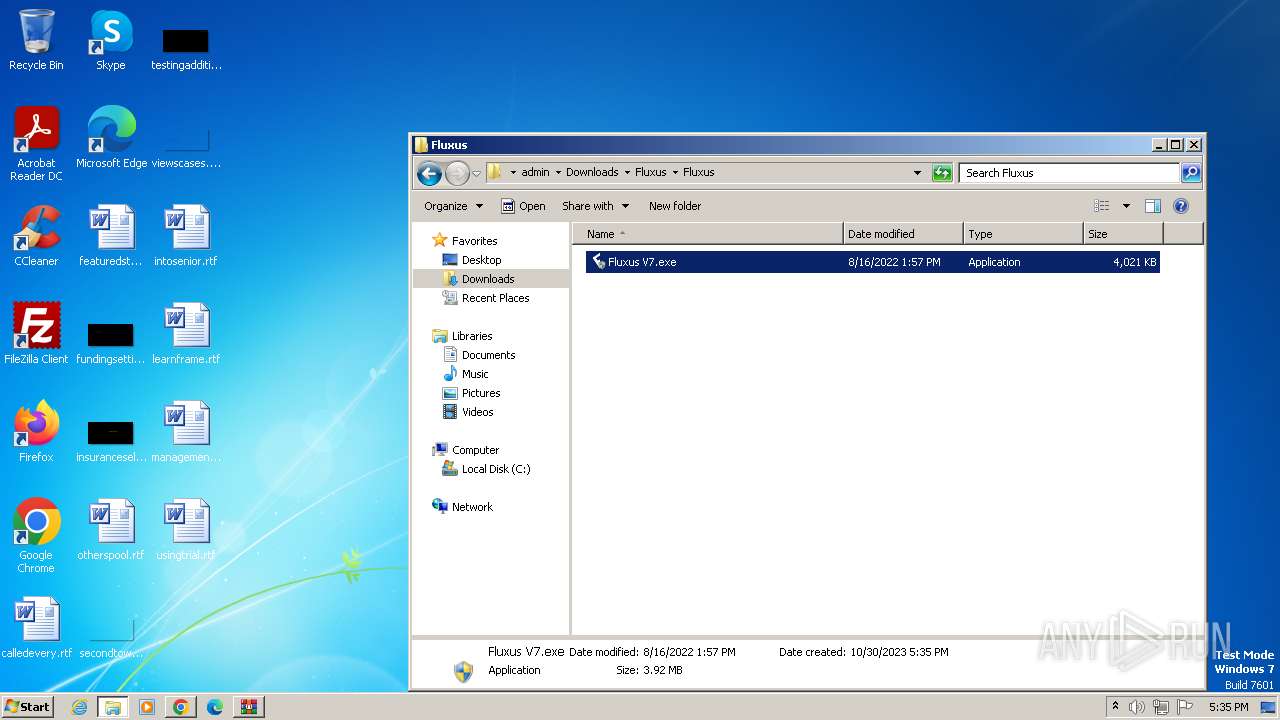
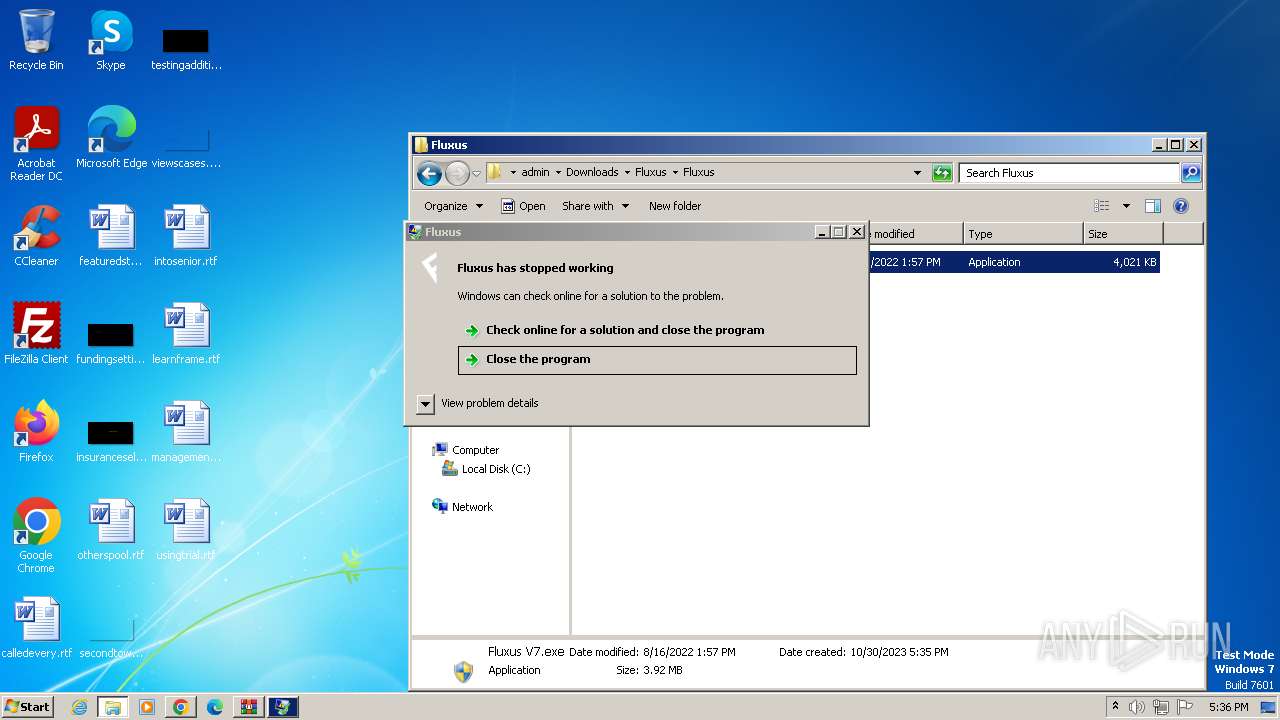
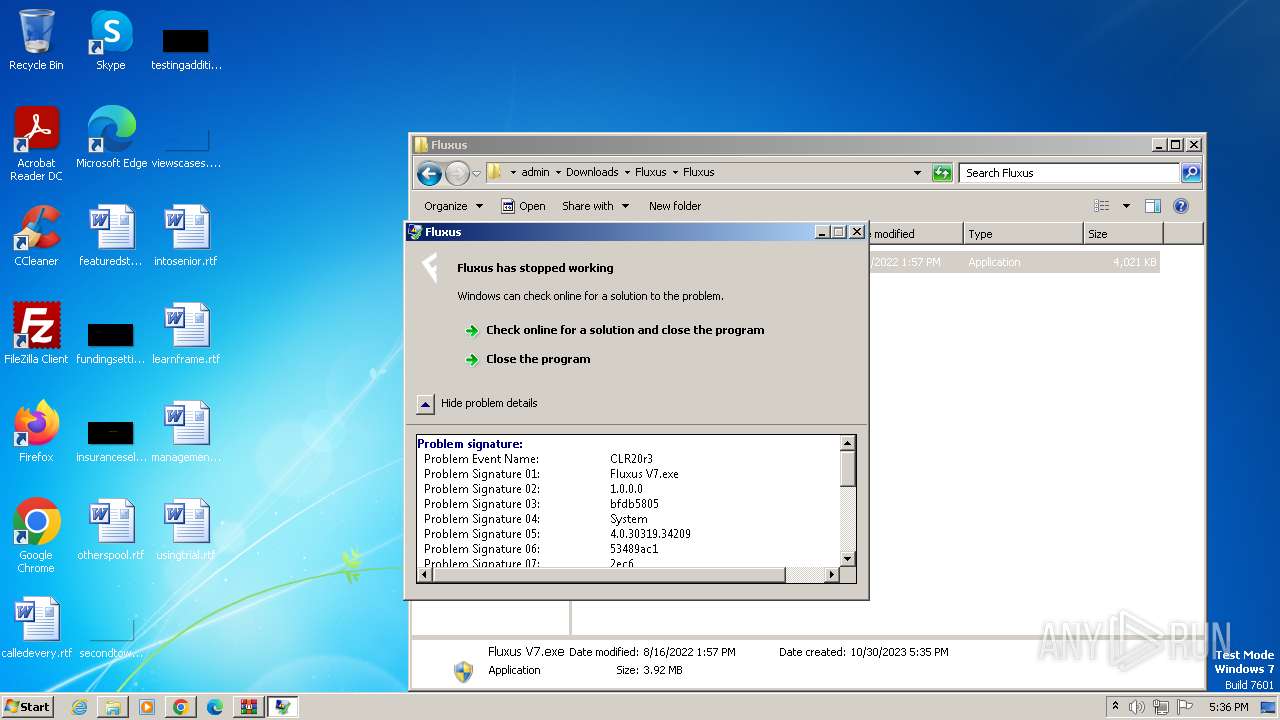
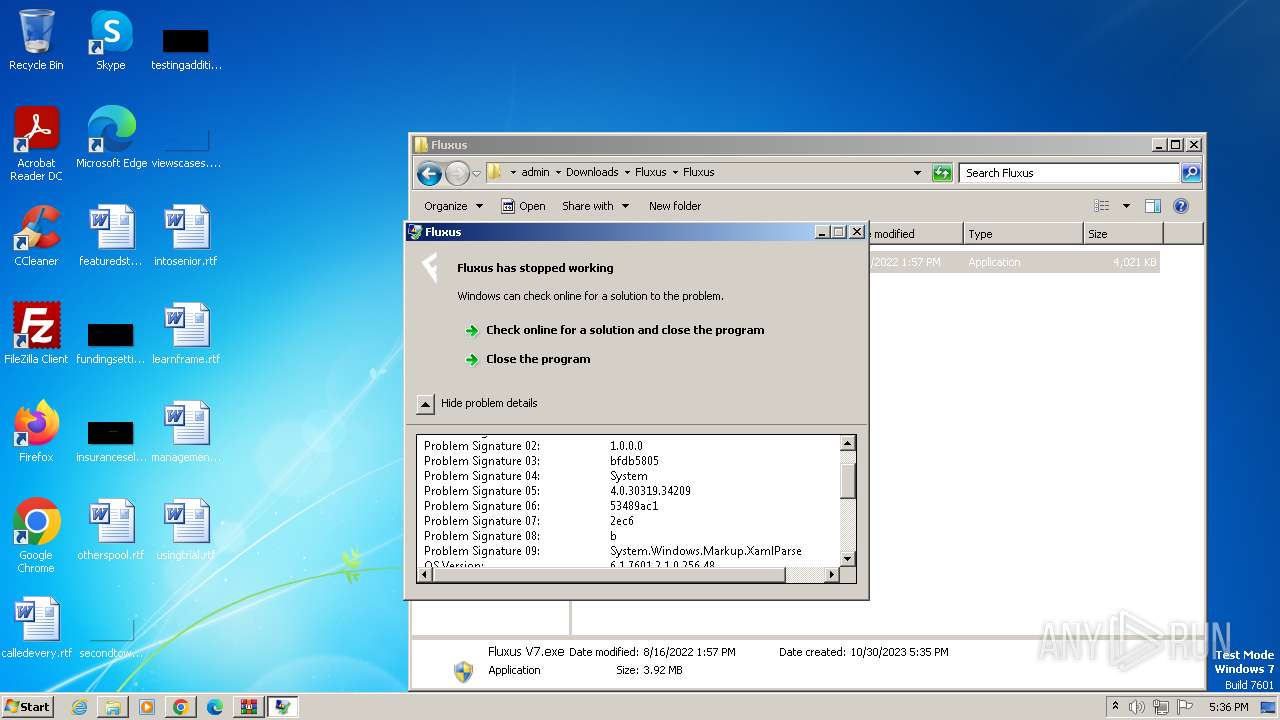
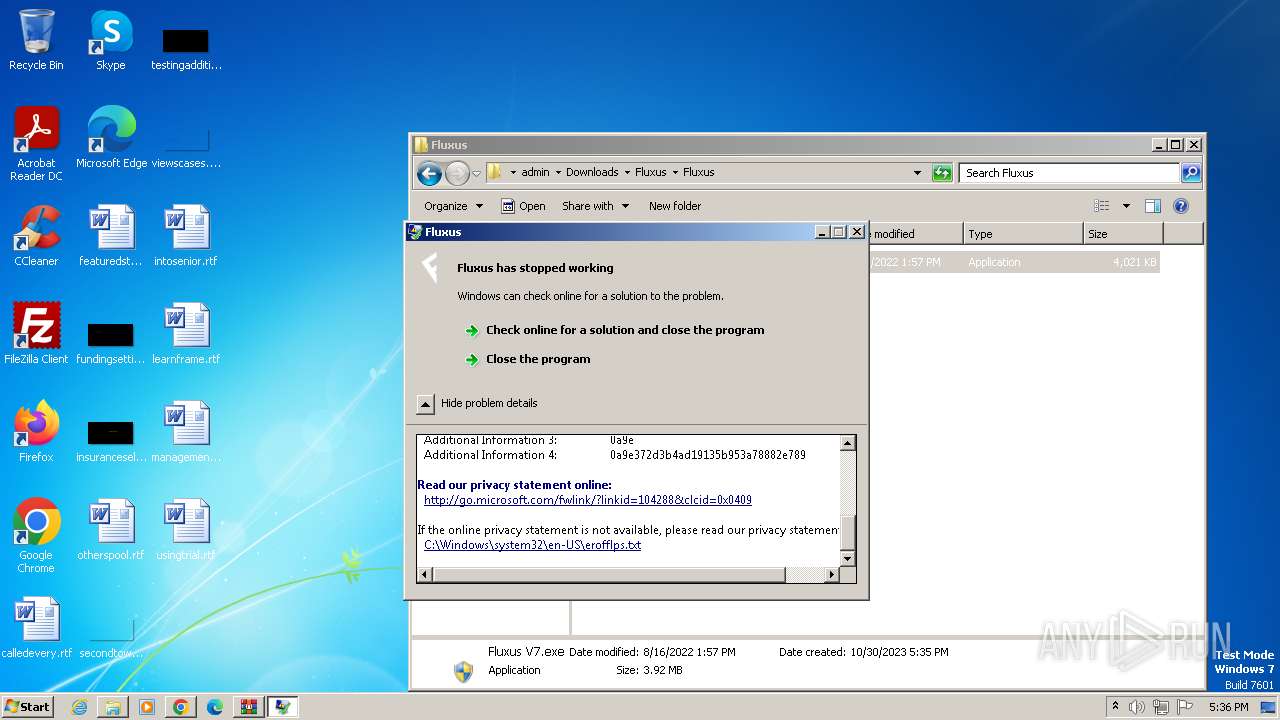
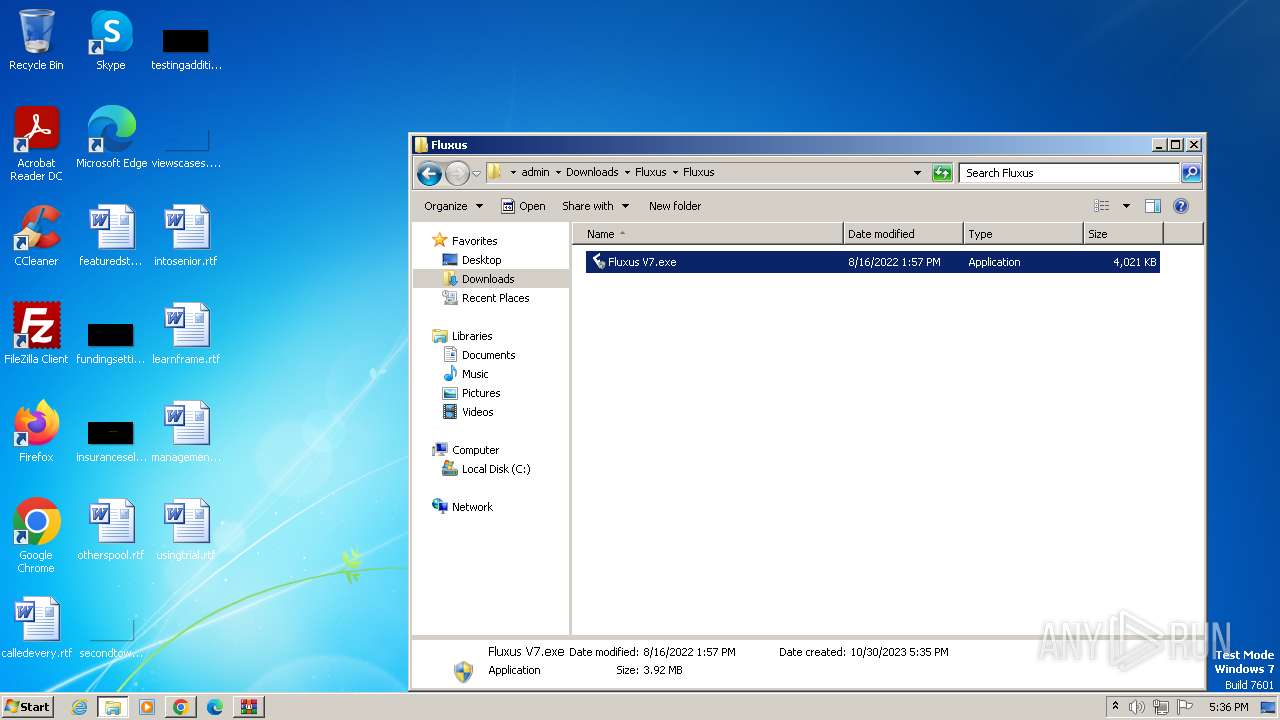
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | 444732F6A63422B71C7E196E8974594B1CEAF783 |
| SHA256: | 20D9426C51B34BF8CE7A31A29B3233B41BB1060A29C54D63452C4A887540396E |
| SSDEEP: | 3:N8Udrjn:2Ijn |
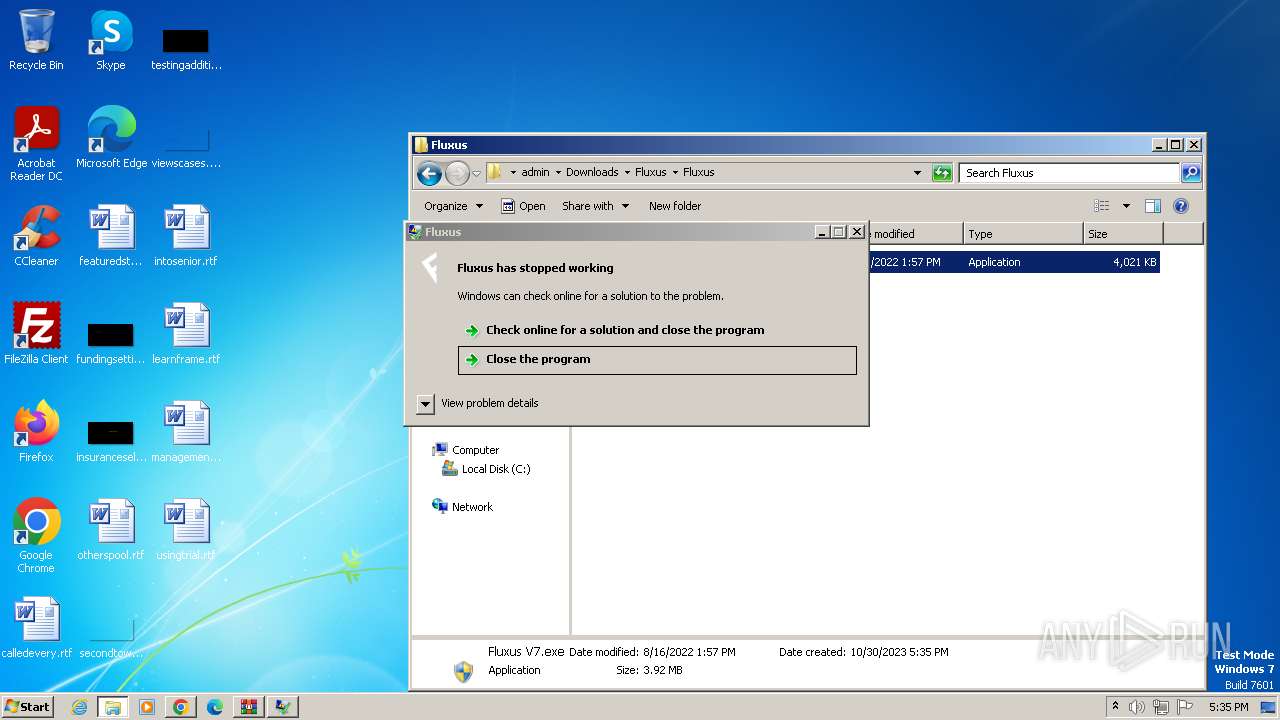
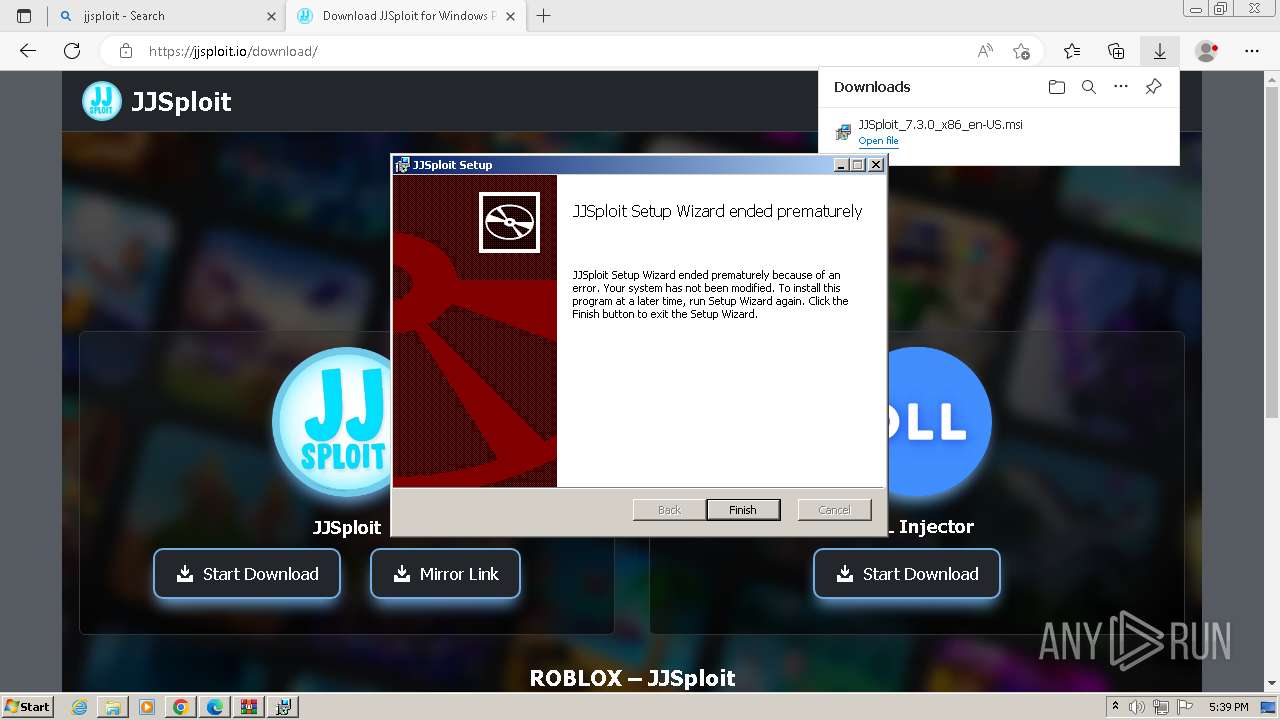
MALICIOUS
Application was dropped or rewritten from another process
- Fluxus V7.exe (PID: 3616)
- Fluxus V7.exe (PID: 2916)
- Fluxus V7.exe (PID: 1612)
- Fluxus V7.exe (PID: 632)
- Fluxus V7.exe (PID: 2888)
- Fluxus V7.exe (PID: 3192)
- Fluxus V7.exe (PID: 3684)
Starts Visual C# compiler
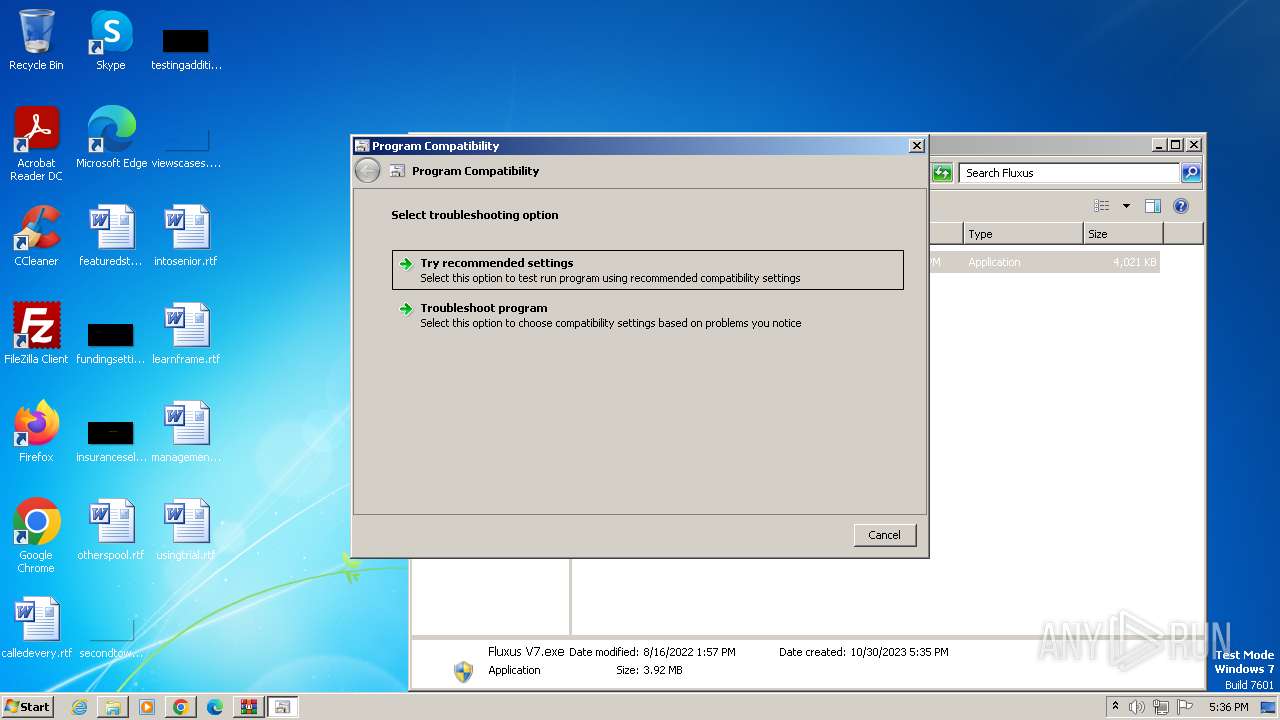
- sdiagnhost.exe (PID: 3452)
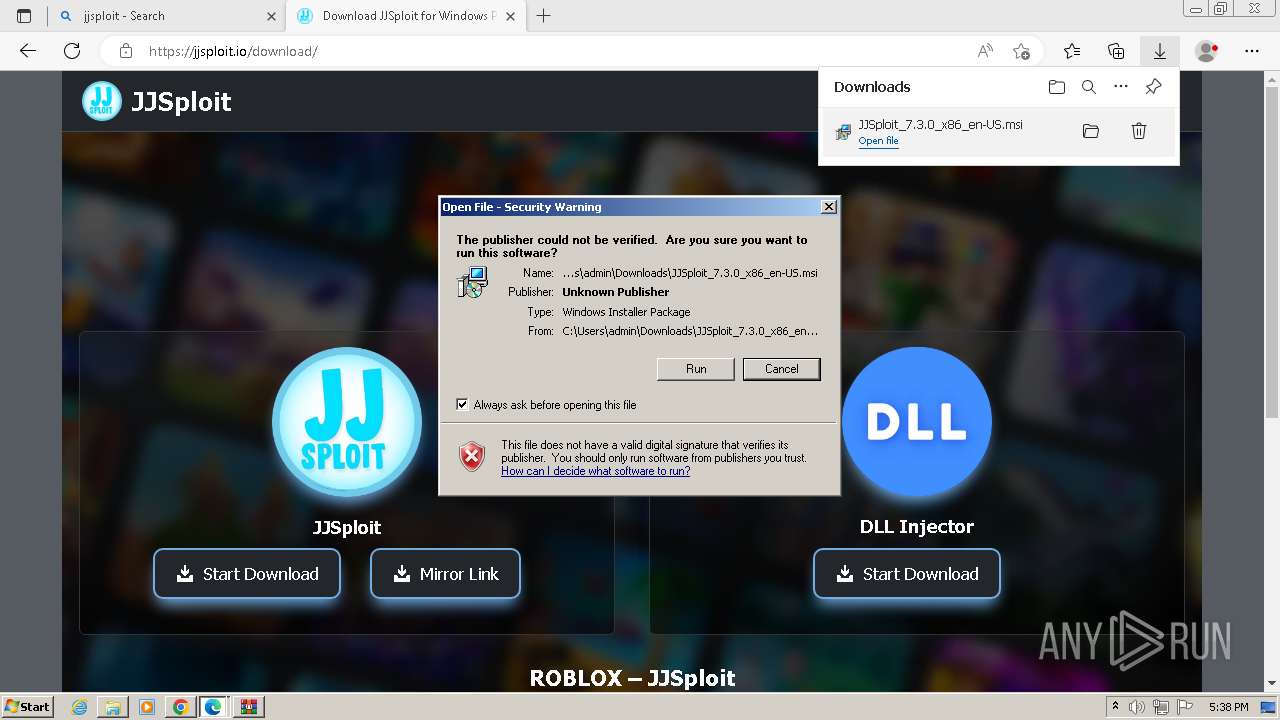
Drops the executable file immediately after the start
- csc.exe (PID: 2416)
- csc.exe (PID: 3388)
- csc.exe (PID: 1600)
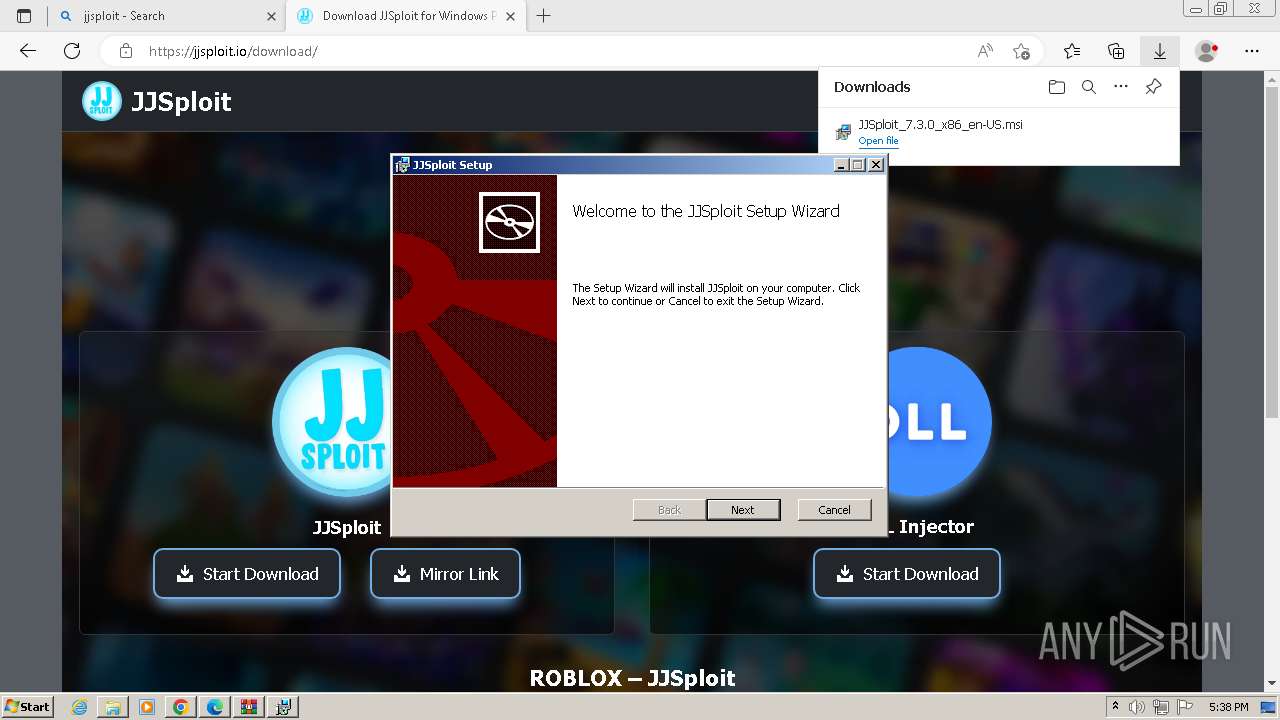
- msiexec.exe (PID: 3936)
Run PowerShell with an invisible window
- powershell.exe (PID: 4332)
SUSPICIOUS
Reads the Internet Settings
- Fluxus V7.exe (PID: 2916)
- Fluxus V7.exe (PID: 2888)
- Fluxus V7.exe (PID: 3192)
- Fluxus V7.exe (PID: 3684)
- sdiagnhost.exe (PID: 3452)
Reads settings of System Certificates
- Fluxus V7.exe (PID: 2916)
- Fluxus V7.exe (PID: 3192)
- Fluxus V7.exe (PID: 3684)
- msdt.exe (PID: 3532)
- Fluxus V7.exe (PID: 2888)
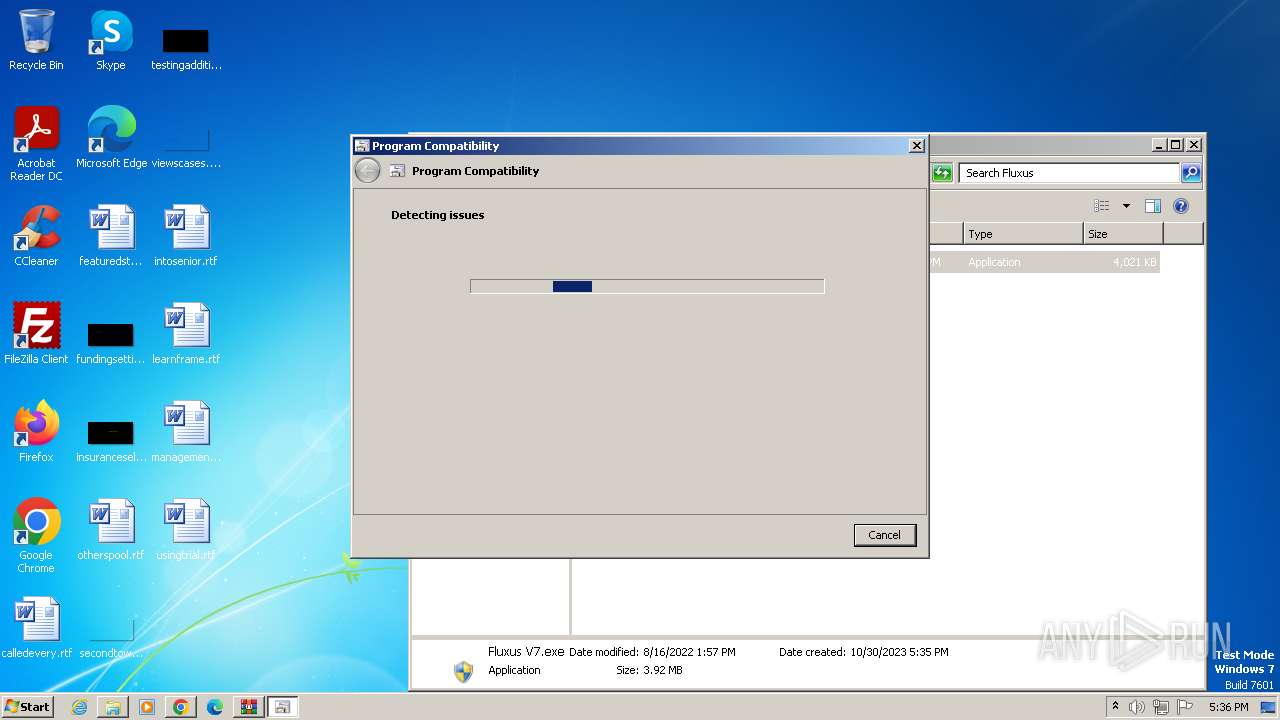
Probably uses Microsoft diagnostics tool to execute malicious payload
- pcwrun.exe (PID: 3584)
Process drops legitimate windows executable
- msdt.exe (PID: 3532)
Uses .NET C# to load dll
- sdiagnhost.exe (PID: 3452)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 3936)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 3936)
Request a resource from the Internet using PowerShell's cmdlet
- msiexec.exe (PID: 3936)
Powershell scripting: start process
- msiexec.exe (PID: 3936)
Executes as Windows Service
- VSSVC.exe (PID: 2512)
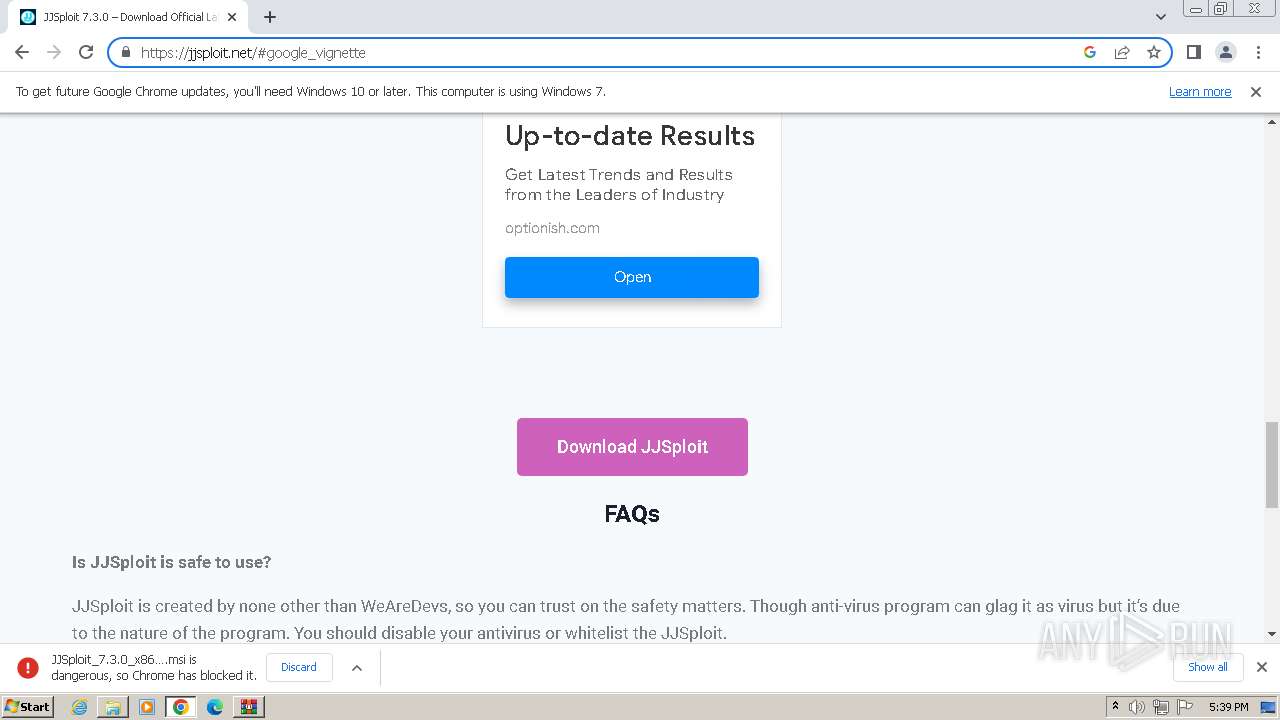
Powershell version downgrade attack
- powershell.exe (PID: 4332)
INFO
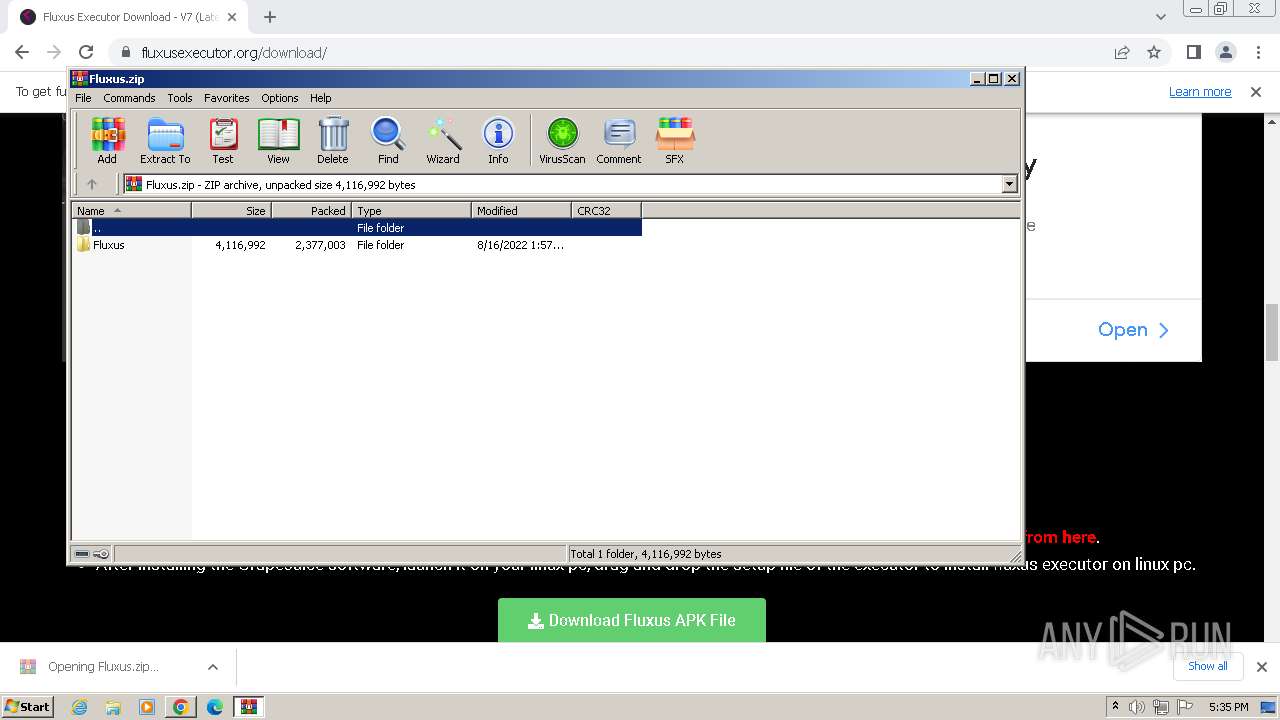
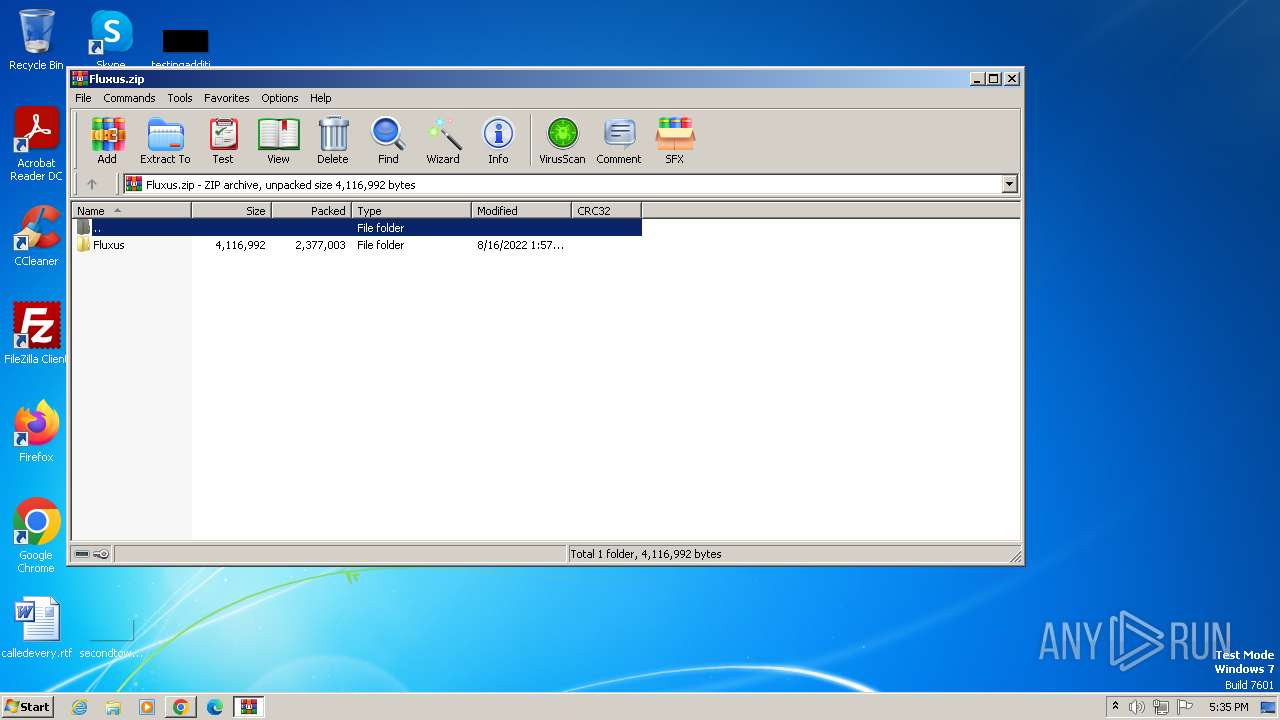
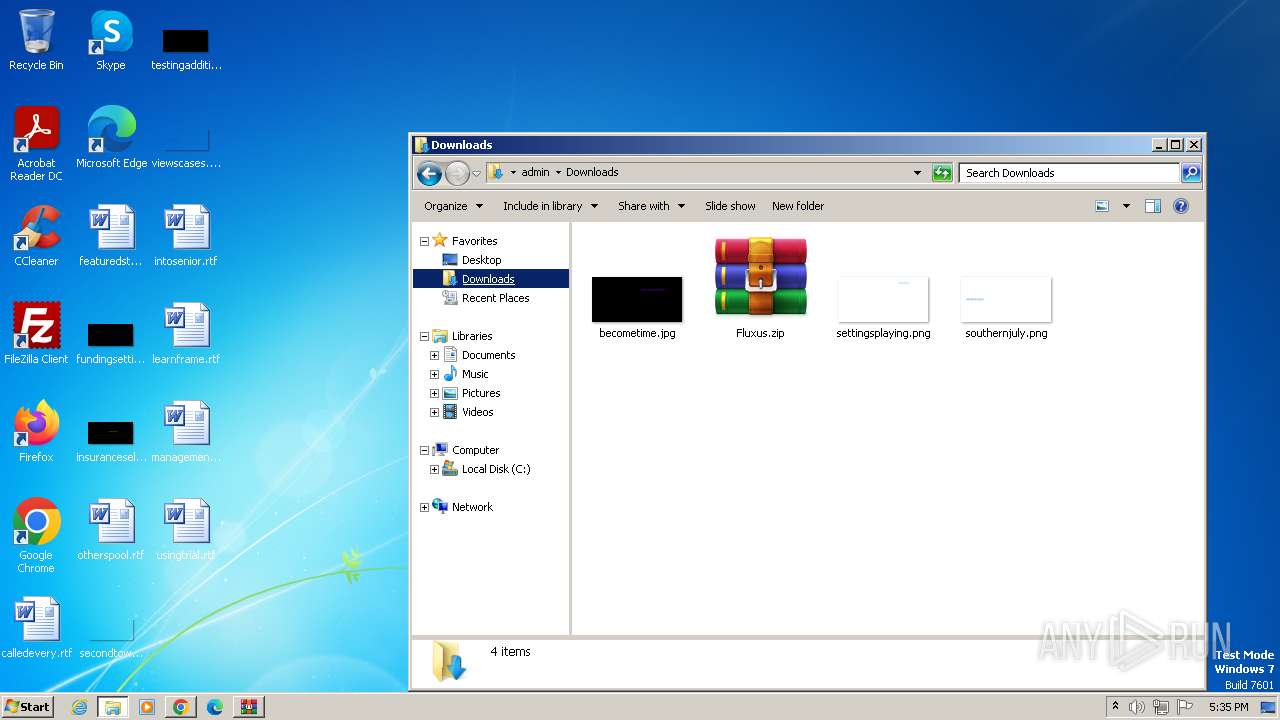
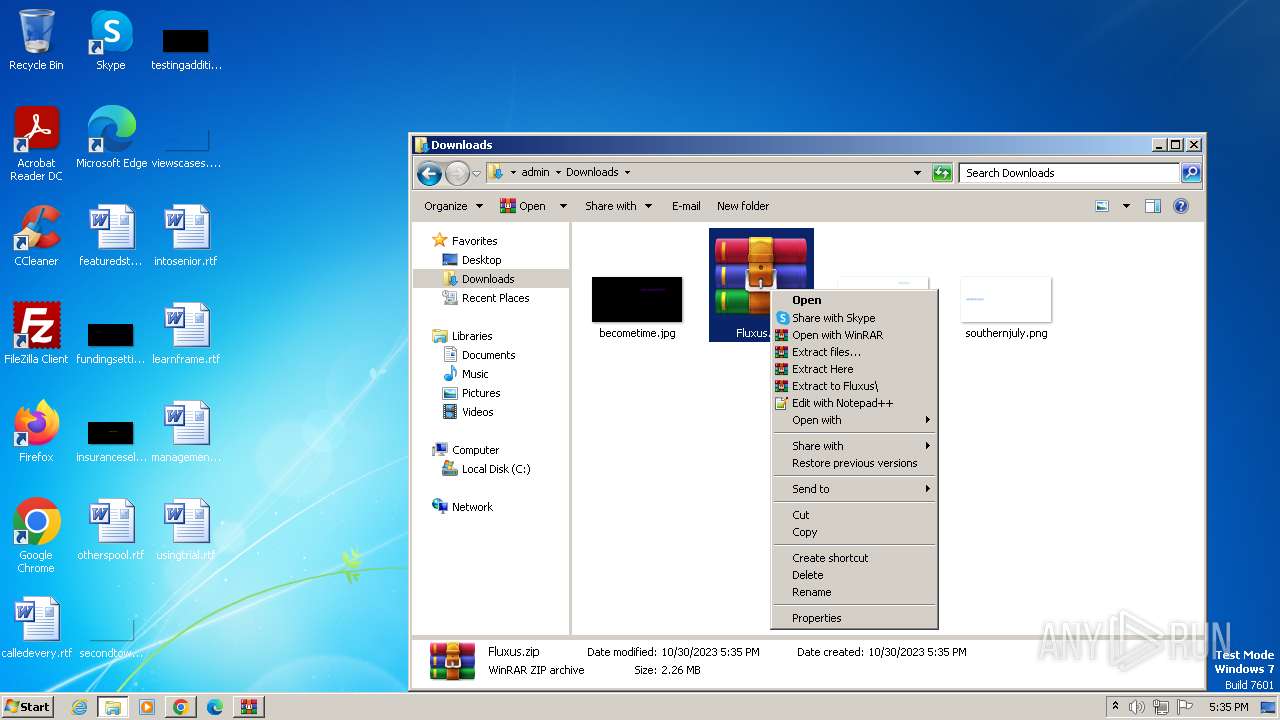
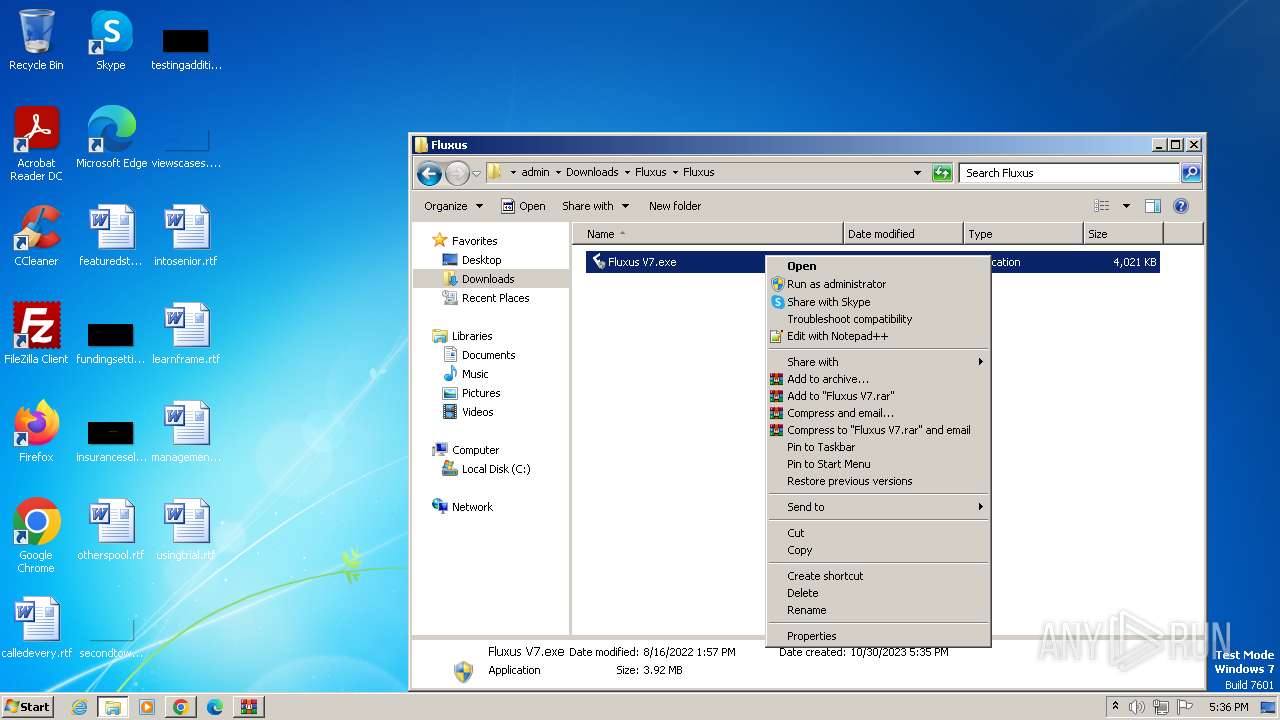
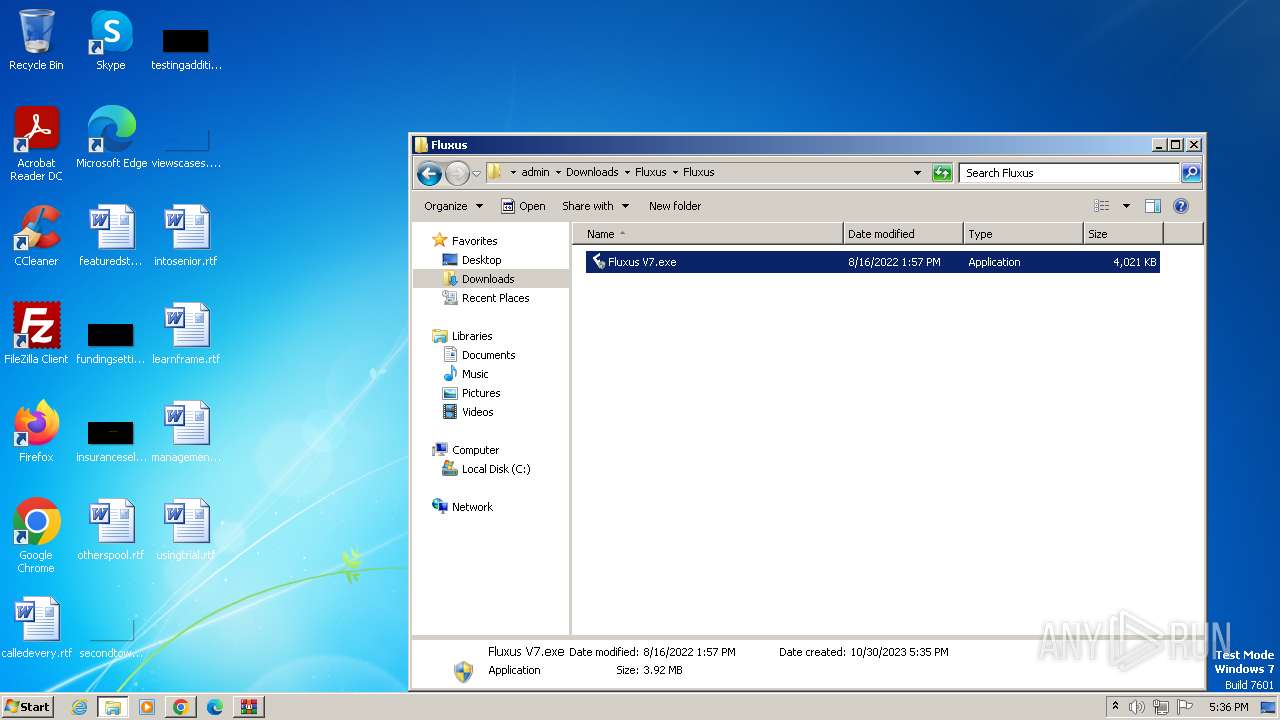
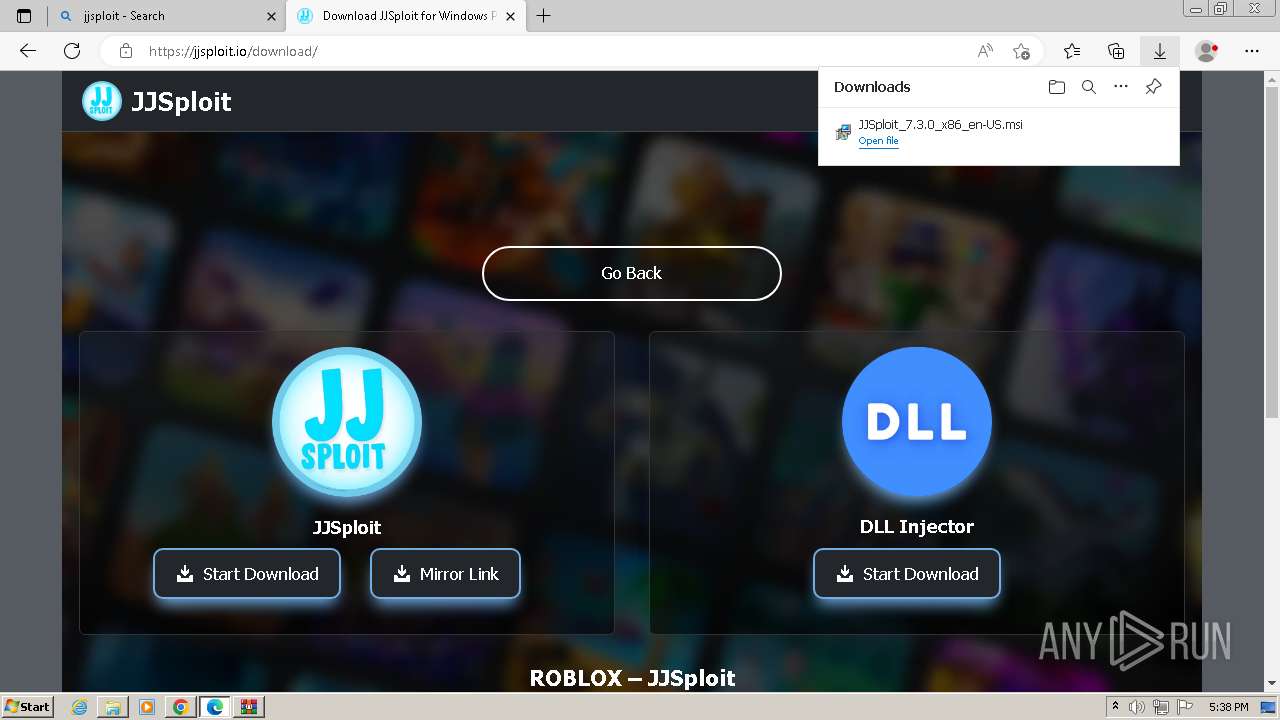
Manual execution by a user
- wmpnscfg.exe (PID: 3772)
- explorer.exe (PID: 2448)
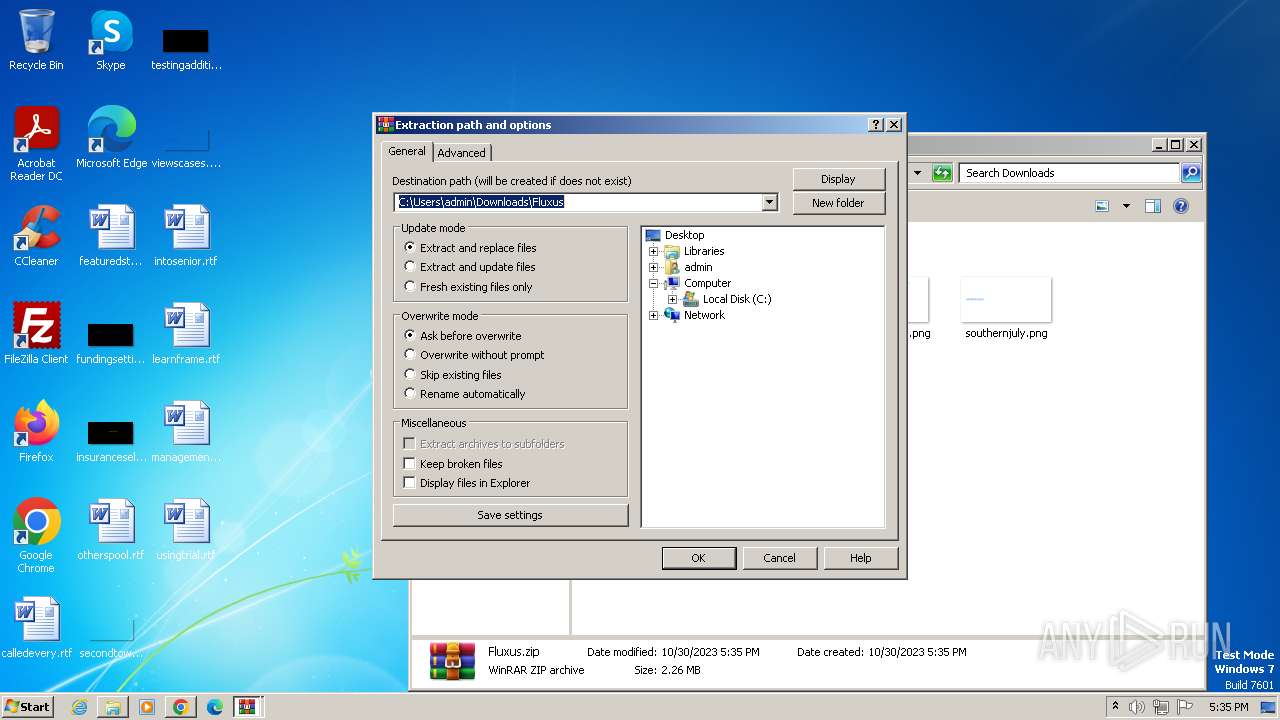
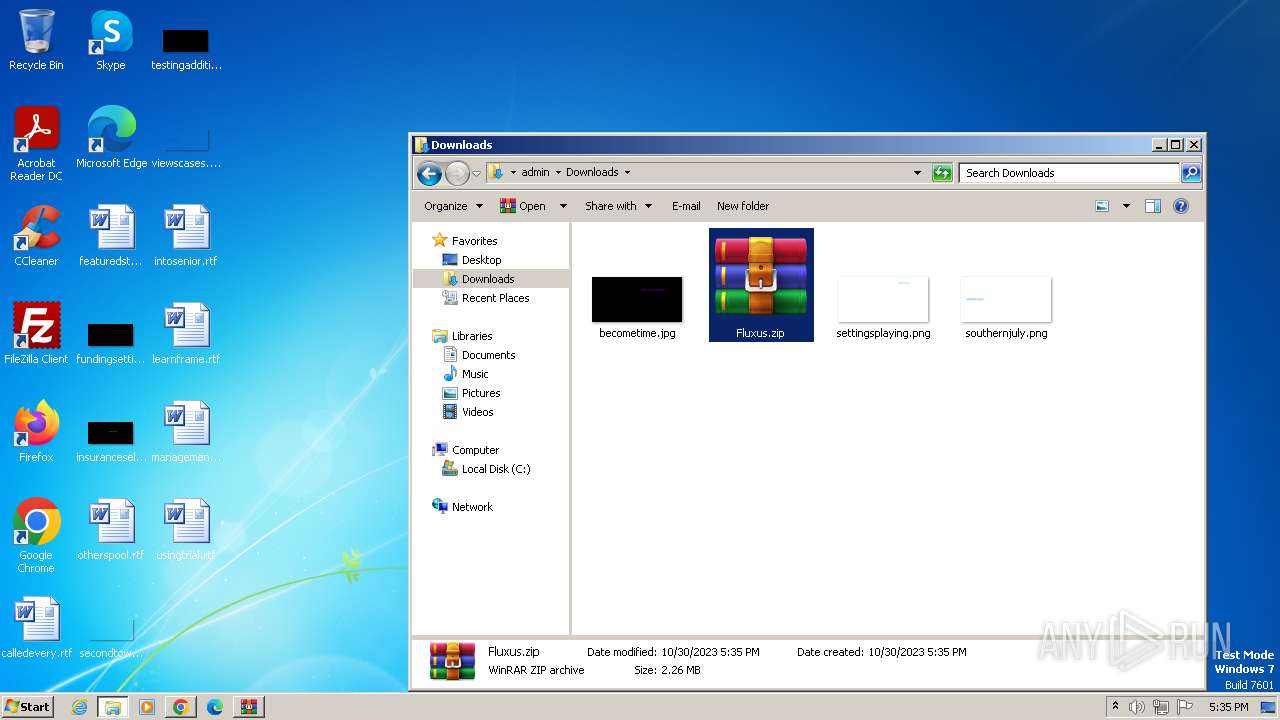
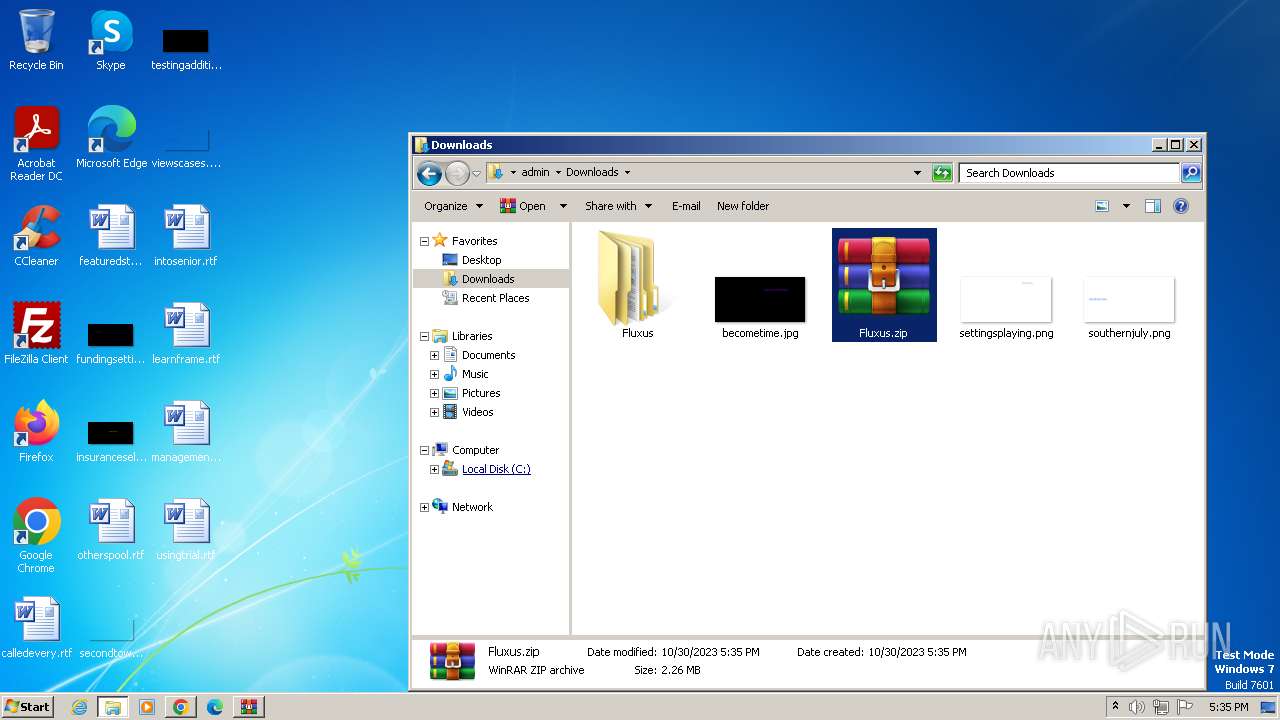
- WinRAR.exe (PID: 3468)
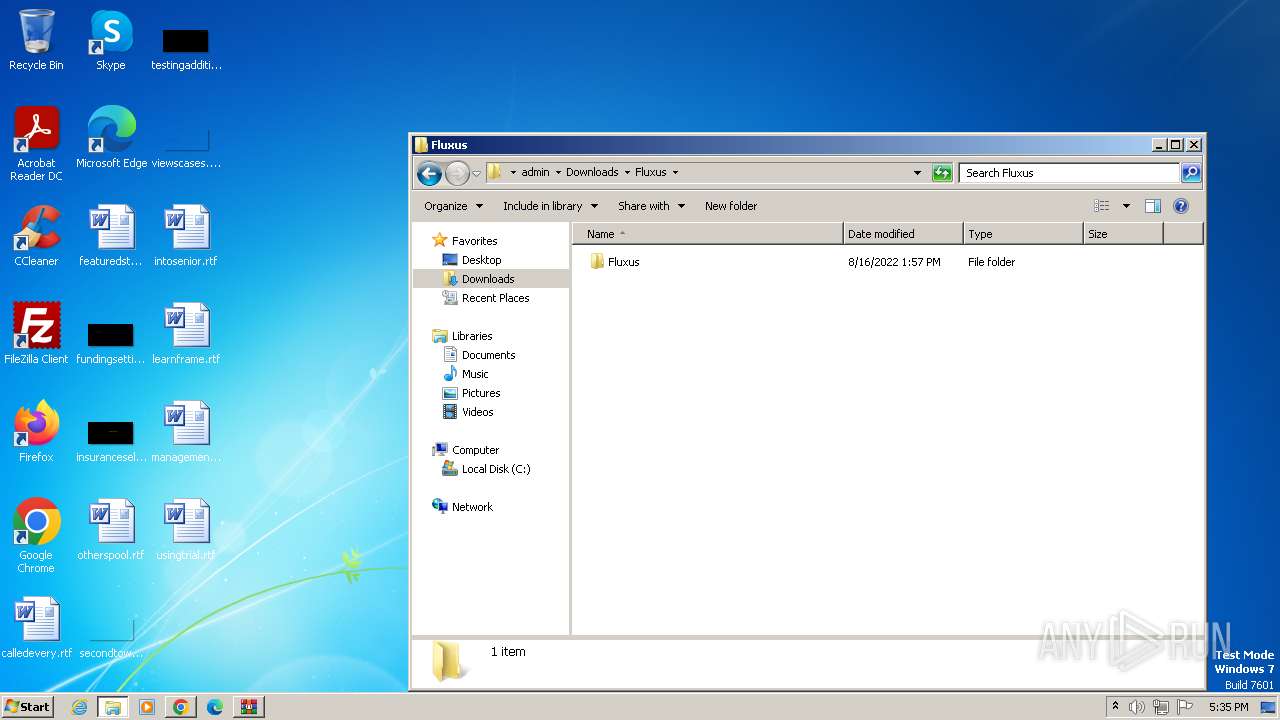
- Fluxus V7.exe (PID: 3616)
- Fluxus V7.exe (PID: 2916)
- Fluxus V7.exe (PID: 1612)
- Fluxus V7.exe (PID: 2888)
- Fluxus V7.exe (PID: 632)
- Fluxus V7.exe (PID: 3192)
- Fluxus V7.exe (PID: 3684)
- pcwrun.exe (PID: 3584)
- msedge.exe (PID: 3220)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3772)
- Fluxus V7.exe (PID: 2916)
- Fluxus V7.exe (PID: 3192)
- Fluxus V7.exe (PID: 3684)
- cvtres.exe (PID: 2700)
- csc.exe (PID: 3388)
- csc.exe (PID: 2416)
- cvtres.exe (PID: 2252)
- csc.exe (PID: 1600)
- Fluxus V7.exe (PID: 2888)
- cvtres.exe (PID: 3416)
- msiexec.exe (PID: 3936)
- msiexec.exe (PID: 3008)
Drops the executable file immediately after the start
- chrome.exe (PID: 4072)
- WinRAR.exe (PID: 3468)
- msdt.exe (PID: 3532)
- msiexec.exe (PID: 2892)
- chrome.exe (PID: 3184)
Reads the computer name
- wmpnscfg.exe (PID: 3772)
- Fluxus V7.exe (PID: 2916)
- Fluxus V7.exe (PID: 2888)
- Fluxus V7.exe (PID: 3192)
- Fluxus V7.exe (PID: 3684)
- msiexec.exe (PID: 3936)
- msiexec.exe (PID: 3008)
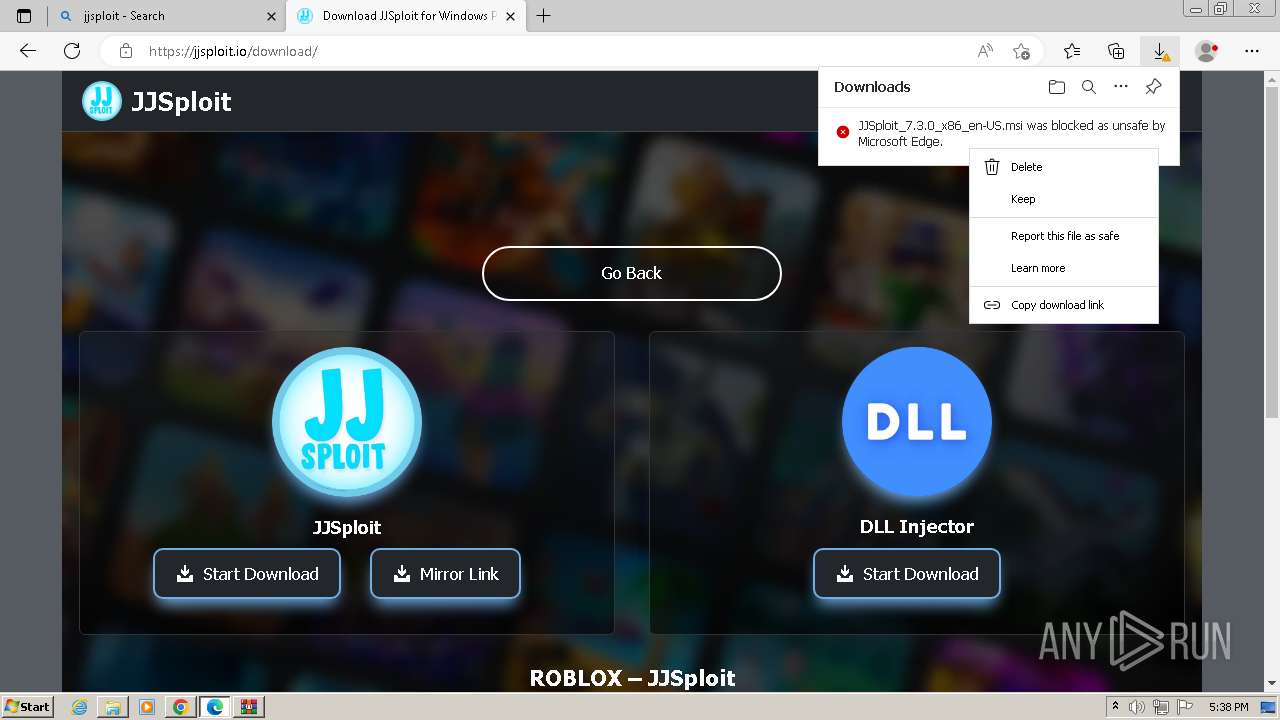
The process uses the downloaded file
- chrome.exe (PID: 2380)
- chrome.exe (PID: 316)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 1824)
- WinRAR.exe (PID: 3468)
- msedge.exe (PID: 3984)
- msedge.exe (PID: 3220)
Checks supported languages
- wmpnscfg.exe (PID: 3772)
- Fluxus V7.exe (PID: 2916)
- Fluxus V7.exe (PID: 2888)
- Fluxus V7.exe (PID: 3192)
- csc.exe (PID: 2416)
- cvtres.exe (PID: 2700)
- csc.exe (PID: 3388)
- cvtres.exe (PID: 2252)
- csc.exe (PID: 1600)
- cvtres.exe (PID: 3416)
- msiexec.exe (PID: 3936)
- msiexec.exe (PID: 3008)
- Fluxus V7.exe (PID: 3684)
Application launched itself
- chrome.exe (PID: 1920)
- msiexec.exe (PID: 3936)
- msedge.exe (PID: 3220)
Create files in a temporary directory
- Fluxus V7.exe (PID: 2916)
- pcwrun.exe (PID: 3584)
- msdt.exe (PID: 3532)
- sdiagnhost.exe (PID: 3452)
- csc.exe (PID: 2416)
- cvtres.exe (PID: 2700)
- csc.exe (PID: 3388)
- cvtres.exe (PID: 2252)
- csc.exe (PID: 1600)
- msiexec.exe (PID: 3936)
- msiexec.exe (PID: 2892)
- cvtres.exe (PID: 3416)
Reads Environment values
- Fluxus V7.exe (PID: 2916)
- Fluxus V7.exe (PID: 3192)
- Fluxus V7.exe (PID: 3684)
- Fluxus V7.exe (PID: 2888)
Reads security settings of Internet Explorer
- sdiagnhost.exe (PID: 3452)
- msdt.exe (PID: 3532)
Creates files or folders in the user directory
- msdt.exe (PID: 3532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
156
Monitored processes
98
Malicious processes
10
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3620 --field-trial-handle=1108,i,17930825848763164960,14465437107726481880,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1720 --field-trial-handle=1164,i,17624975076187117509,6778485960238780051,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 632 | "C:\Users\admin\Downloads\Fluxus\Fluxus\Fluxus V7.exe" | C:\Users\admin\Downloads\Fluxus\Fluxus\Fluxus V7.exe | — | explorer.exe | |||||||||||
User: admin Company: Fluxteam Integrity Level: MEDIUM Description: Fluxus Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4752 --field-trial-handle=1108,i,17930825848763164960,14465437107726481880,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --mojo-platform-channel-handle=1844 --field-trial-handle=1164,i,17624975076187117509,6778485960238780051,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1000 --field-trial-handle=1108,i,17930825848763164960,14465437107726481880,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1380 --field-trial-handle=1164,i,17624975076187117509,6778485960238780051,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=3500 --field-trial-handle=1108,i,17930825848763164960,14465437107726481880,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=37 --mojo-platform-channel-handle=4056 --field-trial-handle=1164,i,17624975076187117509,6778485960238780051,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1580 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=28 --mojo-platform-channel-handle=4508 --field-trial-handle=1108,i,17930825848763164960,14465437107726481880,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
37 078
Read events
36 592
Write events
343
Delete events
143
Modification events
| (PID) Process: | (1920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1920) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (1920) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
77
Suspicious files
1 690
Text files
156
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1eb0fe.TMP | — | |
MD5:— | SHA256:— | |||
| 1920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | text | |
MD5:A5EB529D94D3E97D0EE4A7E07700E0B2 | SHA256:08D211BFC570221AF7995C0625052FA7848F7E707D559C266656CDC3A9CC9F9C | |||
| 1920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:513218482935B0D388C0A990D868387A | SHA256:8E39CBAAF4AACC3A01AFA74EA8C30FB24FE69A22B8B30728AFB1614FD68809D9 | |||
| 1920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:E91E138A25FD7E5BCA5E60111F39C91A | SHA256:B1F7E3537A31A4B847F862858E5D2581993CC9372F19ABF19EA2A9185FE42A4F | |||
| 1920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1eb7a5.TMP | — | |
MD5:— | SHA256:— | |||
| 1920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF1eb302.TMP | text | |
MD5:7C1C23F006788D107F8A01B852CC6701 | SHA256:9FA4E627077EDCBEC8AAA1ED2DD5538E630790893F88F02F1E9CC863E6A27848 | |||
| 1920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\optimization_guide_hint_cache_store\LOG.old~RF1eca24.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
331
DNS requests
380
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
864 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | — | — | unknown |
864 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 5.71 Kb | unknown |
864 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 10.3 Kb | unknown |
864 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 341 Kb | unknown |
864 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 1.07 Mb | unknown |
864 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 80.3 Kb | unknown |
2916 | Fluxus V7.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?f10d87d897de67a5 | unknown | compressed | 61.6 Kb | unknown |
864 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 17.1 Kb | unknown |
864 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 9.06 Kb | unknown |
864 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 10.4 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1920 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2052 | chrome.exe | 142.251.140.45:443 | accounts.google.com | GOOGLE | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2052 | chrome.exe | 165.227.68.125:443 | fluxusexecutor.org | DIGITALOCEAN-ASN | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2052 | chrome.exe | 172.217.17.106:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
2052 | chrome.exe | 172.217.169.163:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
2052 | chrome.exe | 172.217.169.130:443 | pagead2.googlesyndication.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
fluxusexecutor.org |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
stats.wp.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
pixel.wp.com |
| whitelisted |
partner.googleadservices.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2052 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
Process | Message |
|---|---|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|