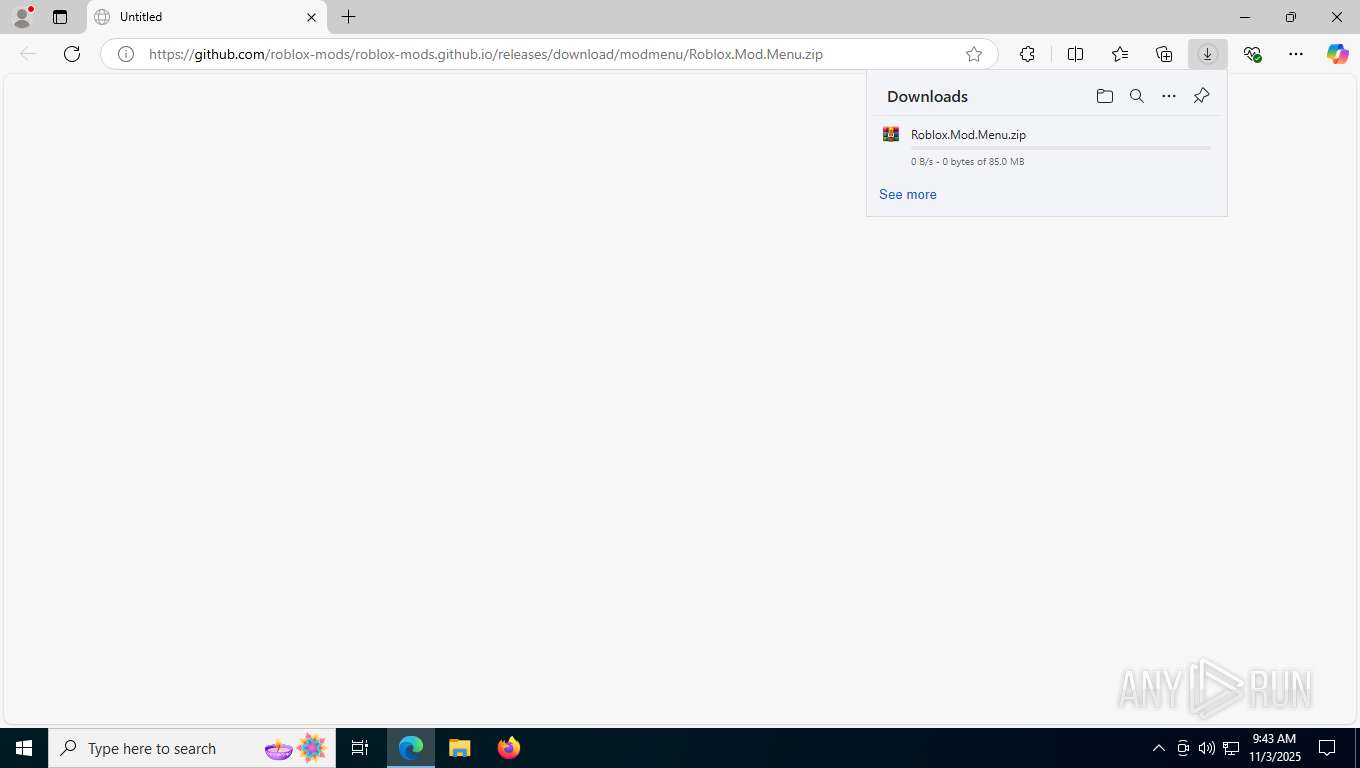
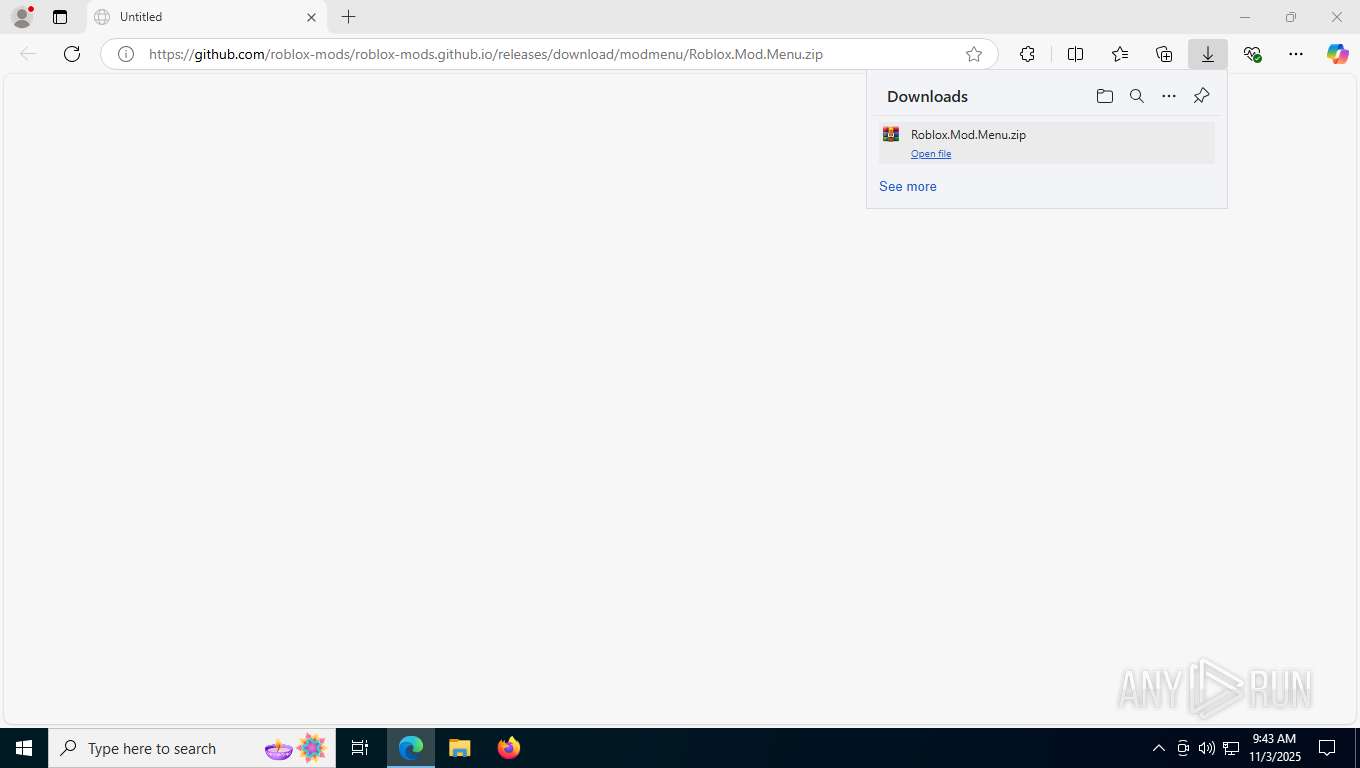
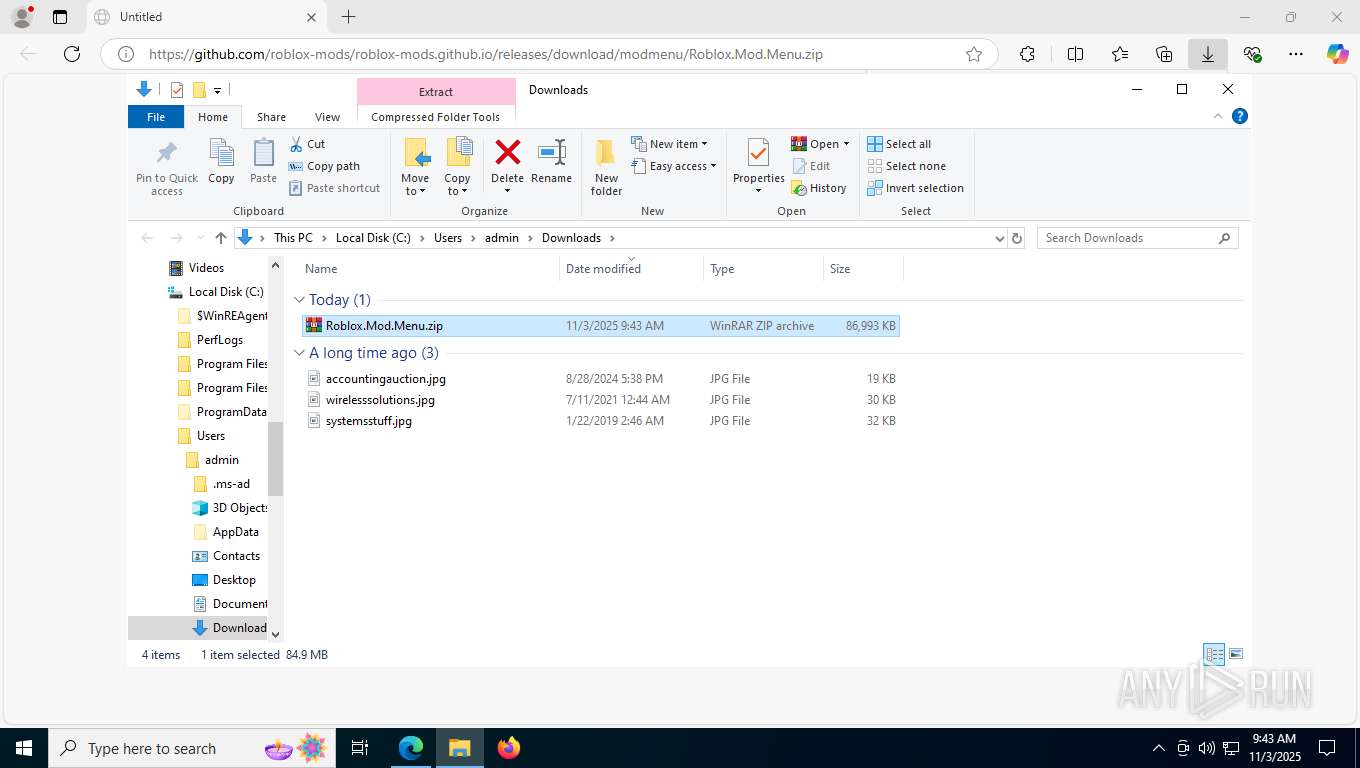
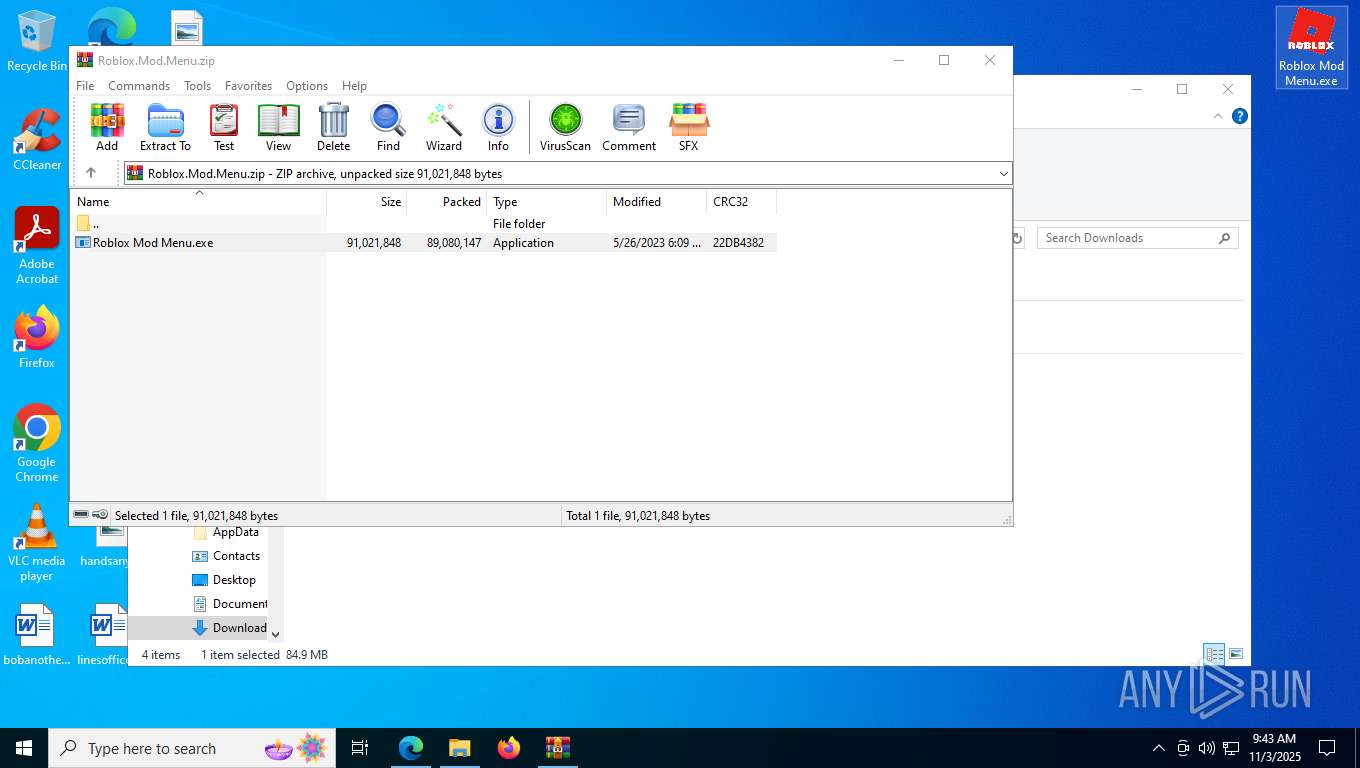
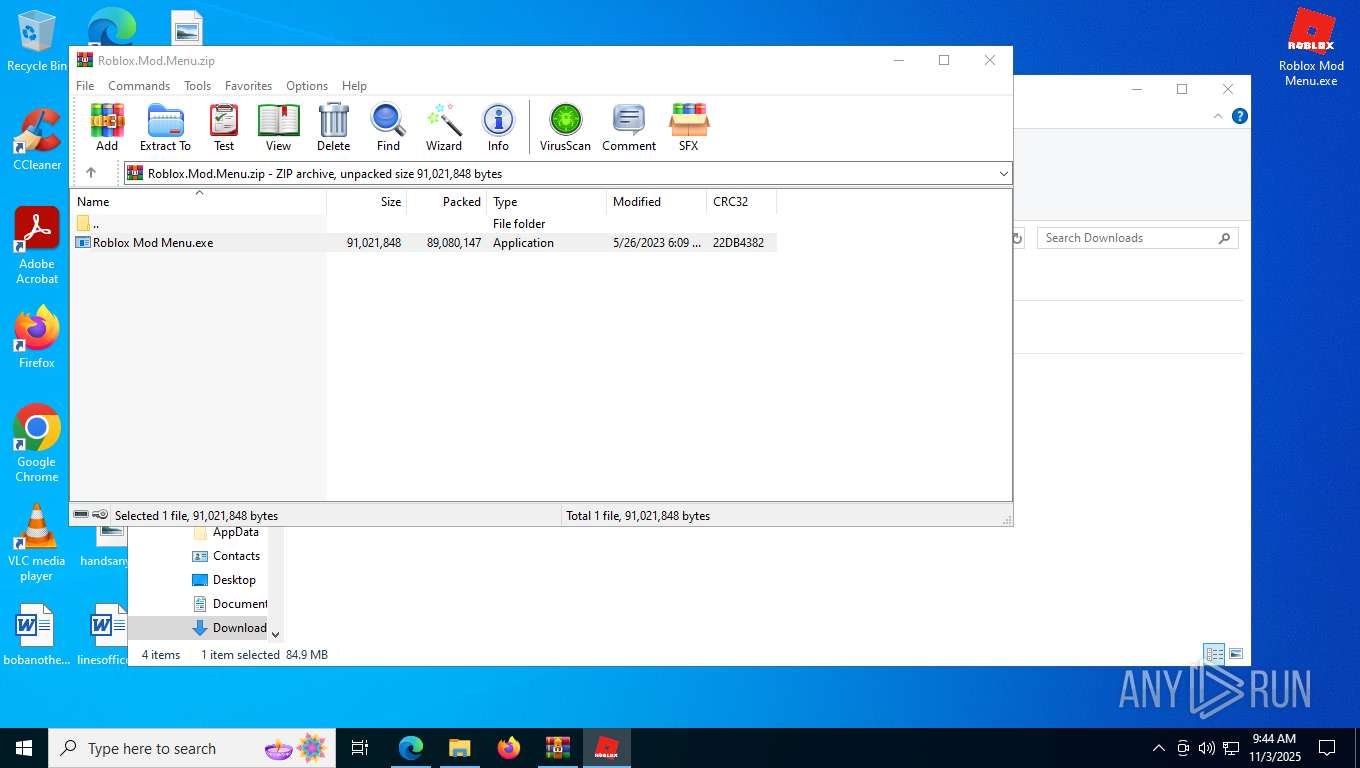
| URL: | https://github.com/roblox-mods/roblox-mods.github.io/releases/download/modmenu/Roblox.Mod.Menu.zip |
| Full analysis: | https://app.any.run/tasks/47ecbd90-d746-43dc-9963-988a19991dfe |
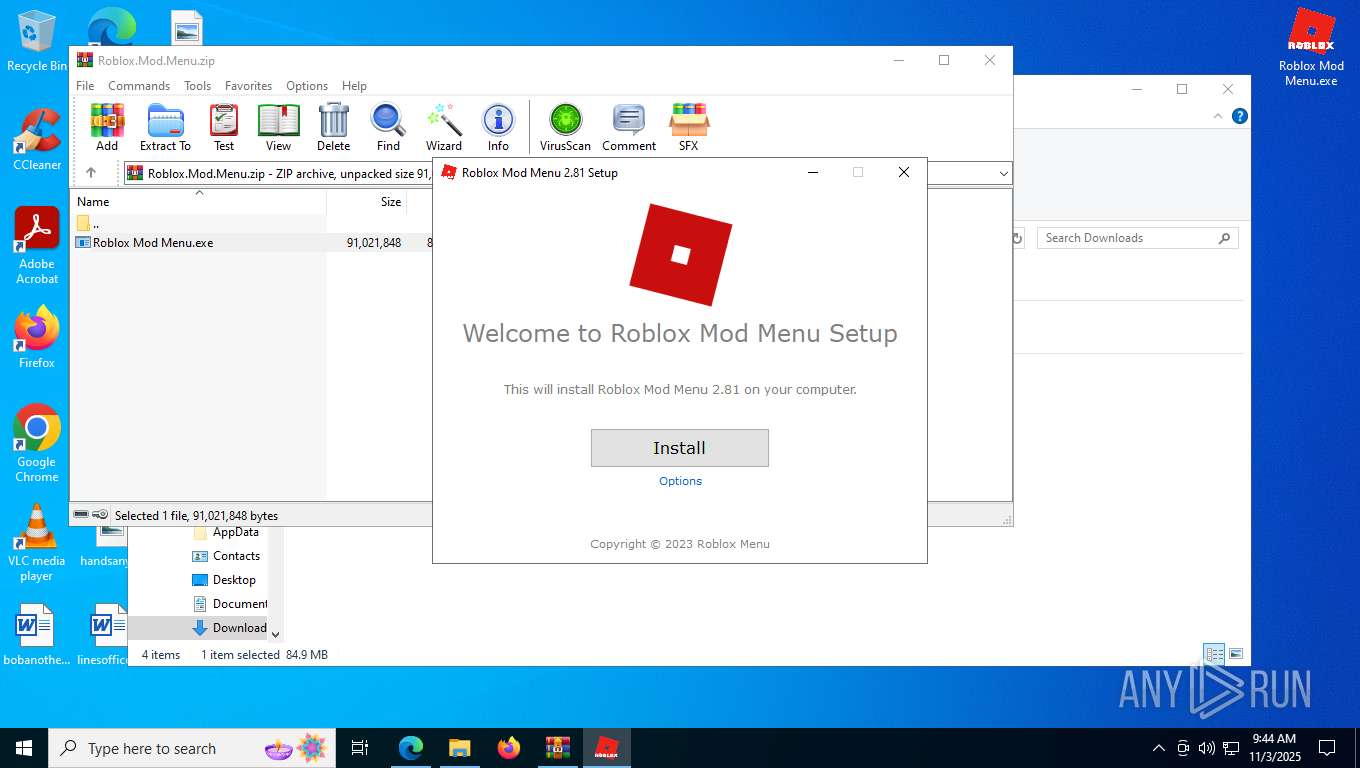
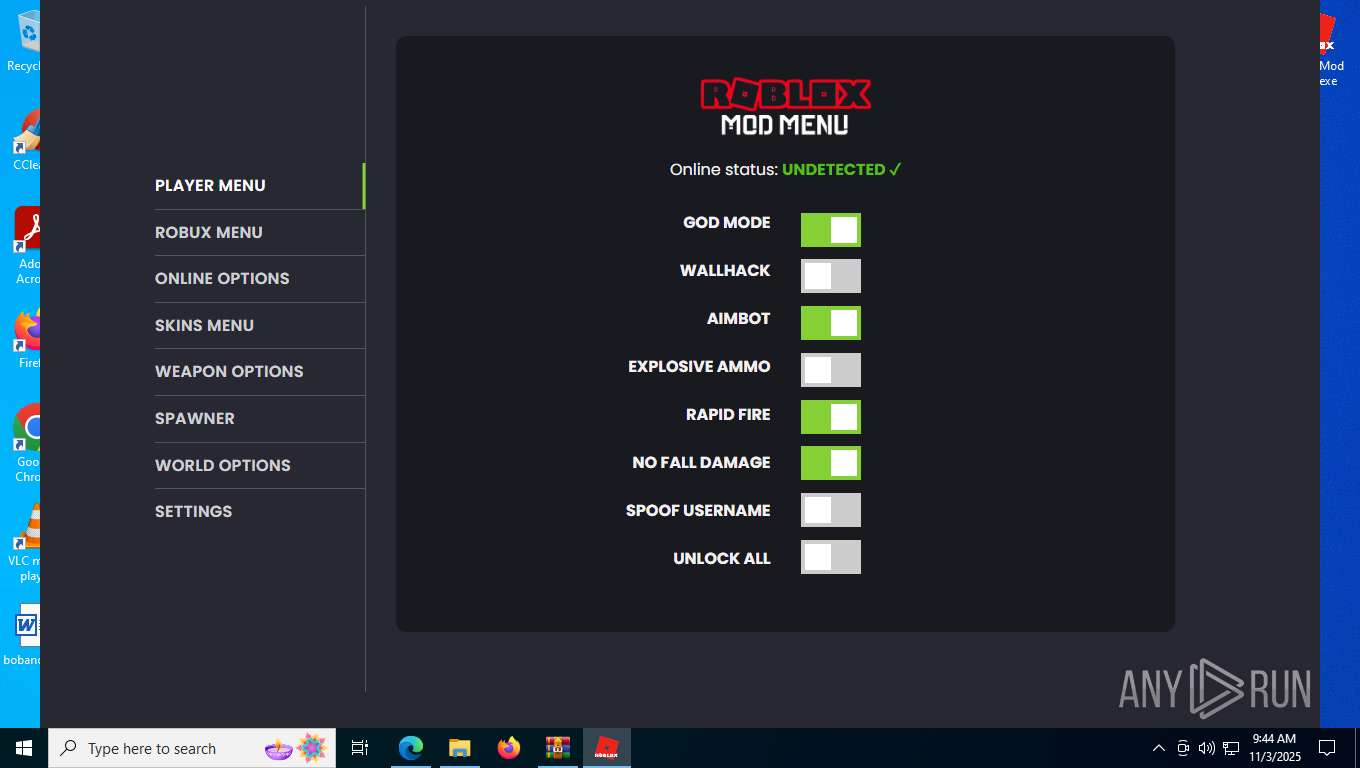
| Verdict: | Malicious activity |
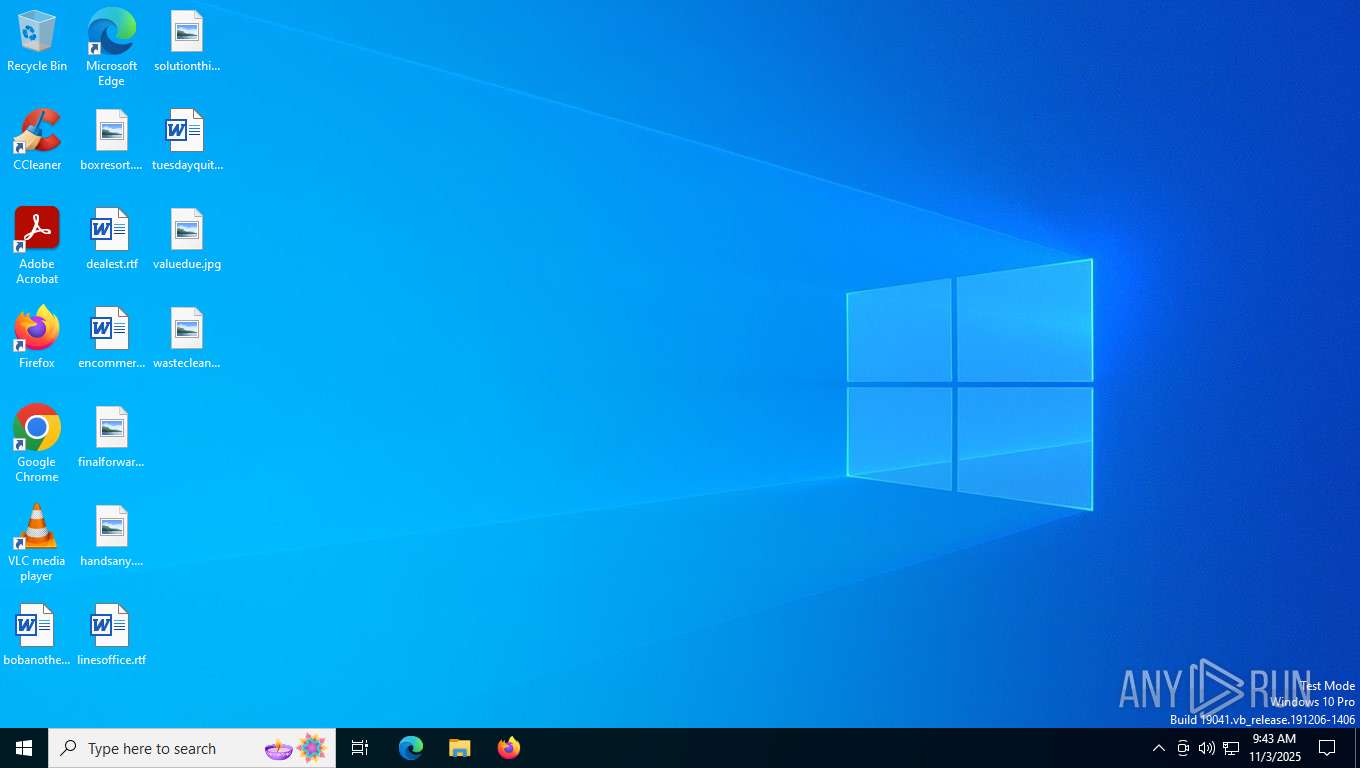
| Analysis date: | November 03, 2025, 09:43:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 866D4948DB2F798BC2B3894DFDC2F9CD |
| SHA1: | 5AB751441585467B6C49CF5A0EE39770DA244C4D |
| SHA256: | 20A1A555229310BB3B334F11596F00D7AD4AF5F087A4A77F5E1A746527B34F78 |
| SSDEEP: | 3:N8tEdnHdAPtAO8IkC3WOLeLcn:2uVdgj8I9Wkxn |
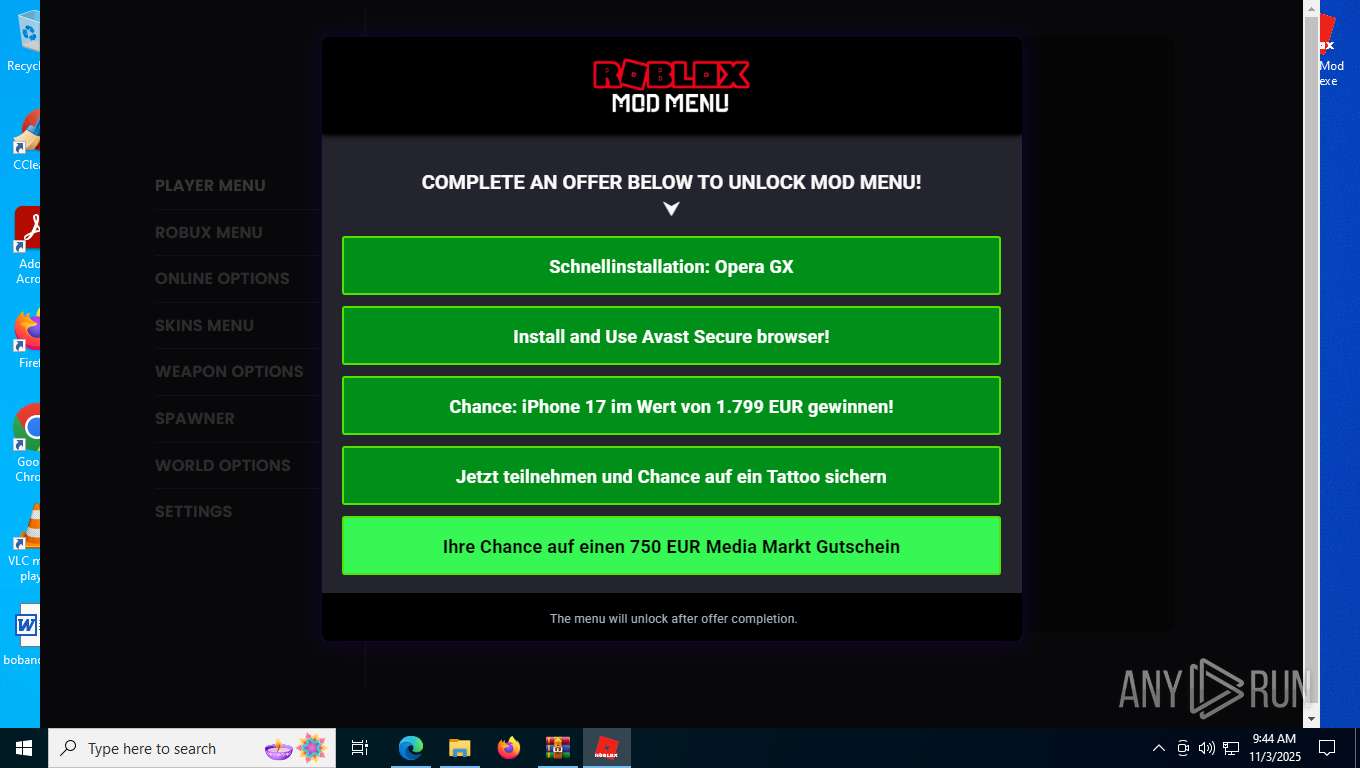
MALICIOUS
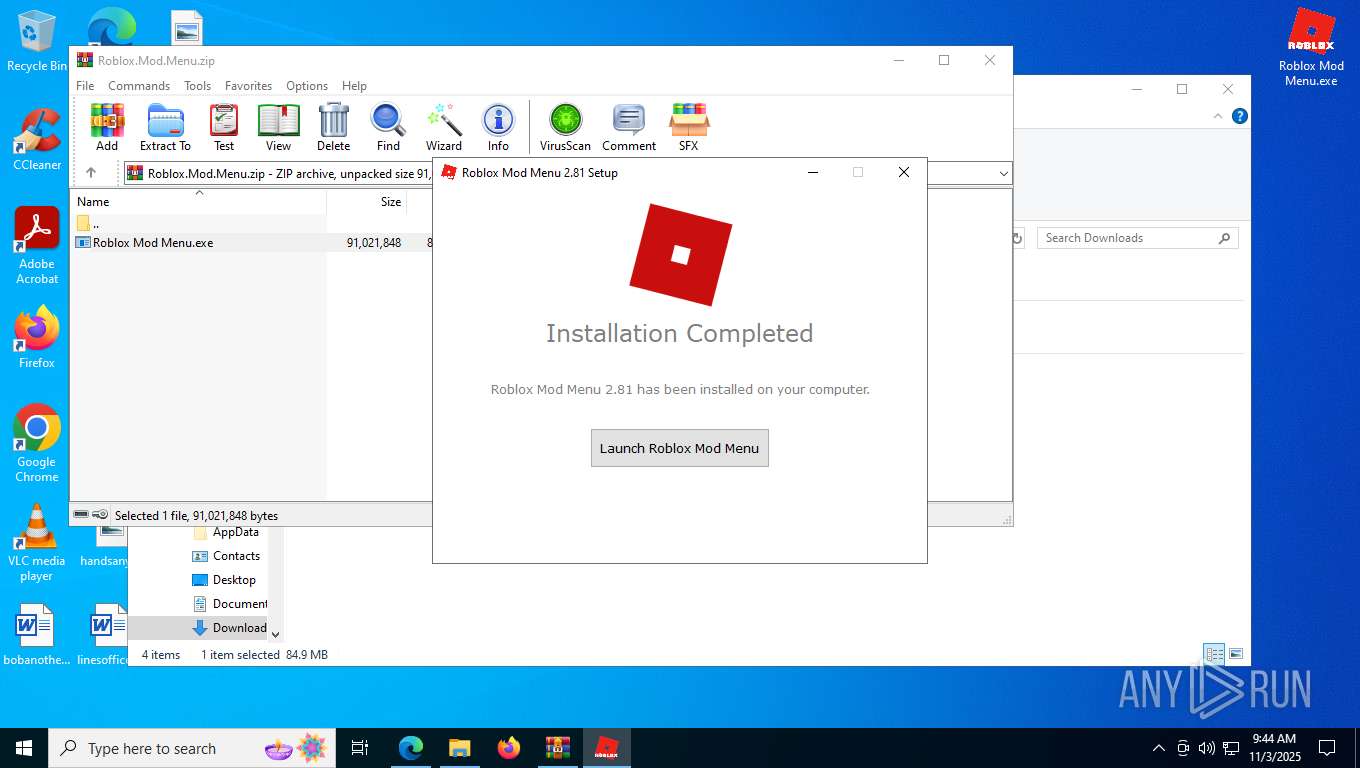
Changes the autorun value in the registry
- Roblox Mod Menu.exe (PID: 8868)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- Roblox Mod Menu.exe (PID: 8868)
Process drops legitimate windows executable
- Roblox Mod Menu.exe (PID: 8868)
Reads security settings of Internet Explorer
- Roblox Mod Menu.exe (PID: 8868)
- Roblox Mod Menu.exe (PID: 8320)
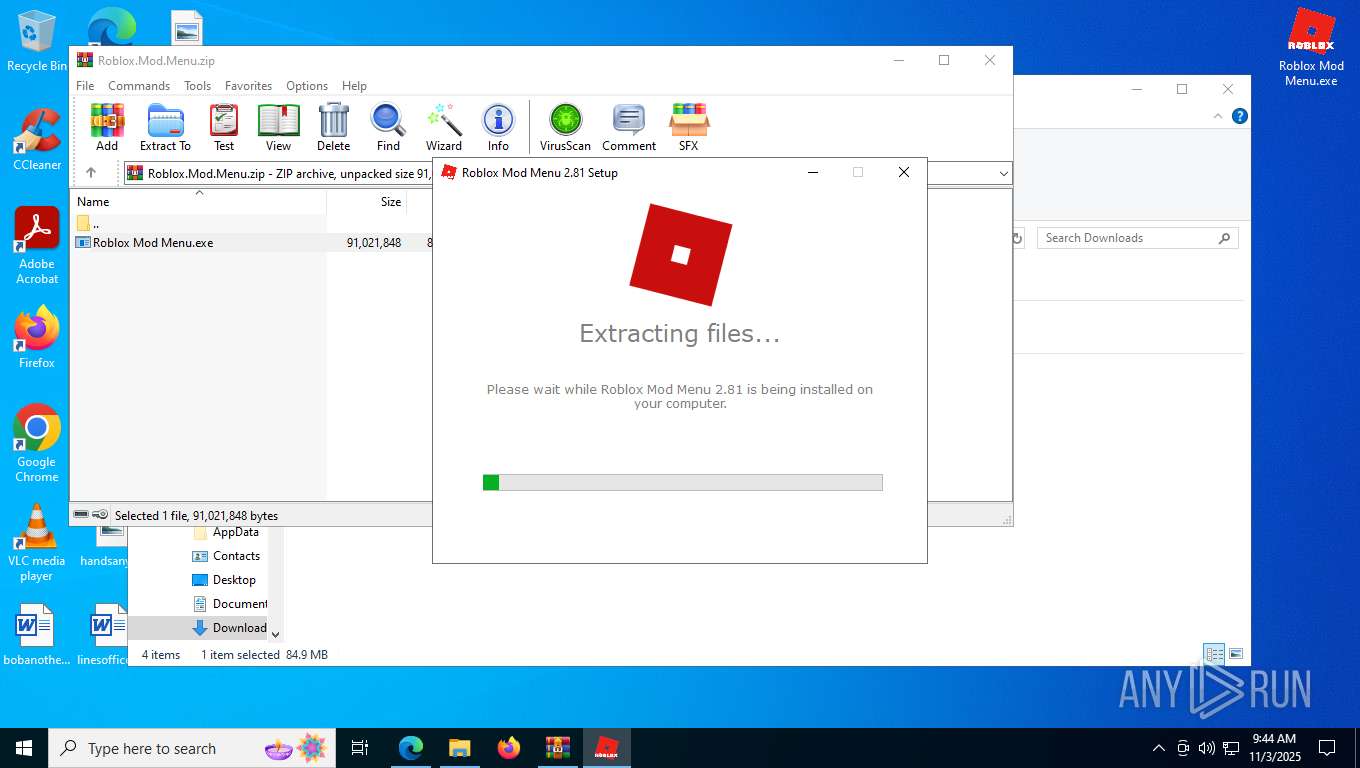
Executable content was dropped or overwritten
- Roblox Mod Menu.exe (PID: 8868)
Application launched itself
- Roblox Mod Menu.exe (PID: 8320)
INFO
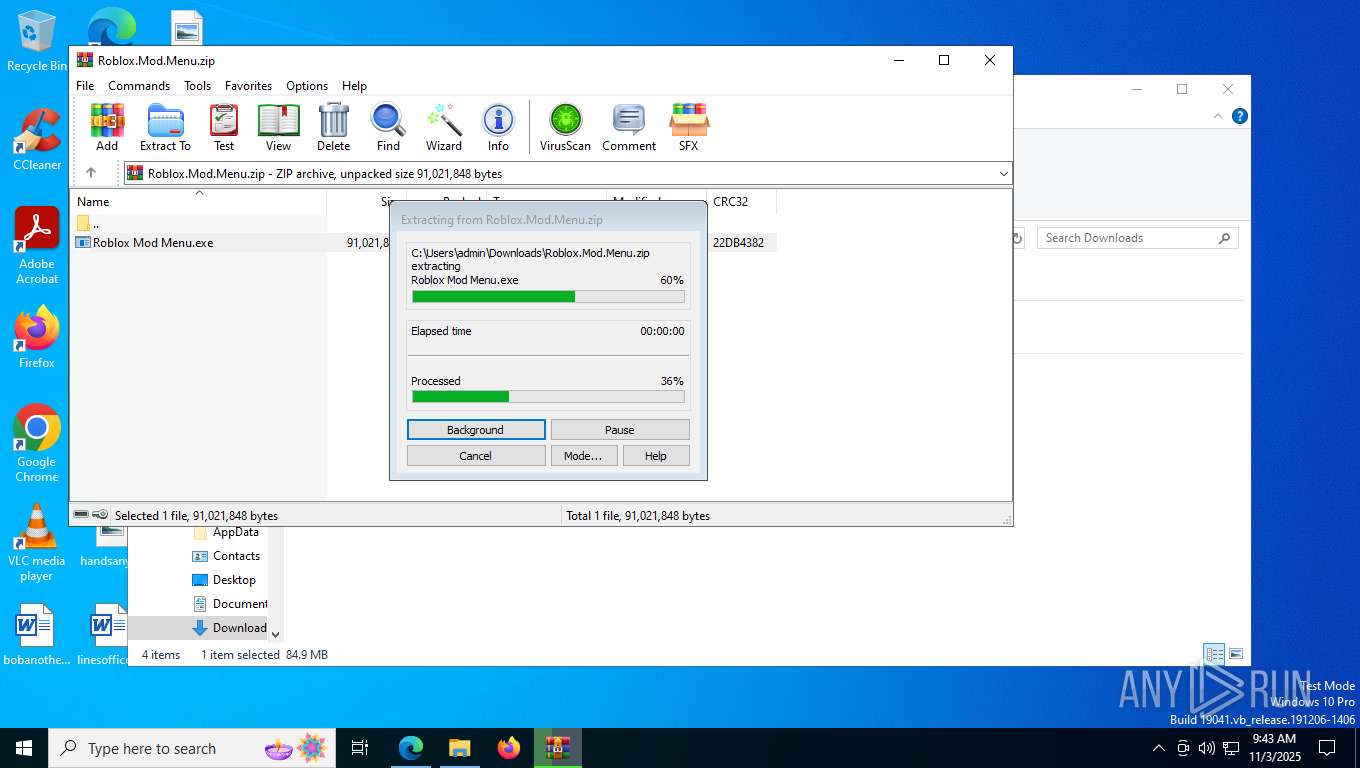
Create files in a temporary directory
- Roblox Mod Menu.exe (PID: 8868)
- Roblox Mod Menu.exe (PID: 8320)
Checks supported languages
- Roblox Mod Menu.exe (PID: 8868)
- Roblox Mod Menu.exe (PID: 8320)
- Roblox Mod Menu.exe (PID: 4324)
- Roblox Mod Menu.exe (PID: 5244)
- Roblox Mod Menu.exe (PID: 5268)
- Roblox Mod Menu.exe (PID: 6272)
Reads the computer name
- Roblox Mod Menu.exe (PID: 8868)
- Roblox Mod Menu.exe (PID: 8320)
- Roblox Mod Menu.exe (PID: 4324)
- Roblox Mod Menu.exe (PID: 5244)
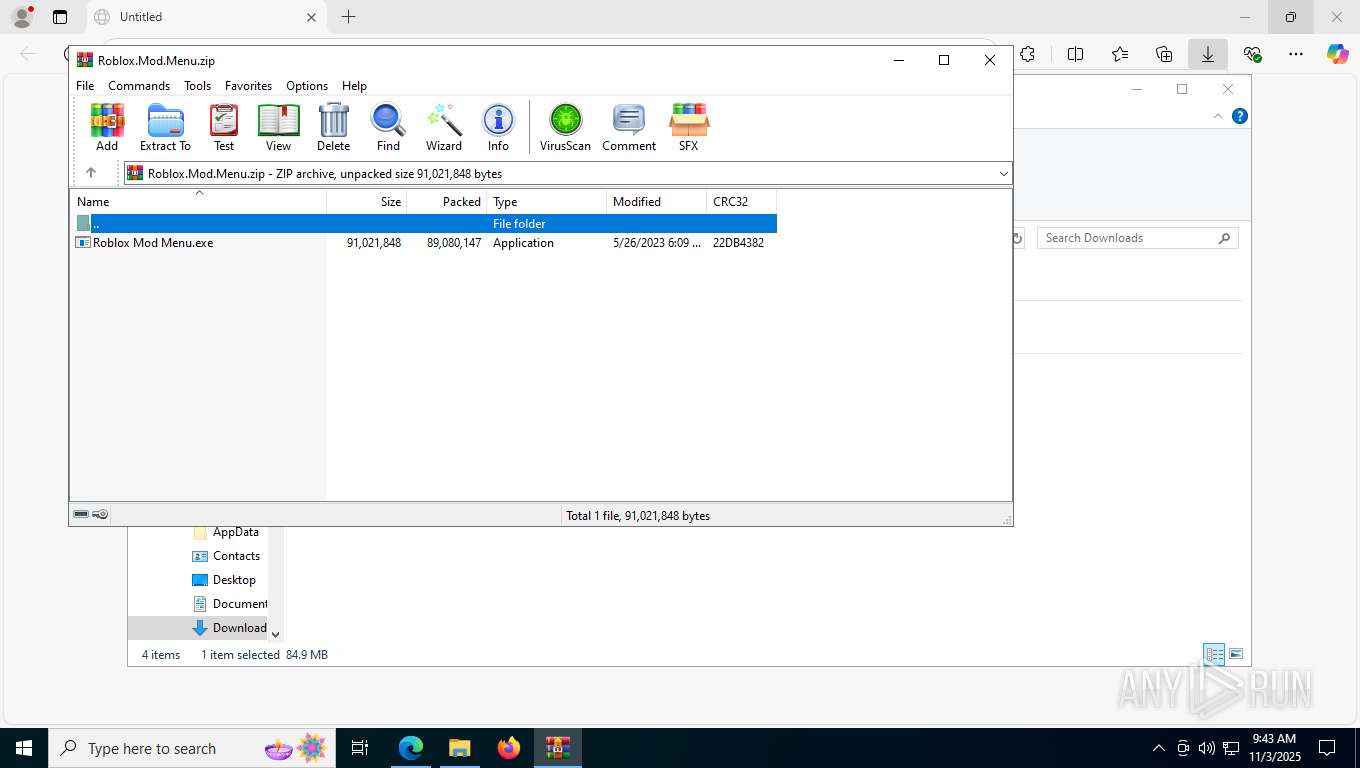
Compiled with Borland Delphi (YARA)
- Roblox Mod Menu.exe (PID: 8868)
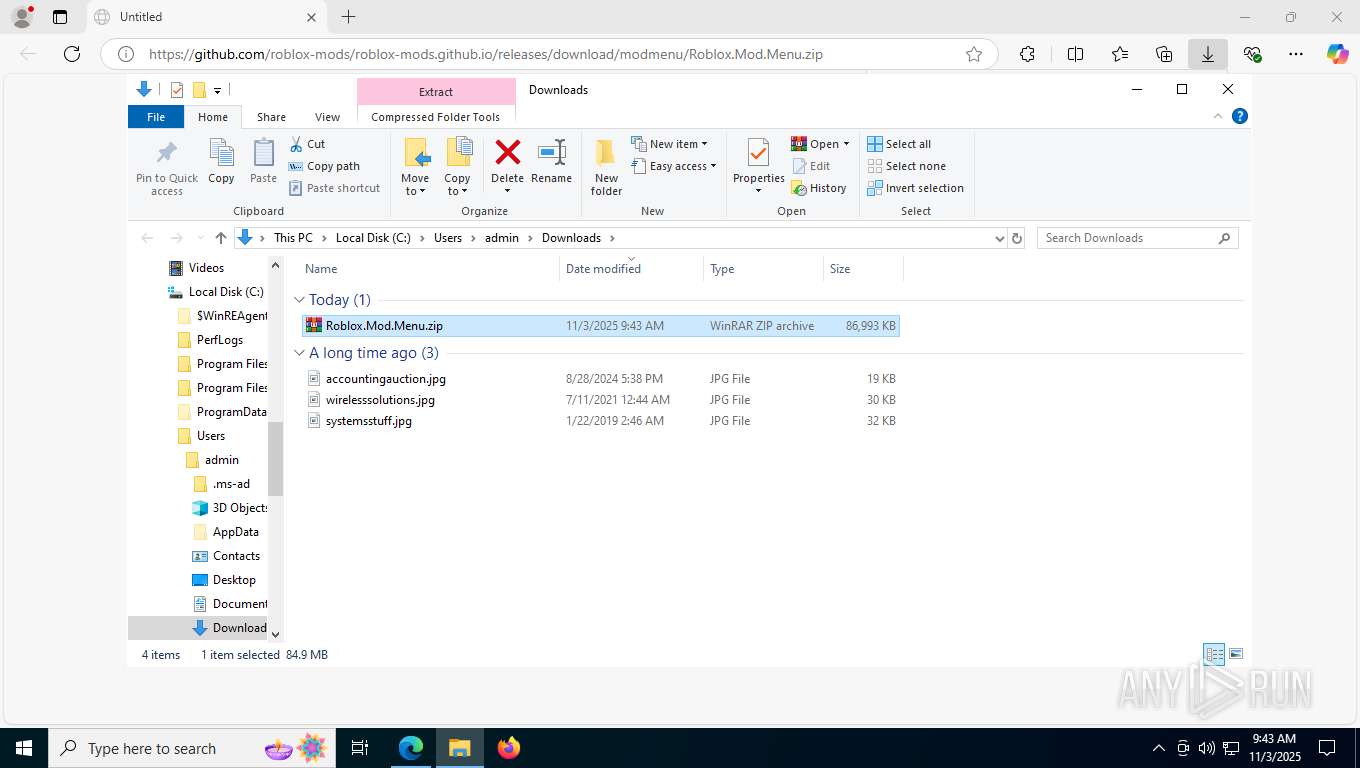
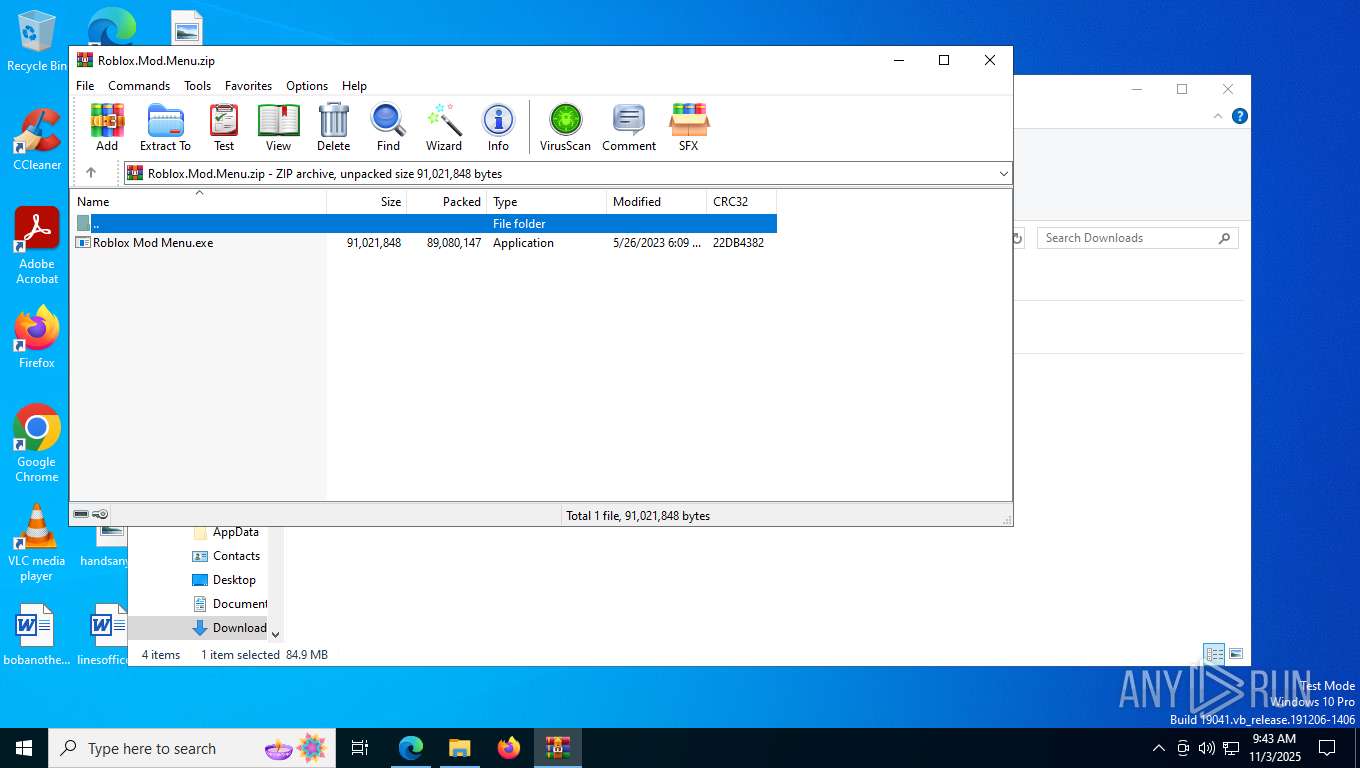
Manual execution by a user
- Roblox Mod Menu.exe (PID: 8868)
- WinRAR.exe (PID: 8784)
Application launched itself
- msedge.exe (PID: 7584)
- msedge.exe (PID: 8620)
The sample compiled with english language support
- Roblox Mod Menu.exe (PID: 8868)
Launching a file from a Registry key
- Roblox Mod Menu.exe (PID: 8868)
Process checks computer location settings
- Roblox Mod Menu.exe (PID: 8868)
- Roblox Mod Menu.exe (PID: 5268)
- Roblox Mod Menu.exe (PID: 8320)
- Roblox Mod Menu.exe (PID: 6272)
Reads product name
- Roblox Mod Menu.exe (PID: 8320)
Creates files or folders in the user directory
- Roblox Mod Menu.exe (PID: 8868)
- Roblox Mod Menu.exe (PID: 8320)
- Roblox Mod Menu.exe (PID: 5244)
Reads Environment values
- Roblox Mod Menu.exe (PID: 8320)
Checks proxy server information
- Roblox Mod Menu.exe (PID: 8320)
Reads the machine GUID from the registry
- Roblox Mod Menu.exe (PID: 8320)
Reads the software policy settings
- Roblox Mod Menu.exe (PID: 8320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
180
Monitored processes
34
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=4796,i,9876575593427424370,6870489325764548406,262144 --variations-seed-version --mojo-platform-channel-handle=5308 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 | |||||||||||||||
| 2288 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6000,i,9876575593427424370,6870489325764548406,262144 --variations-seed-version --mojo-platform-channel-handle=6056 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 | |||||||||||||||
| 2564 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6556,i,9876575593427424370,6870489325764548406,262144 --variations-seed-version --mojo-platform-channel-handle=6636 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
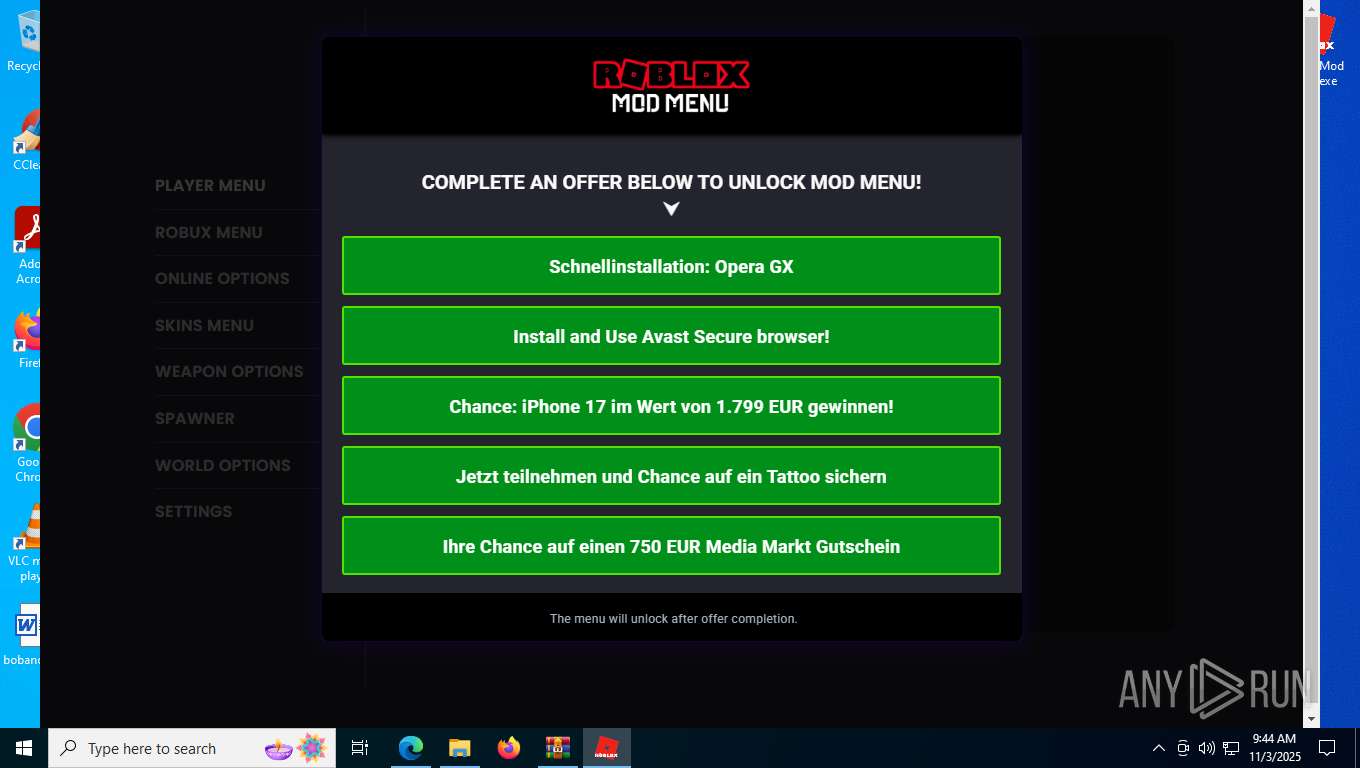
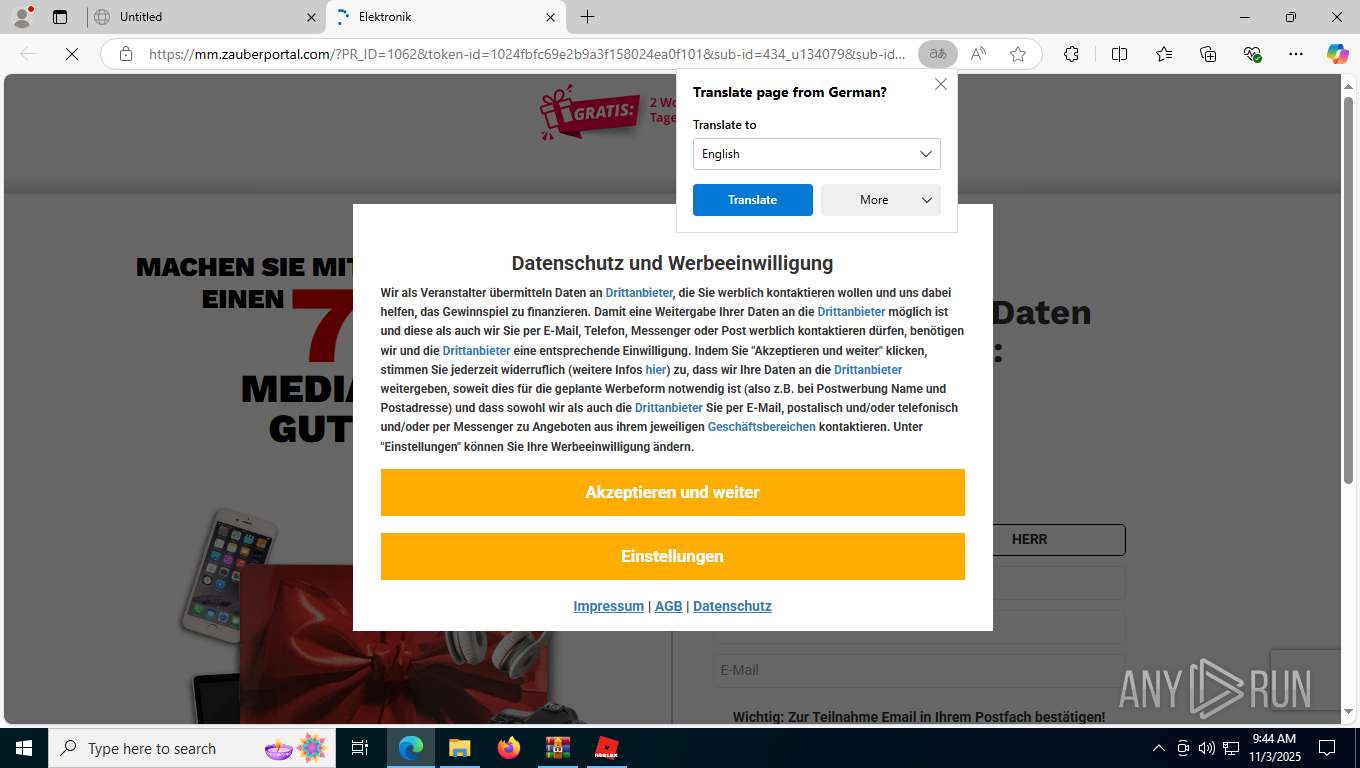
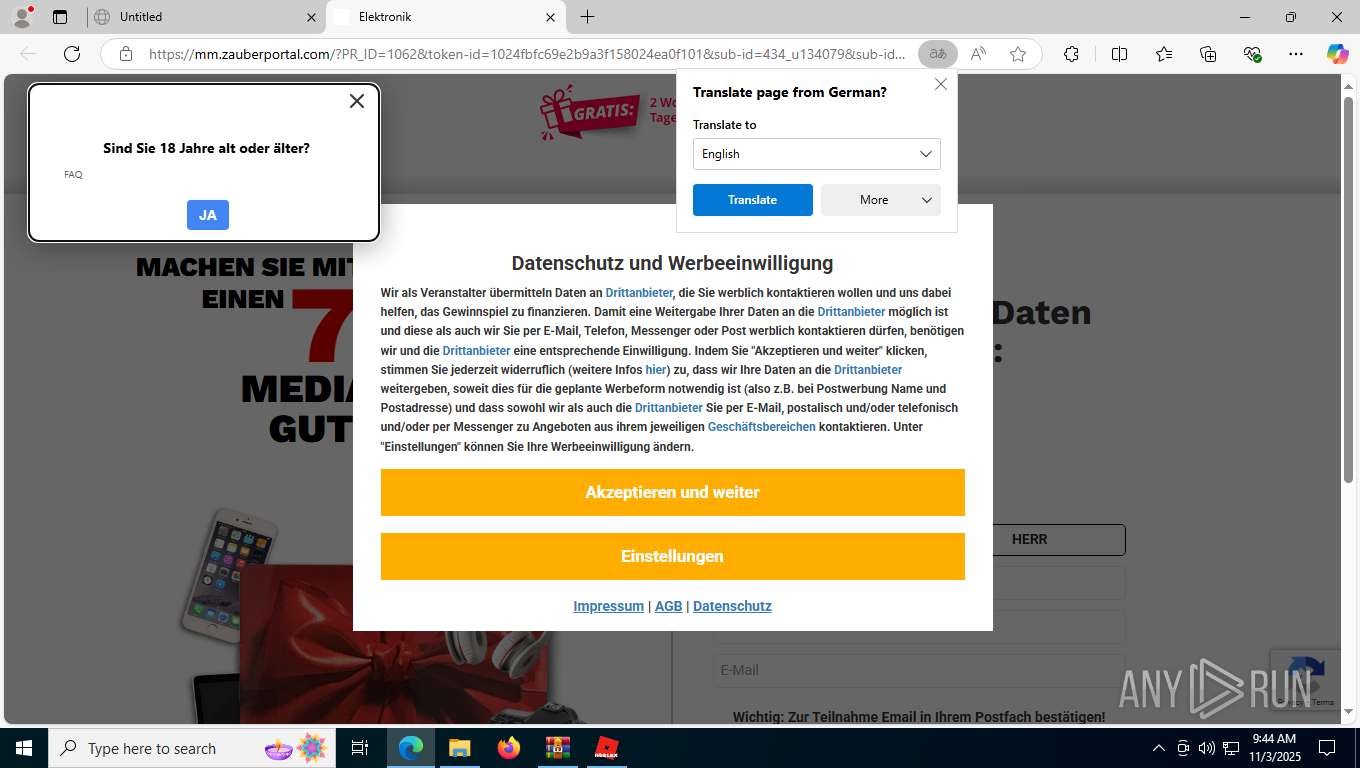
| 3956 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --edge-skip-compat-layer-relaunch --single-argument https://mob.g2trck.com/click?pid=2&offer_id=497&sub2=u134079&sub3=cl437039&sub7=rfhttps%3A%2F%2Fmodmenu.pages.dev%2F&sub8=rdmodmenu.pages.dev&sub15=24329d413bea | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4324 | "C:\Users\admin\AppData\Roaming\Roblox Mod Menu\Roblox Mod Menu.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\roblox-mod-menu-nativefier-043199" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1384 --field-trial-handle=1696,i,6275988463915873635,14401644778610149112,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Roaming\Roblox Mod Menu\Roblox Mod Menu.exe | — | Roblox Mod Menu.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: LOW Description: Roblox Mod Menu Version: 1.0.0 Modules
| |||||||||||||||
| 5244 | "C:\Users\admin\AppData\Roaming\Roblox Mod Menu\Roblox Mod Menu.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\roblox-mod-menu-nativefier-043199" --mojo-platform-channel-handle=2064 --field-trial-handle=1696,i,6275988463915873635,14401644778610149112,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Users\admin\AppData\Roaming\Roblox Mod Menu\Roblox Mod Menu.exe | Roblox Mod Menu.exe | ||||||||||||
User: admin Company: Jia Hao Integrity Level: MEDIUM Description: Roblox Mod Menu Version: 1.0.0 Modules
| |||||||||||||||
| 5268 | "C:\Users\admin\AppData\Roaming\Roblox Mod Menu\Roblox Mod Menu.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\roblox-mod-menu-nativefier-043199" --app-user-model-id=roblox-mod-menu-nativefier-043199 --app-path="C:\Users\admin\AppData\Roaming\Roblox Mod Menu\resources\app" --no-sandbox --no-zygote --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=2440 --field-trial-handle=1696,i,6275988463915873635,14401644778610149112,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Roaming\Roblox Mod Menu\Roblox Mod Menu.exe | — | Roblox Mod Menu.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: MEDIUM Description: Roblox Mod Menu Version: 1.0.0 Modules
| |||||||||||||||
| 5356 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5288,i,9876575593427424370,6870489325764548406,262144 --variations-seed-version --mojo-platform-channel-handle=5296 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 | |||||||||||||||
| 5676 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=24 --always-read-main-dll --field-trial-handle=4516,i,9876575593427424370,6870489325764548406,262144 --variations-seed-version --mojo-platform-channel-handle=6316 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 6272 | "C:\Users\admin\AppData\Roaming\Roblox Mod Menu\Roblox Mod Menu.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\roblox-mod-menu-nativefier-043199" --app-user-model-id=roblox-mod-menu-nativefier-043199 --app-path="C:\Users\admin\AppData\Roaming\Roblox Mod Menu\resources\app" --enable-sandbox --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3304 --field-trial-handle=1696,i,6275988463915873635,14401644778610149112,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Roaming\Roblox Mod Menu\Roblox Mod Menu.exe | — | Roblox Mod Menu.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: LOW Description: Roblox Mod Menu Version: 1.0.0 Modules
| |||||||||||||||
Total events
7 509
Read events
7 479
Write events
12
Delete events
18
Modification events
| (PID) Process: | (8784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (8784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\Roblox.Mod.Menu.zip | |||
| (PID) Process: | (8784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8868) Roblox Mod Menu.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Roblox Mod Menu |
Value: C:\Users\admin\AppData\Roaming\Roblox Mod Menu\Roblox Mod Menu.exe | |||
| (PID) Process: | (8320) Roblox Mod Menu.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en-US |
Value: | |||
Executable files
14
Suspicious files
349
Text files
70
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF161fe1.TMP | — | |
MD5:— | SHA256:— | |||
| 7584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF161fe1.TMP | — | |
MD5:— | SHA256:— | |||
| 7584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF161fe1.TMP | — | |
MD5:— | SHA256:— | |||
| 7584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF161ff0.TMP | — | |
MD5:— | SHA256:— | |||
| 7584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF161ff0.TMP | — | |
MD5:— | SHA256:— | |||
| 7584 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
96
DNS requests
106
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7932 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:GwUP01hbfVr_6h8iEkMea-VFWx8eIlHiBvEYhyDAA3c&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
5948 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1584 | svchost.exe | GET | 200 | 23.55.48.40:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | FR | binary | 825 b | whitelisted |
8904 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | QA | binary | 813 b | whitelisted |
8904 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | QA | binary | 401 b | whitelisted |
8904 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | QA | binary | 814 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5596 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4900 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1584 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.122.8:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
7932 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7932 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7932 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7932 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
release-assets.githubusercontent.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7932 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
2276 | svchost.exe | Misc activity | ET INFO DNS Query to Cloudflare Page Developer Domain (pages .dev) |
2276 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
2276 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
5244 | Roblox Mod Menu.exe | Misc activity | ET INFO Observed Cloudflare Page Developer Domain (pages .dev in TLS SNI) |
2276 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2276 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7932 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7932 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7932 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |