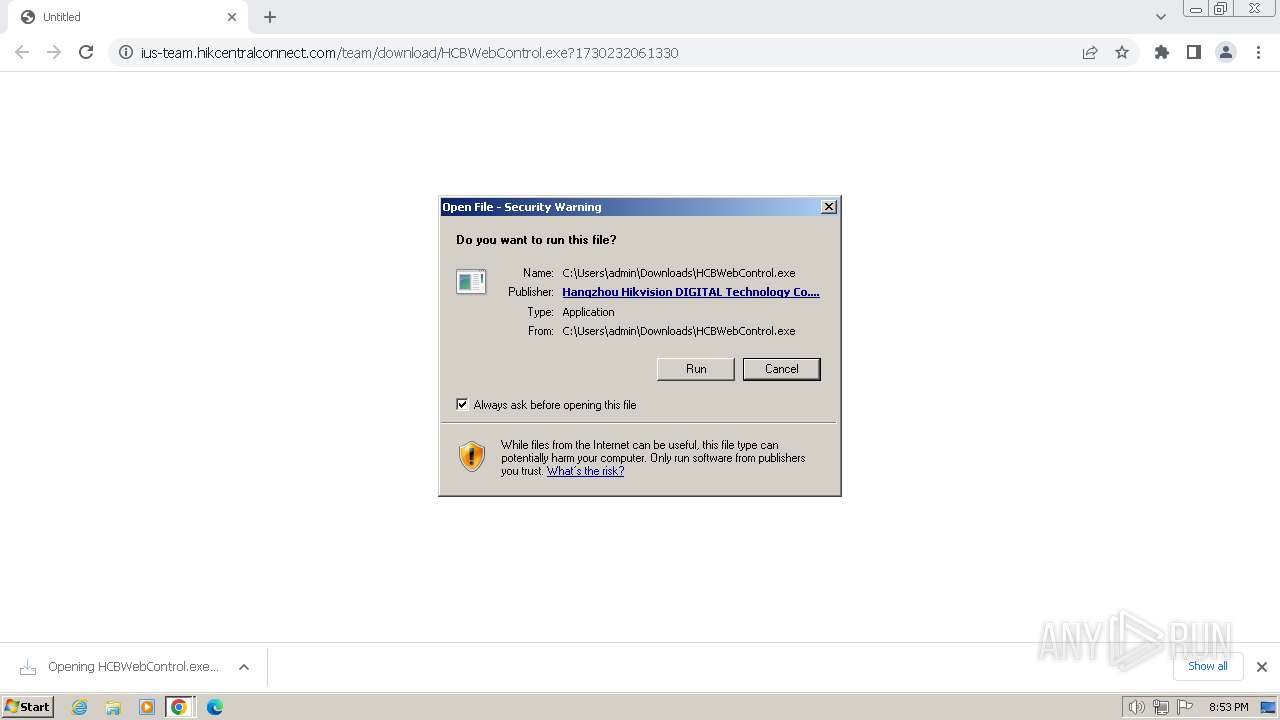
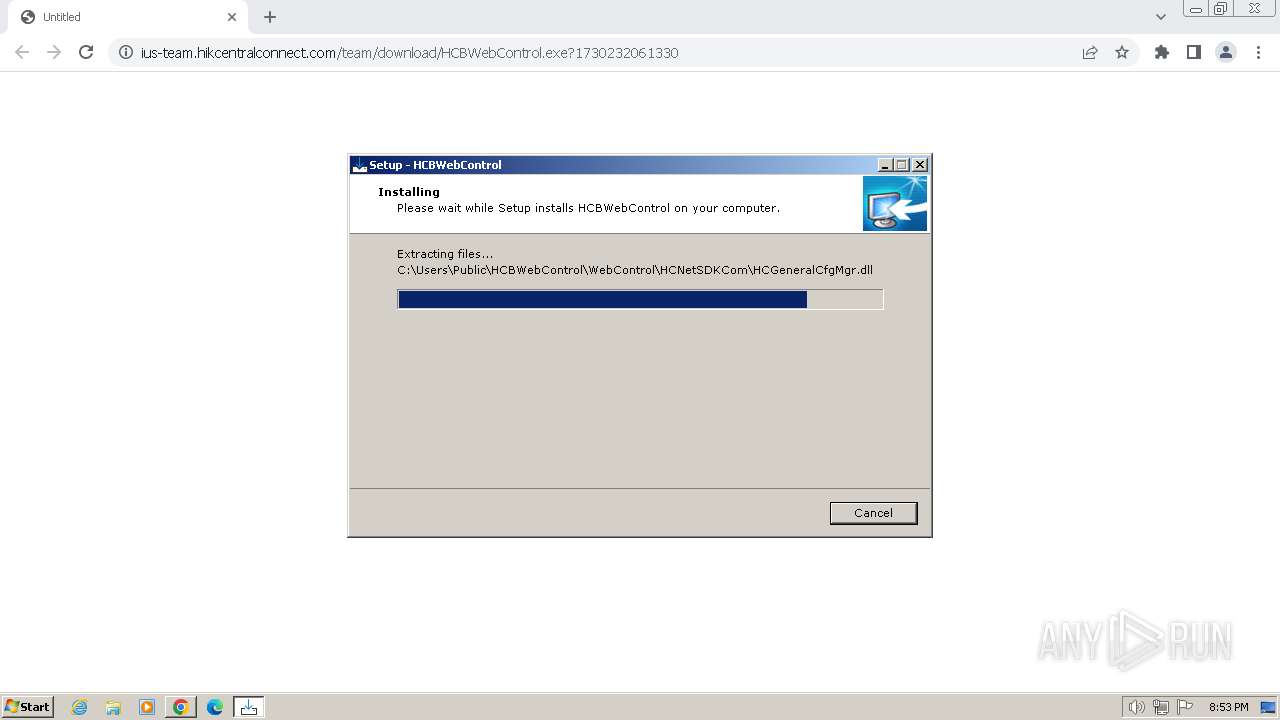
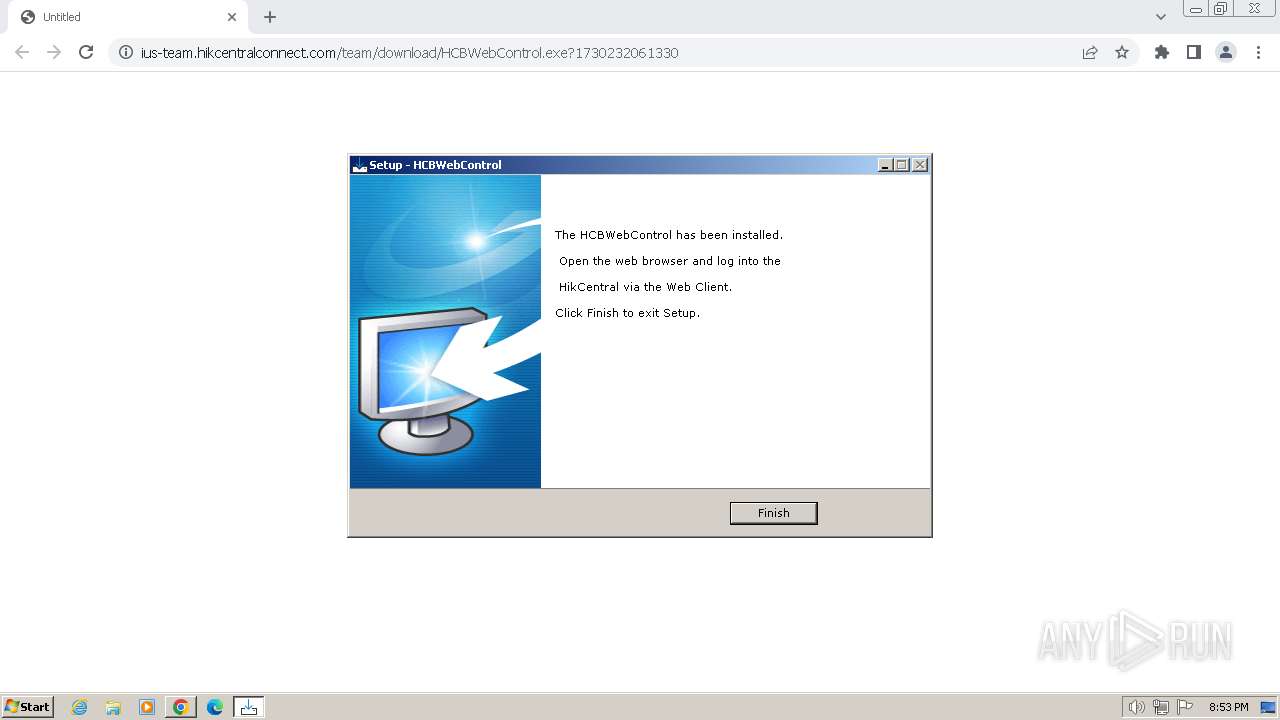
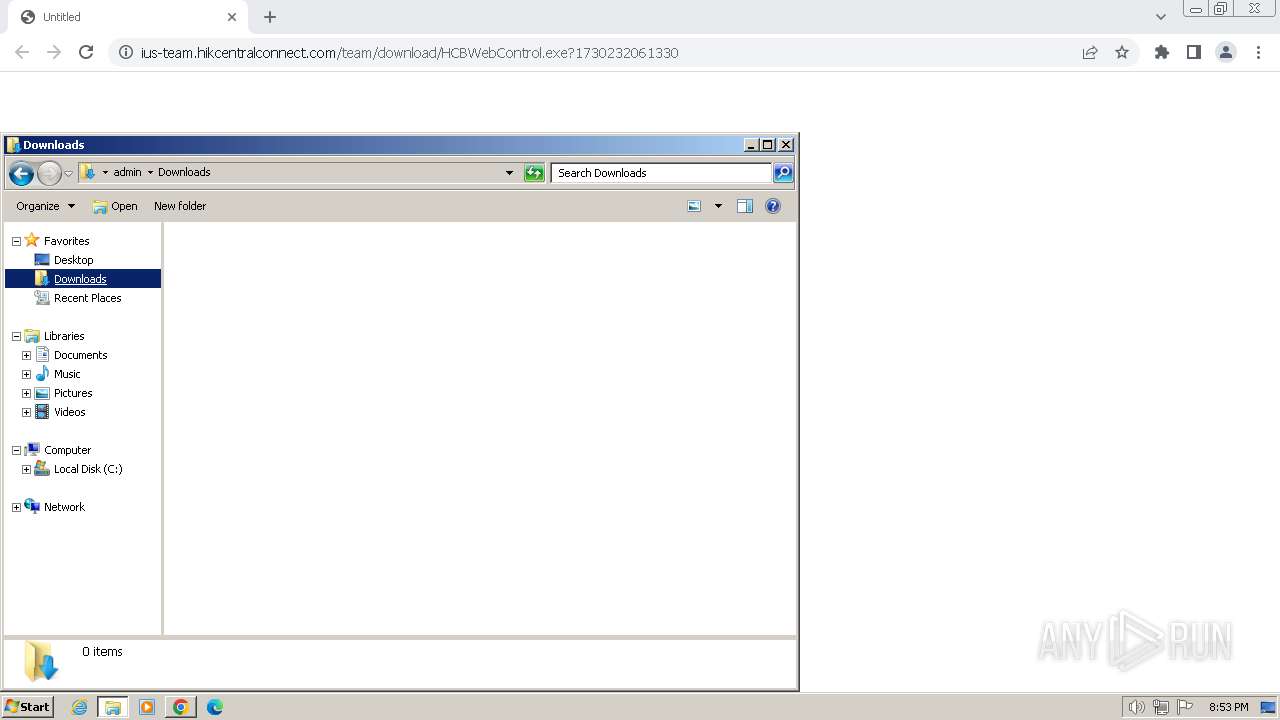
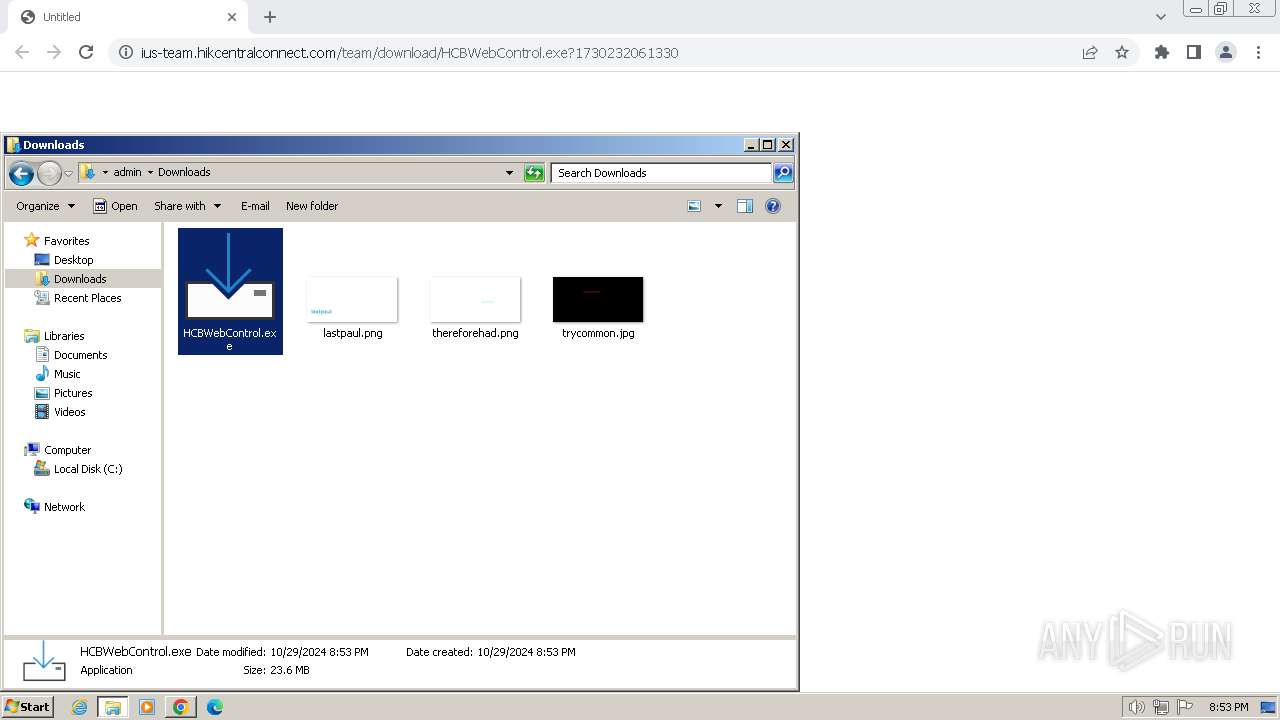
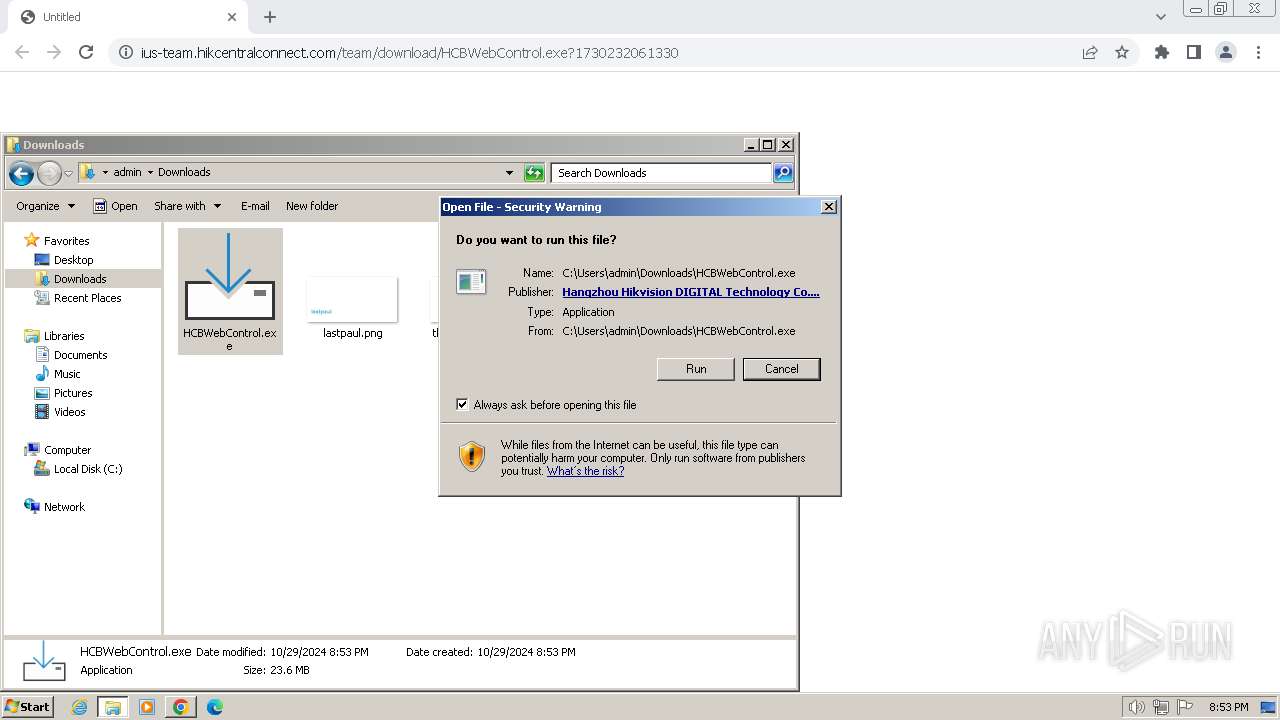
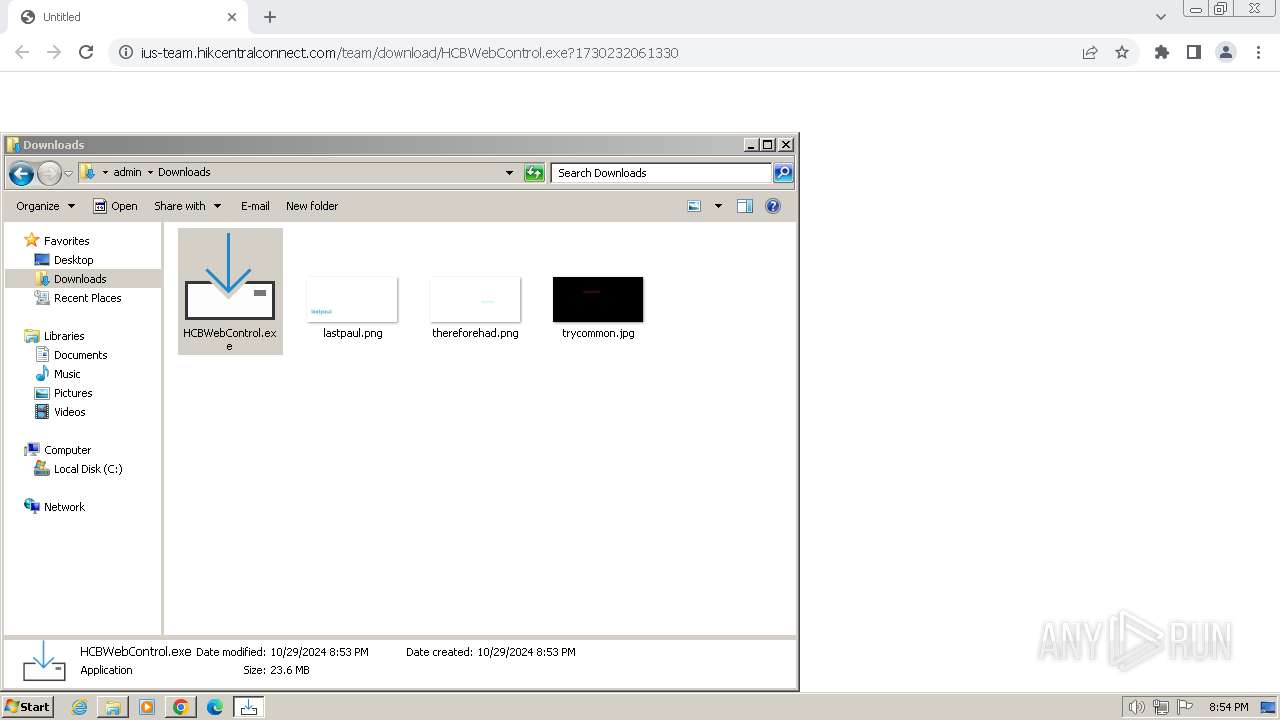
| URL: | https://ius-team.hikcentralconnect.com/team/download/HCBWebControl.exe?1730232061330 |
| Full analysis: | https://app.any.run/tasks/5a49bd6c-6ace-432d-ac14-03b3b73acf21 |
| Verdict: | Malicious activity |
| Analysis date: | October 29, 2024, 20:52:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 88E2B252CA59CC1BA248E78FE7E464A0 |
| SHA1: | BE6C125D7D229557A65D1A949845F72FED771969 |
| SHA256: | 20C0822365306D78B53B049AA7E79EE4AFE6666FCAE777EE6771046DAF733024 |
| SSDEEP: | 3:N8yhLNNXWLKc2UTfXSVw7S:2yhLNcLKiSVw7S |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Windows owner or organization settings
- HCBWebControl.tmp (PID: 2792)
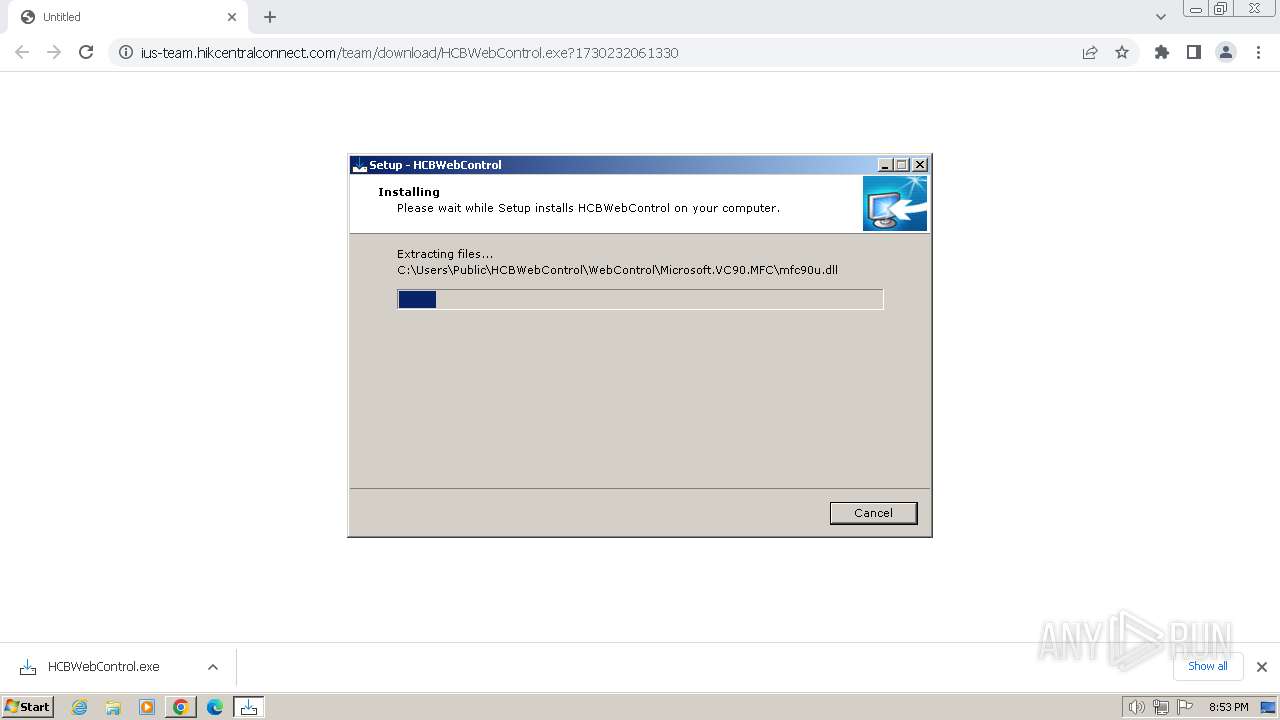
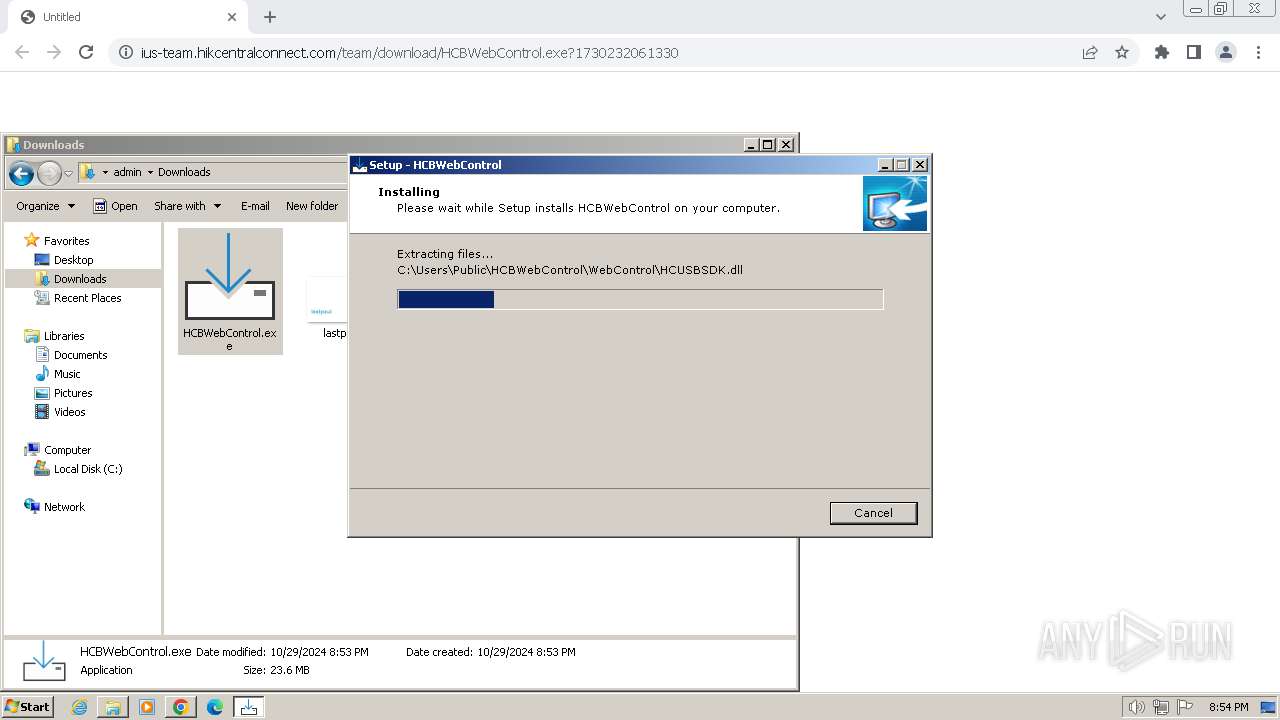
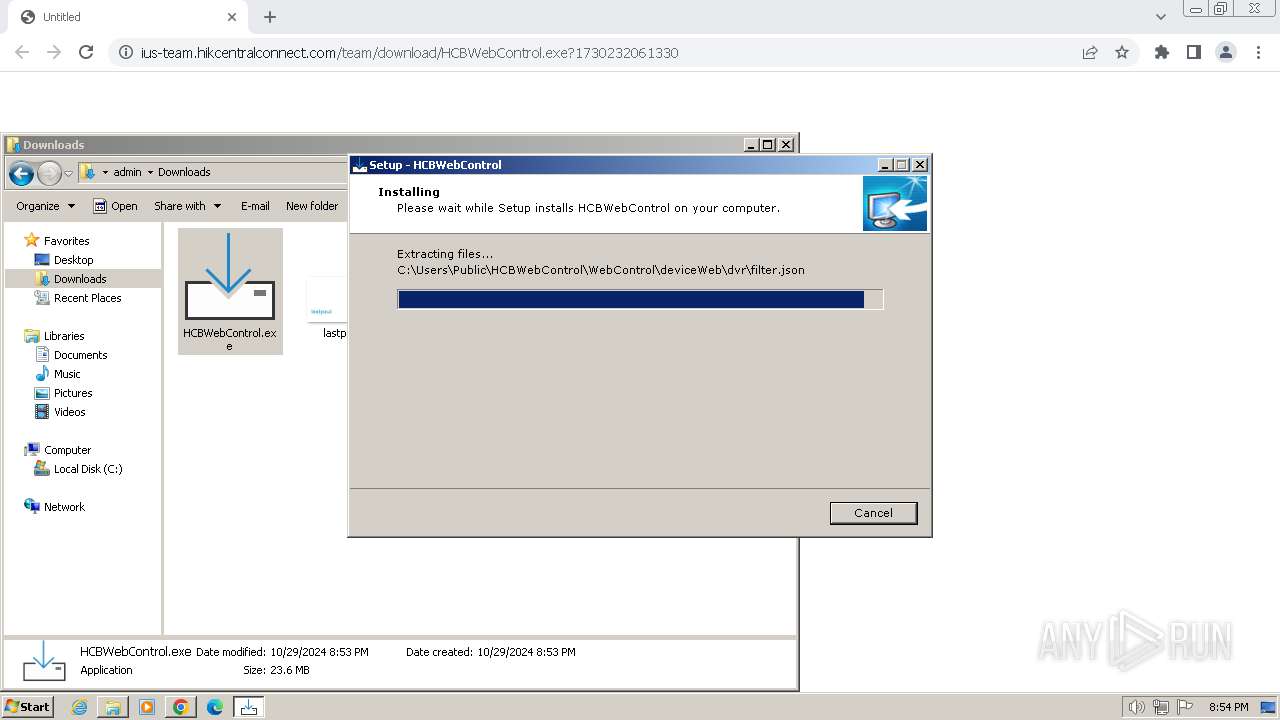
Executable content was dropped or overwritten
- HCBWebControl.tmp (PID: 2792)
- HCBWebControl.exe (PID: 2024)
- unins000.exe (PID: 3840)
- HCBWebControl.tmp (PID: 3364)
- HCBWebControl.exe (PID: 2540)
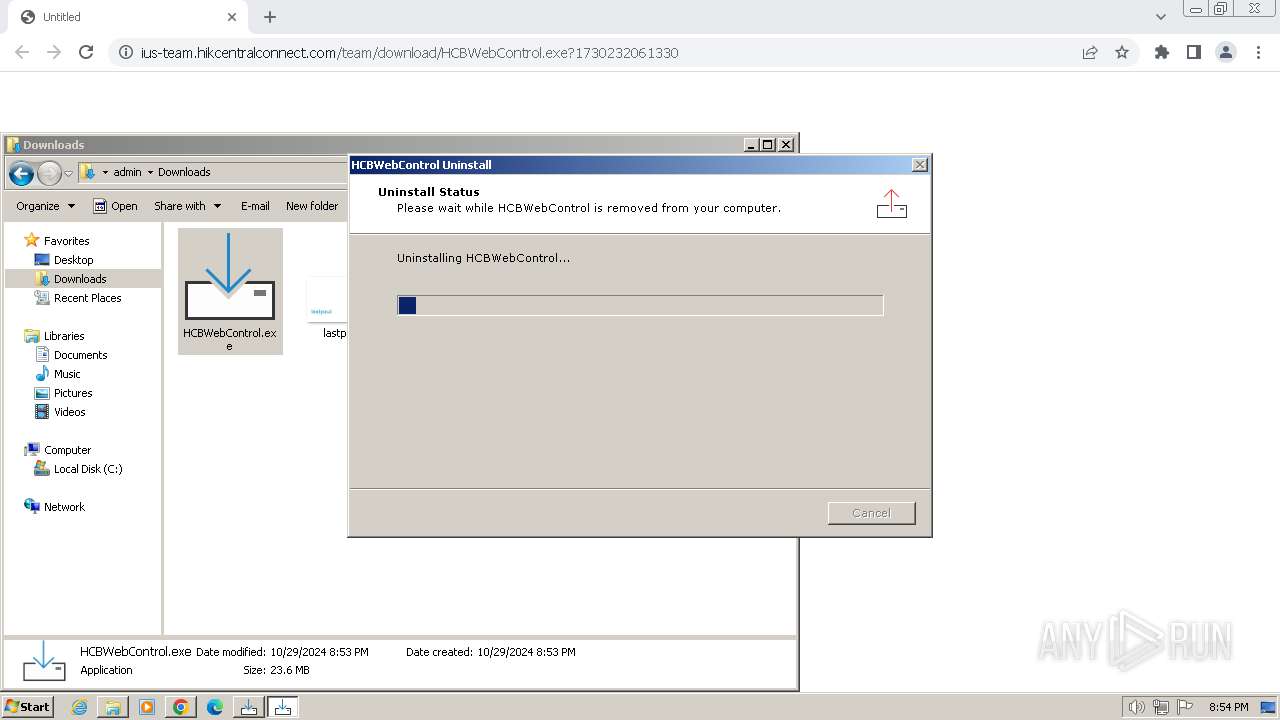
Uses TASKKILL.EXE to kill process
- HCBWebControl.tmp (PID: 2792)
- _iu14D2N.tmp (PID: 3376)
- HCBWebControl.tmp (PID: 3364)
The process drops C-runtime libraries
- HCBWebControl.tmp (PID: 2792)
- HCBWebControl.tmp (PID: 3364)
Drops 7-zip archiver for unpacking
- HCBWebControl.tmp (PID: 2792)
- HCBWebControl.tmp (PID: 3364)
Node.exe was dropped
- HCBWebControl.tmp (PID: 2792)
- HCBWebControl.tmp (PID: 3364)
Drops a system driver (possible attempt to evade defenses)
- HCBWebControl.tmp (PID: 2792)
- HCBWebControl.tmp (PID: 3364)
Likely accesses (executes) a file from the Public directory
- unins000.exe (PID: 3840)
- HCBWebControlService.exe (PID: 3384)
- _iu14D2N.tmp (PID: 3376)
- HCBWebControlService.exe (PID: 3888)
Starts application with an unusual extension
- unins000.exe (PID: 3840)
Process drops legitimate windows executable
- HCBWebControl.tmp (PID: 3364)
- HCBWebControl.tmp (PID: 2792)
Starts itself from another location
- unins000.exe (PID: 3840)
INFO
Application launched itself
- chrome.exe (PID: 3680)
Executable content was dropped or overwritten
- chrome.exe (PID: 3680)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 3708)
Reads the computer name
- wmpnscfg.exe (PID: 3376)
- HCBWebControl.tmp (PID: 2792)
Checks supported languages
- HCBWebControl.exe (PID: 2024)
- wmpnscfg.exe (PID: 3376)
- HCBWebControl.tmp (PID: 2792)
The process uses the downloaded file
- chrome.exe (PID: 660)
- chrome.exe (PID: 3680)
Create files in a temporary directory
- HCBWebControl.exe (PID: 2024)
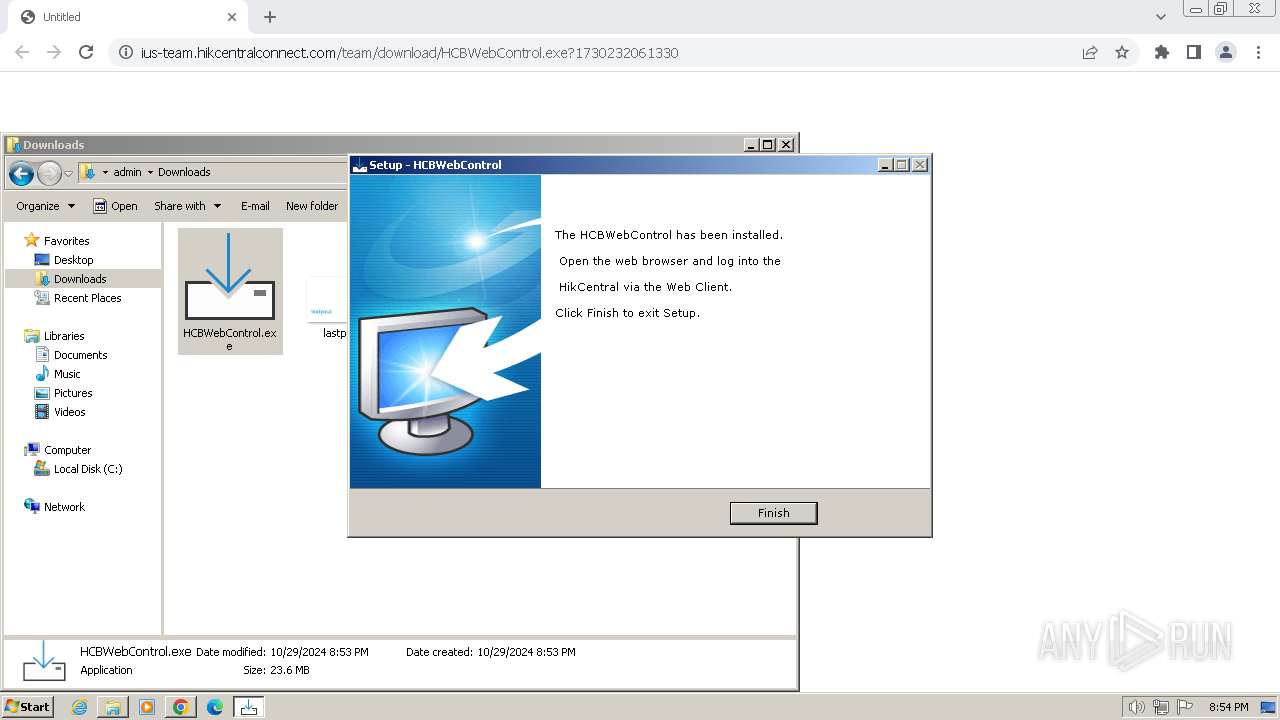
Node.js compiler has been detected
- HCBWebControlService.exe (PID: 3384)
- HCBWebControlService.exe (PID: 3888)
Manual execution by a user
- explorer.exe (PID: 740)
- wmpnscfg.exe (PID: 3376)
- HCBWebControl.exe (PID: 2540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
95
Monitored processes
53
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3024 --field-trial-handle=1120,i,5063446704984409004,7441862366621580708,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3736 --field-trial-handle=1120,i,5063446704984409004,7441862366621580708,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 656 | "taskkill" /F /IM HCBWebControlService* | C:\Windows\System32\taskkill.exe | — | HCBWebControl.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3984 --field-trial-handle=1120,i,5063446704984409004,7441862366621580708,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2000 --field-trial-handle=1120,i,5063446704984409004,7441862366621580708,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 740 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1320 --field-trial-handle=1120,i,5063446704984409004,7441862366621580708,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3604 --field-trial-handle=1120,i,5063446704984409004,7441862366621580708,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3020 --field-trial-handle=1120,i,5063446704984409004,7441862366621580708,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4044 --field-trial-handle=1120,i,5063446704984409004,7441862366621580708,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
11 774
Read events
11 426
Write events
327
Delete events
21
Modification events
| (PID) Process: | (3680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3680) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
703
Suspicious files
355
Text files
260
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF22c4f0.TMP | — | |
MD5:— | SHA256:— | |||
| 3680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:5CB0B2845A3BDF2304E7CEA61A3FC51E | SHA256:0A73277FE3C683BCACFCF2658568C9D750AB78F56A4DEA9FBD563AA5D67EC666 | |||
| 3680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF22c658.TMP | text | |
MD5:98CC34E7F20FD8F55568DB9B3D3B507E | SHA256:8D3D74EC41FF0CCE1F26B23F66E5981B7F59C40AB0DBB468B3A3E5E63C80F3C7 | |||
| 3680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old | text | |
MD5:B5E55E1471D8BF954337879C53C5BDCE | SHA256:91CE82AFB9D29EB21CAD1F4A7283D3F0C3C8DD91446E623D0D7208BA3DD3F0B6 | |||
| 3680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF22c9b3.TMP | — | |
MD5:— | SHA256:— | |||
| 3680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF22c696.TMP | text | |
MD5:6344721DA60A3CF7027C43288C8991C6 | SHA256:DA3AD5C3641E42979DFB9D4178EDE8533F887C3ACF9C49BE9737D83CEDA55473 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
60
DNS requests
47
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3skwo2srs5xchyxzz6ujgnedha_9.52.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.52.0_all_acwwpgcqveuj5szz3wkl52k5lm5a.crx3 | unknown | — | — | whitelisted |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3skwo2srs5xchyxzz6ujgnedha_9.52.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.52.0_all_acwwpgcqveuj5szz3wkl52k5lm5a.crx3 | unknown | — | — | whitelisted |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acnleymbtlsyj53fasabeufn3vda_9253/hfnkpimlhhgieaddgfemjhofmfblmnib_9253_all_acvv5kqwtichdb2avatv3srlaknq.crx3 | unknown | — | — | whitelisted |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3skwo2srs5xchyxzz6ujgnedha_9.52.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.52.0_all_acwwpgcqveuj5szz3wkl52k5lm5a.crx3 | unknown | — | — | whitelisted |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3skwo2srs5xchyxzz6ujgnedha_9.52.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.52.0_all_acwwpgcqveuj5szz3wkl52k5lm5a.crx3 | unknown | — | — | whitelisted |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | — | — | whitelisted |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac6mhlwypzipnufijdvfyhdgvt4q_67/khaoiebndkojlmppeemjhbpbandiljpe_67_win_kfegpqlp6gezs4ree2ol2br2ym.crx3 | unknown | — | — | whitelisted |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | — | — | whitelisted |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | — | — | whitelisted |
844 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac6mhlwypzipnufijdvfyhdgvt4q_67/khaoiebndkojlmppeemjhbpbandiljpe_67_win_kfegpqlp6gezs4ree2ol2br2ym.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3680 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3060 | chrome.exe | 173.194.69.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3060 | chrome.exe | 18.66.147.39:443 | ius-team.hikcentralconnect.com | AMAZON-02 | US | unknown |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
3680 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3060 | chrome.exe | 142.250.186.100:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ius-team.hikcentralconnect.com |
| unknown |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
Process | Message |
|---|---|
PluginTools.exe | [client] {
"method": "connectionStatusChanged",
"status": "disconnected",
"reason": "1016"
}
|