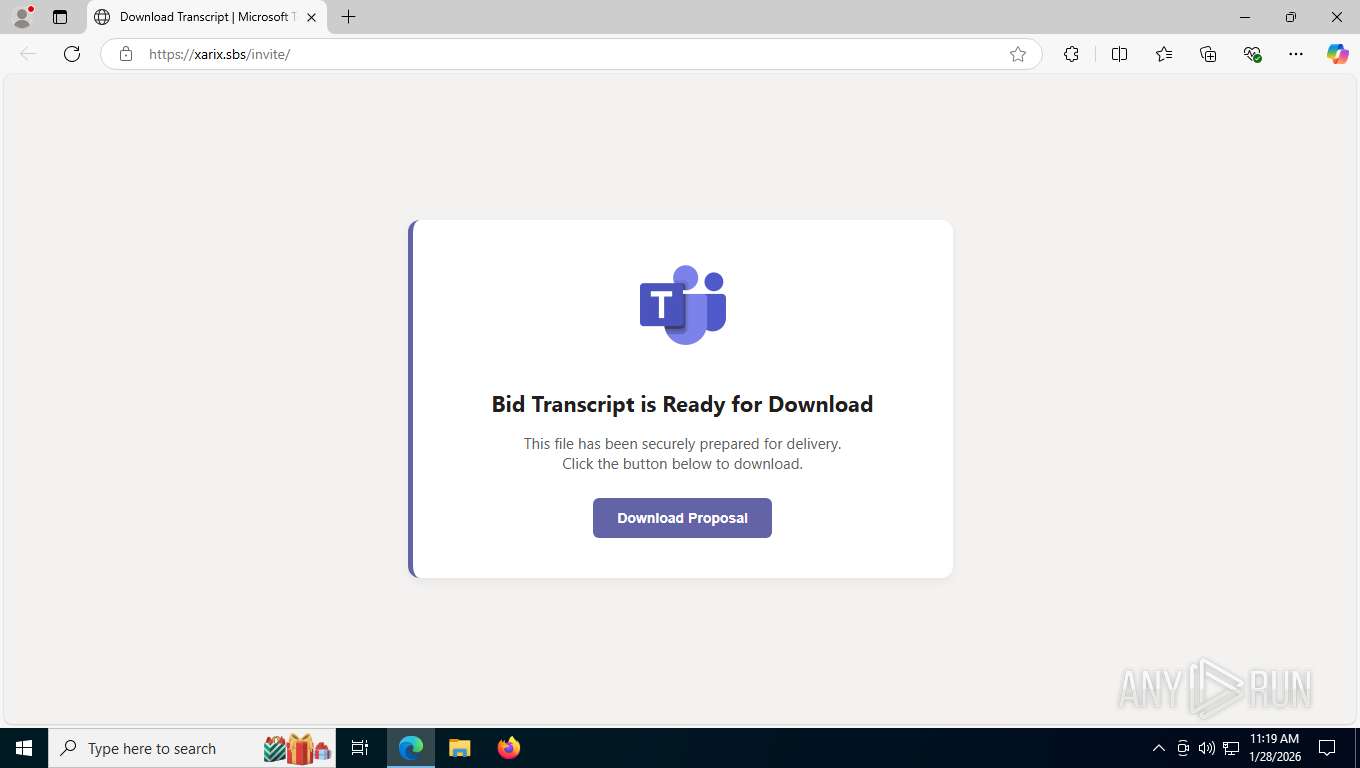
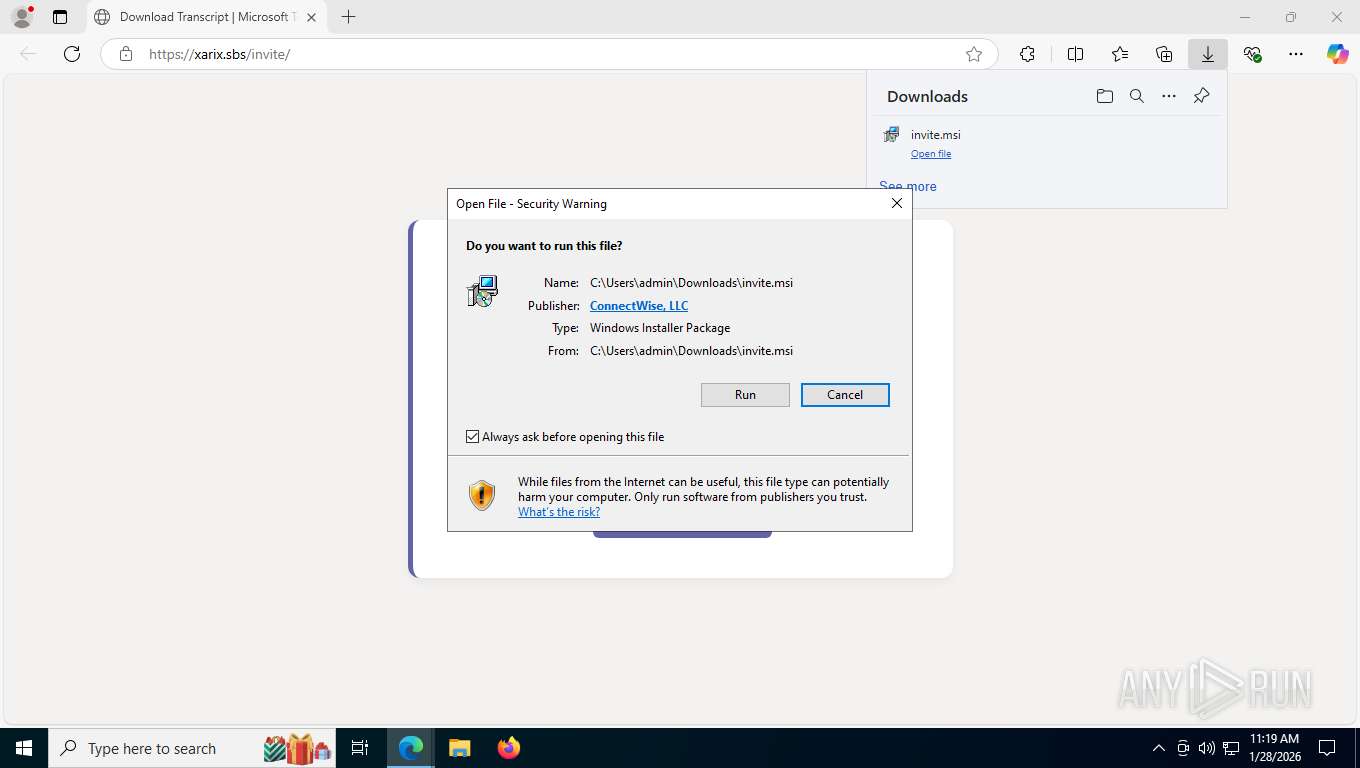
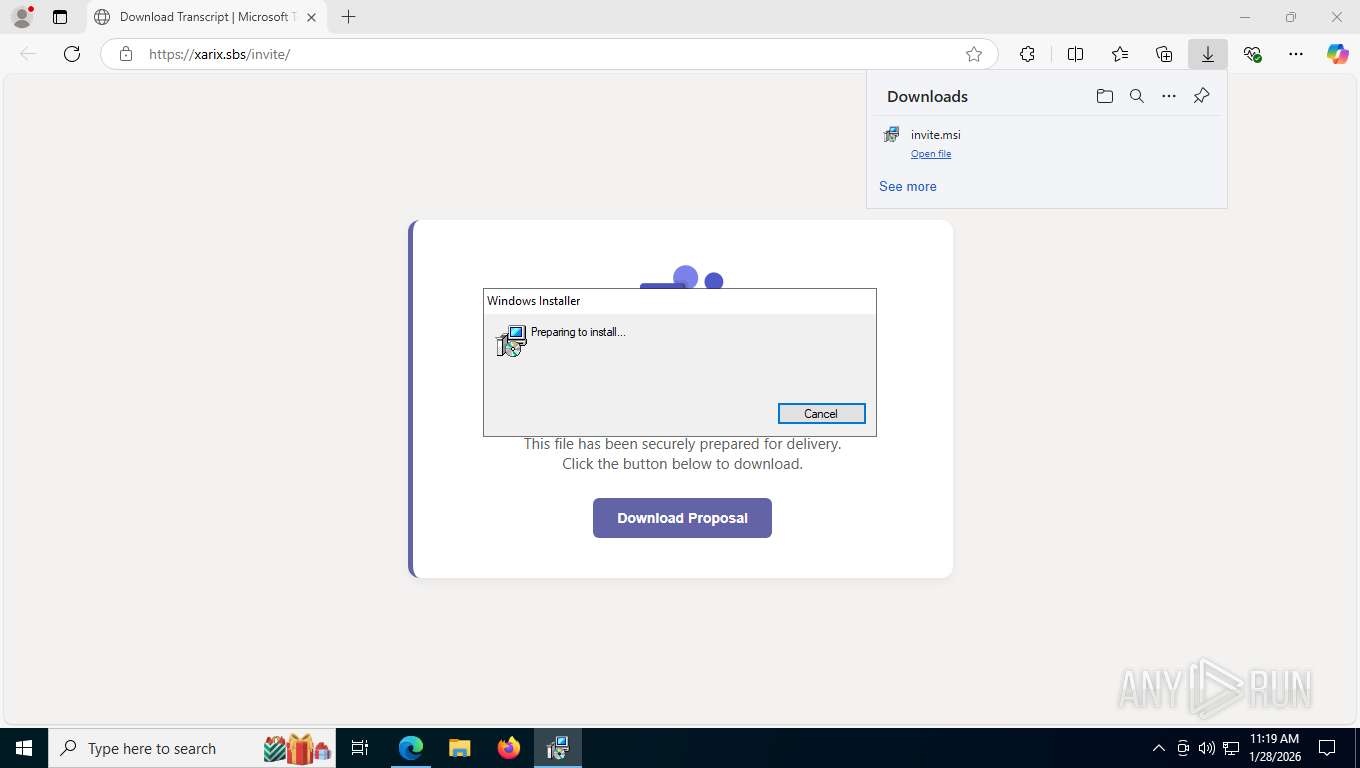
| URL: | https://xarix.sbs/invite/ |
| Full analysis: | https://app.any.run/tasks/cae79b2c-d0dc-4555-a90e-312a11ae0a7a |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2026, 16:19:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DD423B6C6F967CC436C0B3A86D289D66 |
| SHA1: | 5D4DC4C5C36F492FEBDAA52BCC9ECF8136E3C82C |
| SHA256: | 20A08AC9698E67BCA84BE55CBB8240837AD1E83D681FDC80F9D91AC28467DE41 |
| SSDEEP: | 3:N8oXMxM9n:2o0M9n |
MALICIOUS
SCREENCONNECT has been detected
- rundll32.exe (PID: 2252)
- msiexec.exe (PID: 6344)
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 6096)
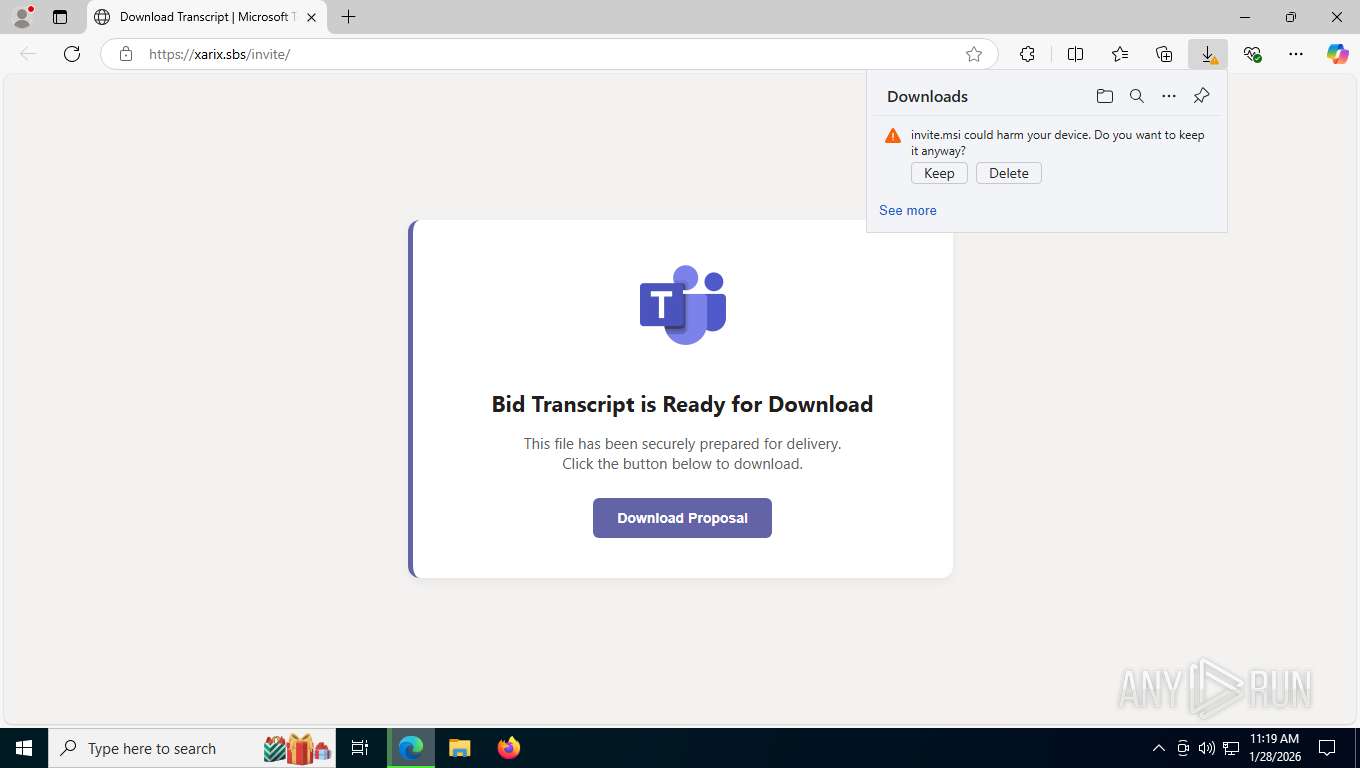
SUSPICIOUS
Executable content was dropped or overwritten
- rundll32.exe (PID: 2252)
Executes as Windows Service
- VSSVC.exe (PID: 8108)
- ScreenConnect.ClientService.exe (PID: 6096)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 6096)
- ScreenConnect.ClientService.exe (PID: 6096)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 6096)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 6096)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 6096)
INFO
Reads Environment values
- identity_helper.exe (PID: 8908)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 9068)
- ScreenConnect.ClientService.exe (PID: 6096)
- ScreenConnect.WindowsClient.exe (PID: 1908)
- ScreenConnect.WindowsClient.exe (PID: 8428)
- ScreenConnect.WindowsClient.exe (PID: 4364)
- ScreenConnect.WindowsBackstageShell.exe (PID: 8672)
- ScreenConnect.WindowsClient.exe (PID: 6948)
Application launched itself
- msedge.exe (PID: 7244)
Checks supported languages
- msiexec.exe (PID: 5828)
- identity_helper.exe (PID: 8908)
- msiexec.exe (PID: 6344)
- msiexec.exe (PID: 1388)
- ScreenConnect.ClientService.exe (PID: 6096)
- msiexec.exe (PID: 1116)
- ScreenConnect.WindowsClient.exe (PID: 8428)
- ScreenConnect.WindowsClient.exe (PID: 1908)
- ScreenConnect.WindowsBackstageShell.exe (PID: 8672)
- ScreenConnect.WindowsClient.exe (PID: 4364)
- ScreenConnect.WindowsClient.exe (PID: 6948)
Drops script file
- msedge.exe (PID: 1508)
Executable content was dropped or overwritten
- msiexec.exe (PID: 9068)
- msiexec.exe (PID: 6344)
Manages system restore points
- SrTasks.exe (PID: 9192)
Reads the computer name
- identity_helper.exe (PID: 8908)
- msiexec.exe (PID: 6344)
- msiexec.exe (PID: 5828)
- msiexec.exe (PID: 1388)
- msiexec.exe (PID: 1116)
- ScreenConnect.ClientService.exe (PID: 6096)
- ScreenConnect.WindowsClient.exe (PID: 1908)
- ScreenConnect.WindowsClient.exe (PID: 8428)
- ScreenConnect.WindowsBackstageShell.exe (PID: 8672)
- ScreenConnect.WindowsClient.exe (PID: 4364)
- ScreenConnect.WindowsClient.exe (PID: 6948)
Create files in a temporary directory
- rundll32.exe (PID: 2252)
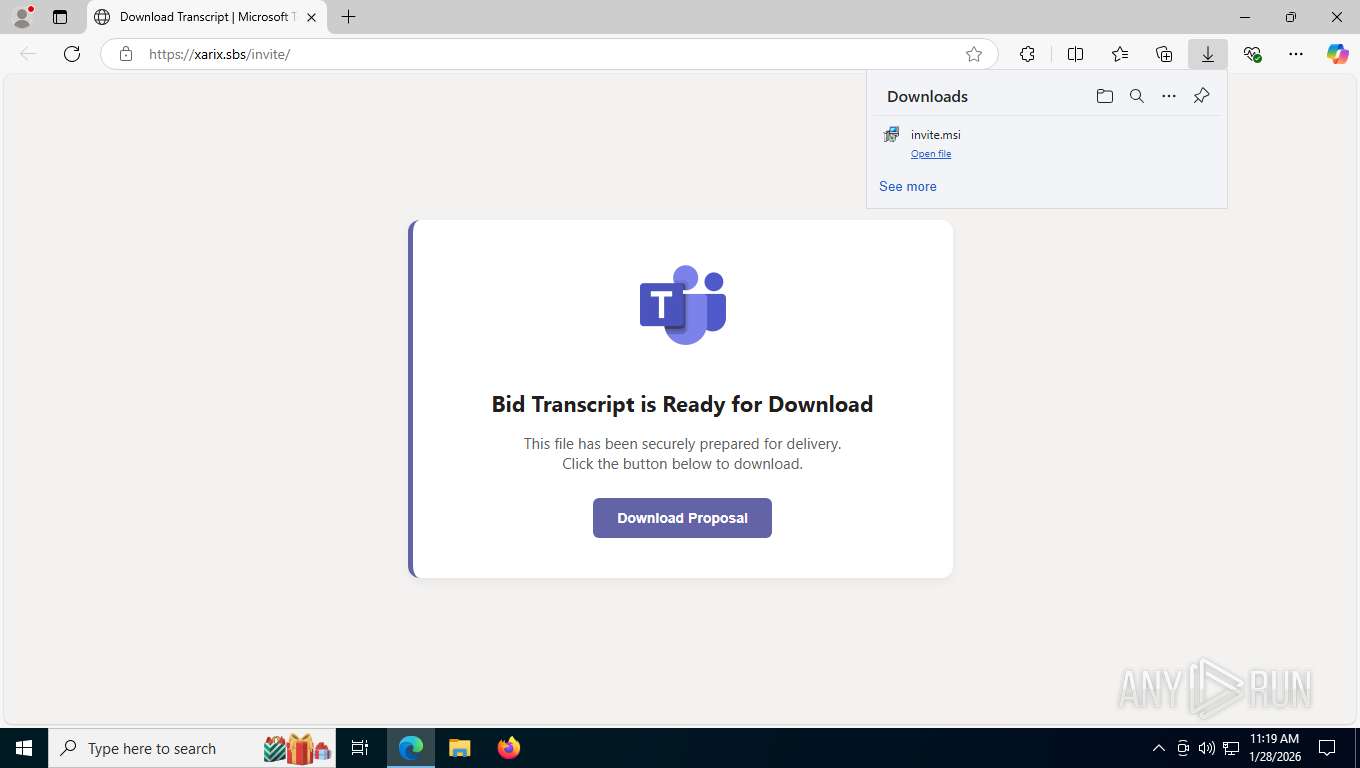
CONNECTWISE has been detected
- msiexec.exe (PID: 9068)
- ScreenConnect.ClientService.exe (PID: 6096)
- ScreenConnect.WindowsClient.exe (PID: 1908)
- ScreenConnect.WindowsClient.exe (PID: 8428)
- ScreenConnect.WindowsClient.exe (PID: 4364)
- ScreenConnect.WindowsBackstageShell.exe (PID: 8672)
- ScreenConnect.WindowsClient.exe (PID: 6948)
Reads the machine GUID from the registry
- ScreenConnect.ClientService.exe (PID: 6096)
- ScreenConnect.WindowsClient.exe (PID: 1908)
- ScreenConnect.WindowsClient.exe (PID: 8428)
- ScreenConnect.WindowsBackstageShell.exe (PID: 8672)
- ScreenConnect.WindowsClient.exe (PID: 4364)
- ScreenConnect.WindowsClient.exe (PID: 6948)
SCREENCONNECT has been detected
- ScreenConnect.ClientService.exe (PID: 6096)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 8428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
195
Monitored processes
39
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 144 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffd6f19f208,0x7ffd6f19f214,0x7ffd6f19f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1116 | C:\Windows\syswow64\MsiExec.exe -Embedding C38ACE06585A2EFABC41DC66CF1697B4 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | C:\Windows\syswow64\MsiExec.exe -Embedding DEDA233D822EB11AE3D5886A06F26957 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1508 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6492,i,659800139823193446,7804194268019111157,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6220 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1908 | "C:\Program Files (x86)\ScreenConnect Client (8aadfb6bc5694c58)\ScreenConnect.WindowsClient.exe" "RunRole" "1494ad78-33cb-4dc0-8e19-7ab7f00a59e3" "User" | C:\Program Files (x86)\ScreenConnect Client (8aadfb6bc5694c58)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Exit code: 0 Version: 25.9.5.9473 Modules
| |||||||||||||||
| 1928 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2252 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSI8C7D.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1805531 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2260 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5412,i,659800139823193446,7804194268019111157,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5216 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2372 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2228,i,659800139823193446,7804194268019111157,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2224 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4364 | "C:\Program Files (x86)\ScreenConnect Client (8aadfb6bc5694c58)\ScreenConnect.WindowsClient.exe" "RunRole" "4caadc55-7a13-46cb-a482-5fa2a188f2d7" "System" | C:\Program Files (x86)\ScreenConnect Client (8aadfb6bc5694c58)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: SYSTEM Company: ScreenConnect Software Integrity Level: SYSTEM Description: ScreenConnect Client Version: 25.9.5.9473 Modules
| |||||||||||||||
Total events
6 756
Read events
6 605
Write events
142
Delete events
9
Modification events
| (PID) Process: | (6344) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000030E0AFF17190DC01C8180000381C0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6344) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000030E0AFF17190DC01C8180000381C0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6344) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000069C9F9F17190DC01C8180000381C0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6344) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000069C9F9F17190DC01C8180000381C0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6344) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000D82AFCF17190DC01C8180000381C0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6344) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 15 | |||
| (PID) Process: | (6344) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000C58B1DF27190DC01C8180000D8100000E8030000010000000000000000000000844EE1B4BC992A48BC23F3BE6246088E00000000000000000000000000000000 | |||
| (PID) Process: | (8108) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000181527F27190DC01AC1F000050210000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8108) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000181527F27190DC01AC1F0000B01E0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8108) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 480000000000000044D532F27190DC01AC1F000050210000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
20
Suspicious files
45
Text files
250
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1b42f1.TMP | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1b42f1.TMP | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1b4310.TMP | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1b4310.TMP | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1b4320.TMP | — | |
MD5:— | SHA256:— | |||
| 7244 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
64
DNS requests
60
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5484 | msedge.exe | OPTIONS | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=T2WmUkF5ypdbhr7qPFX4NKS9Xy88AQAnjeXh49tDeiMNCcxbjDfFia%2Fa8KFd1IBlL0pAElk4SLmYf0Apx1PBSvsEQVd%2FOJNoJw%3D%3D | US | — | — | unknown |
5484 | msedge.exe | GET | 304 | 150.171.27.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
5484 | msedge.exe | GET | 304 | 172.66.47.172:443 | https://main-8xt.pages.dev/logo.png | US | — | — | unknown |
5484 | msedge.exe | GET | 200 | 104.21.49.98:443 | https://xarix.sbs/invite/ | US | html | 2.79 Kb | unknown |
5484 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 295 b | whitelisted |
5484 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:kkOSPv4Nl8JwODJSY6WGnGloXPe4REBWoJspoUpfRWE&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 101 b | whitelisted |
5484 | msedge.exe | GET | 400 | 74.125.29.95:443 | https://fonts.googleapis.com/css2?family=Segoe+UI:wght@400;600&display=swap | US | html | 6.29 Kb | whitelisted |
5484 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/autofillservice/core/page/-116760139485720518/-144684301530915628?CIdAlgoVersion=2 | US | text | 20 b | whitelisted |
5484 | msedge.exe | GET | 200 | 2.16.204.152:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | NL | text | 128 Kb | whitelisted |
5484 | msedge.exe | GET | 200 | 172.66.47.172:443 | https://main-8xt.pages.dev/logo.png | US | image | 16.8 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4336 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6416 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.204.152:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5484 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5484 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5484 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5484 | msedge.exe | 104.21.49.98:443 | xarix.sbs | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
xarix.sbs |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
main-8xt.pages.dev |
| unknown |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5484 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
5484 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
5484 | msedge.exe | Misc activity | ET INFO DNS Query to Cloudflare Page Developer Domain (pages .dev) |
5484 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
5484 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
5484 | msedge.exe | Misc activity | ET INFO Observed Cloudflare Page Developer Domain (pages .dev in TLS SNI) |
5484 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5484 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2292 | svchost.exe | Misc activity | ET REMOTE_ACCESS Observed DNS Query to Known ScreenConnect/ConnectWise Remote Desktop Service Domain |